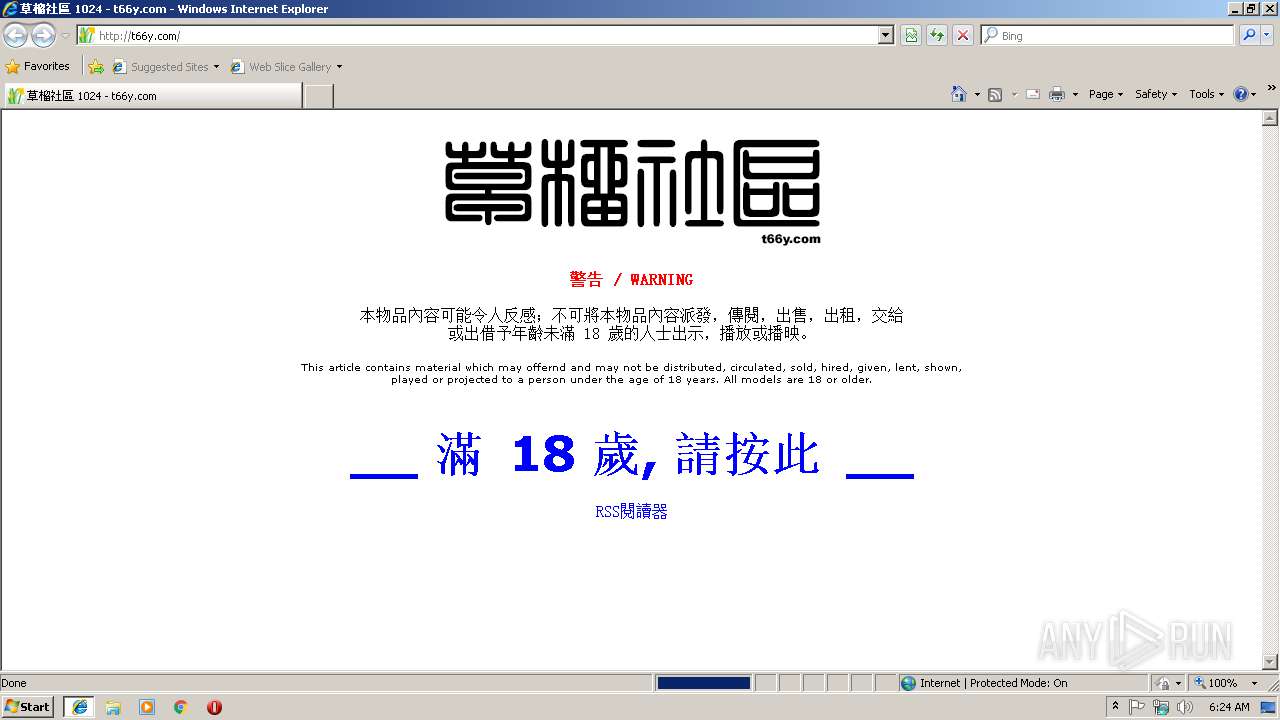
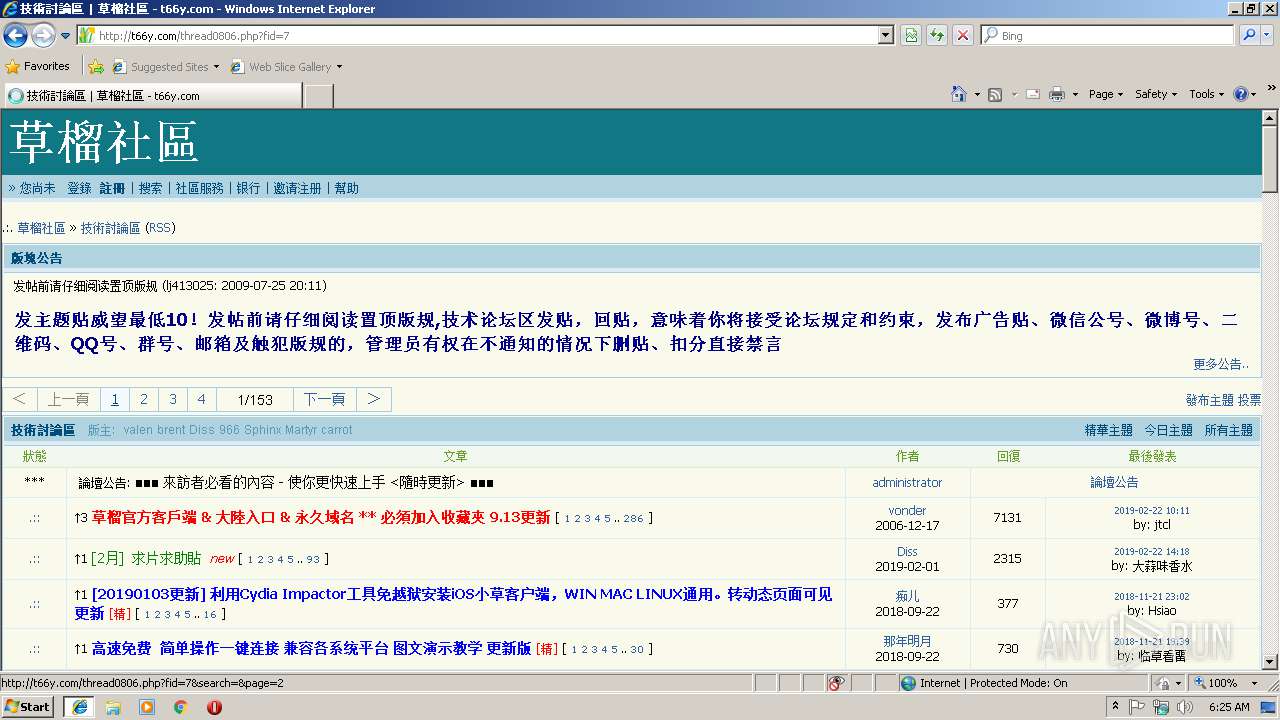
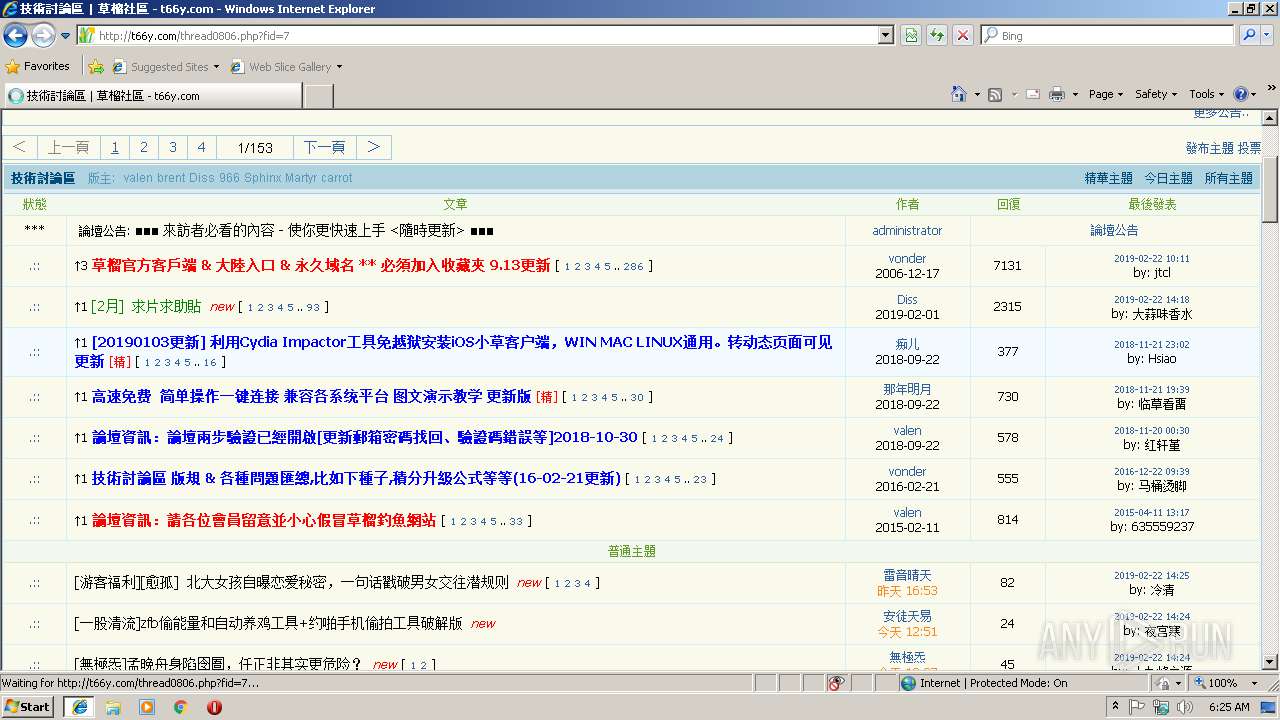
| URL: | http://t66y.com |
| Full analysis: | https://app.any.run/tasks/18503aa4-e6fd-4daa-9a89-a48c865480fa |
| Verdict: | No threats detected |
| Analysis date: | February 22, 2019, 06:24:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E629620CDF0A8E1B43768B217AFF29BB |
| SHA1: | 62F6FE8844C63D9C38B3FBE1C0AFD8C8DD04A25F |
| SHA256: | E49F71FACF69A88B525FF9AD832B02B2CE1660437B43774797D480CF2811B4E9 |
| SSDEEP: | 3:N1KKTQLKn:CKTx |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 3368)
Creates files in the user directory
- iexplore.exe (PID: 3368)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2268)
- iexplore.exe (PID: 3688)
Application launched itself
- iexplore.exe (PID: 3368)
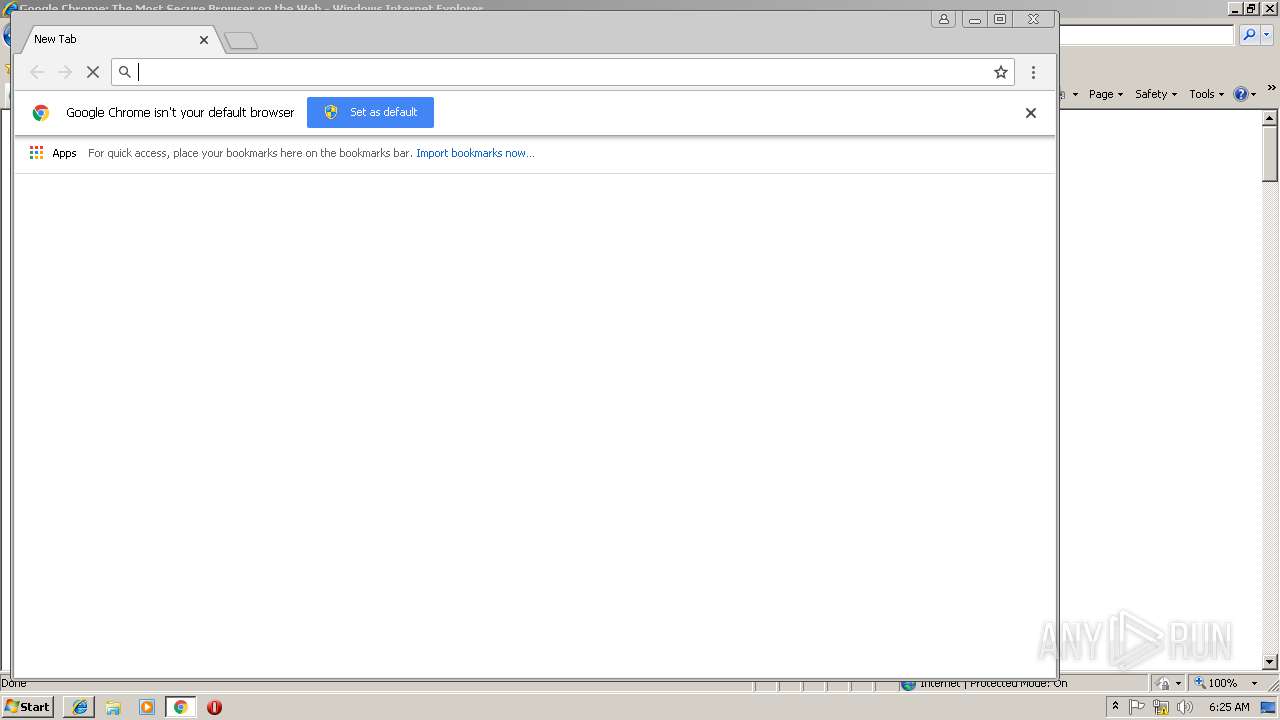
- chrome.exe (PID: 2856)
Reads Internet Cache Settings
- iexplore.exe (PID: 3688)
Reads internet explorer settings
- iexplore.exe (PID: 3688)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3368)
Changes settings of System certificates
- iexplore.exe (PID: 3368)
Reads settings of System Certificates
- chrome.exe (PID: 2856)
- iexplore.exe (PID: 3368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2268 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,8747090694028559049,7780108798324857840,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=F9108477077AC9F731D342F901500F35 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F9108477077AC9F731D342F901500F35 --renderer-client-id=6 --mojo-platform-channel-handle=1668 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,8747090694028559049,7780108798324857840,131072 --enable-features=PasswordImport --service-pipe-token=82A39C49FF3D3300AD5C253F90B54EEA --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=82A39C49FF3D3300AD5C253F90B54EEA --renderer-client-id=5 --mojo-platform-channel-handle=1928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,8747090694028559049,7780108798324857840,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=57518BC768949EEFE59CBFAA7C7F49E5 --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
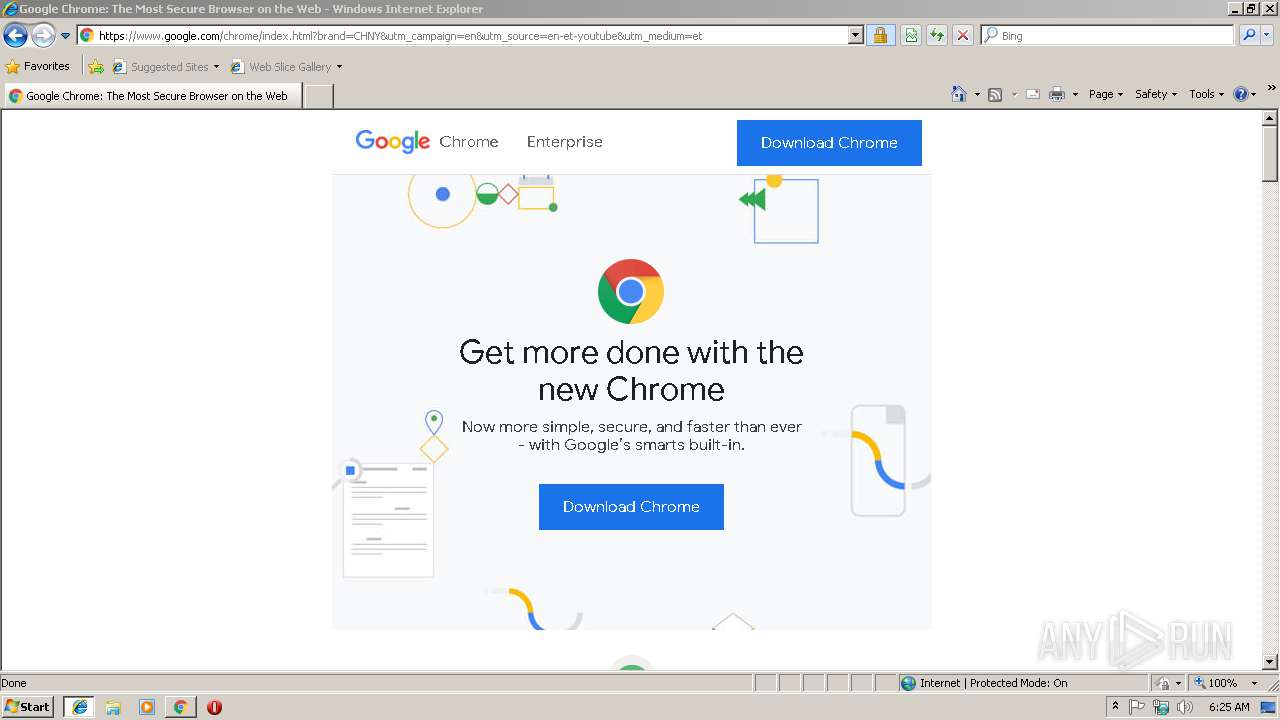
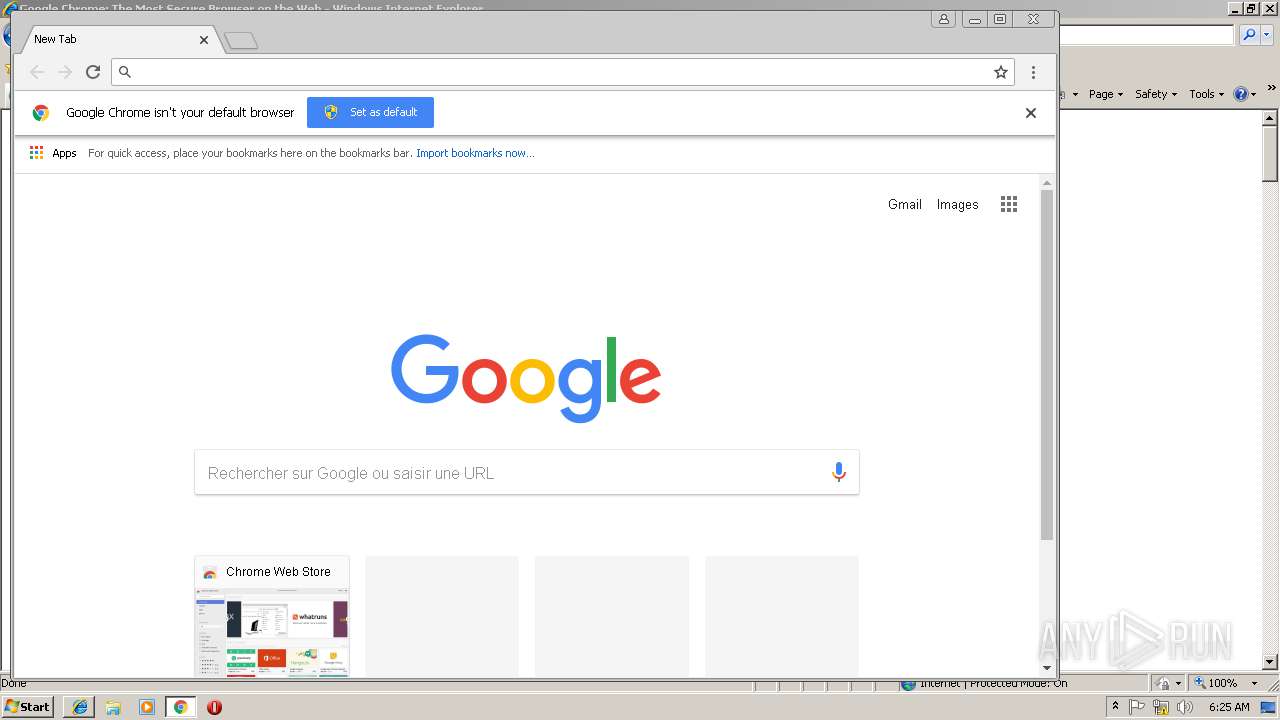
| 2856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,8747090694028559049,7780108798324857840,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=969EE9265DD58603AB0A3A86C4B3915B --mojo-platform-channel-handle=3828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3368 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2876 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,8747090694028559049,7780108798324857840,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=F3CC2021576F0D01186F36397FC8CD9C --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F3CC2021576F0D01186F36397FC8CD9C --renderer-client-id=8 --mojo-platform-channel-handle=3996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 | |||||||||||||||
| 3628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,8747090694028559049,7780108798324857840,131072 --enable-features=PasswordImport --service-pipe-token=0AFBC2A1E1EA5D06AFE079031EF6DF5A --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0AFBC2A1E1EA5D06AFE079031EF6DF5A --renderer-client-id=3 --mojo-platform-channel-handle=2128 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
680
Read events
540
Write events
133
Delete events
7
Modification events
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {8DD3BFF1-366A-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3368) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070200050016000600180032008600 | |||
Executable files
0
Suspicious files
25
Text files
118
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3688 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\style[1].css | — | |
MD5:— | SHA256:— | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@t66y[2].txt | — | |
MD5:— | SHA256:— | |||
| 3368 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3368 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\core[1].php | html | |
MD5:2923DCFC951E227E9177AB52141D4A46 | SHA256:8DD28FA766CE9D66700CC0986CF04492C8C96AC832B5F68B091B6EA3FFBB5541 | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\supported_browsers[1].txt | — | |
MD5:— | SHA256:— | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@t66y[1].txt | text | |
MD5:AF75715DA1A5D97CBFE9626B142989DF | SHA256:42FE9A84200833EF332973DA44E21300555B8D9C3178D40B2F8858BA749F4249 | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\online_v3[1].htm | html | |
MD5:7F986D3C910E735E746356FCAF705797 | SHA256:EA48BF983681F6D00A4B8BACE3FD58F4A40E005FDCA3D963FA1F0254FC221700 | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\stat[1].php | text | |
MD5:C45D083107A6176EB423931F29937A31 | SHA256:06A2A8797061B80266FCF740B4CF0370DAD3601E0B322076E7069B0BB01FDFB4 | |||
| 3688 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\thread0806[1].htm | html | |
MD5:9267609AC9143A4E63FCCE4685AC29BF | SHA256:48277AA8E1F980E27188100F530D4C86C0D925BA3FE282DEC94DAD773CE3F336 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
75
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
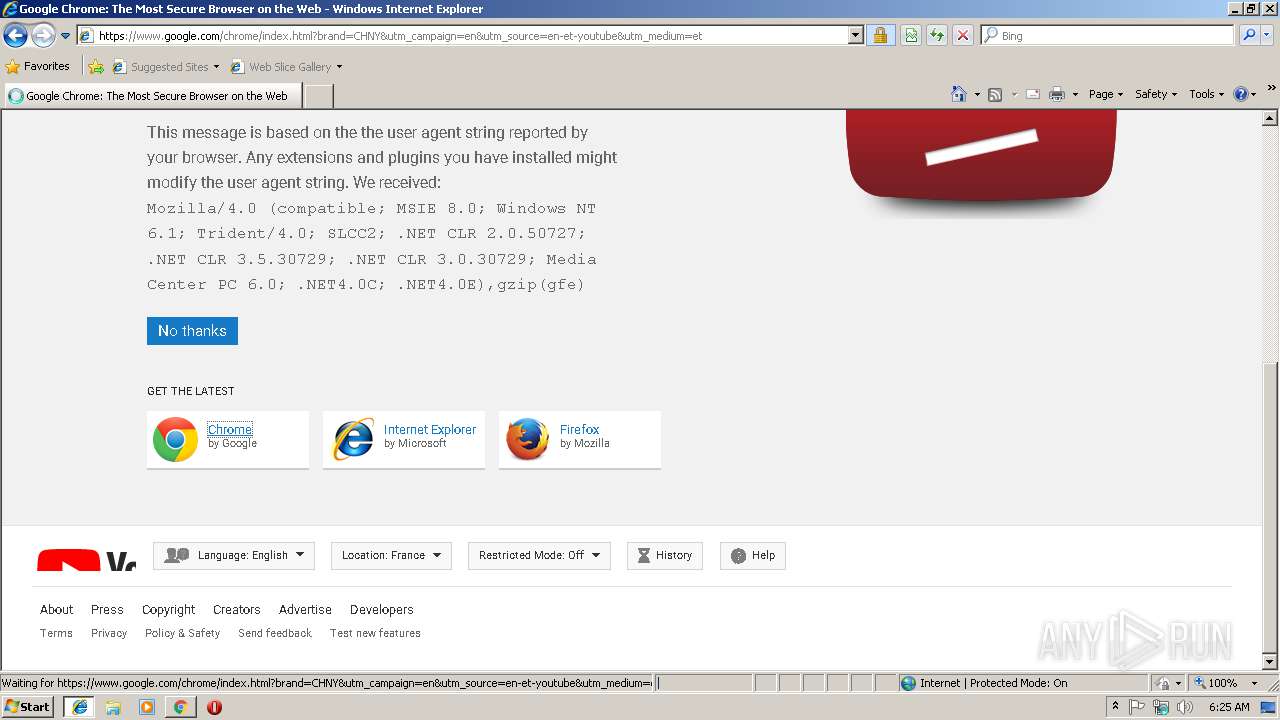
3688 | iexplore.exe | GET | 200 | 104.25.32.112:80 | http://t66y.com/ | US | html | 920 b | whitelisted |
3688 | iexplore.exe | GET | 200 | 104.25.32.112:80 | http://t66y.com/index.gif | US | image | 4.31 Kb | whitelisted |
3688 | iexplore.exe | GET | 200 | 104.27.3.107:80 | http://www.viidii.info/web/style.css?v=2.0263 | US | text | 1.63 Kb | shared |
3688 | iexplore.exe | GET | 200 | 104.25.32.112:80 | http://t66y.com/index.php | US | html | 4.02 Kb | whitelisted |
3368 | iexplore.exe | GET | 200 | 104.25.32.112:80 | http://t66y.com/favicon.ico | US | image | 2.53 Kb | whitelisted |
3688 | iexplore.exe | GET | 200 | 42.81.4.102:80 | http://s103.cnzz.com/stat.php?id=950900&web_id=950900&online=1&show=line | CN | text | 11.4 Kb | whitelisted |
3688 | iexplore.exe | GET | 200 | 203.119.128.195:80 | http://hzs6.cnzz.com/stat.htm?id=950900&r=http%3A%2F%2Ft66y.com%2F&lg=en-us&ntime=none&cnzz_eid=1750078734-1550816088-http%3A%2F%2Ft66y.com%2F&showp=1280x720&t=%E8%8D%89%E6%A6%B4%E7%A4%BE%E5%8D%80%20-%20t66y.com&umuuid=16913e0ddf7355-0dc18978382e5-44703418-e1000-16913e0de07890&h=1&rnd=567882043 | CN | text | 22 b | suspicious |
3688 | iexplore.exe | GET | 200 | 104.27.3.107:80 | http://www.viidii.info/web/style.css?v=2.0263 | US | text | 1.63 Kb | shared |
3688 | iexplore.exe | GET | — | 42.81.4.101:80 | http://c.cnzz.com/core.php?web_id=950900&show=line&online=1&t=z | CN | — | — | whitelisted |
3688 | iexplore.exe | GET | 200 | 125.76.247.199:80 | http://online.cnzz.com/online/online_v3.php?id=950900&h=hzs6.cnzz.com&on=1&s=line | CN | html | 321 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3368 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3688 | iexplore.exe | 104.25.32.112:80 | t66y.com | Cloudflare Inc | US | shared |
3688 | iexplore.exe | 104.27.3.107:80 | www.viidii.info | Cloudflare Inc | US | shared |
3368 | iexplore.exe | 104.25.32.112:80 | t66y.com | Cloudflare Inc | US | shared |
3688 | iexplore.exe | 42.81.4.101:80 | s103.cnzz.com | Yueyang | CN | unknown |
3688 | iexplore.exe | 42.81.4.102:80 | s103.cnzz.com | Yueyang | CN | unknown |
3688 | iexplore.exe | 203.119.128.195:80 | hzs6.cnzz.com | — | CN | malicious |
3688 | iexplore.exe | 125.76.247.199:80 | online.cnzz.com | China Telecom (Group) | CN | unknown |
3368 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
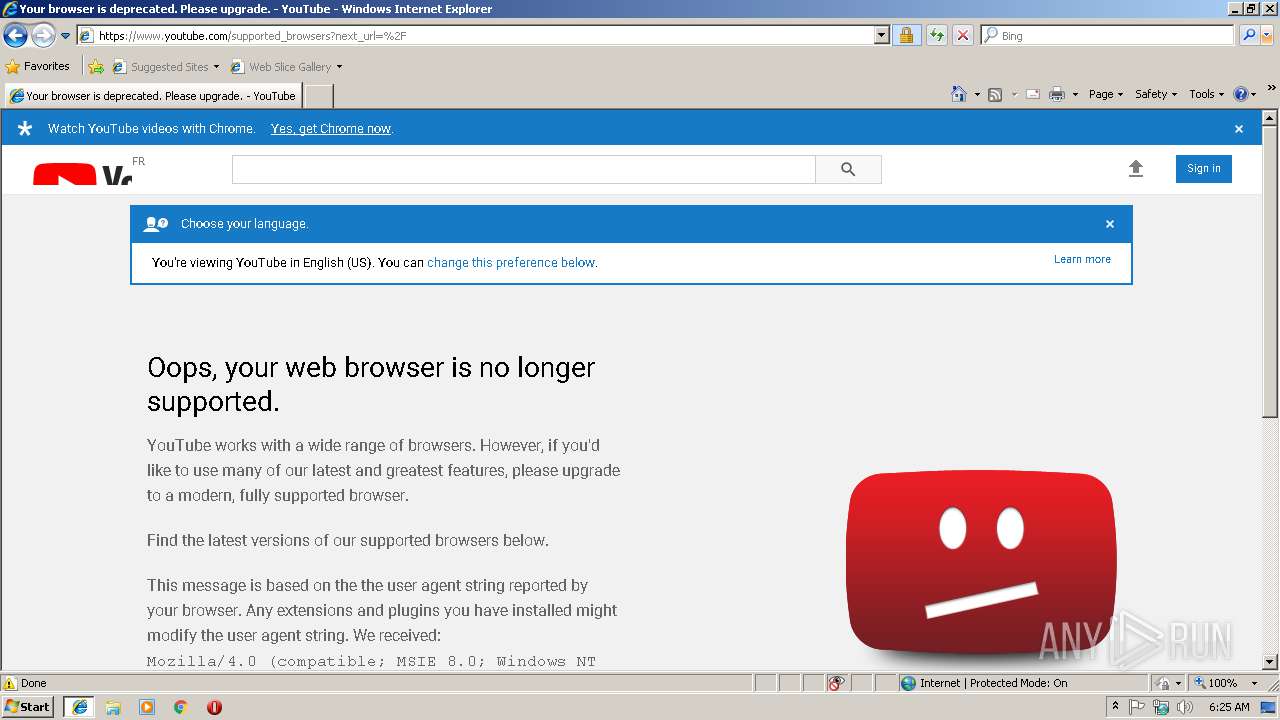
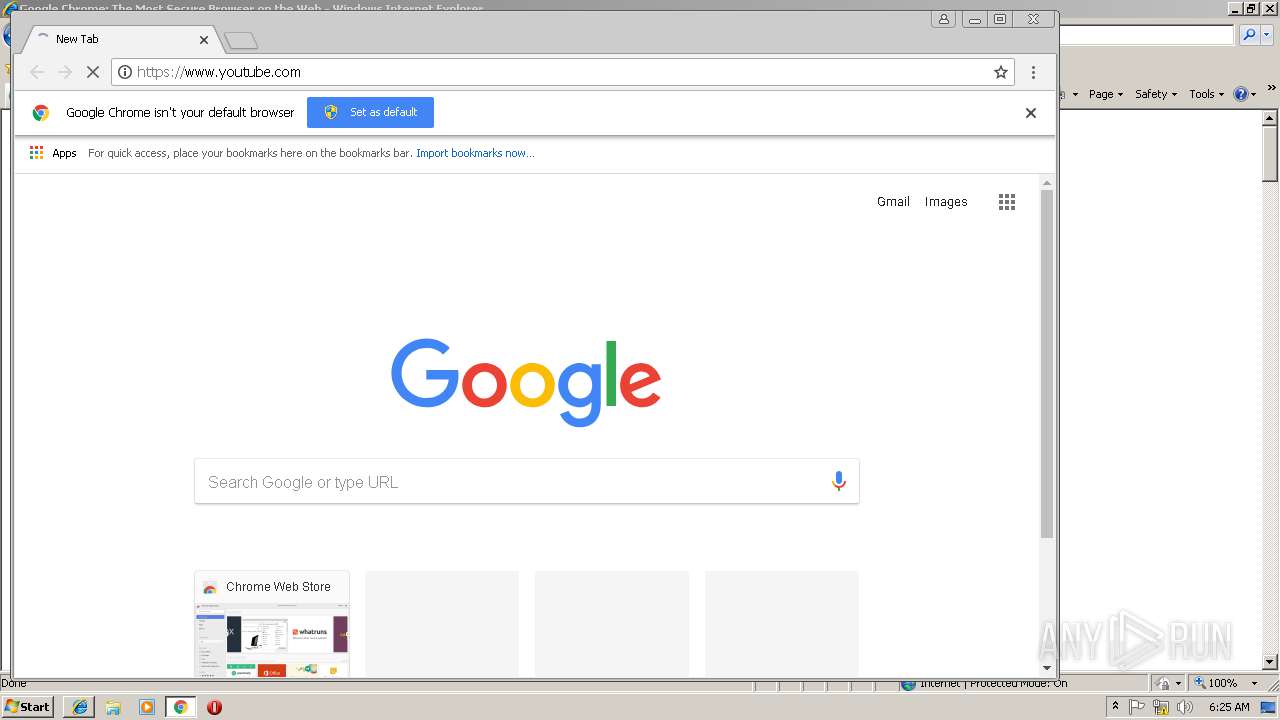
3688 | iexplore.exe | 172.217.22.14:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
t66y.com |
| whitelisted |
www.viidii.info |
| unknown |
s103.cnzz.com |
| unknown |
c.cnzz.com |
| whitelisted |
hzs6.cnzz.com |
| suspicious |
online.cnzz.com |
| suspicious |
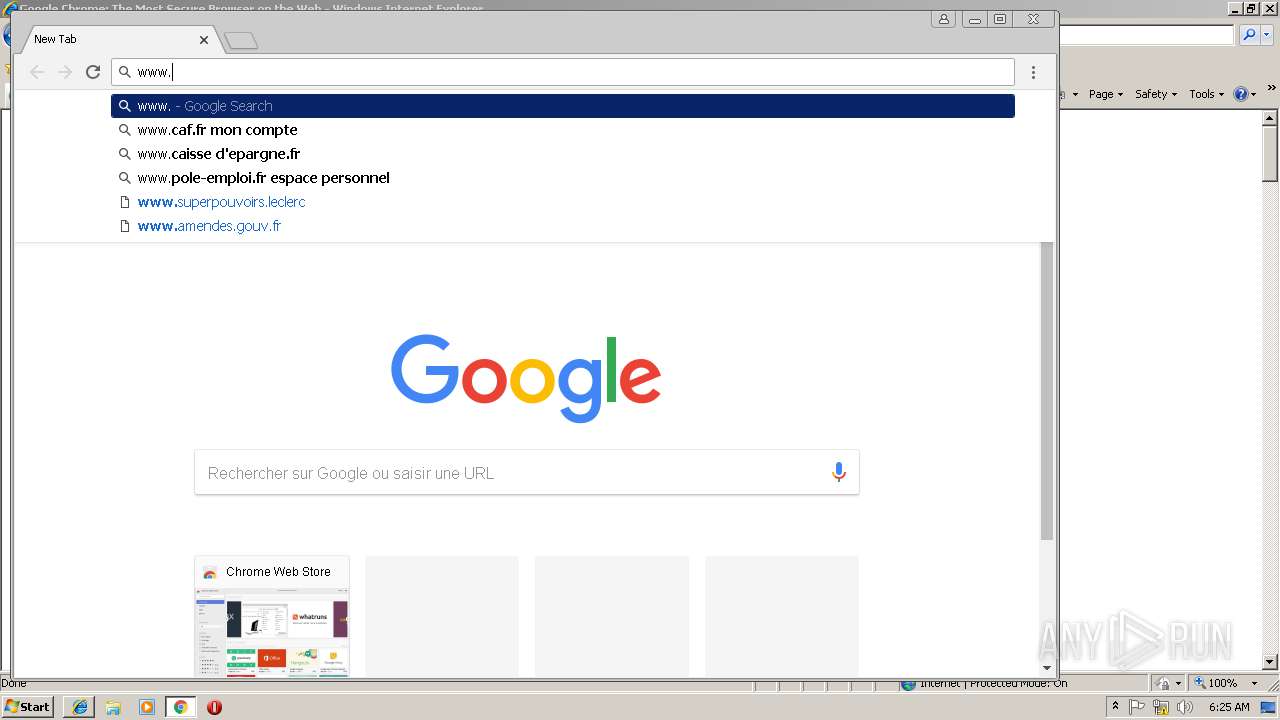
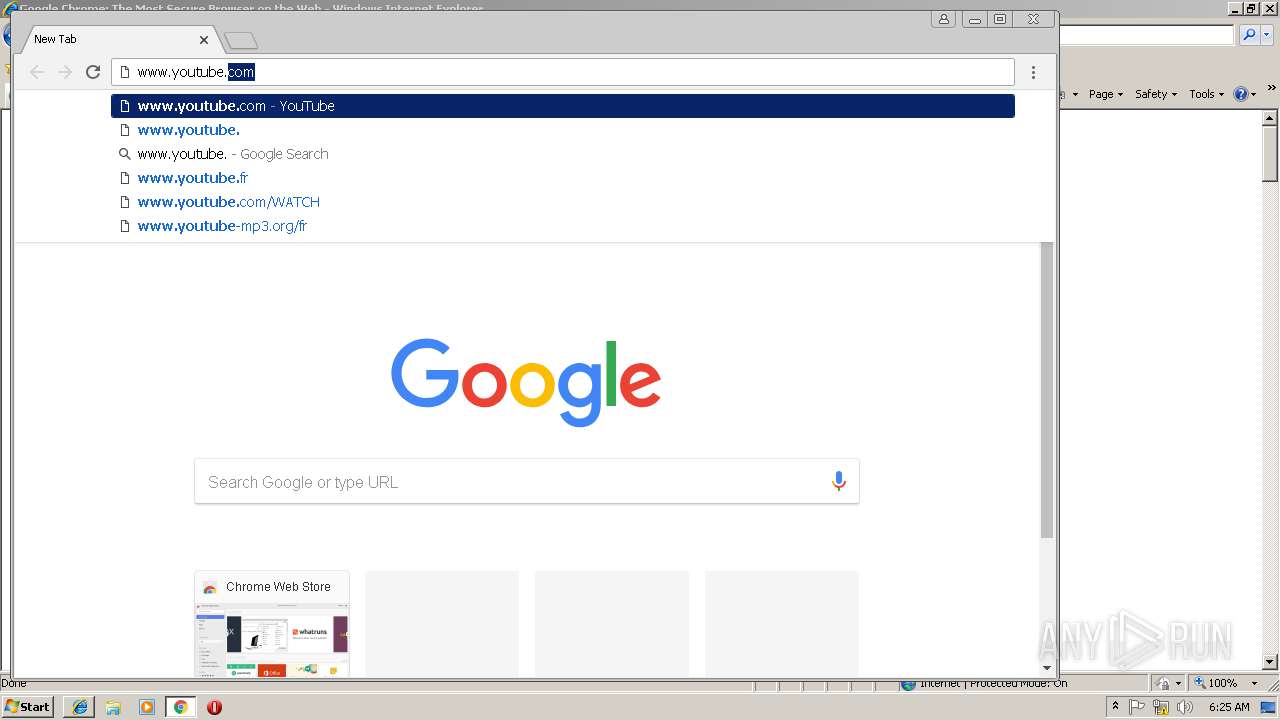
www.youtube.com |
| whitelisted |
s.ytimg.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |