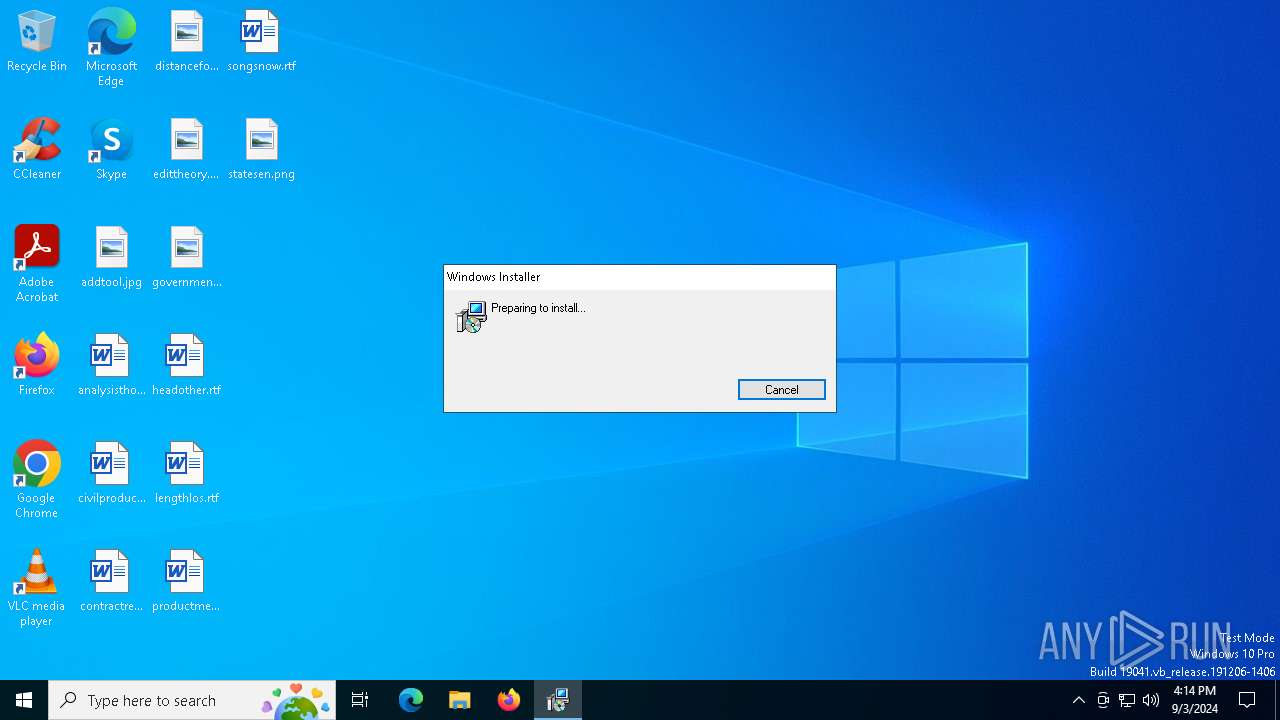
| File name: | BTC-Connect.ClientSetup.exe |
| Full analysis: | https://app.any.run/tasks/6177d530-dbb1-4487-9ea1-b990bb4804ce |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | September 03, 2024, 16:14:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FFB8FEDA07A7ECEC6F8C80966EBA6046 |
| SHA1: | 349C28F9AA90E1F117DBF5A1099352AB8A567E60 |
| SHA256: | E49DA7D5B85635C2C79EDA1408012275EC665B1A1DB1B186578C1A0B11BFB7D5 |
| SSDEEP: | 98304:79cKSTtJtOytH9awXB0DXe3S+5OmxlGwP3AW5JTGG0DR/WdiG+CeXyEMWISBYFxS:cDAE |
MALICIOUS
Connects to the CnC server
- ScreenConnect.ClientService.exe (PID: 6108)
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 6108)
SUSPICIOUS
Reads security settings of Internet Explorer
- BTC-Connect.ClientSetup.exe (PID: 3984)
- ScreenConnect.WindowsClient.exe (PID: 7084)
- ScreenConnect.ClientService.exe (PID: 6108)
- ScreenConnect.WindowsClient.exe (PID: 3672)
The process creates files with name similar to system file names
- msiexec.exe (PID: 5276)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 5276)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 6108)
- VSSVC.exe (PID: 6520)
Executable content was dropped or overwritten
- rundll32.exe (PID: 1688)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5276)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 6108)
There is functionality for taking screenshot (YARA)
- ScreenConnect.ClientService.exe (PID: 6108)
- ScreenConnect.WindowsClient.exe (PID: 7084)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 6108)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 6108)
Reads the date of Windows installation
- BTC-Connect.ClientSetup.exe (PID: 3984)
INFO
Reads the machine GUID from the registry
- BTC-Connect.ClientSetup.exe (PID: 3984)
- ScreenConnect.WindowsClient.exe (PID: 7084)
- ScreenConnect.ClientService.exe (PID: 6108)
- ScreenConnect.WindowsClient.exe (PID: 3672)
Reads the computer name
- BTC-Connect.ClientSetup.exe (PID: 3984)
- msiexec.exe (PID: 5276)
- msiexec.exe (PID: 2768)
- ScreenConnect.ClientService.exe (PID: 6108)
- ScreenConnect.WindowsClient.exe (PID: 7084)
- msiexec.exe (PID: 2464)
- ScreenConnect.WindowsClient.exe (PID: 3672)
- msiexec.exe (PID: 5244)
Checks supported languages
- BTC-Connect.ClientSetup.exe (PID: 3984)
- ScreenConnect.ClientService.exe (PID: 6108)
- msiexec.exe (PID: 2768)
- ScreenConnect.WindowsClient.exe (PID: 7084)
- msiexec.exe (PID: 2464)
- ScreenConnect.WindowsClient.exe (PID: 3672)
- msiexec.exe (PID: 5244)
- msiexec.exe (PID: 5276)
Process checks computer location settings
- BTC-Connect.ClientSetup.exe (PID: 3984)
Create files in a temporary directory
- BTC-Connect.ClientSetup.exe (PID: 3984)
- rundll32.exe (PID: 1688)
The process uses the downloaded file
- BTC-Connect.ClientSetup.exe (PID: 3984)
- ScreenConnect.ClientService.exe (PID: 6108)
- ScreenConnect.WindowsClient.exe (PID: 3672)
- ScreenConnect.WindowsClient.exe (PID: 7084)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4876)
- msiexec.exe (PID: 5276)
Creates a software uninstall entry
- msiexec.exe (PID: 5276)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 3672)
Reads the software policy settings
- slui.exe (PID: 6988)
- slui.exe (PID: 4436)
Checks proxy server information
- slui.exe (PID: 4436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:11:18 20:10:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 45568 |
| InitializedDataSize: | 5308416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14ad |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
149
Monitored processes
17
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1688 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSICB28.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1231765 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2464 | C:\Windows\syswow64\MsiExec.exe -Embedding 10B7FD1DA89225839BD690CBB0F86E90 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2768 | C:\Windows\syswow64\MsiExec.exe -Embedding E78B01E83F2C379BACCA8BB154AB44A7 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
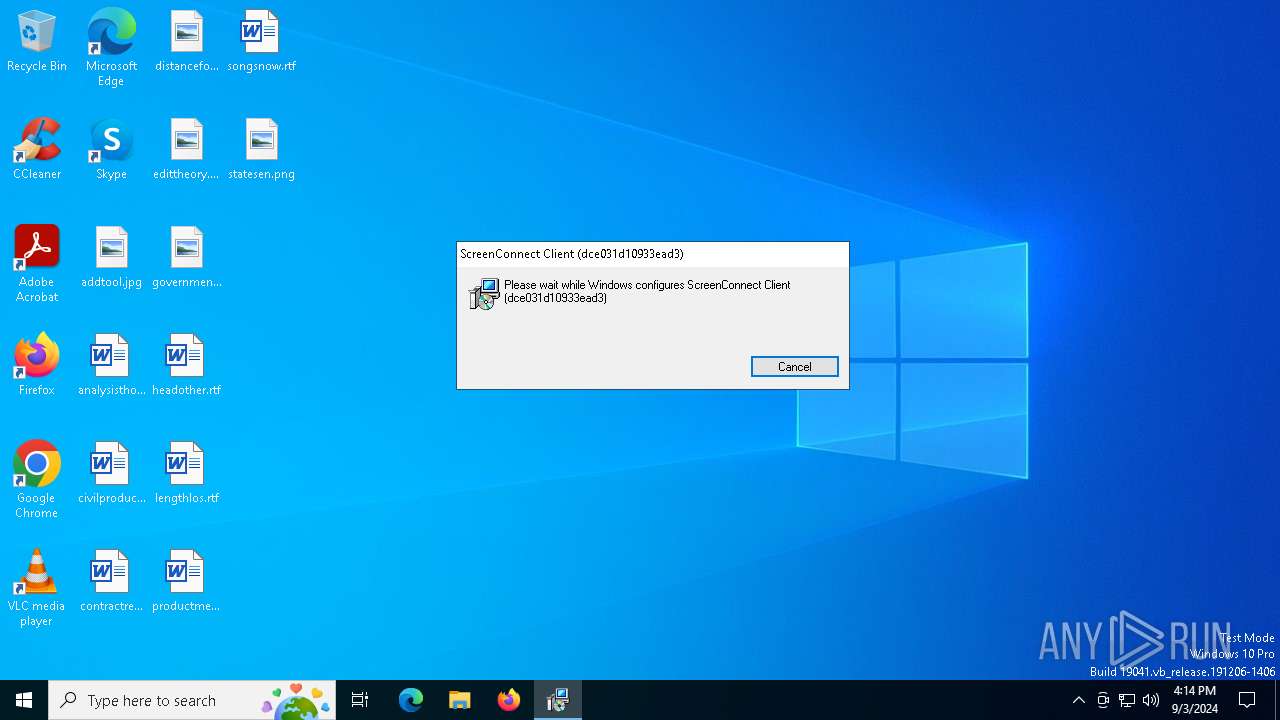
| 3672 | "C:\Program Files (x86)\ScreenConnect Client (dce031d10933ead3)\ScreenConnect.WindowsClient.exe" "RunRole" "ee2618d4-1dde-40ce-a880-85ae1b269ba7" "System" | C:\Program Files (x86)\ScreenConnect Client (dce031d10933ead3)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: SYSTEM Company: ScreenConnect Software Integrity Level: SYSTEM Description: ScreenConnect Client Exit code: 0 Version: 23.9.10.8817 Modules
| |||||||||||||||
| 3984 | "C:\Users\admin\AppData\Local\Temp\BTC-Connect.ClientSetup.exe" | C:\Users\admin\AppData\Local\Temp\BTC-Connect.ClientSetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4020 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4436 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4876 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ScreenConnect\dce031d10933ead3\setup.msi" | C:\Windows\SysWOW64\msiexec.exe | BTC-Connect.ClientSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5244 | C:\Windows\syswow64\MsiExec.exe -Embedding 07270D576785BCAF956EAADD89953985 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5276 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 295
Read events
9 963
Write events
311
Delete events
21
Modification events
| (PID) Process: | (3984) BTC-Connect.ClientSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3984) BTC-Connect.ClientSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3984) BTC-Connect.ClientSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3984) BTC-Connect.ClientSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5276) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000040D2055D1CFEDA019C140000A4190000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5276) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000040D2055D1CFEDA019C140000A4190000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5276) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000024D8625D1CFEDA019C140000A4190000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5276) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000024D8625D1CFEDA019C140000A4190000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5276) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000A58D675D1CFEDA019C140000A4190000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5276) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000000CBD6E5D1CFEDA019C140000A4190000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
16
Suspicious files
20
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3984 | BTC-Connect.ClientSetup.exe | C:\Users\admin\AppData\Local\Temp\ScreenConnect\dce031d10933ead3\setup.msi | — | |
MD5:— | SHA256:— | |||
| 5276 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5276 | msiexec.exe | C:\Windows\Installer\132afb.msi | — | |
MD5:— | SHA256:— | |||
| 1688 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSICB28.tmp-\ScreenConnect.InstallerActions.dll | executable | |
MD5:B0585159161D50E330B7F8EDA50A2770 | SHA256:CA9E51D51F24E16428D1B0E9A0829A44DA2678BFC7BA00F0B46A57DCD6D734B8 | |||
| 1688 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSICB28.tmp-\CustomAction.config | xml | |
MD5:EB99EE012EB63C162EEBC1DF3A15990B | SHA256:C5045C2D482F71215877EB668264EE47E1415792457F19A5A55651C3554CC7CD | |||
| 1688 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSICB28.tmp-\ScreenConnect.Windows.dll | executable | |
MD5:29454A0CB83F28C24805E9A70E53444A | SHA256:998CC3F9AF5BD41CCF0F9BE86192BBE20CDEC08A6FF73C1199E1364195A83E14 | |||
| 1688 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSICB28.tmp-\ScreenConnect.Core.dll | executable | |
MD5:B319407E807BE1A49E366F7F8EA7EE2A | SHA256:761B7E50BAA229E8AFCD9A50990D7F776DDB5ED1EA5FBB131C802E57CF918742 | |||
| 1688 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSICB28.tmp-\Microsoft.Deployment.WindowsInstaller.dll | executable | |
MD5:5EF88919012E4A3D8A1E2955DC8C8D81 | SHA256:3E54286E348EBD3D70EAED8174CCA500455C3E098CDD1FCCB167BC43D93DB29D | |||
| 5276 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:8EE480348D274E0F89E1D13F2AEAC7C9 | SHA256:2896815B63978D5D384E1303929DFA325319D85CB065994F5F59CFFBF18245C8 | |||
| 5276 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{1c326923-7799-416f-ad87-8fcd37aa3f73}_OnDiskSnapshotProp | binary | |
MD5:8EE480348D274E0F89E1D13F2AEAC7C9 | SHA256:2896815B63978D5D384E1303929DFA325319D85CB065994F5F59CFFBF18245C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
38
DNS requests
19
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3296 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3160 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3160 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6160 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6580 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
6160 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3296 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3296 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
openirviscloud.pro |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6108 | ScreenConnect.ClientService.exe | Misc activity | ET INFO ScreenConnect/ConnectWise Initial Checkin Packet M2 |
6108 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |
6108 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |