| File name: | getscreen-865436612-x86 (1).exe |
| Full analysis: | https://app.any.run/tasks/9d2d0097-fc8a-4a1f-8325-3f64fa5c12b3 |
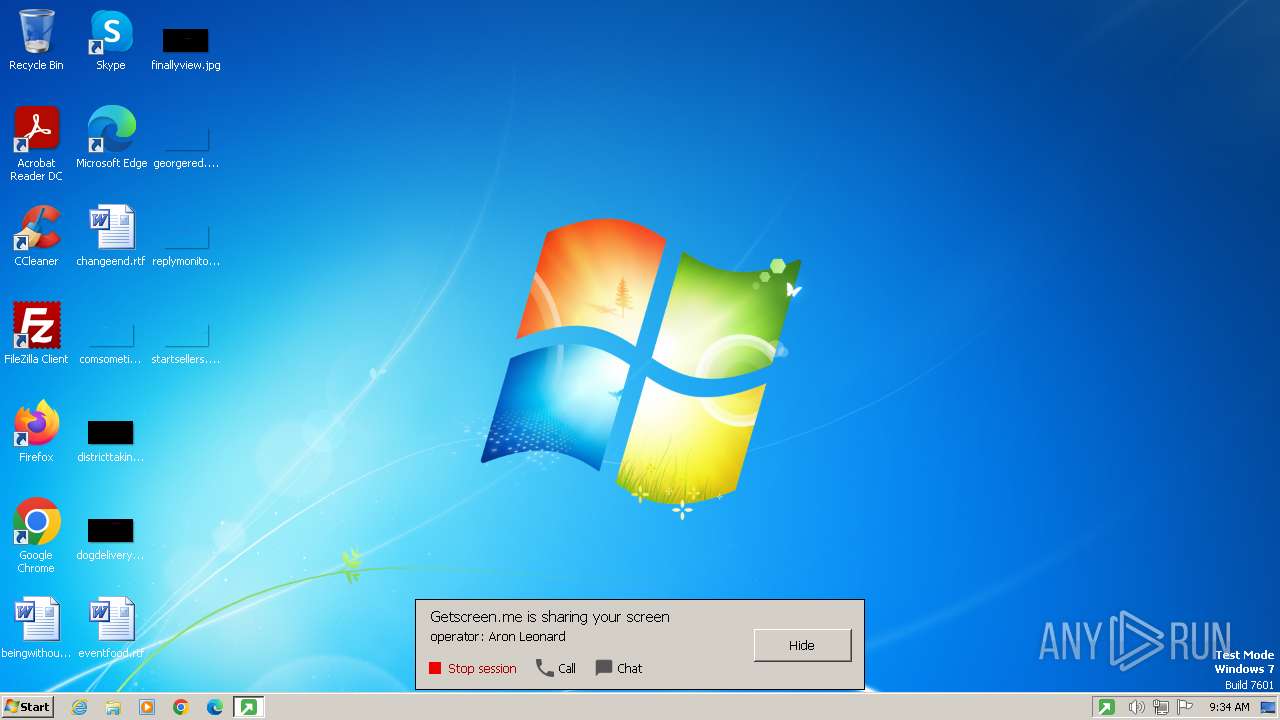
| Verdict: | Malicious activity |
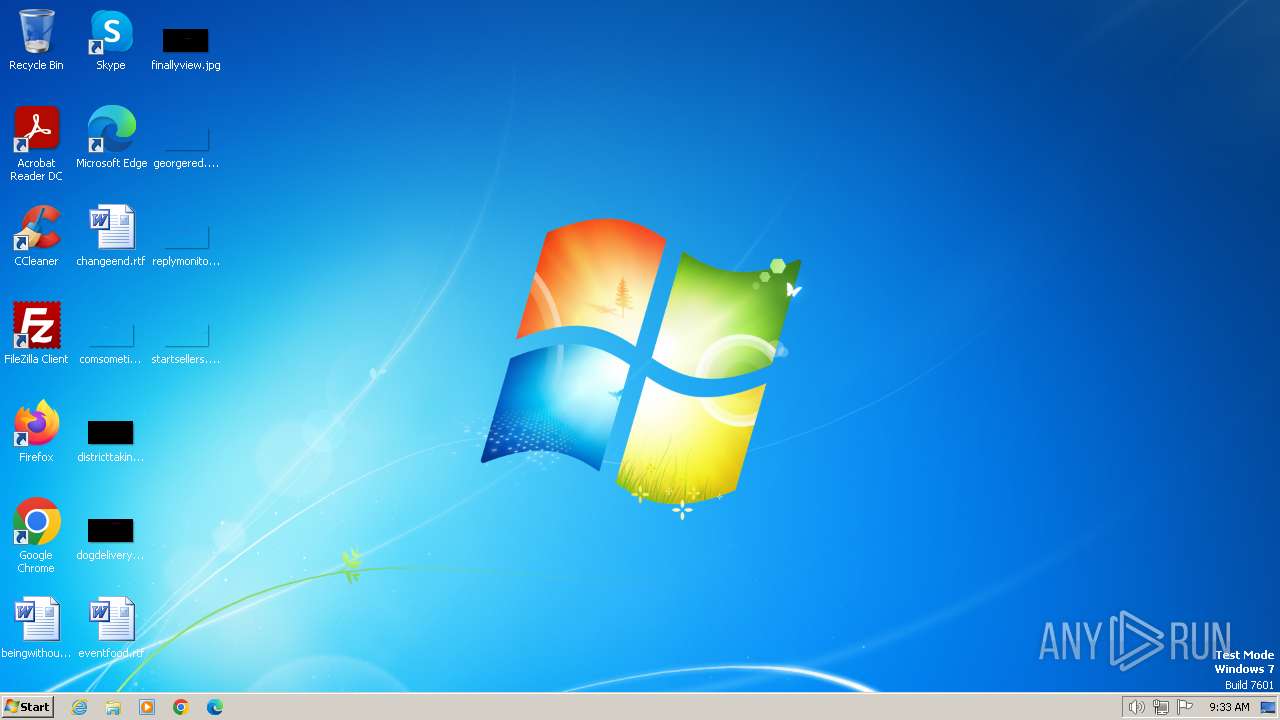
| Analysis date: | March 03, 2024, 09:33:22 |
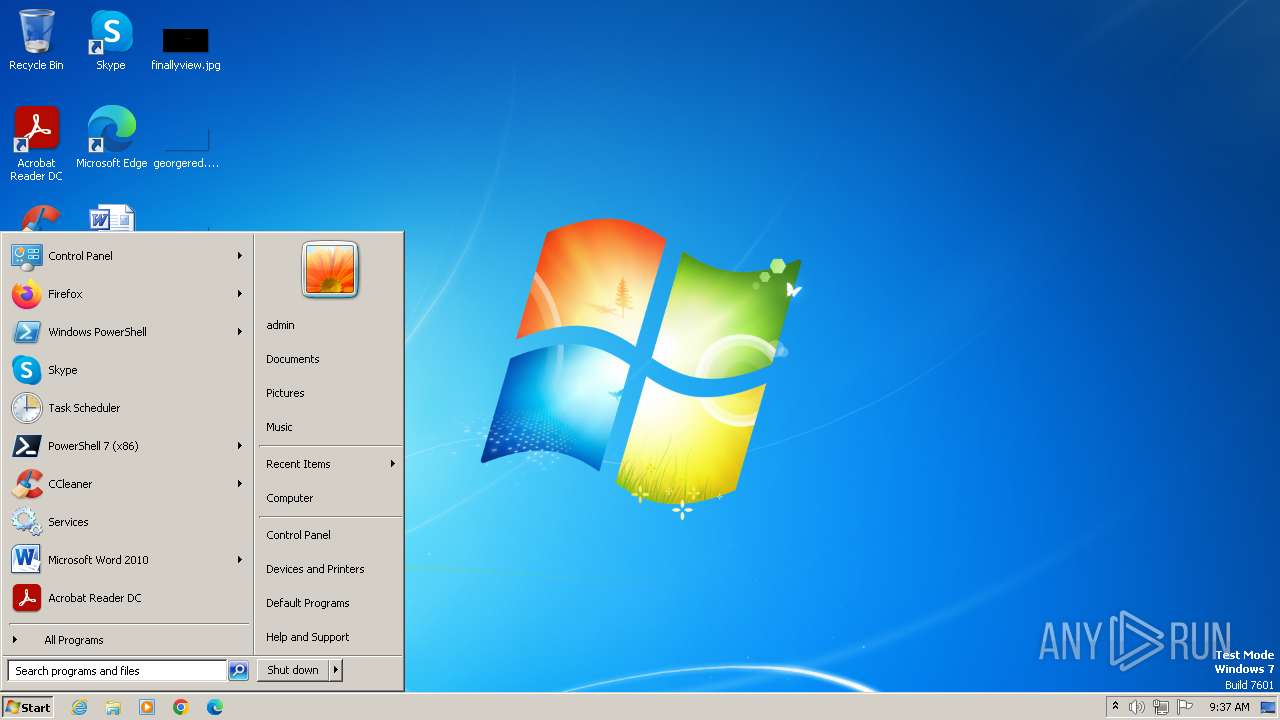
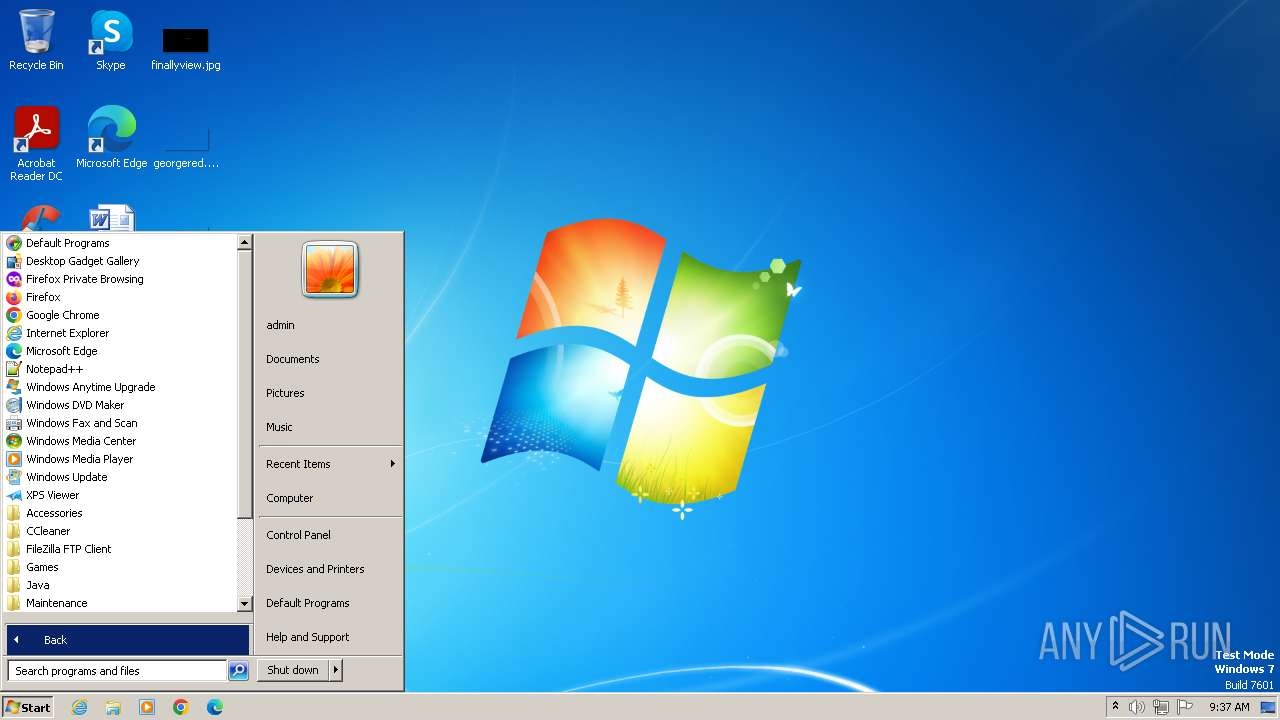
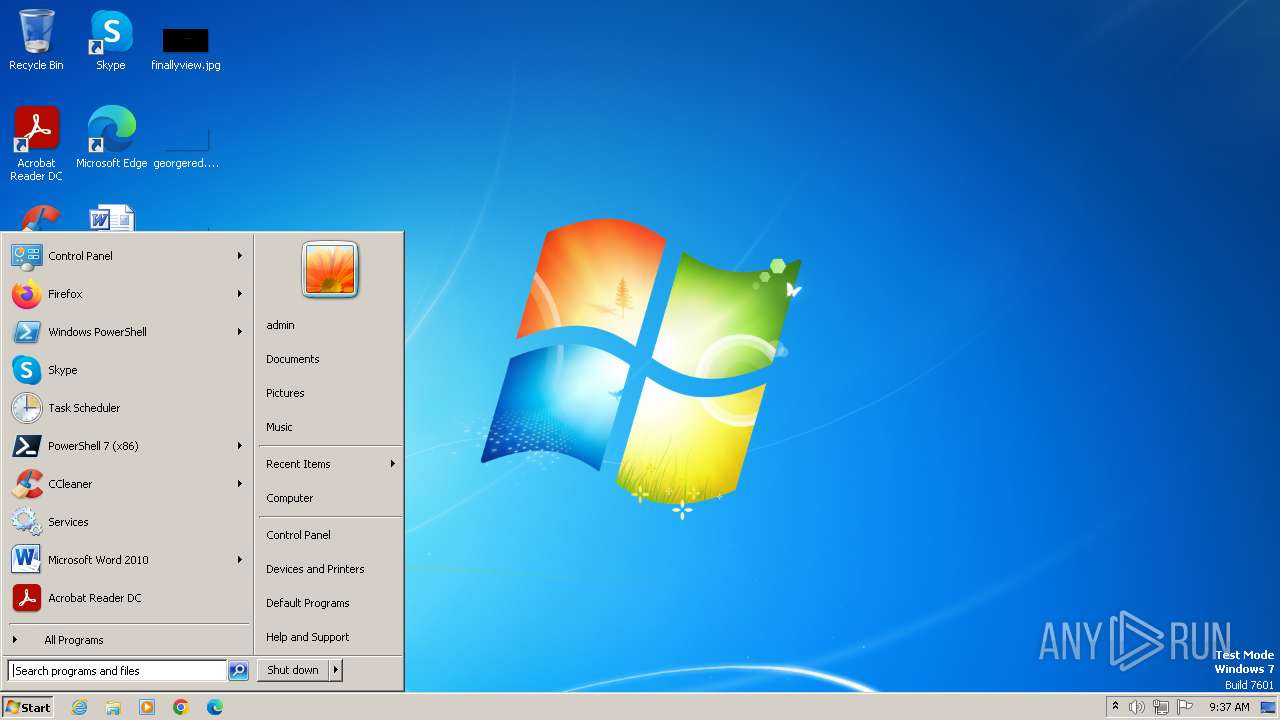
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 17121B7B824B66F4BAA94E67DA133E80 |
| SHA1: | 9078E52CC8F7BA5E738A7770493C399F77F090C8 |
| SHA256: | E49564D7D8C65BBBC93E24EB66BCCE92F3C2F343A8135BE128EDE43902322610 |
| SSDEEP: | 98304:fqrJNNcxEpbA8Xv763d5M5ggRVA33Azr1gL/4k2u8iR/mrZZfjDv/wmM+pFo/LIc:ha+WDO |
MALICIOUS
Drops the executable file immediately after the start
- getscreen-865436612-x86 (1).exe (PID: 3700)
- getscreen-865436612-x86 (1).exe (PID: 2752)
SUSPICIOUS
Reads security settings of Internet Explorer
- getscreen-865436612-x86 (1).exe (PID: 3700)
Application launched itself
- getscreen-865436612-x86 (1).exe (PID: 3700)
- getscreen-865436612-x86 (1).exe (PID: 2752)
Reads the Internet Settings
- getscreen-865436612-x86 (1).exe (PID: 3700)
- getscreen-865436612-x86 (1).exe (PID: 2752)
Executable content was dropped or overwritten
- getscreen-865436612-x86 (1).exe (PID: 2752)
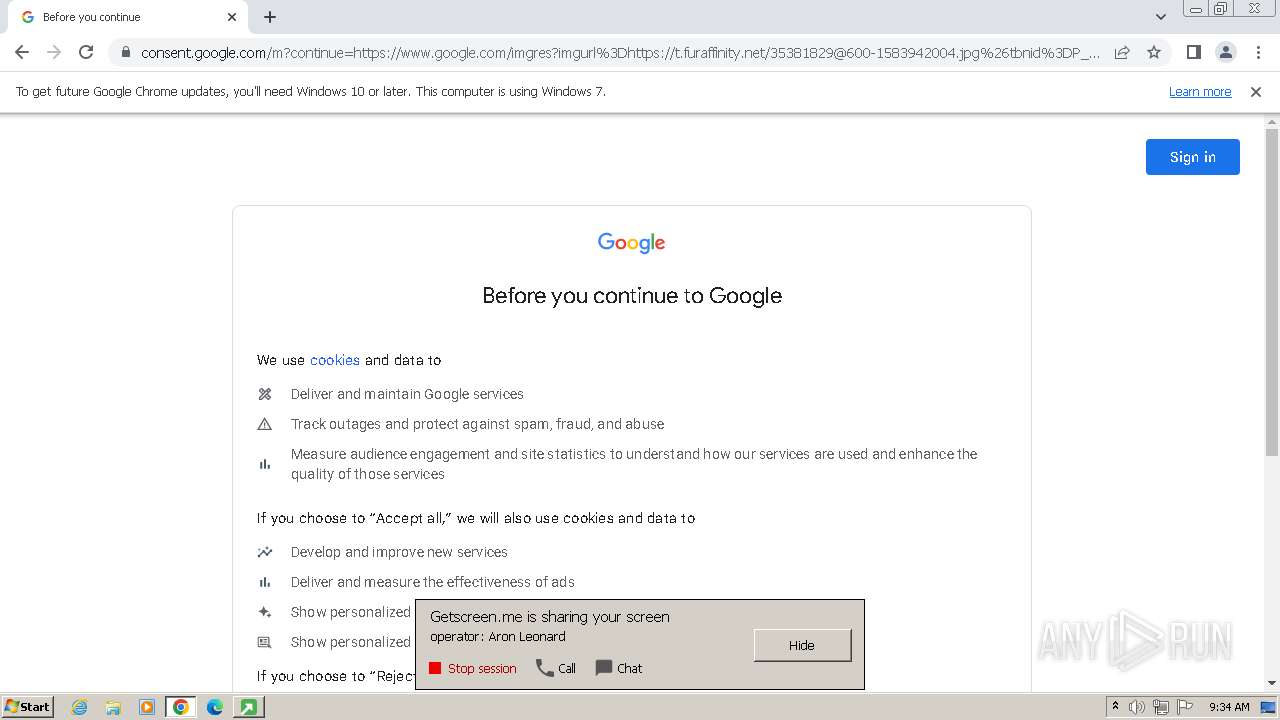
Changes Internet Explorer settings (feature browser emulation)
- getscreen-865436612-x86 (1).exe (PID: 3464)
Executes as Windows Service
- gogrmzkrbnthavesmqwemygprfpqwqj-elevate.exe (PID: 2444)
Connects to unusual port
- getscreen-865436612-x86 (1).exe (PID: 2752)
INFO
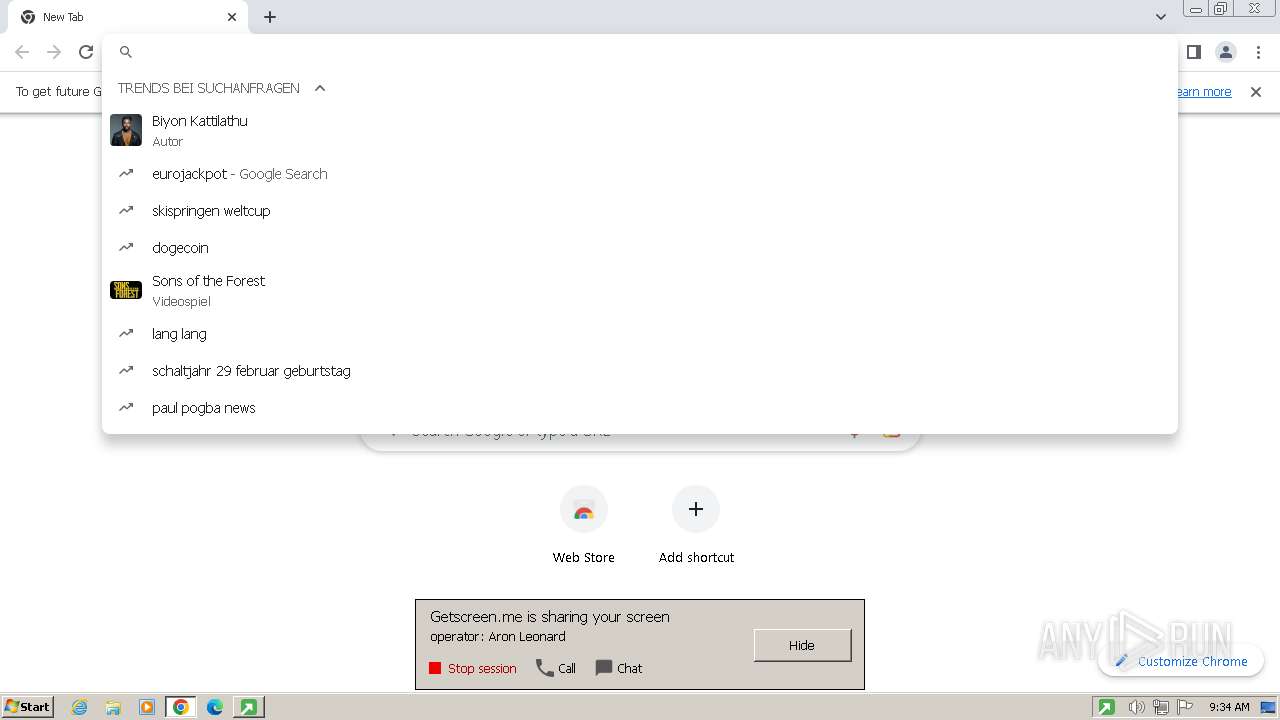
Checks supported languages
- getscreen-865436612-x86 (1).exe (PID: 2752)
- getscreen-865436612-x86 (1).exe (PID: 3700)
- getscreen-865436612-x86 (1).exe (PID: 3464)
- gogrmzkrbnthavesmqwemygprfpqwqj-elevate.exe (PID: 2444)
- getscreen-865436612-x86 (1).exe (PID: 2292)
- getscreen-865436612-x86 (1).exe (PID: 2240)
- getscreen-865436612-x86 (1).exe (PID: 1484)
- getscreen-865436612-x86 (1).exe (PID: 984)
- getscreen-865436612-x86 (1).exe (PID: 1392)
- getscreen-865436612-x86 (1).exe (PID: 2240)
Reads the computer name
- getscreen-865436612-x86 (1).exe (PID: 3700)
- getscreen-865436612-x86 (1).exe (PID: 2752)
- getscreen-865436612-x86 (1).exe (PID: 3464)
- gogrmzkrbnthavesmqwemygprfpqwqj-elevate.exe (PID: 2444)
- getscreen-865436612-x86 (1).exe (PID: 2240)
- getscreen-865436612-x86 (1).exe (PID: 2292)
- getscreen-865436612-x86 (1).exe (PID: 984)
- getscreen-865436612-x86 (1).exe (PID: 1484)
- getscreen-865436612-x86 (1).exe (PID: 1392)
- getscreen-865436612-x86 (1).exe (PID: 2240)
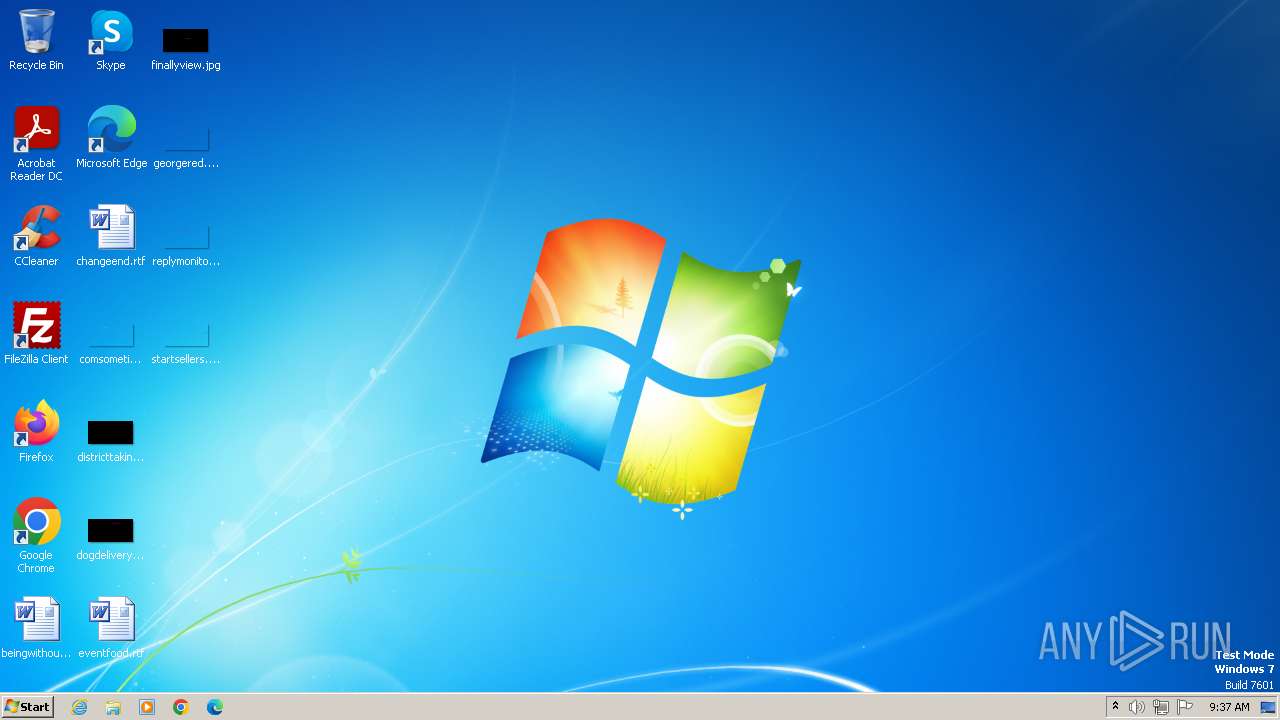
Creates files in the program directory
- getscreen-865436612-x86 (1).exe (PID: 3700)
- getscreen-865436612-x86 (1).exe (PID: 2752)
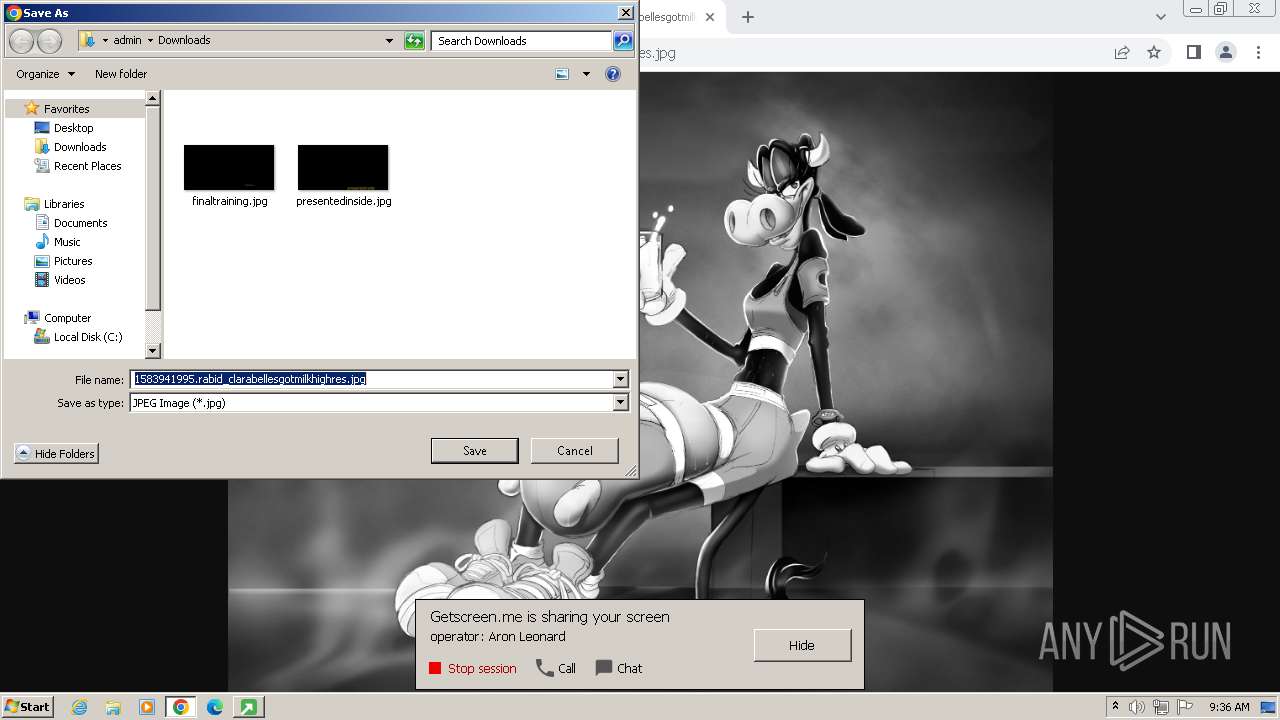
Creates files or folders in the user directory
- getscreen-865436612-x86 (1).exe (PID: 2752)
Reads the machine GUID from the registry
- getscreen-865436612-x86 (1).exe (PID: 2752)
Reads mouse settings
- getscreen-865436612-x86 (1).exe (PID: 1484)
- getscreen-865436612-x86 (1).exe (PID: 1392)
Executable content was dropped or overwritten
- chrome.exe (PID: 1924)
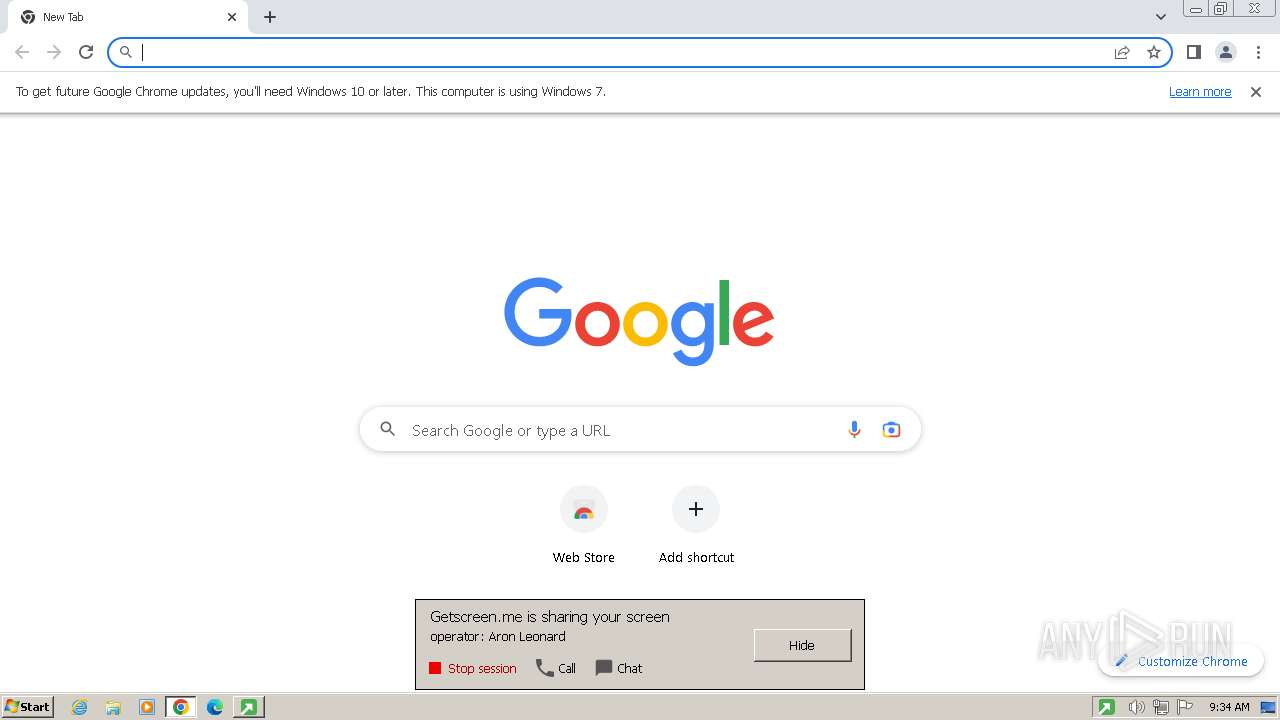
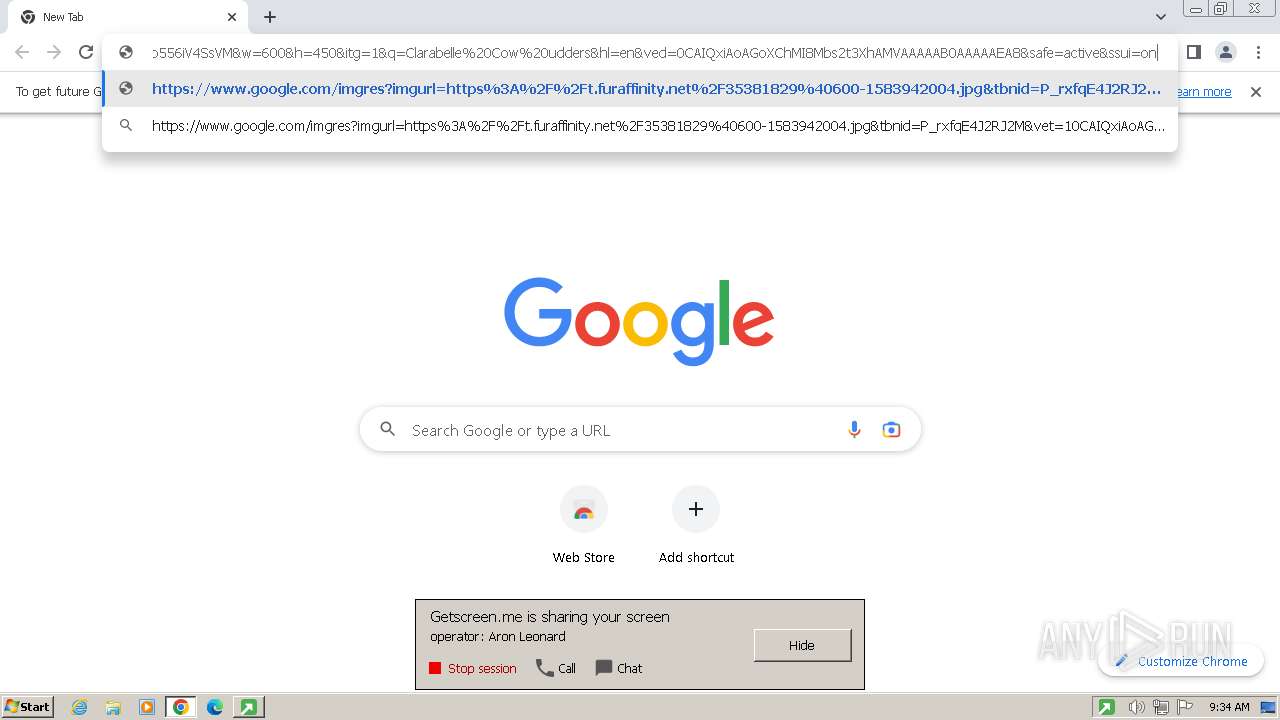
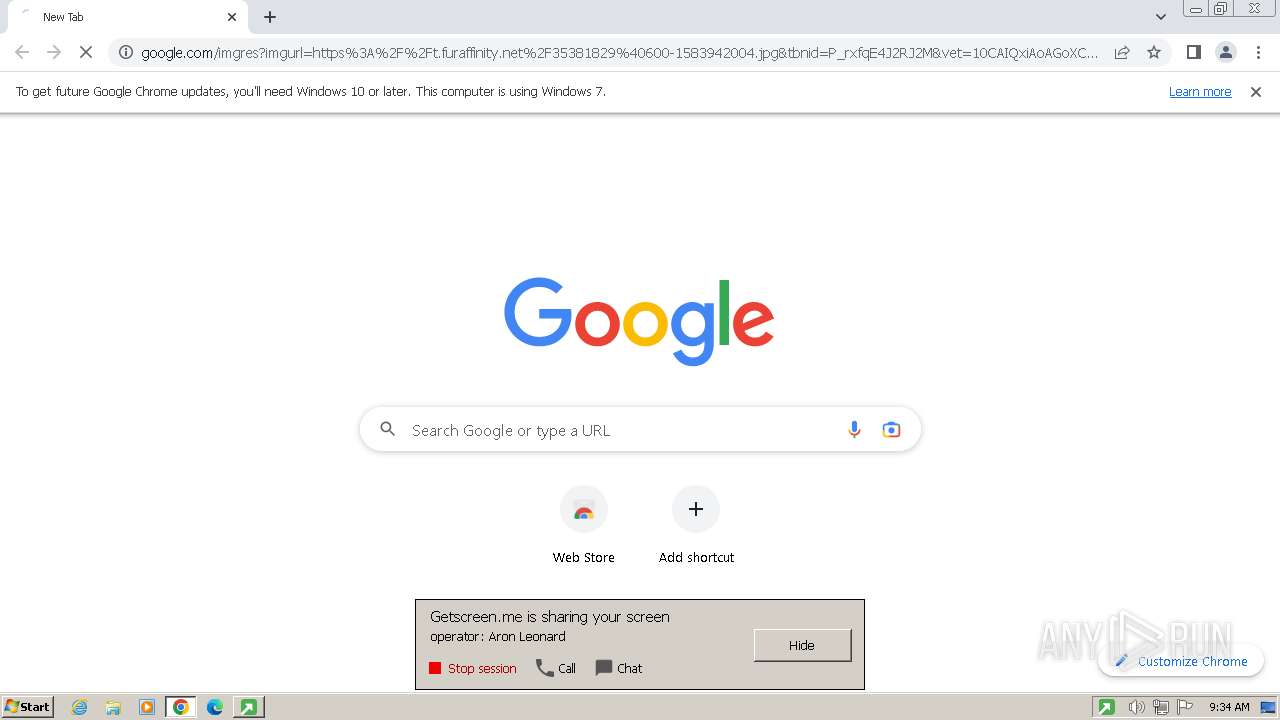
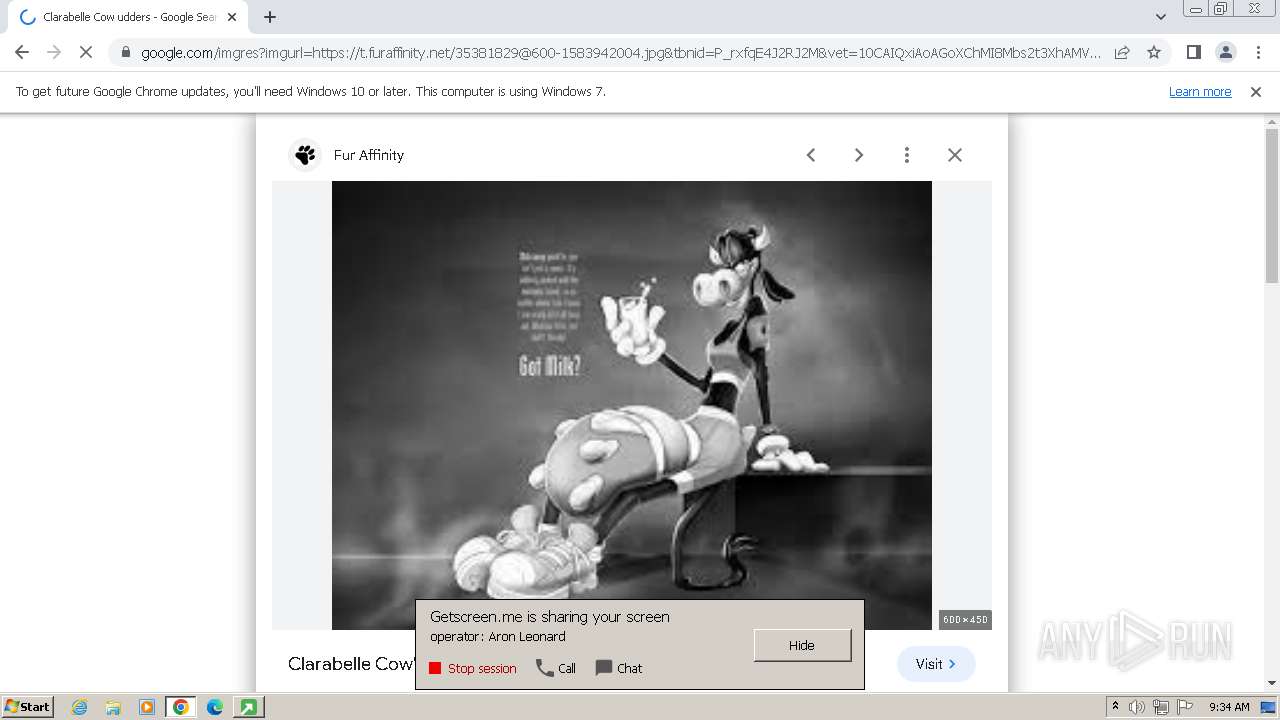
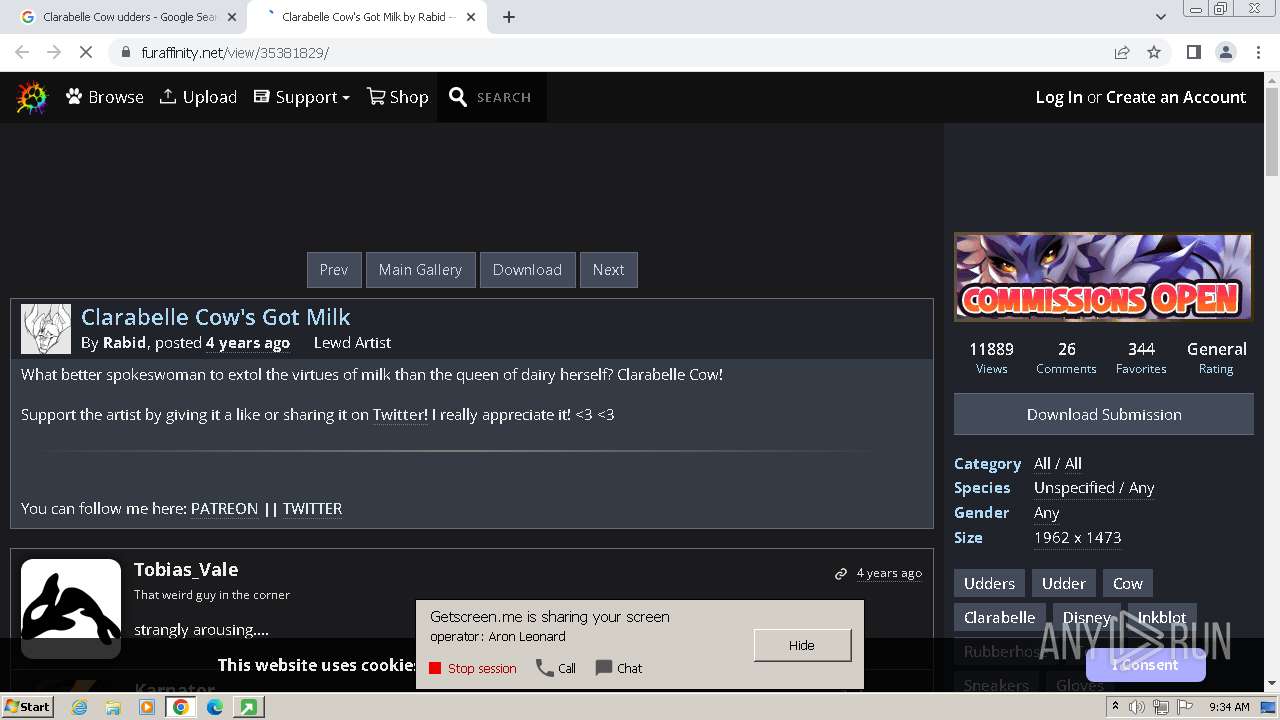
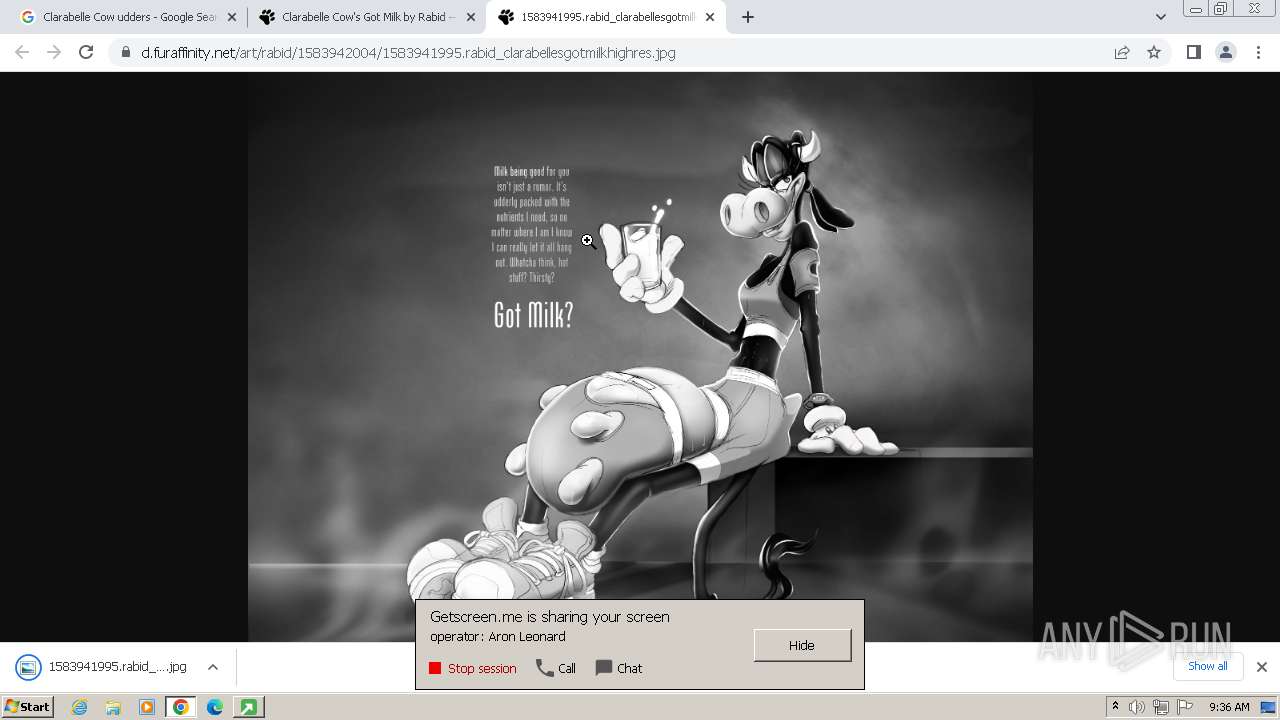
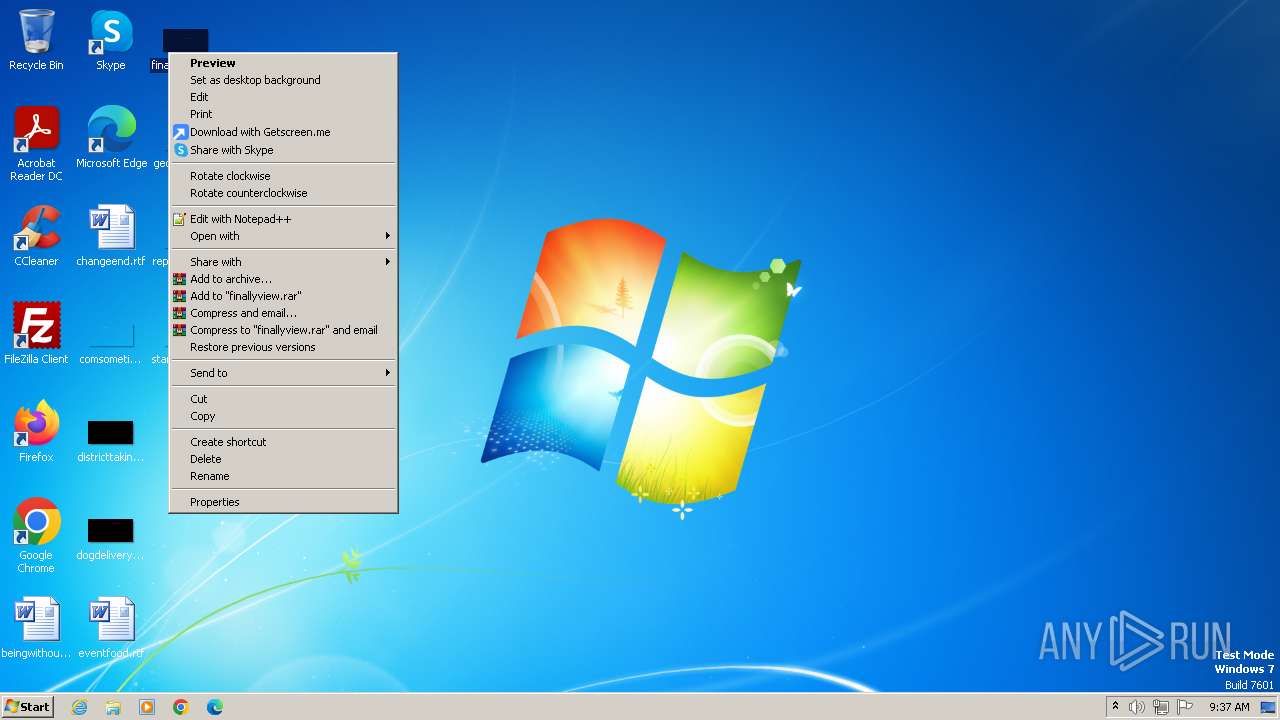
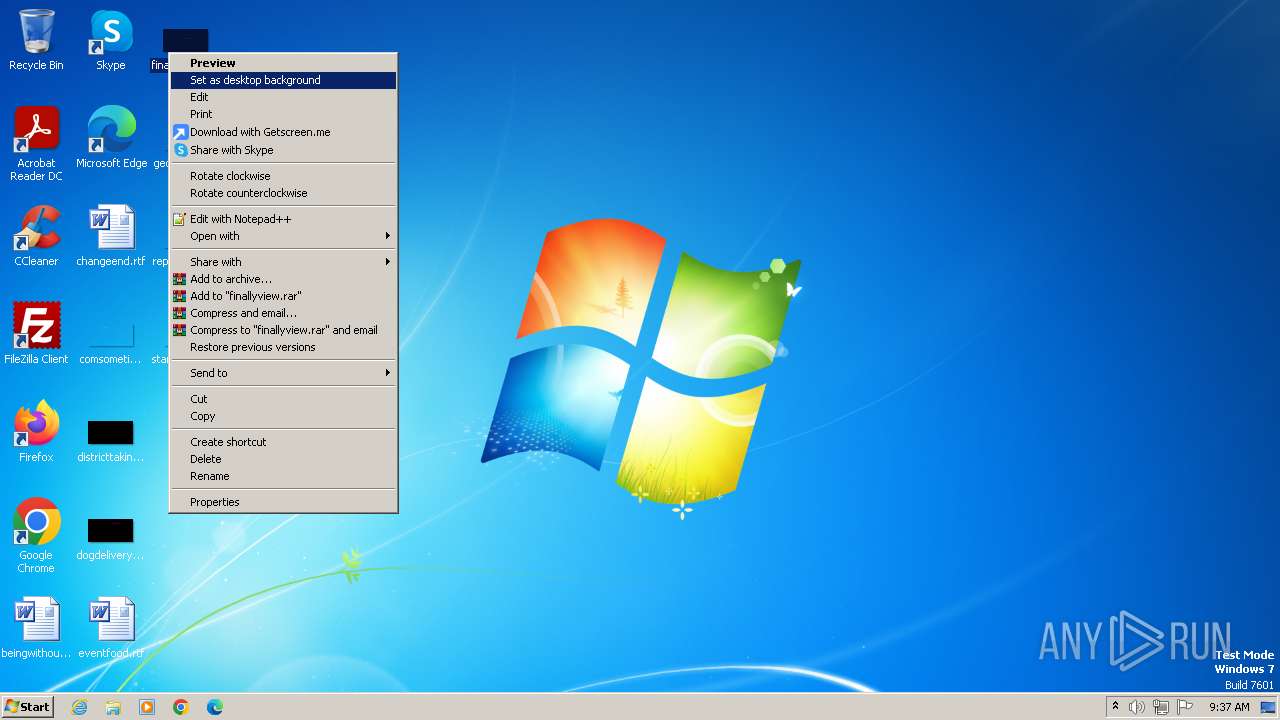
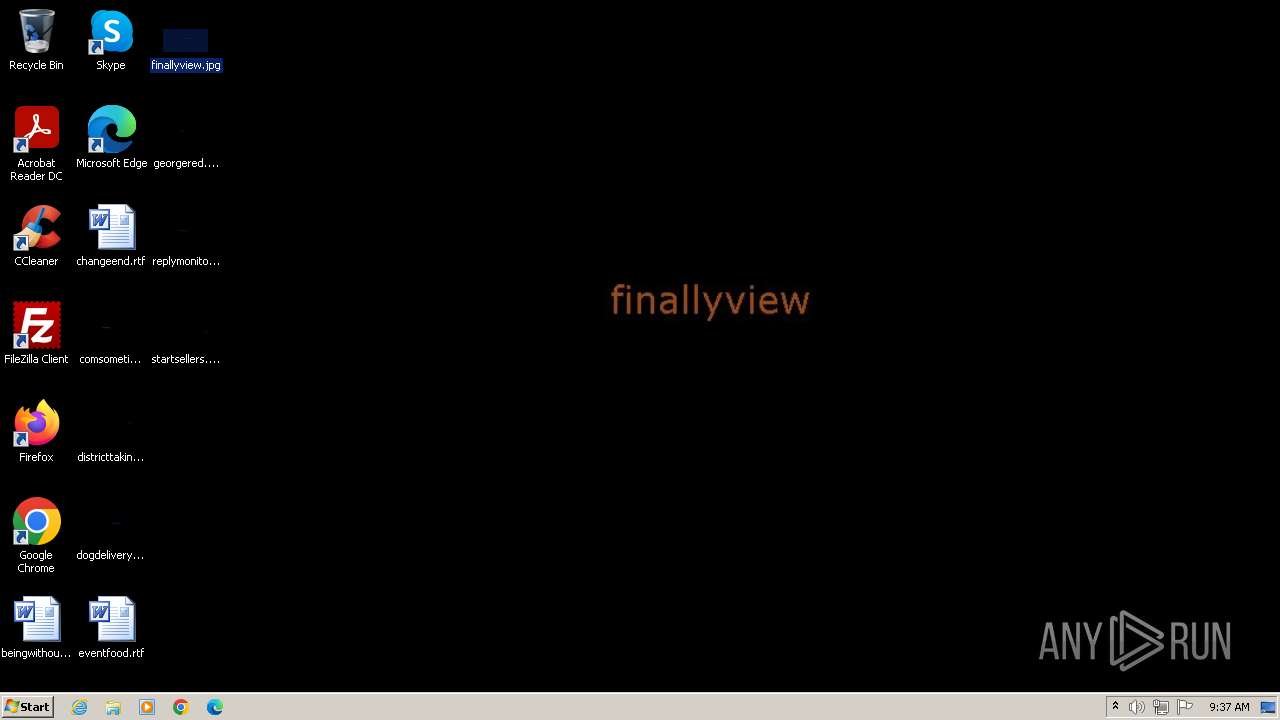
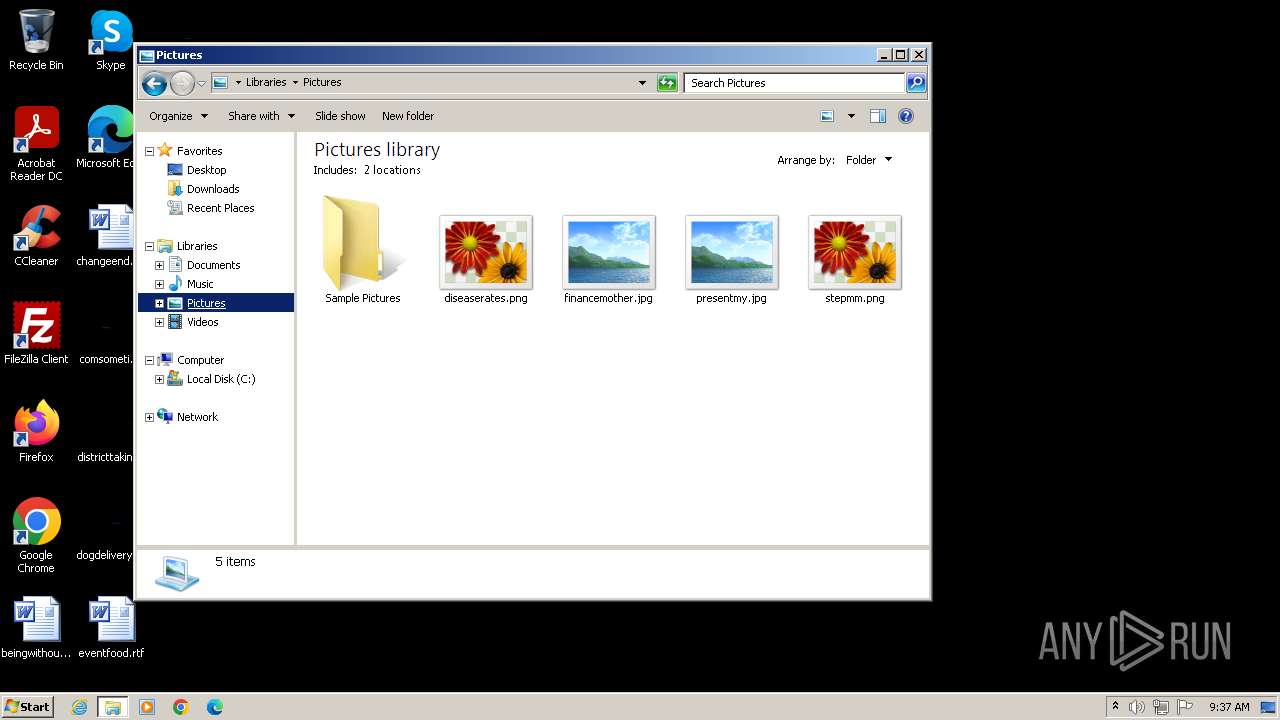
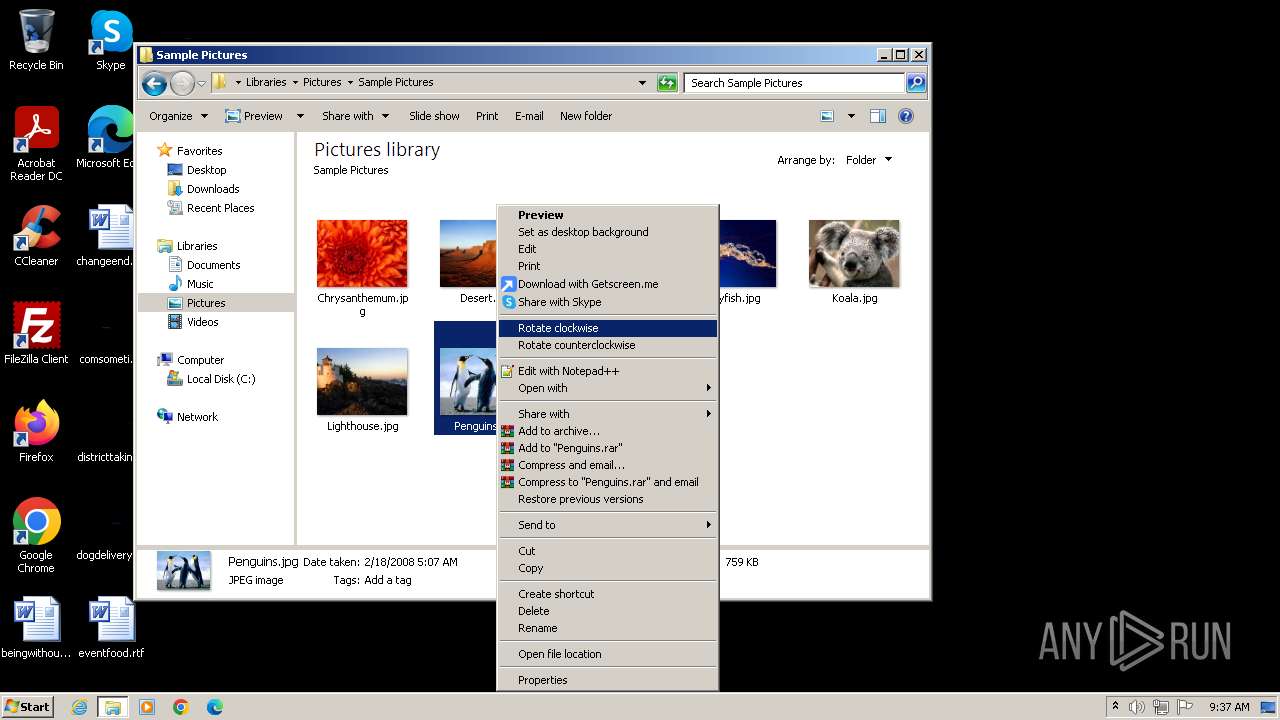
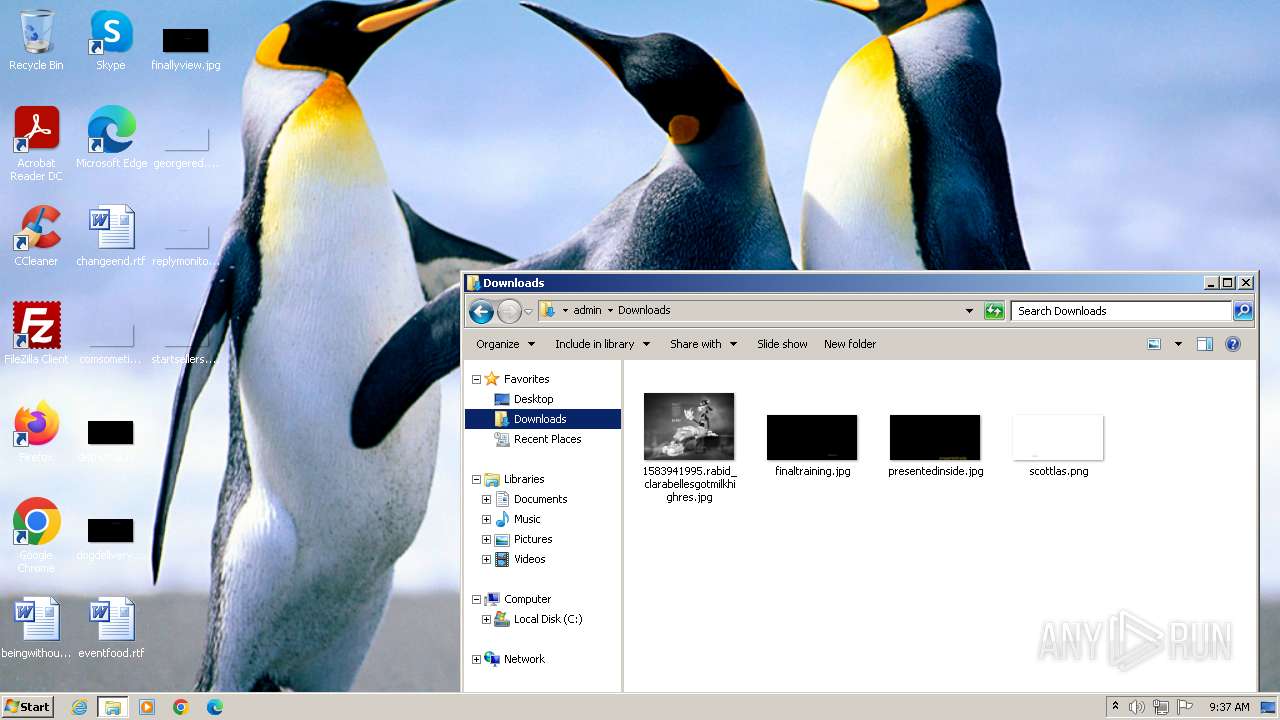
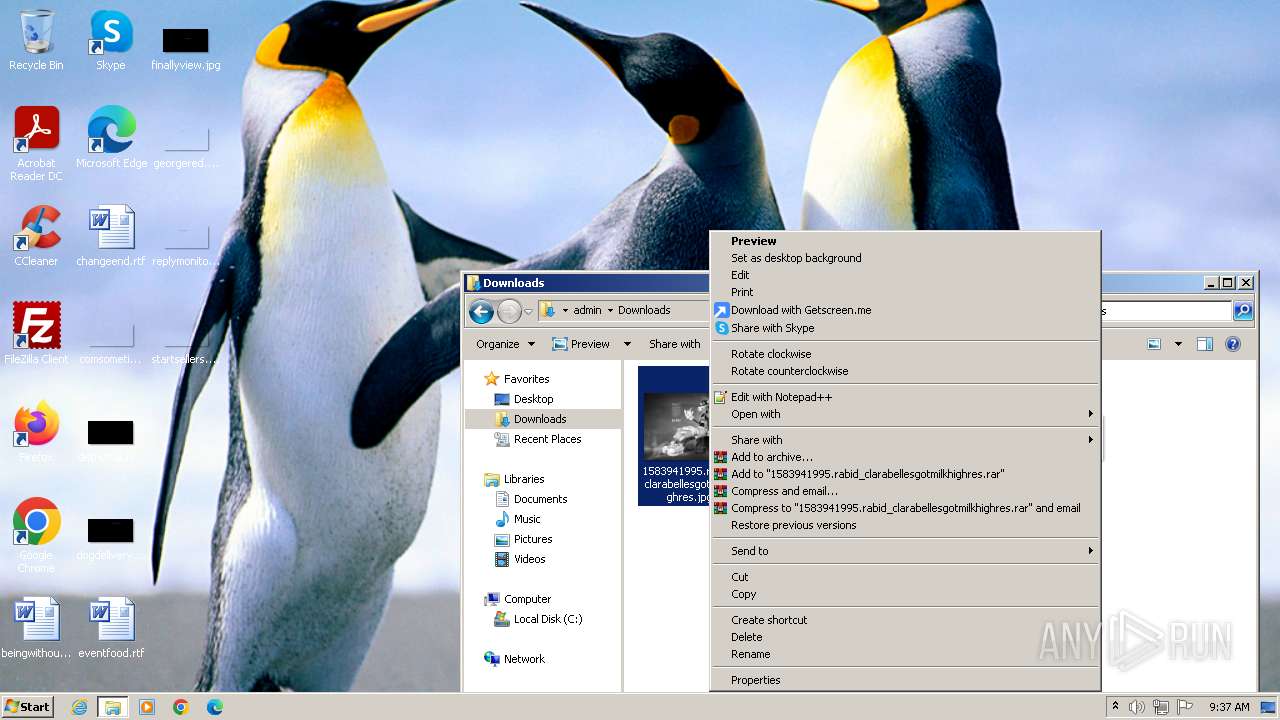
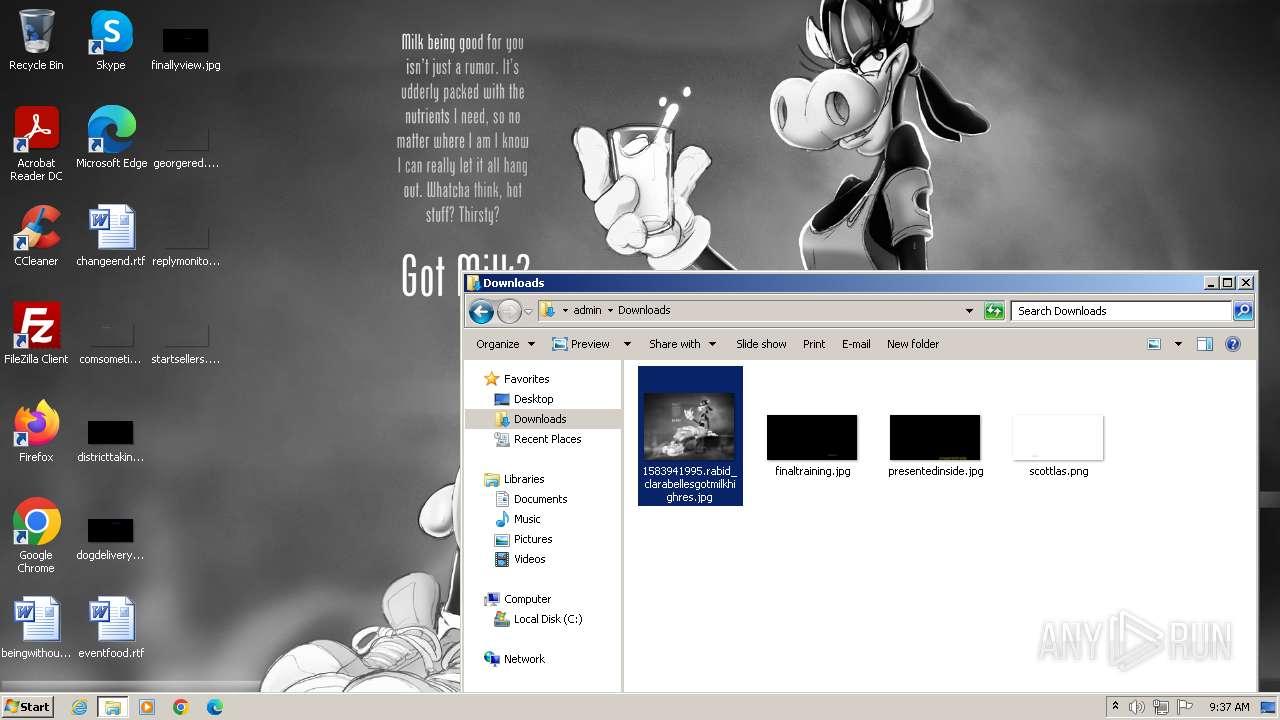
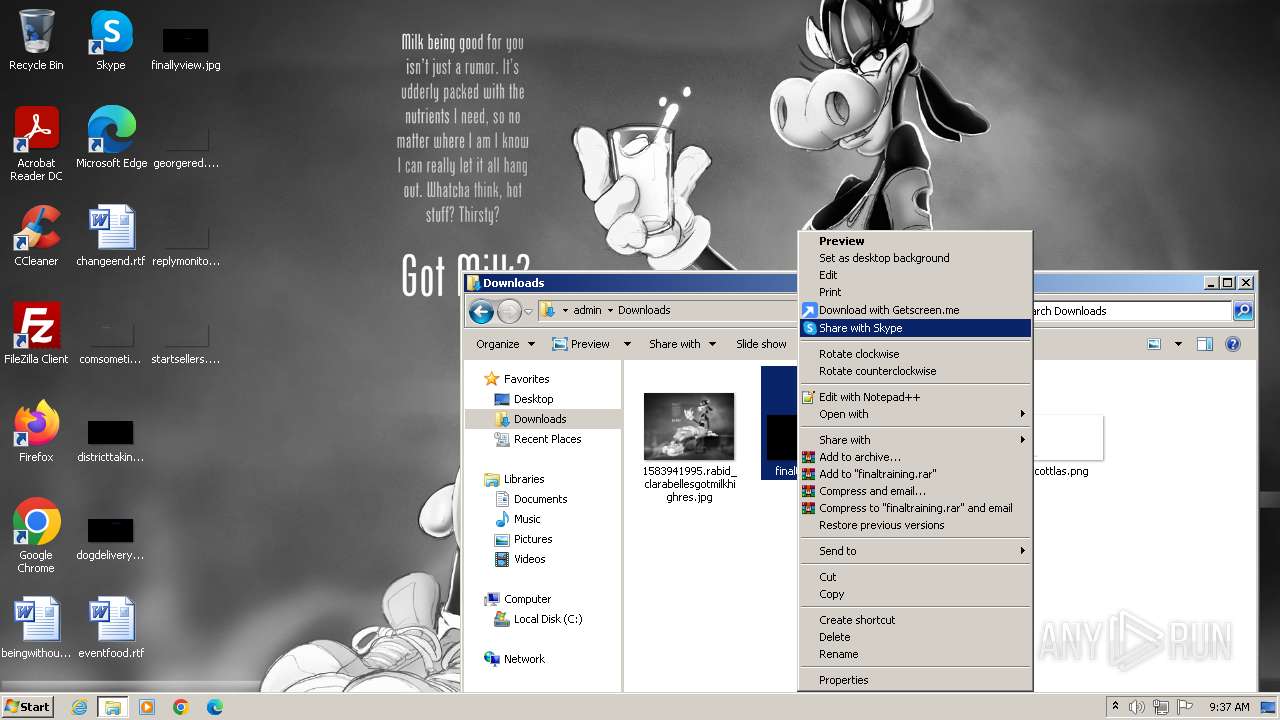
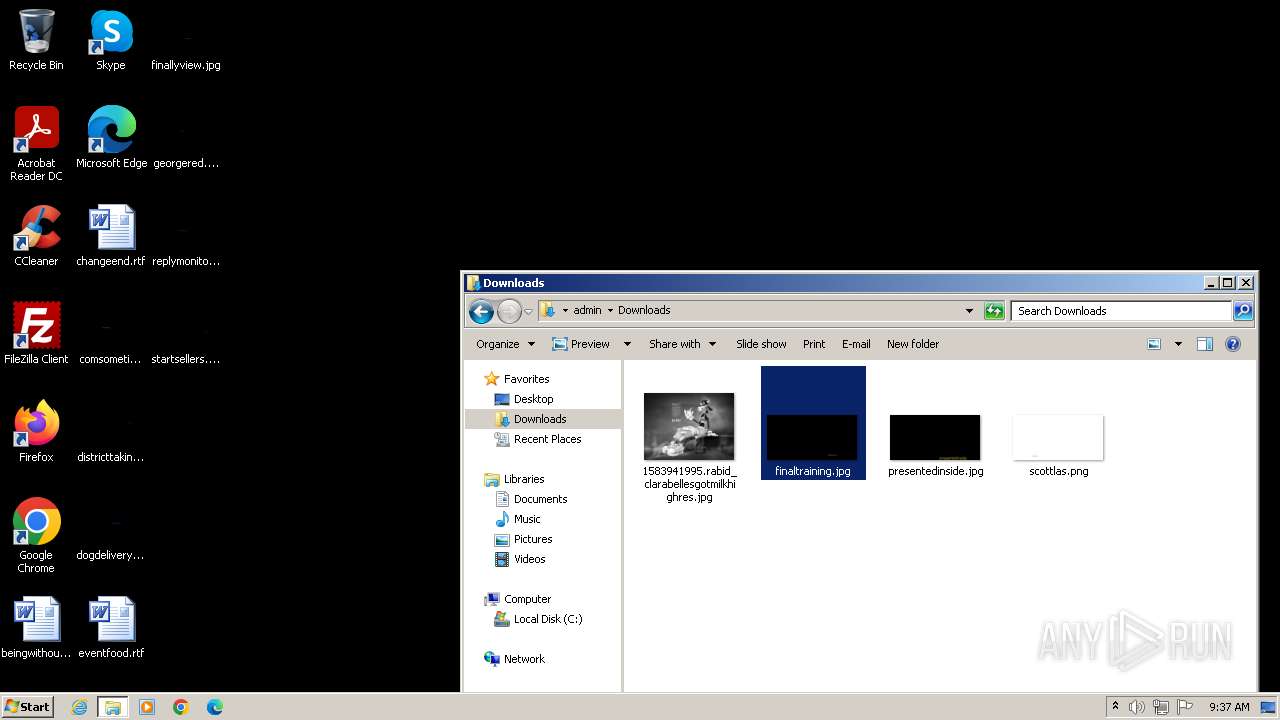
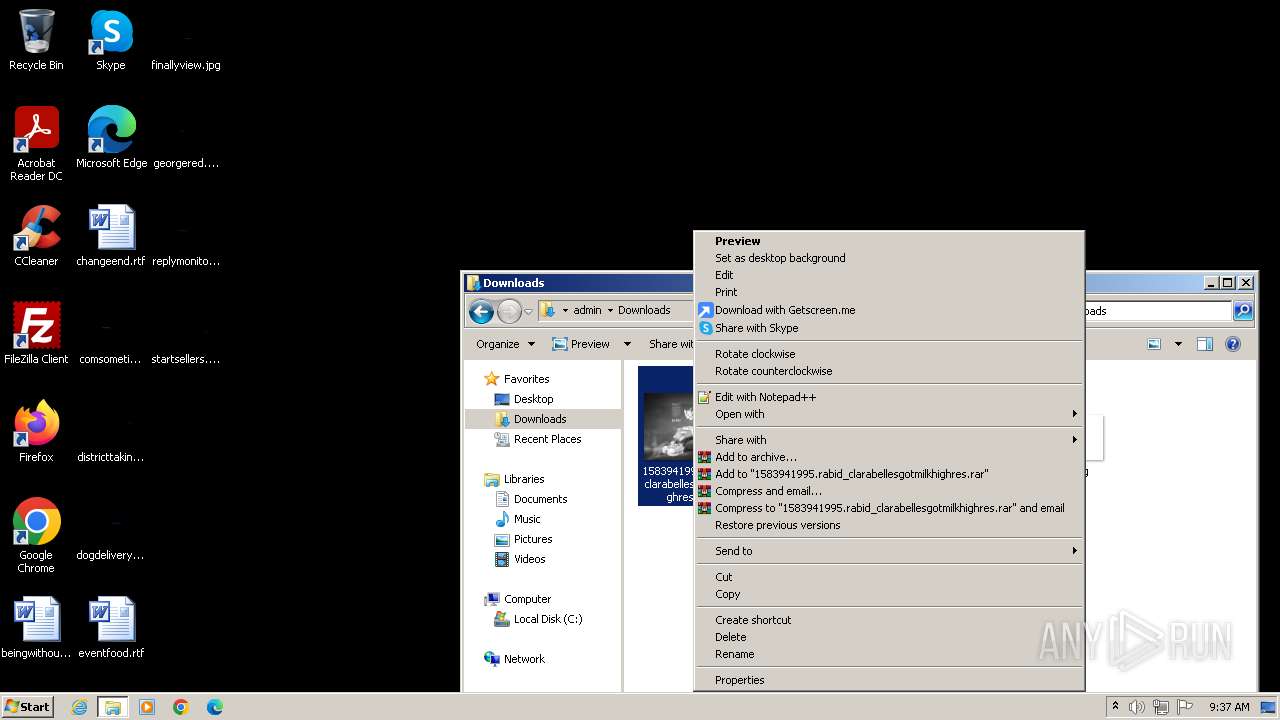
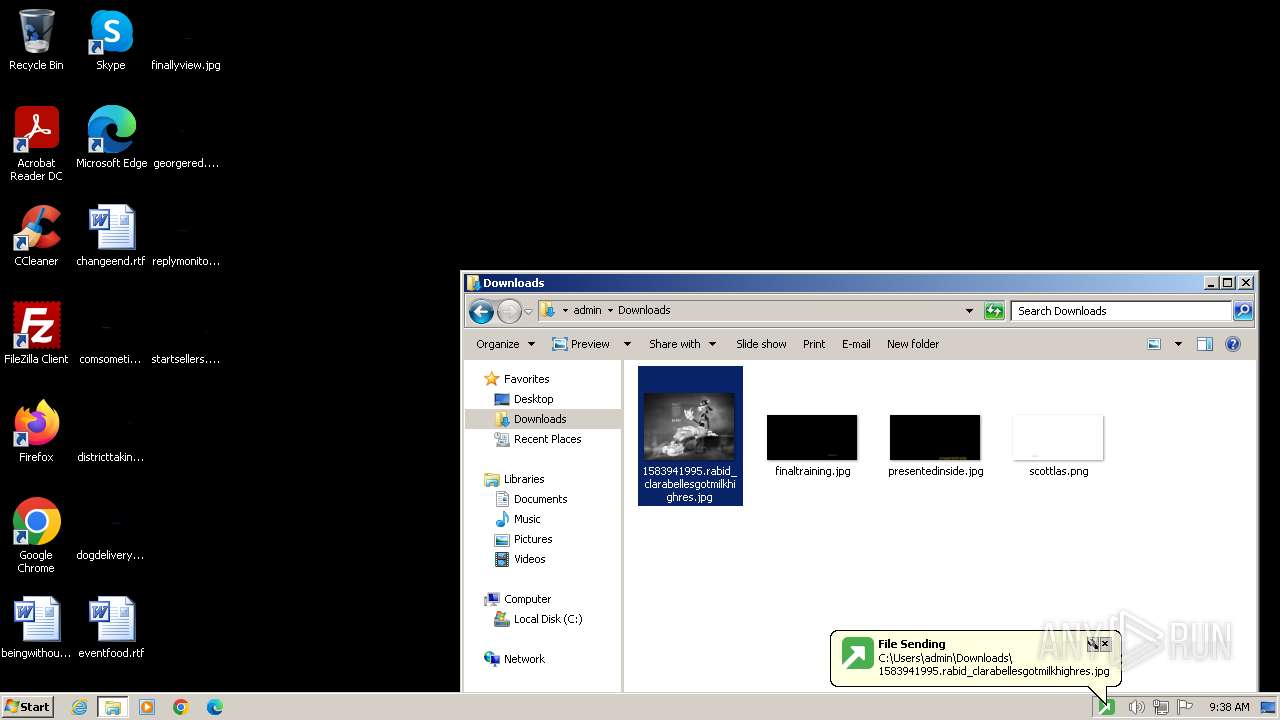
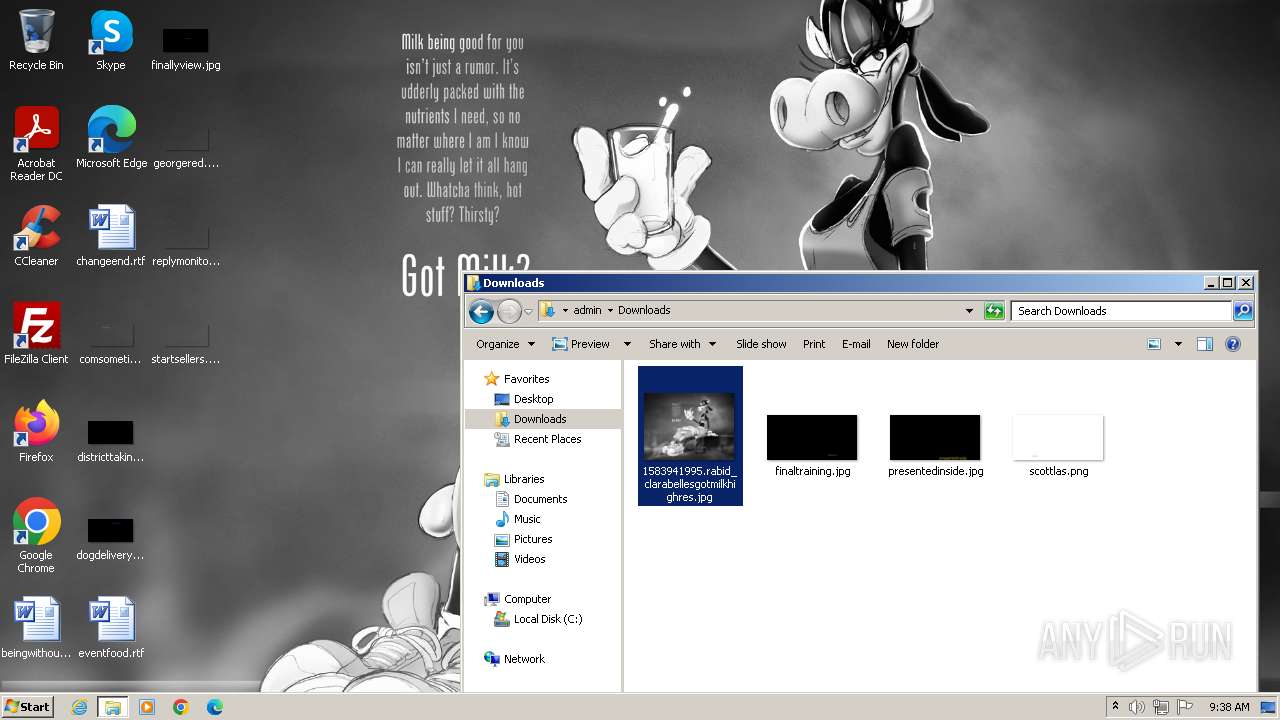
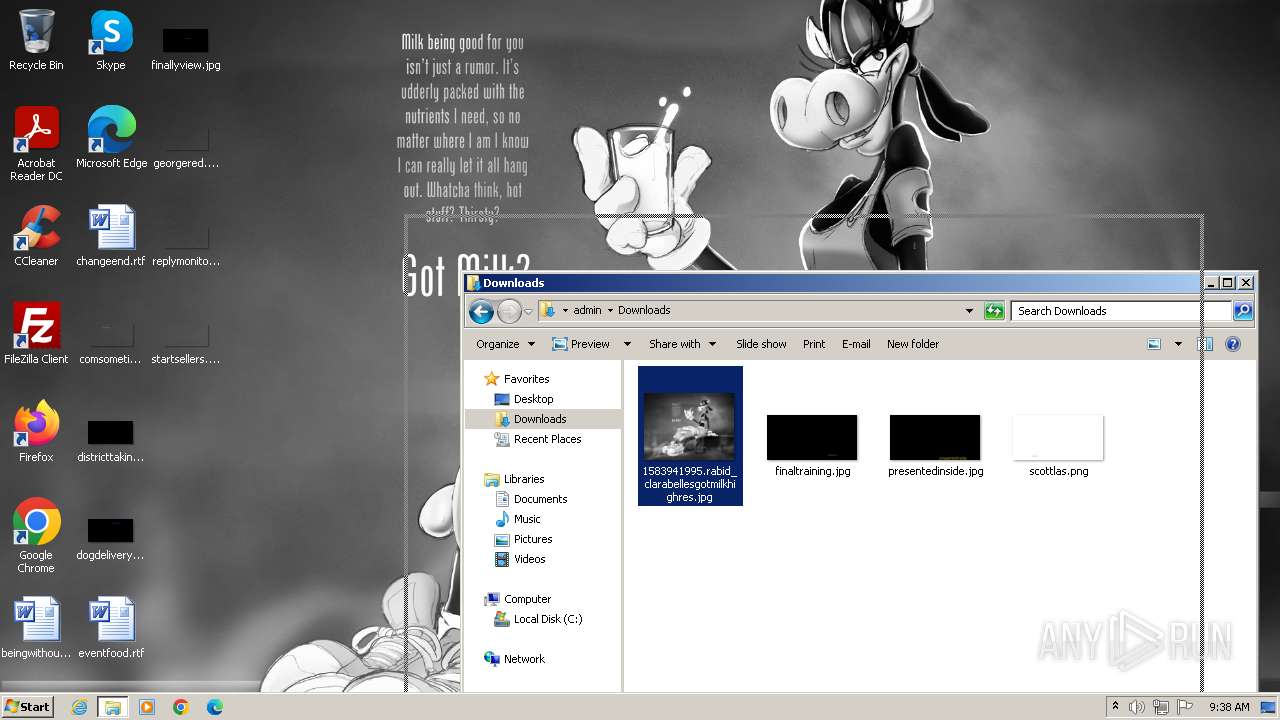
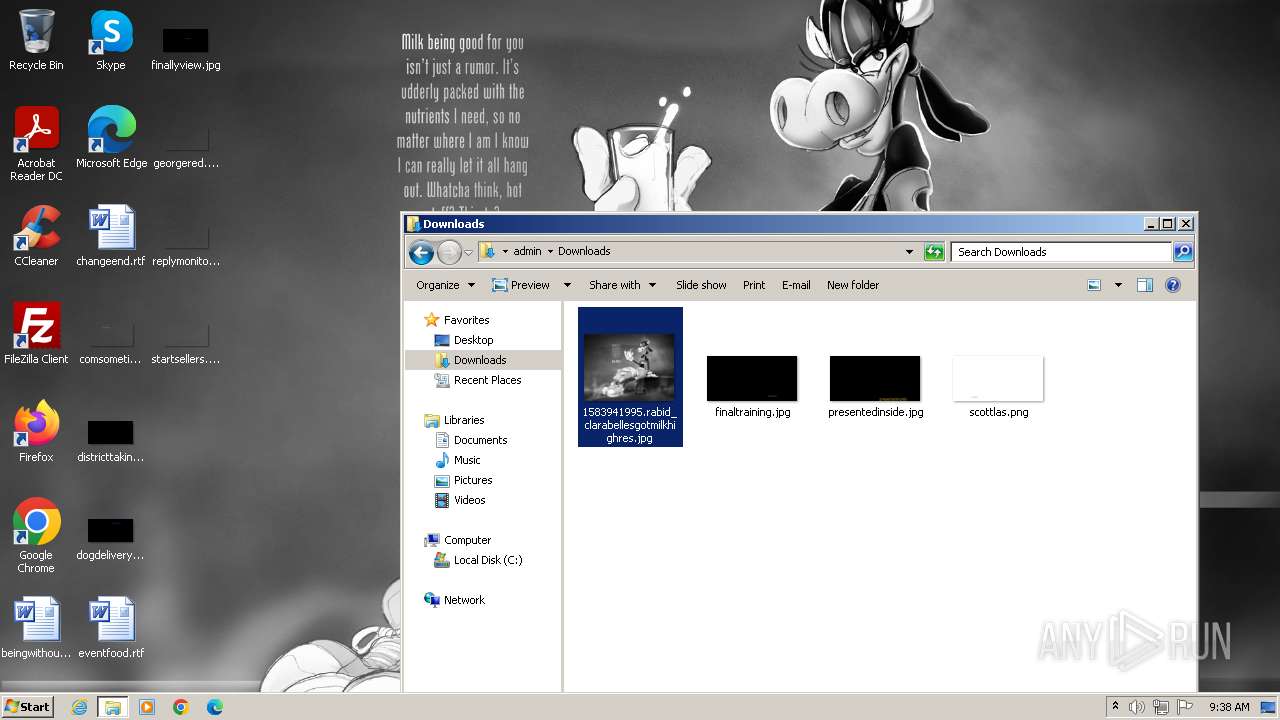
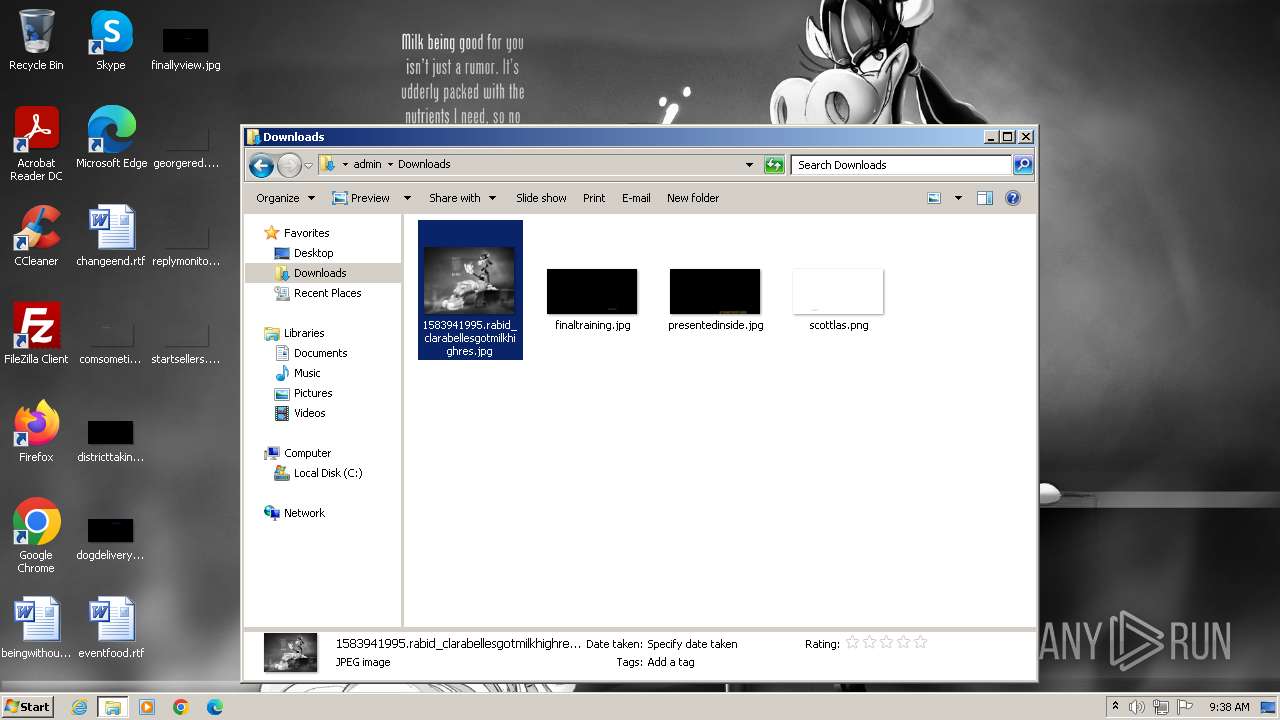
Manual execution by a user
- chrome.exe (PID: 2028)
- explorer.exe (PID: 3100)
- getscreen-865436612-x86 (1).exe (PID: 2240)
Drops the executable file immediately after the start
- chrome.exe (PID: 1924)
The process uses the downloaded file
- chrome.exe (PID: 3256)
Application launched itself
- chrome.exe (PID: 2028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:01 08:03:49+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.36 |
| CodeSize: | 3620864 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | 20402176 |
| EntryPoint: | 0x16e9100 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.18.1.0 |
| ProductVersionNumber: | 2.18.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (0009) |
| CharacterSet: | Unicode |
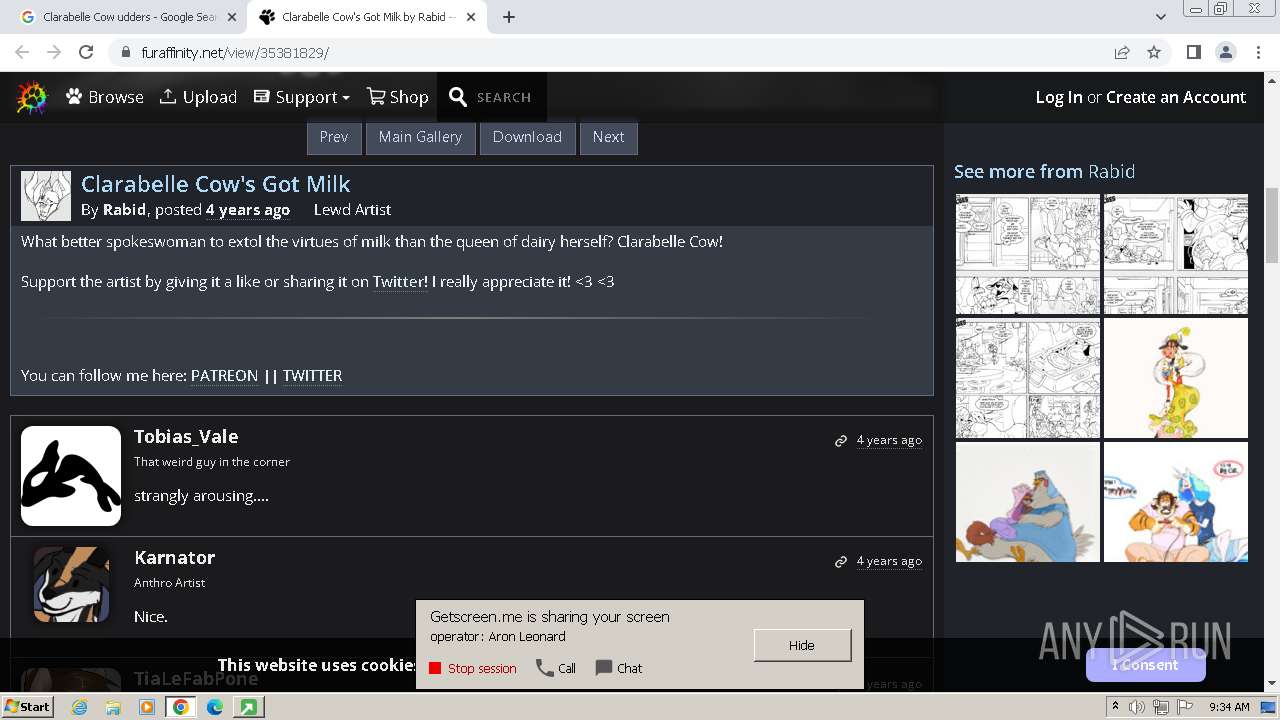
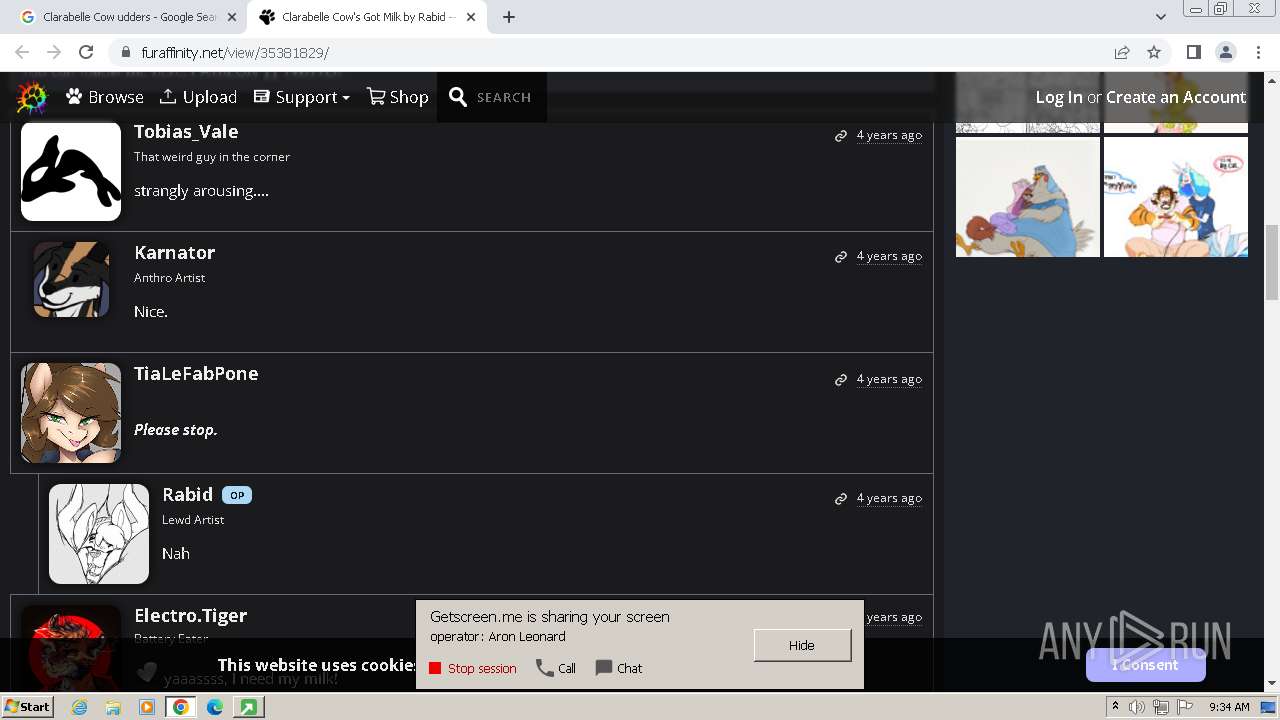
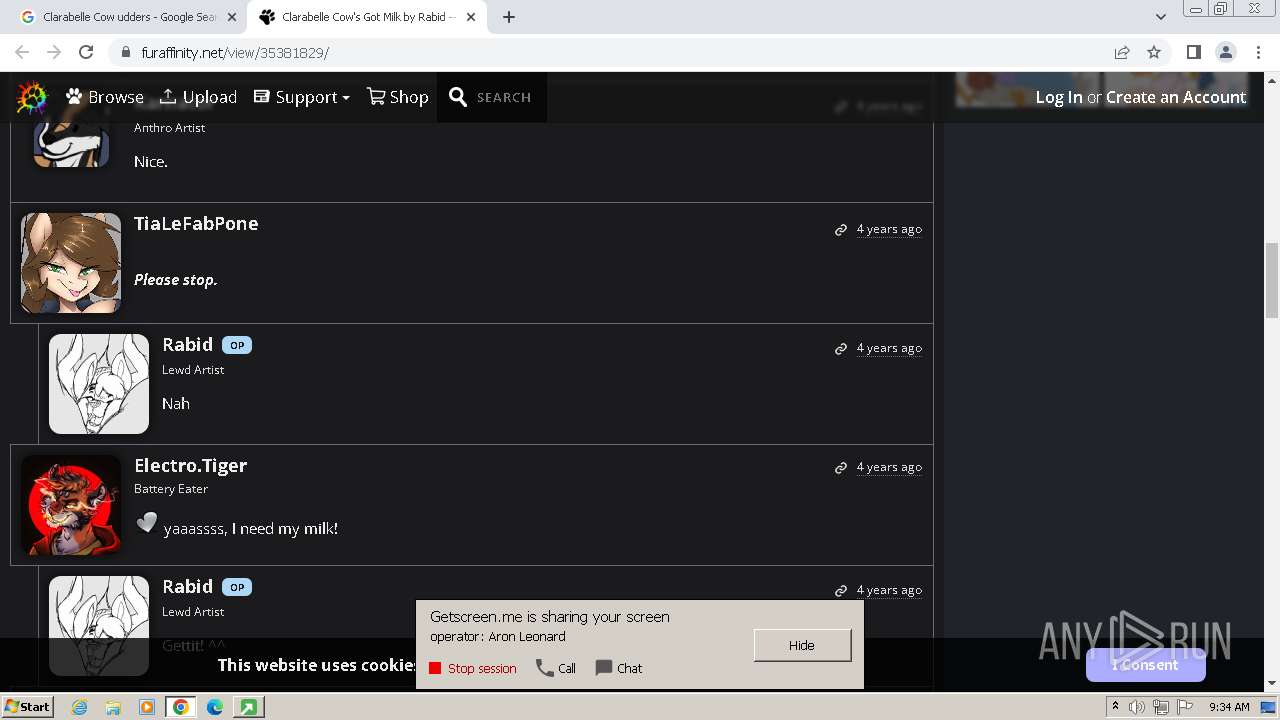
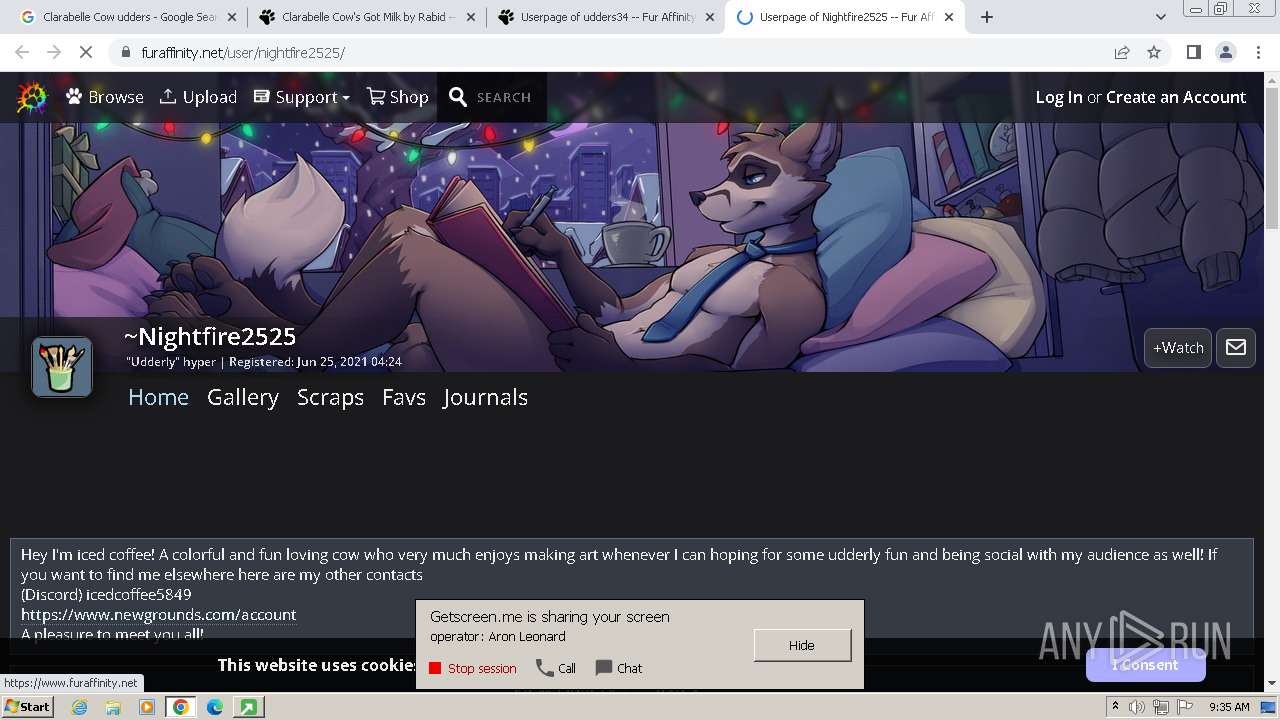
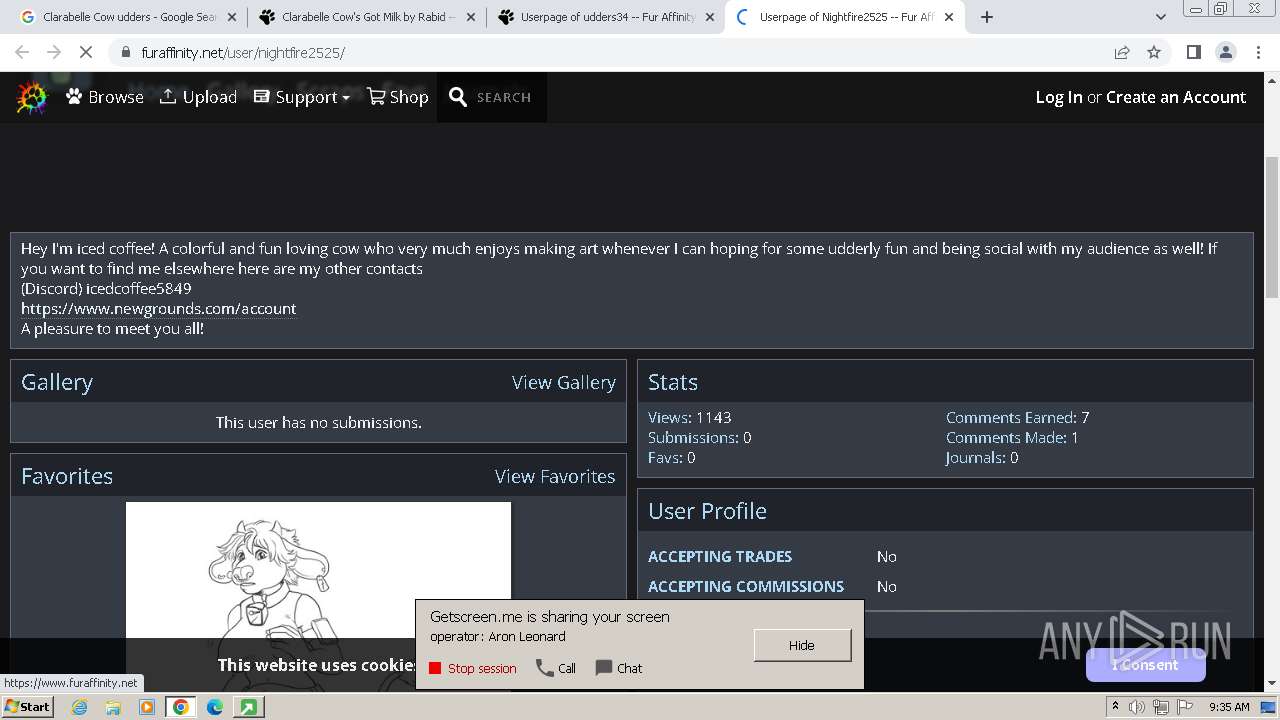
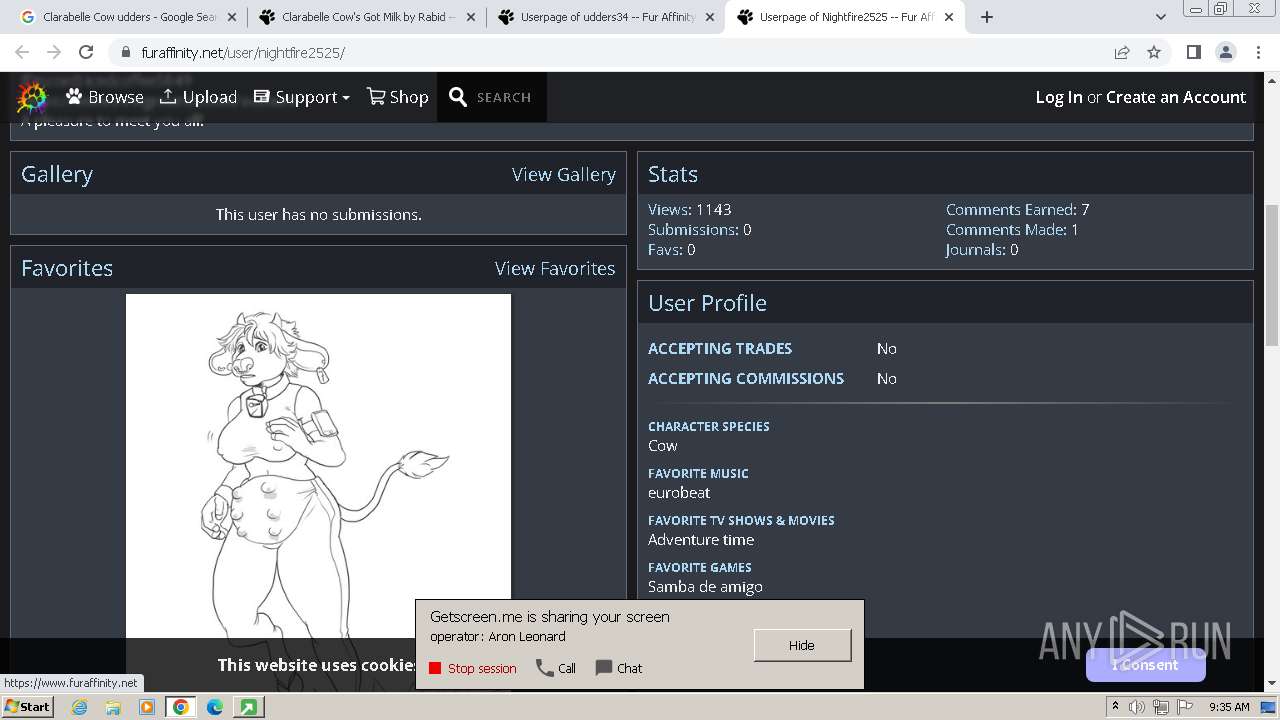
| CompanyName: | Getscreen.me |
| InternalName: | Getscreen.me |
| OriginalFileName: | getscreen.exe |
| ProductName: | Getscreen.me |
| FileVersion: | 2.18.1 |
| LegalCopyright: | Copyright (C) 2023 |
| ProductVersion: | 2.18.1 |
Total processes
102
Monitored processes
54
Malicious processes
2
Suspicious processes
0
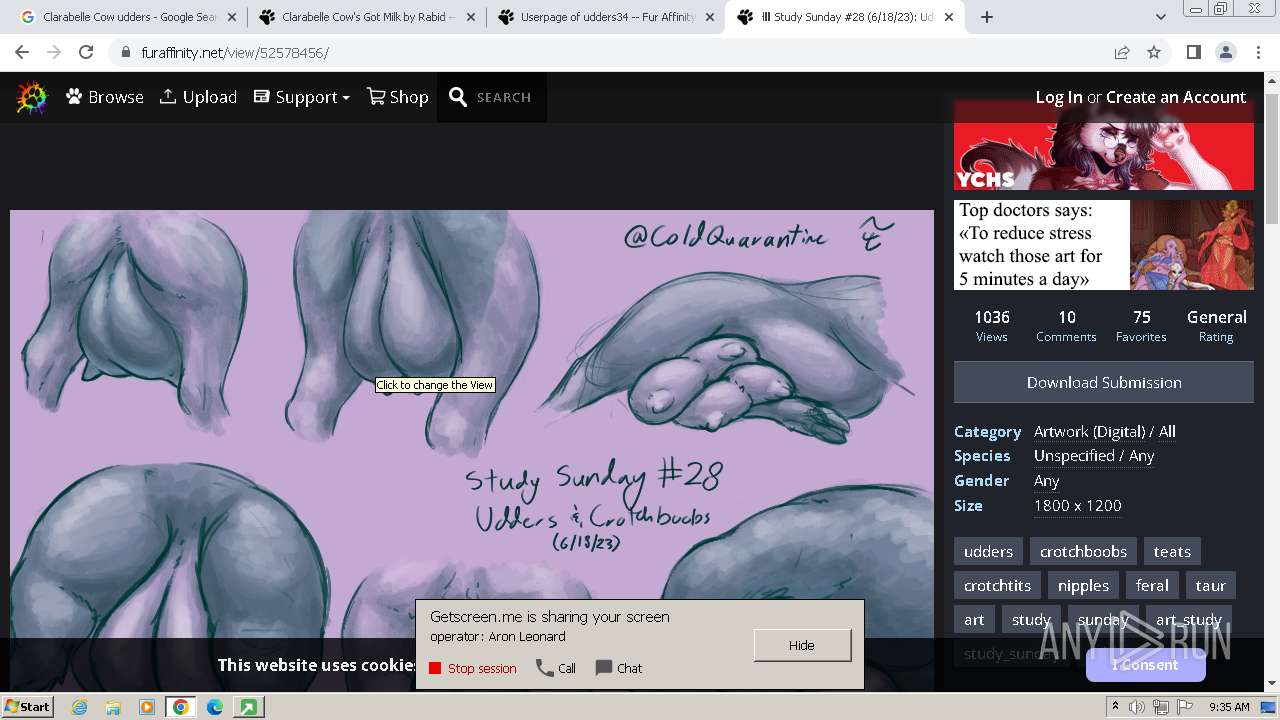
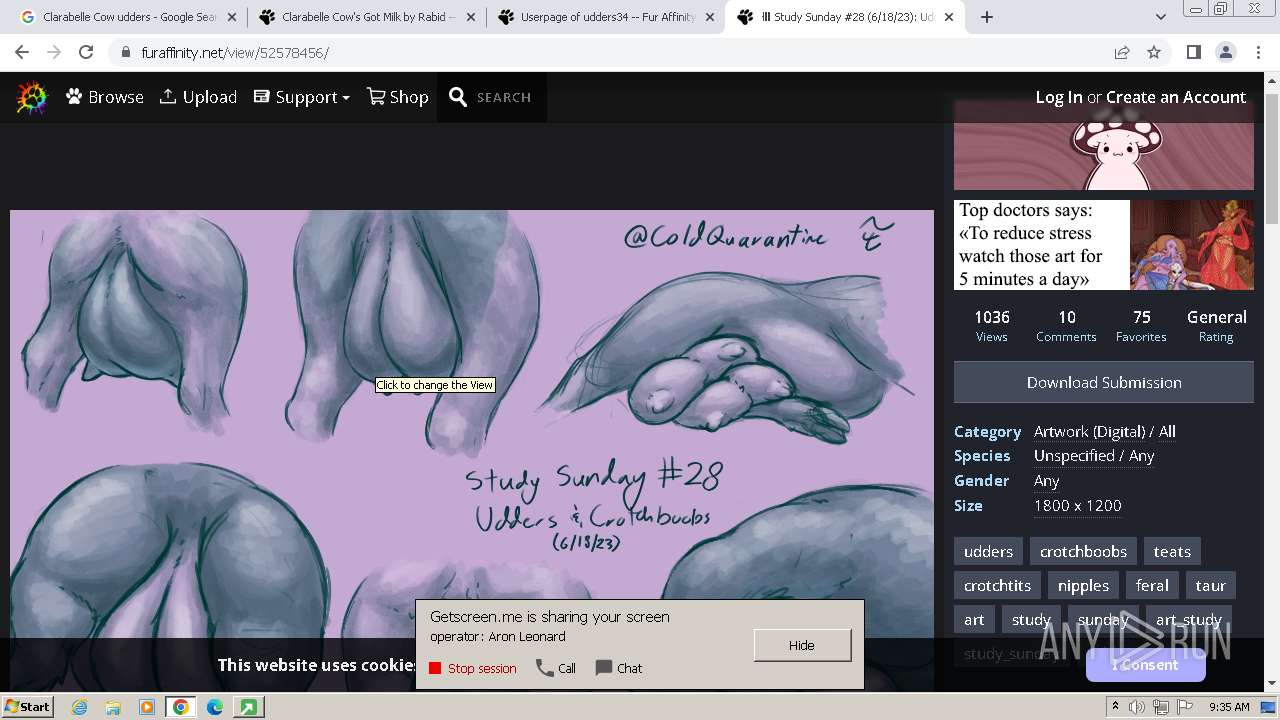
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1396 --field-trial-handle=1164,i,12782338820855371530,67575391446221337,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 604 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=3940 --field-trial-handle=1164,i,12782338820855371530,67575391446221337,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=2060 --field-trial-handle=1164,i,12782338820855371530,67575391446221337,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=40 --mojo-platform-channel-handle=3788 --field-trial-handle=1164,i,12782338820855371530,67575391446221337,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --mojo-platform-channel-handle=3908 --field-trial-handle=1164,i,12782338820855371530,67575391446221337,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 984 | "C:\Users\admin\AppData\Local\Temp\getscreen-865436612-x86 (1).exe" -epipe \\.\pipe\PCommand98xfircvscxggbwkf -environment | C:\Users\admin\AppData\Local\Temp\getscreen-865436612-x86 (1).exe | — | getscreen-865436612-x86 (1).exe | |||||||||||
User: admin Company: Getscreen.me Integrity Level: HIGH Exit code: 1 Version: 2.18.1 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bba8b38,0x6bba8b48,0x6bba8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1392 | "C:\Users\admin\AppData\Local\Temp\getscreen-865436612-x86 (1).exe" -cpipe \\.\pipe\PCommand96uonhhfzqdiqcrlt -child | C:\Users\admin\AppData\Local\Temp\getscreen-865436612-x86 (1).exe | getscreen-865436612-x86 (1).exe | ||||||||||||
User: SYSTEM Company: Getscreen.me Integrity Level: SYSTEM Exit code: 0 Version: 2.18.1 Modules
| |||||||||||||||
| 1484 | "C:\Users\admin\AppData\Local\Temp\getscreen-865436612-x86 (1).exe" -cpipe \\.\pipe\PCommand96uonhhfzqdiqcrlt -child | C:\Users\admin\AppData\Local\Temp\getscreen-865436612-x86 (1).exe | getscreen-865436612-x86 (1).exe | ||||||||||||
User: SYSTEM Company: Getscreen.me Integrity Level: SYSTEM Exit code: 4294967295 Version: 2.18.1 Modules
| |||||||||||||||
Total events
29 871
Read events
29 659
Write events
198
Delete events
14
Modification events
| (PID) Process: | (3700) getscreen-865436612-x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3700) getscreen-865436612-x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3700) getscreen-865436612-x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3700) getscreen-865436612-x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3464) getscreen-865436612-x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | getscreen-865436612-x86 (1).exe |
Value: 11001 | |||
| (PID) Process: | (3464) getscreen-865436612-x86 (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\MAIN\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | getscreen-865436612-x86 (1).exe |
Value: 11001 | |||
| (PID) Process: | (3464) getscreen-865436612-x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\getscreen.me |
| Operation: | write | Name: | http |
Value: 2 | |||
| (PID) Process: | (3464) getscreen-865436612-x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\getscreen.me |
| Operation: | write | Name: | https |
Value: 2 | |||
| (PID) Process: | (3464) getscreen-865436612-x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\EscDomains\getscreen.me |
| Operation: | write | Name: | http |
Value: 2 | |||
| (PID) Process: | (3464) getscreen-865436612-x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\EscDomains\getscreen.me |
| Operation: | write | Name: | https |
Value: 2 | |||
Executable files
4
Suspicious files
306
Text files
140
Unknown types
193
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2292 | getscreen-865436612-x86 (1).exe | C:\ProgramData\Getscreen.me\memory\0000pipe0PCommand96uonhhfzqdiqcrlt0 | — | |
MD5:— | SHA256:— | |||
| 2752 | getscreen-865436612-x86 (1).exe | C:\ProgramData\Getscreen.me\memory\A186DF344A6DDA0106A84CE64D6DDA01C00A0000FFFFFFFF | — | |
MD5:— | SHA256:— | |||
| 1484 | getscreen-865436612-x86 (1).exe | C:\ProgramData\Getscreen.me\memory\0000pipe0PCommand96uonhhfzqdiqcrlt0 | — | |
MD5:— | SHA256:— | |||
| 2752 | getscreen-865436612-x86 (1).exe | C:\ProgramData\Getscreen.me\memory\A186DF344A6DDA0177487EE94D6DDA01C00A0000FEFFFFFF | — | |
MD5:— | SHA256:— | |||
| 2028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF188f6a.TMP | — | |
MD5:— | SHA256:— | |||
| 2028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2752 | getscreen-865436612-x86 (1).exe | C:\ProgramData\Getscreen.me\folder\settings.dat | binary | |
MD5:70538B46B7825EC1178A6D8187FFE360 | SHA256:93C581FA8733098860CDBD0CFECF2AEE6028C39334C1D1705387726BD6C5A10C | |||
| 2028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 2028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF188f79.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 2028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
216
DNS requests
167
Threats
964
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 17.4 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 14.5 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 31.1 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 53.3 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 50.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 18.3 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 461 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 367 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 1.25 Mb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | unknown | binary | 1.28 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2752 | getscreen-865436612-x86 (1).exe | 78.47.165.25:443 | getscreen.me | Hetzner Online GmbH | DE | unknown |
2752 | getscreen-865436612-x86 (1).exe | 162.55.165.163:3478 | px-eu1.getscreen.me | — | — | unknown |
2752 | getscreen-865436612-x86 (1).exe | 146.185.219.90:3478 | px-il1.getscreen.me | — | — | unknown |
2752 | getscreen-865436612-x86 (1).exe | 45.65.9.108:3478 | px-us1.getscreen.me | — | — | unknown |
2752 | getscreen-865436612-x86 (1).exe | 95.85.71.16:3478 | px-in1.getscreen.me | — | — | unknown |
2752 | getscreen-865436612-x86 (1).exe | 5.188.225.23:3478 | px-br1.getscreen.me | — | — | unknown |
2752 | getscreen-865436612-x86 (1).exe | 5.161.108.215:3478 | px-us2.getscreen.me | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
getscreen.me |
| unknown |
image.getscreen.me |
| unknown |
px-us2.getscreen.me |
| unknown |
px-il1.getscreen.me |
| unknown |
px-us1.getscreen.me |
| unknown |
px-eu1.getscreen.me |
| unknown |
px-in1.getscreen.me |
| unknown |
px-au1.getscreen.me |
| unknown |
px-br1.getscreen.me |
| unknown |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2752 | getscreen-865436612-x86 (1).exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2752 | getscreen-865436612-x86 (1).exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2752 | getscreen-865436612-x86 (1).exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2752 | getscreen-865436612-x86 (1).exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2752 | getscreen-865436612-x86 (1).exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2752 | getscreen-865436612-x86 (1).exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2752 | getscreen-865436612-x86 (1).exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2752 | getscreen-865436612-x86 (1).exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2752 | getscreen-865436612-x86 (1).exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2752 | getscreen-865436612-x86 (1).exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |