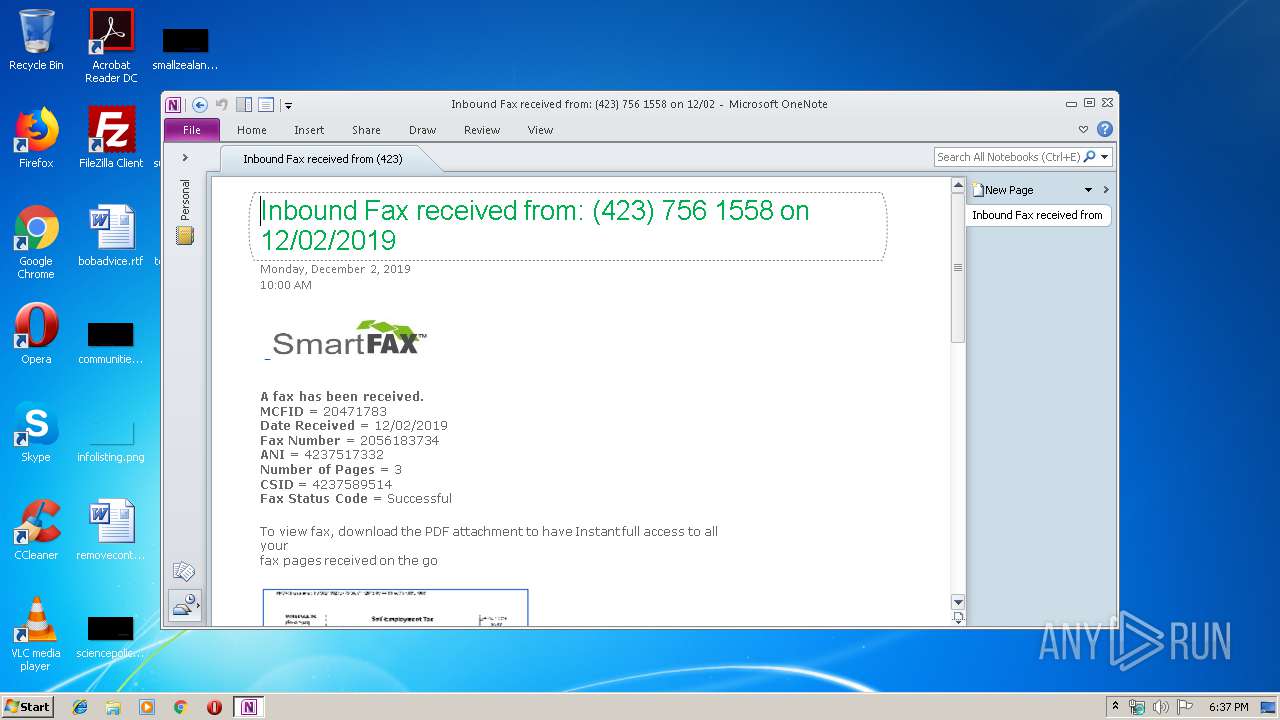
| File name: | Inbound Fax received from (423).one |
| Full analysis: | https://app.any.run/tasks/bc86e6f6-3adc-40de-b7d9-da675172c7c5 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 18:37:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | 4CC5A3DC3AA8CFD26BEEB4CCFBF7C5E2 |
| SHA1: | 9FEE5C1AB48E553BD6FA7114508F678C6E77AF72 |
| SHA256: | E48244099606259D2FA6DBE003934CCA181338D5E96132C2D531157753116605 |
| SSDEEP: | 1536:/ELTDB188HMNGEOytDzwa44N6yGfaCcFEANani:/ELnB188HMNvD0a5EfxcFEAQn |
MALICIOUS
Writes to a start menu file
- ONENOTE.EXE (PID: 944)
Unusual execution from Microsoft Office
- ONENOTE.EXE (PID: 944)
SUSPICIOUS
Starts Internet Explorer
- ONENOTE.EXE (PID: 944)
Starts Microsoft Office Application
- ONENOTE.EXE (PID: 944)
INFO
Creates files in the user directory
- ONENOTE.EXE (PID: 944)
Changes internet zones settings
- iexplore.exe (PID: 1884)
Reads internet explorer settings
- iexplore.exe (PID: 2812)
Reads settings of System Certificates
- iexplore.exe (PID: 1884)
Reads Internet Cache Settings
- iexplore.exe (PID: 2812)
- iexplore.exe (PID: 1884)
Changes settings of System certificates
- iexplore.exe (PID: 1884)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1884)
Application launched itself
- iexplore.exe (PID: 1884)
Reads Microsoft Office registry keys
- ONENOTE.EXE (PID: 944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .one | | | Microsoft OneNote note (100) |
|---|
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 944 | "C:\Program Files\Microsoft Office\Office14\ONENOTE.EXE" "C:\Users\admin\AppData\Local\Temp\Inbound Fax received from (423).one" | C:\Program Files\Microsoft Office\Office14\ONENOTE.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Exit code: 0 Version: 14.0.6022.1000 Modules
| |||||||||||||||
| 1784 | /tsr | C:\Program Files\Microsoft Office\Office14\ONENOTEM.EXE | — | ONENOTE.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Quick Launcher Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | ONENOTE.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1884 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 341
Read events
1 163
Write events
171
Delete events
7
Modification events
| (PID) Process: | (944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (944) ONENOTE.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | OneNoteFiles |
Value: 1333919750 | |||
| (PID) Process: | (944) ONENOTE.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1333919924 | |||
Executable files
0
Suspicious files
0
Text files
23
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 944 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\CVRA737.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1884 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1884 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 944 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Microsoft\OneNote\14.0\OneNoteOfflineCache_Files\6182b896-cf62-4007-abee-2b416c9c0180.png | image | |
MD5:— | SHA256:— | |||
| 944 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\{BD644A3F-24BA-4577-8BFE-A6151959A882} | image | |
MD5:— | SHA256:— | |||
| 2812 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 944 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Microsoft\OneNote\14.0\OneNoteOfflineCache_Files\f8f8698b-d7ab-40ba-9067-244241fca1b4.png | image | |
MD5:— | SHA256:— | |||
| 944 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\{AD2C8946-5905-483E-9C59-C87224864D8E} | image | |
MD5:— | SHA256:— | |||
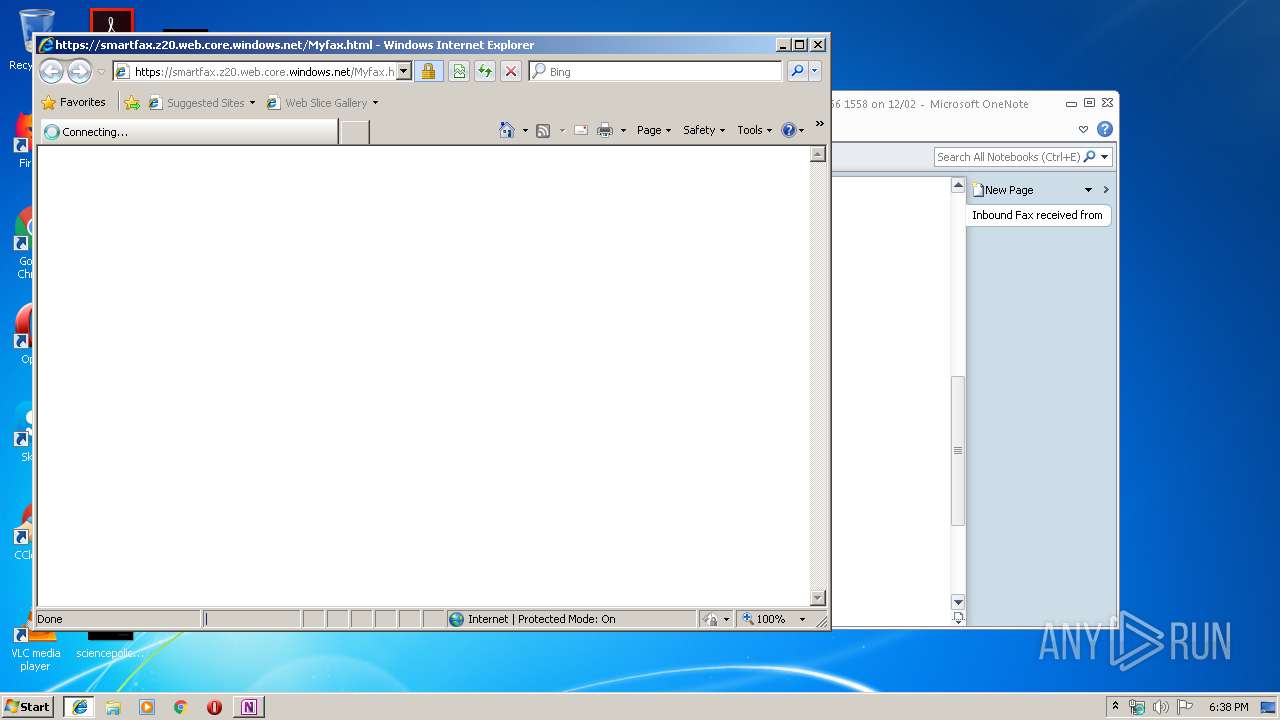
| 944 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\Myfax[1].html | text | |
MD5:— | SHA256:— | |||
| 944 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Microsoft\OneNote\14.0\OneNoteOfflineCache_Files\dfcbd1cb-0a4c-474f-beae-23f1c3c69891.png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
14
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
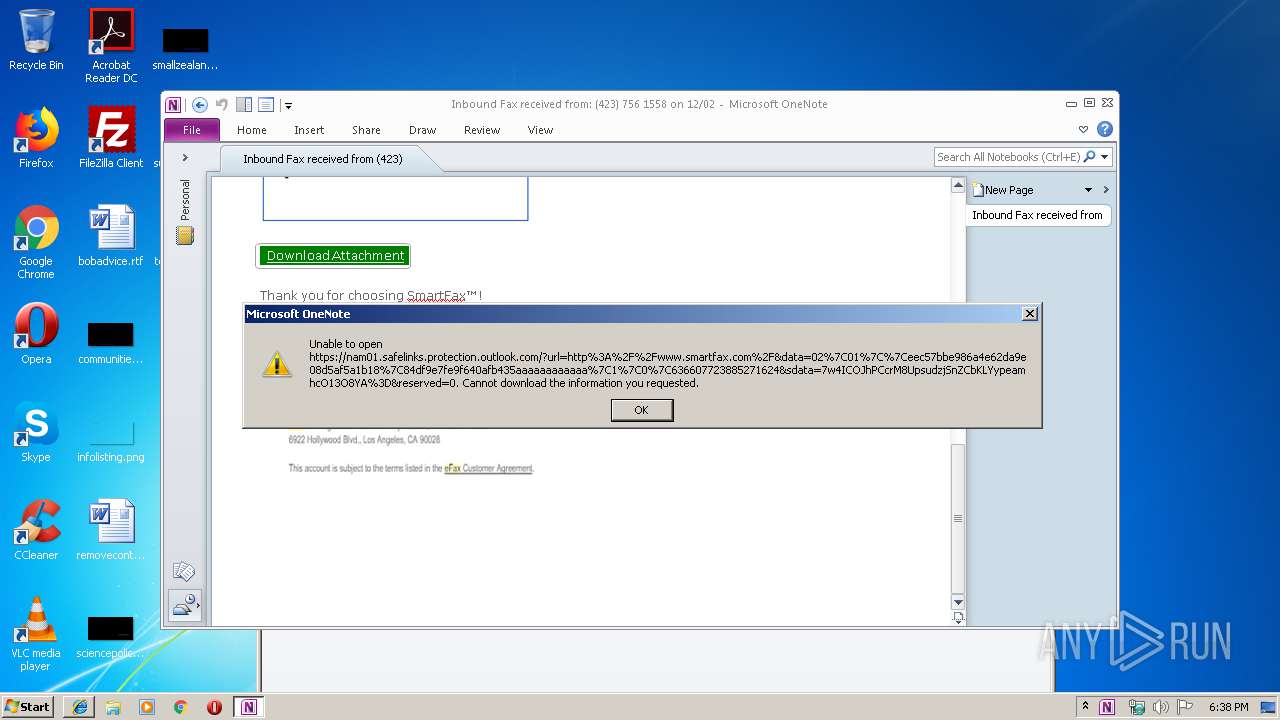
944 | ONENOTE.EXE | GET | 301 | 2.19.38.37:80 | http://www.smartfax.com/ | unknown | — | — | malicious |
1884 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
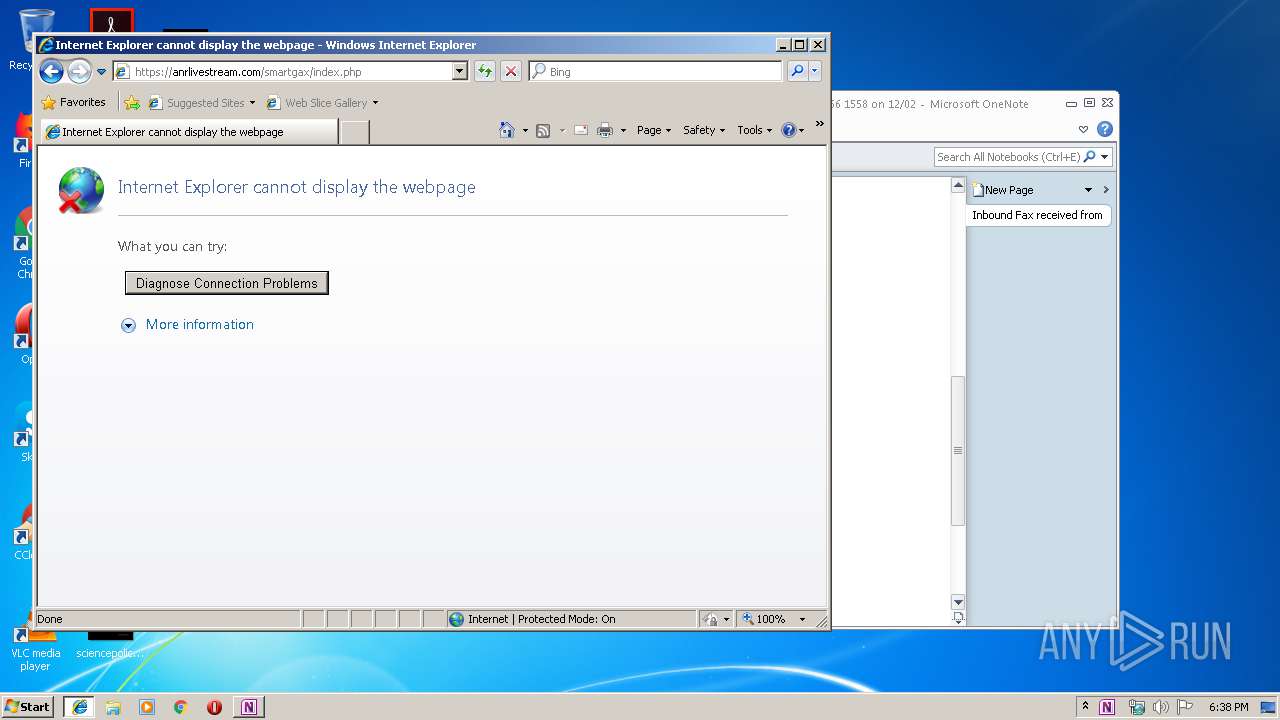
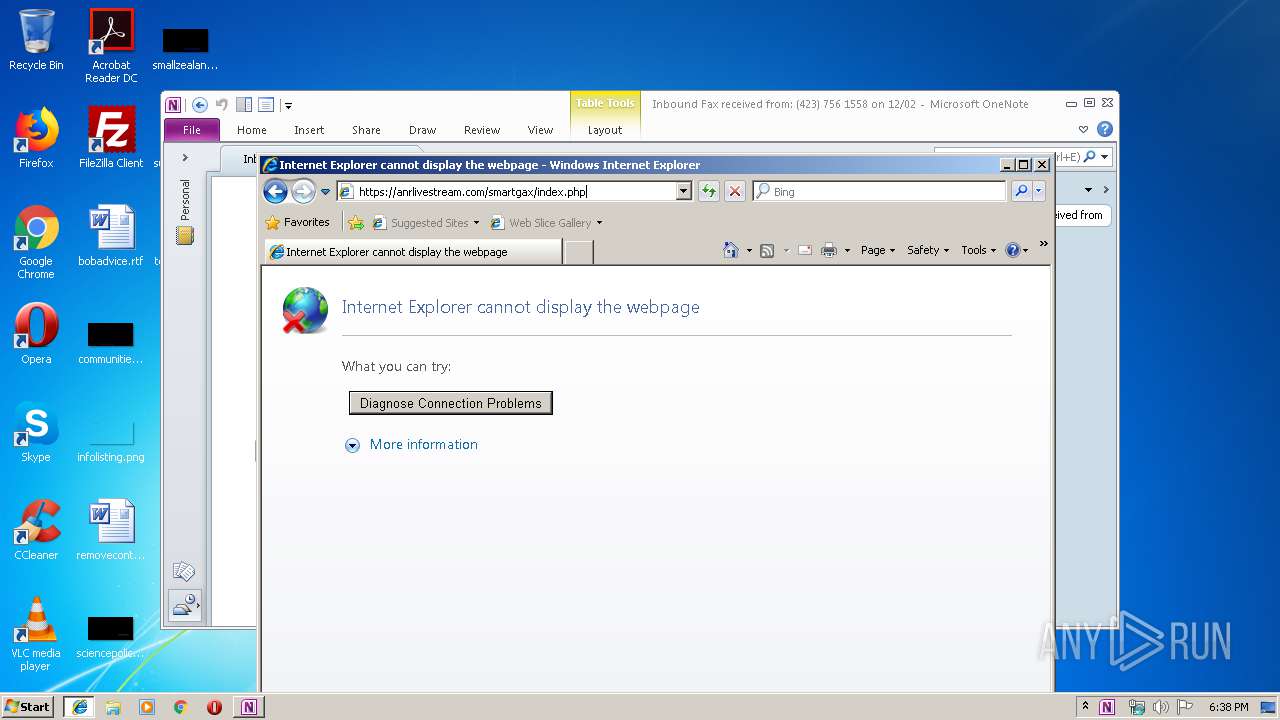
2812 | iexplore.exe | 18.197.25.107:443 | anrlivestream.com | Amazon.com, Inc. | DE | suspicious |
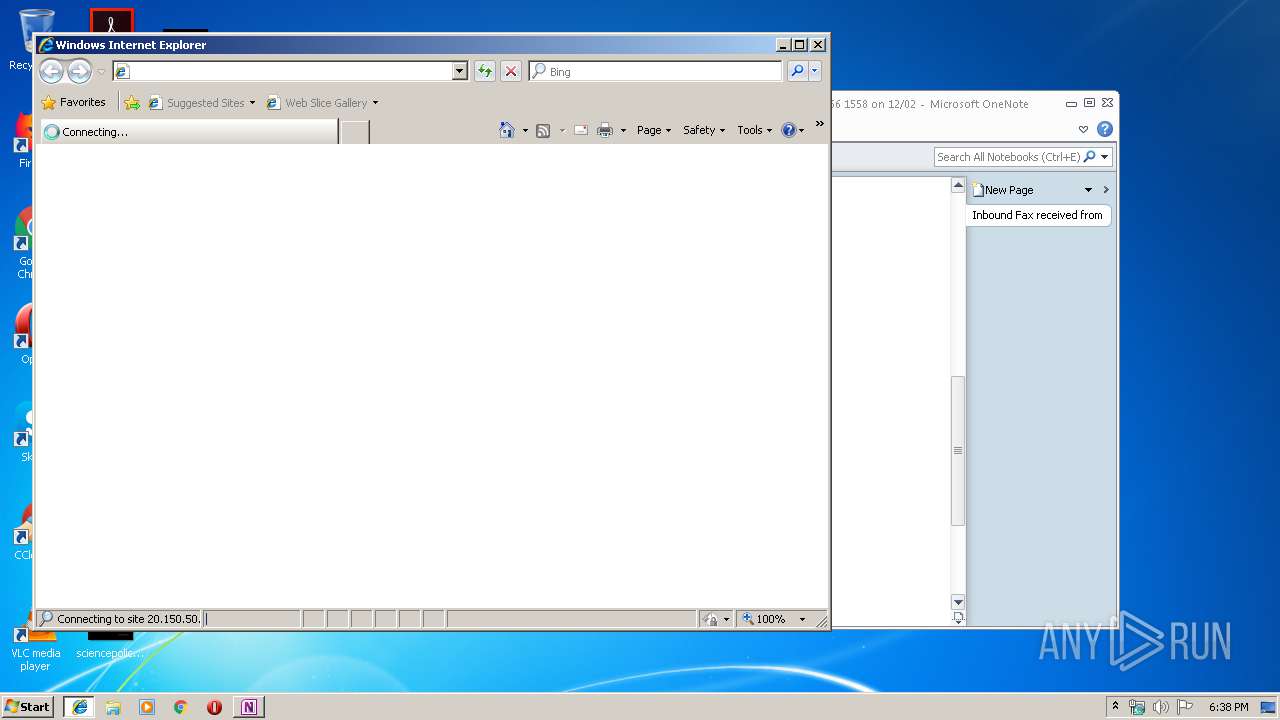
944 | ONENOTE.EXE | 20.150.50.1:443 | smartfax.z20.web.core.windows.net | — | US | unknown |
1884 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 2.19.39.72:443 | www.efax.eu | Akamai International B.V. | — | whitelisted |
944 | ONENOTE.EXE | 2.19.39.72:443 | www.efax.eu | Akamai International B.V. | — | whitelisted |
944 | ONENOTE.EXE | 104.47.33.28:443 | nam01.safelinks.protection.outlook.com | Microsoft Corporation | US | whitelisted |
944 | ONENOTE.EXE | 2.19.38.37:80 | www.smartfax.com | Akamai International B.V. | — | whitelisted |
2812 | iexplore.exe | 20.150.50.1:443 | smartfax.z20.web.core.windows.net | — | US | unknown |
— | — | 18.197.25.107:443 | anrlivestream.com | Amazon.com, Inc. | DE | suspicious |
1884 | iexplore.exe | 20.150.50.1:443 | smartfax.z20.web.core.windows.net | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
smartfax.z20.web.core.windows.net |
| unknown |
www.bing.com |
| whitelisted |
anrlivestream.com |
| suspicious |
nam01.safelinks.protection.outlook.com |
| whitelisted |
www.smartfax.com |
| malicious |
www.efax.eu |
| suspicious |