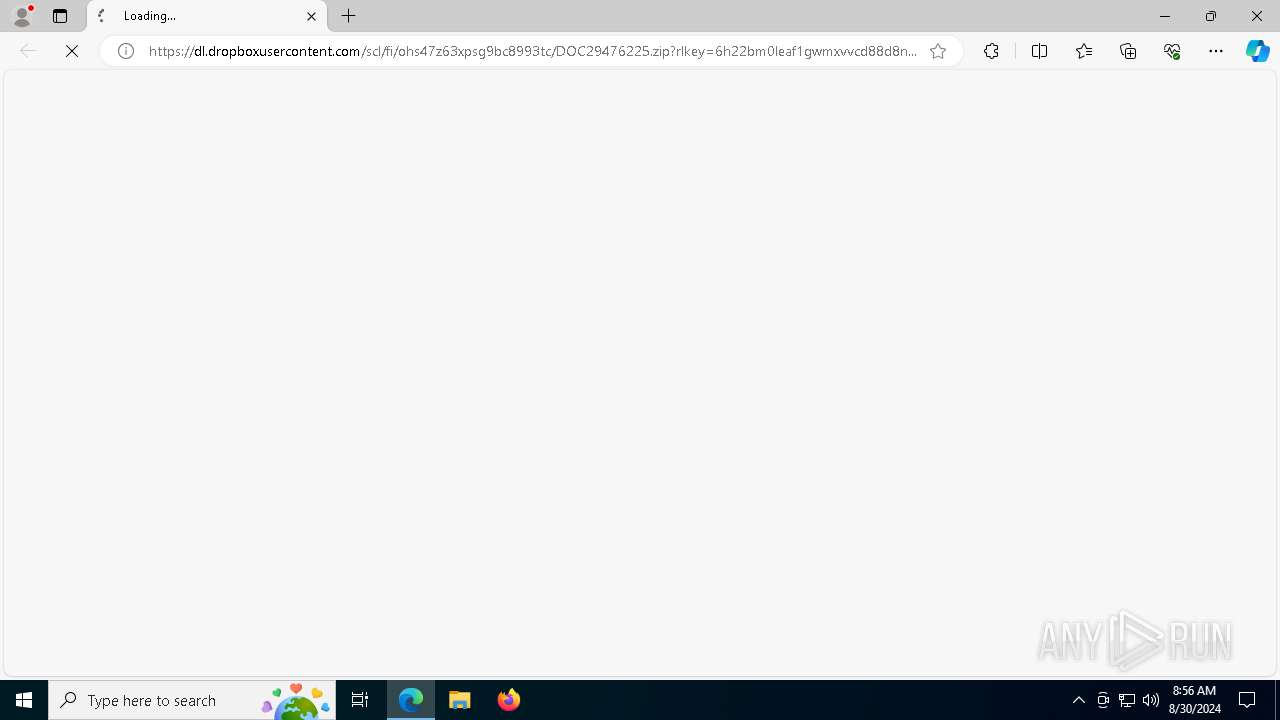
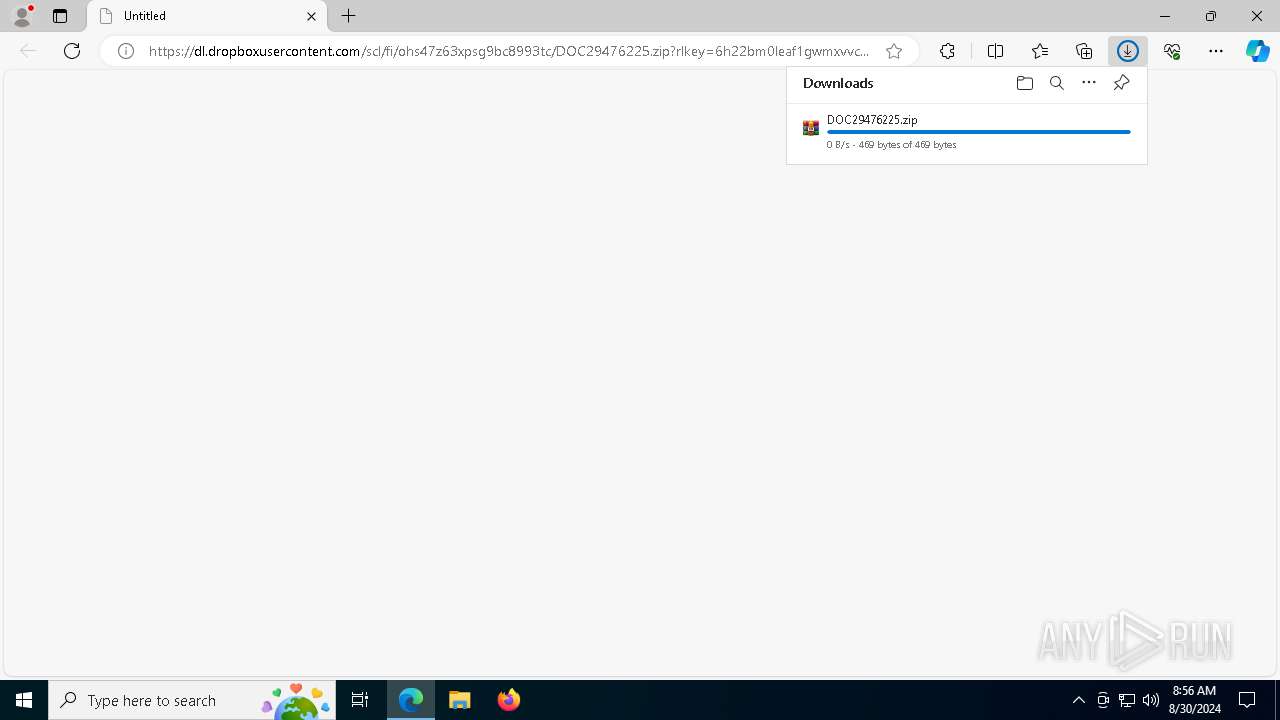
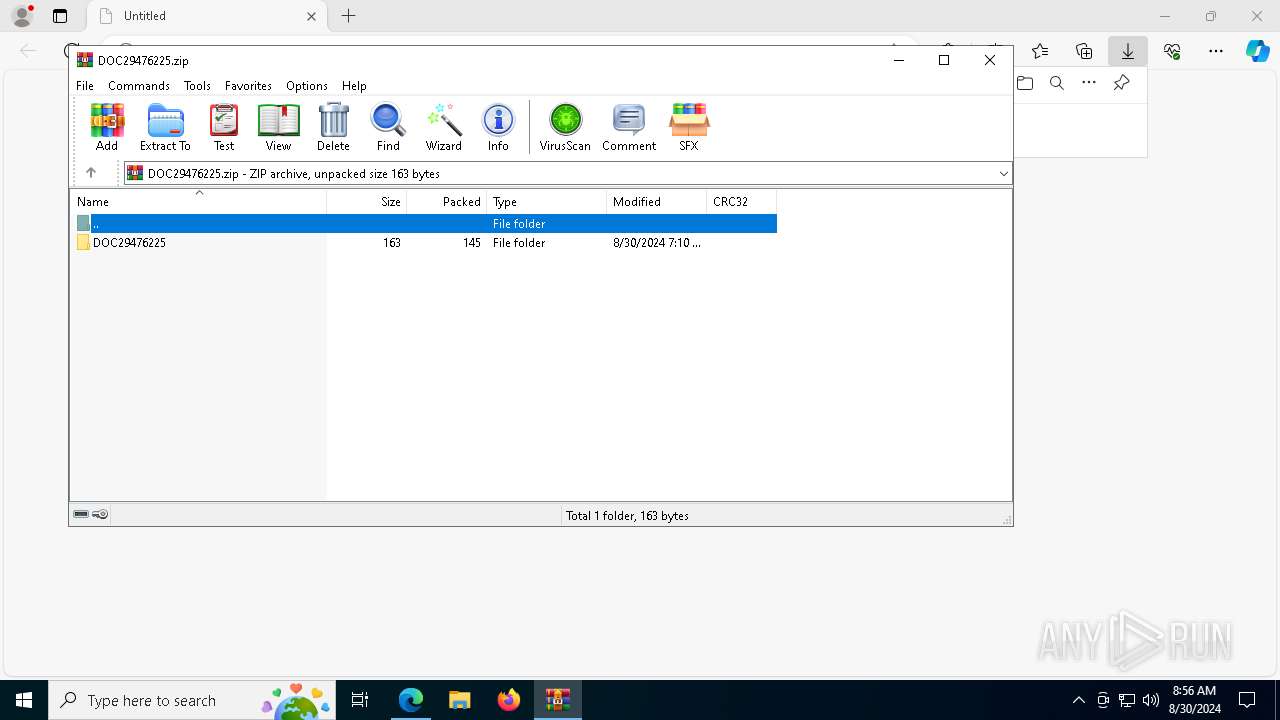
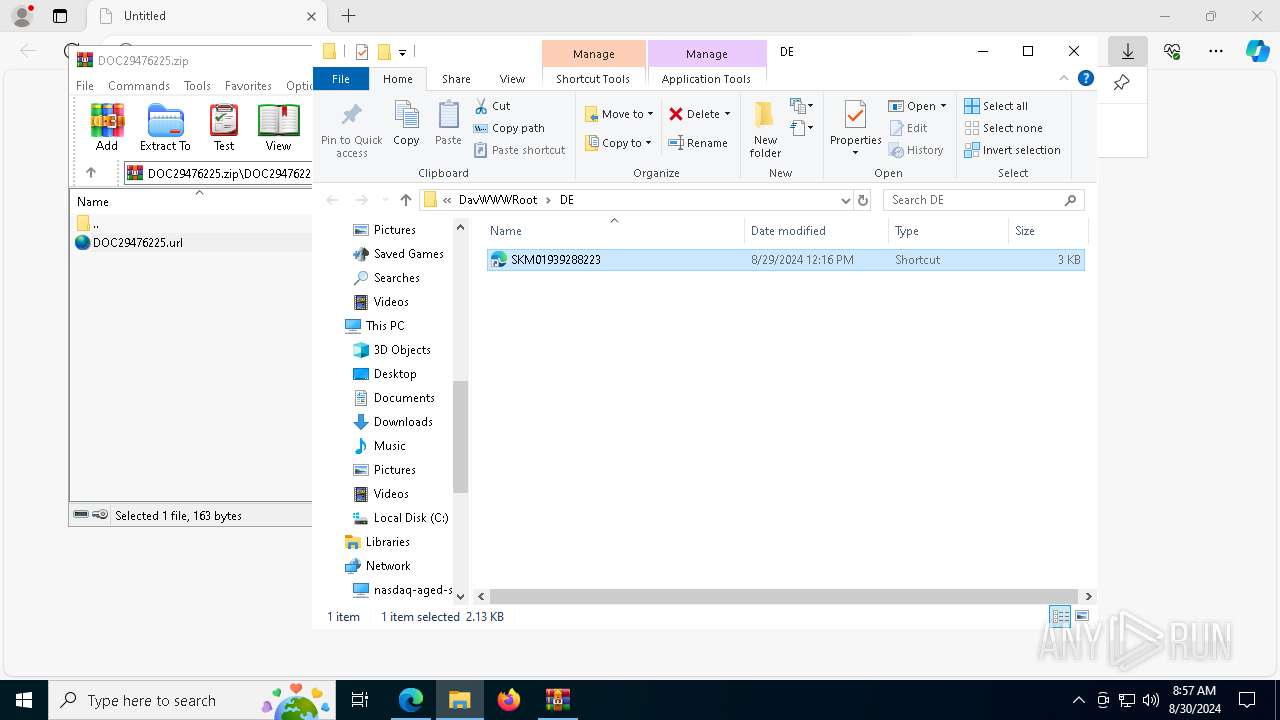
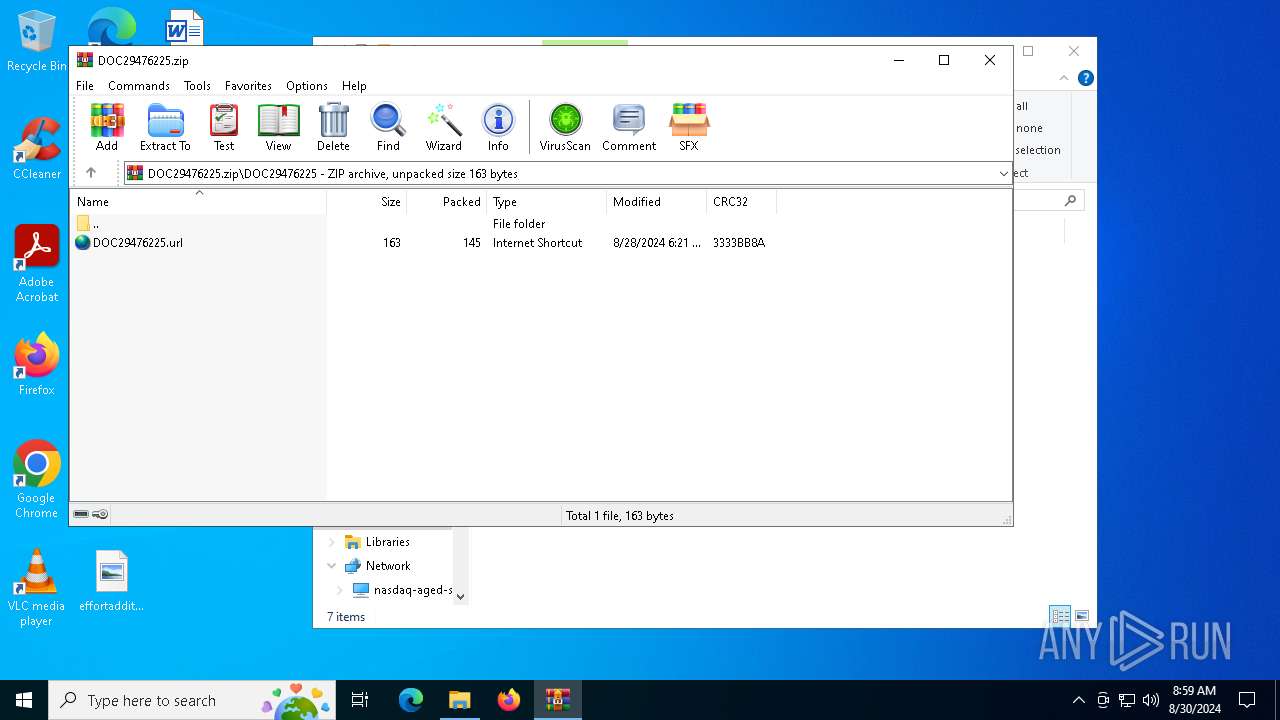
| URL: | https://dl.dropboxusercontent.com/scl/fi/ohs47z63xpsg9bc8993tc/DOC29476225.zip?rlkey=6h22bm0leaf1gwmxvvcd88d8n&st=36jjnqw8&dl=0 |
| Full analysis: | https://app.any.run/tasks/fad58c97-46b0-4414-84c7-781f9765eea2 |
| Verdict: | Malicious activity |
| Analysis date: | August 30, 2024, 08:56:45 |
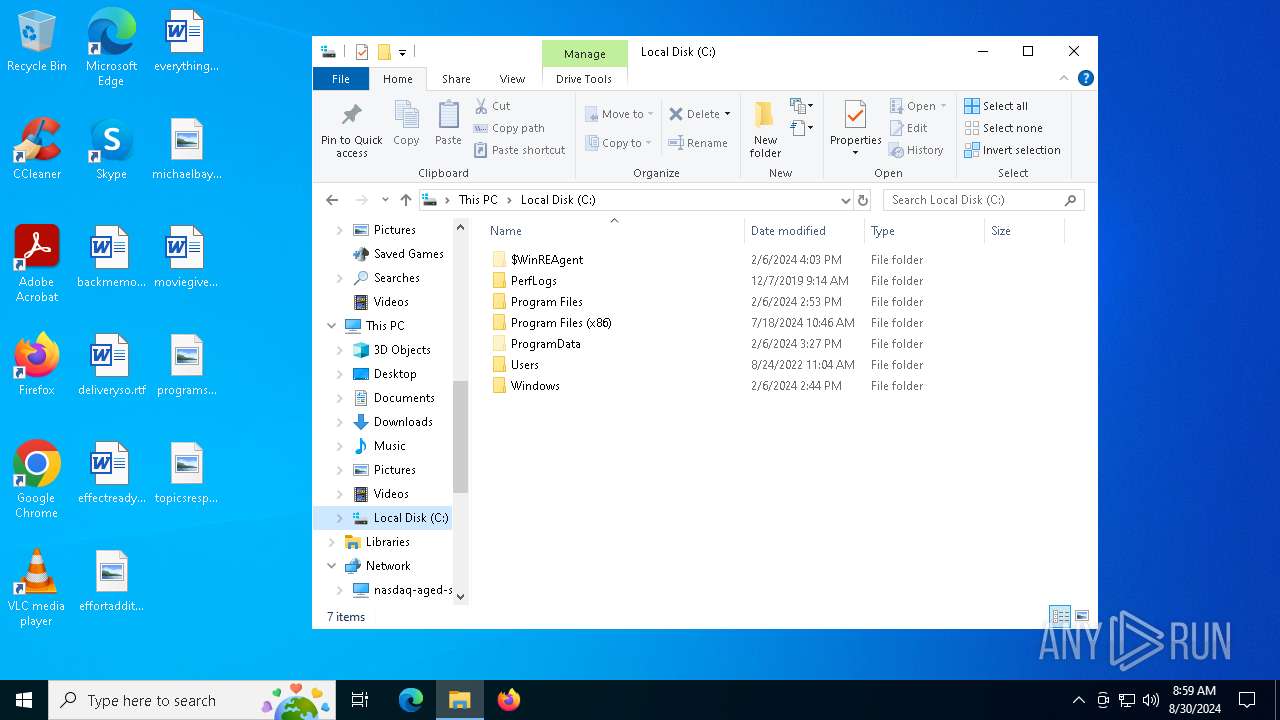
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
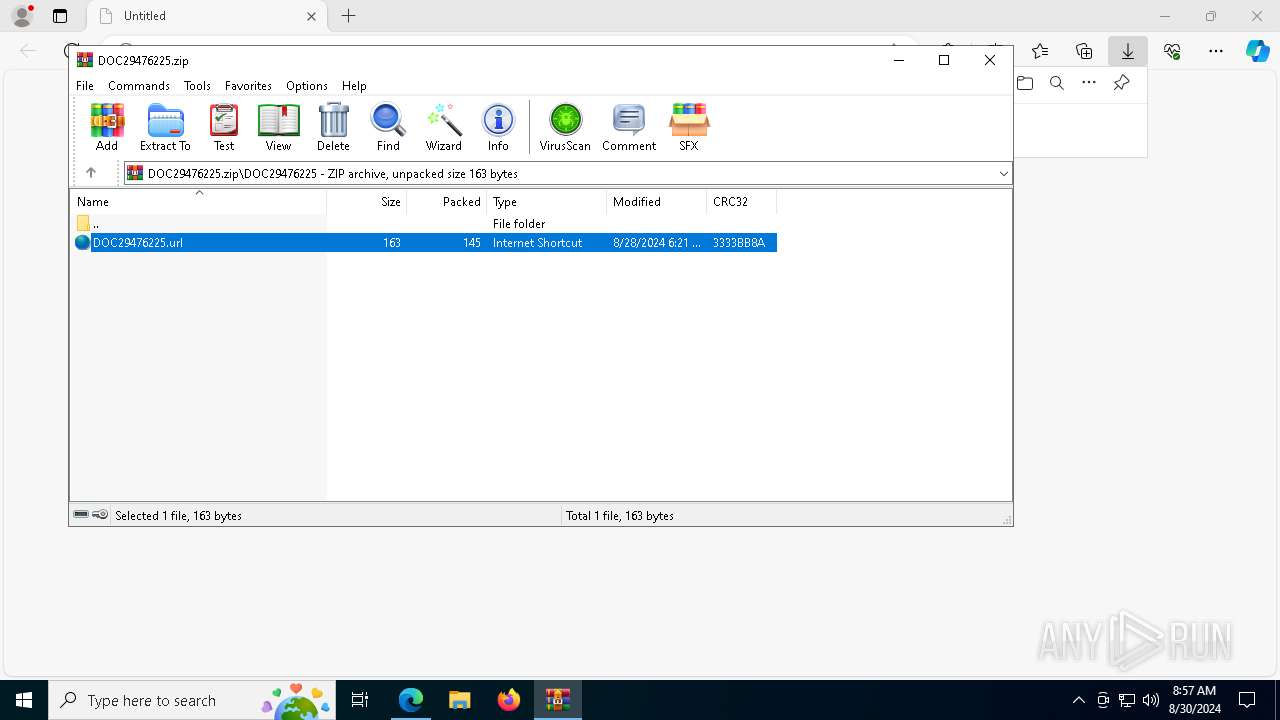
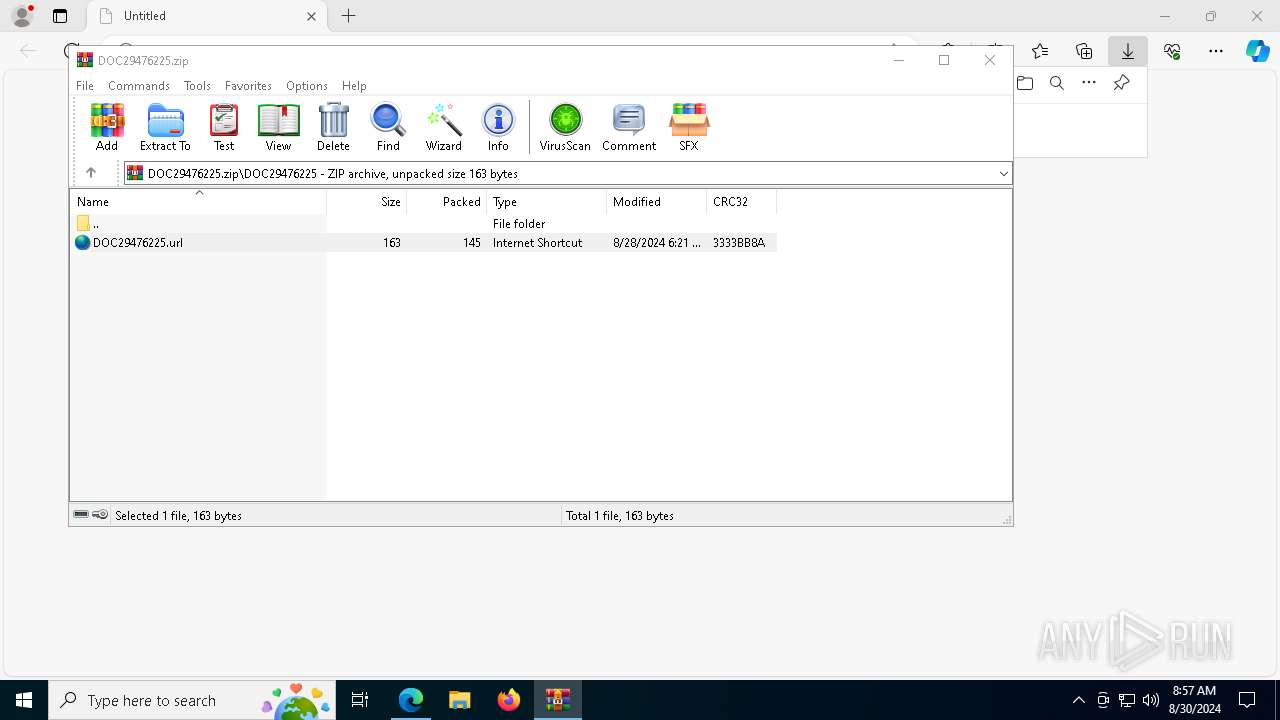
| MD5: | 9C651103E8104C159DDF444510B2A174 |
| SHA1: | 0C209439CB3F371A58B7954978515C8536EDB992 |
| SHA256: | E476C6096E9866D61100E9D30AA6B2E978376FE6F029F7CA93863C5E875D8B1B |
| SSDEEP: | 3:N8RdNcvALtGTU6RRVacWGKhdMqXraZOAcYjq2I1WrILUS3WV:27NFGrVGhMqbD5YFxrILzS |
MALICIOUS
Changes the autorun value in the registry
- python-3.12.5-amd64.exe (PID: 7040)
- python-3.12.5-amd64.exe (PID: 2580)
SUSPICIOUS
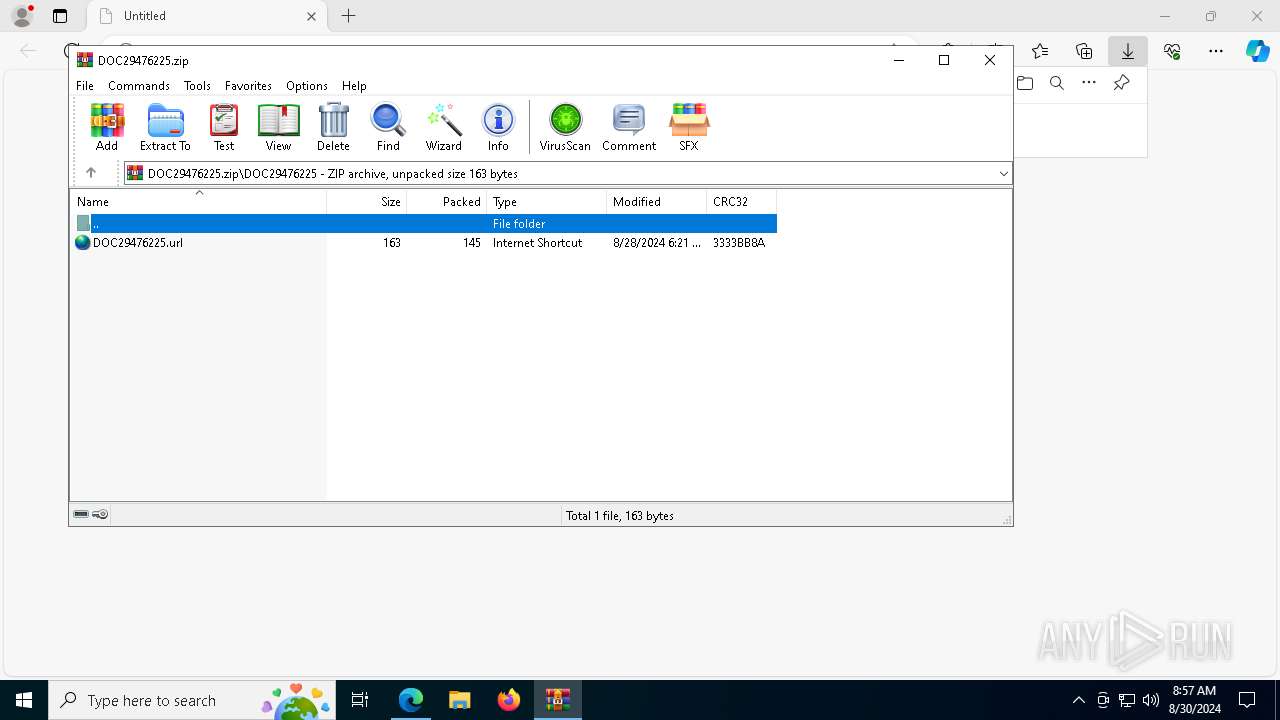
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6644)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 2992)
Executing commands from a ".bat" file
- conhost.exe (PID: 7212)
- conhost.exe (PID: 8100)
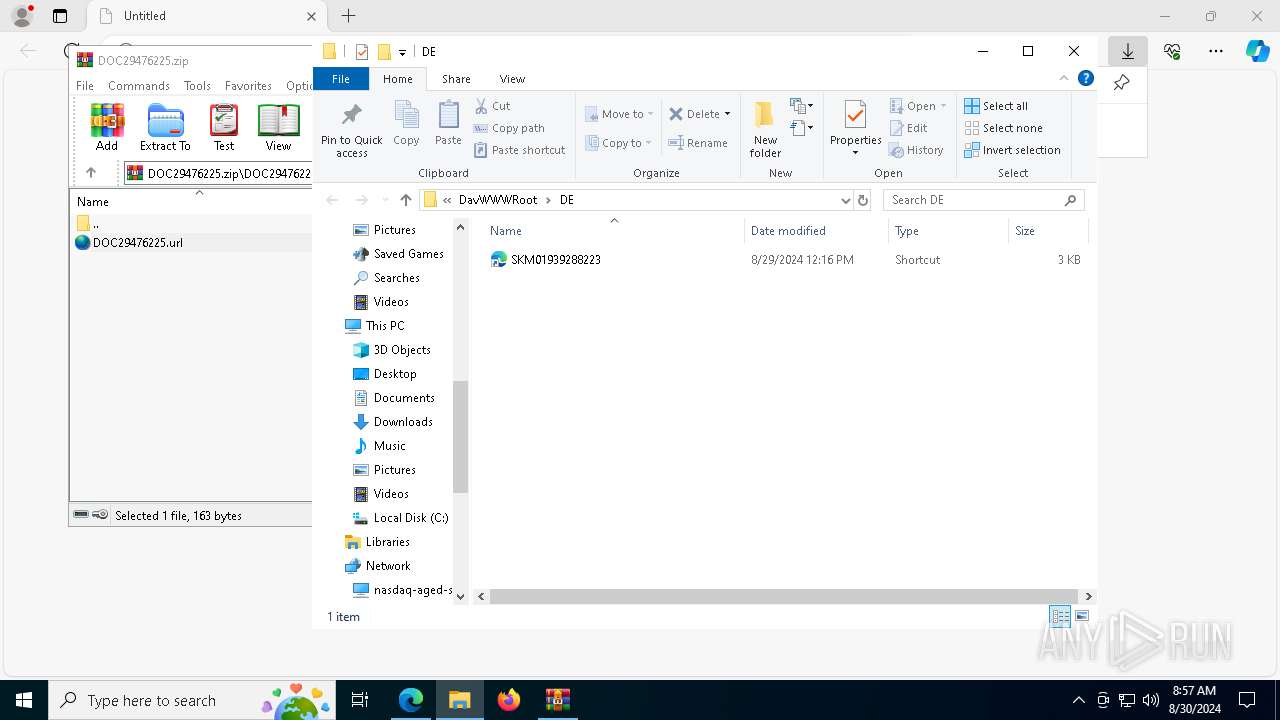
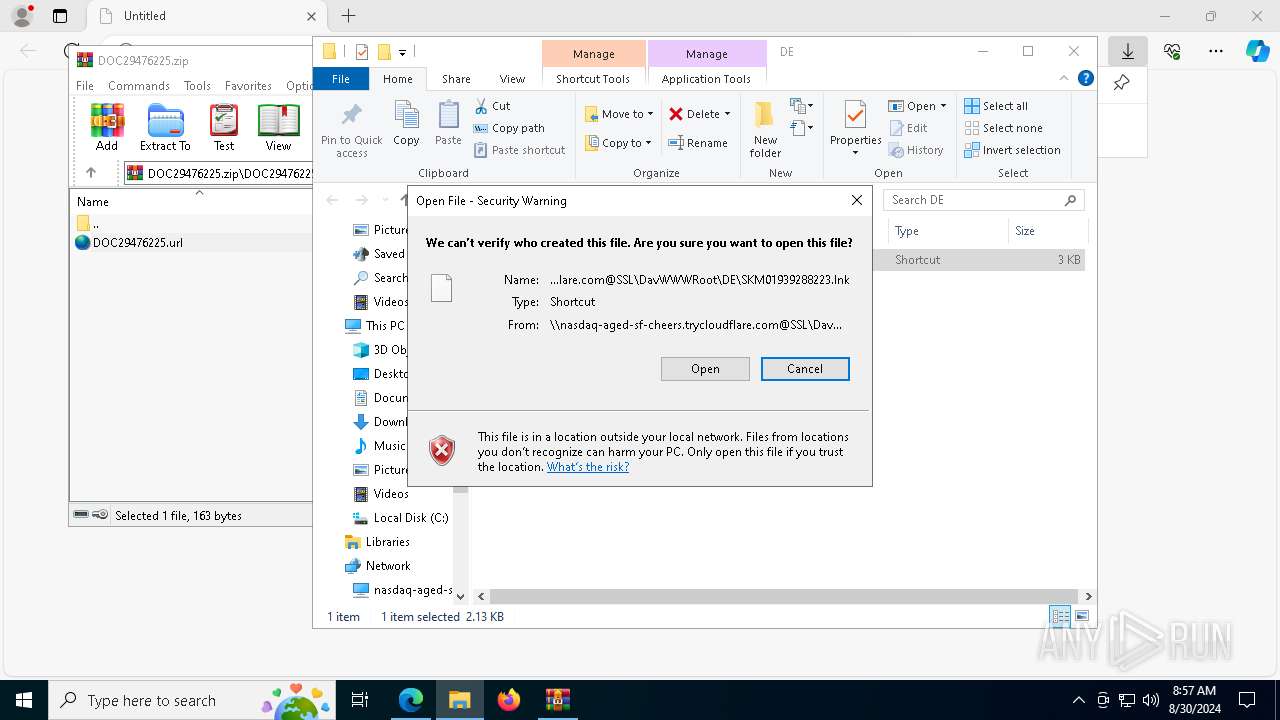
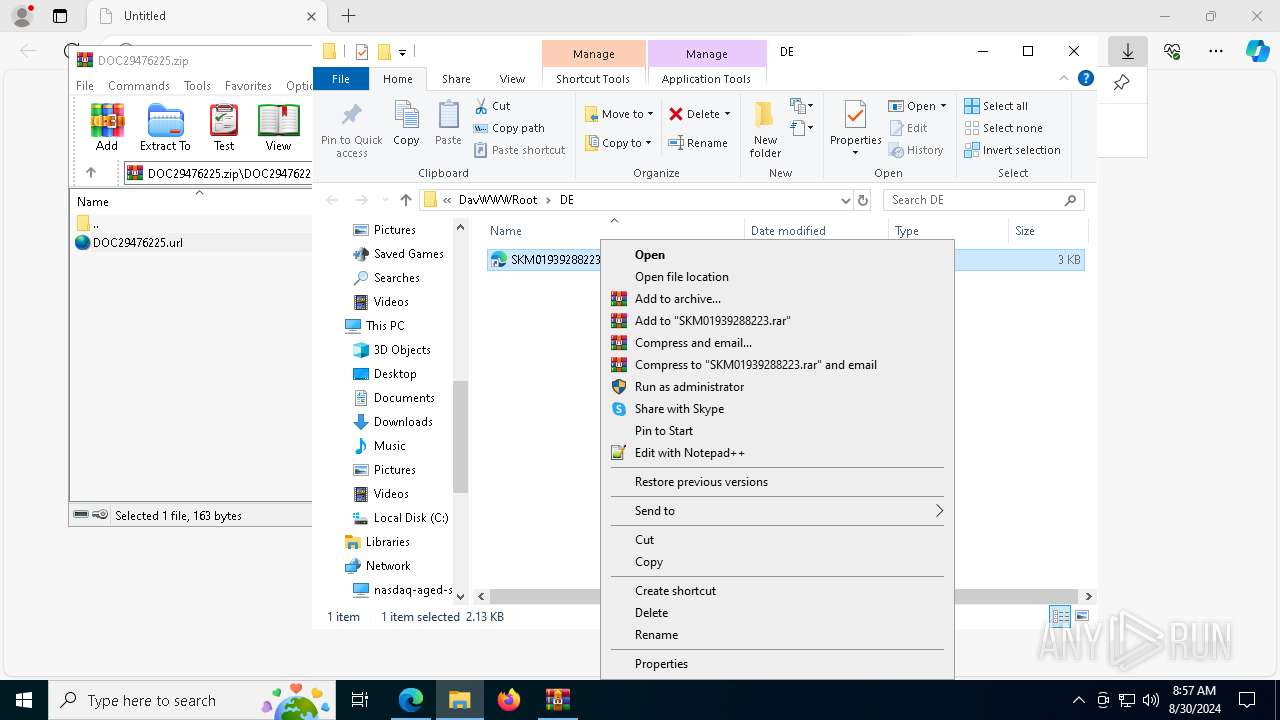
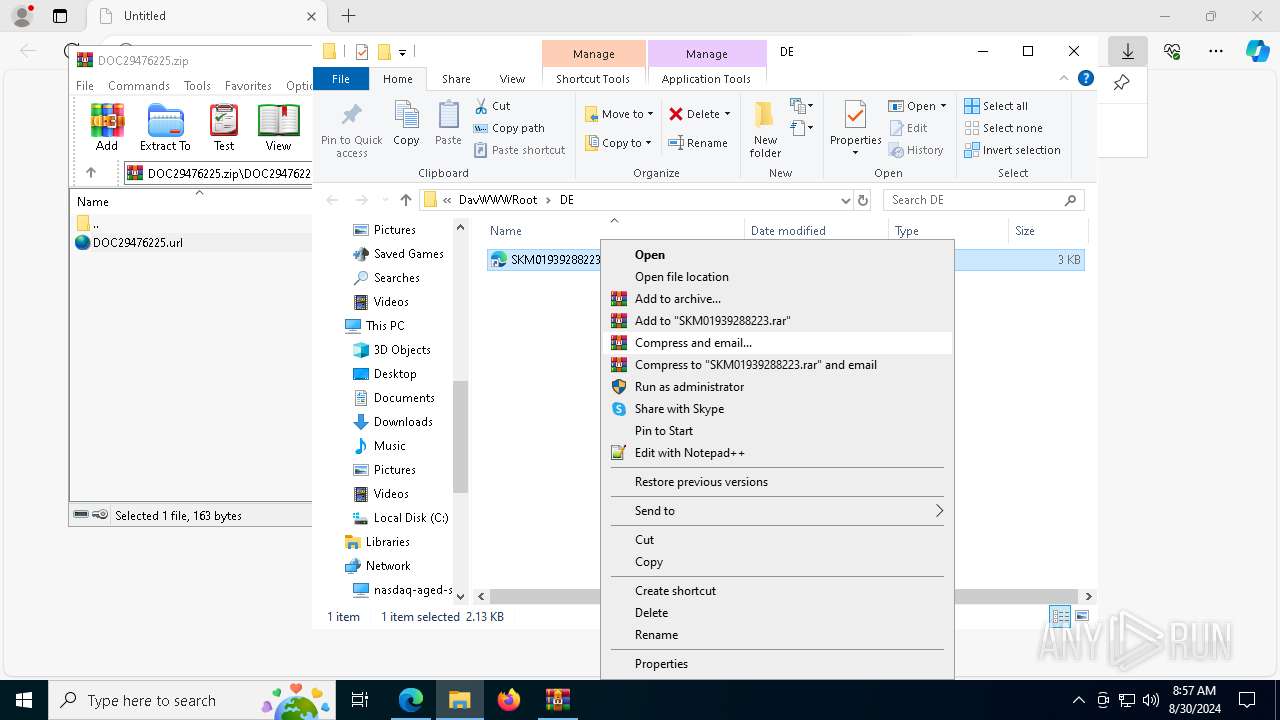
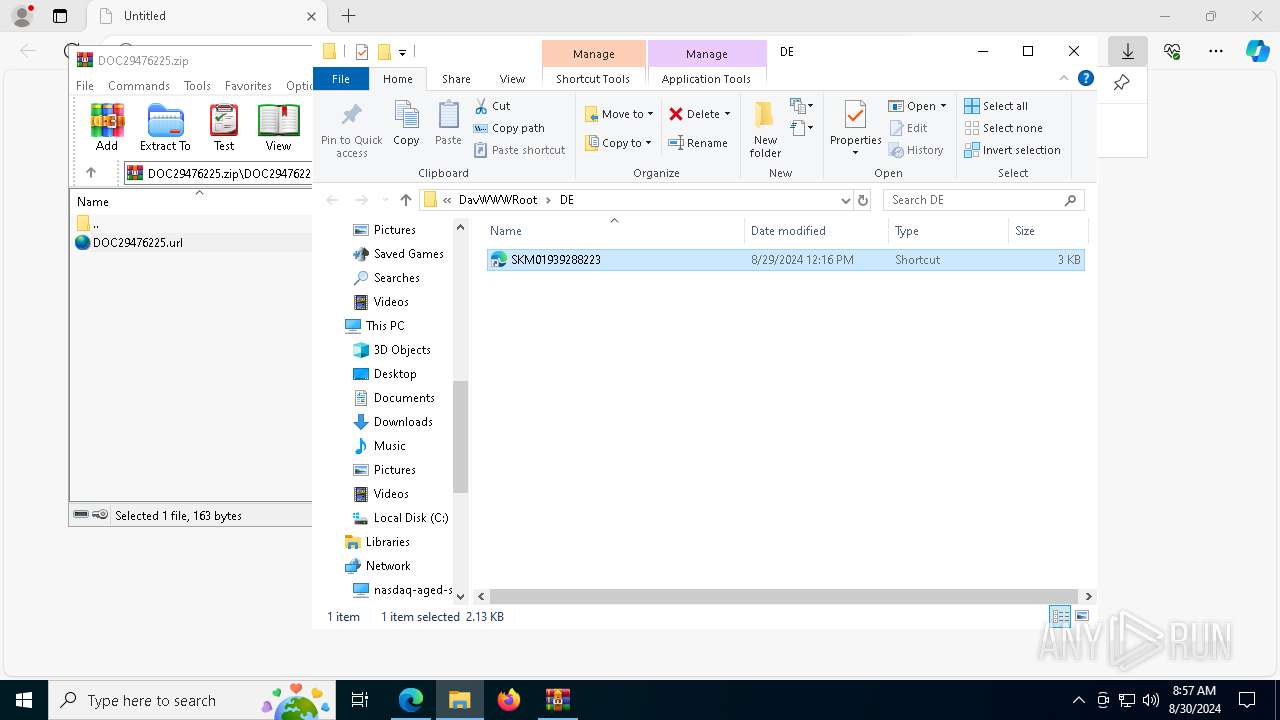
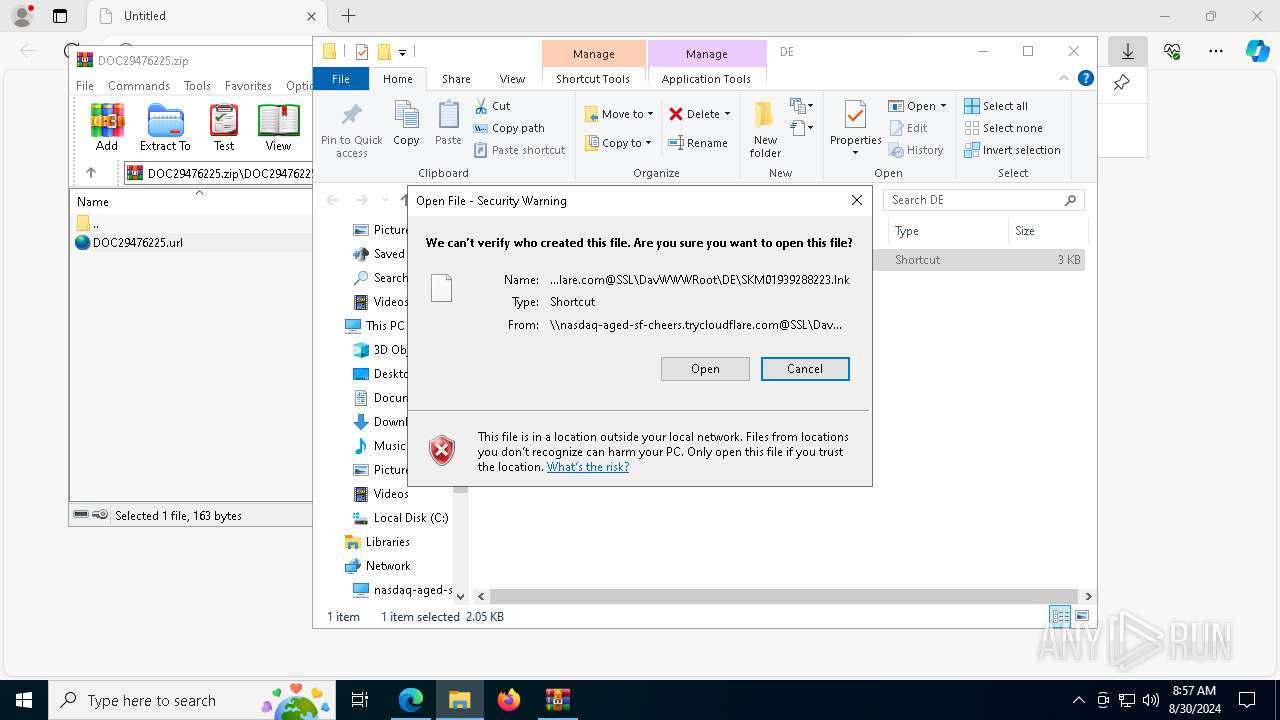
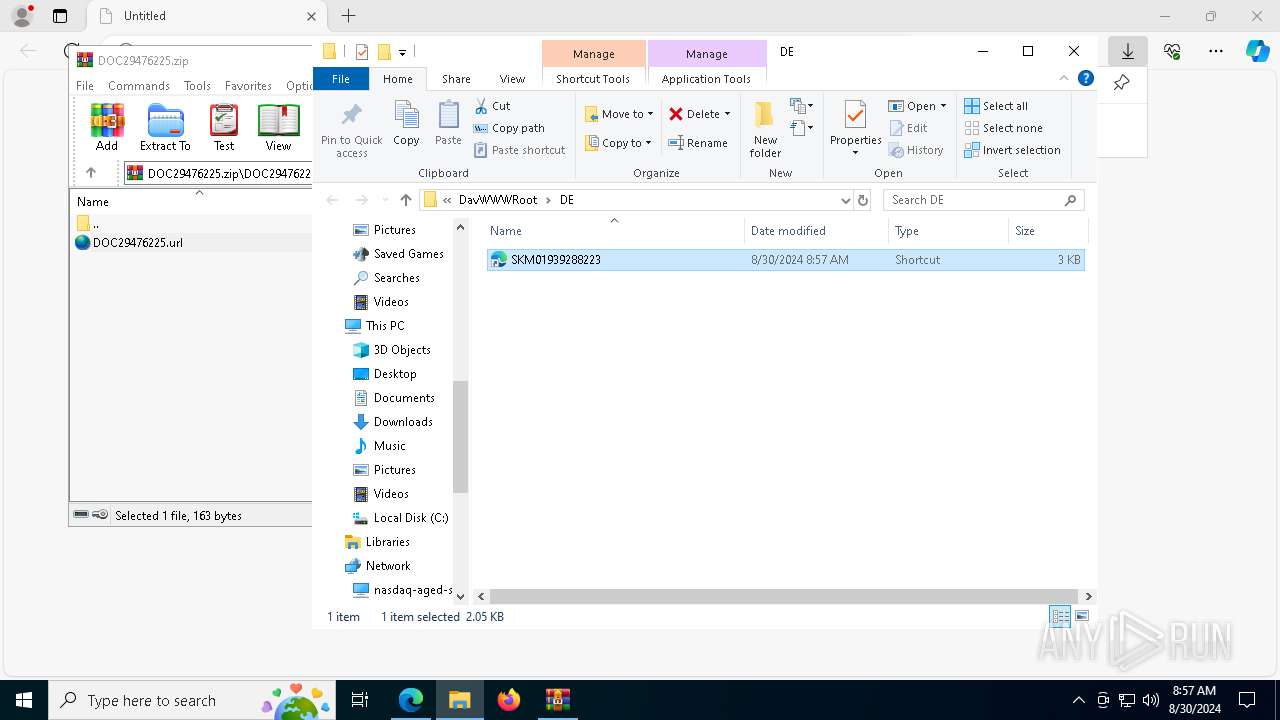
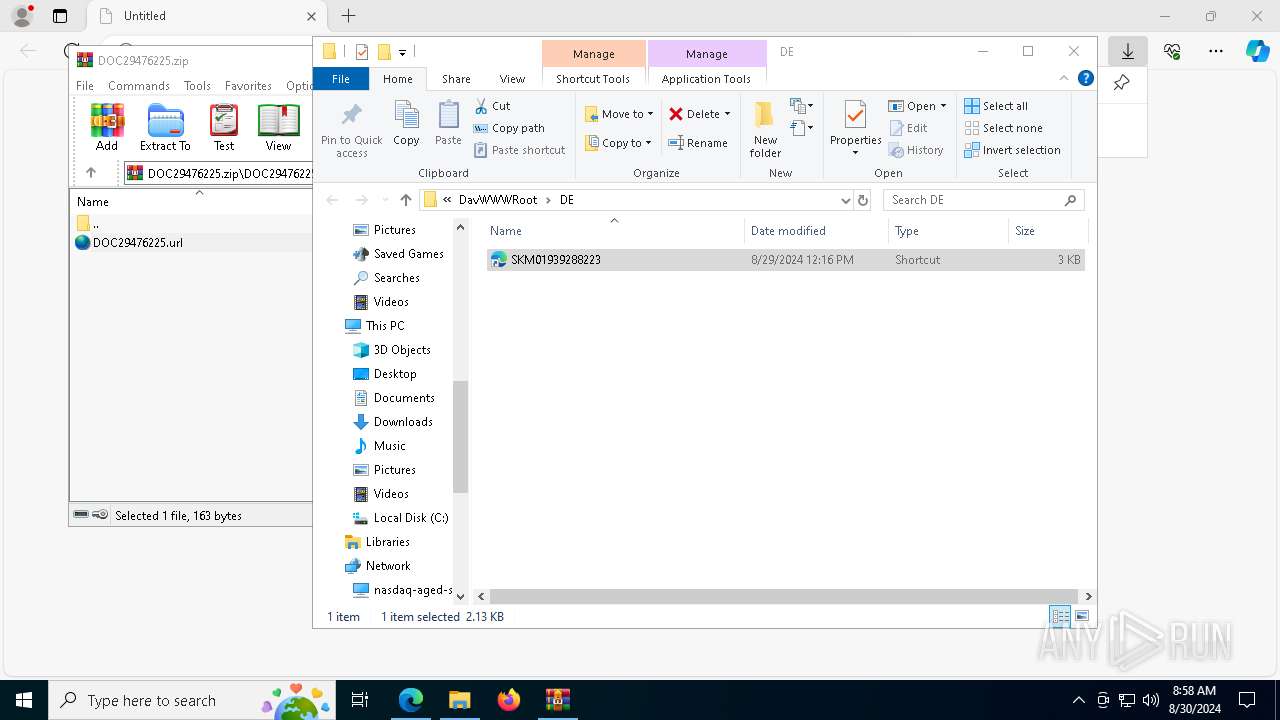
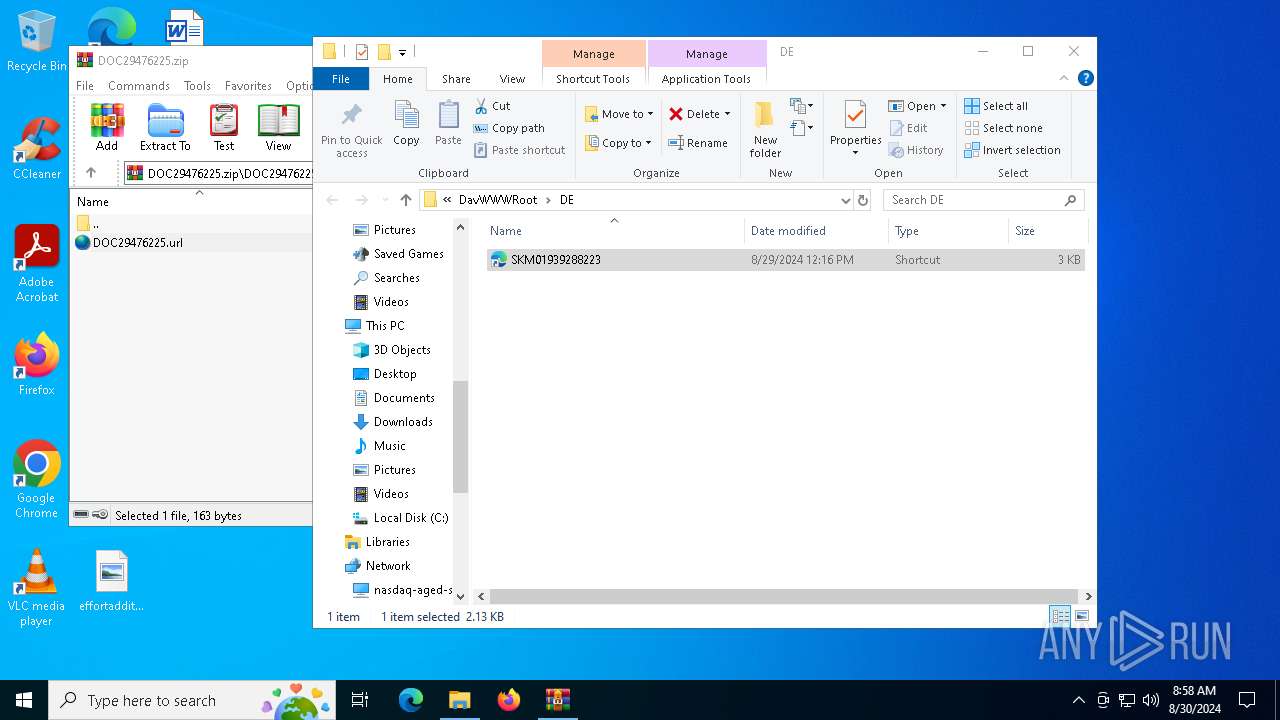
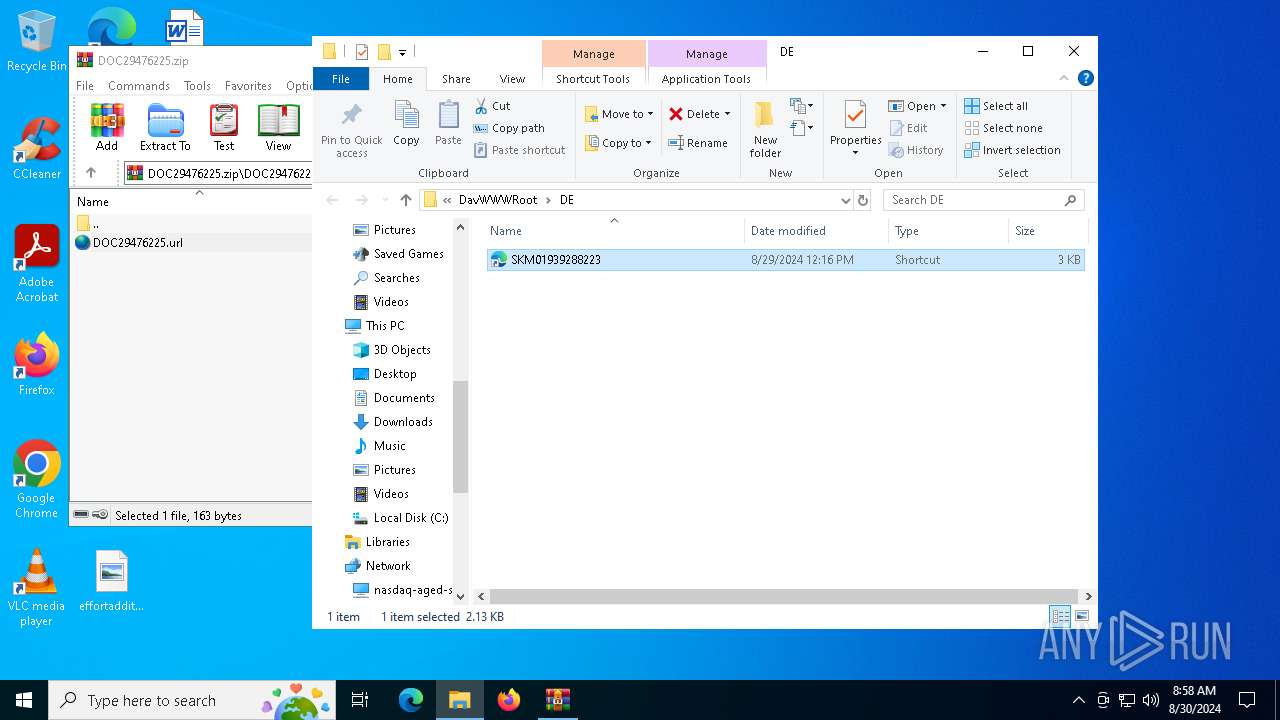
Abuses WebDav for code execution
- svchost.exe (PID: 2992)
Request a resource from the Internet using PowerShell's cmdlet
- cmd.exe (PID: 7236)
- cmd.exe (PID: 8120)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7236)
- cmd.exe (PID: 8120)
Starts CMD.EXE for commands execution
- conhost.exe (PID: 7212)
- conhost.exe (PID: 8100)
Downloads file from URI
- powershell.exe (PID: 7296)
- powershell.exe (PID: 8180)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 7296)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7296)
- powershell.exe (PID: 8180)
Drops the executable file immediately after the start
- powershell.exe (PID: 7296)
- python-3.12.5-amd64.exe (PID: 6984)
- python-3.12.5-amd64.exe (PID: 7040)
- msiexec.exe (PID: 7472)
- python-3.12.5-amd64.exe (PID: 6892)
- python-3.12.5-amd64.exe (PID: 2580)
Executable content was dropped or overwritten
- powershell.exe (PID: 7296)
- python-3.12.5-amd64.exe (PID: 6984)
- python-3.12.5-amd64.exe (PID: 7040)
- python-3.12.5-amd64.exe (PID: 2580)
- python-3.12.5-amd64.exe (PID: 6892)
The executable file from the user directory is run by the CMD process
- python-3.12.5-amd64.exe (PID: 6984)
- python-3.12.5-amd64.exe (PID: 6892)
Loads Python modules
- python-3.12.5-amd64.exe (PID: 7040)
- python-3.12.5-amd64.exe (PID: 2580)
The process drops C-runtime libraries
- python-3.12.5-amd64.exe (PID: 7040)
- msiexec.exe (PID: 7472)
Process drops legitimate windows executable
- python-3.12.5-amd64.exe (PID: 7040)
- msiexec.exe (PID: 7472)
Creates a software uninstall entry
- python-3.12.5-amd64.exe (PID: 7040)
- python-3.12.5-amd64.exe (PID: 2580)
Checks Windows Trust Settings
- msiexec.exe (PID: 7472)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7472)
Searches for installed software
- python-3.12.5-amd64.exe (PID: 2580)
- python-3.12.5-amd64.exe (PID: 7040)
Process drops python dynamic module
- msiexec.exe (PID: 7472)
INFO
The process uses the downloaded file
- iexplore.exe (PID: 2684)
- WinRAR.exe (PID: 6644)
- msedge.exe (PID: 2820)
- msedge.exe (PID: 6628)
Application launched itself
- msedge.exe (PID: 2820)
- msedge.exe (PID: 2608)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6644)
- msedge.exe (PID: 2820)
- msedge.exe (PID: 2608)
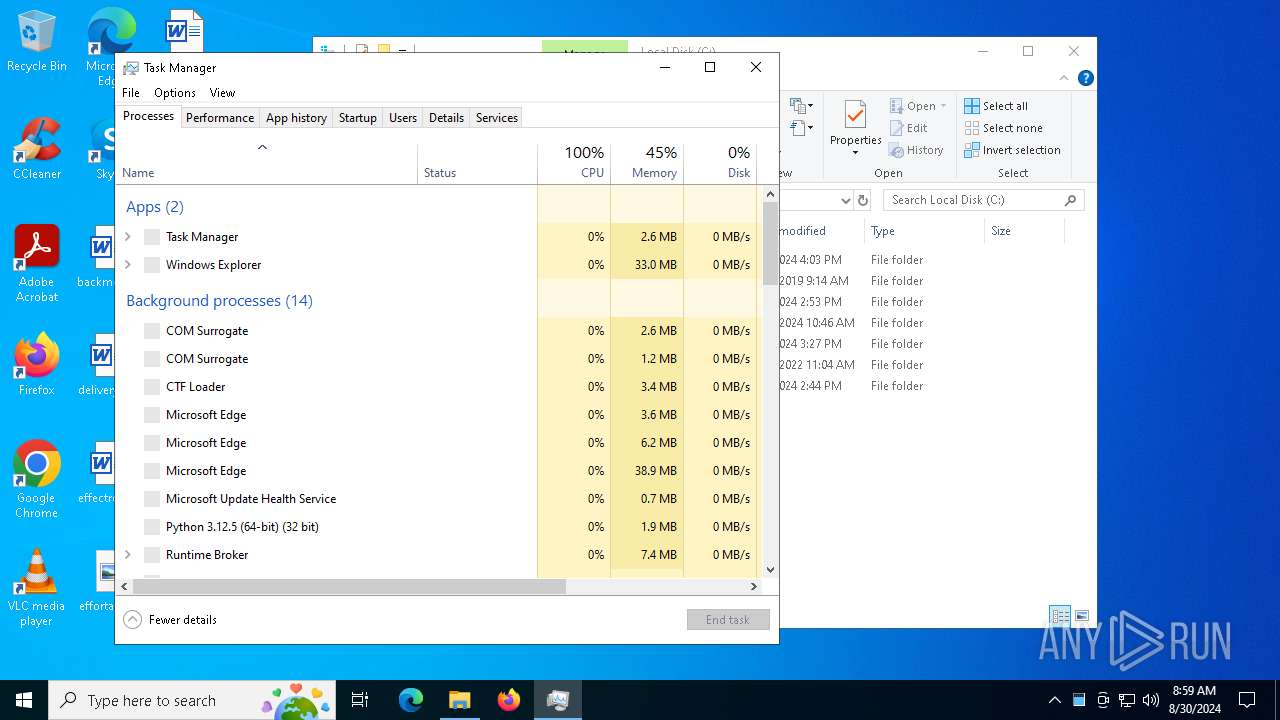
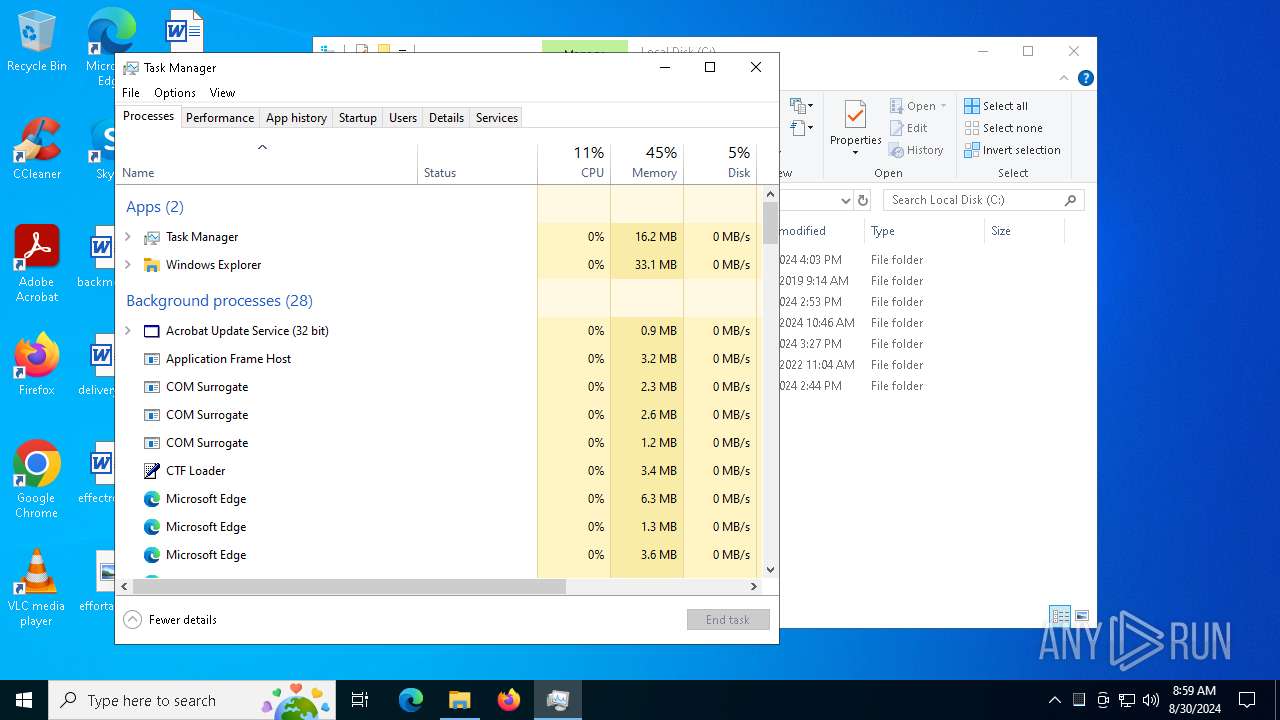
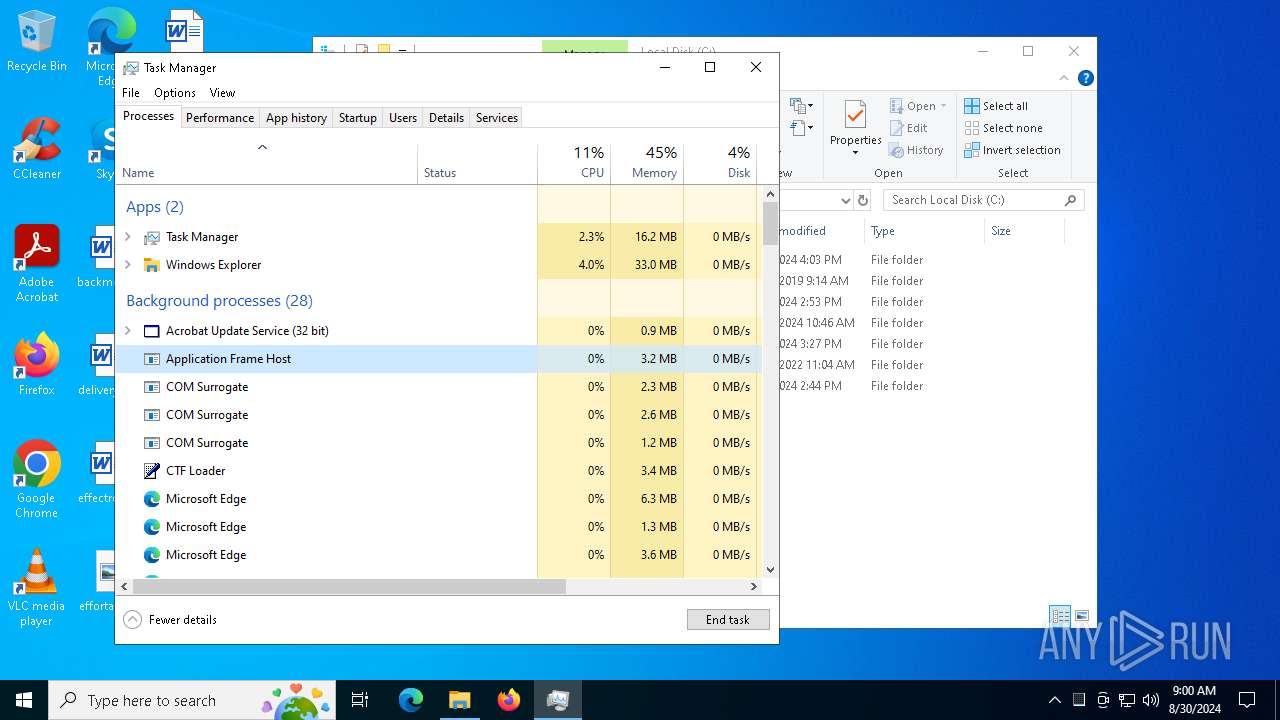
Manual execution by a user
- conhost.exe (PID: 7212)
- conhost.exe (PID: 8100)
- Taskmgr.exe (PID: 1104)
- Taskmgr.exe (PID: 780)
Checks proxy server information
- WinRAR.exe (PID: 6644)
- conhost.exe (PID: 7212)
- conhost.exe (PID: 8100)
- powershell.exe (PID: 7296)
- powershell.exe (PID: 8180)
Reads the software policy settings
- WinRAR.exe (PID: 6644)
- msiexec.exe (PID: 7472)
Reads security settings of Internet Explorer
- conhost.exe (PID: 7212)
- conhost.exe (PID: 8100)
- Taskmgr.exe (PID: 780)
Checks supported languages
- identity_helper.exe (PID: 7020)
- python-3.12.5-amd64.exe (PID: 6984)
- python-3.12.5-amd64.exe (PID: 7040)
- msiexec.exe (PID: 7472)
- python-3.12.5-amd64.exe (PID: 6892)
- python-3.12.5-amd64.exe (PID: 2580)
- identity_helper.exe (PID: 6708)
Disables trace logs
- powershell.exe (PID: 7296)
- powershell.exe (PID: 8180)
Reads the computer name
- identity_helper.exe (PID: 7020)
- python-3.12.5-amd64.exe (PID: 7040)
- msiexec.exe (PID: 7472)
- python-3.12.5-amd64.exe (PID: 2580)
- identity_helper.exe (PID: 6708)
Reads Environment values
- identity_helper.exe (PID: 7020)
- identity_helper.exe (PID: 6708)
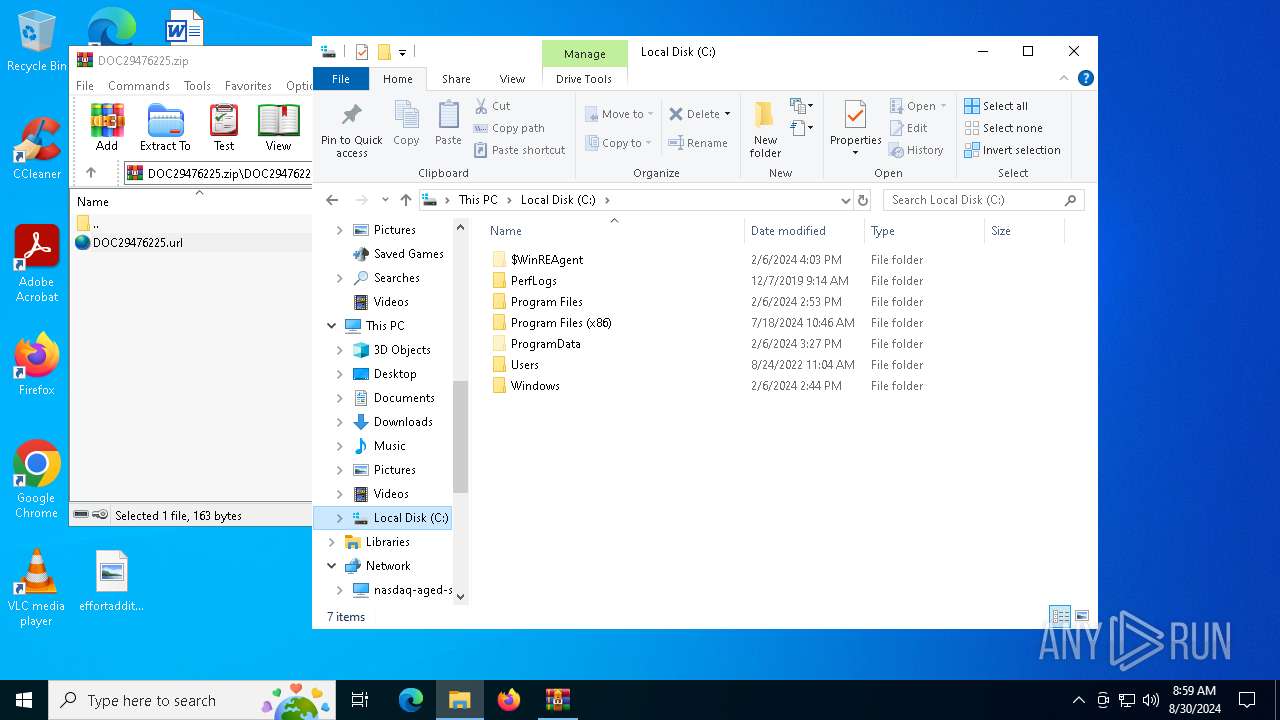
Create files in a temporary directory
- python-3.12.5-amd64.exe (PID: 6984)
- python-3.12.5-amd64.exe (PID: 7040)
- python-3.12.5-amd64.exe (PID: 6892)
- python-3.12.5-amd64.exe (PID: 2580)
Creates files or folders in the user directory
- python-3.12.5-amd64.exe (PID: 7040)
- msiexec.exe (PID: 7472)
Reads the machine GUID from the registry
- python-3.12.5-amd64.exe (PID: 7040)
- msiexec.exe (PID: 7472)
- python-3.12.5-amd64.exe (PID: 2580)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8180)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7472)
Creates a software uninstall entry
- msiexec.exe (PID: 7472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
215
Monitored processes
78
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6876 --field-trial-handle=2400,i,4201786922881000182,7843918326039361617,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5536 --field-trial-handle=2284,i,15599916275029125219,3769700768029372762,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1104 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4192 --field-trial-handle=2284,i,15599916275029125219,3769700768029372762,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6064 --field-trial-handle=2400,i,4201786922881000182,7843918326039361617,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2040 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2264 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x200,0x1d8,0x1f8,0x180,0x2b4,0x7fffd27a5fd8,0x7fffd27a5fe4,0x7fffd27a5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2468 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=5612 --field-trial-handle=2400,i,4201786922881000182,7843918326039361617,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
77 512
Read events
73 364
Write events
4 040
Delete events
108
Modification events
| (PID) Process: | (2684) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (2684) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (2684) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (2684) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (2684) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2684) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31128250 | |||
| (PID) Process: | (2684) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2684) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2684) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2684) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
82
Suspicious files
507
Text files
2 838
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2820 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF12a11a.TMP | — | |
MD5:— | SHA256:— | |||
| 2820 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2820 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF12a11a.TMP | — | |
MD5:— | SHA256:— | |||
| 2820 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF12a11a.TMP | — | |
MD5:— | SHA256:— | |||
| 2820 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2820 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2820 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF12a168.TMP | — | |
MD5:— | SHA256:— | |||
| 2820 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2820 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF12a188.TMP | — | |
MD5:— | SHA256:— | |||
| 2820 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
76
DNS requests
63
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5612 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7652 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1725571405&P2=404&P3=2&P4=GiMw%2f0N%2bEpATNkorU6DsmoEg%2bg8%2bHr9CcysozlwvRoBniKdM%2brxp85%2bs84xA01QjCRIVMGfVssWd3ypZHdaaUw%3d%3d | unknown | — | — | whitelisted |
7652 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1725571405&P2=404&P3=2&P4=GiMw%2f0N%2bEpATNkorU6DsmoEg%2bg8%2bHr9CcysozlwvRoBniKdM%2brxp85%2bs84xA01QjCRIVMGfVssWd3ypZHdaaUw%3d%3d | unknown | — | — | whitelisted |
5612 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7472 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7652 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1725571405&P2=404&P3=2&P4=GiMw%2f0N%2bEpATNkorU6DsmoEg%2bg8%2bHr9CcysozlwvRoBniKdM%2brxp85%2bs84xA01QjCRIVMGfVssWd3ypZHdaaUw%3d%3d | unknown | — | — | whitelisted |
7472 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAcfFBuLMA0l8xTrIwzQ0d0%3D | unknown | — | — | whitelisted |
7652 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1725571405&P2=404&P3=2&P4=GiMw%2f0N%2bEpATNkorU6DsmoEg%2bg8%2bHr9CcysozlwvRoBniKdM%2brxp85%2bs84xA01QjCRIVMGfVssWd3ypZHdaaUw%3d%3d | unknown | — | — | whitelisted |
7472 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
7652 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ec3f42ff-db07-4960-b560-3fa136bcb5d5?P1=1725609775&P2=404&P3=2&P4=BPQ%2fzBVddhRtgbynIEiO%2b47wOaeI3nGhnZJaPPWsospUHwFTkUzHqwDVsj6spoqBq%2b6HBqOIc9SxOnfukW3Xpg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7128 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6168 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2820 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6168 | msedge.exe | 162.125.66.15:443 | dl.dropboxusercontent.com | DROPBOX | DE | shared |
6168 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6168 | msedge.exe | 13.107.246.42:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6168 | msedge.exe | 94.245.104.56:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
dl.dropboxusercontent.com |
| shared |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6168 | msedge.exe | Misc activity | ET INFO DropBox User Content Domain (dl .dropboxusercontent .com in TLS SNI) |
2256 | svchost.exe | Potentially Bad Traffic | ET POLICY Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
2256 | svchost.exe | Potentially Bad Traffic | ET POLICY Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |