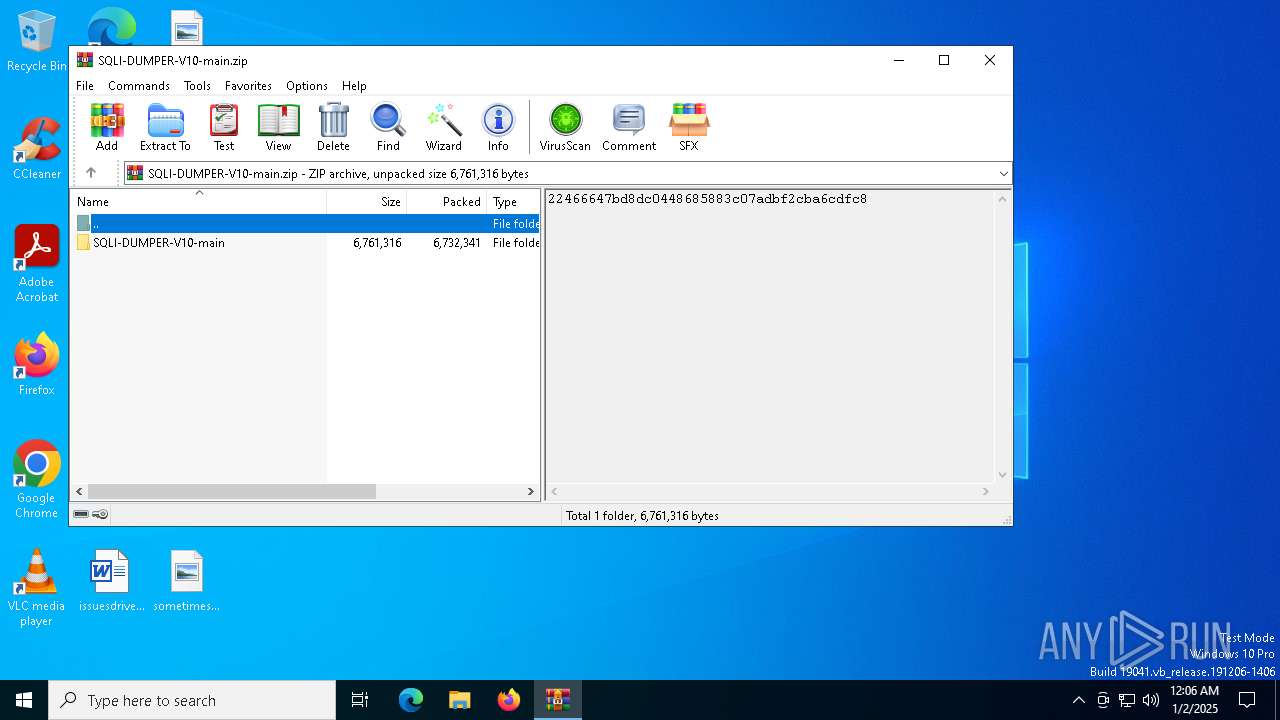
| File name: | SQLI-DUMPER-V10-main.zip |
| Full analysis: | https://app.any.run/tasks/490839ec-c560-4694-a5c6-e451bfd65f35 |
| Verdict: | Malicious activity |
| Analysis date: | January 02, 2025, 00:06:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 3A3C5A04059C5121D2A567536D3FE358 |
| SHA1: | 11058B9C56F7C472D7C2F79577C21239E24C2DB1 |
| SHA256: | E474F5C019570CB28BDDD13CB642C7A0A86E935976527D274994FB671F865755 |
| SSDEEP: | 98304:/aOVnFZiJG0i3kK5zpZrrw5yCbL4QE9iRxu9pIj9oPv8YAvYKK+0lnBF+5Bk1Lsk:/TlSjdYqlL4mIzLzp |
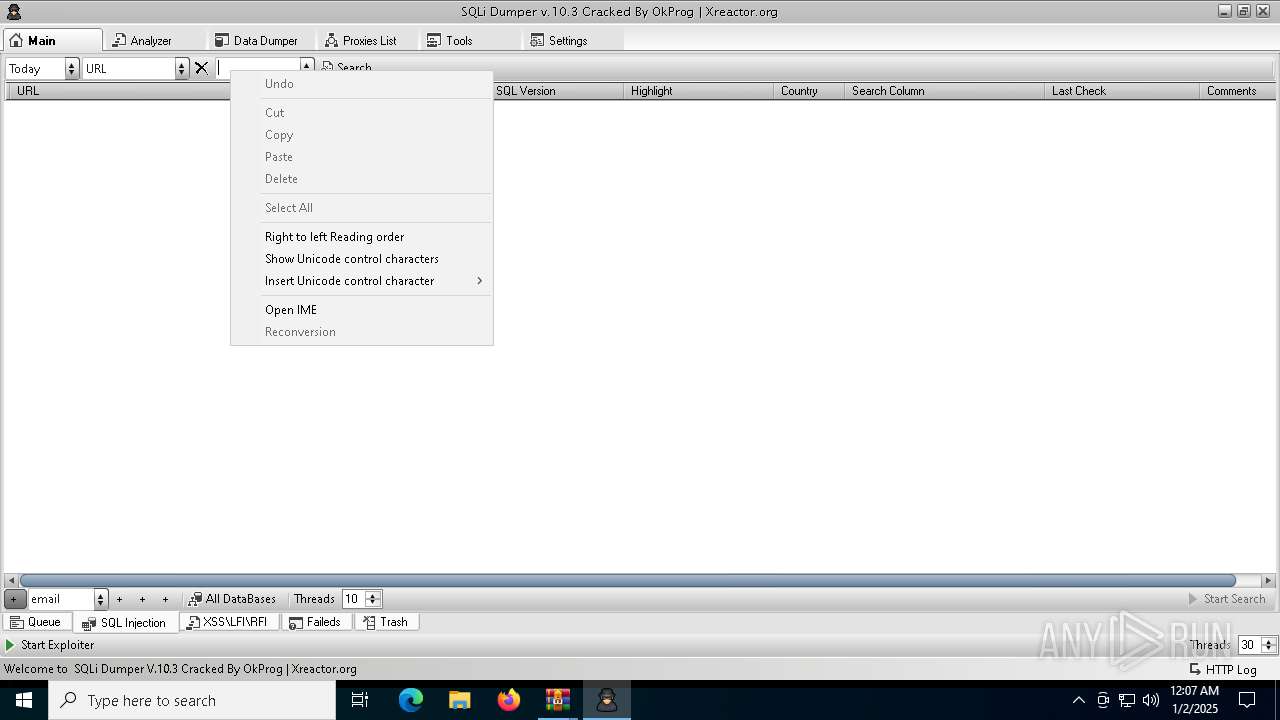
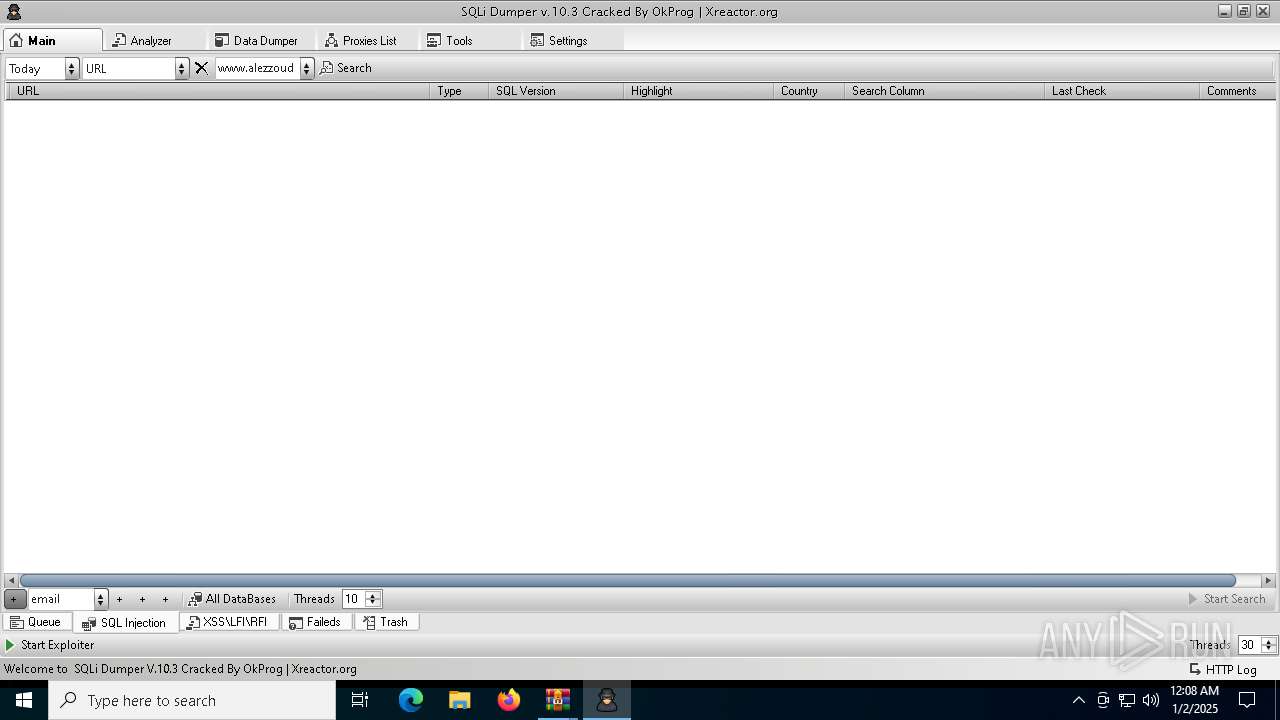
MALICIOUS
No malicious indicators.SUSPICIOUS
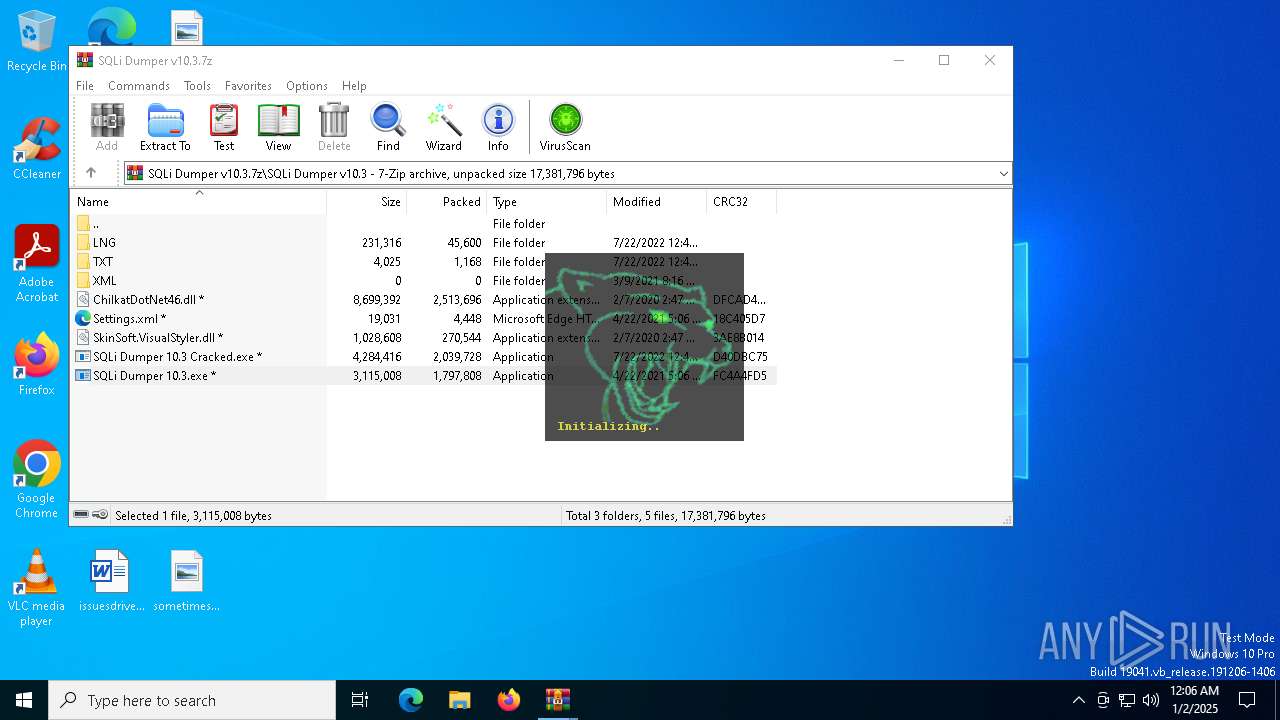
Application launched itself
- WinRAR.exe (PID: 6504)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6504)
- WinRAR.exe (PID: 6220)
- SQLi Dumper 10.3.exe (PID: 6320)
Executable content was dropped or overwritten
- SQLi Dumper 10.3.exe (PID: 6320)
Checks for external IP
- svchost.exe (PID: 2192)
- SQLi Dumper 10.3.exe (PID: 6320)
There is functionality for taking screenshot (YARA)
- SQLi Dumper 10.3.exe (PID: 6320)
Reads Internet Explorer settings
- SQLi Dumper 10.3.exe (PID: 6320)
Reads Microsoft Outlook installation path
- SQLi Dumper 10.3.exe (PID: 6320)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 6220)
- WinRAR.exe (PID: 6504)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6220)
The sample compiled with english language support
- WinRAR.exe (PID: 6220)
- SQLi Dumper 10.3.exe (PID: 6320)
Checks supported languages
- SQLi Dumper 10.3.exe (PID: 6320)
Reads the computer name
- SQLi Dumper 10.3.exe (PID: 6320)
Reads the machine GUID from the registry
- SQLi Dumper 10.3.exe (PID: 6320)
Creates files or folders in the user directory
- SQLi Dumper 10.3.exe (PID: 6320)
Disables trace logs
- SQLi Dumper 10.3.exe (PID: 6320)
Reads Environment values
- SQLi Dumper 10.3.exe (PID: 6320)
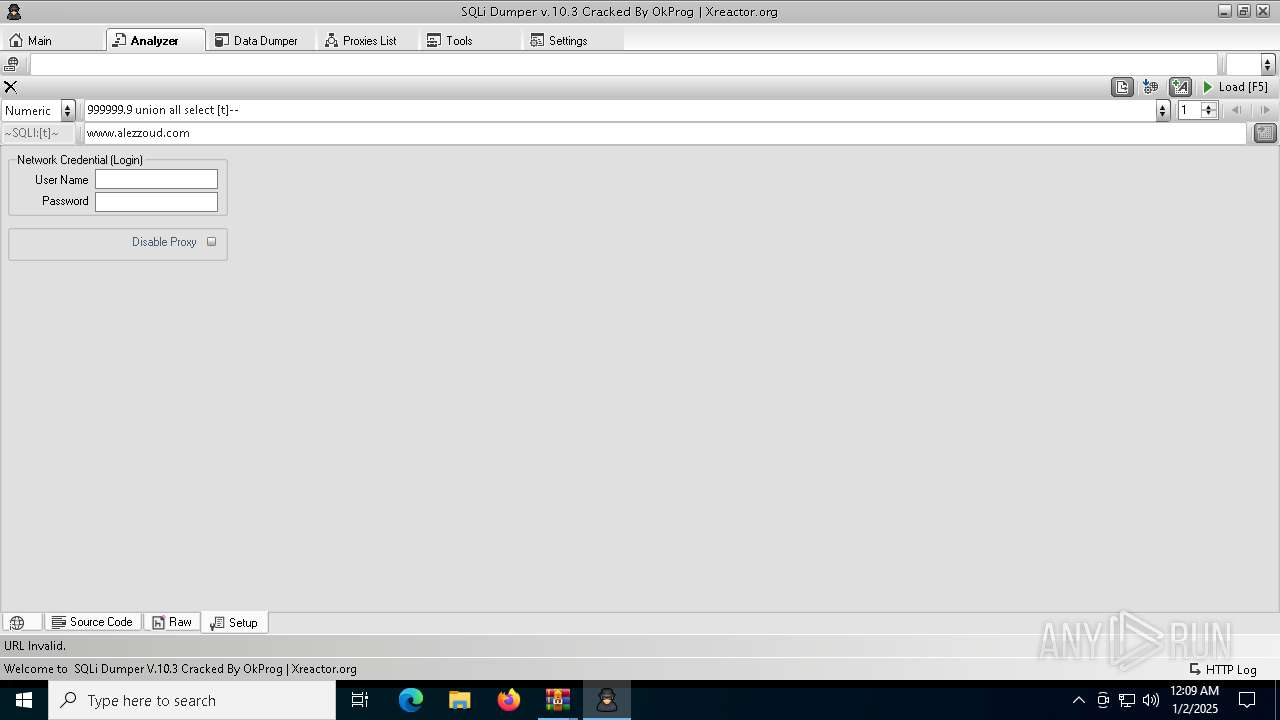
Checks proxy server information
- SQLi Dumper 10.3.exe (PID: 6320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2022:11:30 09:28:40 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | SQLI-DUMPER-V10-main/ |
Total processes
130
Monitored processes
4
Malicious processes
3
Suspicious processes
1
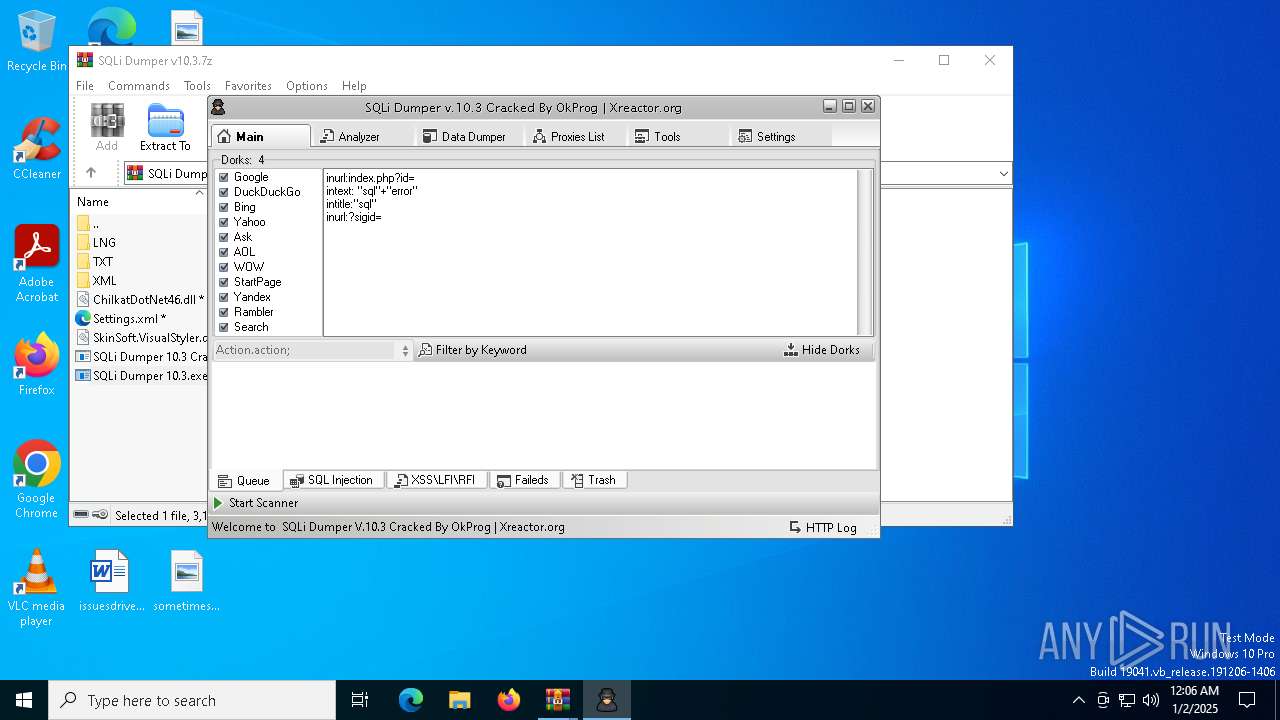
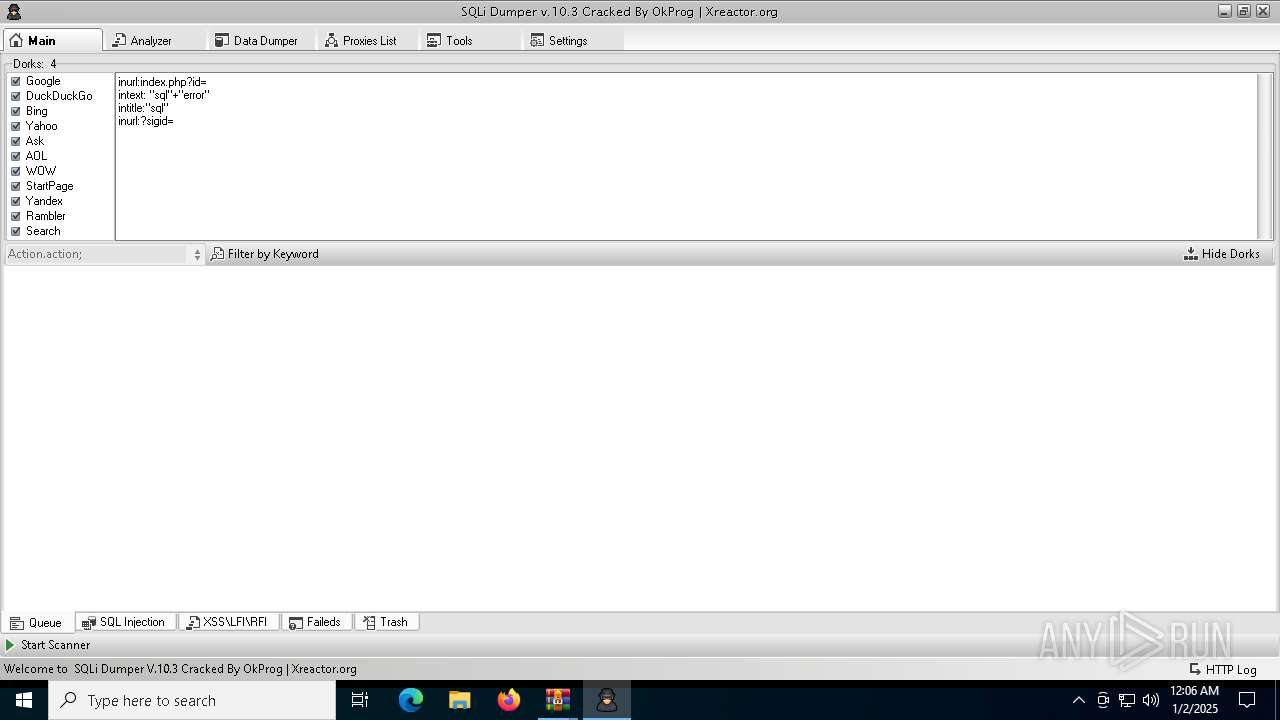
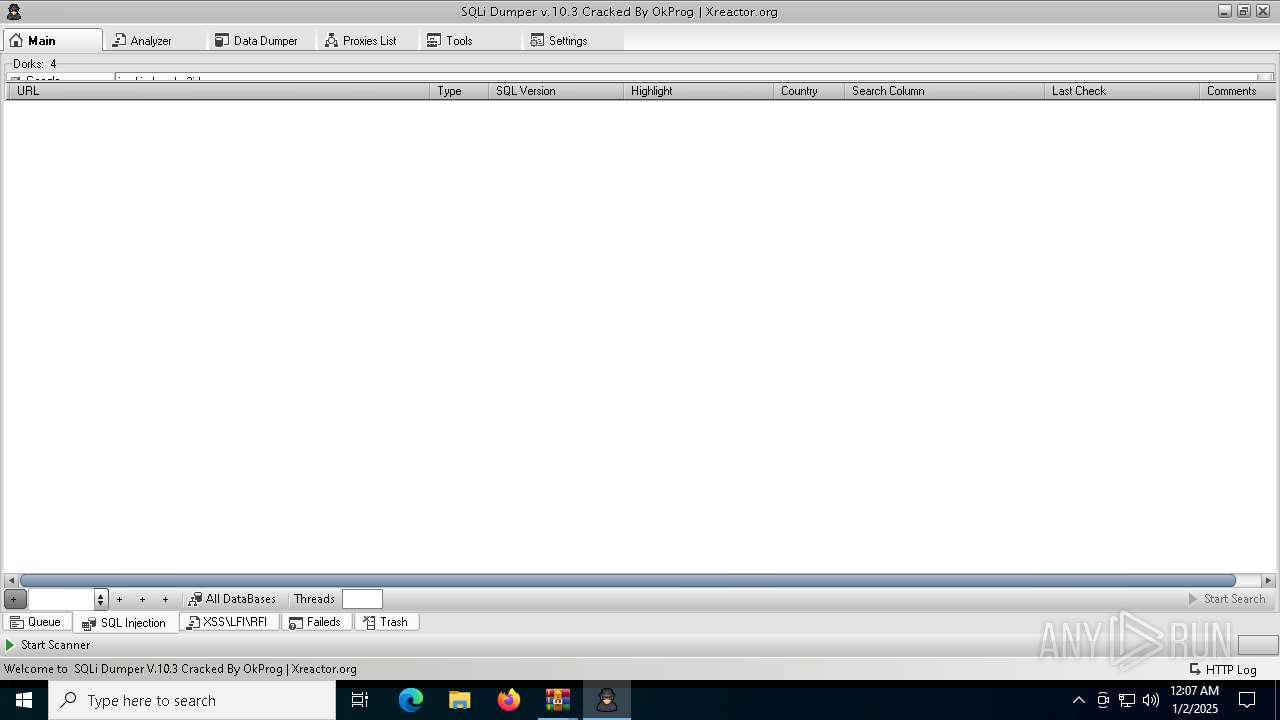
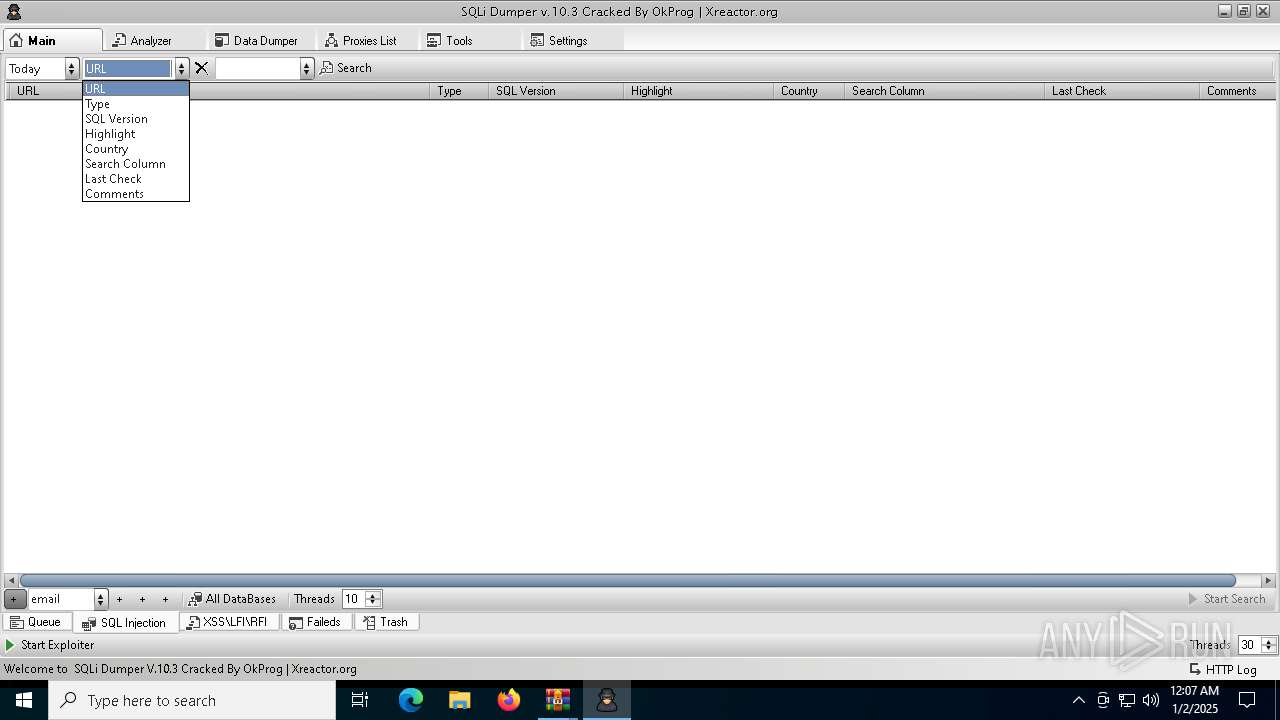
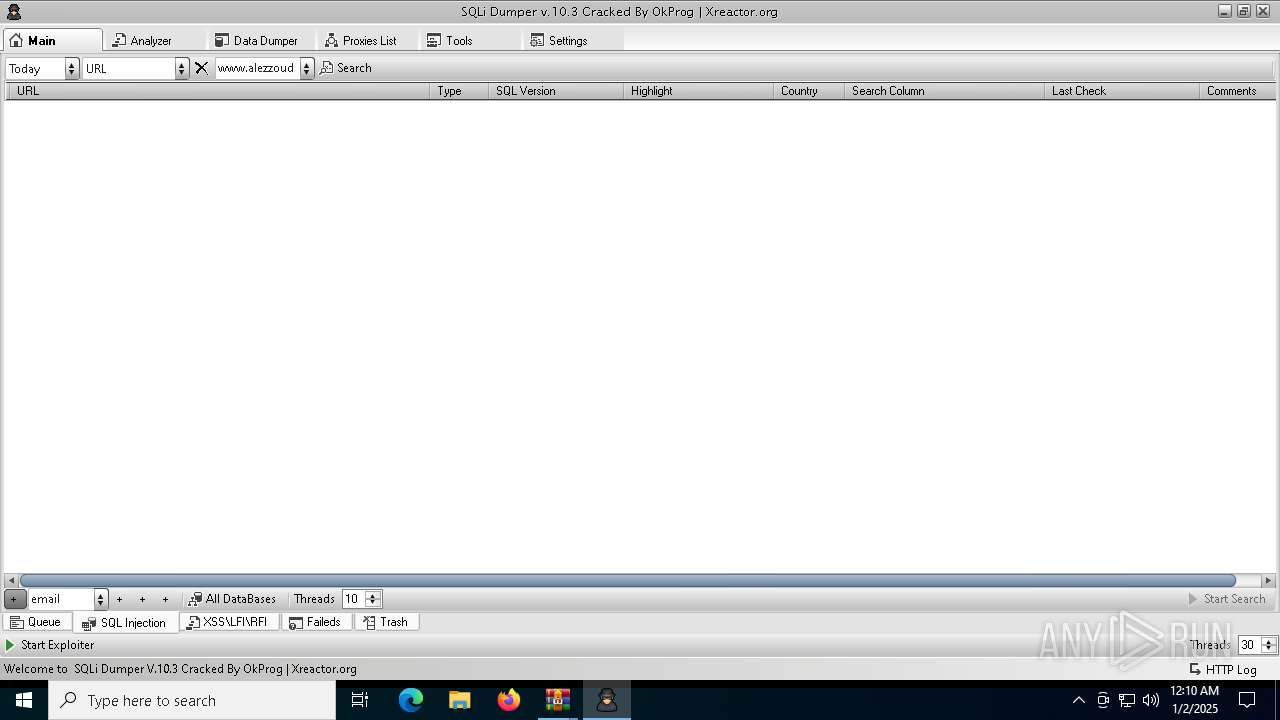
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
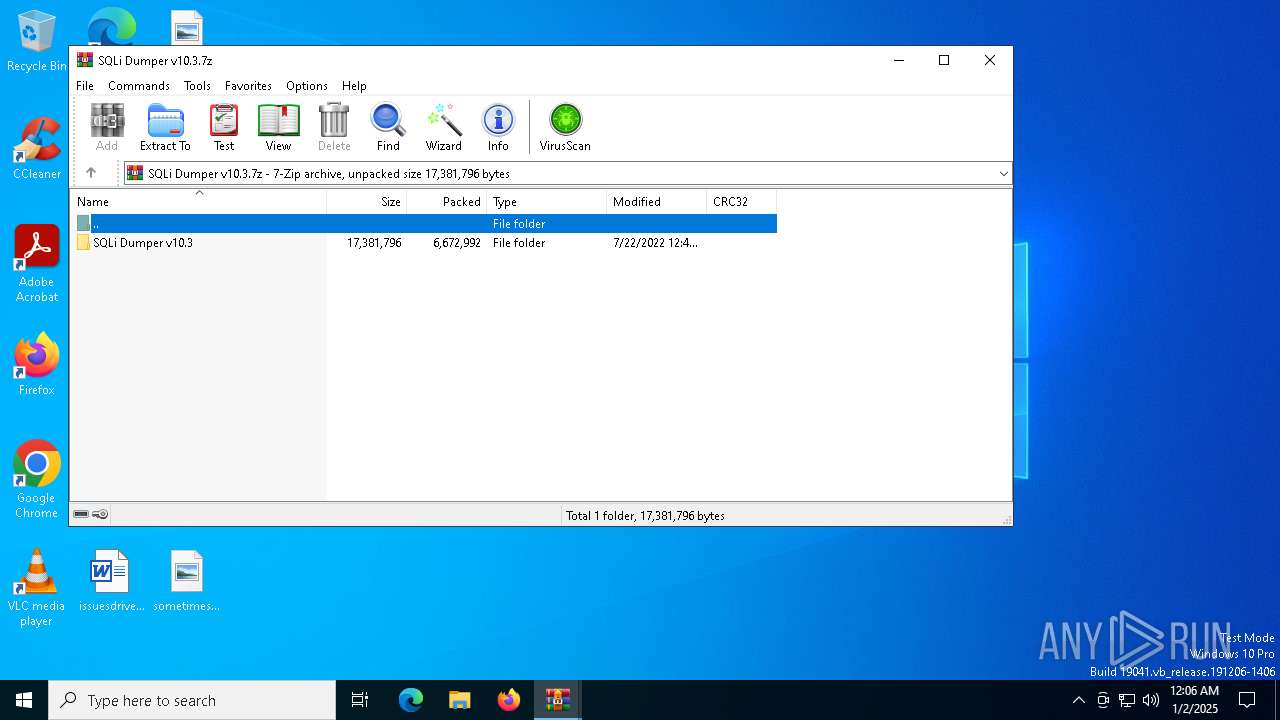
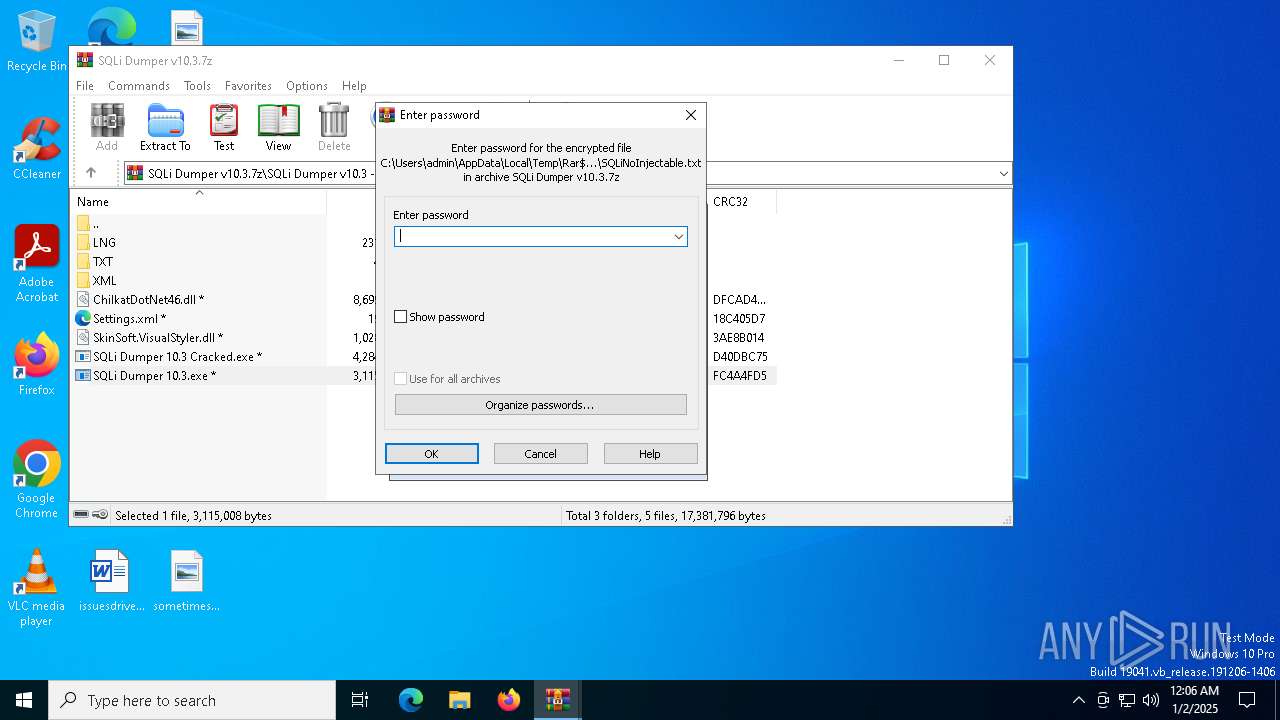
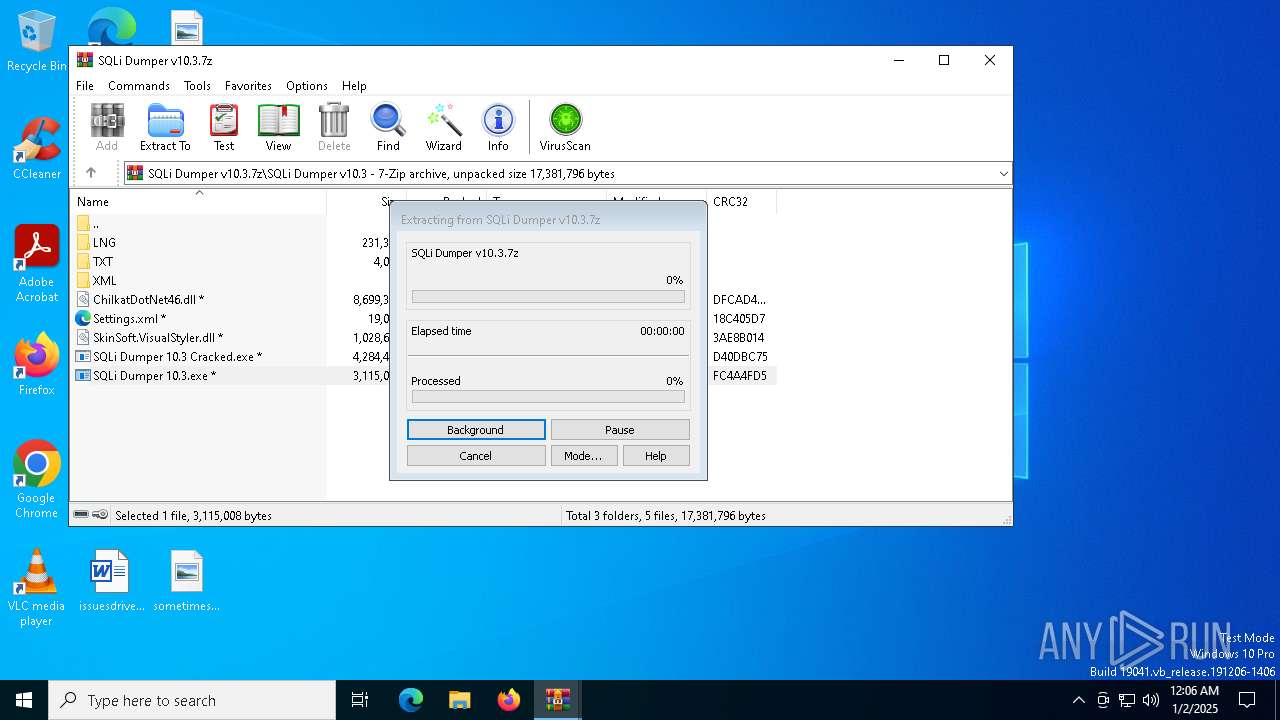
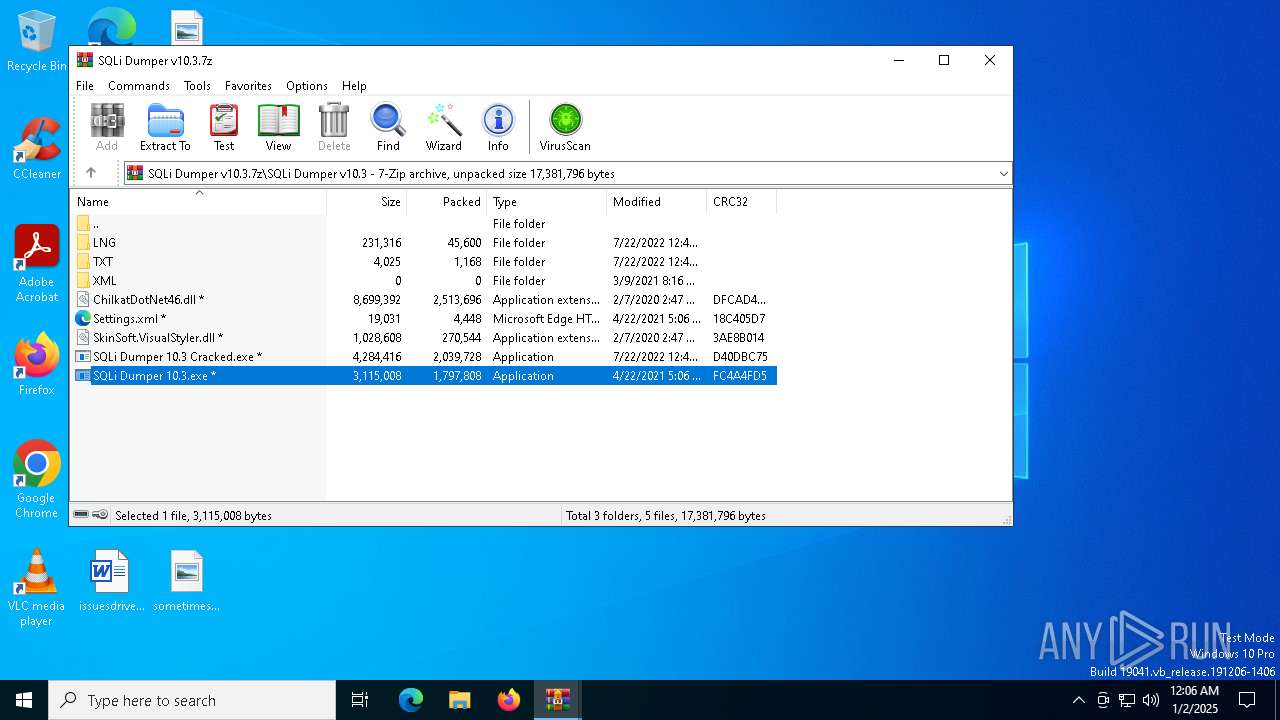
| 6220 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa6504.20200\SQLi Dumper v10.3.7z" | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
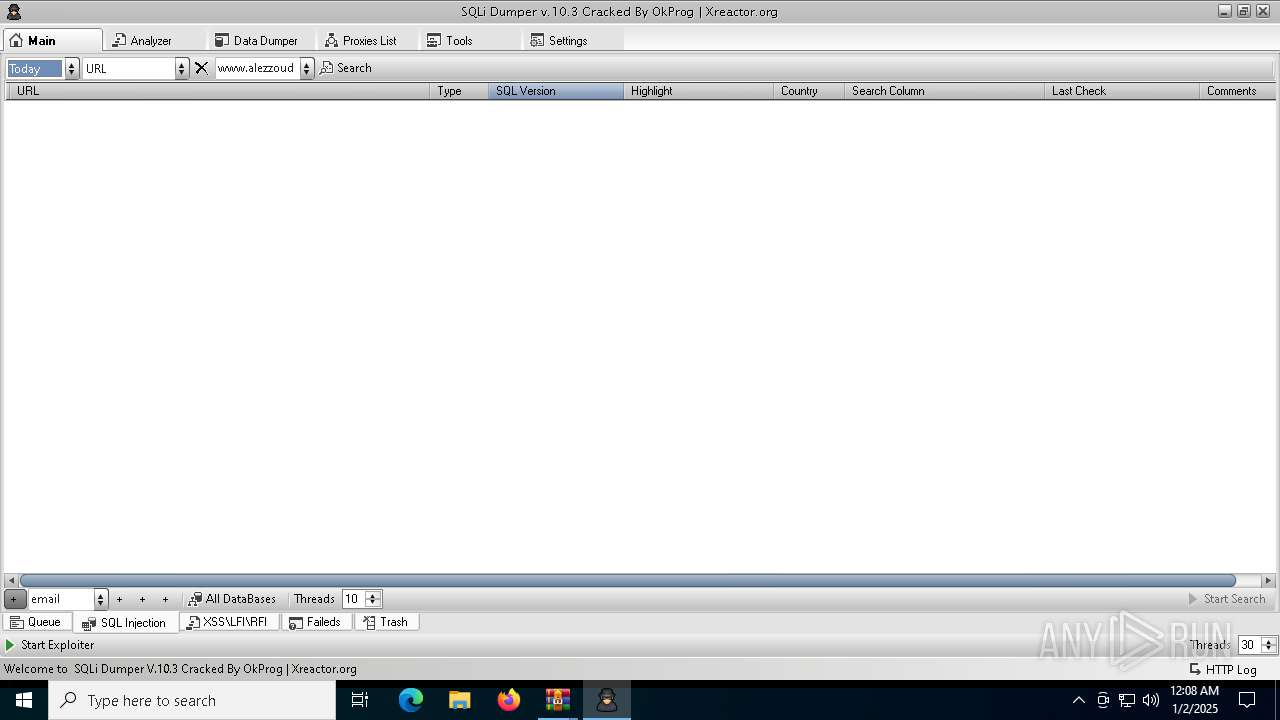
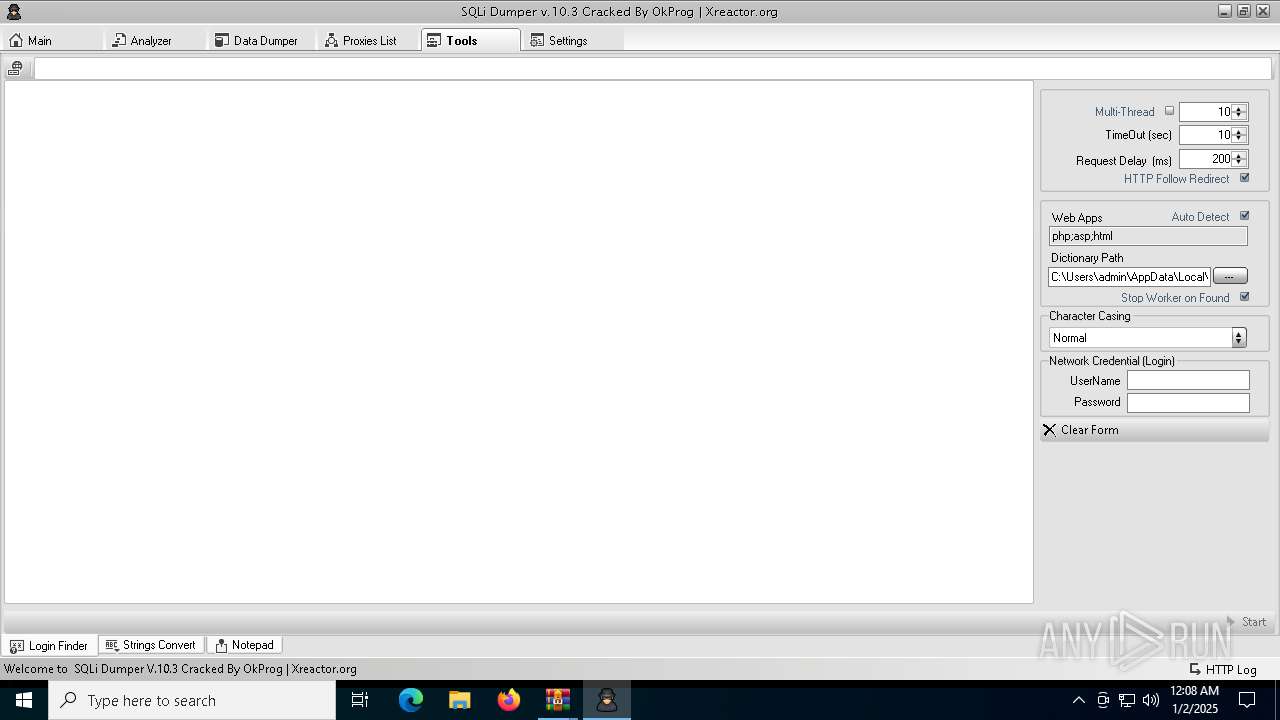
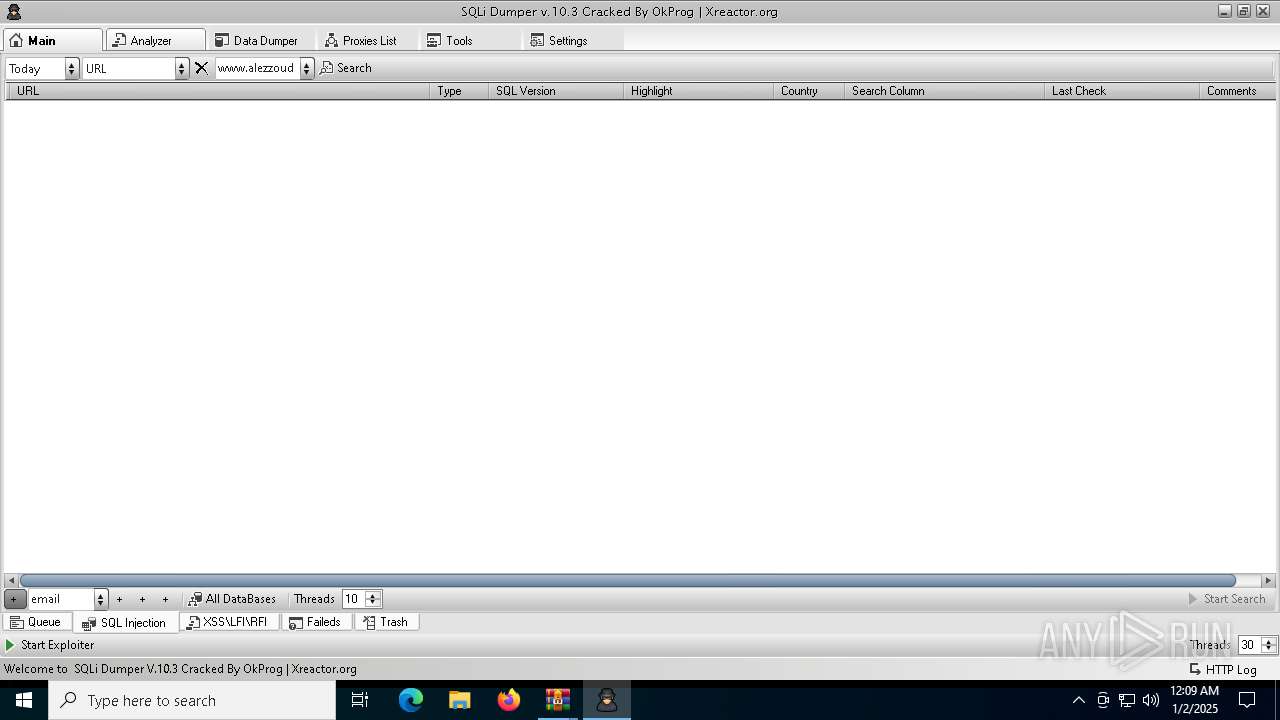
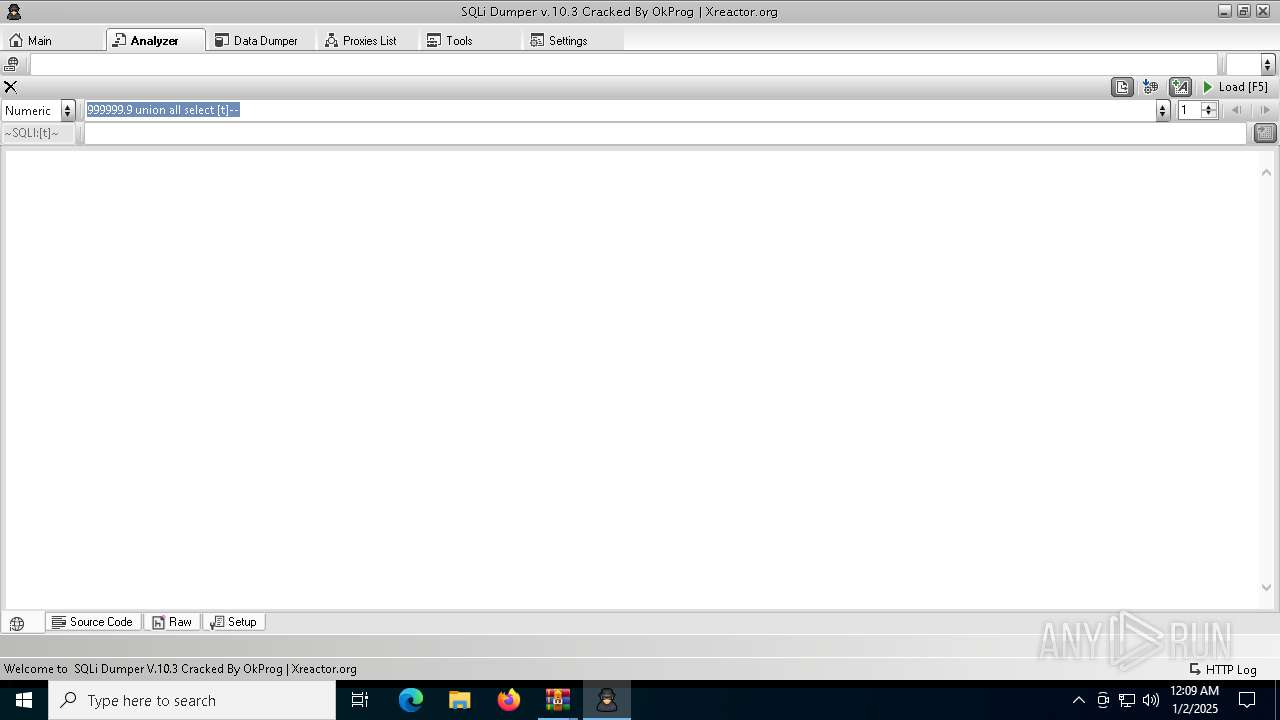
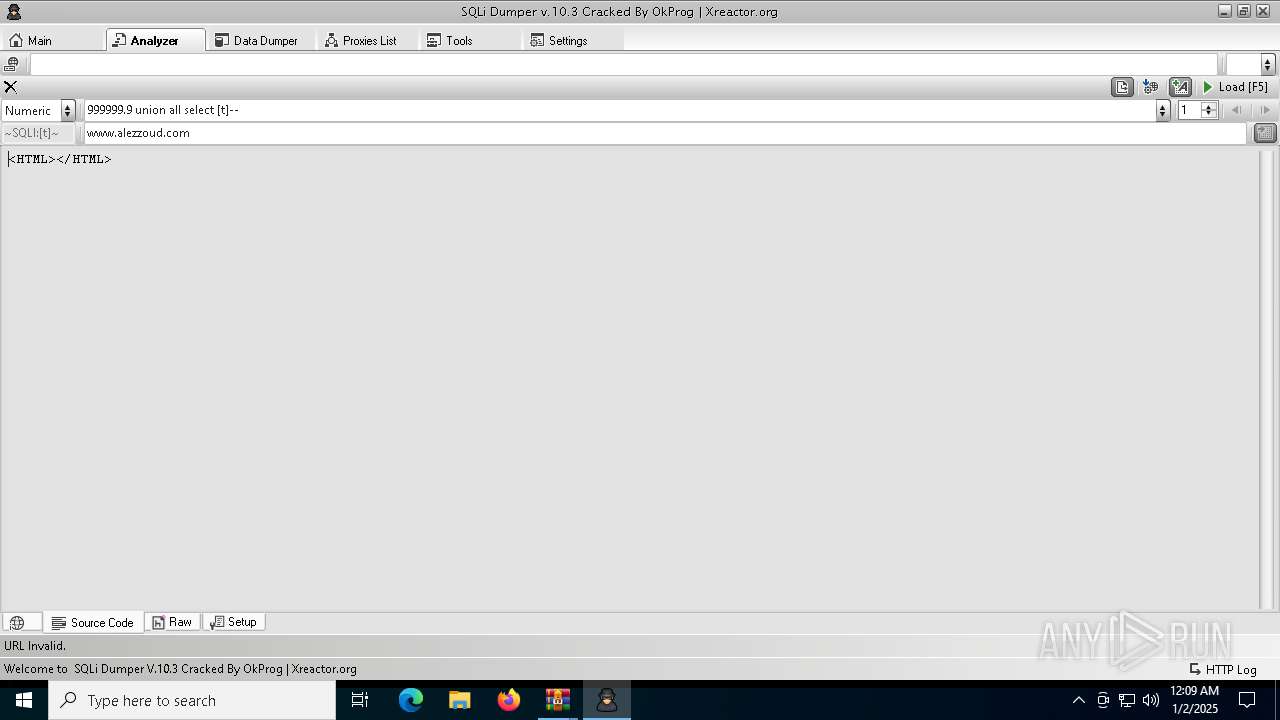
| 6320 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb6220.20865\SQLi Dumper v10.3\SQLi Dumper 10.3.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb6220.20865\SQLi Dumper v10.3\SQLi Dumper 10.3.exe | WinRAR.exe | ||||||||||||
User: admin Company: fLaSh Integrity Level: MEDIUM Description: SQLi Dumper Version: 10.1.0.0 Modules
| |||||||||||||||
| 6504 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\SQLI-DUMPER-V10-main.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
6 109
Read events
6 075
Write events
34
Delete events
0
Modification events
| (PID) Process: | (6504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SQLI-DUMPER-V10-main.zip | |||
| (PID) Process: | (6504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6504) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6220) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
5
Suspicious files
0
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
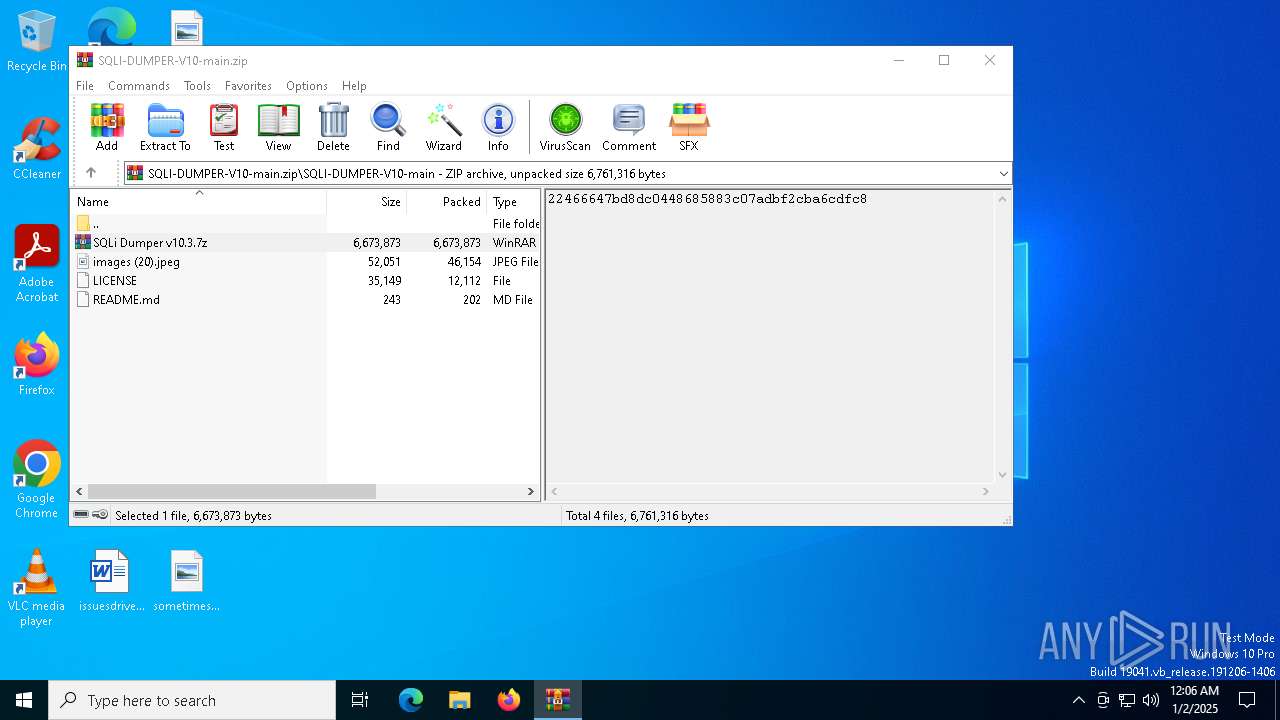
| 6504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa6504.20200\SQLi Dumper v10.3.7z | — | |
MD5:— | SHA256:— | |||
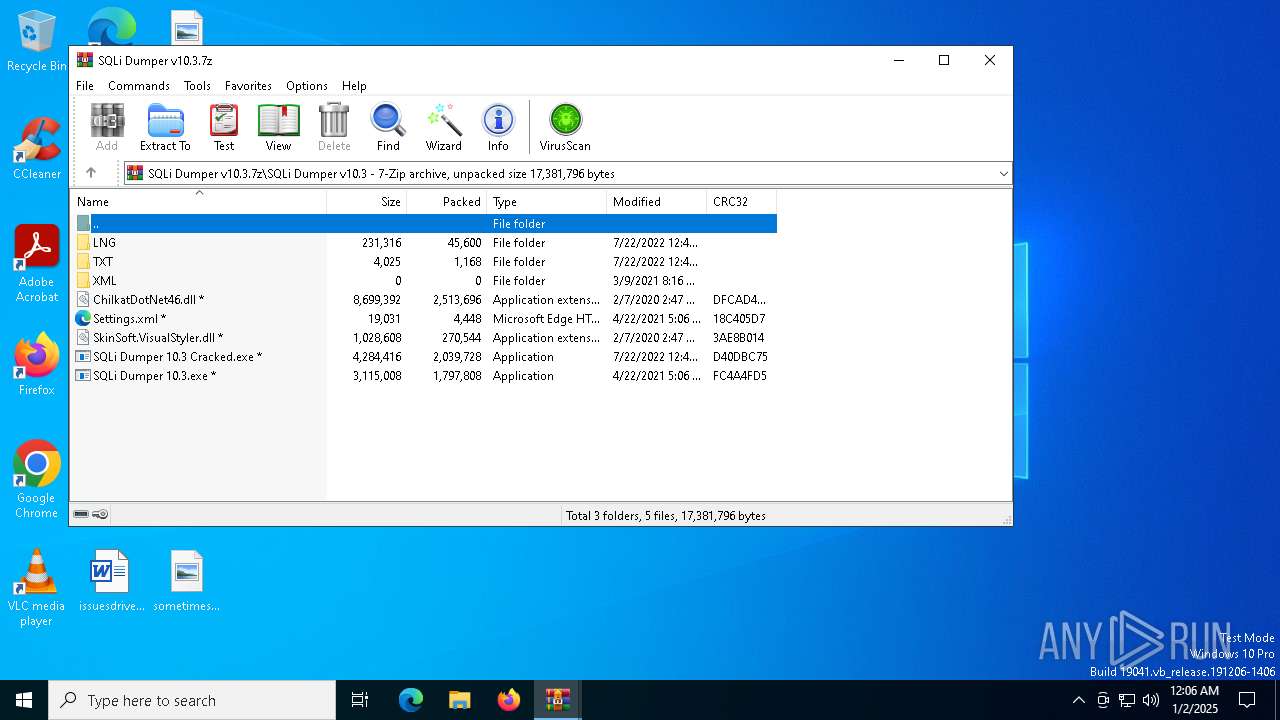
| 6220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6220.20865\SQLi Dumper v10.3\ChilkatDotNet46.dll | executable | |
MD5:C347B978DB64C5B0922FDB620A30A757 | SHA256:FA3A167968BE8ADFD68B88BF303EFC8F71E895366BF9297679988549534A8895 | |||
| 6220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6220.20865\SQLi Dumper v10.3\LNG\English.xml | xml | |
MD5:E932EA4DD931CD9039EC0CEA098DDF85 | SHA256:E4284B97BE769C04F1E49DD649F7116D364D72EAC74443A7CD2C46C13220D06B | |||
| 6220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6220.20865\SQLi Dumper v10.3\SQLi Dumper 10.3.exe | executable | |
MD5:2125D9A2D353E1336709BC5407E551B7 | SHA256:3632023198C152DBBEAFD1AB70E4AF83E036AA64847EEBC98BDAE2CB70E9D88E | |||
| 6220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6220.20865\SQLi Dumper v10.3\SQLi Dumper 10.3 Cracked.exe | executable | |
MD5:DCA4C30AF8E1F59E8C113947C89D77BA | SHA256:5003BFB12E4B796ABBF3A7D9781070053379627134B14E7F9C3579965692F9A4 | |||
| 6220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6220.20865\SQLi Dumper v10.3\TXT\DicLoginFinder.txt | text | |
MD5:AE4118C172D58469E180E5D0F74C2C2B | SHA256:2631153A5617725015F19817374985DCBD1E649F9F5D633269239C78639DB7B0 | |||
| 6220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6220.20865\SQLi Dumper v10.3\Settings.xml | xml | |
MD5:75A5096A8D55E17102DF4580D915D6EE | SHA256:84EF09FA32AA6C8E1171ED02EF98B2F3FCB64BDA620E74BCBC9B4B4969038457 | |||
| 6220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6220.20865\SQLi Dumper v10.3\SkinSoft.VisualStyler.dll | executable | |
MD5:D93366374B57B5A0FE3A1A8A1CA95F78 | SHA256:14F231441DAD16EF046AB97415C33195056A61B0240D7D890971E5F626068925 | |||
| 6220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6220.20865\SQLi Dumper v10.3\LNG\French.xml | xml | |
MD5:A46FDB87ECF4E654CAC6348C542A6D2C | SHA256:A4A5086AB9BFC8755F199B0F1C80F70EBF660768D031727BF71A624FBF99D2D9 | |||
| 6220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6220.20865\SQLi Dumper v10.3\LNG\German.xml | xml | |
MD5:4A25B19B26DEF334C719E8D543F23486 | SHA256:97BB355062589C2C89E139E8174B71A15FBE89F10E2C72DE1489AD3B9B035B91 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
36
DNS requests
21
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6092 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6092 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6656 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3000 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3000 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6320 | SQLi Dumper 10.3.exe | GET | 502 | 158.101.44.242:80 | http://checkip.dyndns.org/ | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6092 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6092 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 92.123.104.32:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
6320 | SQLi Dumper 10.3.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup - checkip.dyndns.org |
1 ETPRO signatures available at the full report