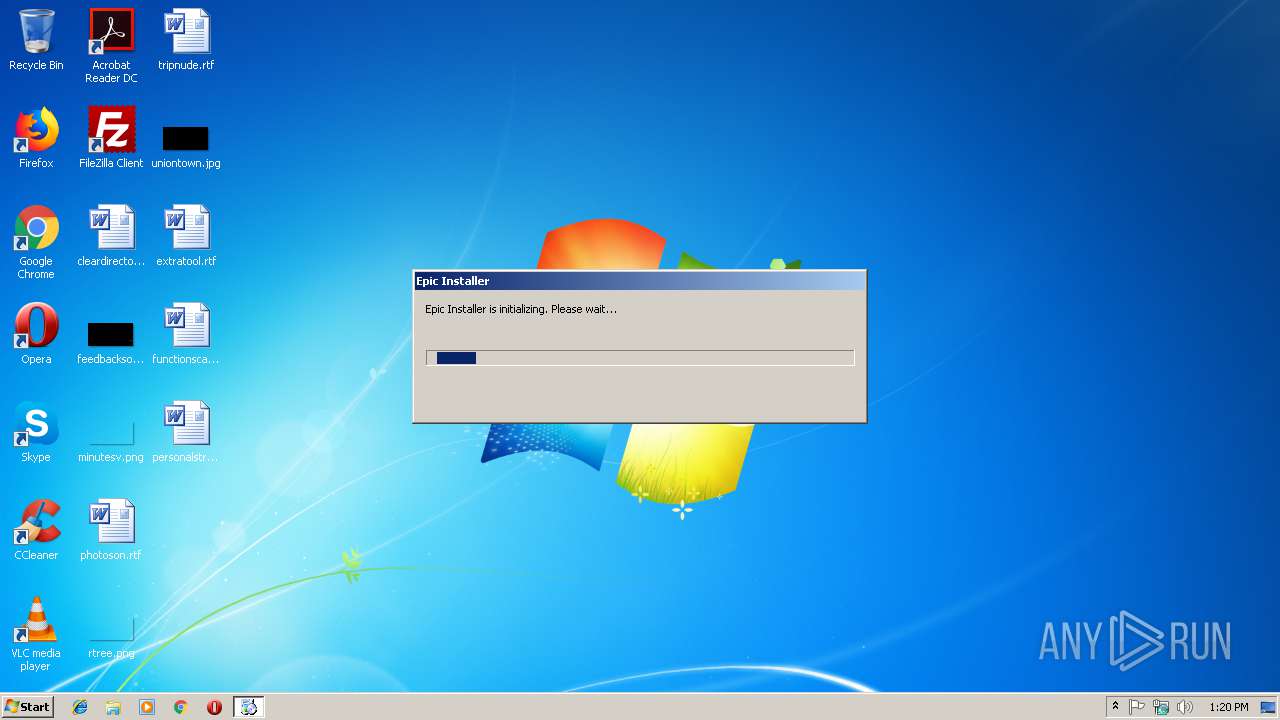
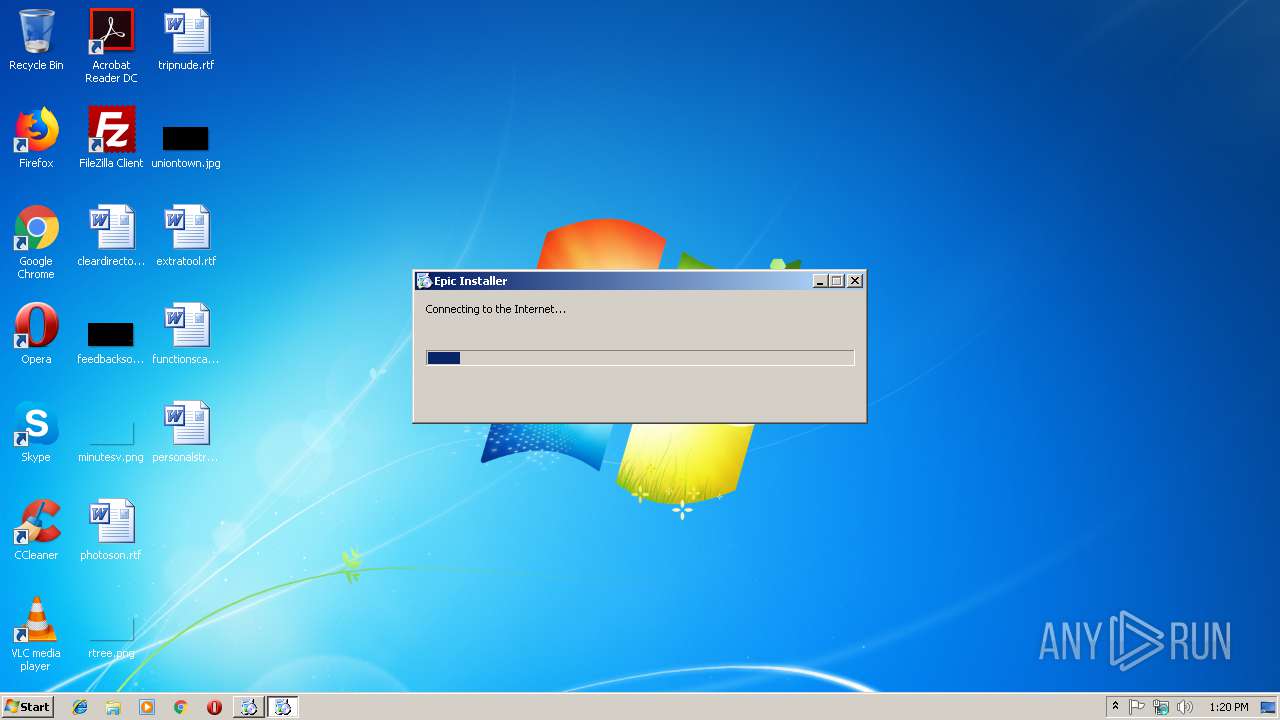
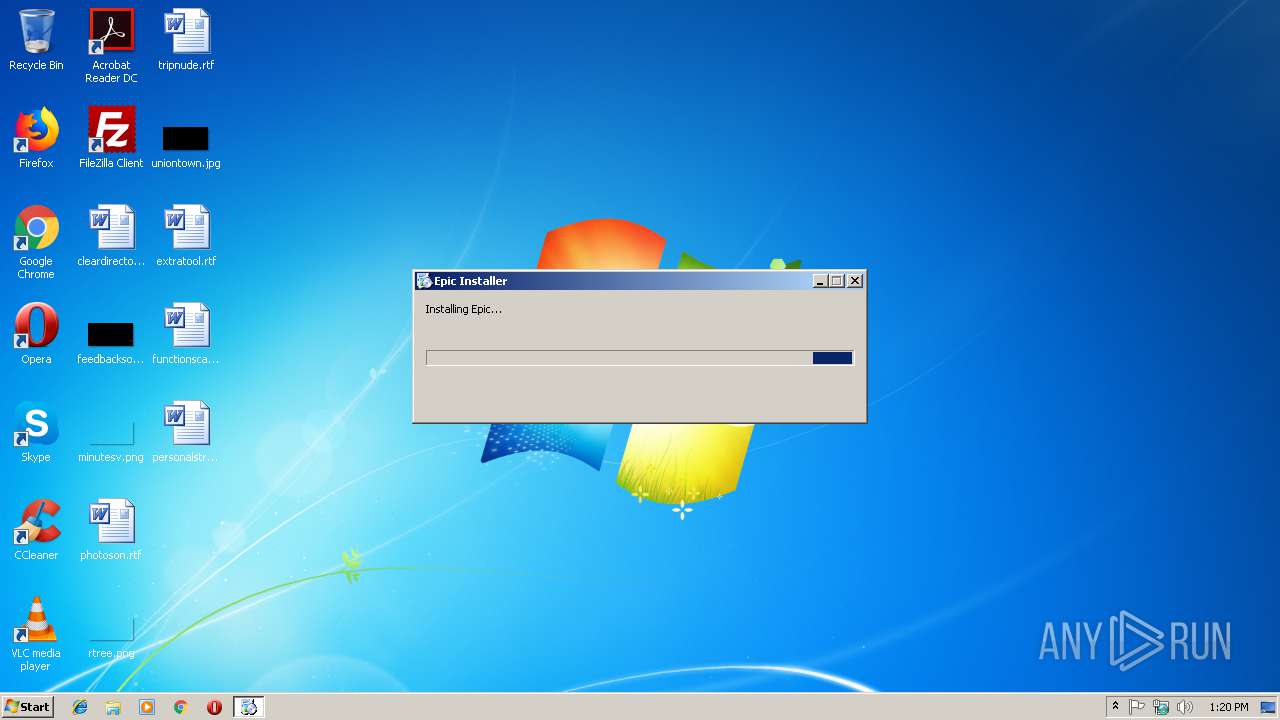
| download: | epicsetup.exe |
| Full analysis: | https://app.any.run/tasks/099e98fa-bdbc-495a-a4f5-079ddaa9e910 |
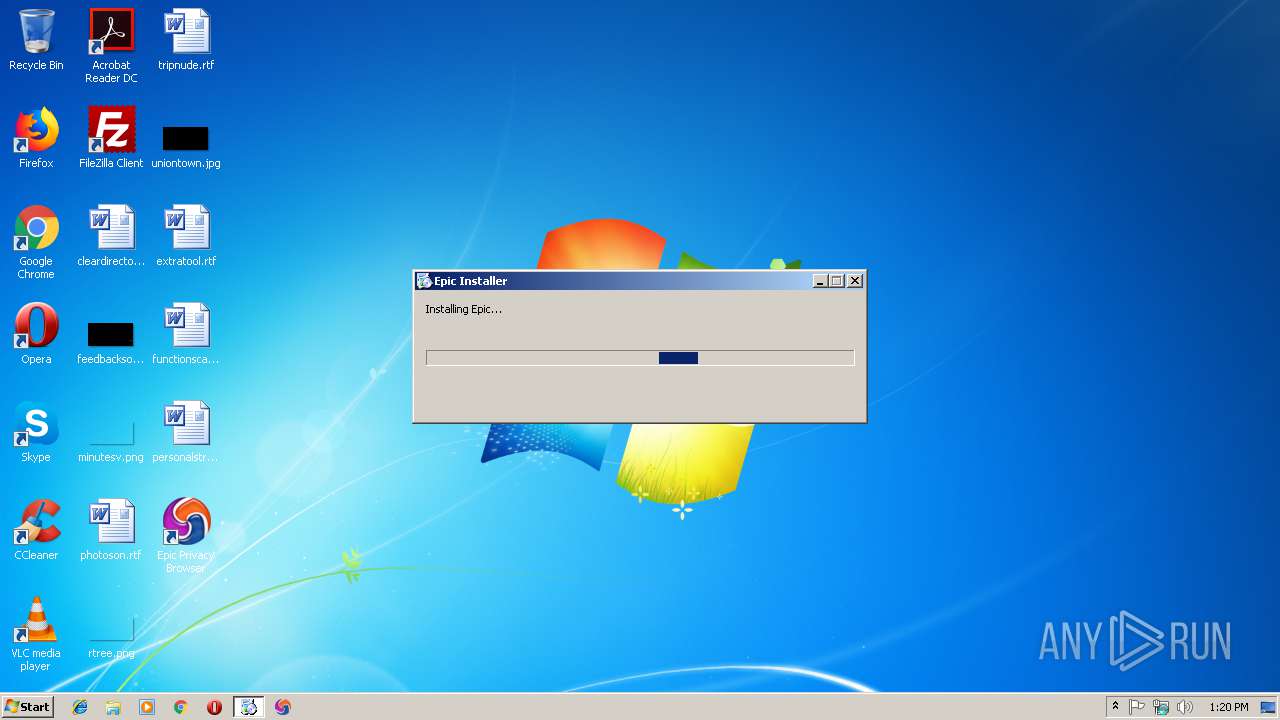
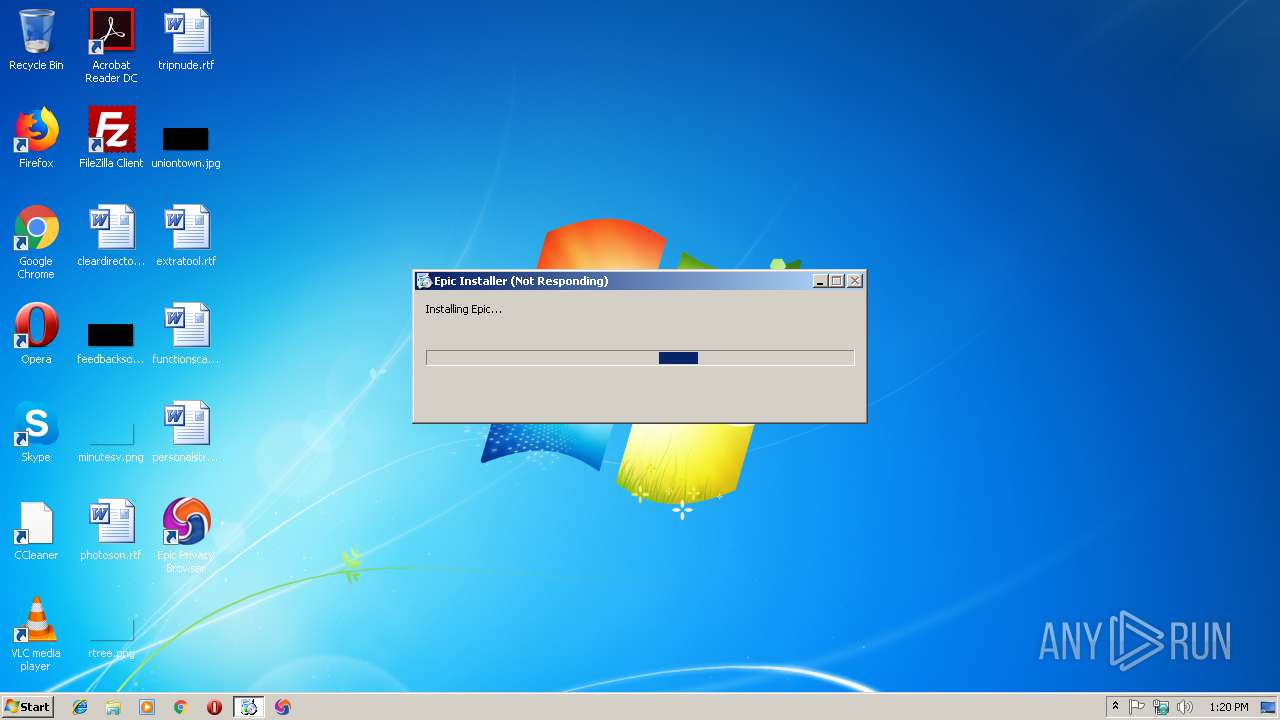
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2018, 13:19:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 607B6DA10B6DDB74610D8FD72AC85ADC |
| SHA1: | C76FABD1ABDDFCD7BD9307C04685674F009BBC6D |
| SHA256: | E46853CAAF6ADF679F3BDB116761AA7EF199F148641CFF7EC9D76FD67EF5305F |
| SSDEEP: | 49152:9aECKpr/+dFlBRdngJI1YRKa8YuYnlVobKb:sEt/+dXBRdngGa8UnlVoOb |
MALICIOUS
Application was dropped or rewritten from another process
- EpicUpdate.exe (PID: 3556)
- EpicUpdate.exe (PID: 2224)
- EpicUpdate.exe (PID: 2408)
- EpicUpdate.exe (PID: 3716)
- EpicCrashHandler.exe (PID: 3944)
- EpicUpdate.exe (PID: 2612)
- EpicUpdate.exe (PID: 2800)
- EpicUpdate.exe (PID: 3768)
- EpicUpdate.exe (PID: 2188)
- EpicUpdate.exe (PID: 3540)
- setup.exe (PID: 2572)
- setup.exe (PID: 3108)
- epic.exe (PID: 2620)
- EpicUpdate.exe (PID: 2812)
- epic.exe (PID: 560)
- epic.exe (PID: 3840)
- epic.exe (PID: 4064)
- epic.exe (PID: 1520)
- epic.exe (PID: 2940)
- epic.exe (PID: 3432)
- epic.exe (PID: 3988)
- epic.exe (PID: 2192)
- epic.exe (PID: 2868)
- epic.exe (PID: 3176)
- epic.exe (PID: 2652)
- epic.exe (PID: 3460)
- epic.exe (PID: 3476)
- epic.exe (PID: 3136)
- epic.exe (PID: 4056)
- epic.exe (PID: 908)
- epic.exe (PID: 2608)
- epic.exe (PID: 2888)
- epic.exe (PID: 2196)
- epic.exe (PID: 3796)
Changes the autorun value in the registry
- EpicUpdate.exe (PID: 3556)
Loads dropped or rewritten executable
- EpicUpdate.exe (PID: 3556)
- EpicUpdate.exe (PID: 2224)
- EpicUpdate.exe (PID: 2408)
- EpicUpdate.exe (PID: 3716)
- EpicUpdate.exe (PID: 2188)
- EpicCrashHandler.exe (PID: 3944)
- EpicUpdate.exe (PID: 2612)
- EpicUpdate.exe (PID: 2800)
- EpicUpdate.exe (PID: 3540)
- EpicUpdate.exe (PID: 3768)
- epic.exe (PID: 2620)
- epic.exe (PID: 560)
- epic.exe (PID: 4064)
- EpicUpdate.exe (PID: 2812)
- epic.exe (PID: 3840)
- epic.exe (PID: 1520)
- epic.exe (PID: 2940)
- epic.exe (PID: 2868)
- epic.exe (PID: 3476)
- epic.exe (PID: 3432)
- epic.exe (PID: 3988)
- epic.exe (PID: 2192)
- epic.exe (PID: 2652)
- epic.exe (PID: 4056)
- epic.exe (PID: 3460)
- epic.exe (PID: 3136)
- epic.exe (PID: 3176)
- epic.exe (PID: 3796)
- epic.exe (PID: 2608)
- epic.exe (PID: 2888)
- epic.exe (PID: 908)
- epic.exe (PID: 2196)
Loads the Task Scheduler COM API
- EpicUpdate.exe (PID: 3556)
Loads the Task Scheduler DLL interface
- EpicUpdate.exe (PID: 3556)
- EpicUpdate.exe (PID: 2408)
Changes settings of System certificates
- EpicUpdate.exe (PID: 3540)
Actions looks like stealing of personal data
- epic.exe (PID: 2620)
SUSPICIOUS
Creates files in the program directory
- EpicUpdate.exe (PID: 3556)
Executable content was dropped or overwritten
- EpicUpdate.exe (PID: 3556)
- epicsetup.exe (PID: 2976)
- mini_installer.exe (PID: 3916)
- setup.exe (PID: 2572)
Starts itself from another location
- EpicUpdate.exe (PID: 3556)
- EpicUpdate.exe (PID: 2408)
Creates COM task schedule object
- EpicUpdate.exe (PID: 2224)
- EpicUpdate.exe (PID: 3556)
Application launched itself
- EpicUpdate.exe (PID: 2408)
- EpicUpdate.exe (PID: 2612)
- setup.exe (PID: 2572)
- epic.exe (PID: 2620)
- EpicUpdate.exe (PID: 3540)
Creates files in the user directory
- setup.exe (PID: 2572)
- epic.exe (PID: 2620)
Creates a software uninstall entry
- setup.exe (PID: 2572)
Modifies the open verb of a shell class
- setup.exe (PID: 2572)
INFO
Dropped object may contain Bitcoin addresses
- setup.exe (PID: 2572)
- epic.exe (PID: 2868)
Dropped object may contain TOR URL's
- epic.exe (PID: 2868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:05:24 11:16:53+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 333312 |
| InitializedDataSize: | 1491968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.27.13 |
| ProductVersionNumber: | 1.3.27.13 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Epic Privacy Browser |
| FileDescription: | Epic Privacy Browser Installer Setup |
| FileVersion: | 1.3.27.13 |
| InternalName: | Epic Privacy Browser Installer Setup |
| LegalCopyright: | Copyright 2007-2010 Google Inc. |
| OriginalFileName: | EpicUpdateSetup.exe |
| ProductName: | Epic Privacy Browser Installer |
| ProductVersion: | 1.3.27.13 |
| LanguageId: | en |
| Debug: | - |
| PrivateBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-May-2017 09:16:53 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Epic Privacy Browser |
| FileDescription: | Epic Privacy Browser Installer Setup |
| FileVersion: | 1.3.27.13 |
| InternalName: | Epic Privacy Browser Installer Setup |
| LegalCopyright: | Copyright 2007-2010 Google Inc. |
| OriginalFilename: | EpicUpdateSetup.exe |
| ProductName: | Epic Privacy Browser Installer |
| ProductVersion: | 1.3.27.13 |
| LanguageId: | en |
| Debug: | - |
| PrivateBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-May-2017 09:16:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00051561 | 0x00051600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.20794 |
.rdata | 0x00053000 | 0x00010FEC | 0x00011000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.47829 |
.data | 0x00064000 | 0x00002EFC | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.42225 |
.rsrc | 0x00067000 | 0x001562D0 | 0x00156400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99021 |
.reloc | 0x001BE000 | 0x00003C28 | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64679 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09285 | 738 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 4.13669 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.91985 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.83772 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.68656 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.50268 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.86669 | 90 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
102 | 7.99988 | 1369007 | Latin 1 / Western European | UNKNOWN | B |
1321 | 3.64009 | 422 | Latin 1 / Western European | Serbian - Serbia (Cyrillic) | RT_STRING |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
67
Monitored processes
36
Malicious processes
19
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Users\admin\AppData\Local\Epic Privacy Browser\Application\epic.exe" --type=crashpad-handler /prefetch:7 "--database=C:\Users\admin\AppData\Local\Epic Privacy Browser\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Epic Privacy Browser\User Data" --annotation=channel= --annotation=plat=Win32 --annotation=prod=Epic --annotation=ver=62.0.3202.94 --initial-client-data=0x24,0x28,0x2c,0x20,0x78,0x6f3c82e4,0x6f3c82f4,0x6f3c8304 | C:\Users\admin\AppData\Local\Epic Privacy Browser\Application\epic.exe | — | epic.exe | |||||||||||
User: admin Company: Hidden Reflex Authors Integrity Level: MEDIUM Description: Epic Privacy Bowser Exit code: 0 Version: 62.0.3202.94 Modules
| |||||||||||||||
| 908 | "C:\Users\admin\AppData\Local\Epic Privacy Browser\Application\epic.exe" --type=renderer --field-trial-handle=1612 --primordial-pipe-token=61D59F801F35B0916B8966B99030F4BF --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true,parseHTMLOnMainThreadCoalesceChunks=false,parseHTMLOnMainThreadSyncTokenize=false,cssExternalScannerNoPreload=false,cssExternalScannerPreload=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553 --disable-accelerated-video-decode --disable-webrtc-hw-vp8-encoding --disable-gpu-compositing --service-request-channel-token=61D59F801F35B0916B8966B99030F4BF --renderer-client-id=20 --mojo-platform-channel-handle=3020 /prefetch:1 | C:\Users\admin\AppData\Local\Epic Privacy Browser\Application\epic.exe | — | epic.exe | |||||||||||
User: admin Company: Hidden Reflex Authors Integrity Level: LOW Description: Epic Privacy Bowser Exit code: 0 Version: 62.0.3202.94 Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\AppData\Local\Epic Privacy Browser\Application\epic.exe" --type=renderer --field-trial-handle=1612 --primordial-pipe-token=D9FEEBDF7139DA62C8B0F778CFFBCC6C --lang=en-US --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true,parseHTMLOnMainThreadCoalesceChunks=false,parseHTMLOnMainThreadSyncTokenize=false,cssExternalScannerNoPreload=false,cssExternalScannerPreload=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553 --disable-accelerated-video-decode --disable-webrtc-hw-vp8-encoding --disable-gpu-compositing --service-request-channel-token=D9FEEBDF7139DA62C8B0F778CFFBCC6C --renderer-client-id=5 --mojo-platform-channel-handle=1752 /prefetch:1 | C:\Users\admin\AppData\Local\Epic Privacy Browser\Application\epic.exe | — | epic.exe | |||||||||||
User: admin Company: Hidden Reflex Authors Integrity Level: LOW Description: Epic Privacy Bowser Exit code: 0 Version: 62.0.3202.94 Modules
| |||||||||||||||
| 2188 | "C:\Users\admin\AppData\Local\Epic Privacy Browser\Installer\EpicUpdate.exe" /uninstall | C:\Users\admin\AppData\Local\Epic Privacy Browser\Installer\EpicUpdate.exe | EpicUpdate.exe | ||||||||||||
User: admin Company: Epic Privacy Browser Integrity Level: MEDIUM Description: Epic Privacy Browser Installer Exit code: 0 Version: 1.3.27.13 Modules
| |||||||||||||||
| 2192 | "C:\Users\admin\AppData\Local\Epic Privacy Browser\Application\epic.exe" --type=utility --lang=en-US --utility-allowed-dir="C:\Users\admin\AppData\Local\Temp\scoped_dir_2620_28147" --service-request-channel-token=C93EFBDACC6E749CFDF03C6835BD6EA7 --mojo-platform-channel-handle=2684 --ignored=" --type=renderer " /prefetch:8 | C:\Users\admin\AppData\Local\Epic Privacy Browser\Application\epic.exe | — | epic.exe | |||||||||||
User: admin Company: Hidden Reflex Authors Integrity Level: LOW Description: Epic Privacy Bowser Exit code: 0 Version: 62.0.3202.94 Modules
| |||||||||||||||
| 2196 | "C:\Users\admin\AppData\Local\Epic Privacy Browser\Application\epic.exe" --type=renderer --field-trial-handle=1612 --primordial-pipe-token=9D975E66F7050D4DAC2F4803CD0066FD --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true,parseHTMLOnMainThreadCoalesceChunks=false,parseHTMLOnMainThreadSyncTokenize=false,cssExternalScannerNoPreload=false,cssExternalScannerPreload=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553 --disable-accelerated-video-decode --disable-webrtc-hw-vp8-encoding --disable-gpu-compositing --service-request-channel-token=9D975E66F7050D4DAC2F4803CD0066FD --renderer-client-id=21 --mojo-platform-channel-handle=3024 /prefetch:1 | C:\Users\admin\AppData\Local\Epic Privacy Browser\Application\epic.exe | — | epic.exe | |||||||||||
User: admin Company: Hidden Reflex Authors Integrity Level: LOW Description: Epic Privacy Bowser Exit code: 0 Version: 62.0.3202.94 Modules
| |||||||||||||||
| 2224 | "C:\Users\admin\AppData\Local\Epic Privacy Browser\Installer\EpicUpdate.exe" /regserver | C:\Users\admin\AppData\Local\Epic Privacy Browser\Installer\EpicUpdate.exe | EpicUpdate.exe | ||||||||||||
User: admin Company: Epic Privacy Browser Integrity Level: MEDIUM Description: Epic Privacy Browser Installer Exit code: 0 Version: 1.3.27.13 Modules
| |||||||||||||||
| 2408 | "C:\Users\admin\AppData\Local\Epic Privacy Browser\Installer\EpicUpdate.exe" /c | C:\Users\admin\AppData\Local\Epic Privacy Browser\Installer\EpicUpdate.exe | EpicUpdate.exe | ||||||||||||
User: admin Company: Epic Privacy Browser Integrity Level: MEDIUM Description: Epic Privacy Browser Installer Exit code: 0 Version: 1.3.27.13 Modules
| |||||||||||||||
| 2572 | "C:\Users\admin\AppData\Local\Temp\CR_87703.tmp\setup.exe" --install-archive="C:\Users\admin\AppData\Local\Temp\CR_87703.tmp\CHROME.PACKED.7Z" | C:\Users\admin\AppData\Local\Temp\CR_87703.tmp\setup.exe | mini_installer.exe | ||||||||||||
User: admin Company: Hidden Reflex Authors Integrity Level: MEDIUM Description: Epic Privacy Browser Installer Exit code: 0 Version: 62.0.3202.94 Modules
| |||||||||||||||
| 2608 | "C:\Users\admin\AppData\Local\Epic Privacy Browser\Application\epic.exe" --type=renderer --field-trial-handle=1612 --primordial-pipe-token=169A6932578DA8811D306513A50E003E --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --blink-settings=disallowFetchForDocWrittenScriptsInMainFrame=false,disallowFetchForDocWrittenScriptsInMainFrameOnSlowConnections=true,parseHTMLOnMainThreadCoalesceChunks=false,parseHTMLOnMainThreadSyncTokenize=false,cssExternalScannerNoPreload=false,cssExternalScannerPreload=true --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553 --disable-accelerated-video-decode --disable-webrtc-hw-vp8-encoding --disable-gpu-compositing --service-request-channel-token=169A6932578DA8811D306513A50E003E --renderer-client-id=18 --mojo-platform-channel-handle=3396 /prefetch:1 | C:\Users\admin\AppData\Local\Epic Privacy Browser\Application\epic.exe | — | epic.exe | |||||||||||
User: admin Company: Hidden Reflex Authors Integrity Level: LOW Description: Epic Privacy Bowser Exit code: 0 Version: 62.0.3202.94 Modules
| |||||||||||||||
Total events
2 083
Read events
1 639
Write events
435
Delete events
9
Modification events
| (PID) Process: | (2224) EpicUpdate.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{82610E6D-11CA-45A9-98B1-D03B9AEDBD13}\InprocHandler32 |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Epic Privacy Browser\Installer\1.3.27.13\psuser.dll | |||
| (PID) Process: | (2224) EpicUpdate.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{82610E6D-11CA-45A9-98B1-D03B9AEDBD13}\InprocHandler32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2224) EpicUpdate.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{84D964EE-0441-4A42-8146-0699AE05DDC3}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Epic Privacy Browser\Installer\1.3.27.13\psuser.dll | |||
| (PID) Process: | (2224) EpicUpdate.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{84D964EE-0441-4A42-8146-0699AE05DDC3}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2224) EpicUpdate.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{9BA04732-4369-45EF-9DA1-90561134DE6D}\InProcServer32 |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Epic Privacy Browser\Installer\1.3.27.13\psuser.dll | |||
| (PID) Process: | (2224) EpicUpdate.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{9BA04732-4369-45EF-9DA1-90561134DE6D}\InProcServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (2224) EpicUpdate.exe | Key: | HKEY_CLASSES_ROOT\CLSID\{9BA04732-4369-45EF-9DA1-90561134DE6D} |
| Operation: | write | Name: | |
Value: PSFactoryBuffer | |||
| (PID) Process: | (2224) EpicUpdate.exe | Key: | HKEY_CLASSES_ROOT\Interface\{BB14760B-E6FA-4A12-80A8-0B4831229E82}\ProxyStubClsid32 |
| Operation: | write | Name: | |
Value: {9BA04732-4369-45EF-9DA1-90561134DE6D} | |||
| (PID) Process: | (2224) EpicUpdate.exe | Key: | HKEY_CLASSES_ROOT\Interface\{BB14760B-E6FA-4A12-80A8-0B4831229E82} |
| Operation: | write | Name: | |
Value: ICurrentState | |||
| (PID) Process: | (2224) EpicUpdate.exe | Key: | HKEY_CLASSES_ROOT\Interface\{BB14760B-E6FA-4A12-80A8-0B4831229E82}\NumMethods |
| Operation: | write | Name: | |
Value: 24 | |||
Executable files
138
Suspicious files
70
Text files
229
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | epicsetup.exe | C:\Users\admin\AppData\Local\Temp\GUM88CD.tmp\EpicUpdate.exe | executable | |
MD5:BA86A3AD65404FC5E08078A638611F52 | SHA256:A722FA6E47F612DAE6A3B90838843A9ADD4AF52BF5E19ED025F9DF5332E444B9 | |||
| 2976 | epicsetup.exe | C:\Users\admin\AppData\Local\Temp\GUM88CD.tmp\npEpicUpdate3.dll | executable | |
MD5:B498BE7C886353A79315F3AFFB53C02F | SHA256:84683A8956BE084F7201DD0BCFE1C109997B14BF8A6C3F7C93BD7ABF599D412D | |||
| 2976 | epicsetup.exe | C:\Users\admin\AppData\Local\Temp\GUM88CD.tmp\psmachine.dll | executable | |
MD5:456547F13C9082D512E65BD73D1E306E | SHA256:5A7A95FBE52B34EDB6575170EBF11FC5A28BC892F763A7C6EF1882E90399D217 | |||
| 2976 | epicsetup.exe | C:\Users\admin\AppData\Local\Temp\GUM88CD.tmp\goopdate.dll | executable | |
MD5:AA8C6DB4925ADF7B02FF646E2A8D744F | SHA256:D9359E17DC24D47EFF57799DACF56401ADD24C34029048C905416AF6A2C182E3 | |||
| 2976 | epicsetup.exe | C:\Users\admin\AppData\Local\Temp\GUM88CD.tmp\goopdateres_am.dll | executable | |
MD5:E34ABA0124A8ADD9C4D24569147C8167 | SHA256:507929E0064EC683AE2A1C34B856BDAEC9D198EE1F15E0985BF756C0DB8F1862 | |||
| 2976 | epicsetup.exe | C:\Users\admin\AppData\Local\Temp\GUM88CD.tmp\EpicUpdateHelper.msi | executable | |
MD5:A39C5B57BB946852A41B21F540D54D2B | SHA256:E4207DAC538CEE89A84776482EECBF19F9F06ED2A75C6898D195B3183AE8B913 | |||
| 2976 | epicsetup.exe | C:\Users\admin\AppData\Local\Temp\GUM88CD.tmp\EpicUpdateOnDemand.exe | executable | |
MD5:0C34A4F1DA39D6DB6A584628E72BE7E9 | SHA256:F9C8F2D658FAF86ED3963739E985A5C2A624E0F2C84E8F8D27ED7473A07709A1 | |||
| 2976 | epicsetup.exe | C:\Users\admin\AppData\Local\Temp\GUM88CD.tmp\goopdateres_ar.dll | executable | |
MD5:E9B4909C22C80AFF9E6A3948BA9F0A96 | SHA256:B5ECFD924F970165553B56EEBFC5BB898D54A39D1FDC93ADCFB372FACA44963A | |||
| 2976 | epicsetup.exe | C:\Users\admin\AppData\Local\Temp\GUM88CD.tmp\goopdateres_bg.dll | executable | |
MD5:B808250A6900087DEFF5D2C585DE19FB | SHA256:33E24FC64C6EBD8EC5E97C1D8BEC88B0C6353A1551D526BFB0705DA555DE4FF0 | |||
| 2976 | epicsetup.exe | C:\Users\admin\AppData\Local\Temp\GUM88CD.tmp\EpicUpdateBroker.exe | executable | |
MD5:E2C11186B9373FBC8D0F8C301BD5B867 | SHA256:117EC60AA324B6D0719B1FFBD70E346B1892C0A30A51B4FAC63ADEE8D120B6EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
24
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3540 | EpicUpdate.exe | POST | 200 | 206.189.4.63:80 | http://updates.epicbrowser.com/service/update2?w=3:OX7CrZds0eI3k0Can3VYVkO-4O5eij4rqxSOUIHayxW3kaMdTyk0r0ADHMBAg9N1ay8MHYDfe5j6-AhKMCFSrOFXPsp8wshDbtXWqon61mYGRvcrwok39aR40K4rRBp454HAWK2vaqyQ03nUjDcCHe7iQU1cvmc4KEWhJG5sduQ | US | xml | 869 b | whitelisted |
2800 | EpicUpdate.exe | POST | 200 | 206.189.4.63:80 | http://updates.epicbrowser.com/service/update2 | US | xml | 352 b | whitelisted |
2812 | EpicUpdate.exe | POST | 200 | 206.189.4.63:80 | http://updates.epicbrowser.com/service/update2 | US | xml | 1.01 Kb | whitelisted |
2620 | epic.exe | GET | 200 | 128.199.39.15:80 | http://updates.epicbrowser.com/extensions/newtab/newAdd.html | NL | html | 958 b | whitelisted |
2620 | epic.exe | GET | 200 | 128.199.39.15:80 | http://updates.epicbrowser.com/extensions/newtab/newTabAd.xml | NL | text | 118 b | whitelisted |
3716 | EpicUpdate.exe | GET | 404 | 206.189.4.63:80 | http://updates.epicbrowser.com/service/check2?appid=%7BB852E7B1-908A-48EF-9576-CBE23654D907%7D&appversion=1.3.27.13&applang=&machine=0&version=0.0.0.0&osversion=6.1&servicepack=Service%20Pack%201 | US | html | 2.74 Kb | whitelisted |
3540 | EpicUpdate.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSADomainValidationSecureServerCA.crt | GB | der | 1.51 Kb | whitelisted |
3540 | EpicUpdate.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3540 | EpicUpdate.exe | 206.189.4.63:80 | updates.epicbrowser.com | — | US | unknown |
3540 | EpicUpdate.exe | 91.199.212.52:80 | crt.comodoca.com | Comodo CA Ltd | GB | suspicious |
— | — | 62.113.194.2:443 | cdn.epicbrowser.com | 23media GmbH | DE | malicious |
2620 | epic.exe | 173.194.76.153:443 | chromium-i18n.appspot.com | Google Inc. | US | unknown |
2620 | epic.exe | 82.196.2.74:443 | epicbrowser.com | Digital Ocean, Inc. | NL | unknown |
2812 | EpicUpdate.exe | 206.189.4.63:80 | updates.epicbrowser.com | — | US | unknown |
2620 | epic.exe | 128.199.39.15:80 | updates.epicbrowser.com | Digital Ocean, Inc. | NL | unknown |
2620 | epic.exe | 216.58.215.234:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3716 | EpicUpdate.exe | 206.189.4.63:80 | updates.epicbrowser.com | — | US | unknown |
3540 | EpicUpdate.exe | 206.189.4.63:443 | updates.epicbrowser.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
updates.epicbrowser.com |
| whitelisted |
crt.comodoca.com |
| whitelisted |
cdn.epicbrowser.com |
| malicious |
www.google.com |
| malicious |
chromium-i18n.appspot.com |
| whitelisted |
epicbrowser.com |
| unknown |
www.epicbrowser.com |
| unknown |
translate.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
EpicUpdate.exe | LOG_SYSTEM: [EpicUpdate:goopdate]: ERROR - Cannot create ETW log writer |
EpicUpdate.exe | [12/14/18 13:20:11.468][EpicUpdate:goopdate][3556:3560][OS][version: OS_WINDOWS_7][service pack: 1]
|
EpicUpdate.exe | [12/14/18 13:20:11.468][EpicUpdate:goopdate][3556:3560][GetNamedObjectAttributes][named_object=Global\ES-1-5-21-1302019708-1500728564-335382590-1000_Epic Privacy Browser_Installer_Report_Ids_Lock_57146B01-6A07-4b8d-A1D8-0C3AFC3B2F9B]
|
EpicUpdate.exe | [12/14/18 13:20:11.468][EpicUpdate:goopdate][3556:3560][DllEntry][C:\Users\admin\AppData\Local\Temp\GUM88CD.tmp\EpicUpdate.exe /installsource taggedmi /install "appguid={A3AA2AD6-C357-4BB3-9625-6550647D956D}&appname=Epic&needsadmin=False&lang=en"]
|
EpicUpdate.exe | [12/14/18 13:20:11.468][EpicUpdate:goopdate][3556:3560][Goopdate::Goopdate]
|
EpicUpdate.exe | [12/14/18 13:20:11.468][EpicUpdate:goopdate][3556:3560][Crash::InstallCrashHandler][is_machine 0]
|
EpicUpdate.exe | [12/14/18 13:20:11.484][EpicUpdate:goopdate][3556:3560][crash dir C:\Users\admin\AppData\Local\Epic Privacy Browser\CrashReports]
|
EpicUpdate.exe | [12/14/18 13:20:11.484][EpicUpdate:goopdate][3556:3560][exception handler has been installed]
|
EpicUpdate.exe | [12/14/18 13:20:11.484][EpicUpdate:goopdate][3556:3560][ThreadPool::ThreadPool]
|
EpicUpdate.exe | [12/14/18 13:20:11.484][EpicUpdate:goopdate][3556:3560][C:\Users\admin\AppData\Local\Temp\GUM88CD.tmp\goopdate.dll][version 1.3.27.13][dbg][dev]
|