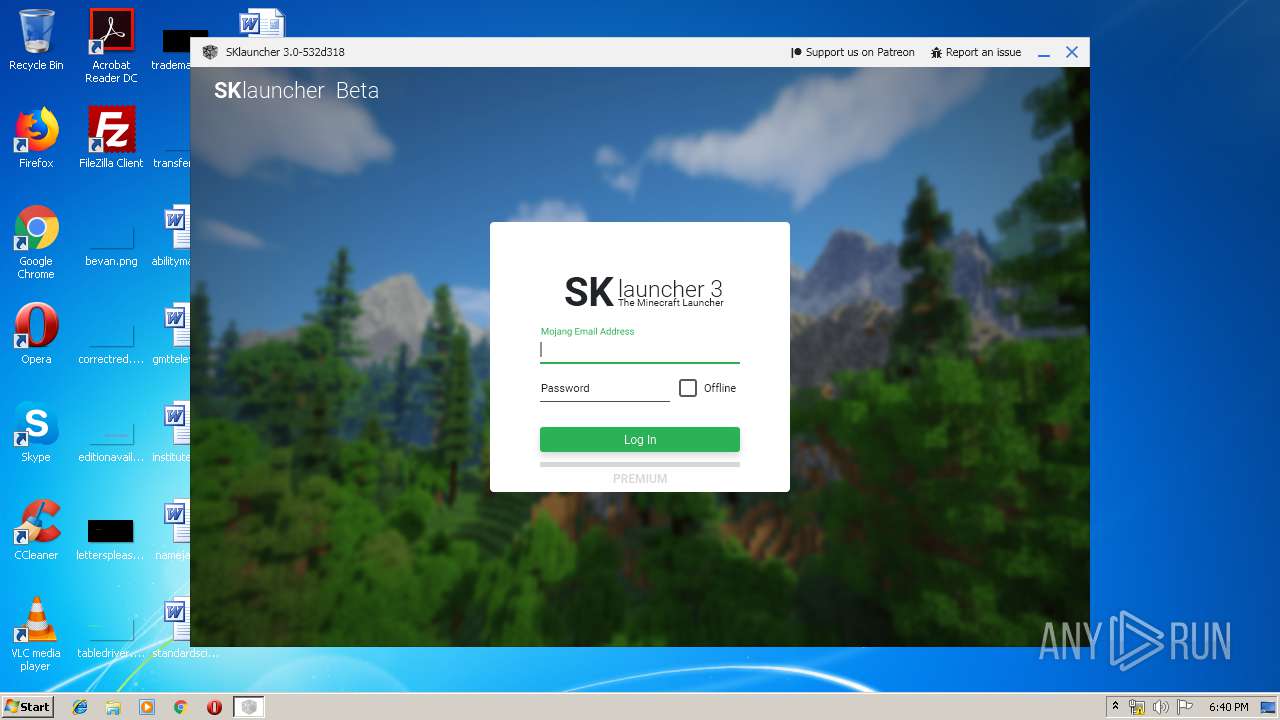
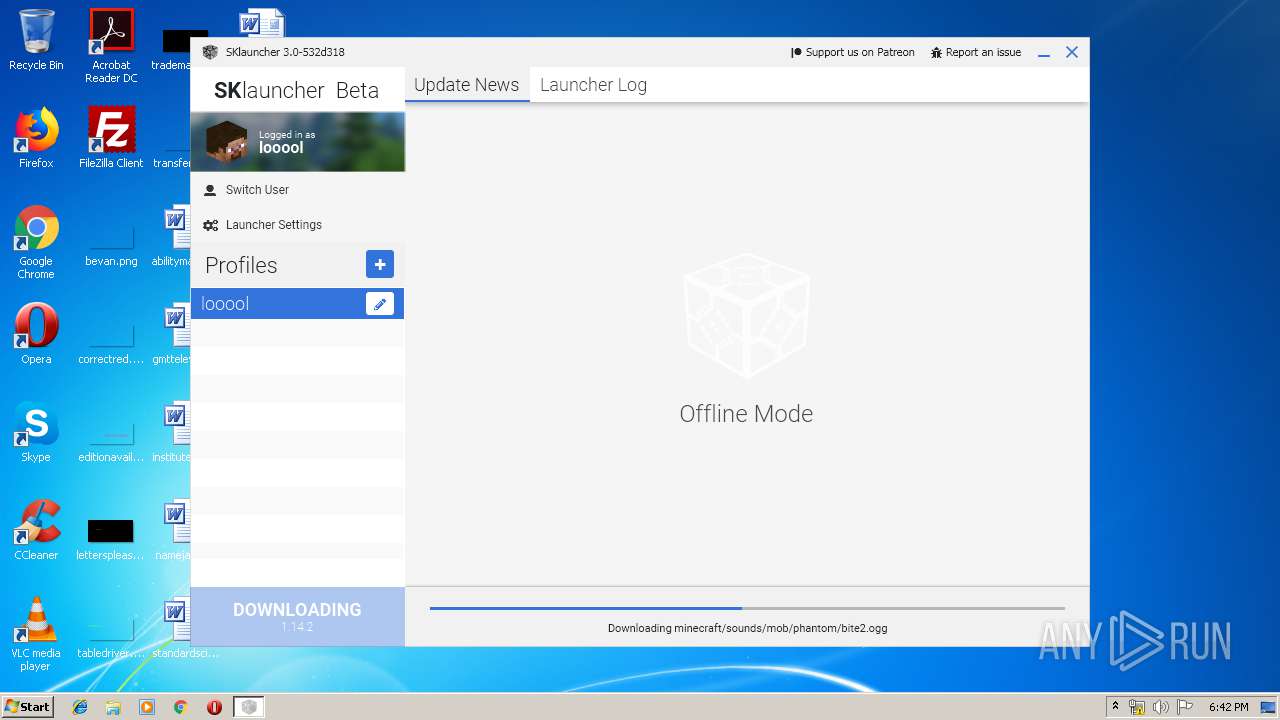
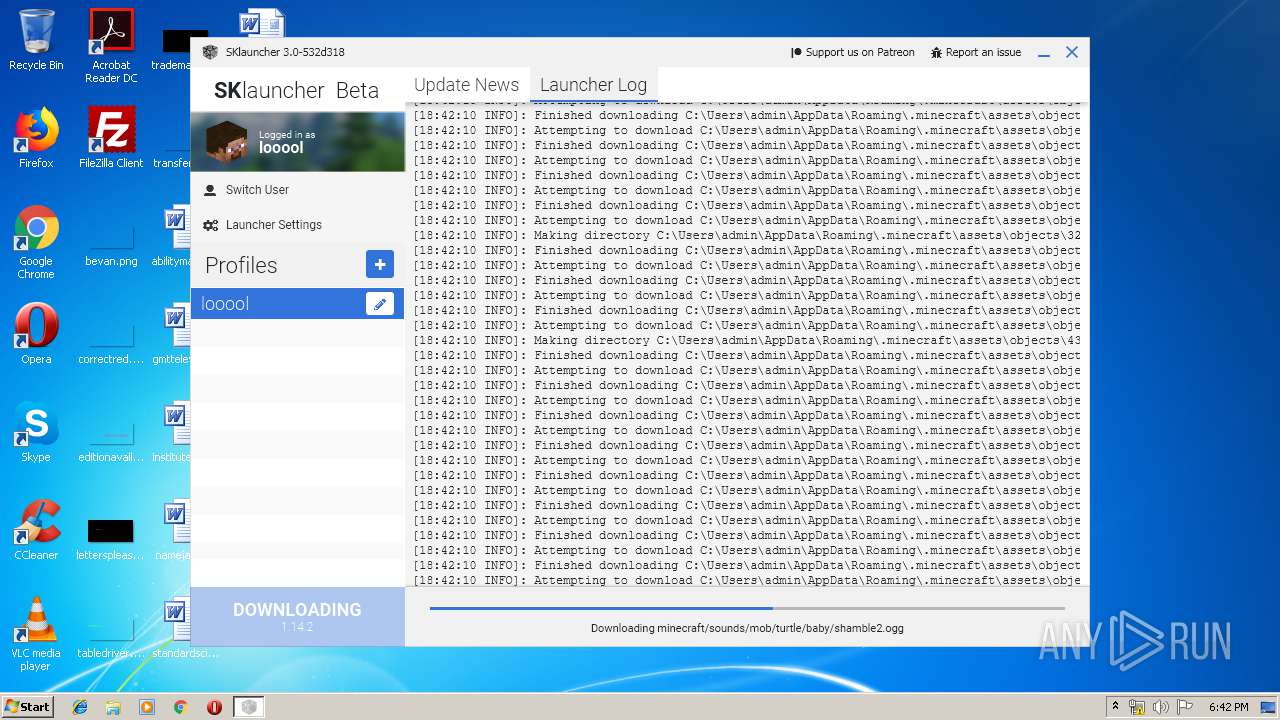
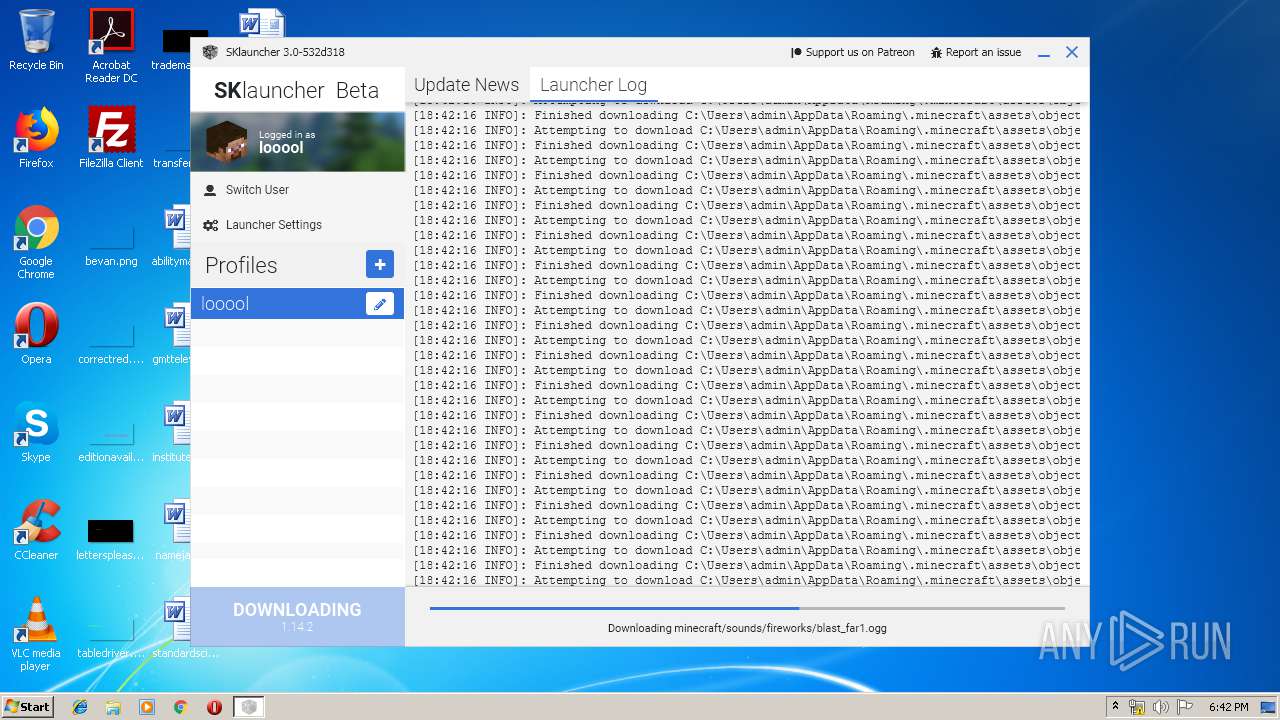
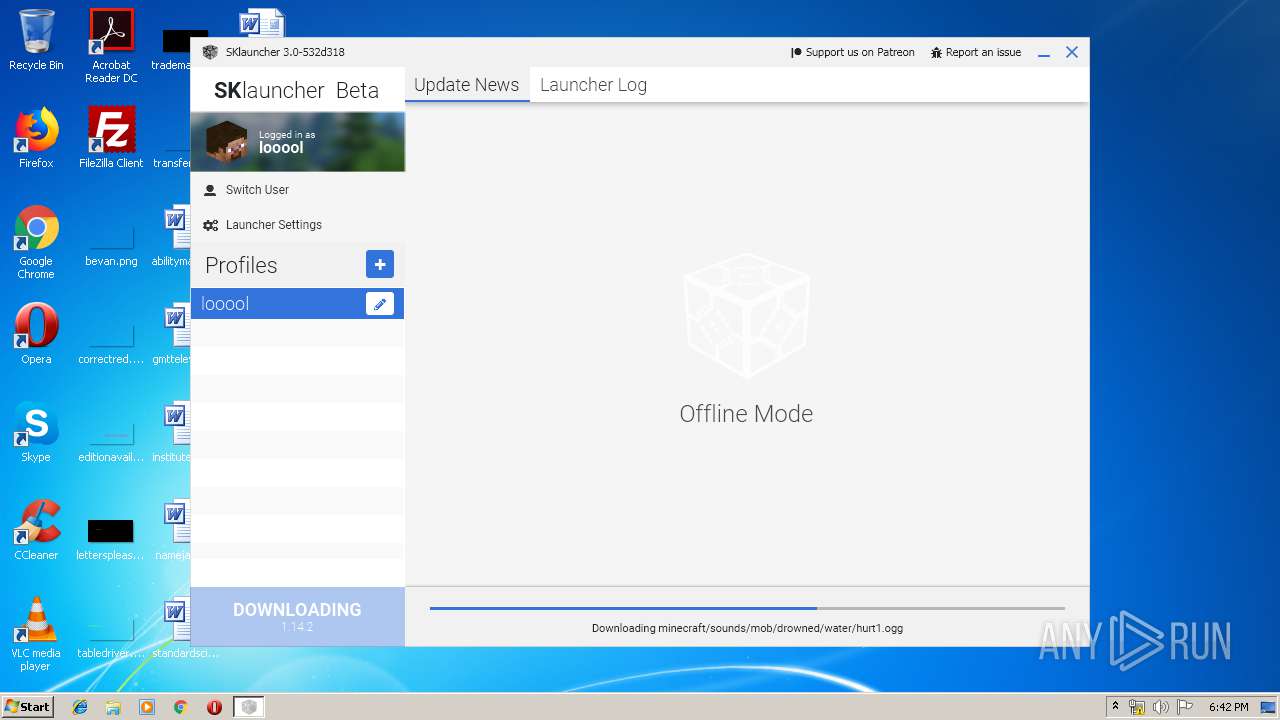
| download: | SKlauncher%203-beta.10.exe |
| Full analysis: | https://app.any.run/tasks/f882a55a-676b-40ac-b177-f8e859efcd43 |
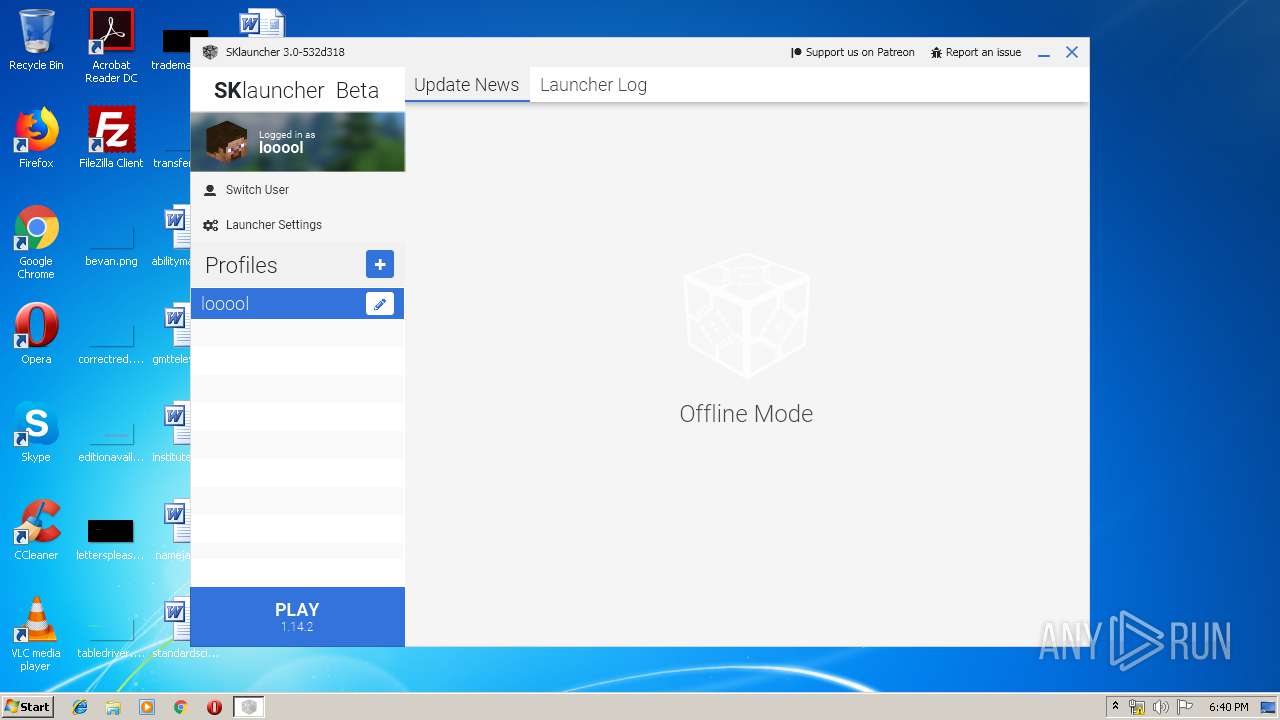
| Verdict: | Malicious activity |
| Analysis date: | June 06, 2019, 17:39:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 73D95BB002185D0BB147410F0B3B5405 |
| SHA1: | 71D1112E933E6D5D405676BB1A4C3E30B35EA23D |
| SHA256: | E464B30F6AFCD84ACD73CD6526F4E52E149DA55FB35054651338D91F2434F22F |
| SSDEEP: | 12288:qfAv6B8azBwdiLwsxAXEao3HDN8IrUm0xhhFUcQNb9+3MA35+N:Qk6+c2diFxYEh3jN8IAm0zheJ9+3VI |
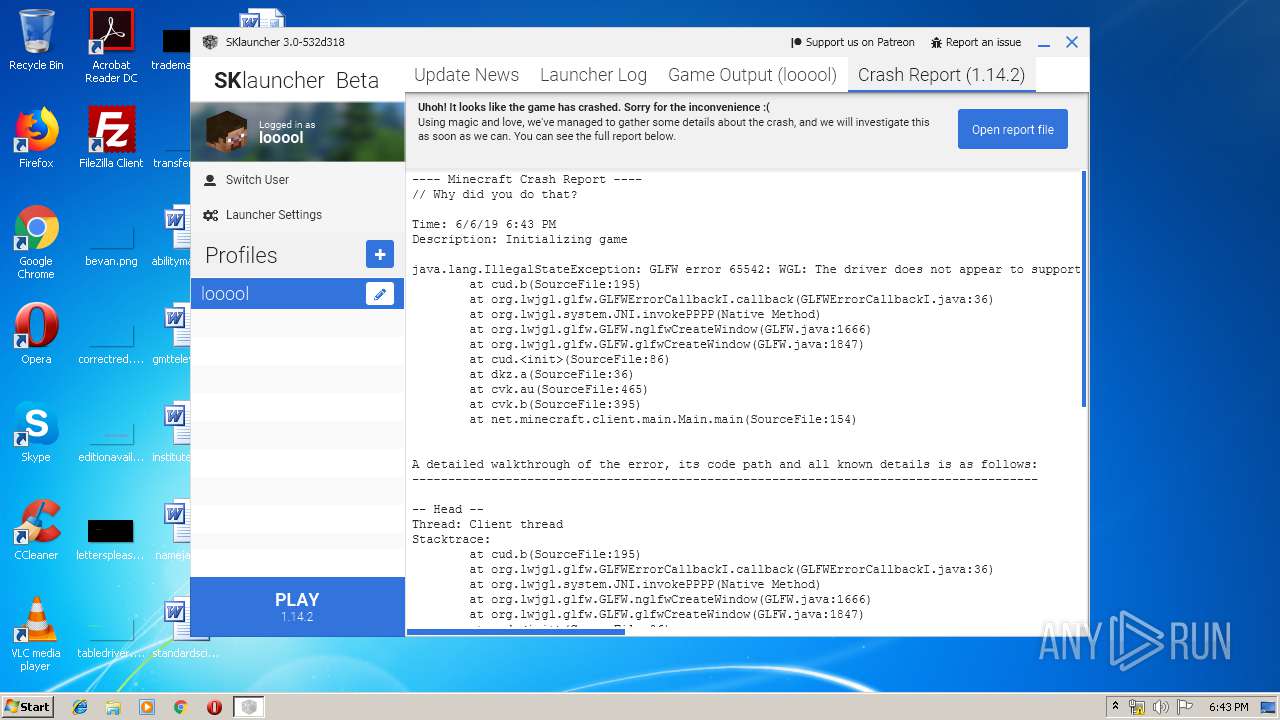
MALICIOUS
Application was dropped or rewritten from another process
- SKlauncher 3-beta.10.exe (PID: 2732)
Loads dropped or rewritten executable
- javaw.exe (PID: 636)
Uses SVCHOST.EXE for hidden code execution
- ba885337-a92c-43d3-a5a1-97cd057a1890.exe (PID: 1244)
SUSPICIOUS
Executable content was dropped or overwritten
- ba885337-a92c-43d3-a5a1-97cd057a1890.exe (PID: 1244)
- javaw.exe (PID: 3568)
Executes JAVA applets
- javaw.exe (PID: 3568)
- SKlauncher 3-beta.10.exe (PID: 2732)
Creates files in the user directory
- ba885337-a92c-43d3-a5a1-97cd057a1890.exe (PID: 1244)
- javaw.exe (PID: 636)
- javaw.exe (PID: 3568)
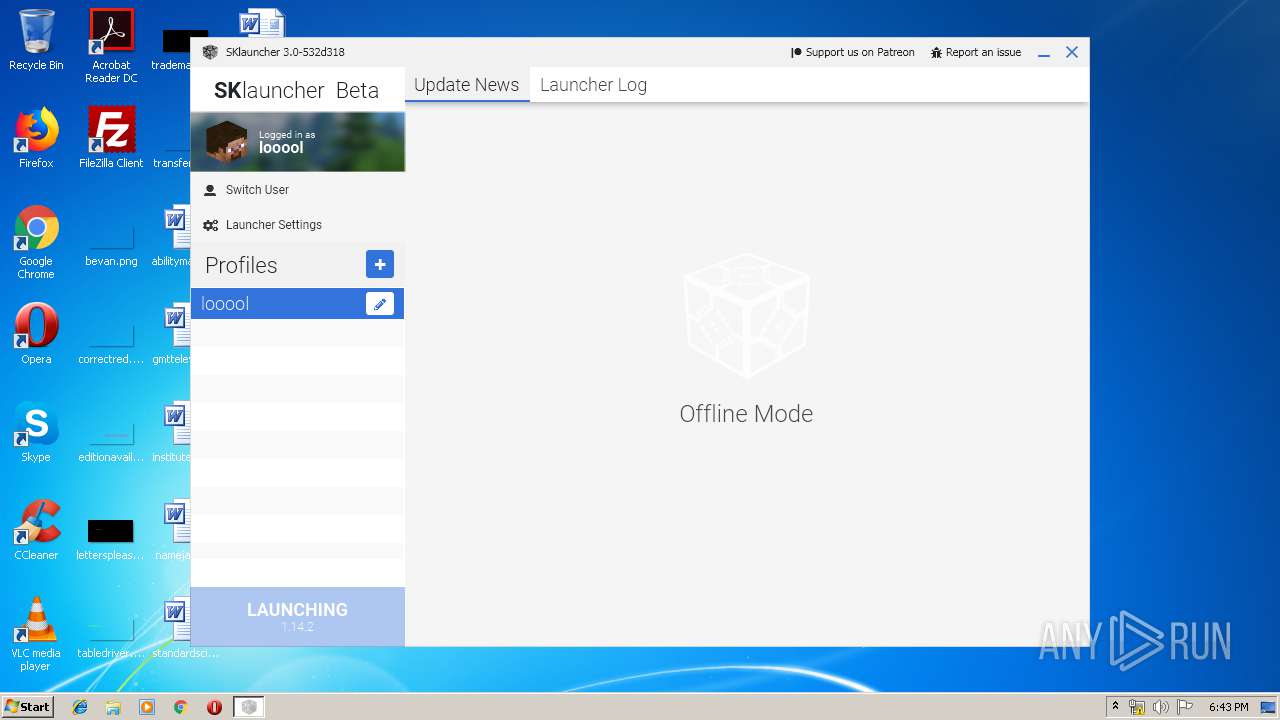
Application launched itself
- javaw.exe (PID: 3568)
INFO
Dropped object may contain Bitcoin addresses
- javaw.exe (PID: 3568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:30 20:01:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 251904 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d549 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Sep-2018 18:01:44 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 30-Sep-2018 18:01:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E924 | 0x0002EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69845 |
.rdata | 0x00030000 | 0x00009A8C | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13014 |
.data | 0x0003A000 | 0x000203A0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.23545 |
.gfids | 0x0005B000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.09308 |
.rsrc | 0x0005C000 | 0x000114DB | 0x00011600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.46298 |
.reloc | 0x0006E000 | 0x00001FDC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.67876 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.61341 | 2440 | UNKNOWN | English - United States | RT_ICON |
3 | 6.65371 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 6.30866 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 7.97926 | 34399 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
11 | 3.2036 | 1094 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
40
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 636 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -Xss1M -XX:+UnlockExperimentalVMOptions -XX:+UseG1GC -XX:G1NewSizePercent=20 -XX:G1ReservePercent=20 -XX:MaxGCPauseMillis=50 -XX:G1HeapRegionSize=16M -Xmx1024m -javaagent:C:\Users\admin\AppData\Roaming\.minecraft\sklauncher-fx.jar -XX:HeapDumpPath=MojangTricksIntelDriversForPerformance_javaw.exe_minecraft.exe.heapdump -Xss1M -Djava.library.path=C:\Users\admin\AppData\Roaming\.minecraft\versions\1.14.2\1.14.2-natives-1377056572058 -Dminecraft.launcher.brand=java-minecraft-launcher -Dminecraft.launcher.version=3.0-532d318 -cp C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\patchy\1.1\patchy-1.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\oshi-project\oshi-core\1.1\oshi-core-1.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\java\dev\jna\jna\4.4.0\jna-4.4.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\java\dev\jna\platform\3.4.0\platform-3.4.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\ibm\icu\icu4j-core-mojang\51.2\icu4j-core-mojang-51.2.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\javabridge\1.0.22\javabridge-1.0.22.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\sf\jopt-simple\jopt-simple\5.0.3\jopt-simple-5.0.3.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\io\netty\netty-all\4.1.25.Final\netty-all-4.1.25.Final.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\google\guava\guava\21.0\guava-21.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\apache\commons\commons-lang3\3.5\commons-lang3-3.5.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\commons-io\commons-io\2.5\commons-io-2.5.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\commons-codec\commons-codec\1.10\commons-codec-1.10.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\java\jinput\jinput\2.0.5\jinput-2.0.5.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\java\jutils\jutils\1.0.0\jutils-1.0.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\brigadier\1.0.17\brigadier-1.0.17.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\datafixerupper\2.0.24\datafixerupper-2.0.24.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\google\code\gson\gson\2.8.0\gson-2.8.0.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\authlib\1.5.25\authlib-1.5.25.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\apache\commons\commons-compress\1.8.1\commons-compress-1.8.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\apache\httpcomponents\httpclient\4.3.3\httpclient-4.3.3.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\commons-logging\commons-logging\1.1.3\commons-logging-1.1.3.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\apache\httpcomponents\httpcore\4.3.2\httpcore-4.3.2.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\it\unimi\dsi\fastutil\8.2.1\fastutil-8.2.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\apache\logging\log4j\log4j-api\2.8.1\log4j-api-2.8.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\apache\logging\log4j\log4j-core\2.8.1\log4j-core-2.8.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\realms\1.14.16\realms-1.14.16.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl\3.2.1\lwjgl-3.2.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl-jemalloc\3.2.1\lwjgl-jemalloc-3.2.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl-openal\3.2.1\lwjgl-openal-3.2.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl-opengl\3.2.1\lwjgl-opengl-3.2.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl-glfw\3.2.1\lwjgl-glfw-3.2.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\org\lwjgl\lwjgl-stb\3.2.1\lwjgl-stb-3.2.1.jar;C:\Users\admin\AppData\Roaming\.minecraft\libraries\com\mojang\text2speech\1.11.3\text2speech-1.11.3.jar;C:\Users\admin\AppData\Roaming\.minecraft\versions\1.14.2\1.14.2.jar net.minecraft.client.main.Main --username looool --version 1.14.2 --gameDir C:\Users\admin\AppData\Roaming\.minecraft --assetsDir C:\Users\admin\AppData\Roaming\.minecraft\assets --assetIndex 1.14 --uuid d24ec912e40f3db587208c7f90f8553c --accessToken db11bdb5a3a4dd970e39bbce3244cb2a --userType mojang --versionType release | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 4294967295 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1244 | "C:\Users\admin\AppData\Local\Temp\ba885337-a92c-43d3-a5a1-97cd057a1890.exe" | C:\Users\admin\AppData\Local\Temp\ba885337-a92c-43d3-a5a1-97cd057a1890.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2608 | "C:\Windows\System32\svchost.exe" | C:\Windows\System32\svchost.exe | — | ba885337-a92c-43d3-a5a1-97cd057a1890.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2732 | "C:\Users\admin\AppData\Roaming\SKlauncher 3-beta.10.exe" | C:\Users\admin\AppData\Roaming\SKlauncher 3-beta.10.exe | — | ba885337-a92c-43d3-a5a1-97cd057a1890.exe | |||||||||||
User: admin Company: Mojang Integrity Level: MEDIUM Description: The Minecraft Launcher Exit code: 0 Version: 3.0.beta.10 Modules
| |||||||||||||||
| 3568 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -Xms32m -Xmx256m -jar "C:\Users\admin\AppData\Roaming\SKlauncher 3-beta.10.exe" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | SKlauncher 3-beta.10.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3808 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -version | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
414
Read events
403
Write events
11
Delete events
0
Modification events
| (PID) Process: | (1244) ba885337-a92c-43d3-a5a1-97cd057a1890.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1244) ba885337-a92c-43d3-a5a1-97cd057a1890.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3568) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (636) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\JAVAW.EXE56FDF6070002EC40 |
| Operation: | write | Name: | Name |
Value: JAVAW.EXE | |||
| (PID) Process: | (636) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\JAVAW.EXE56FDF6070002EC40 |
| Operation: | write | Name: | UsesMapper |
Value: 00000000 | |||
| (PID) Process: | (636) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: JAVAW.EXE | |||
| (PID) Process: | (636) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Id |
Value: JAVAW.EXE56FDF6070002EC40 | |||
| (PID) Process: | (636) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | Version |
Value: 00080000 | |||
| (PID) Process: | (636) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\DirectInput\MostRecentApplication |
| Operation: | write | Name: | MostRecentStart |
Value: 48EA855B8F1CD501 | |||
Executable files
34
Suspicious files
26
Text files
282
Unknown types
1 770
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3568 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher\sklauncher.pack | — | |
MD5:— | SHA256:— | |||
| 3568 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF5363387288642460446.tmp | ttf | |
MD5:— | SHA256:— | |||
| 3568 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher\sklauncher.json | text | |
MD5:— | SHA256:— | |||
| 3568 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3568 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF571374871129610811.tmp | ttf | |
MD5:— | SHA256:— | |||
| 3568 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher\sklauncher.data | text | |
MD5:— | SHA256:— | |||
| 1244 | ba885337-a92c-43d3-a5a1-97cd057a1890.exe | C:\Users\admin\AppData\Roaming\Minecraft.exe | executable | |
MD5:— | SHA256:— | |||
| 1244 | ba885337-a92c-43d3-a5a1-97cd057a1890.exe | C:\Users\admin\AppData\Roaming\SKlauncher 3-beta.10.exe | executable | |
MD5:— | SHA256:— | |||
| 3568 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF3893812523694762302.tmp | ttf | |
MD5:— | SHA256:— | |||
| 3568 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher-fx.jar | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
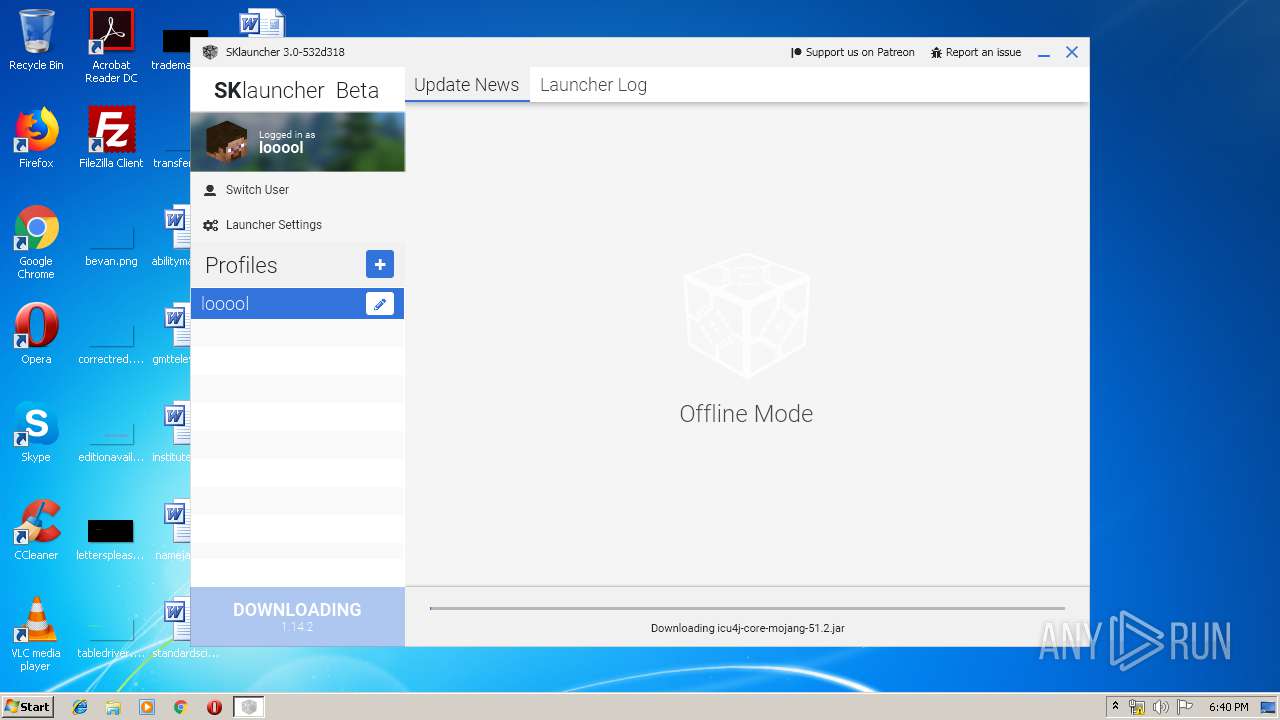
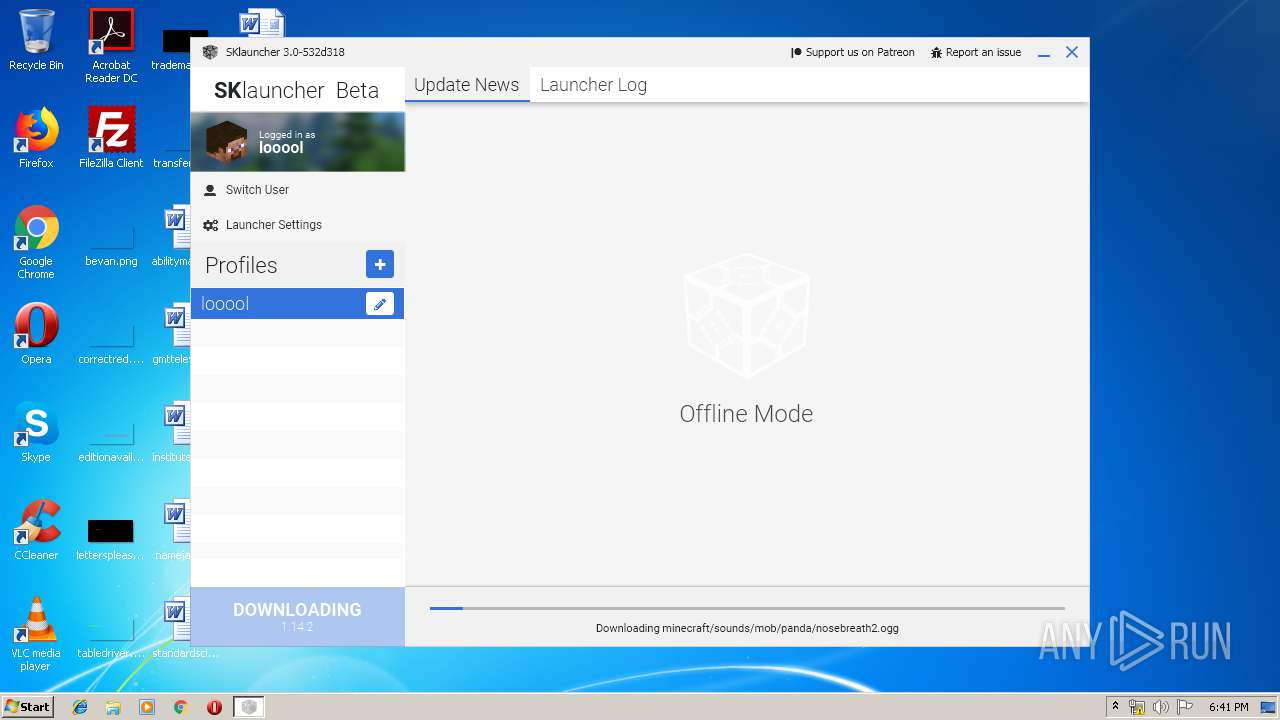
HTTP(S) requests
2 017
TCP/UDP connections
45
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
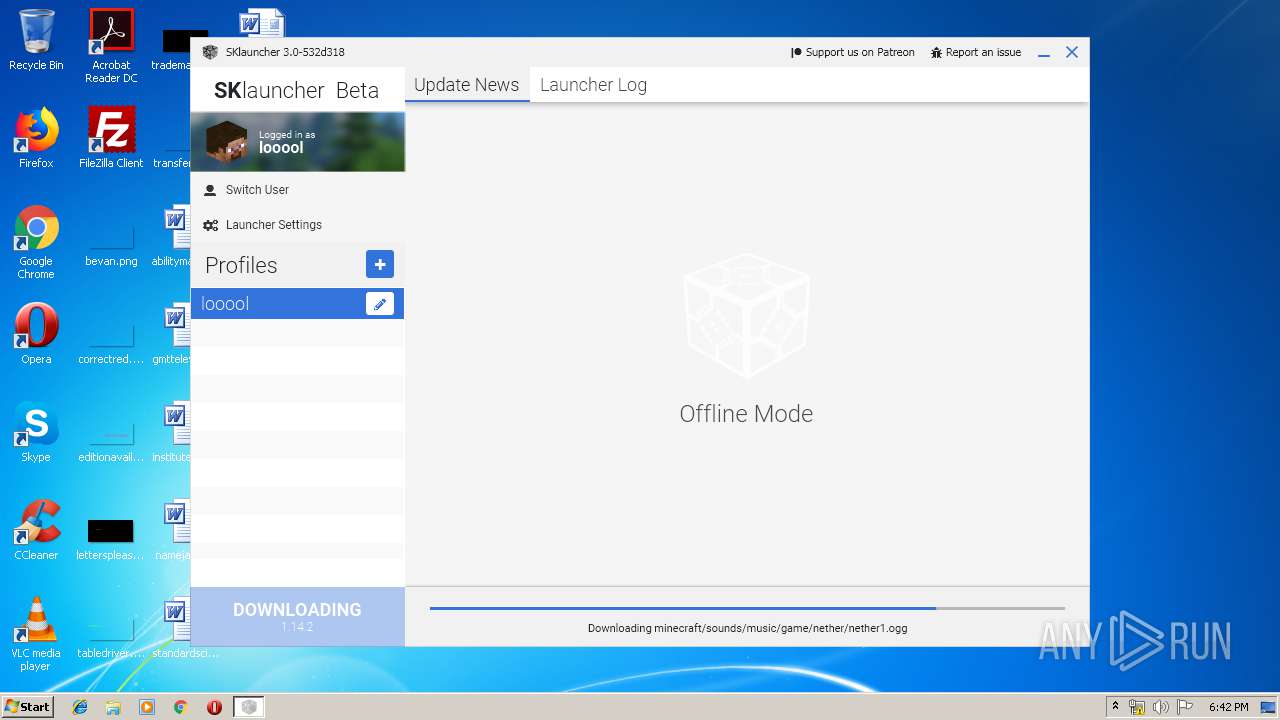
3568 | javaw.exe | GET | 200 | 104.31.74.141:80 | http://s1.hapel.pl/launcher/3.0/data/ | US | text | 655 b | suspicious |
3568 | javaw.exe | GET | 200 | 104.31.81.246:80 | http://api.skmedix.pl/launcher/3.0/ | US | text | 151 b | malicious |
3568 | javaw.exe | GET | 200 | 104.31.74.141:80 | http://s1.hapel.pl/launcher/3.0/data/ | US | text | 655 b | suspicious |
3568 | javaw.exe | GET | 200 | 104.31.81.246:80 | http://api.skmedix.pl/launcher/3.0/ | US | text | 151 b | malicious |
3568 | javaw.exe | GET | 301 | 104.31.74.141:80 | http://s1.hapel.pl/launcher/3.0/data | US | html | 245 b | suspicious |
3568 | javaw.exe | GET | 301 | 104.31.74.141:80 | http://s1.hapel.pl/launcher/3.0/data | US | html | 245 b | suspicious |
3568 | javaw.exe | GET | 200 | 143.204.15.60:80 | http://resources.download.minecraft.net/e7/e7e8d393fc03a476227890e9ec9319dcc4b400ea | US | ogg | 10.8 Kb | shared |
3568 | javaw.exe | GET | 200 | 143.204.15.60:80 | http://resources.download.minecraft.net/6d/6dd3ec952a2f8815c4bb027c9bea3879a5fa835f | US | text | 286 Kb | shared |
3568 | javaw.exe | GET | 200 | 104.31.74.141:80 | http://s1.hapel.pl/launcher/3.0/files/stable/launcher.comp.pack | US | xz | 7.73 Mb | suspicious |
3568 | javaw.exe | GET | 200 | 143.204.15.60:80 | http://resources.download.minecraft.net/9a/9abf29bfb81edc9796c62d96610f363b9d3c1697 | US | text | 14.7 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3568 | javaw.exe | 104.31.81.246:443 | api.skmedix.pl | Cloudflare Inc | US | shared |
3568 | javaw.exe | 104.31.81.246:80 | api.skmedix.pl | Cloudflare Inc | US | shared |
3568 | javaw.exe | 104.31.74.141:80 | s1.hapel.pl | Cloudflare Inc | US | shared |
— | — | 104.31.74.141:443 | s1.hapel.pl | Cloudflare Inc | US | shared |
3568 | javaw.exe | 143.204.2.134:443 | launchermeta.mojang.com | — | US | unknown |
3568 | javaw.exe | 143.204.14.81:443 | libraries.minecraft.net | — | US | unknown |
3568 | javaw.exe | 143.204.15.60:80 | resources.download.minecraft.net | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.skmedix.pl |
| malicious |
s1.hapel.pl |
| suspicious |
skmedix.pl |
| malicious |
launchermeta.mojang.com |
| whitelisted |
libraries.minecraft.net |
| shared |
launcher.mojang.com |
| whitelisted |
resources.download.minecraft.net |
| shared |