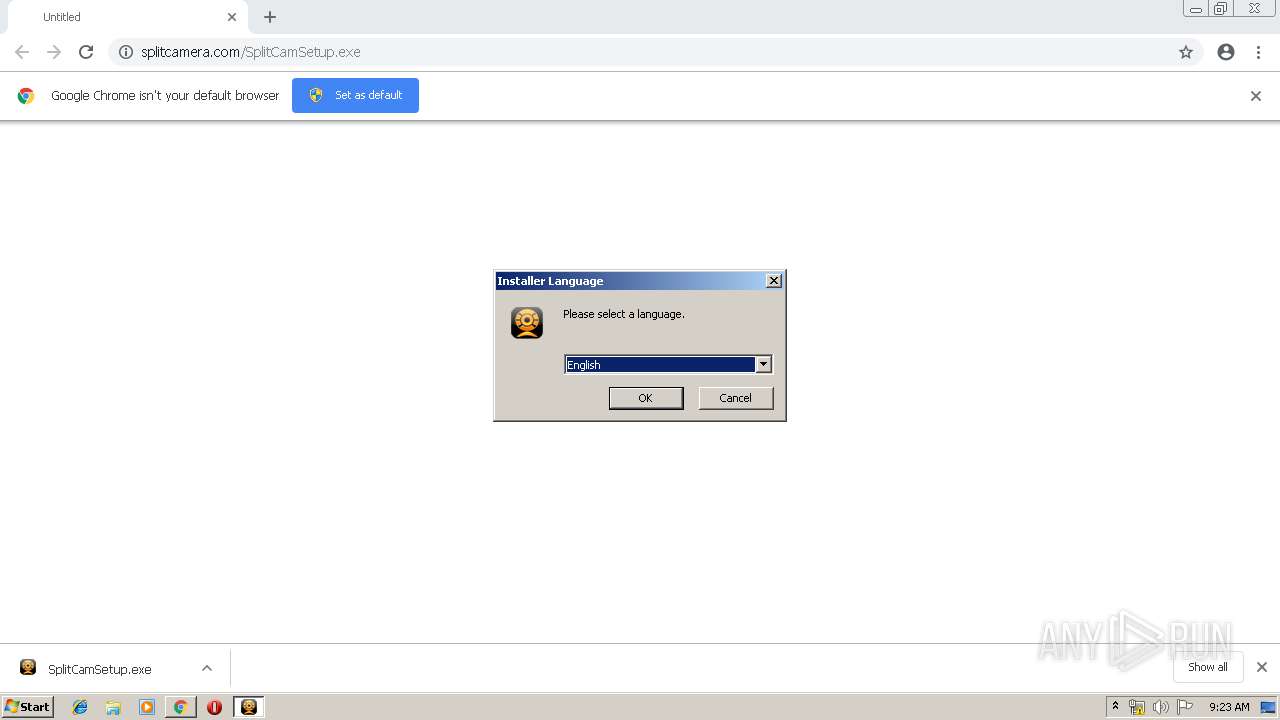
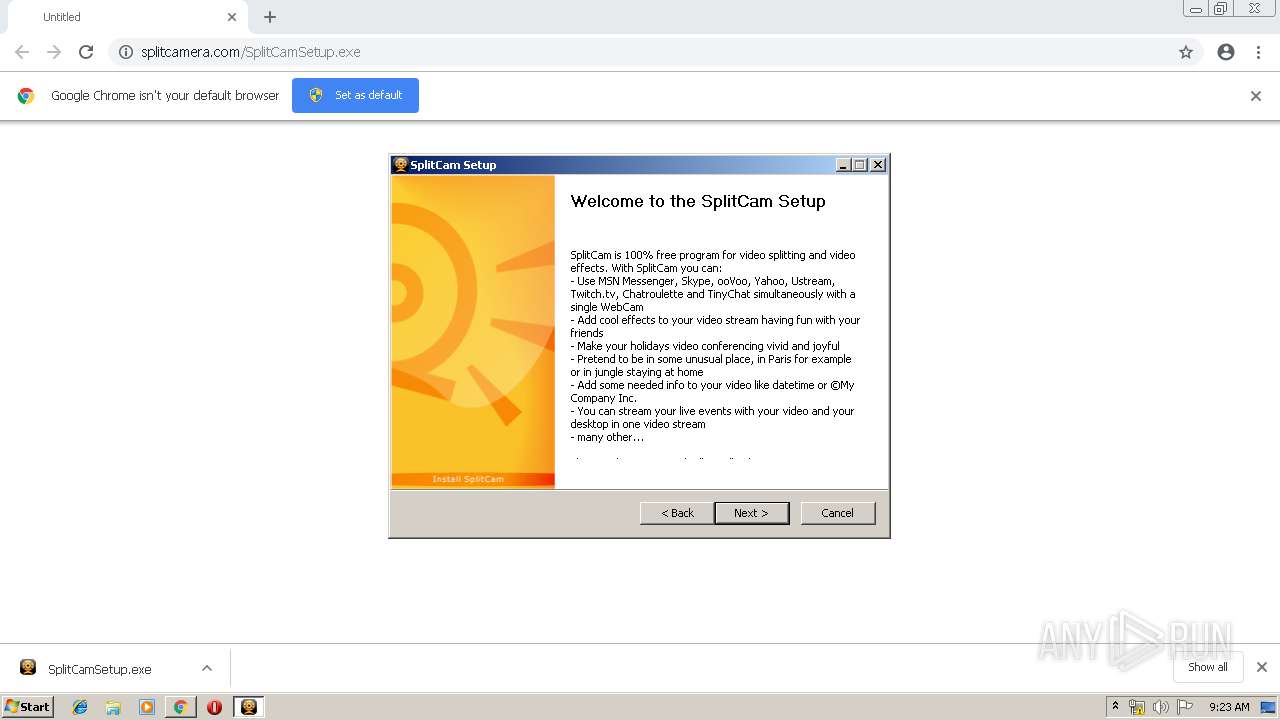
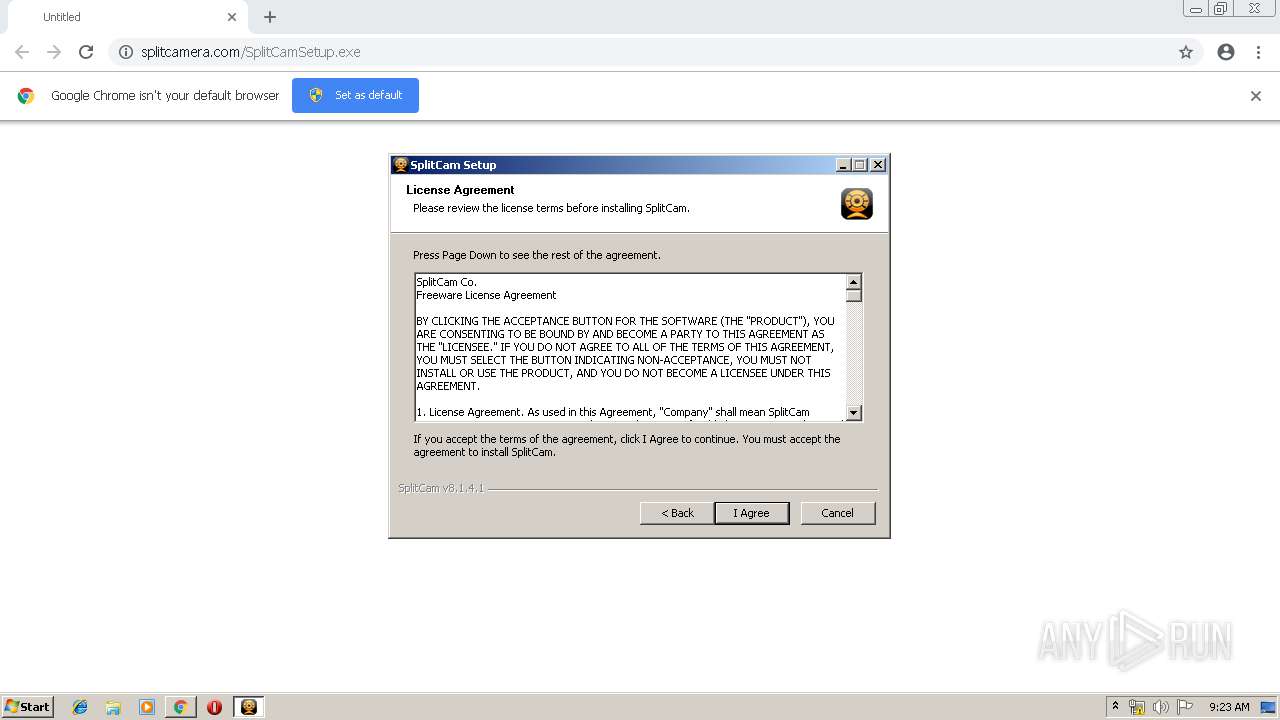
| URL: | http://splitcamera.com/SplitCamSetup.exe |
| Full analysis: | https://app.any.run/tasks/54c76758-6921-4439-959d-09b84f4aa8f2 |
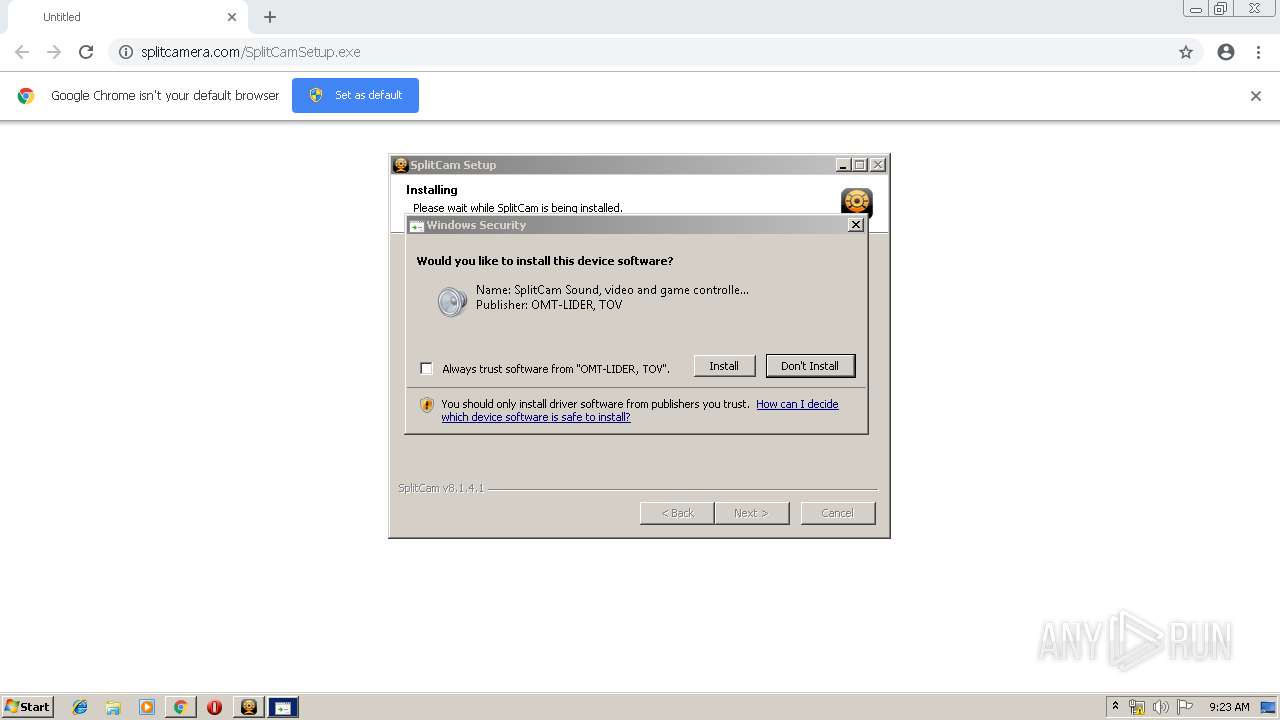
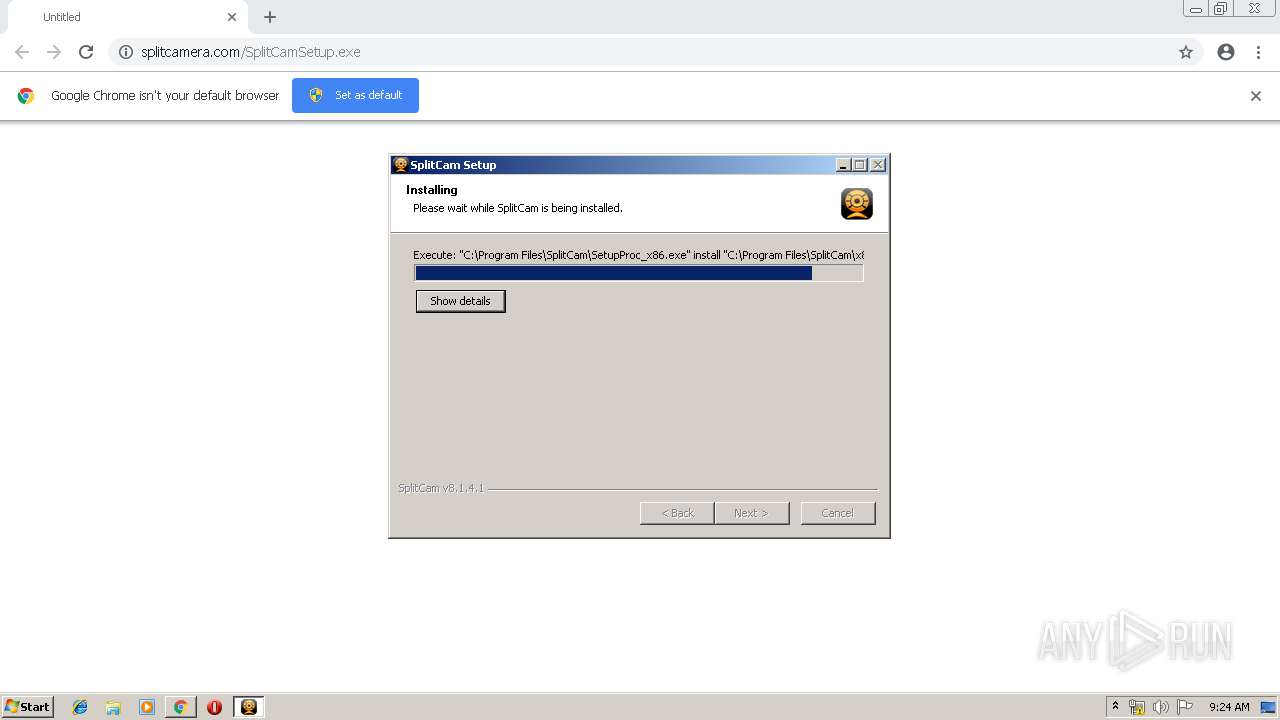
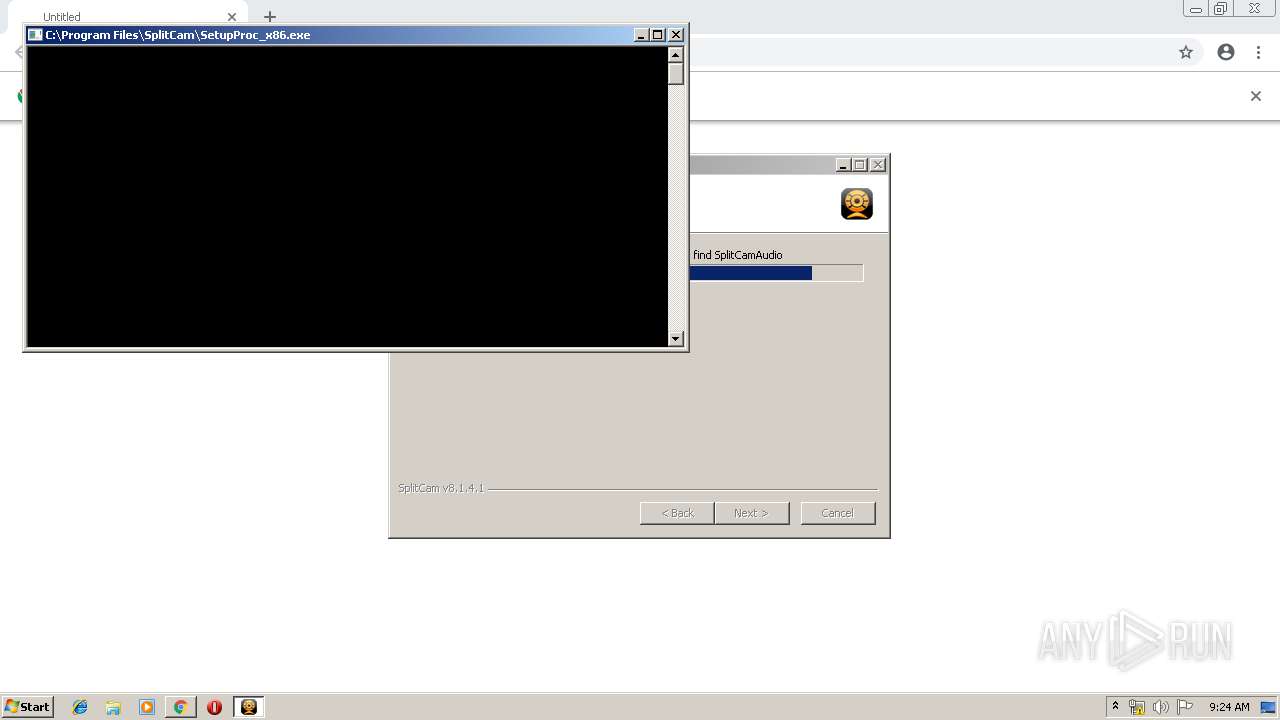
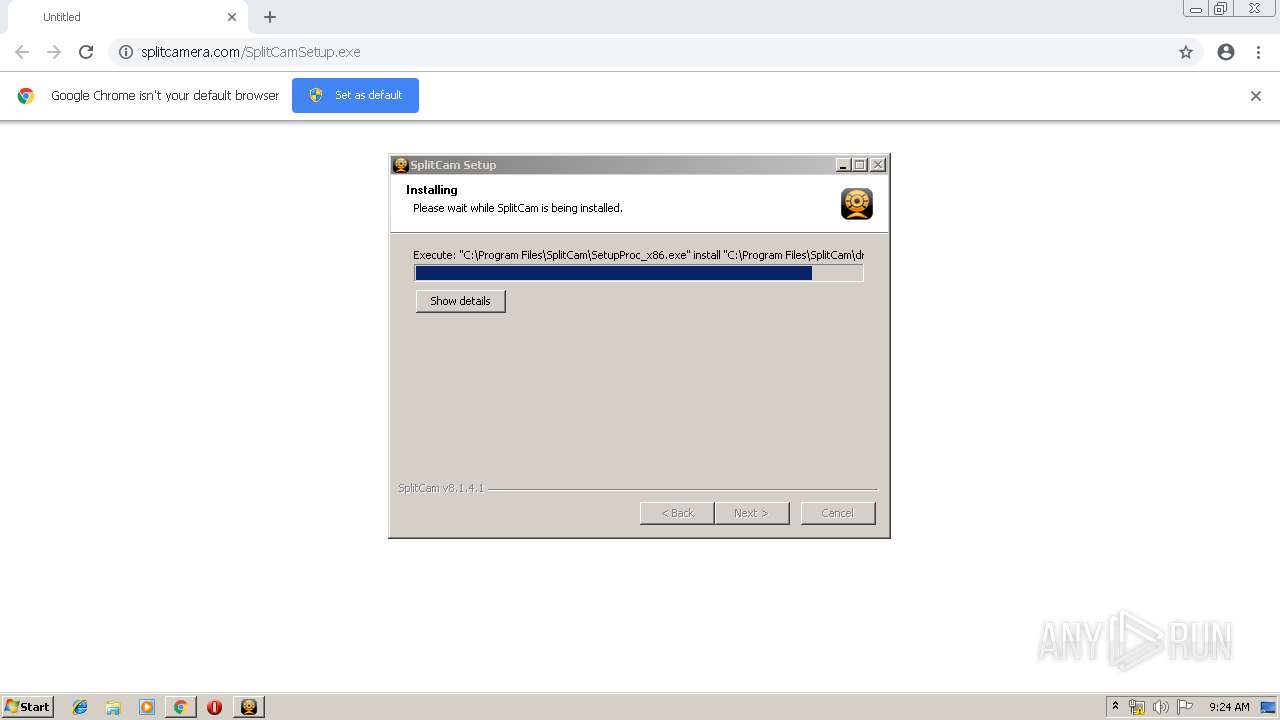
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2019, 09:22:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CCFDA7CE55F8CBEFD5D02338BA0A87B8 |
| SHA1: | 7F53924F6FF21C6B6E4855EF1527DA1C4BC05698 |
| SHA256: | E452617F3F61D64F75352E679B05C8629FC4568ABA1ED23E63C2287D9436EE3B |
| SSDEEP: | 3:N1KNVSTOyGaVRlA:CuOMlA |
MALICIOUS
Loads dropped or rewritten executable
- SplitCamSetup.exe (PID: 2504)
- regsvr32.exe (PID: 2492)
- regsvr32.exe (PID: 3524)
- regsvr32.exe (PID: 3752)
- regsvr32.exe (PID: 2376)
- SplitCamService.exe (PID: 3284)
- SplitCam.exe (PID: 2980)
Application was dropped or rewritten from another process
- SplitCamSetup.exe (PID: 2504)
- SplitCamSetup.exe (PID: 3648)
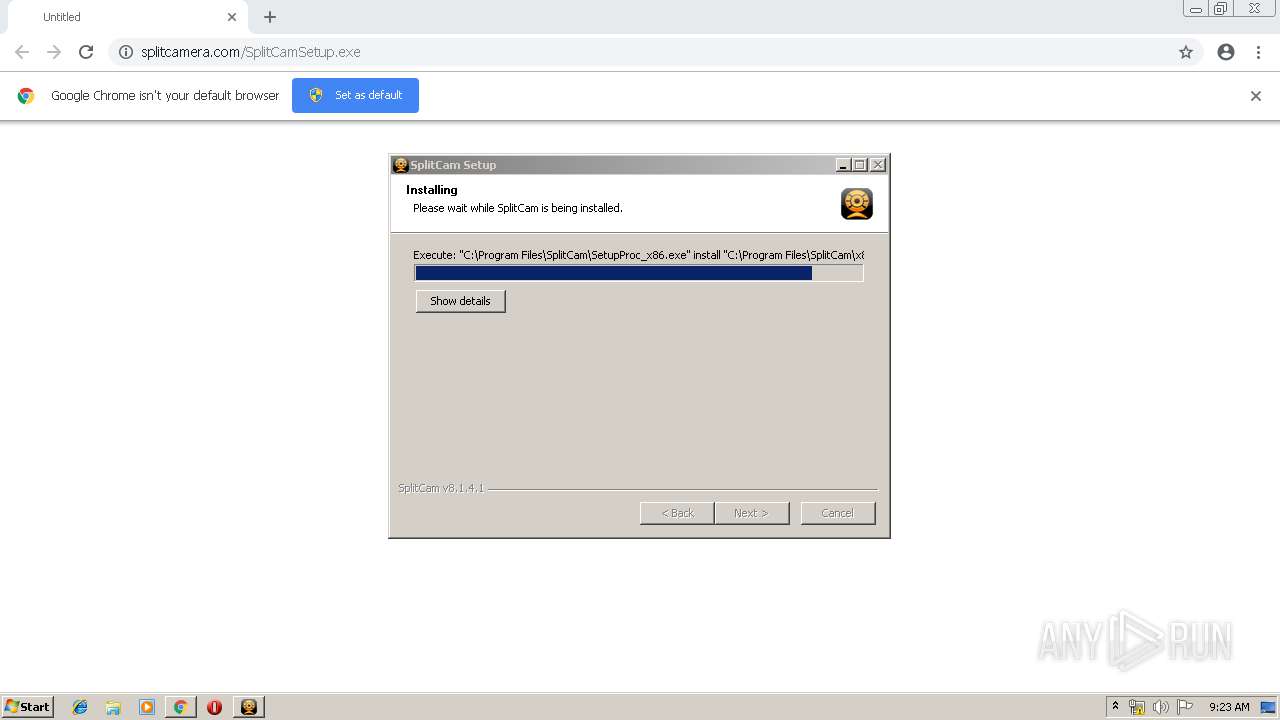
- SetupProc_x86.exe (PID: 3384)
- SetupProc_x86.exe (PID: 2876)
- SetupProc_x86.exe (PID: 2348)
- SplitCamService.exe (PID: 3284)
- SetupProc_x86.exe (PID: 3604)
- nsDB0D.tmp (PID: 3500)
- SplitCam.exe (PID: 2980)
- nsDB7B.tmp (PID: 3748)
- nsDBF9.tmp (PID: 4012)
- SetupProc_x86.exe (PID: 1464)
Changes settings of System certificates
- SetupProc_x86.exe (PID: 2876)
- SplitCam.exe (PID: 2980)
Registers / Runs the DLL via REGSVR32.EXE
- SplitCamSetup.exe (PID: 2504)
Changes the autorun value in the registry
- SplitCamSetup.exe (PID: 2504)
- SplitCam.exe (PID: 2980)
SUSPICIOUS
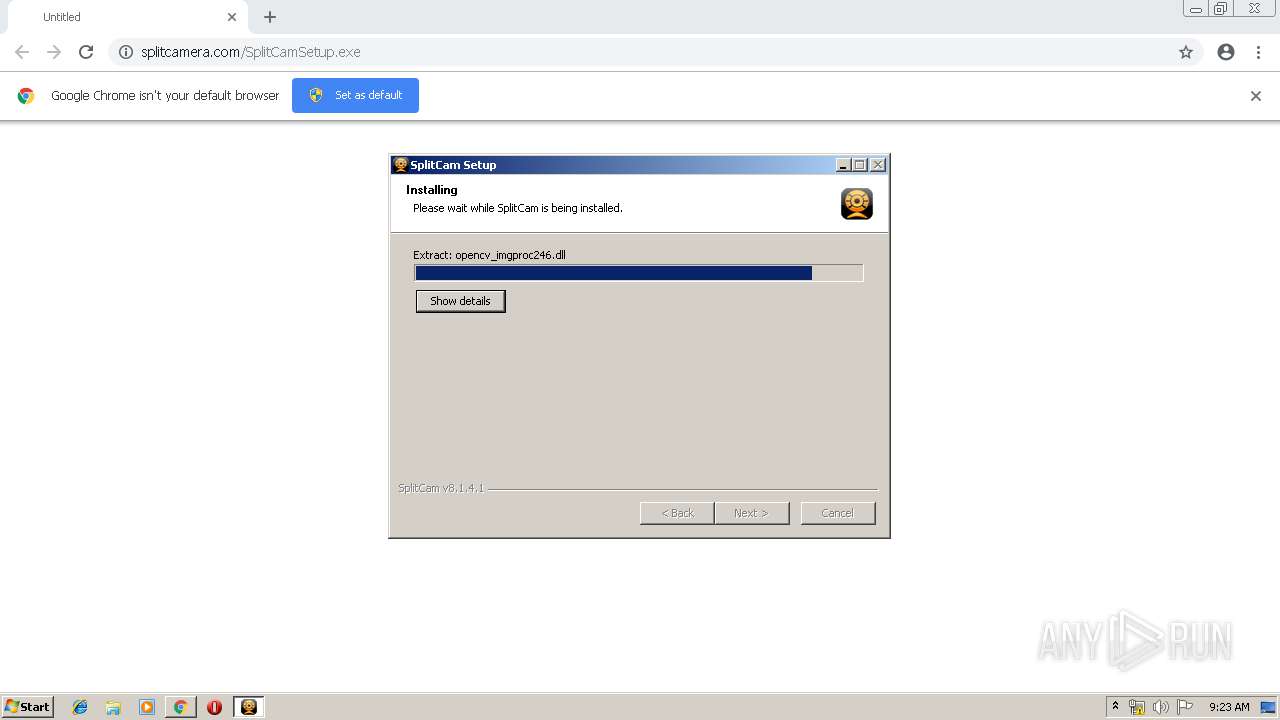
Executable content was dropped or overwritten
- chrome.exe (PID: 2952)
- msiexec.exe (PID: 936)
- SplitCamSetup.exe (PID: 2504)
- SetupProc_x86.exe (PID: 2876)
- DrvInst.exe (PID: 3376)
- DrvInst.exe (PID: 2756)
- DrvInst.exe (PID: 1864)
Creates a software uninstall entry
- SplitCamSetup.exe (PID: 2504)
Starts Microsoft Installer
- SplitCamSetup.exe (PID: 2504)
Removes files from Windows directory
- msiexec.exe (PID: 936)
- DrvInst.exe (PID: 3376)
- DrvInst.exe (PID: 2756)
- DrvInst.exe (PID: 352)
- DrvInst.exe (PID: 1864)
Creates files in the Windows directory
- SetupProc_x86.exe (PID: 2876)
- msiexec.exe (PID: 936)
- DrvInst.exe (PID: 3376)
- DrvInst.exe (PID: 2756)
- DrvInst.exe (PID: 1864)
- DrvInst.exe (PID: 352)
Adds / modifies Windows certificates
- SetupProc_x86.exe (PID: 2876)
- SplitCam.exe (PID: 2980)
Creates files in the driver directory
- DrvInst.exe (PID: 3376)
- DrvInst.exe (PID: 2756)
- DrvInst.exe (PID: 1864)
- DrvInst.exe (PID: 352)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 3376)
Searches for installed software
- DrvInst.exe (PID: 3376)
Starts SC.EXE for service management
- nsDB7B.tmp (PID: 3748)
- nsDBF9.tmp (PID: 4012)
Starts application with an unusual extension
- SplitCamSetup.exe (PID: 2504)
Reads internet explorer settings
- SplitCam.exe (PID: 2980)
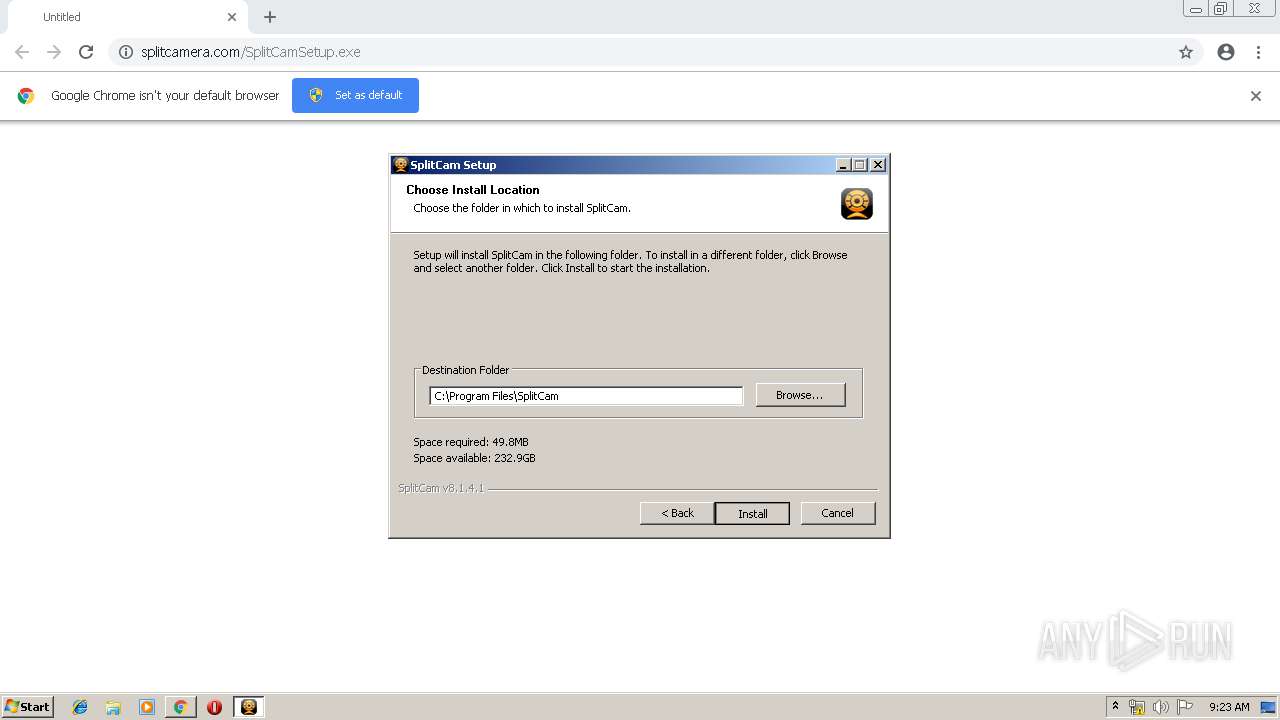
Creates files in the program directory
- SplitCamSetup.exe (PID: 2504)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2952)
Creates files in the user directory
- SplitCam.exe (PID: 2980)
- SplitCamSetup.exe (PID: 2504)
INFO
Application launched itself
- chrome.exe (PID: 2952)
- msiexec.exe (PID: 936)
Dropped object may contain Bitcoin addresses
- SplitCamSetup.exe (PID: 2504)
Creates a software uninstall entry
- msiexec.exe (PID: 936)
Creates files in the program directory
- msiexec.exe (PID: 936)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1668)
Reads settings of System Certificates
- SplitCam.exe (PID: 2980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
46
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,5334696401984182156,7162549936702466436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=246547932283713955 --mojo-platform-channel-handle=3616 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 352 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{7d008805-fef2-3b99-4105-754c4f888505}\splitcamaudio.inf" "0" "6512f2603" "000005C4" "WinSta0\Default" "00000064" "208" "c:\program files\splitcam\drvpkg\win7" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 936 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1340 | sc start SpliCamService | C:\Windows\system32\sc.exe | — | nsDBF9.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1464 | "C:\Program Files\SplitCam\SetupProc_x86.exe" find splitcam_hd_driver | C:\Program Files\SplitCam\SetupProc_x86.exe | — | SplitCamSetup.exe | |||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 4 Version: 6.1.7600.16385 built by: WinDDK Modules
| |||||||||||||||
| 1668 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1864 | DrvInst.exe "2" "211" "ROOT\MEDIA\0001" "C:\Windows\INF\oem5.inf" "splitcamaudio.inf:MicrosoftDS.NT:SCVAD_Simple:7.0.1000.6:splitcamaudio" "6512f2603" "000005C4" "000005E8" "000005E4" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,5334696401984182156,7162549936702466436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14442776708542984664 --mojo-platform-channel-handle=3688 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,5334696401984182156,7162549936702466436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7475644128857316070 --mojo-platform-channel-handle=1808 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,5334696401984182156,7162549936702466436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3825452102402672732 --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
11 934
Read events
10 359
Write events
1 534
Delete events
41
Modification events
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2952-13197720152448875 |
Value: 259 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2952) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
101
Suspicious files
118
Text files
309
Unknown types
1 188
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\140afe5e-f9d9-4742-9958-24fddb1d6803.tmp | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2096 | chrome.exe | GET | — | 104.27.171.192:80 | http://splitcamera.com/SplitCamSetup.exe | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2096 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 104.27.171.192:80 | splitcamera.com | Cloudflare Inc | US | shared |
2096 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2096 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
splitcamera.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2096 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |