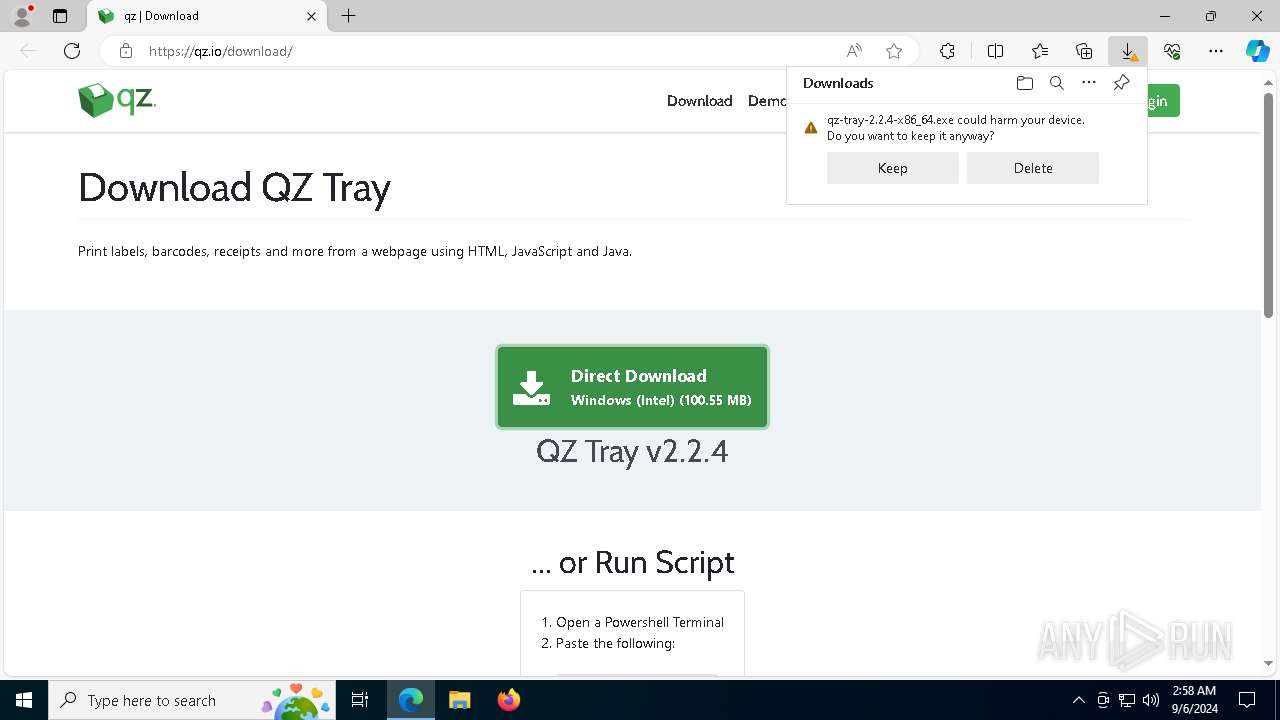
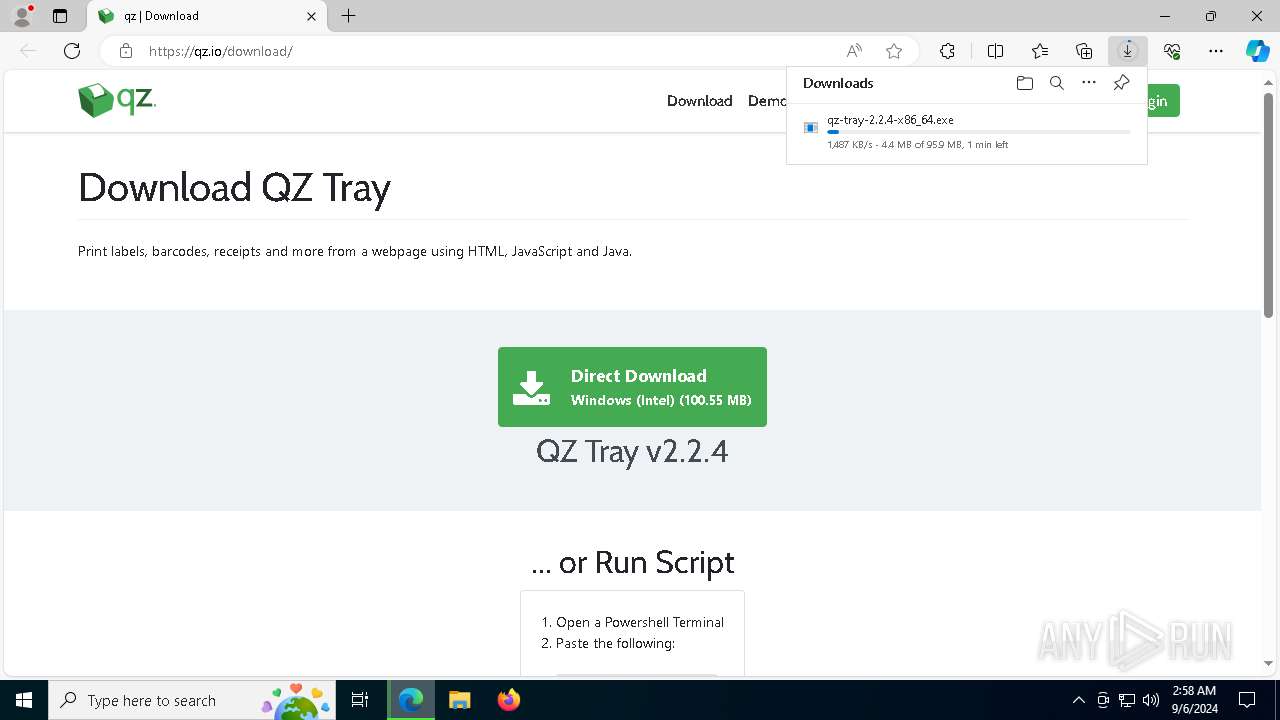
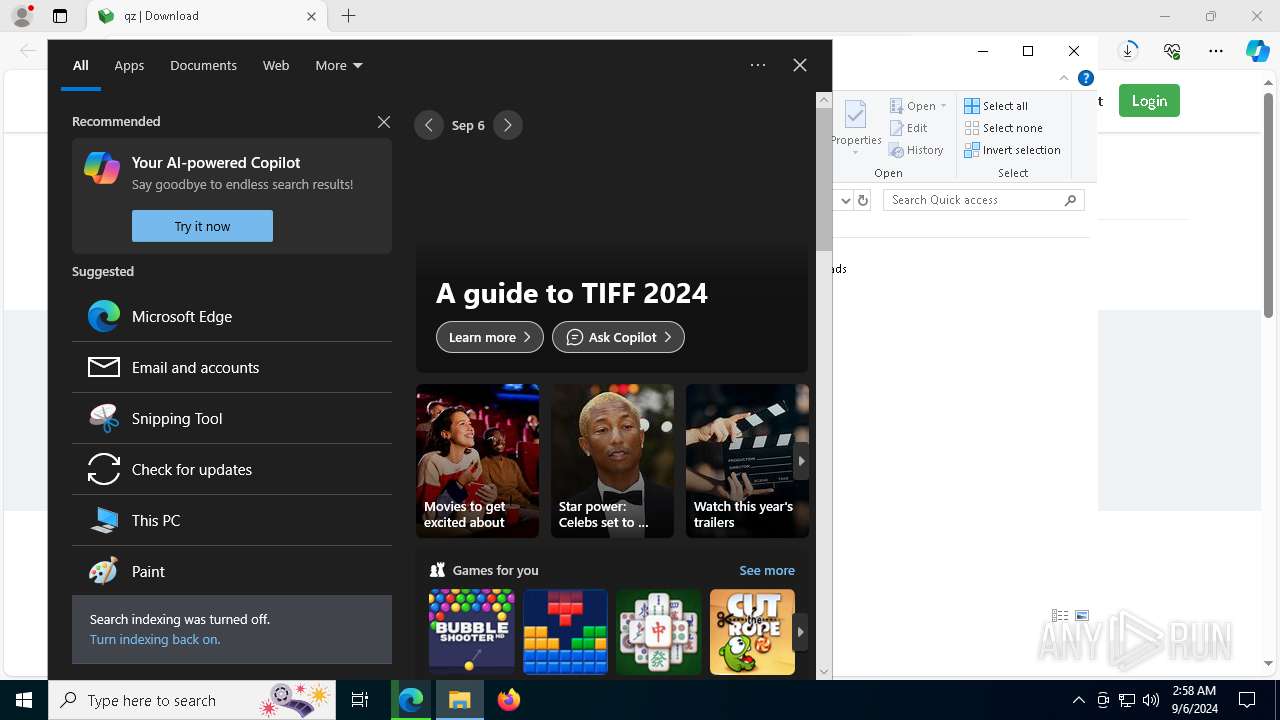
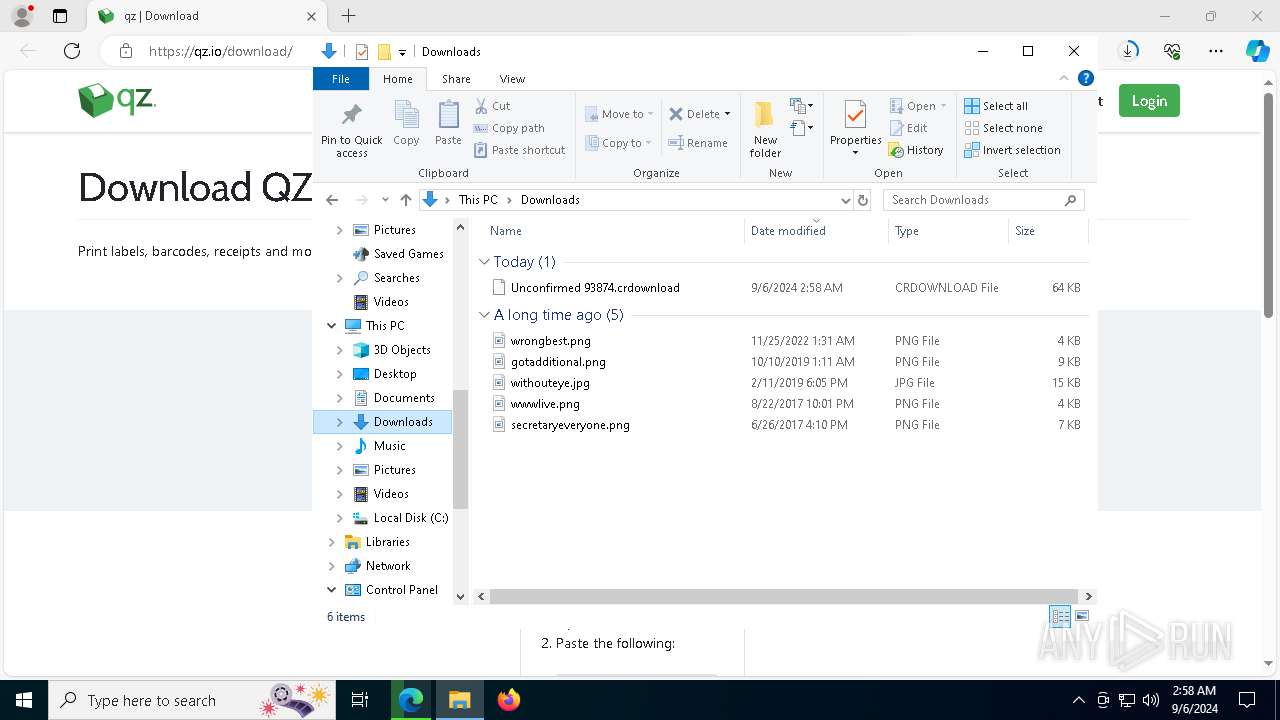
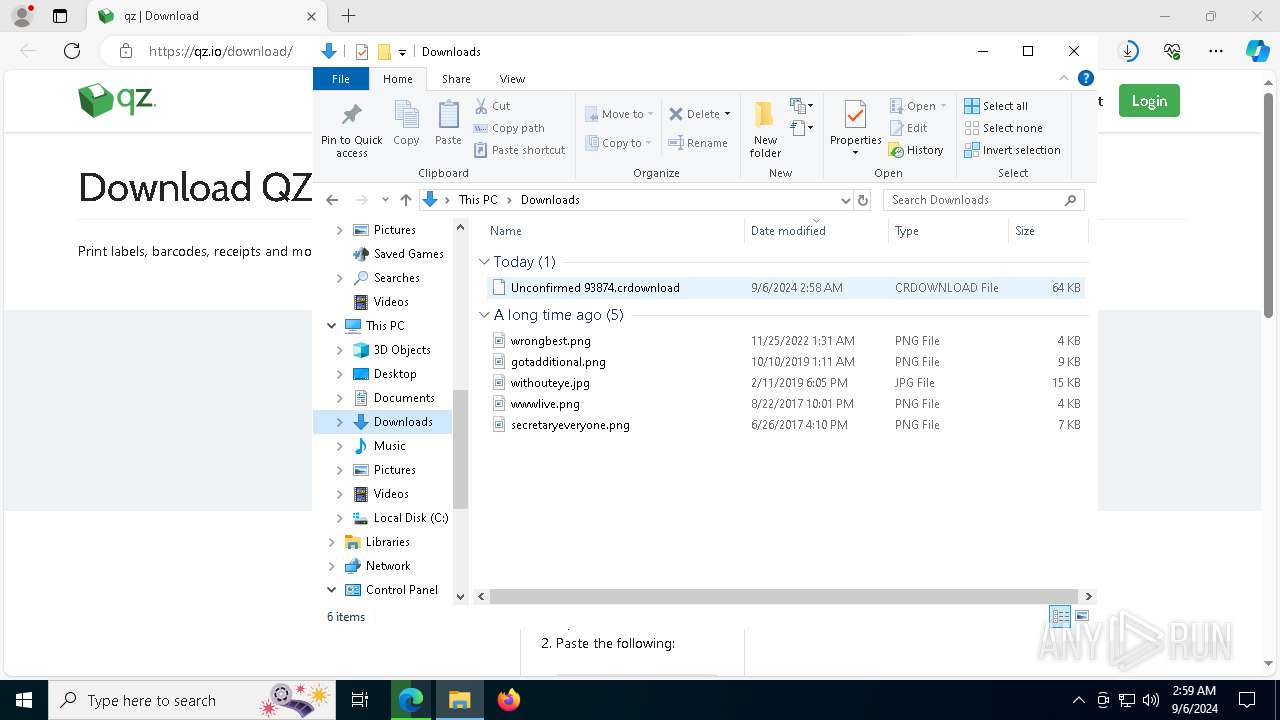
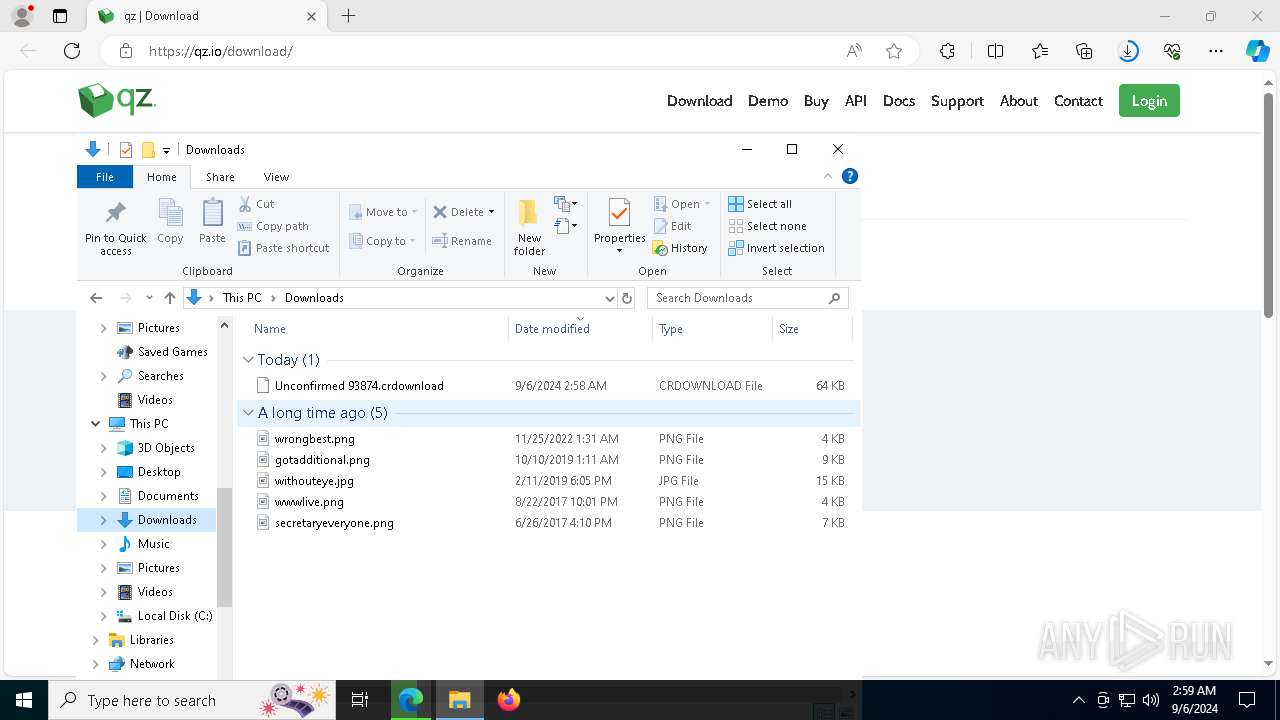
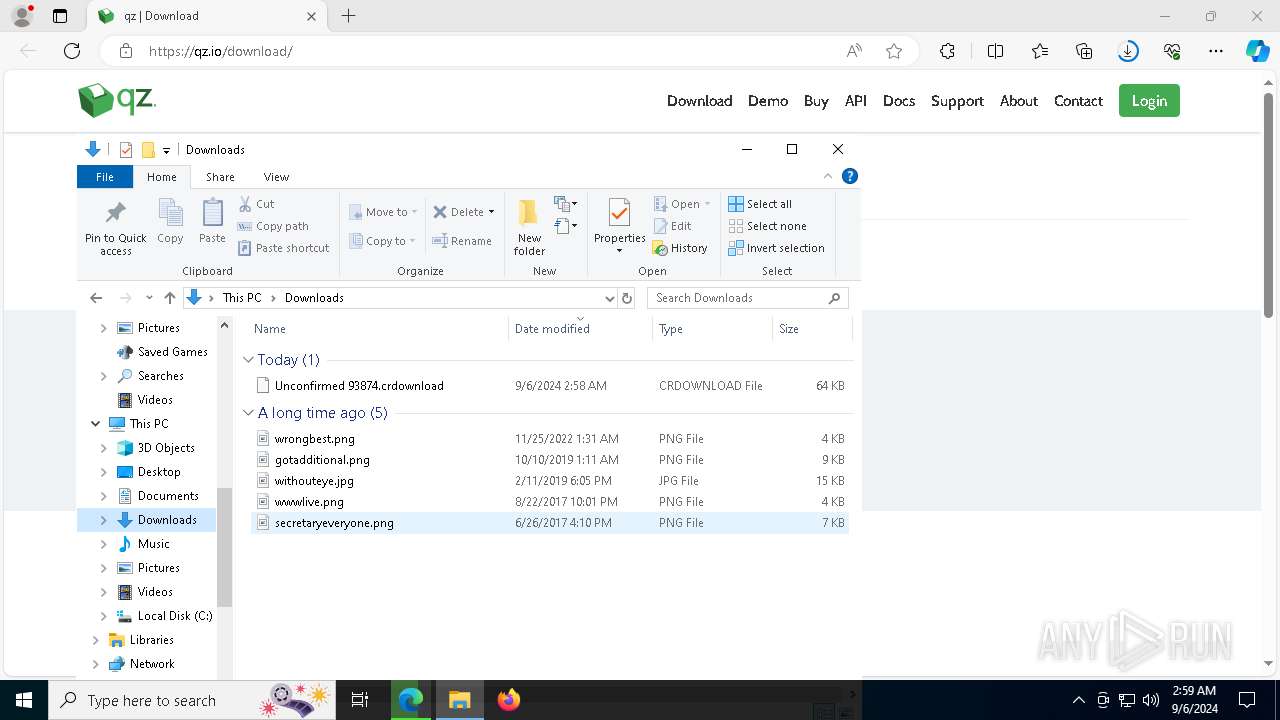
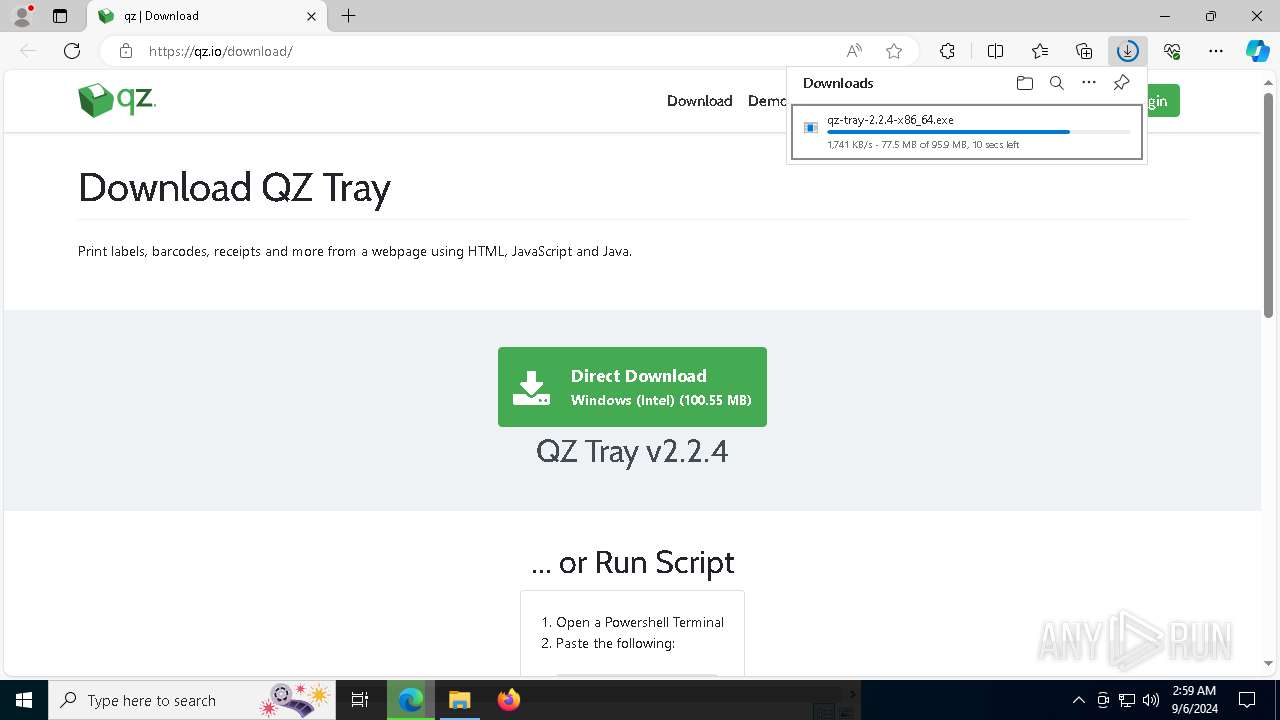
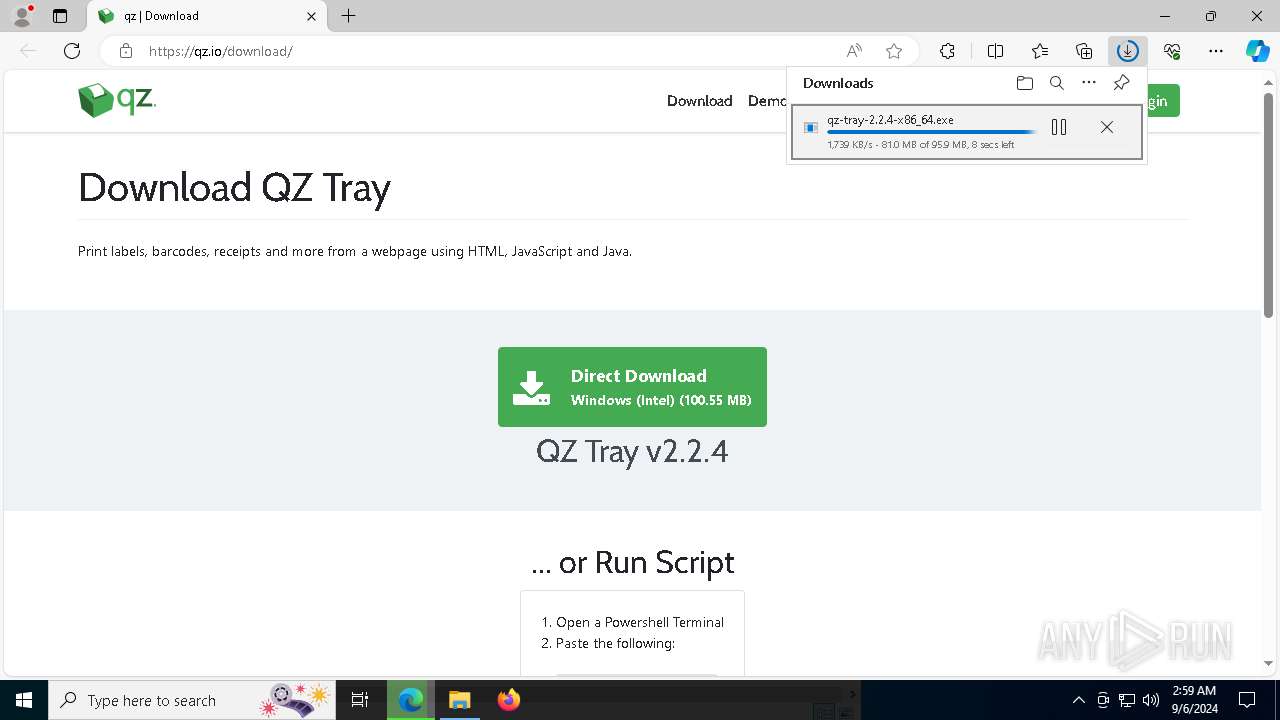
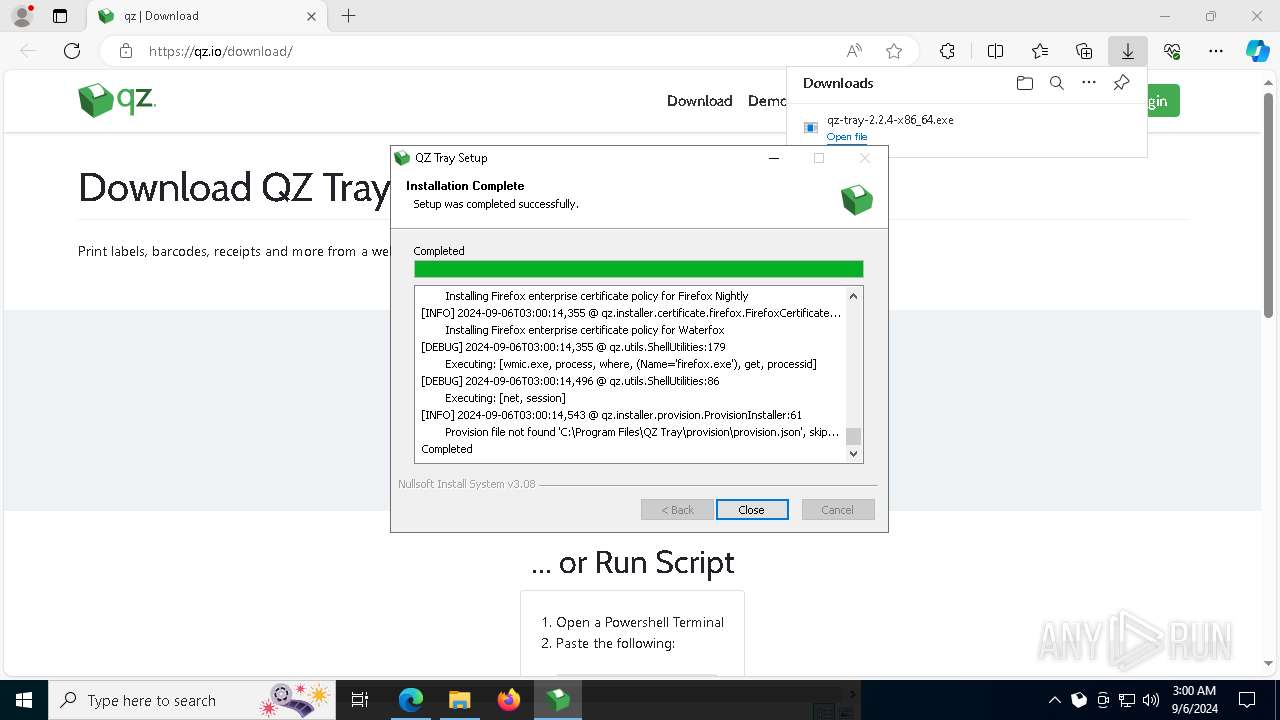
| URL: | https://qz.io/download/ |
| Full analysis: | https://app.any.run/tasks/cce9c95f-78e5-474c-93ec-dce2d7ef30f7 |
| Verdict: | Malicious activity |
| Analysis date: | September 06, 2024, 02:58:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 505224833087F2BC870556BF7D2A5263 |
| SHA1: | 353DAAE17BF6AAC68D083D4473537ADD412A344A |
| SHA256: | E4473B0C319789864C02AA12D7E52546A0256B87B3A826C1EEE4D19DC4CADD52 |
| SSDEEP: | 3:N8vKLn:2w |
MALICIOUS
Create files in the Startup directory
- java.exe (PID: 2092)
SUSPICIOUS
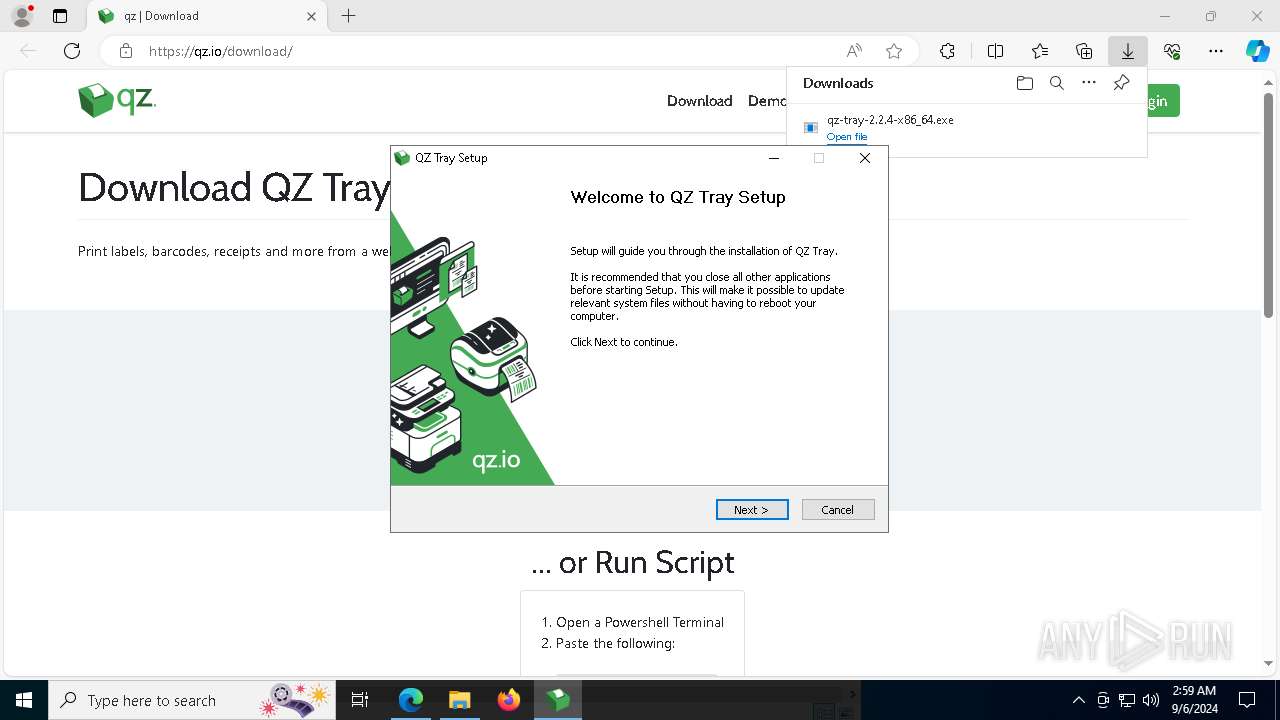
Process drops legitimate windows executable
- qz-tray-2.2.4-x86_64.exe (PID: 8064)
- java.exe (PID: 2092)
The process creates files with name similar to system file names
- qz-tray-2.2.4-x86_64.exe (PID: 8064)
- qz-tray.exe (PID: 6456)
Executable content was dropped or overwritten
- qz-tray-2.2.4-x86_64.exe (PID: 8064)
- java.exe (PID: 2092)
- qz-tray.exe (PID: 6456)
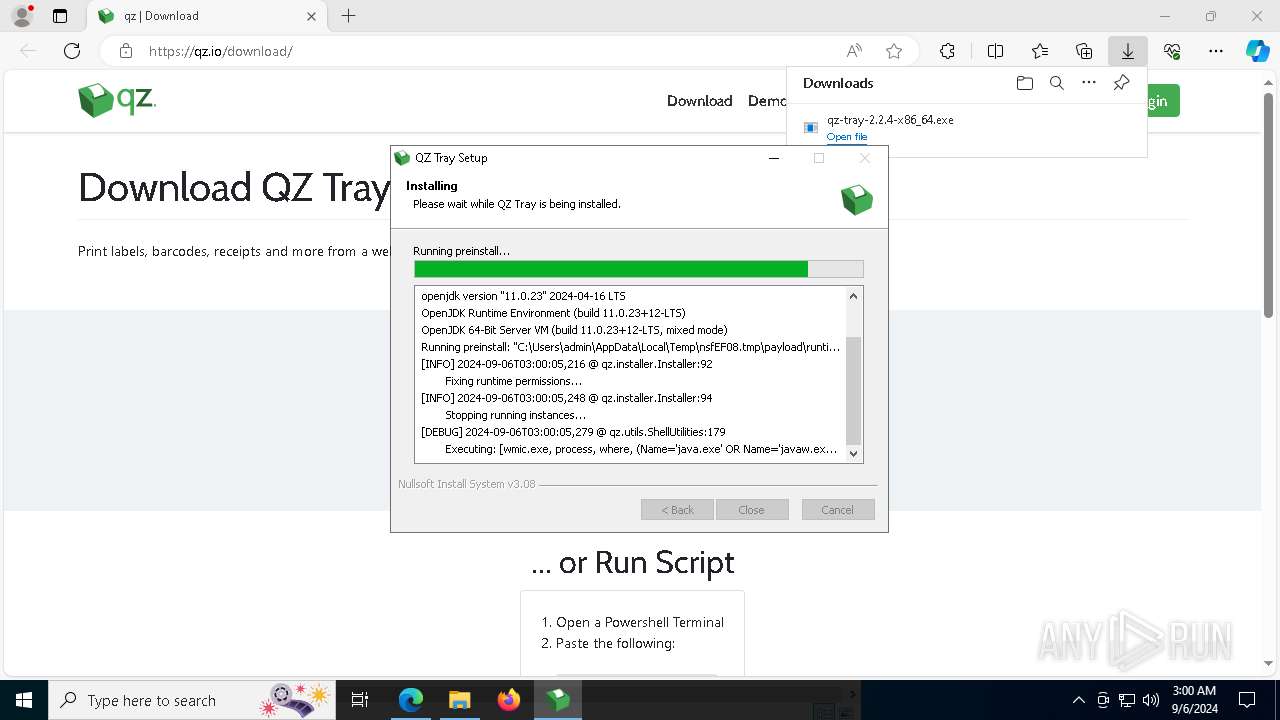
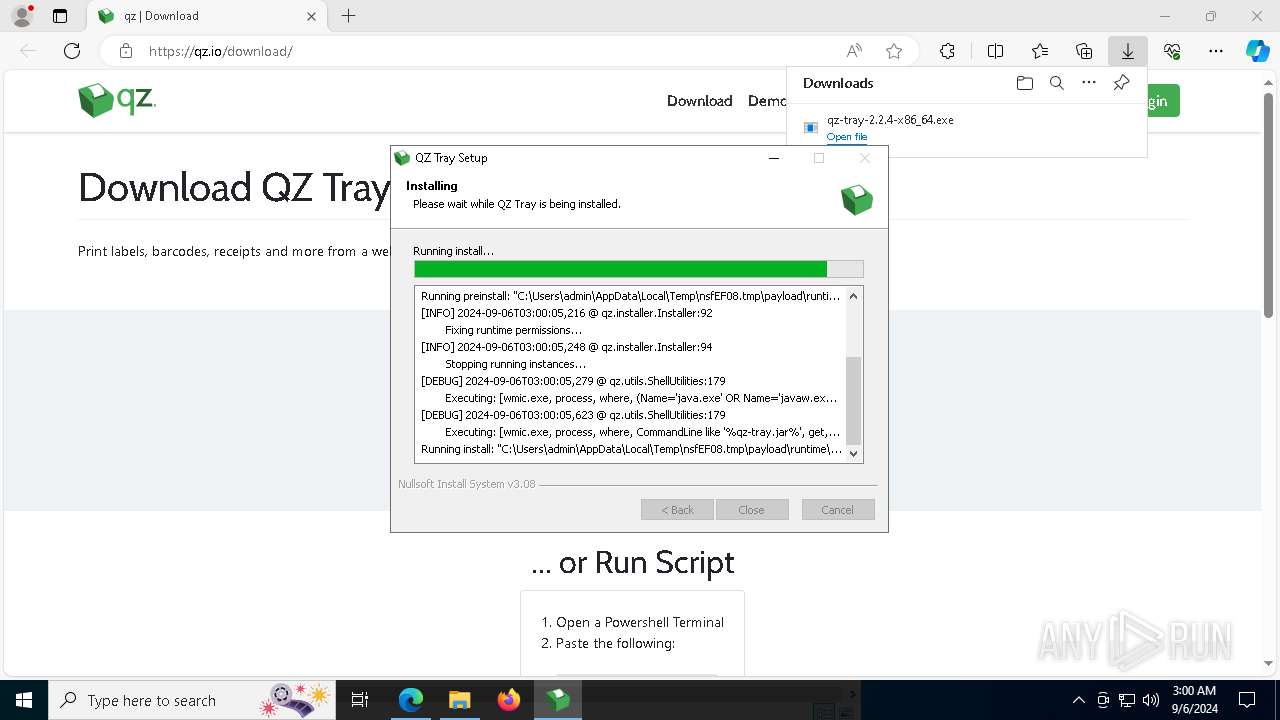
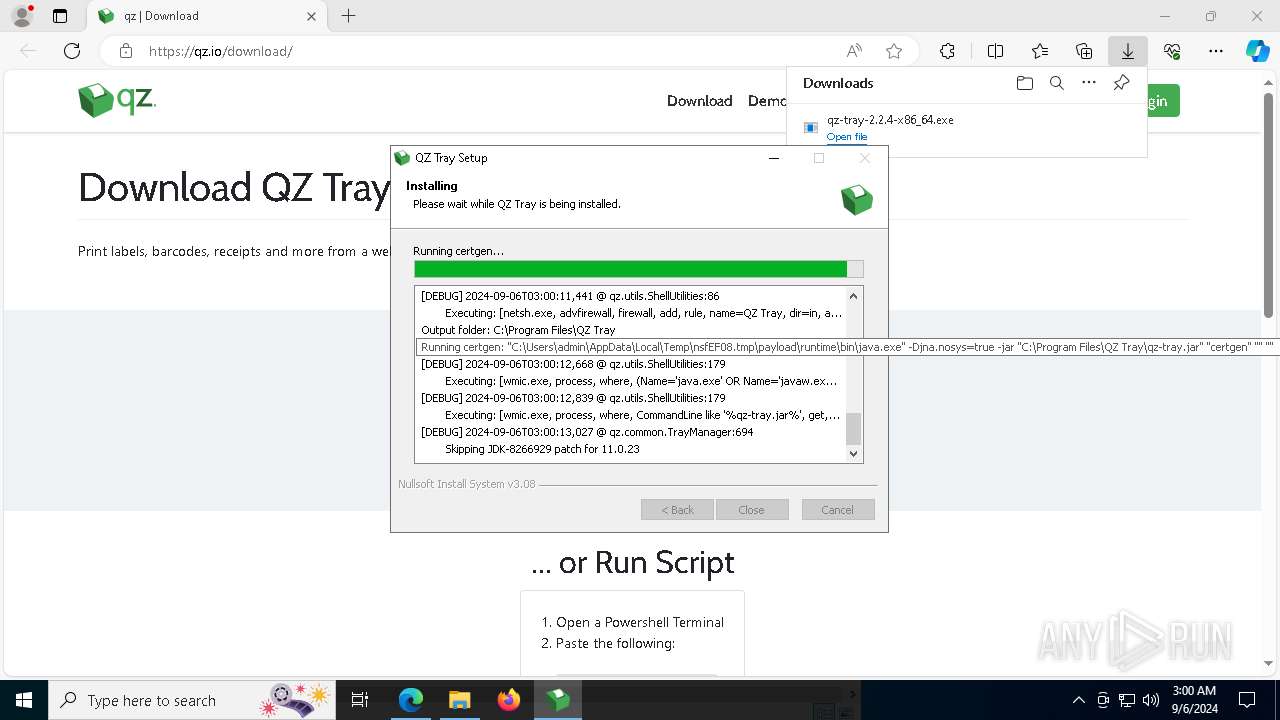
Uses WMIC.EXE to obtain data on processes
- java.exe (PID: 1440)
- java.exe (PID: 5980)
The process drops C-runtime libraries
- java.exe (PID: 2092)
- qz-tray-2.2.4-x86_64.exe (PID: 8064)
Creates a software uninstall entry
- java.exe (PID: 2092)
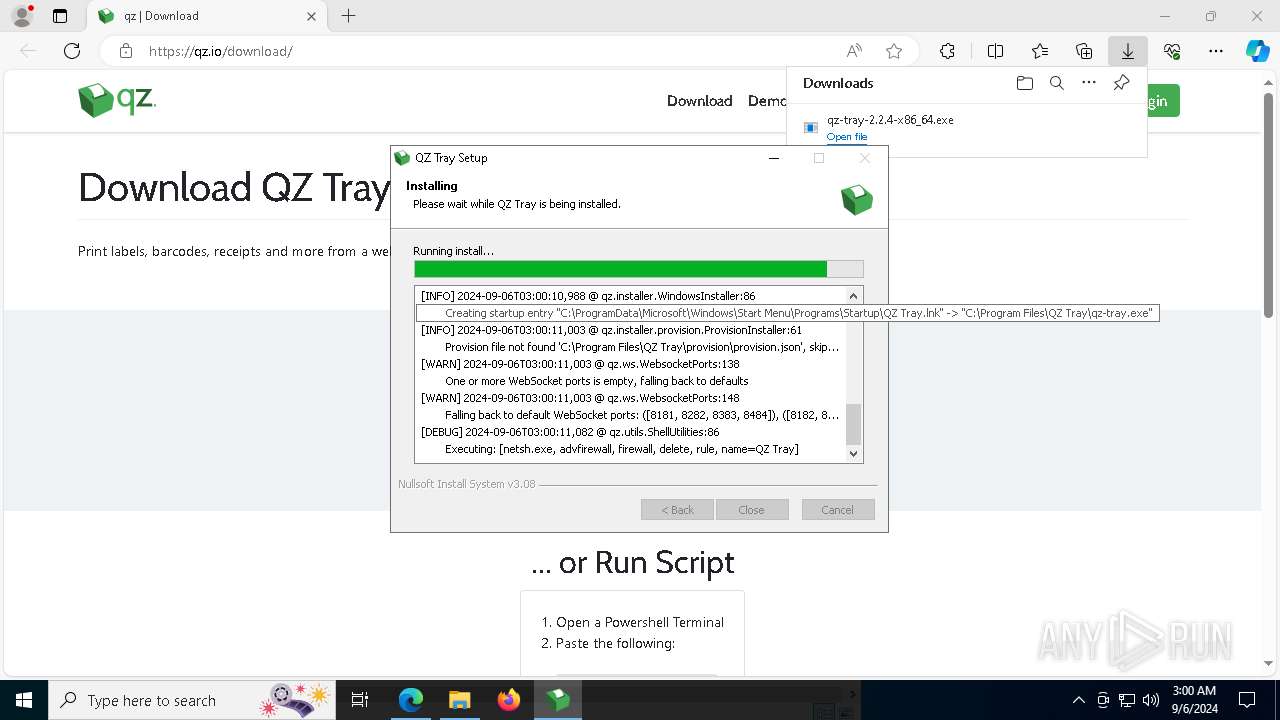
Uses NETSH.EXE to delete a firewall rule or allowed programs
- java.exe (PID: 2092)
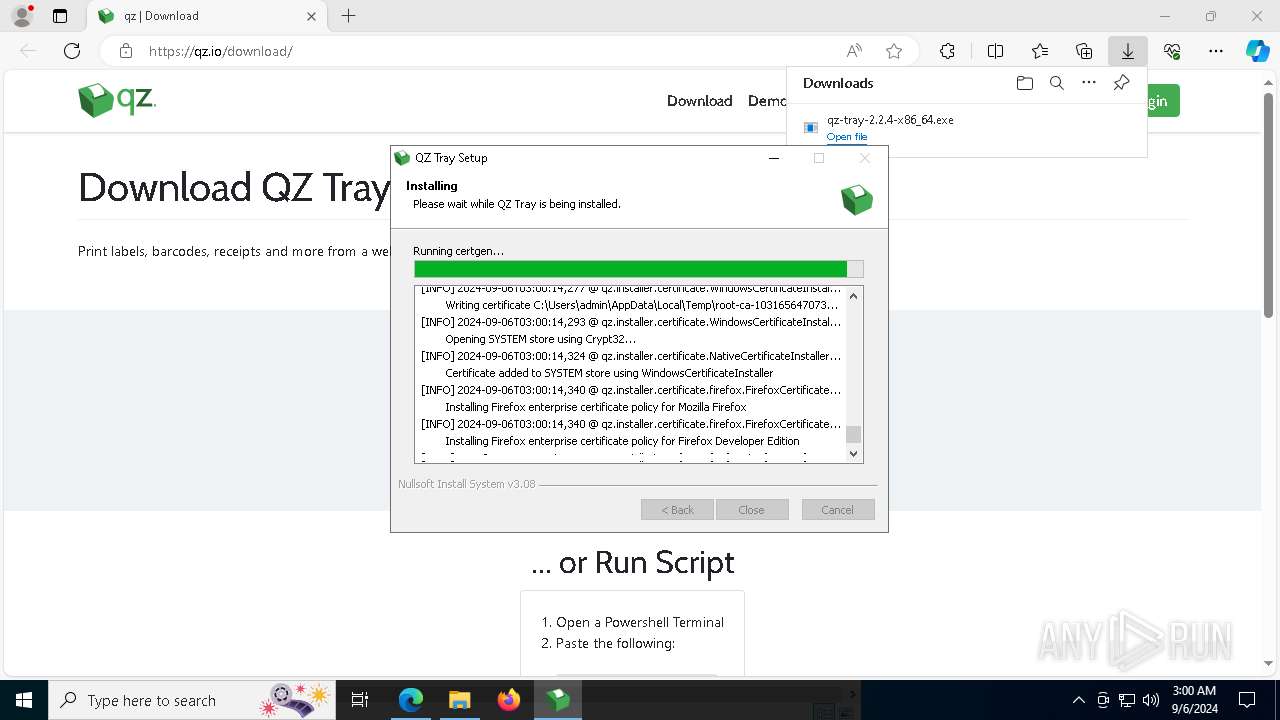
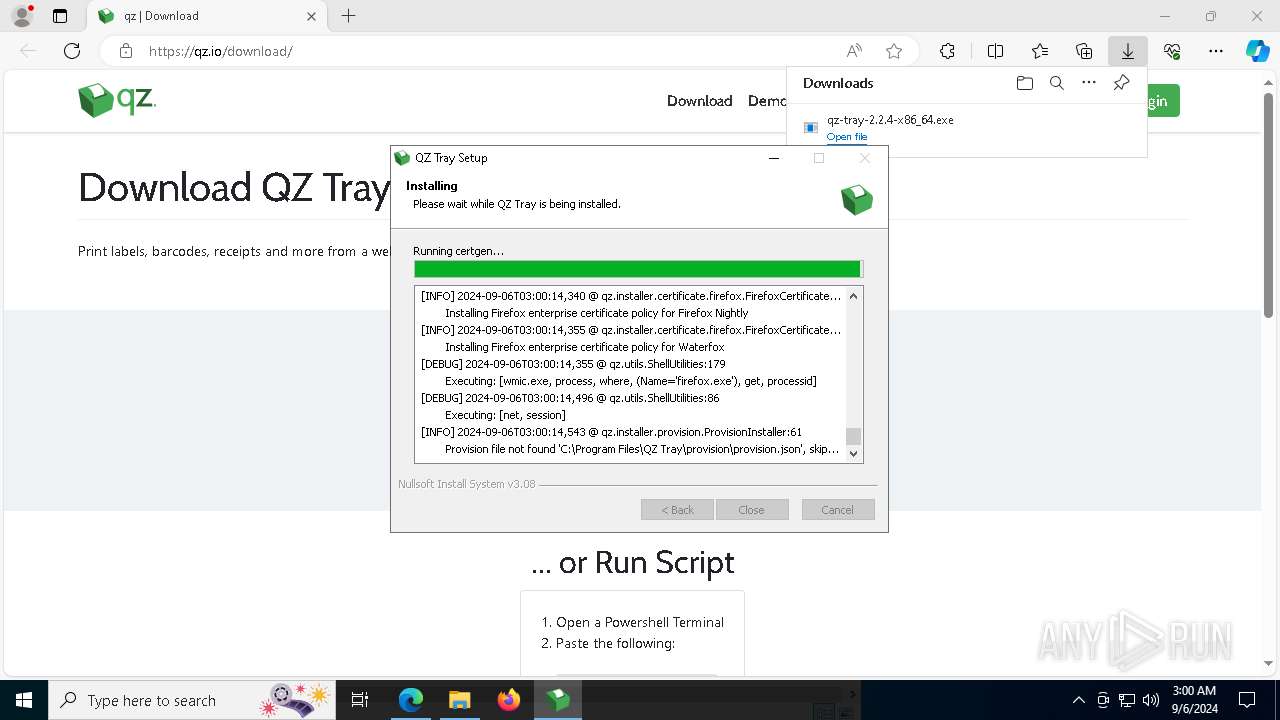
Adds/modifies Windows certificates
- java.exe (PID: 5980)
Malware-specific behavior (creating "System.dll" in Temp)
- qz-tray.exe (PID: 6456)
- qz-tray-2.2.4-x86_64.exe (PID: 8064)
Uses NETSH.EXE to add a firewall rule or allowed programs
- java.exe (PID: 2092)
INFO
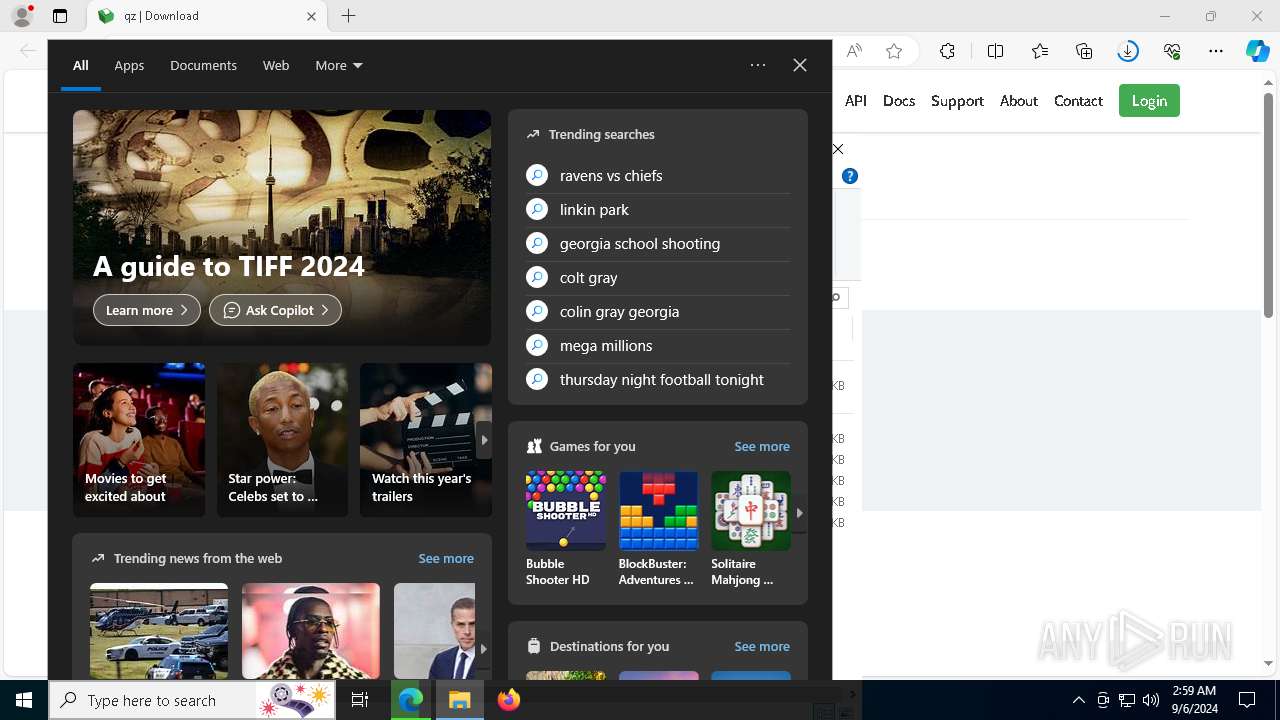
Application launched itself
- msedge.exe (PID: 376)
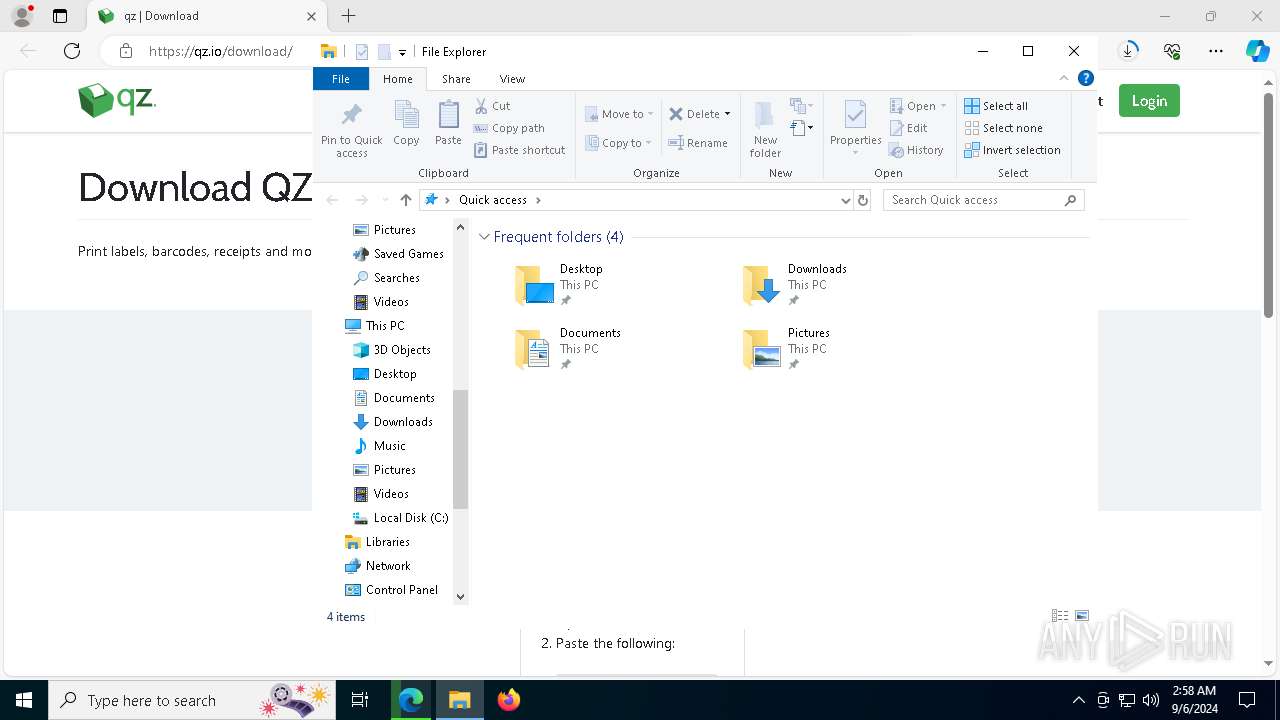
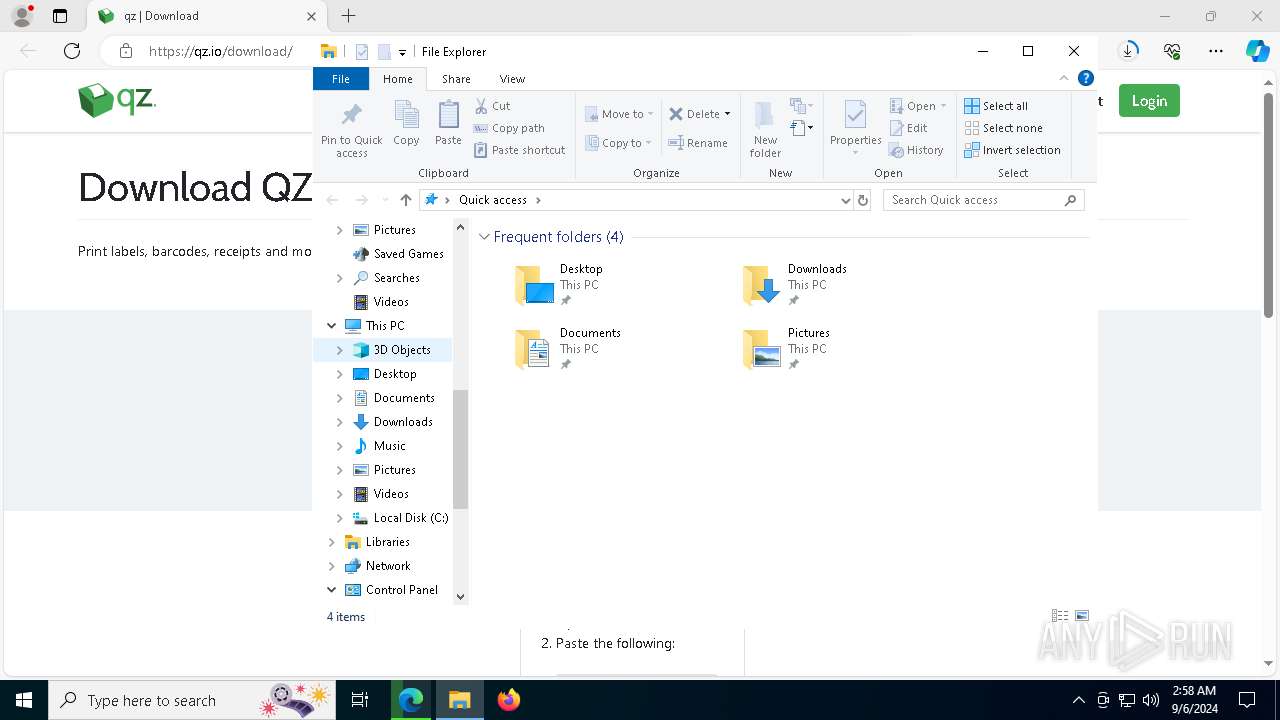
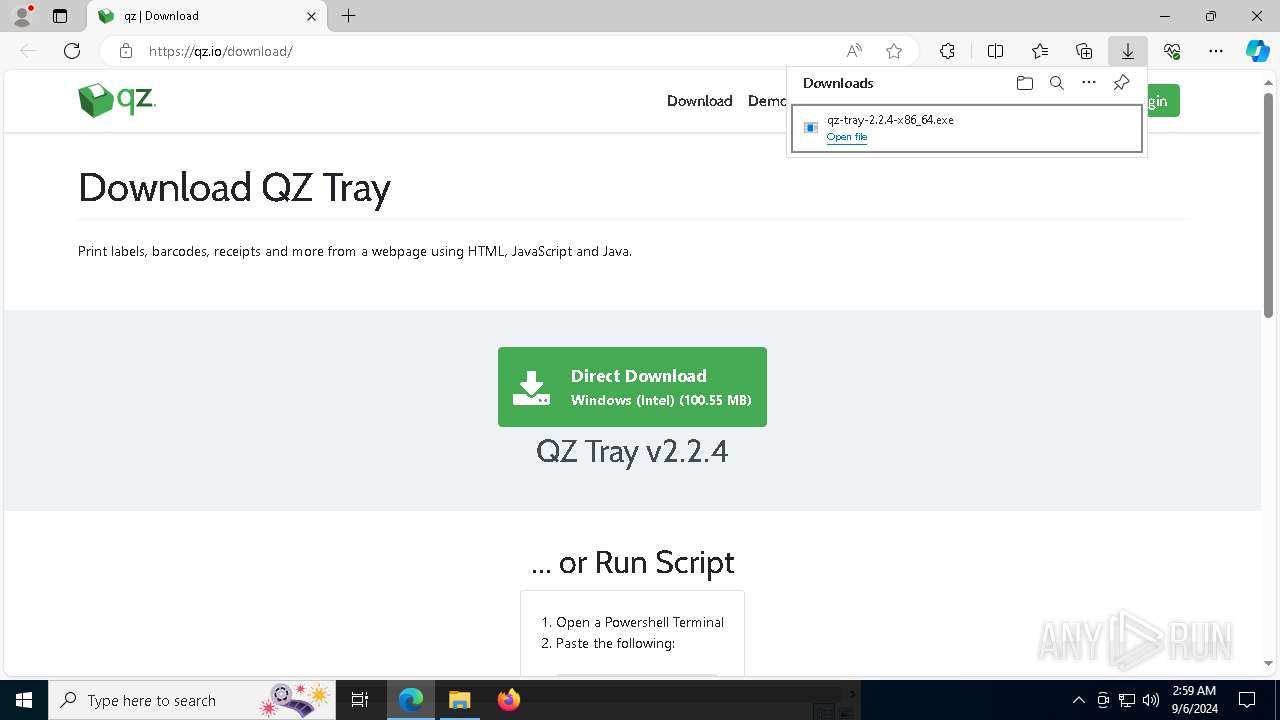
The process uses the downloaded file
- msedge.exe (PID: 7872)
- msedge.exe (PID: 376)
Creates files in the program directory
- qz-tray-2.2.4-x86_64.exe (PID: 8064)
- java.exe (PID: 2092)
- java.exe (PID: 5980)
- javaw.exe (PID: 7876)
Reads the computer name
- qz-tray-2.2.4-x86_64.exe (PID: 8064)
- identity_helper.exe (PID: 7880)
- java.exe (PID: 1440)
- java.exe (PID: 2092)
- java.exe (PID: 5980)
- javaw.exe (PID: 7876)
Create files in a temporary directory
- qz-tray-2.2.4-x86_64.exe (PID: 8064)
- java.exe (PID: 6456)
- java.exe (PID: 1440)
- java.exe (PID: 2092)
- java.exe (PID: 5980)
- javaw.exe (PID: 7876)
- qz-tray.exe (PID: 6456)
- java.exe (PID: 3180)
- java.exe (PID: 4128)
Checks supported languages
- java.exe (PID: 6456)
- java.exe (PID: 4128)
- identity_helper.exe (PID: 7880)
- java.exe (PID: 2092)
- java.exe (PID: 5980)
- qz-tray.exe (PID: 6456)
- qz-tray-2.2.4-x86_64.exe (PID: 8064)
- javaw.exe (PID: 7876)
- java.exe (PID: 3180)
- java.exe (PID: 1440)
Reads CPU info
- java.exe (PID: 1440)
- java.exe (PID: 4128)
- java.exe (PID: 2092)
- java.exe (PID: 5980)
- java.exe (PID: 3180)
- javaw.exe (PID: 7876)
- java.exe (PID: 6456)
Process checks computer location settings
- java.exe (PID: 1440)
- java.exe (PID: 2092)
- java.exe (PID: 5980)
- javaw.exe (PID: 7876)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7772)
- WMIC.exe (PID: 6876)
- WMIC.exe (PID: 7832)
- WMIC.exe (PID: 6192)
- WMIC.exe (PID: 2960)
Reads the machine GUID from the registry
- java.exe (PID: 2092)
- java.exe (PID: 1440)
- java.exe (PID: 5980)
- javaw.exe (PID: 7876)
Creates files or folders in the user directory
- java.exe (PID: 1440)
- javaw.exe (PID: 7876)
Reads Environment values
- identity_helper.exe (PID: 7880)
Executable content was dropped or overwritten
- msedge.exe (PID: 376)
Manual execution by a user
- qz-tray.exe (PID: 6456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
225
Monitored processes
91
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5496 --field-trial-handle=2420,i,11057628515565971586,7889005643117738803,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 376 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://qz.io/download/" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 508 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2488 --field-trial-handle=2420,i,11057628515565971586,7889005643117738803,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 788 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=7200 --field-trial-handle=2420,i,11057628515565971586,7889005643117738803,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1372 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5776 --field-trial-handle=2420,i,11057628515565971586,7889005643117738803,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1440 | "C:\Users\admin\AppData\Local\Temp\nsfEF08.tmp\payload\runtime\bin\java.exe" -Djna.nosys=true -jar "C:\Users\admin\AppData\Local\Temp\nsfEF08.tmp\payload\qz-tray.jar" "preinstall" "" "" | C:\Users\admin\AppData\Local\Temp\nsfEF08.tmp\payload\runtime\bin\java.exe | — | qz-tray-2.2.4-x86_64.exe | |||||||||||
User: admin Company: BellSoft Integrity Level: HIGH Description: OpenJDK Platform binary Exit code: 0 Version: 11.0.23 Modules
| |||||||||||||||
| 1700 | netsh.exe advfirewall firewall add rule "name=QZ Tray" dir=in action=allow profile=any localport=8181,8282,8383,8484,8182,8283,8384,8485 localip=any protocol=tcp | C:\Windows\System32\netsh.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1828 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6196 --field-trial-handle=2420,i,11057628515565971586,7889005643117738803,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
15 903
Read events
15 865
Write events
37
Delete events
1
Modification events
| (PID) Process: | (376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (376) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B13A68DD00802F00 | |||
| (PID) Process: | (376) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B8B76EDD00802F00 | |||
| (PID) Process: | (376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590730 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {ECAE0B1B-102E-49F6-A8C7-EB105661F728} | |||
| (PID) Process: | (376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590730 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {ECD623B9-F540-45B4-ABEE-2099908C817E} | |||
| (PID) Process: | (376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590730 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0585FE65-4D23-48AC-8CBD-995F582CB07F} | |||
| (PID) Process: | (376) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590730 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2893EFC9-F60E-4ABA-A1E4-162740E1E926} | |||
Executable files
294
Suspicious files
410
Text files
290
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF129bfa.TMP | — | |
MD5:— | SHA256:— | |||
| 376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF129c19.TMP | — | |
MD5:— | SHA256:— | |||
| 376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF129c19.TMP | — | |
MD5:— | SHA256:— | |||
| 376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF129c29.TMP | — | |
MD5:— | SHA256:— | |||
| 376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF129c29.TMP | — | |
MD5:— | SHA256:— | |||
| 376 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
92
DNS requests
77
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6612 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3832 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7920 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1726194917&P2=404&P3=2&P4=Ueg3s5gVkYM53qOiBxpfCihCrV%2fFXwwvTSzwbrkwZL5M13q%2fDTzOcjOKKFD8Zsf7CGkwuQmBS2MmTljYG1z96Q%3d%3d | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8124 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7920 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4e7e4c6f-7b62-49ca-a1fd-f625399e76b3?P1=1726194917&P2=404&P3=2&P4=Ueg3s5gVkYM53qOiBxpfCihCrV%2fFXwwvTSzwbrkwZL5M13q%2fDTzOcjOKKFD8Zsf7CGkwuQmBS2MmTljYG1z96Q%3d%3d | unknown | — | — | whitelisted |
7920 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3f7756bd-b1cc-4d5e-96d8-fd938a5c5bb6?P1=1725980036&P2=404&P3=2&P4=PZVfX8%2b4351IWjSJrNS76Ti5NKin%2bmCrreiCpIhOKJS5DKZVB3SlXCH7BZGuNcU8mpNdeWlV73jppUt5wLa2zg%3d%3d | unknown | — | — | whitelisted |
7920 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3f7756bd-b1cc-4d5e-96d8-fd938a5c5bb6?P1=1725980036&P2=404&P3=2&P4=PZVfX8%2b4351IWjSJrNS76Ti5NKin%2bmCrreiCpIhOKJS5DKZVB3SlXCH7BZGuNcU8mpNdeWlV73jppUt5wLa2zg%3d%3d | unknown | — | — | whitelisted |
7920 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3f7756bd-b1cc-4d5e-96d8-fd938a5c5bb6?P1=1725980036&P2=404&P3=2&P4=PZVfX8%2b4351IWjSJrNS76Ti5NKin%2bmCrreiCpIhOKJS5DKZVB3SlXCH7BZGuNcU8mpNdeWlV73jppUt5wLa2zg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6612 | svchost.exe | 20.49.150.241:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6232 | RUXIMICS.exe | 20.49.150.241:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.49.150.241:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
376 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
508 | msedge.exe | 168.220.86.107:443 | qz.io | FLY | US | unknown |
508 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
508 | msedge.exe | 13.107.246.60:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
508 | msedge.exe | 52.153.155.231:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
508 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
qz.io |
| unknown |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |