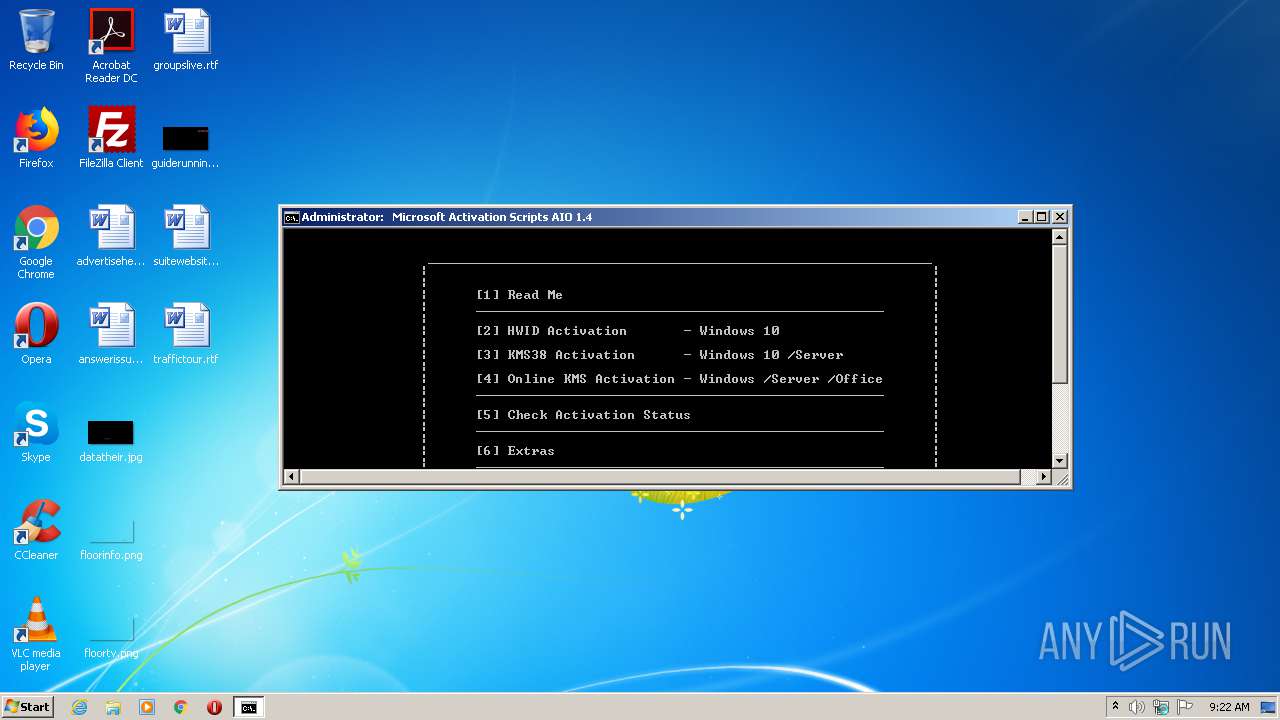
| File name: | MAS_1.4_AIO_CRC32_9A7B5B05.cmd |
| Full analysis: | https://app.any.run/tasks/94b06d62-b033-4ccd-807b-8b8b419ebd9d |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2021, 08:22:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 35F17DCF189FF654276CBD3777C474C5 |
| SHA1: | D0106953BB6026D874CA5F09FDEC59E57B483B36 |
| SHA256: | E44229E925D7BCB00773FBA75910EA74F5470627A68431F157B24413FAAE94C5 |
| SSDEEP: | 49152:g+ay1I0JxlXsyZ6tmDbR56nAfl5P/r/SI:rp/eyZ6tmDlTfbX |
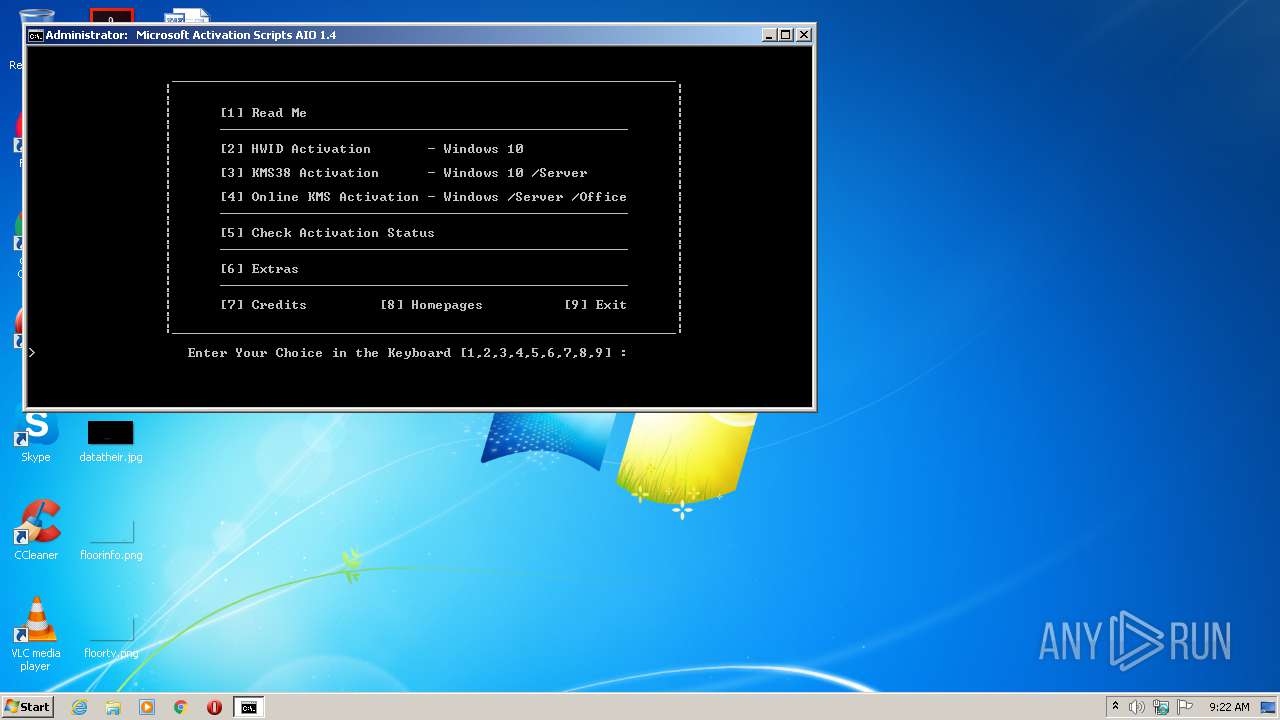
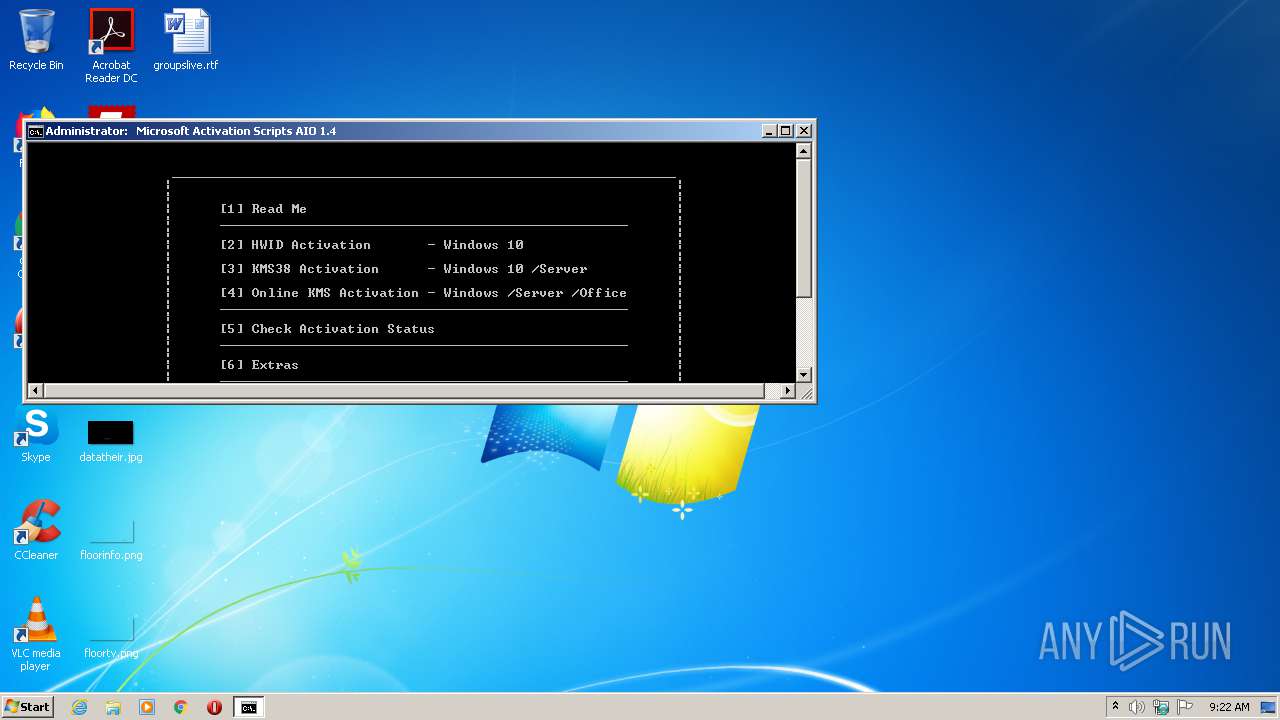
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3452)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 1724)
- cmd.exe (PID: 3452)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3452)
- cmd.exe (PID: 1724)
- cscript.exe (PID: 3584)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1724)
- cmd.exe (PID: 3452)
Creates files in the user directory
- powershell.exe (PID: 1304)
- powershell.exe (PID: 2016)
- powershell.exe (PID: 3372)
- powershell.exe (PID: 1248)
Creates files in the Windows directory
- powershell.exe (PID: 1304)
- powershell.exe (PID: 2016)
- powershell.exe (PID: 3372)
- powershell.exe (PID: 1248)
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 3452)
Uses RUNDLL32.EXE to load library
- cscript.exe (PID: 3584)
Executes scripts
- cmd.exe (PID: 1724)
Removes files from Windows directory
- cmd.exe (PID: 3452)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bib/bibtex/txt | | | BibTeX references (100) |
|---|
Total processes
73
Monitored processes
32
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | mode con cols=98 lines=32 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
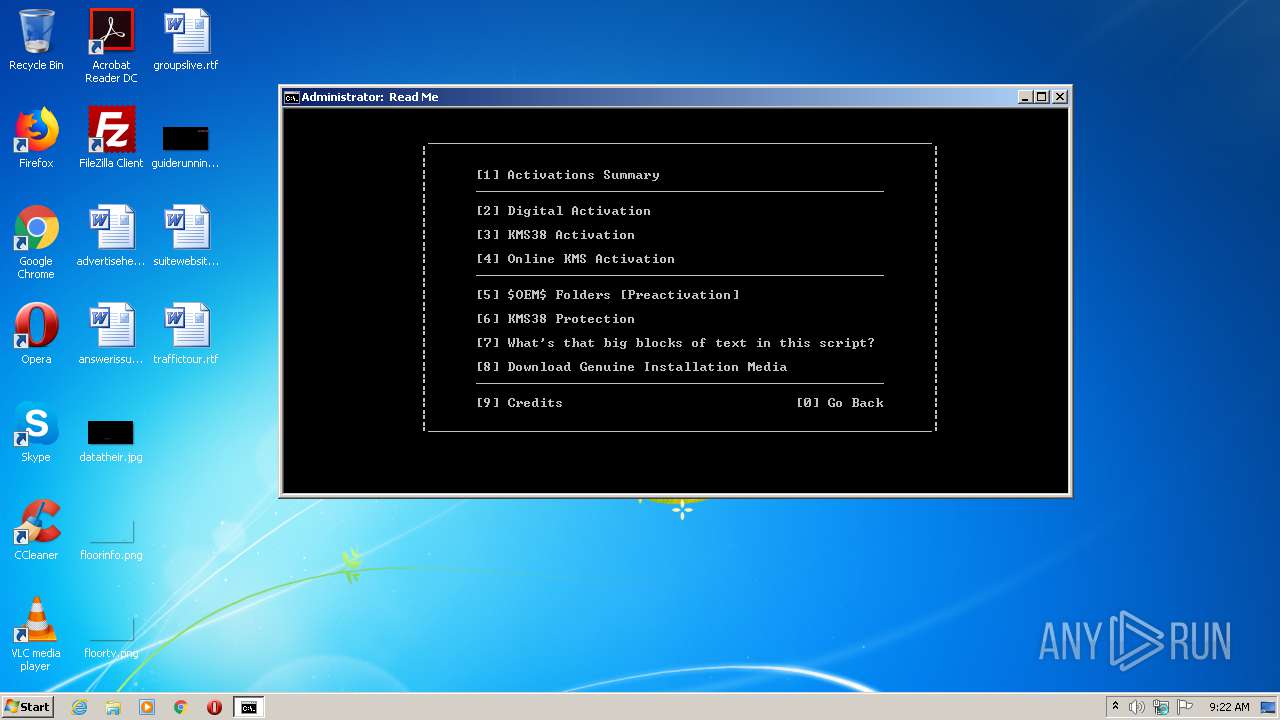
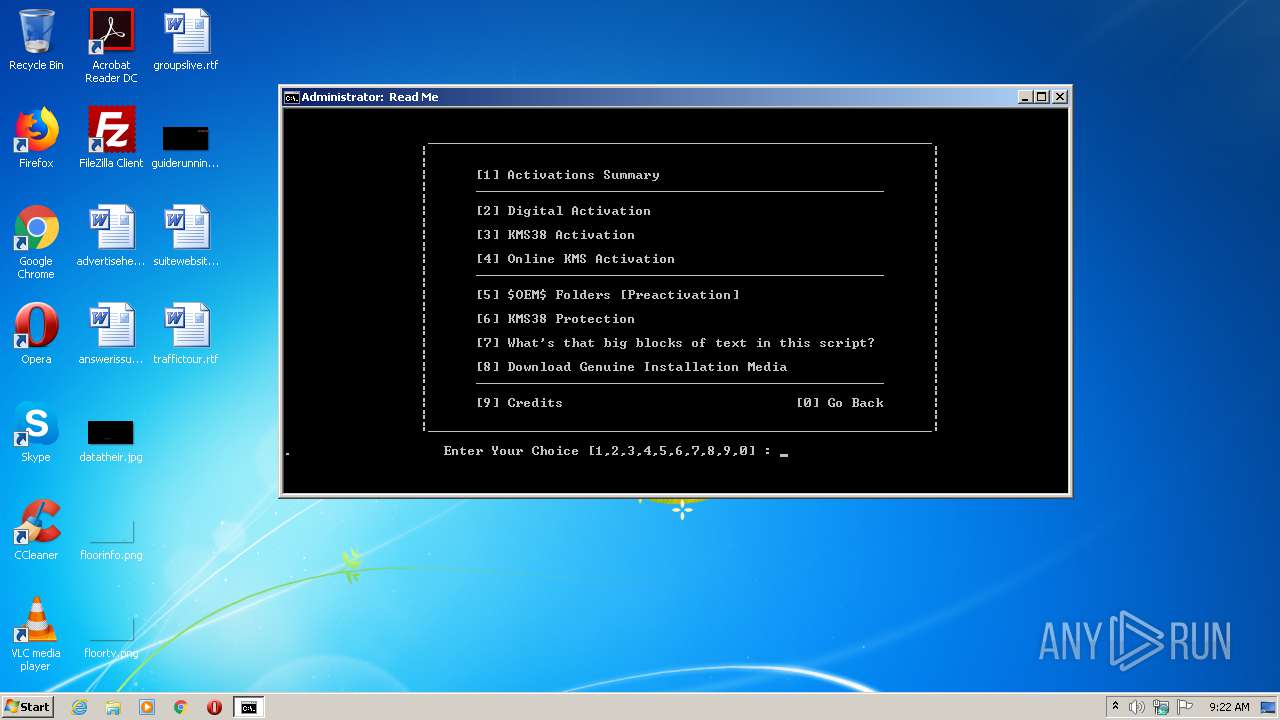
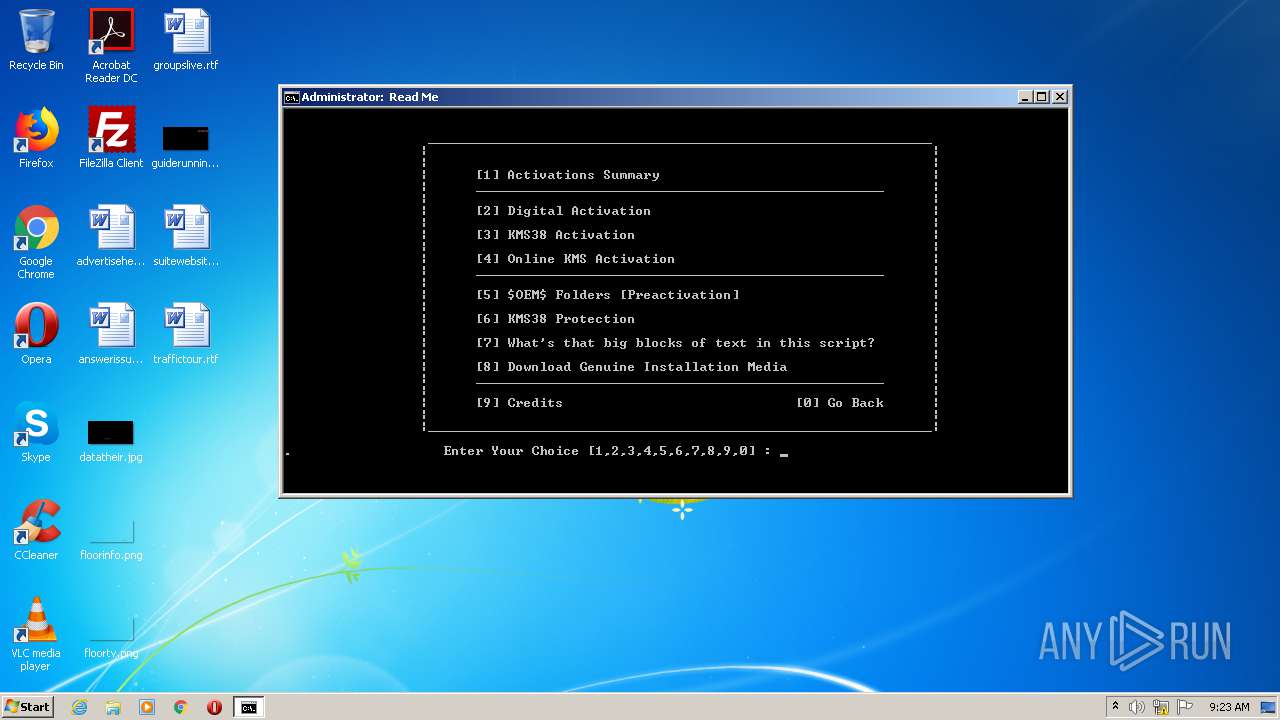
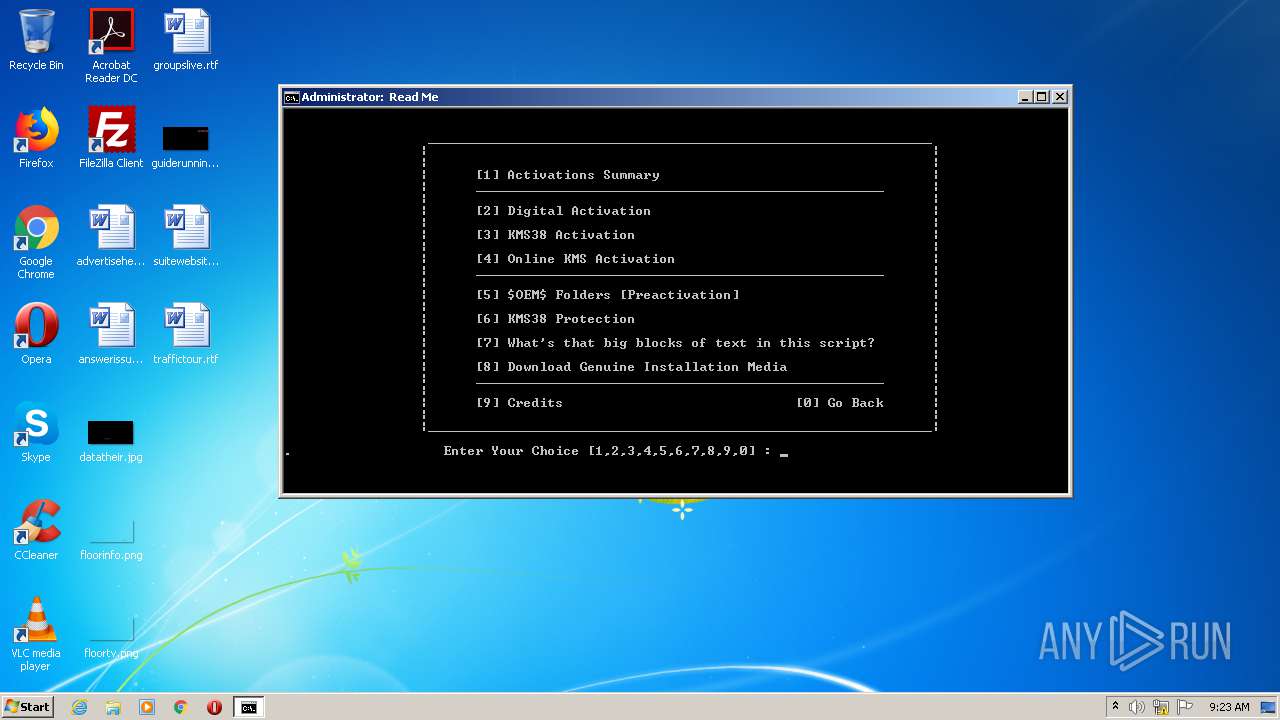
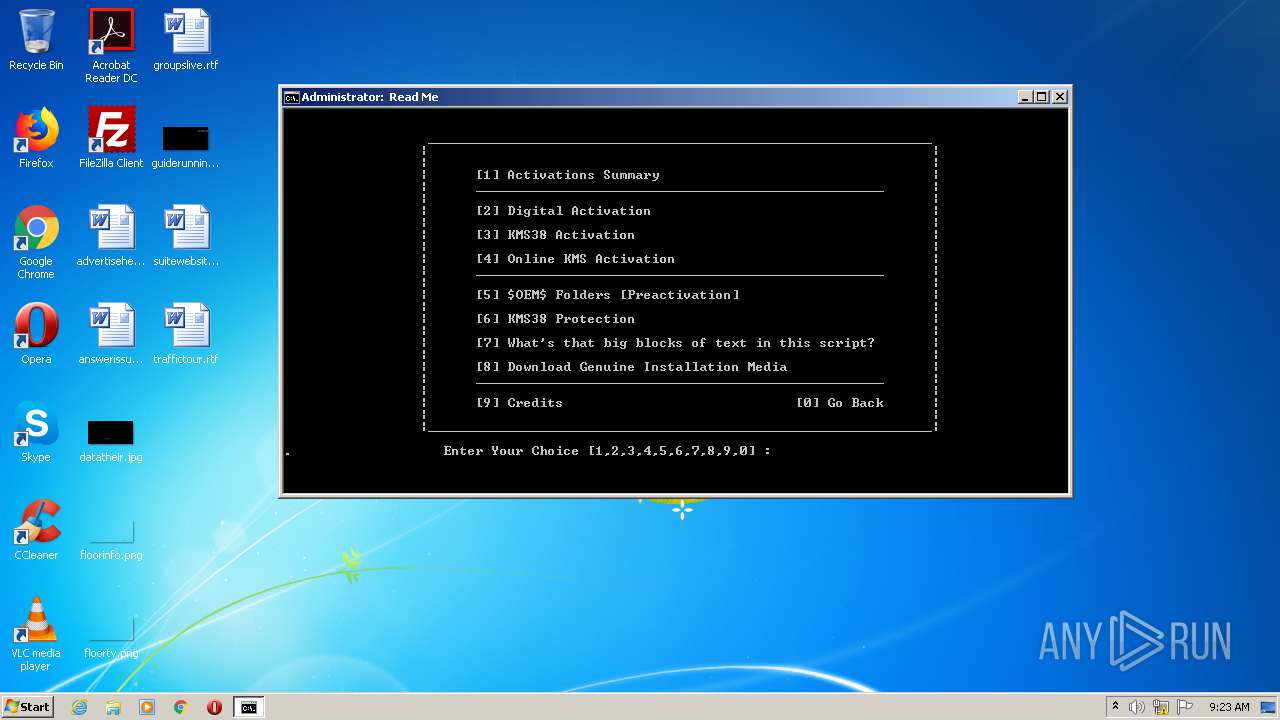
| 956 | choice /C:1234567890 /N /M ". Enter Your Choice [1,2,3,4,5,6,7,8,9,0] : " | C:\Windows\system32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 980 | mode con cols=98 lines=32 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1204 | rundll32 kernel32,Sleep | C:\Windows\system32\rundll32.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
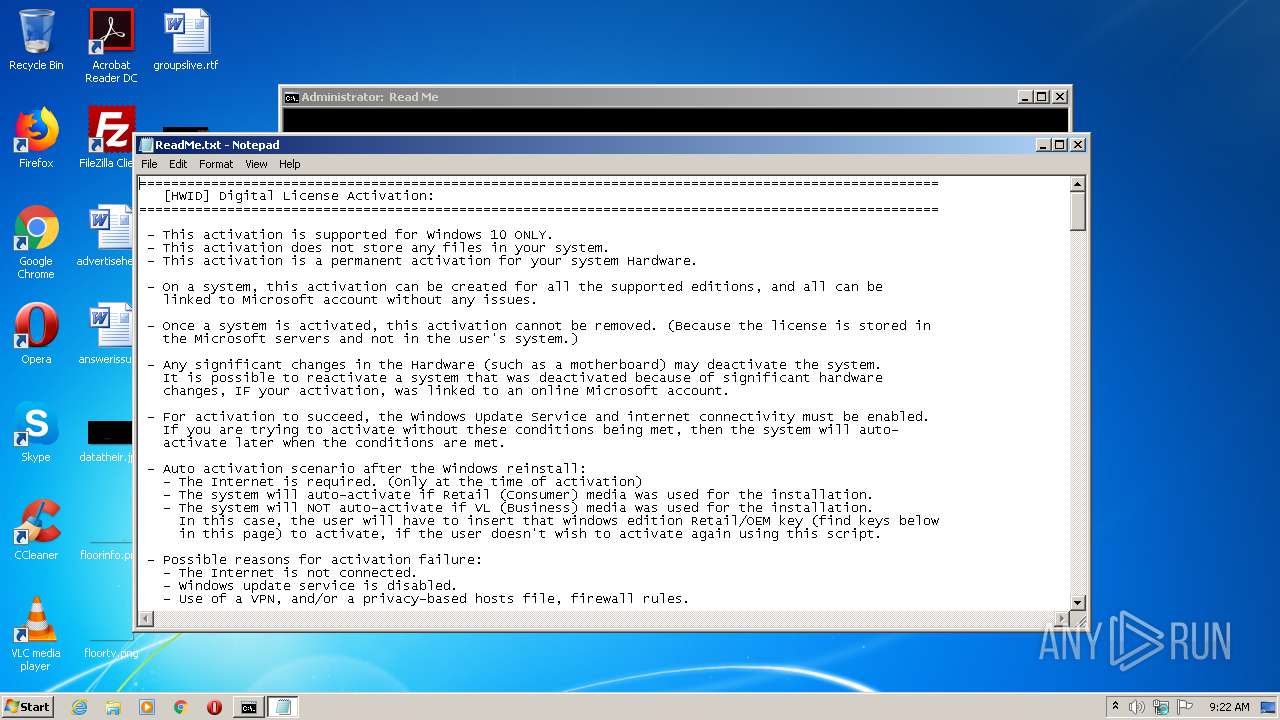
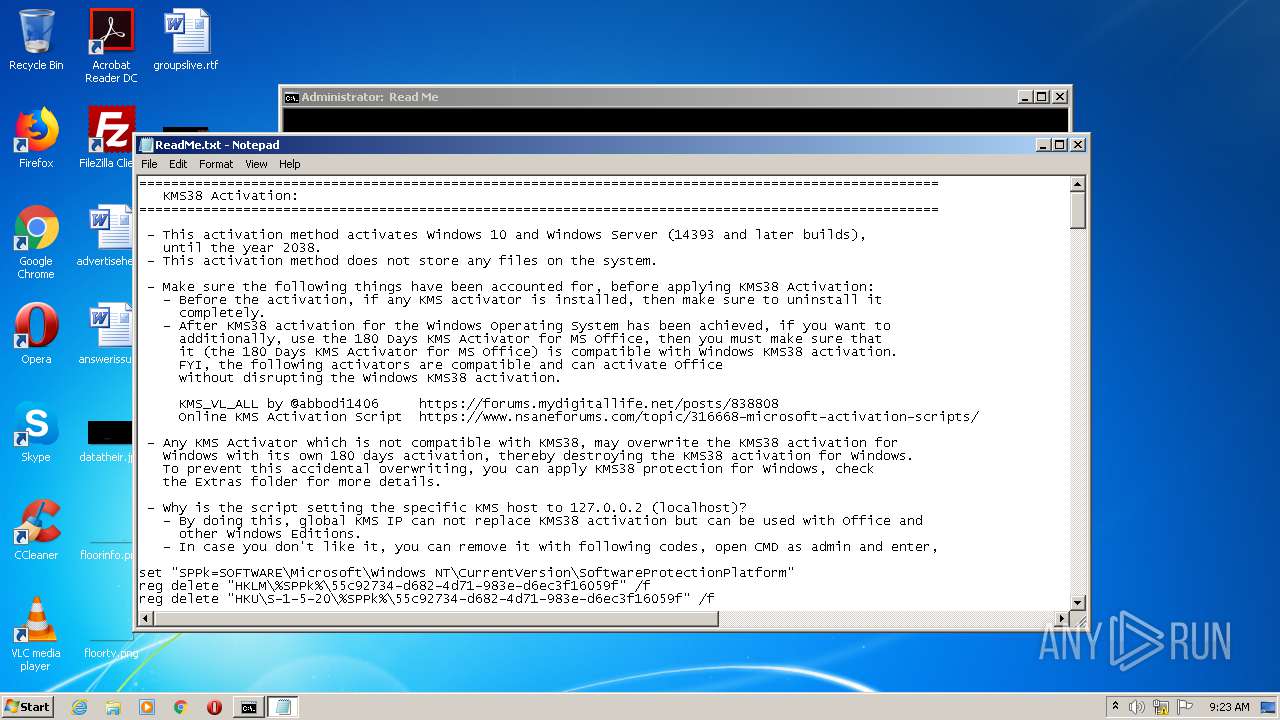
| 1248 | powershell "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_1.4_AIO_CRC32_9A7B5B05.cmd') -split \":9\:.*`r`n\"; [io.file]::WriteAllText('C:\Windows\Temp\ReadMe.txt',$f[1].Trim(),[System.Text.Encoding]::ASCII);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1304 | powershell "$f=[io.file]::ReadAllText('C:\Users\admin\AppData\Local\Temp\MAS_1.4_AIO_CRC32_9A7B5B05.cmd') -split \":1\:.*`r`n\"; [io.file]::WriteAllText('C:\Windows\Temp\ReadMe.txt',$f[1].Trim(),[System.Text.Encoding]::ASCII);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1368 | choice /C:1234567890 /N /M ". Enter Your Choice [1,2,3,4,5,6,7,8,9,0] : " | C:\Windows\system32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1508 | mode con cols=98 lines=32 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | cmd /c ""C:\Users\admin\AppData\Local\Temp\MAS_1.4_AIO_CRC32_9A7B5B05.cmd" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
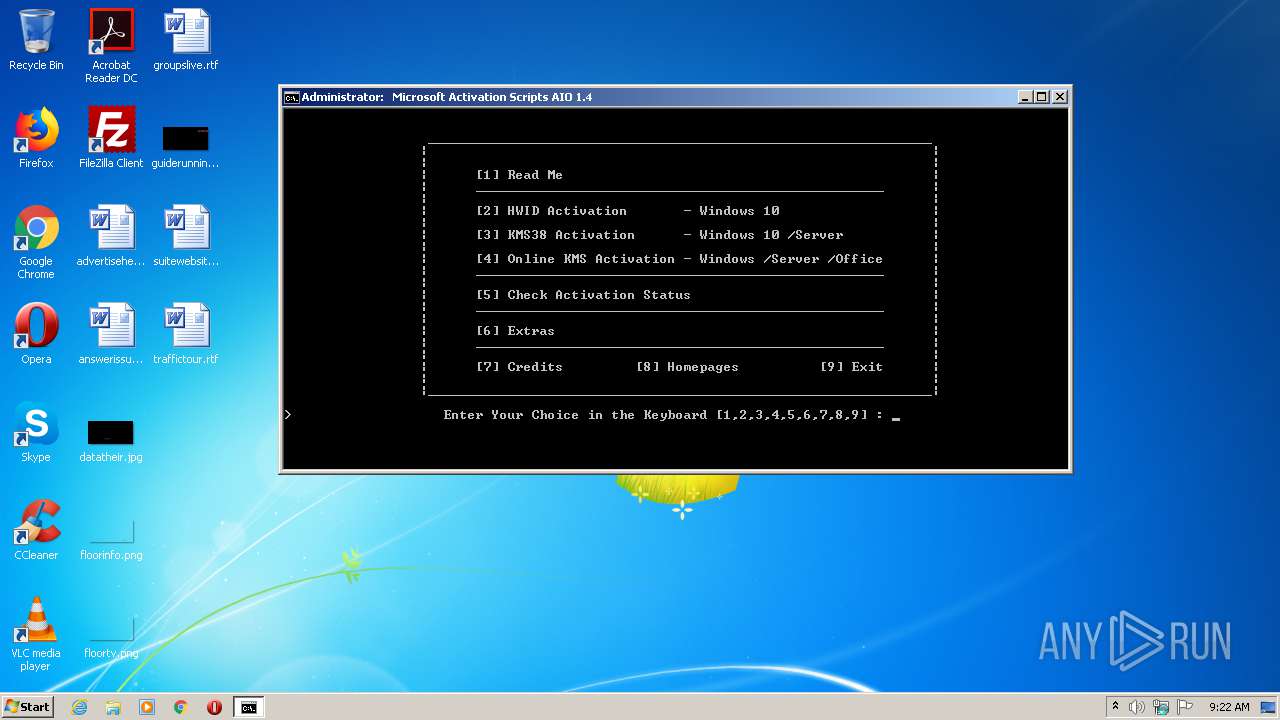
| 1768 | choice /C:123456789 /N /M "> Enter Your Choice in the Keyboard [1,2,3,4,5,6,7,8,9] : " | C:\Windows\system32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Offers the user a choice Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 143
Read events
919
Write events
224
Delete events
0
Modification events
| (PID) Process: | (3584) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3584) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1304) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2016) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3372) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1248) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
8
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1304 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8W2MLIGCQQIESETC77UD.temp | — | |
MD5:— | SHA256:— | |||
| 2016 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HIJD8TXP4CQ3LWFYDOEQ.temp | — | |
MD5:— | SHA256:— | |||
| 3372 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DVEA8LFOXWSE3U2LHXNA.temp | — | |
MD5:— | SHA256:— | |||
| 1248 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JDESRGIJL2PK3EVW84WC.temp | — | |
MD5:— | SHA256:— | |||
| 3372 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2016 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFe3515.TMP | binary | |
MD5:— | SHA256:— | |||
| 1248 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFed165.TMP | binary | |
MD5:— | SHA256:— | |||
| 2016 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1304 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3372 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFea043.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report