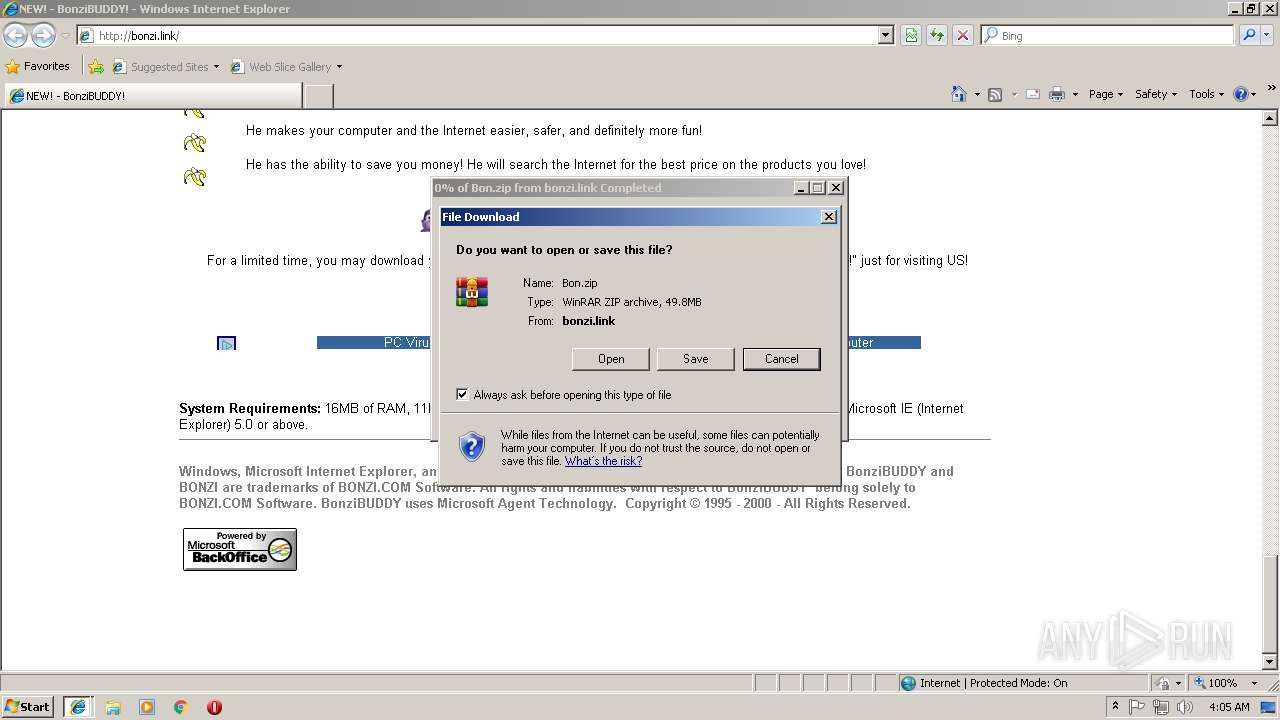
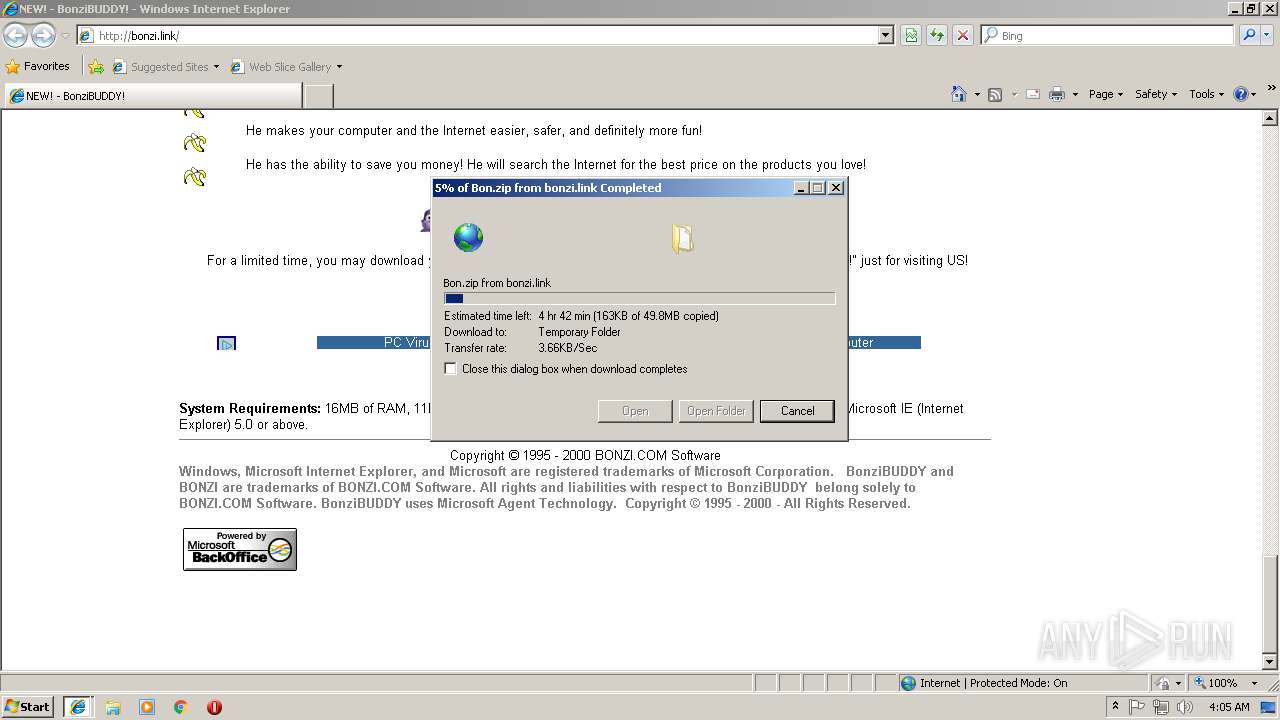
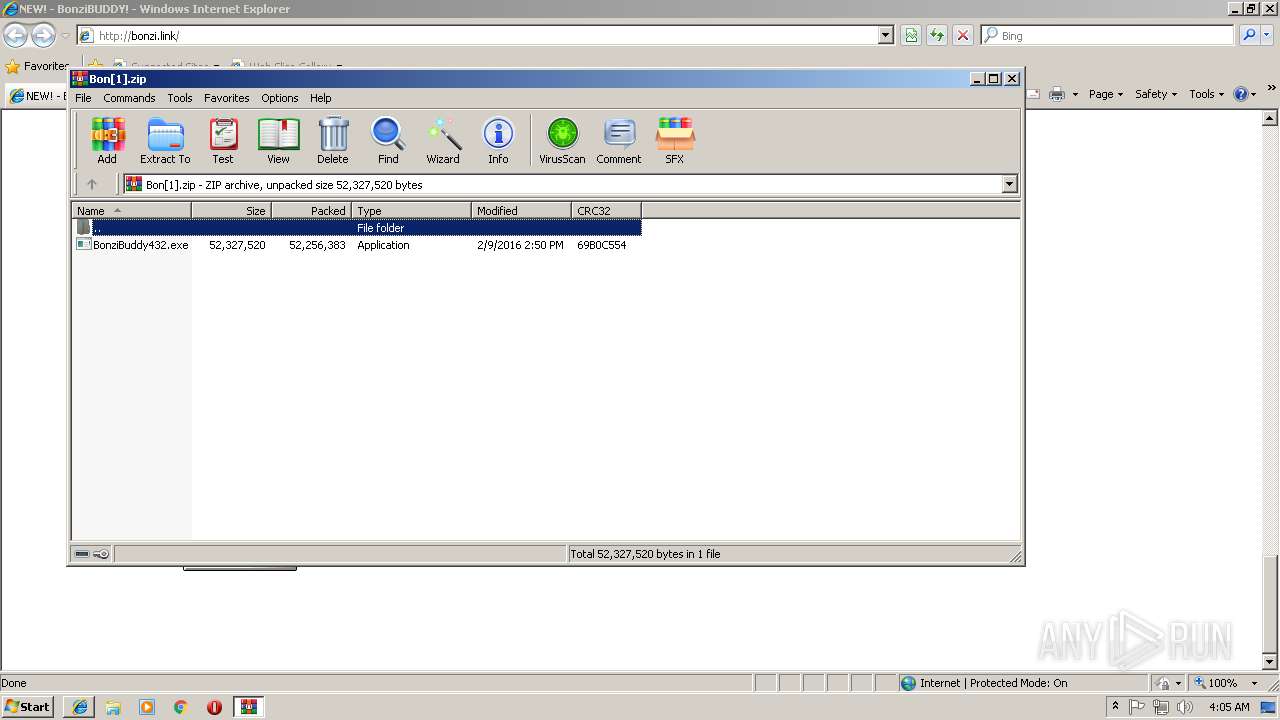
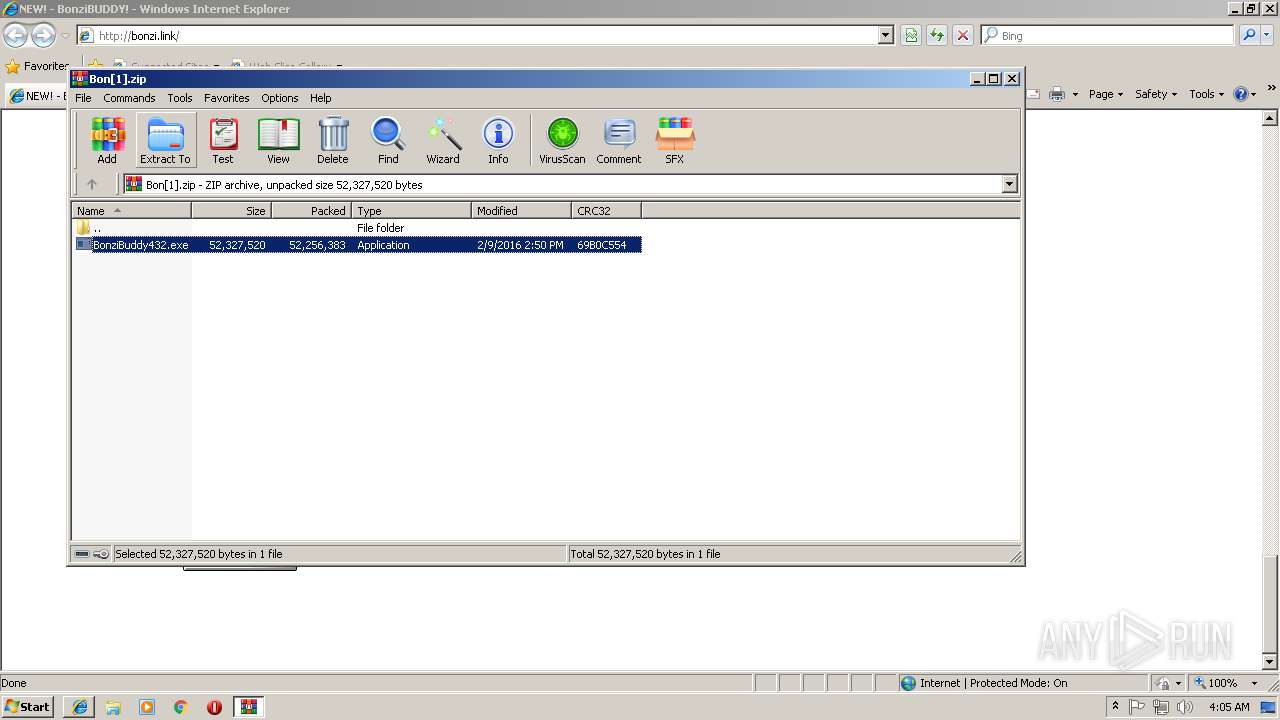
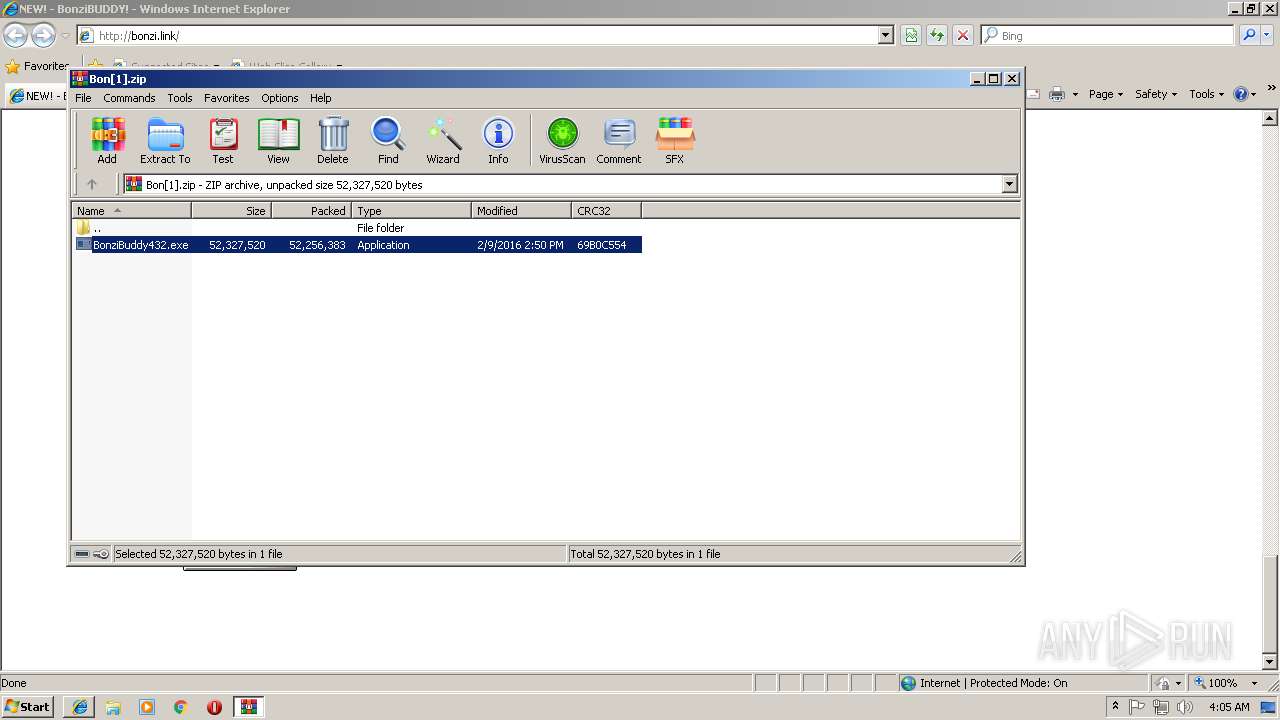
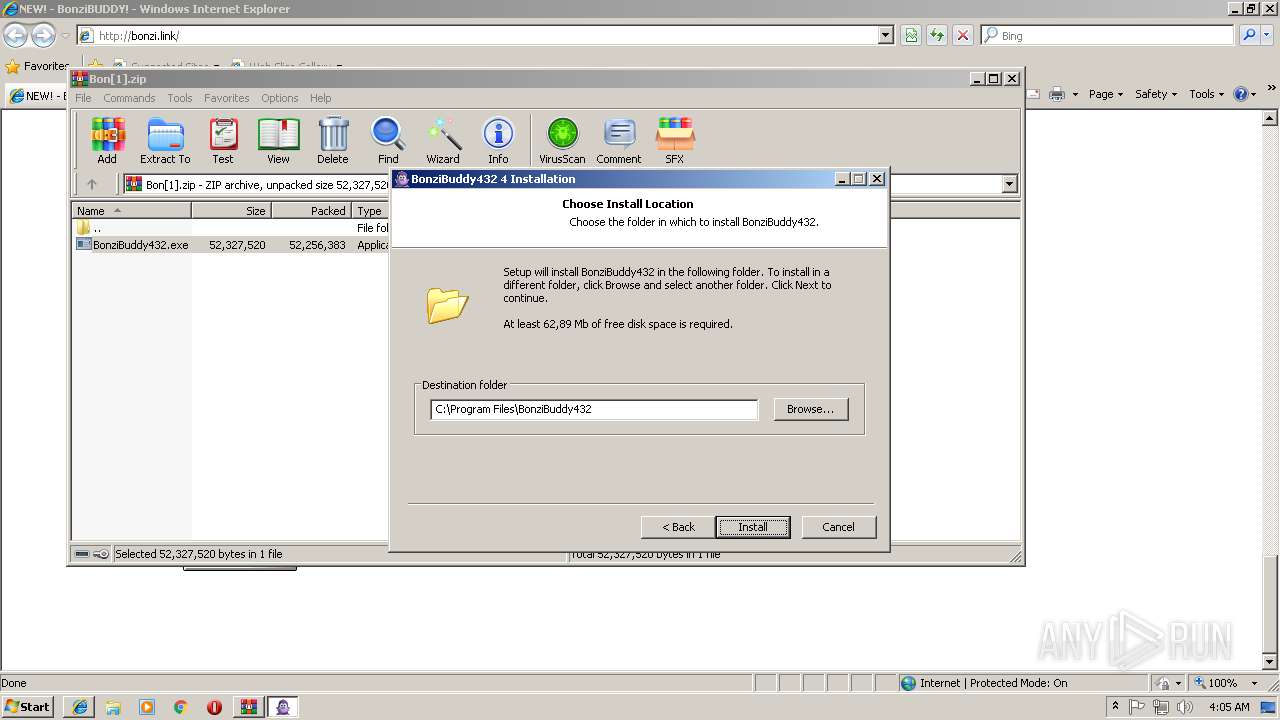
| URL: | http://bonzi.link/Bon.zip |
| Full analysis: | https://app.any.run/tasks/9e414084-29b5-4e85-8641-31594ecf6069 |
| Verdict: | Malicious activity |
| Analysis date: | September 22, 2018, 03:04:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 160CD11A1E15679936A39E369F47FD8E |
| SHA1: | 7A0731DCDC8045BE3C43323A57BE46D88F2B725F |
| SHA256: | E43FDC3373157BB1CA279EFF37D046081BB75D8C984E25C43320A0E9FDDA3560 |
| SSDEEP: | 3:N1KcX8KL4:CcX8Kk |
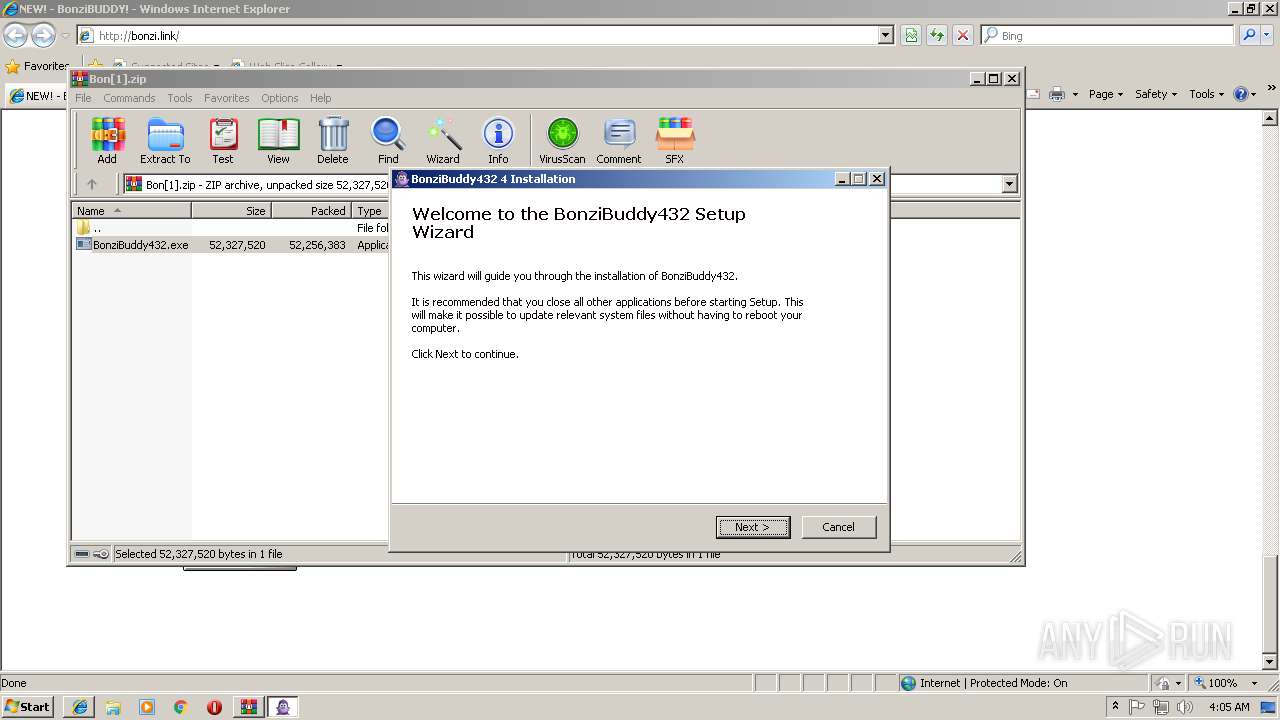
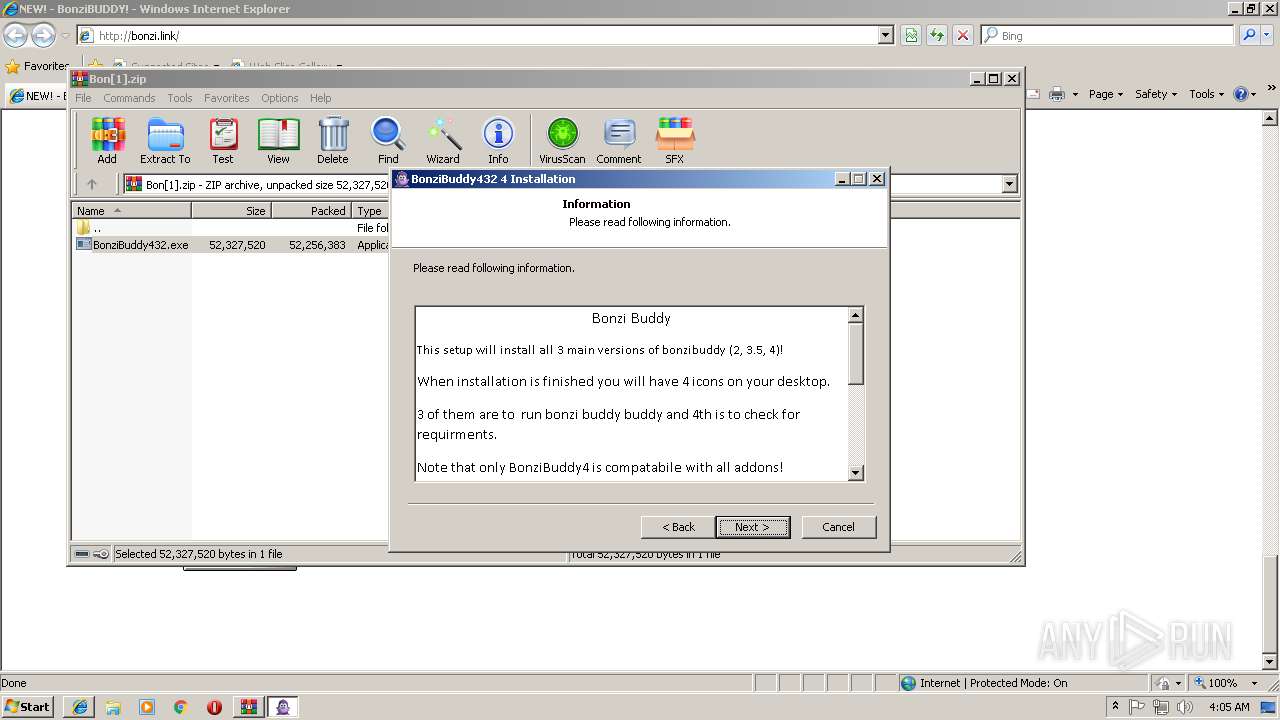
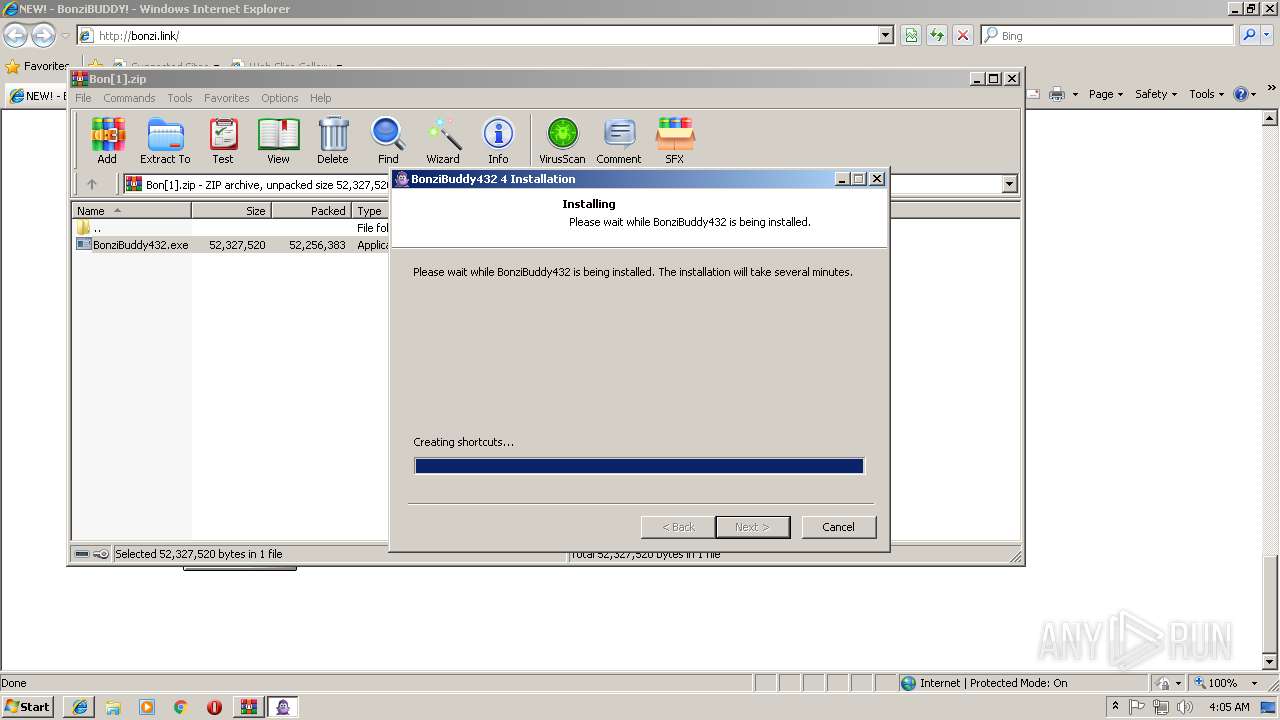
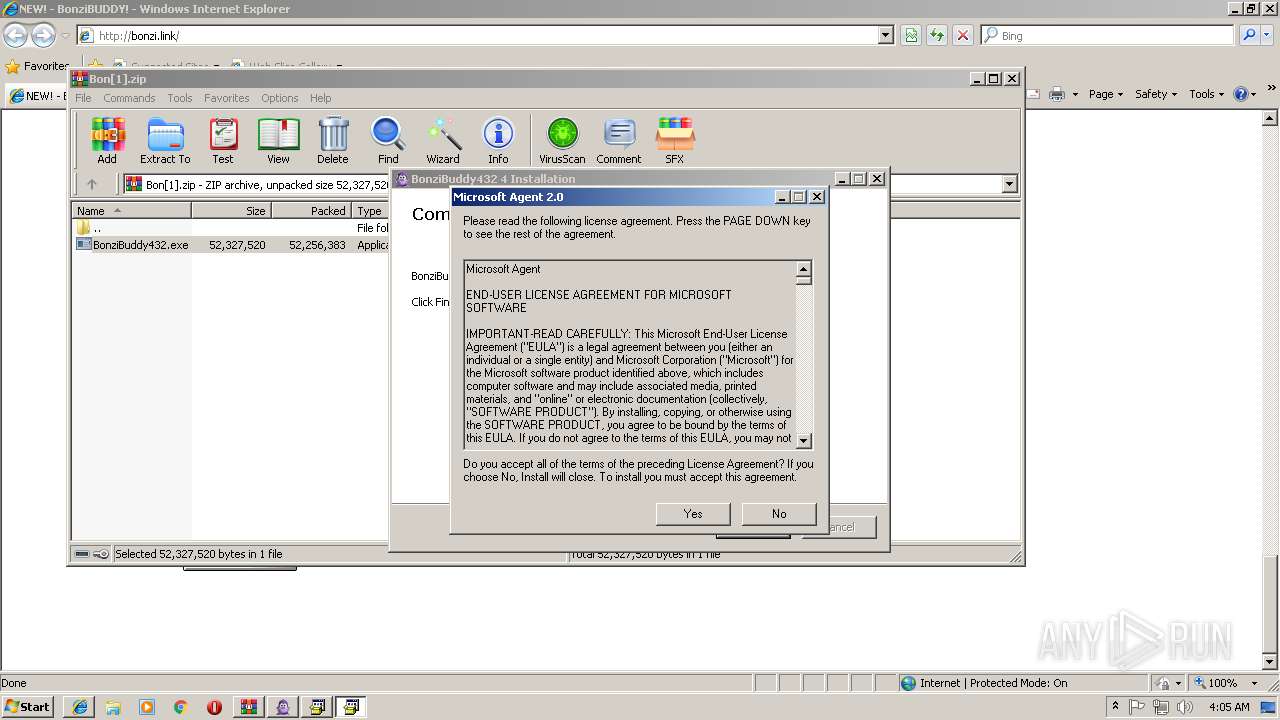
MALICIOUS
Loads dropped or rewritten executable
- BonziBuddy432.exe (PID: 2776)
- regsvr32.exe (PID: 1904)
- tv_enua.exe (PID: 3208)
- MSAGENT.EXE (PID: 1600)
- regsvr32.exe (PID: 1460)
- regsvr32.exe (PID: 3268)
- regsvr32.exe (PID: 3236)
- regsvr32.exe (PID: 3512)
- regsvr32.exe (PID: 3552)
- regsvr32.exe (PID: 1812)
- regsvr32.exe (PID: 3240)
- regsvr32.exe (PID: 1692)
Application was dropped or rewritten from another process
- MSAGENT.EXE (PID: 1600)
- tv_enua.exe (PID: 3208)
- AgentSvr.exe (PID: 2900)
Registers / Runs the DLL via REGSVR32.EXE
- MSAGENT.EXE (PID: 1600)
- tv_enua.exe (PID: 3208)
Changes the autorun value in the registry
- tv_enua.exe (PID: 3208)
SUSPICIOUS
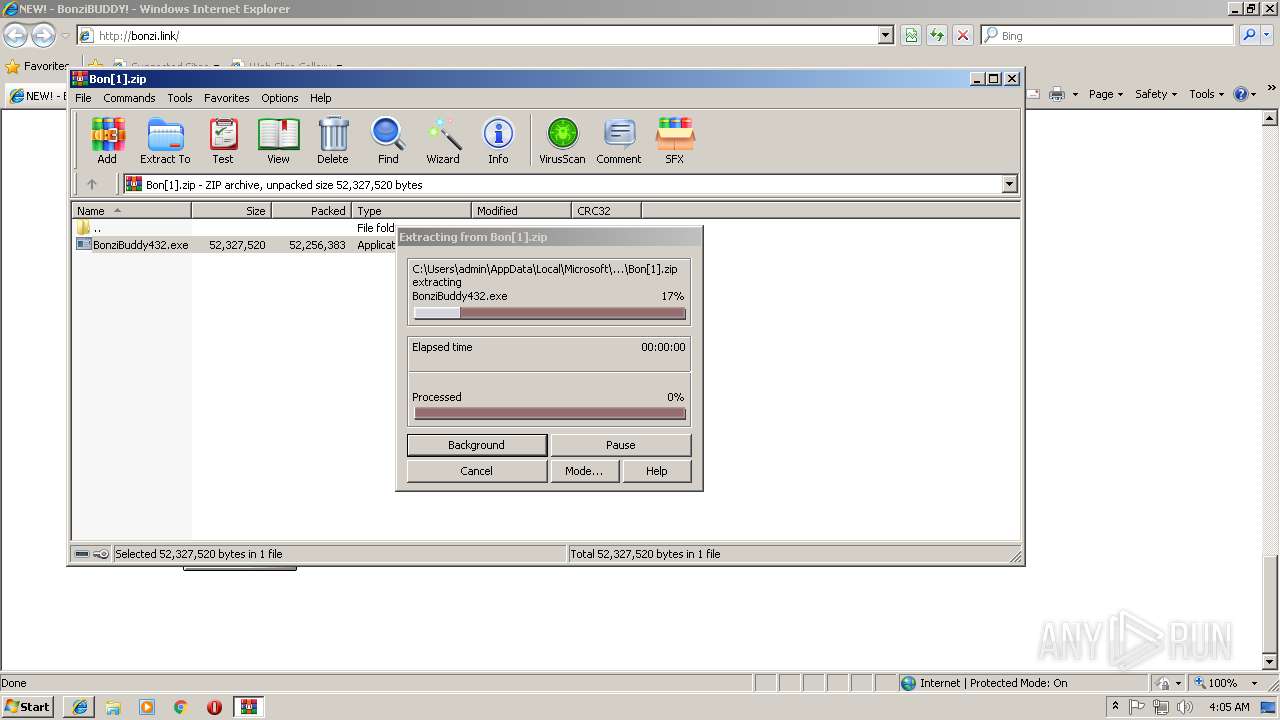
Executable content was dropped or overwritten
- BonziBuddy432.exe (PID: 2776)
- MSAGENT.EXE (PID: 1600)
- tv_enua.exe (PID: 3208)
Creates files in the Windows directory
- BonziBuddy432.exe (PID: 2776)
- MSAGENT.EXE (PID: 1600)
- tv_enua.exe (PID: 3208)
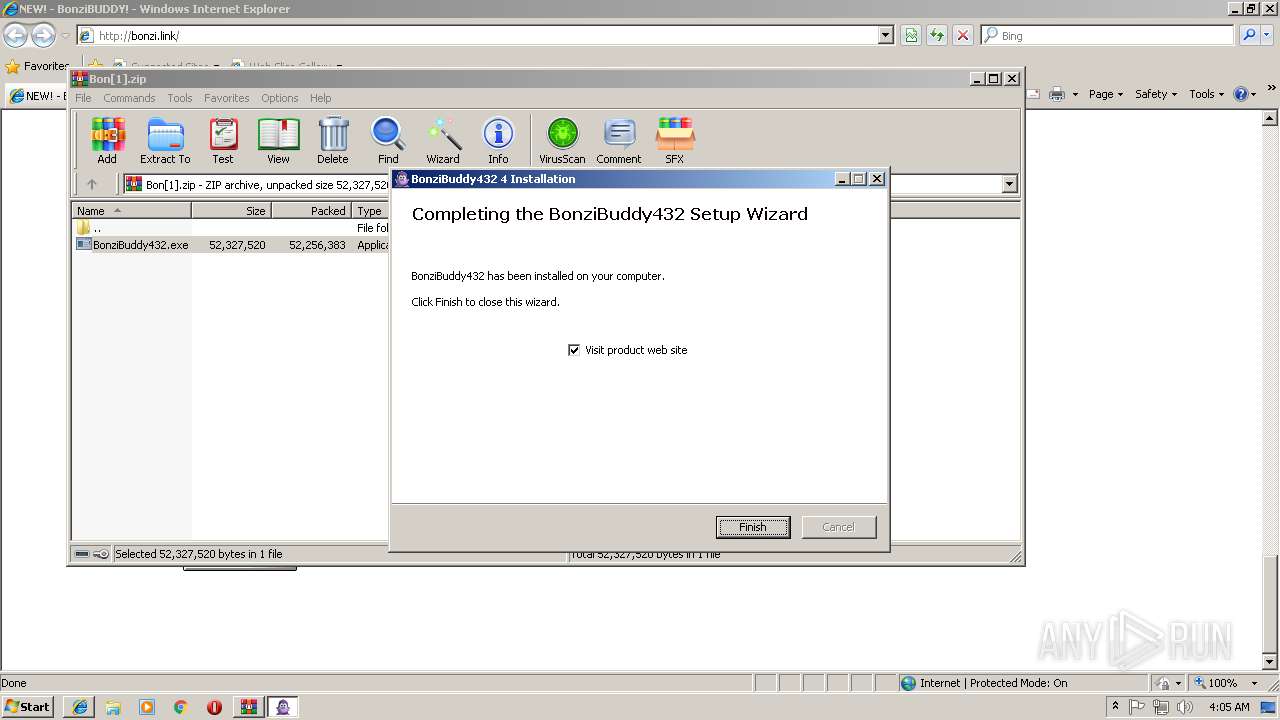
Creates a software uninstall entry
- BonziBuddy432.exe (PID: 2776)
- tv_enua.exe (PID: 3208)
Creates files in the user directory
- BonziBuddy432.exe (PID: 2776)
Starts CMD.EXE for commands execution
- BonziBuddy432.exe (PID: 2776)
Removes files from Windows directory
- MSAGENT.EXE (PID: 1600)
- tv_enua.exe (PID: 3208)
Creates COM task schedule object
- regsvr32.exe (PID: 1460)
- regsvr32.exe (PID: 3236)
- regsvr32.exe (PID: 3268)
- regsvr32.exe (PID: 1904)
- regsvr32.exe (PID: 3512)
- regsvr32.exe (PID: 1812)
- regsvr32.exe (PID: 3552)
- regsvr32.exe (PID: 3240)
- regsvr32.exe (PID: 1692)
Creates files in the program directory
- BonziBuddy432.exe (PID: 2776)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3584)
Reads Internet Cache Settings
- iexplore.exe (PID: 3868)
- iexplore.exe (PID: 116)
Reads internet explorer settings
- iexplore.exe (PID: 3868)
- iexplore.exe (PID: 116)
Creates files in the user directory
- iexplore.exe (PID: 3868)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1308)
- iexplore.exe (PID: 116)
Reads settings of System Certificates
- iexplore.exe (PID: 3868)
- iexplore.exe (PID: 3584)
Application launched itself
- iexplore.exe (PID: 3584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
22
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3584 CREDAT:6403 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 236 | cmd /c ""C:\Program Files\BonziBuddy432\Runtimes\CheckRuntimes.bat" " | C:\Windows\system32\cmd.exe | — | BonziBuddy432.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
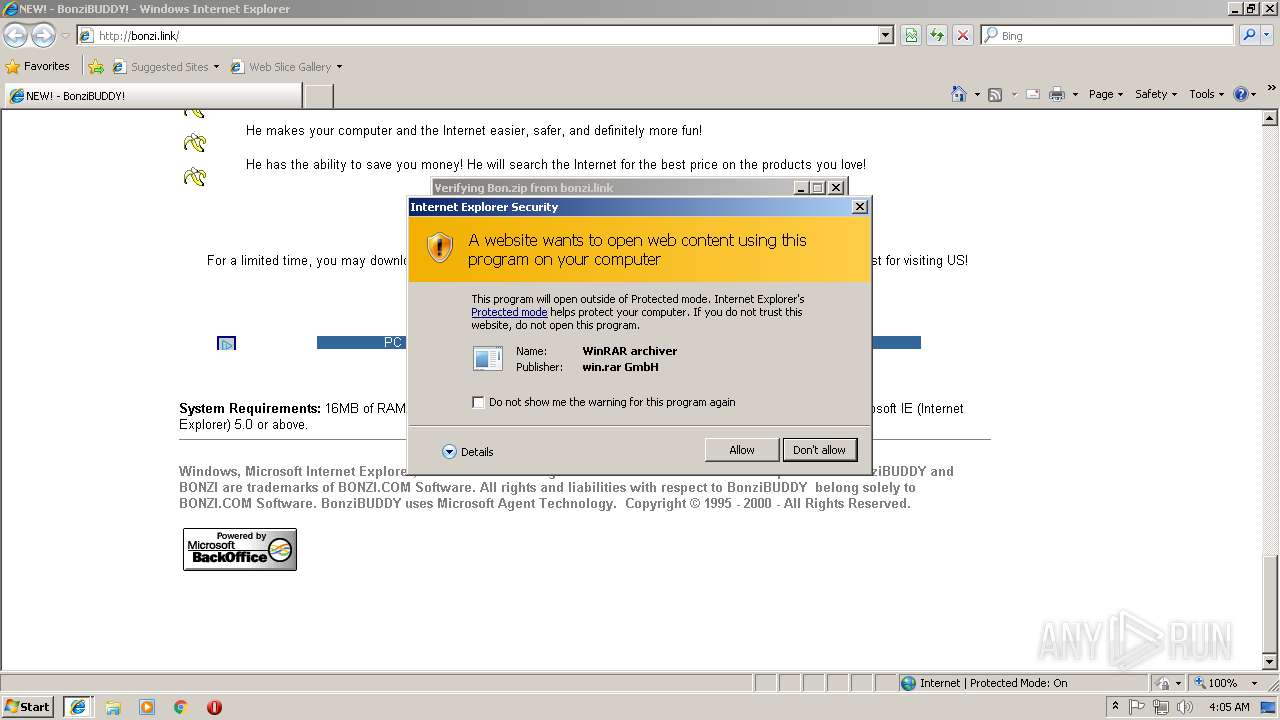
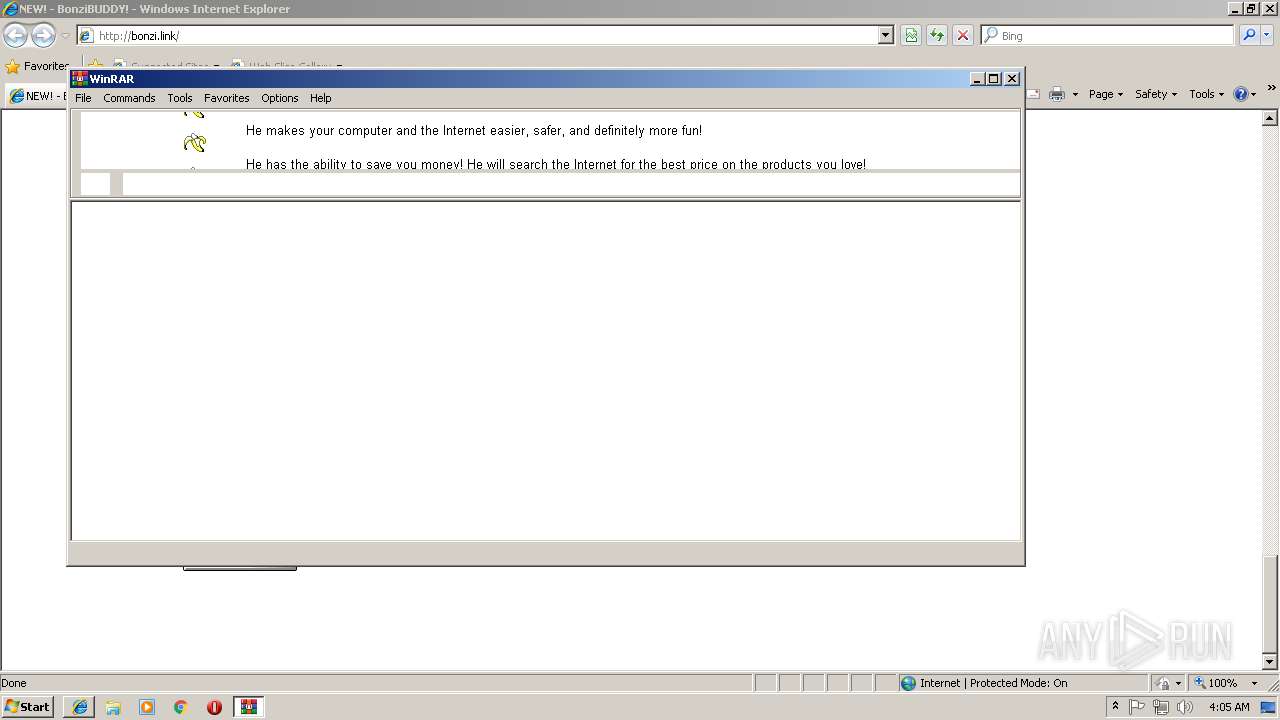
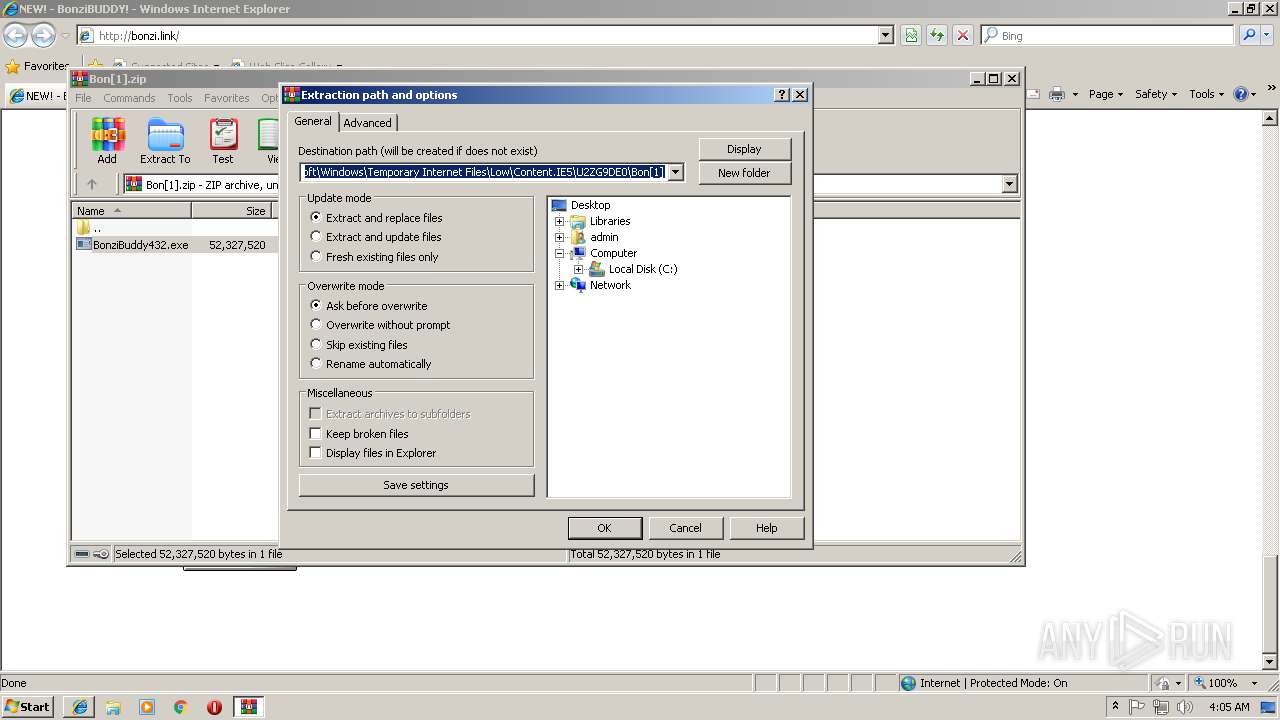
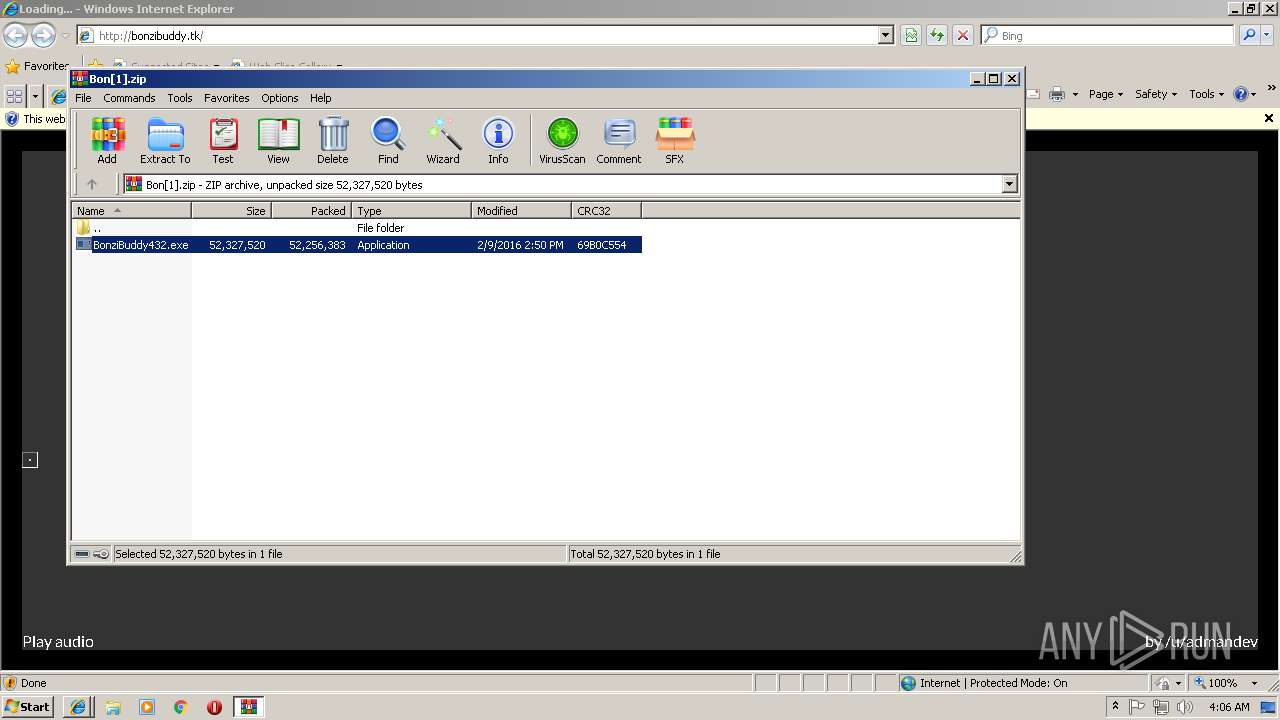
| 272 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\Bon[1].zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1308 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 1460 | regsvr32 /s "C:\Windows\msagent\AgentCtl.dll" | C:\Windows\system32\regsvr32.exe | — | MSAGENT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | grpconv.exe -o | C:\Windows\system32\grpconv.exe | — | tv_enua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1600 | MSAGENT.EXE | C:\Program Files\BonziBuddy432\Runtimes\MSAGENT.EXE | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.71.1015.0 Modules
| |||||||||||||||
| 1692 | regsvr32 /s "C:\Windows\msagent\AgentSR.dll" | C:\Windows\system32\regsvr32.exe | — | MSAGENT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1812 | regsvr32 /s "C:\Windows\msagent\AgentMPx.dll" | C:\Windows\system32\regsvr32.exe | — | MSAGENT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | regsvr32 /s "C:\Windows\msagent\AgentDPv.dll" | C:\Windows\system32\regsvr32.exe | — | MSAGENT.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 718
Read events
1 901
Write events
1 751
Delete events
66
Modification events
| (PID) Process: | (3584) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3584) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3584) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3584) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3584) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3584) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005F000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3584) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {47294CF7-BE14-11E8-BFAB-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (3584) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3584) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3584) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070900060016000300040037005401 | |||
Executable files
68
Suspicious files
23
Text files
206
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3868 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\f[1].txt | text | |
MD5:421A64D09C4786634BF3A5FEA7154809 | SHA256:B33235FA19DC2B9F183092E4AAD80554427E2BE8ECD6401724C23F8AEC24909C | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 3868 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\DOMStore\index.dat | dat | |
MD5:61C2FE8186BFE5E751F01AD5954E0C3B | SHA256:3B5BFF441BEFF3DABE566E9115BD989F963BA3A55FEE347E216D813F72C3A04D | |||
| 3868 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\download[1].gif | image | |
MD5:4B1C229D42D8604A214C6A6799AAA868 | SHA256:820701D14CAD06E81EB0FEC257AEB9A384CB55F8C9946F3D94FA7322043542E7 | |||
| 3868 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\sepbar[1].jpg | image | |
MD5:F6FCE4E768B316D08877AD56DE0037DA | SHA256:5639B593EC413C89628E70906F615AD36FE8AC78754A58A56A71152751306483 | |||
| 3868 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\bbvine[1].gif | image | |
MD5:C1F1DF26B445100C74EFF268CAA3112F | SHA256:58D0BF159A3DF8BBDE468999B349AE0DF54820936A4D5F089754B1DE54B8D260 | |||
| 3868 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\bbmail[1].gif | image | |
MD5:B34F8EB666476E3B8D6DEE6C3C61CA5F | SHA256:F8DB7B8A83AB68B181271C2A877A2D436A2357ABEBAC9DBD8C8203105646D432 | |||
| 3868 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\f[2].txt | text | |
MD5:00523766B66DD52984D5A09BF6021CDC | SHA256:B4101D77ACB26394850AA7C7DF0348072384D1684A5BD70DBCB41FD7583CD5E8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
64
DNS requests
29
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
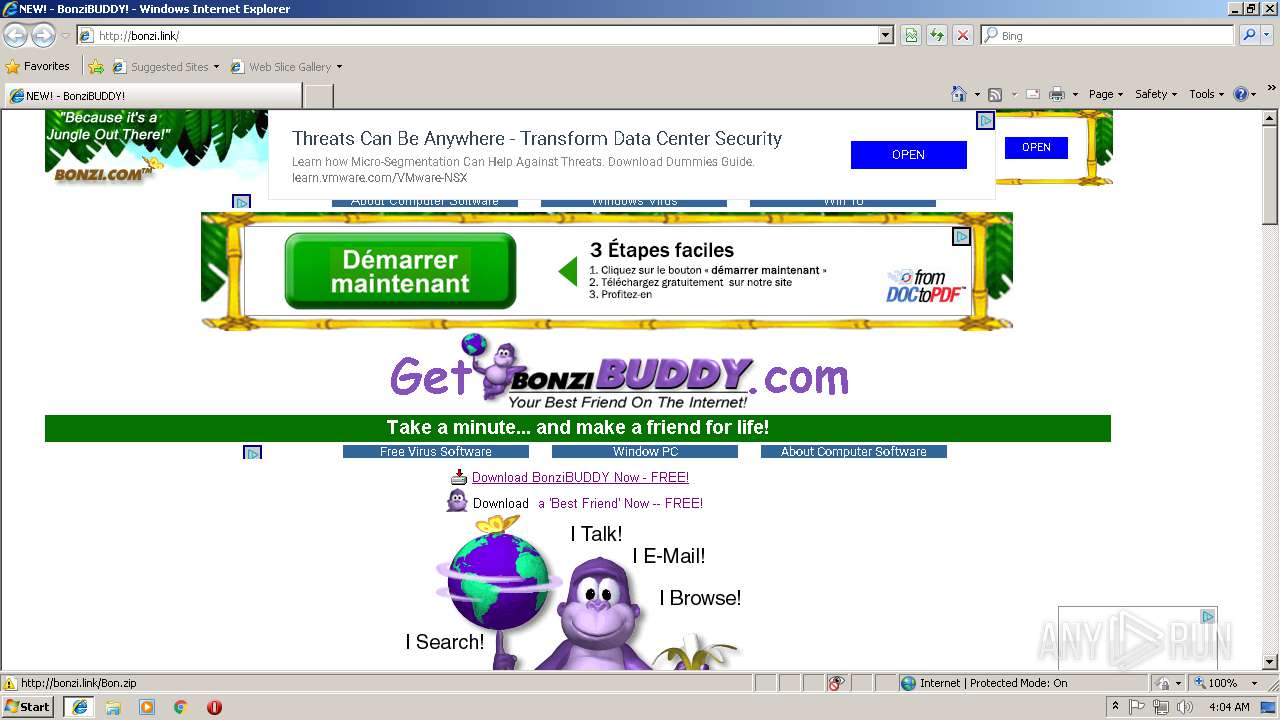
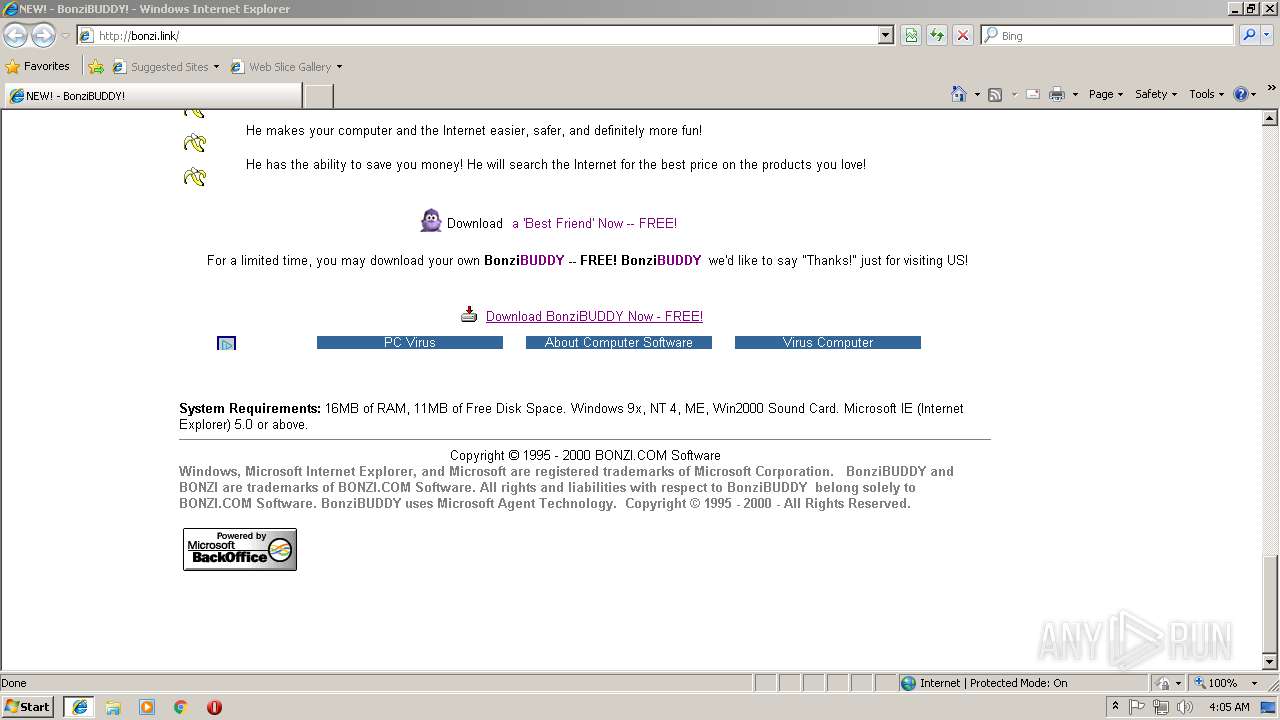
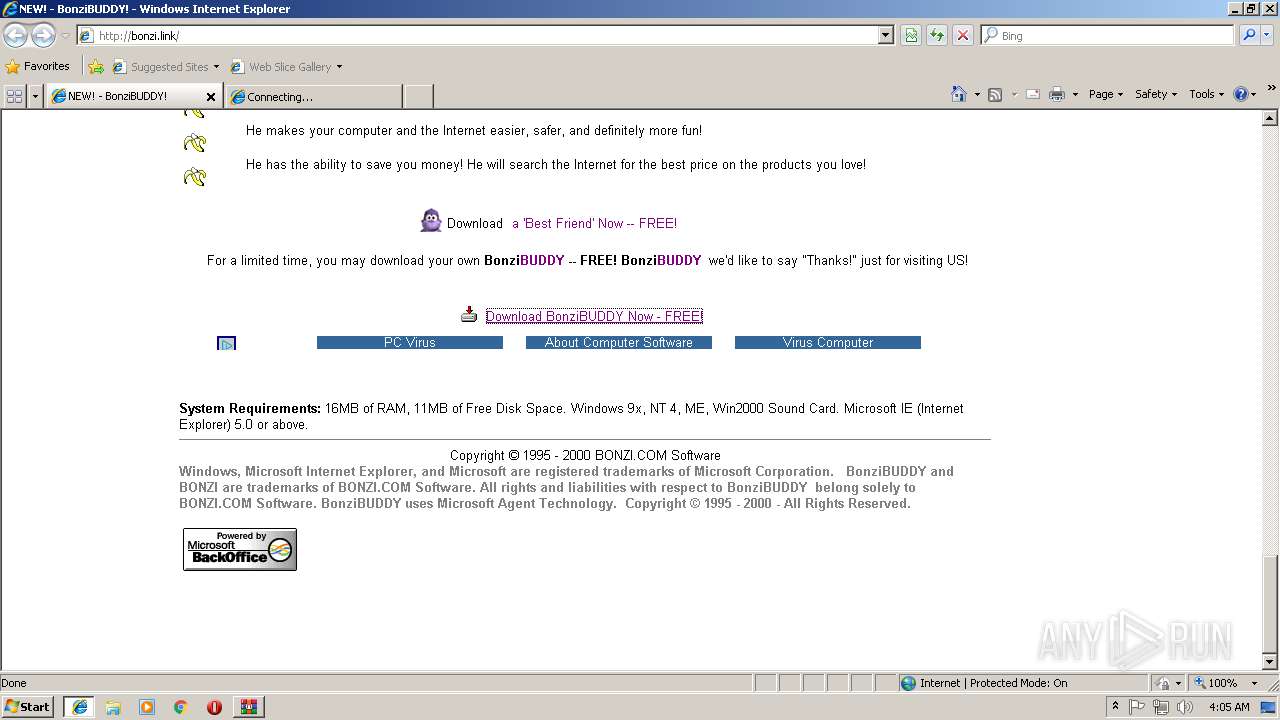
3868 | iexplore.exe | GET | 302 | 77.72.0.110:80 | http://bonzi.link/Bon.zip | GB | html | 1.10 Kb | suspicious |
3584 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3868 | iexplore.exe | GET | 200 | 77.72.0.110:80 | http://bonzi.link/images/download.gif | GB | image | 151 b | suspicious |
3868 | iexplore.exe | GET | 200 | 77.72.0.110:80 | http://bonzi.link/images/bbmail.gif | GB | image | 23.0 Kb | suspicious |
3868 | iexplore.exe | GET | 200 | 77.72.0.110:80 | http://bonzi.link/ | GB | html | 4.13 Kb | suspicious |
3868 | iexplore.exe | GET | 200 | 77.72.0.110:80 | http://bonzi.link/images/bbabilities2.gif | GB | image | 24.8 Kb | suspicious |
3868 | iexplore.exe | GET | 200 | 216.58.210.2:80 | http://pagead2.googlesyndication.com/pagead/show_ads.js | US | text | 19.8 Kb | whitelisted |
3868 | iexplore.exe | GET | 200 | 77.72.0.110:80 | http://bonzi.link/images/bonz24.gif | GB | image | 613 b | suspicious |
3868 | iexplore.exe | GET | 200 | 77.72.0.110:80 | http://bonzi.link/images/bbvine.gif | GB | image | 4.59 Kb | suspicious |
3868 | iexplore.exe | GET | 200 | 216.58.210.2:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 26.8 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3584 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3868 | iexplore.exe | 216.58.210.2:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3868 | iexplore.exe | 77.72.0.110:80 | bonzi.link | Krystal Hosting Ltd | GB | suspicious |
3868 | iexplore.exe | 216.58.210.2:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3868 | iexplore.exe | 172.217.16.194:443 | adservice.google.fr | Google Inc. | US | whitelisted |
3868 | iexplore.exe | 172.217.22.2:443 | adservice.google.com | Google Inc. | US | whitelisted |
3868 | iexplore.exe | 216.58.207.34:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
3868 | iexplore.exe | 13.32.222.195:443 | d36ee2fcip1434.cloudfront.net | Amazon.com, Inc. | US | unknown |
3868 | iexplore.exe | 52.0.141.183:443 | track.gaug.es | Amazon.com, Inc. | US | unknown |
3868 | iexplore.exe | 172.217.21.225:443 | tpc.googlesyndication.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
bonzi.link |
| suspicious |
pagead2.googlesyndication.com |
| whitelisted |
adservice.google.fr |
| whitelisted |
adservice.google.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
d36ee2fcip1434.cloudfront.net |
| shared |
track.gaug.es |
| unknown |
tpc.googlesyndication.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
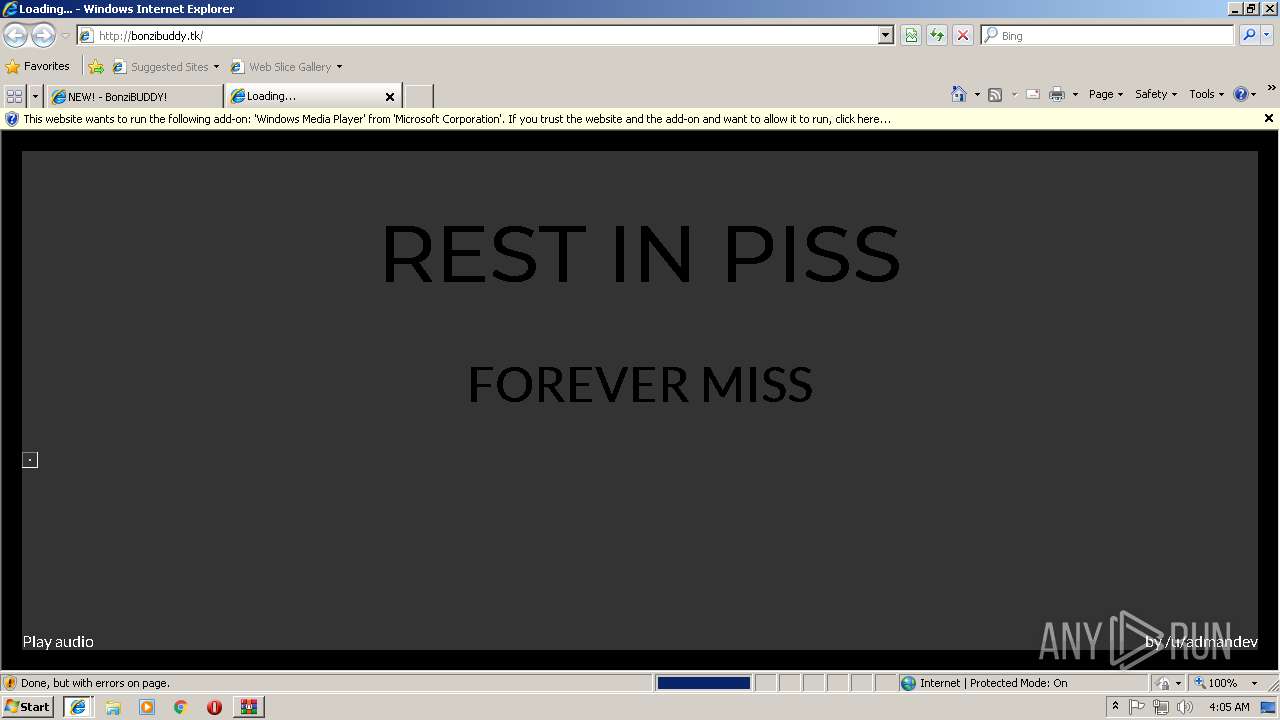
116 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
116 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
116 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
116 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
116 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
116 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
3584 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |