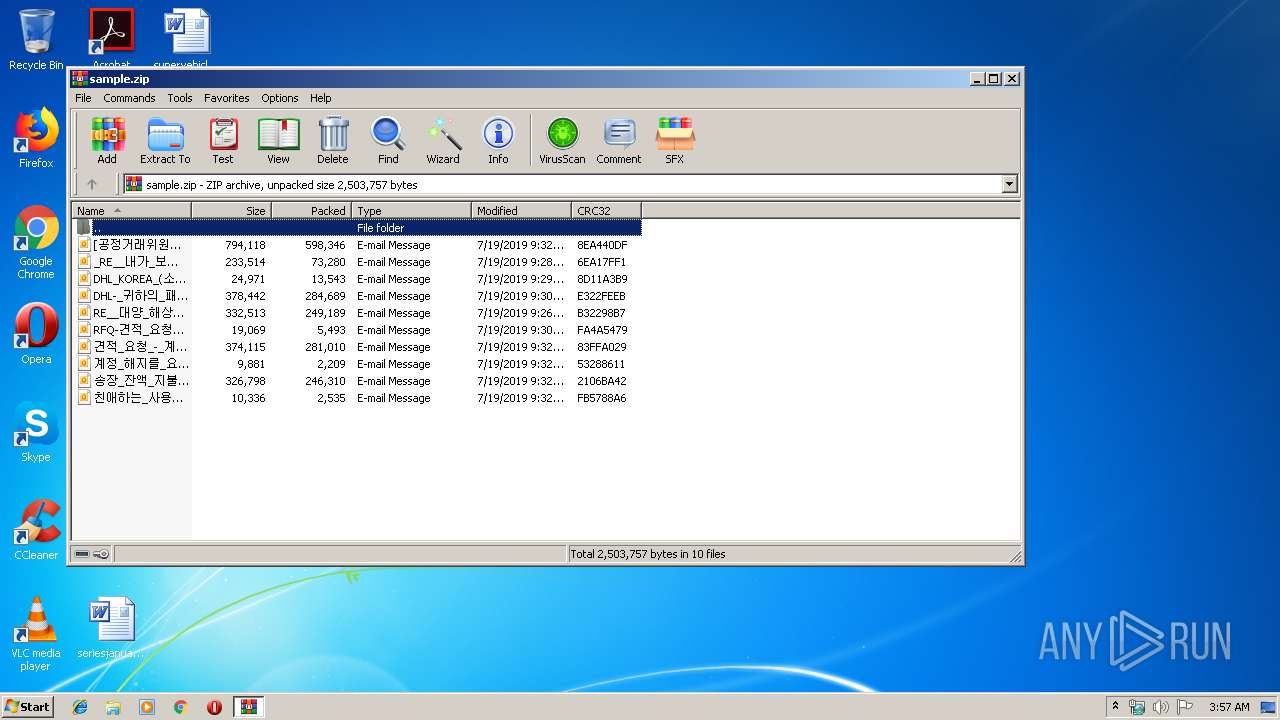
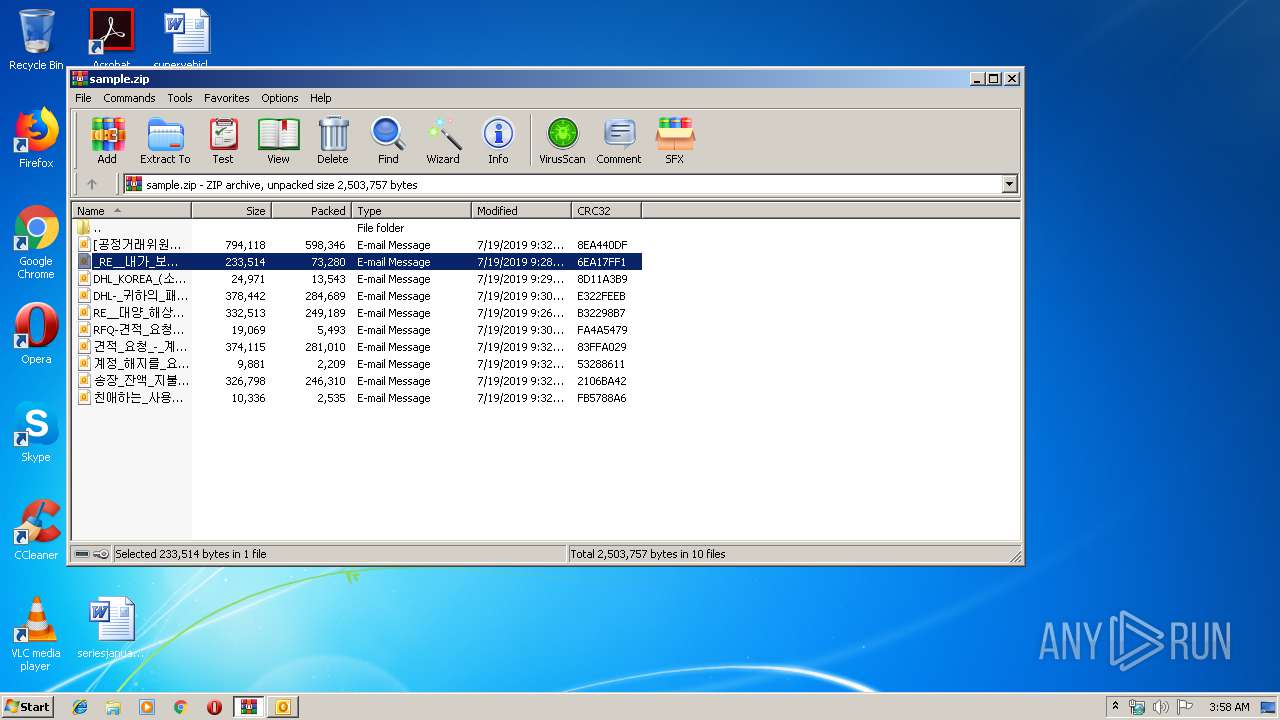
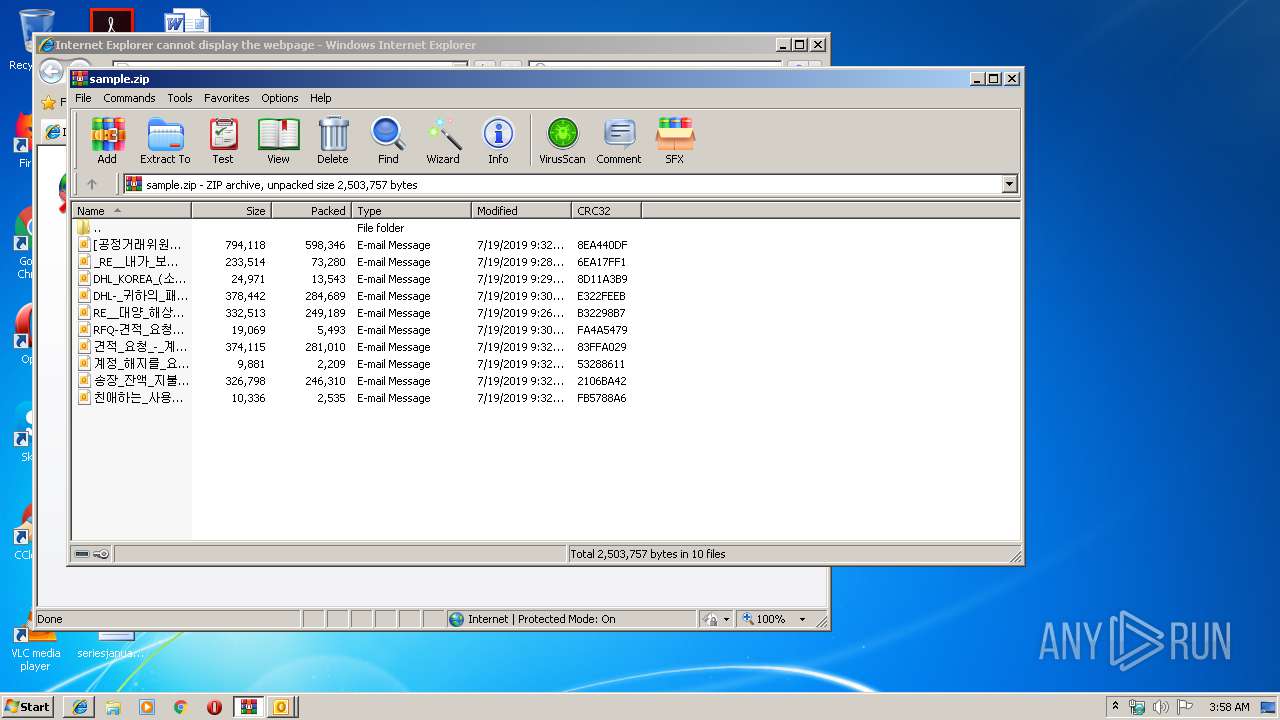
| File name: | sample.zip |
| Full analysis: | https://app.any.run/tasks/10f7ad5b-cc65-4a77-a908-eec2bcc07eb5 |
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2019, 02:57:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F795DF8A0DA8D41A1BAB6ABD849069AB |
| SHA1: | EE01E019F6B3BF9D03D8D4F5A396F98C35DB34B2 |
| SHA256: | E43026AF2858B2A0CE40E0836A24F554640016841C60041DCAB73E534279A304 |
| SSDEEP: | 49152:6EwSnmT8k2QbRyMwAGu8PEE6LXIt/FKSotb1ZB:nwomTz2Qbf9MEE6LYE1/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3144)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3144)
Reads internet explorer settings
- prevhost.exe (PID: 2464)
Executed via COM
- prevhost.exe (PID: 2464)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3520)
- iexplore.exe (PID: 2832)
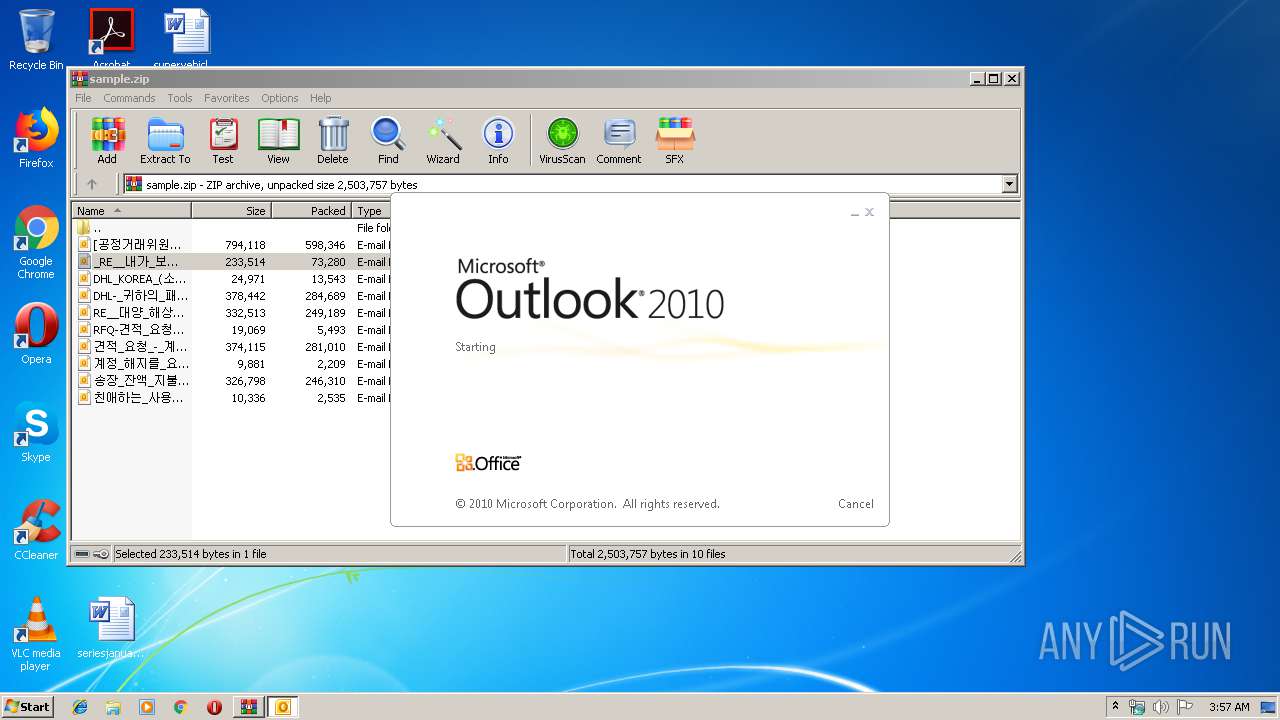
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2152)
- OUTLOOK.EXE (PID: 3144)
- OUTLOOK.EXE (PID: 3876)
Reads internet explorer settings
- iexplore.exe (PID: 3520)
- iexplore.exe (PID: 2832)
Changes internet zones settings
- iexplore.exe (PID: 2840)
- iexplore.exe (PID: 3868)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3548)
Application launched itself
- iexplore.exe (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:07:19 17:32:16 |
| ZipCRC: | 0x8ea440df |
| ZipCompressedSize: | 598346 |
| ZipUncompressedSize: | 794118 |
| ZipFileName: | [?????ŷ?????ȸ]_???ڻ??ŷ?_??%UFFFD%UFFFD????_??????????(2019.07.12).eml |
Total processes
43
Monitored processes
9
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
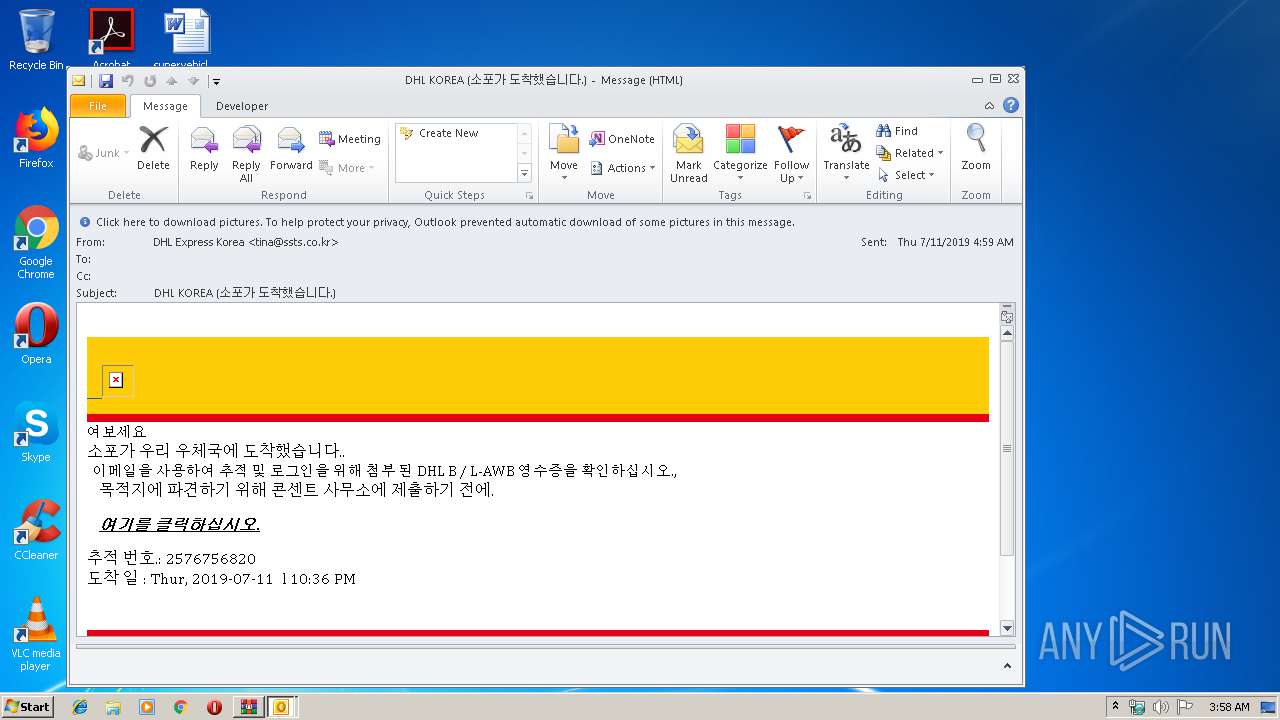
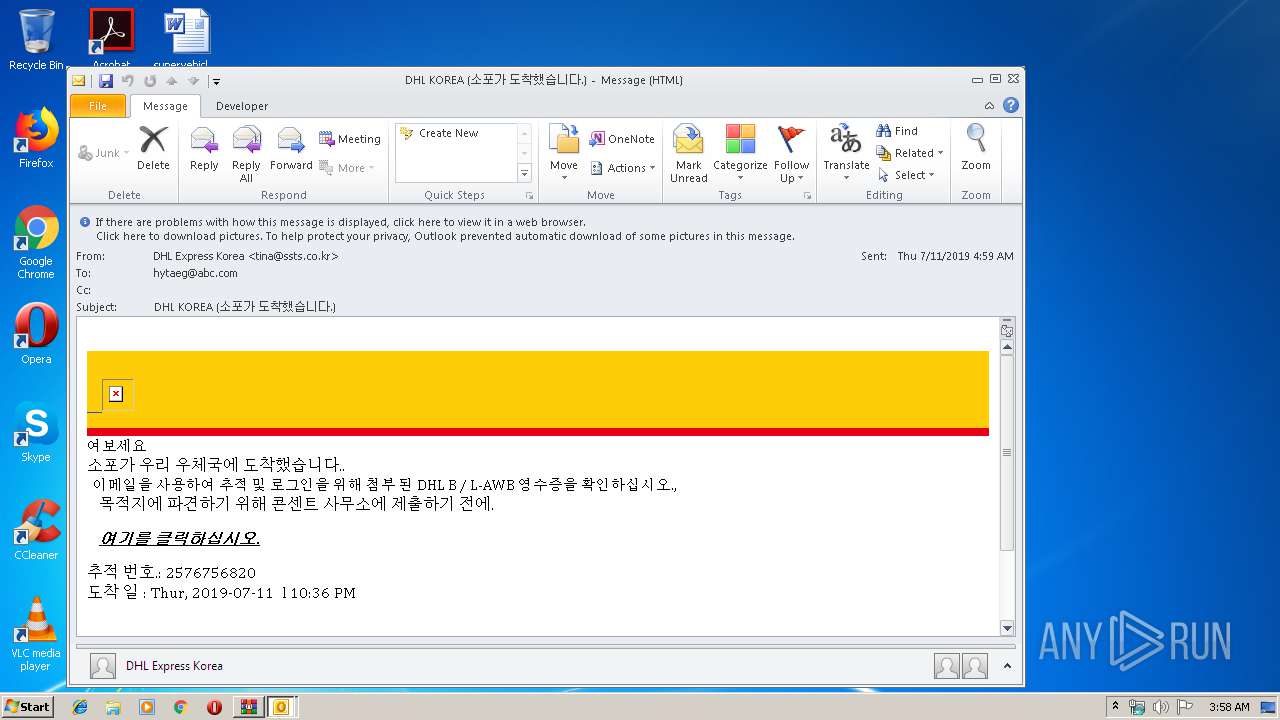
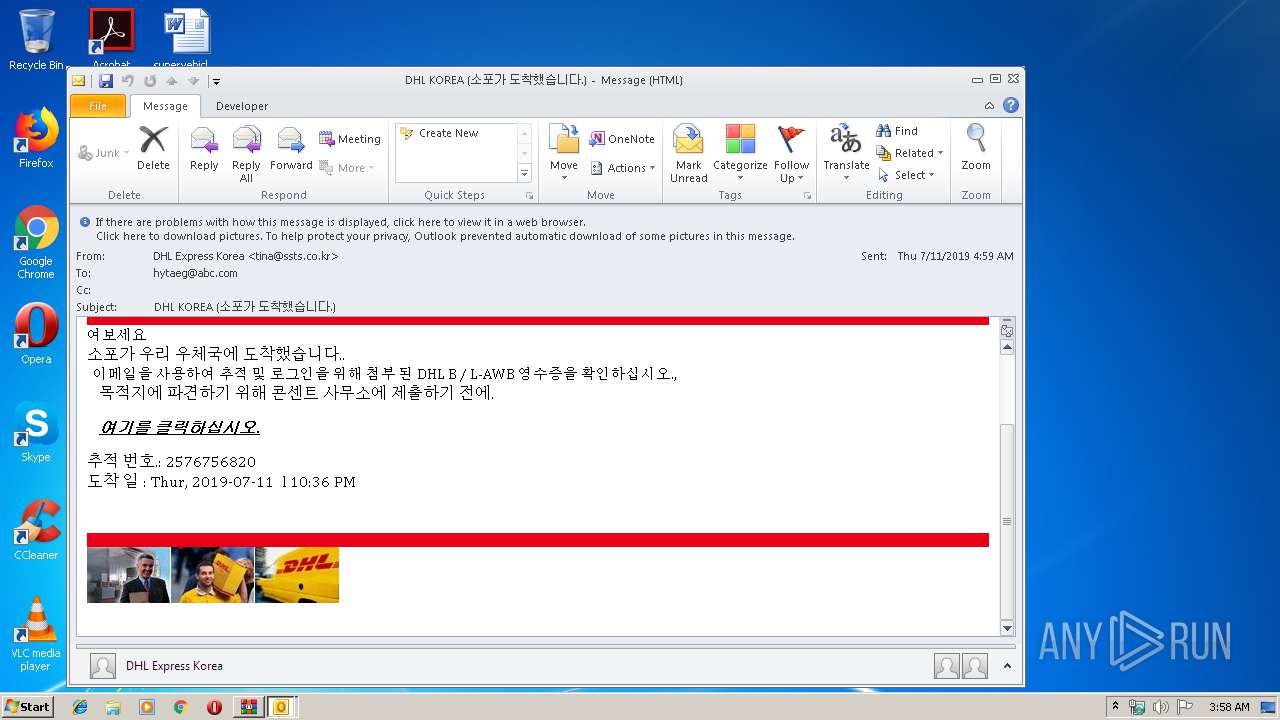
| 2152 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Rar$DIa3548.30725\DHL_KOREA_(소포가_도착했습니다.).eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2464 | C:\Windows\system32\prevhost.exe {F8B8412B-DEA3-4130-B36C-5E8BE73106AC} -Embedding | C:\Windows\system32\prevhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Preview Handler Surrogate Host Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3868 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Internet Explorer\iexplore.exe" http://bigfile.mail.naver.com/bigfileupload/download?fid=MmYjDBFq1rYlFA2wFIYZKA2jKogwaxgXKxgwFAUwKAKjKxErFxKrKobla3Ywax34MxU/MrJCM6UqMou/MoiopAtlaxMmM6JSp4i0Mt== | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
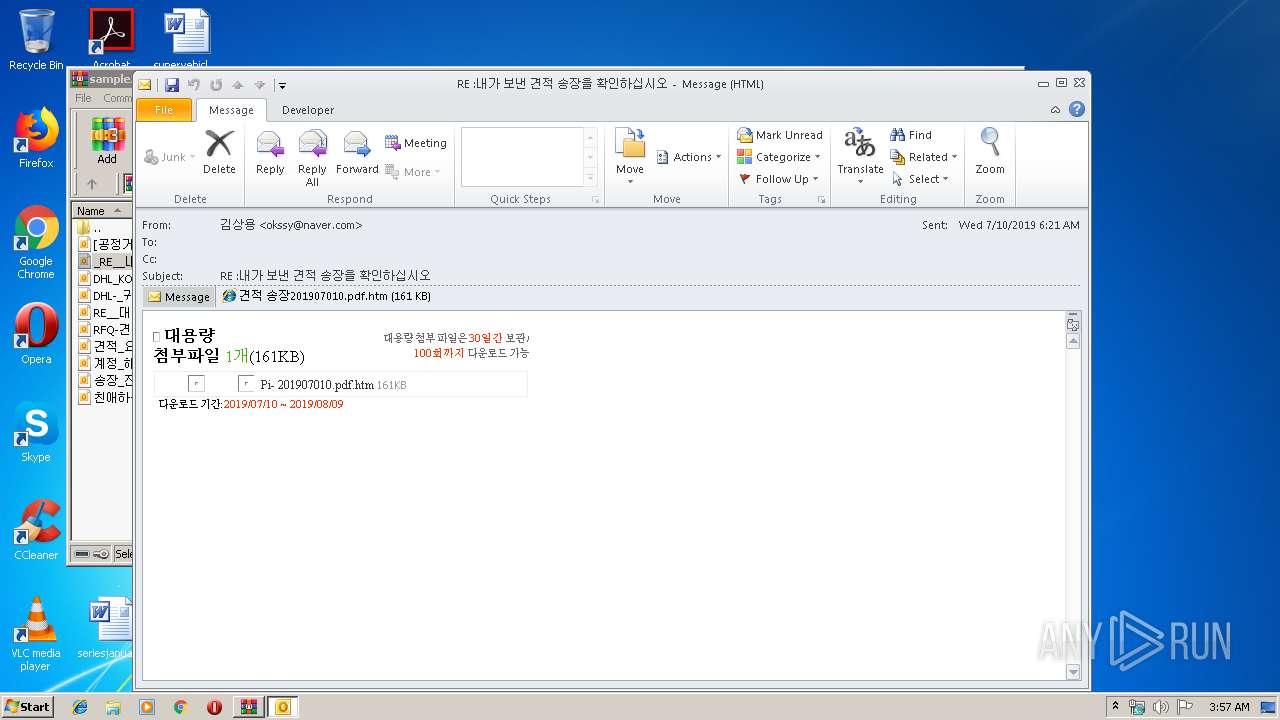
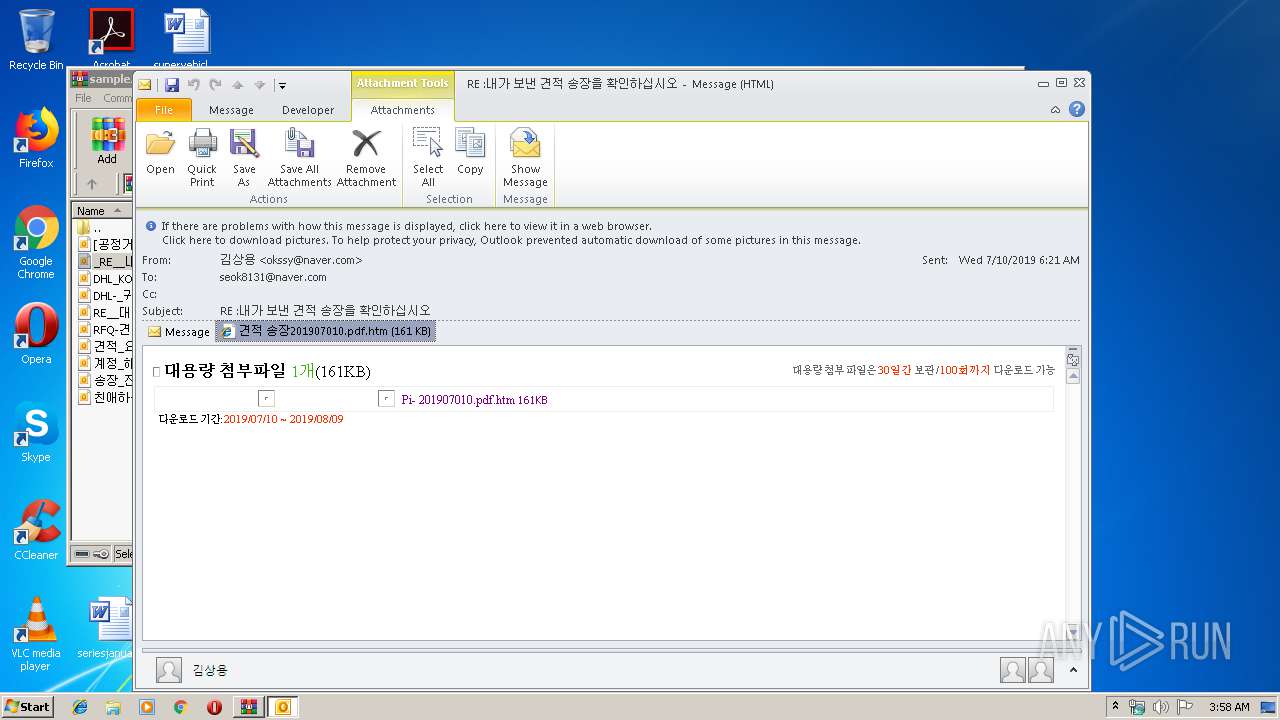
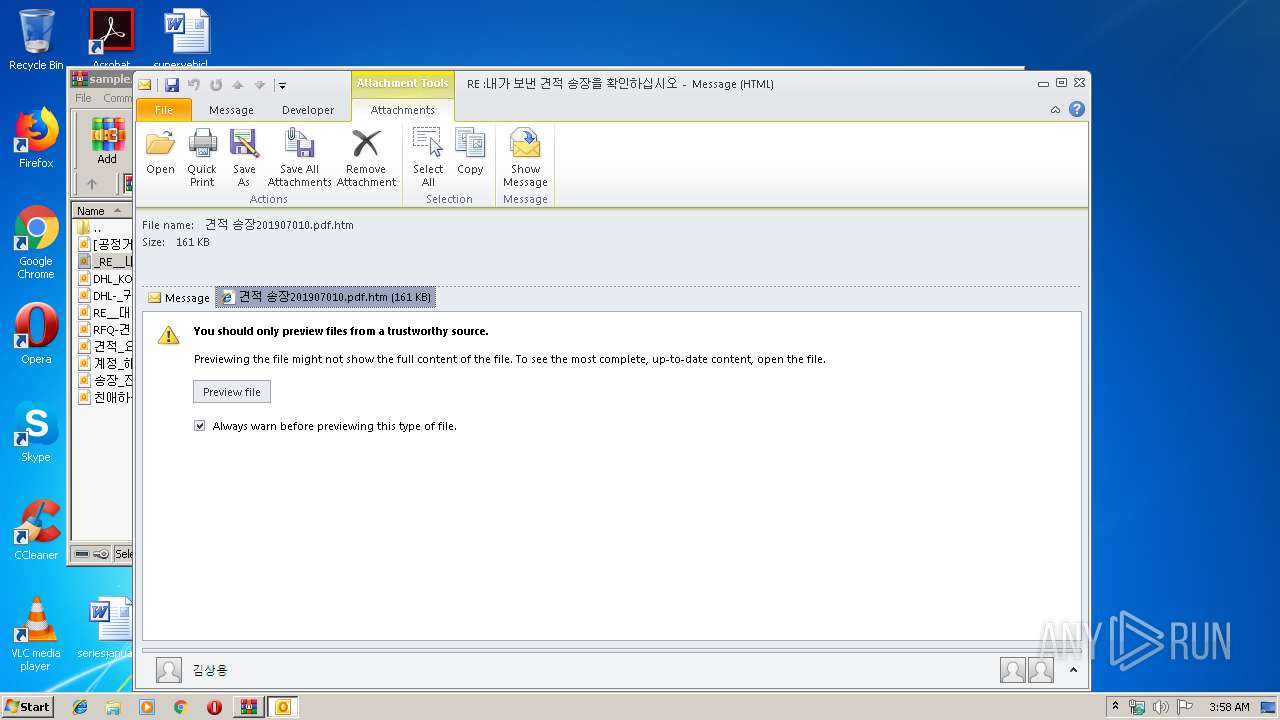
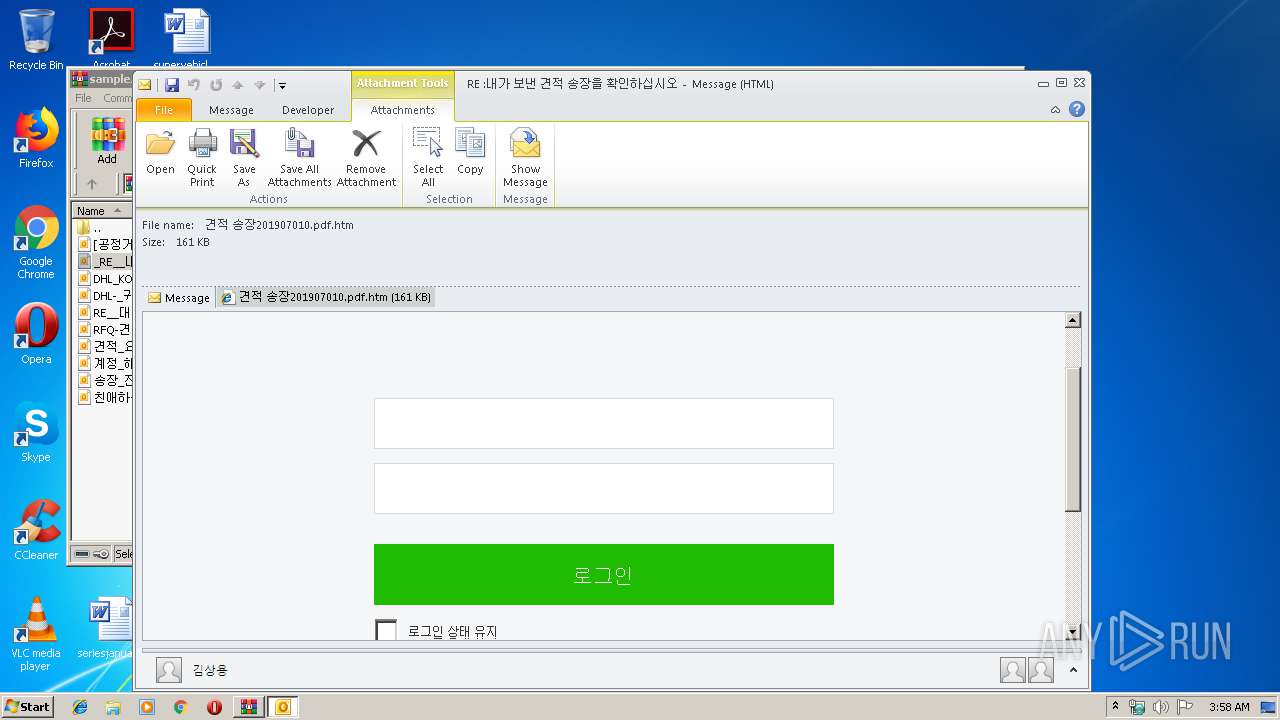
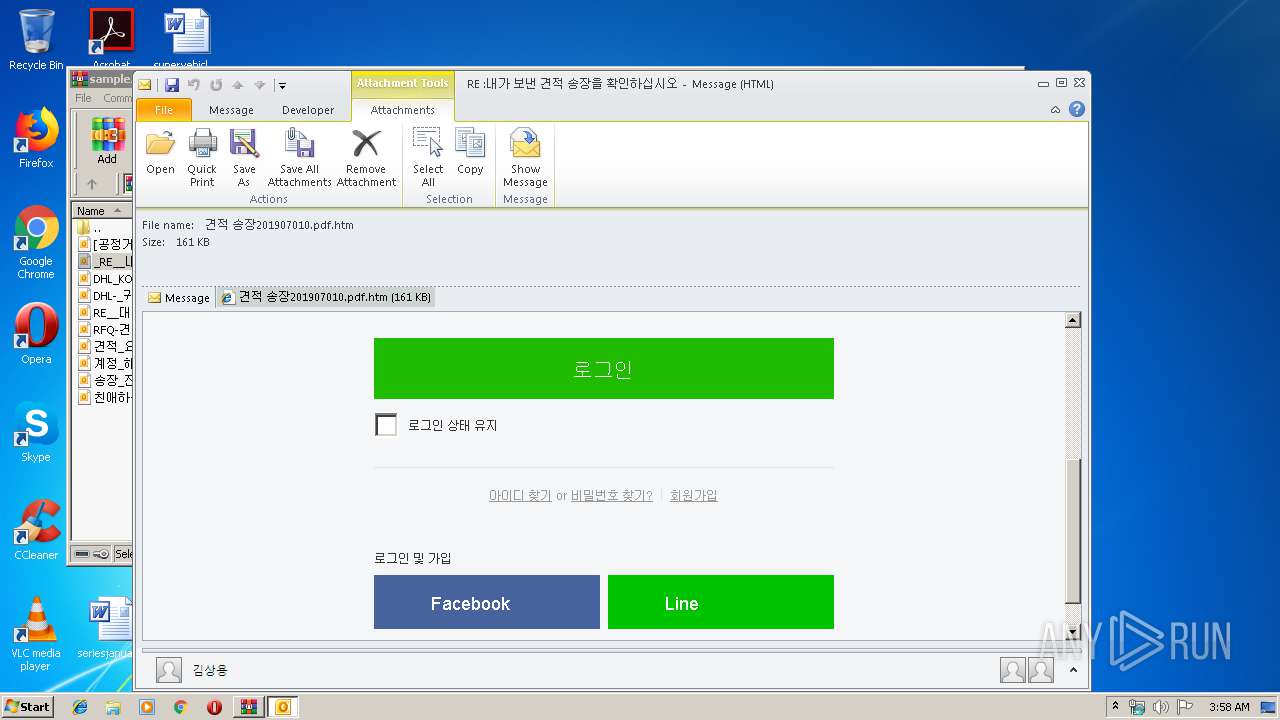
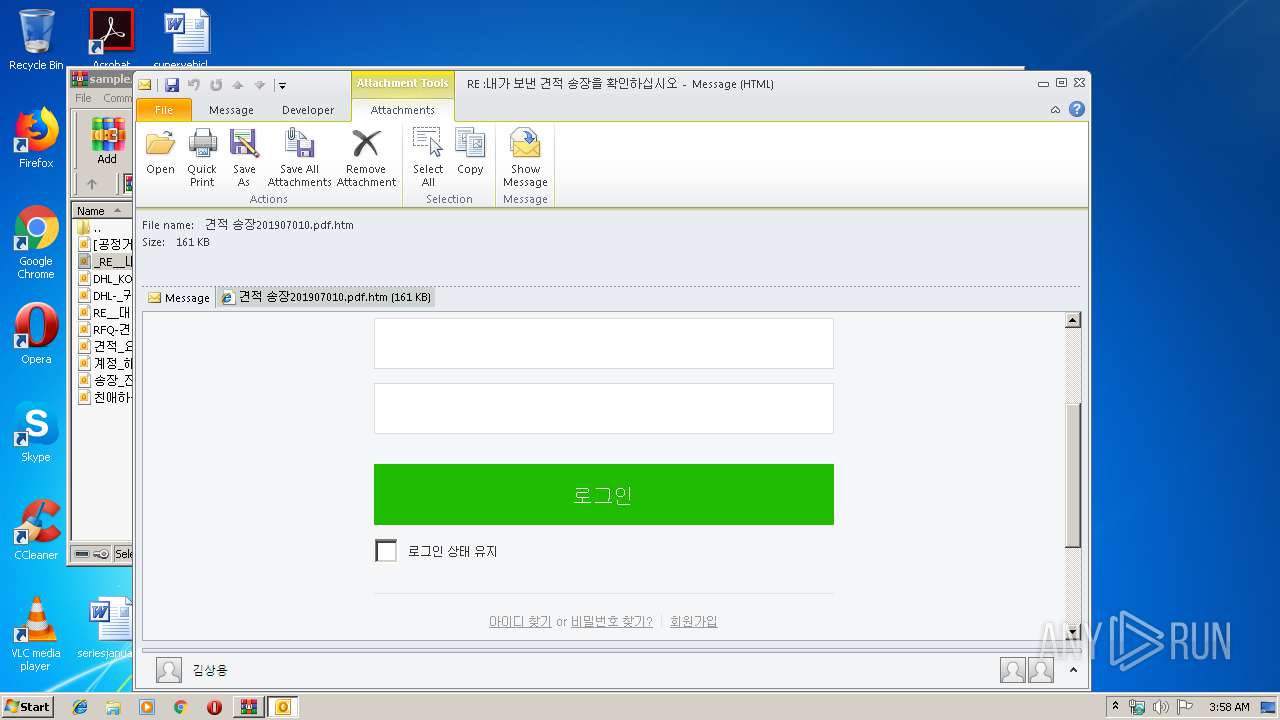
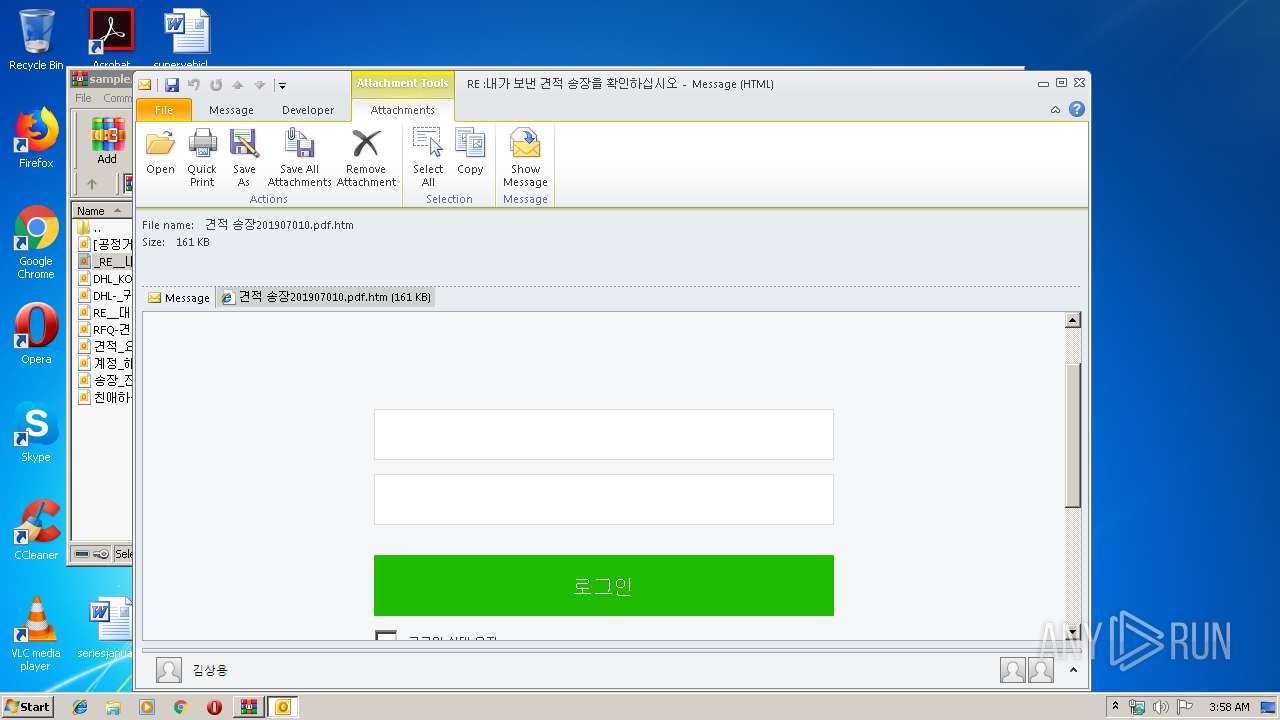
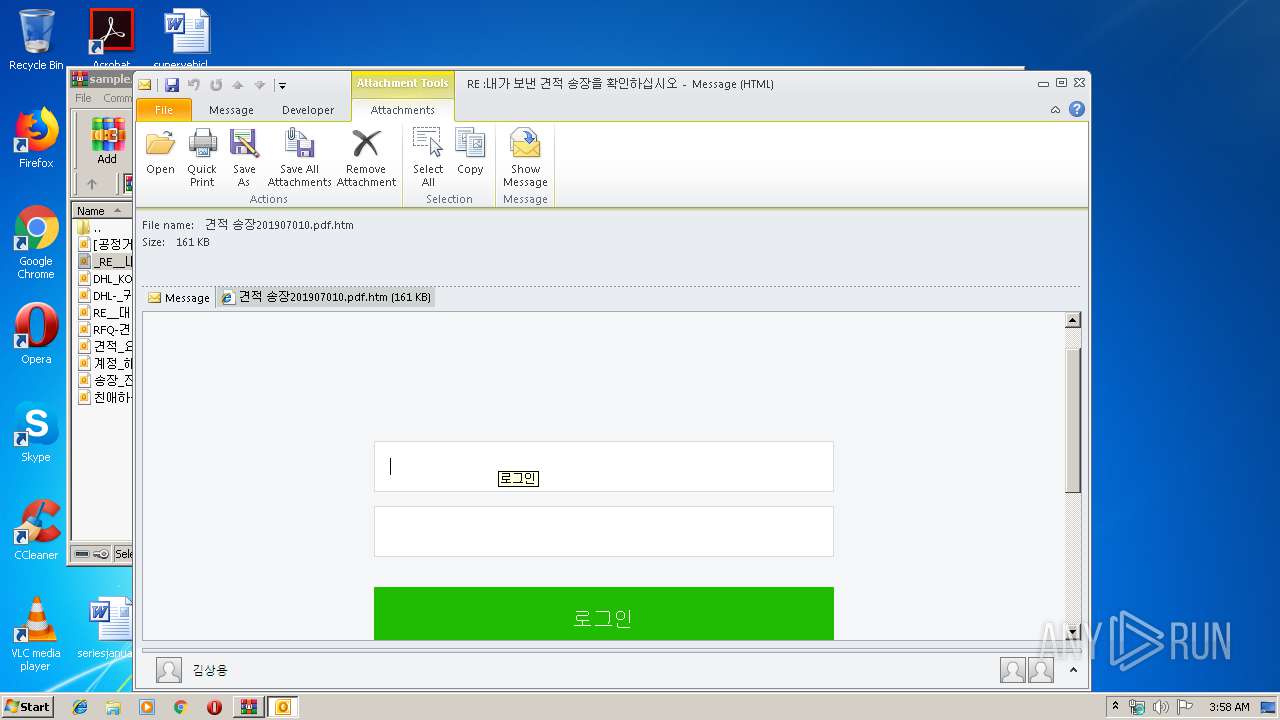
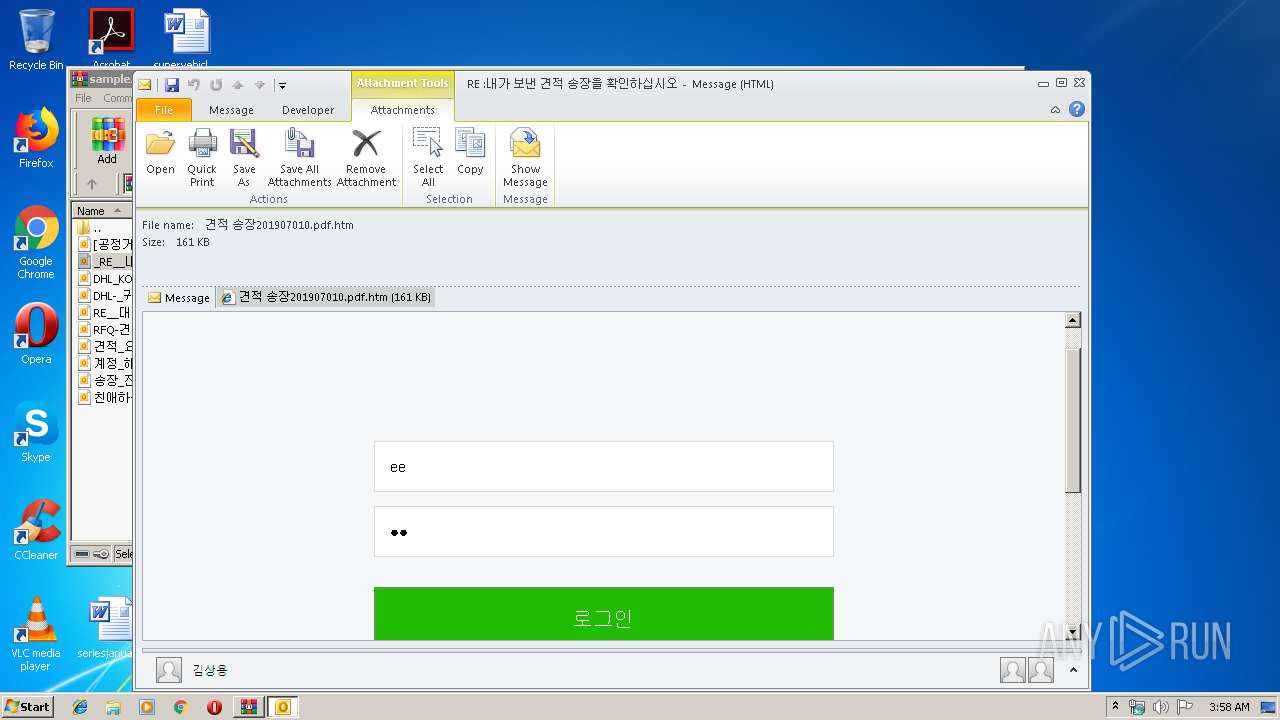
| 3144 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Rar$DIa3548.27163\_RE__내가_보낸_견적_송장을_확인하십시오.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3520 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2840 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3548 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
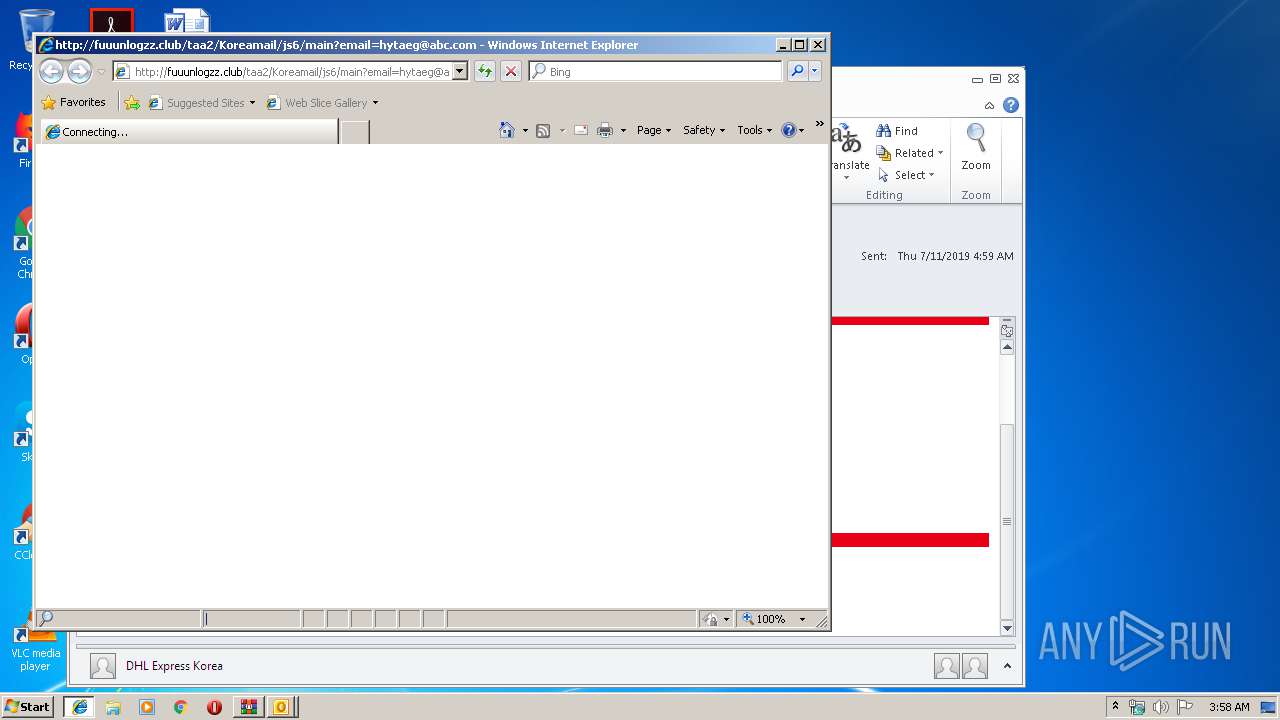
| 3868 | "C:\Program Files\Internet Explorer\iexplore.exe" http://fuuunlogzz.club/taa2/Koreamail/js6/main?email=hytaeg@abc.com | C:\Program Files\Internet Explorer\iexplore.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
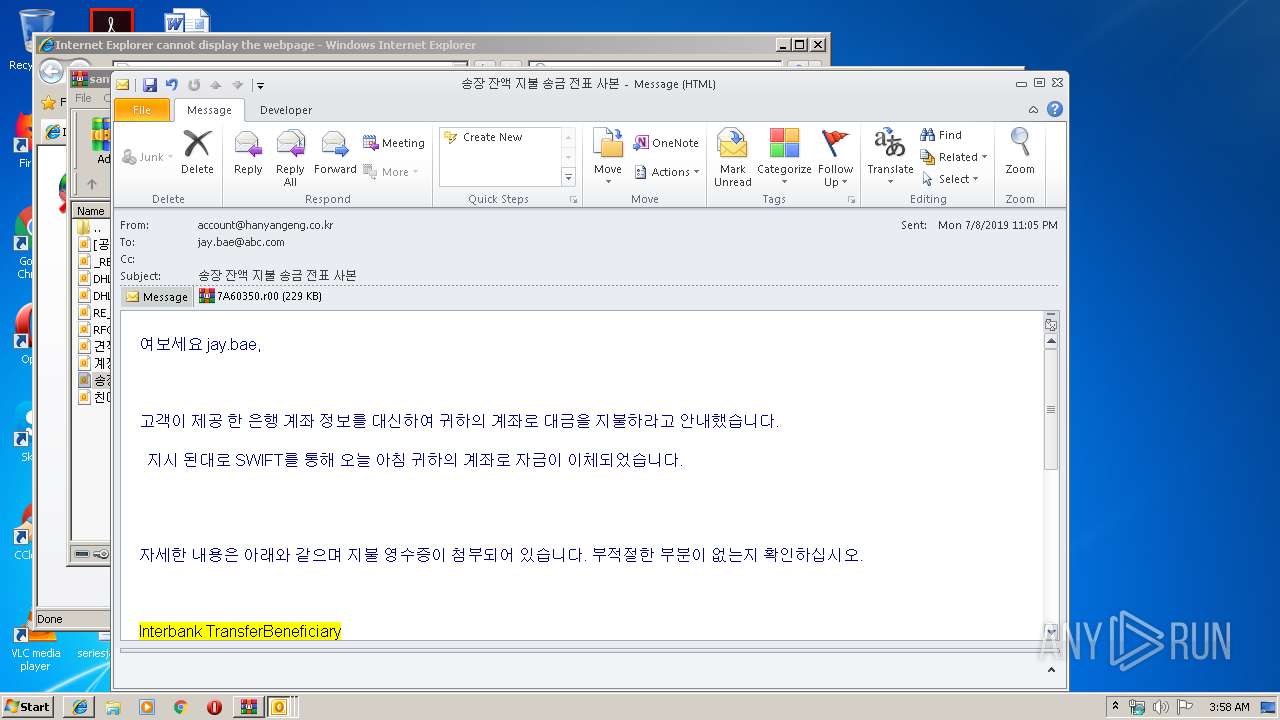
| 3876 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Rar$DIa3548.31941\송장_잔액_지불_송금_전표_사본.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
2 537
Read events
1 989
Write events
524
Delete events
24
Modification events
| (PID) Process: | (3548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3548) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample.zip | |||
| (PID) Process: | (3548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3144) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3144) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
Executable files
0
Suspicious files
2
Text files
48
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3144 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRB078.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3144 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpB2AC.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFDD85896CB4E1B45B.TMP | — | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{4DCB4EB4-C7AD-11E9-B86F-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3548.27163\_RE__내가_보낸_견적_송장을_확인하십시오.eml | text | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFEE77C42C4F9443F0.TMP | — | |
MD5:— | SHA256:— | |||
| 2840 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{4DCB4EB3-C7AD-11E9-B86F-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3520 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3144 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
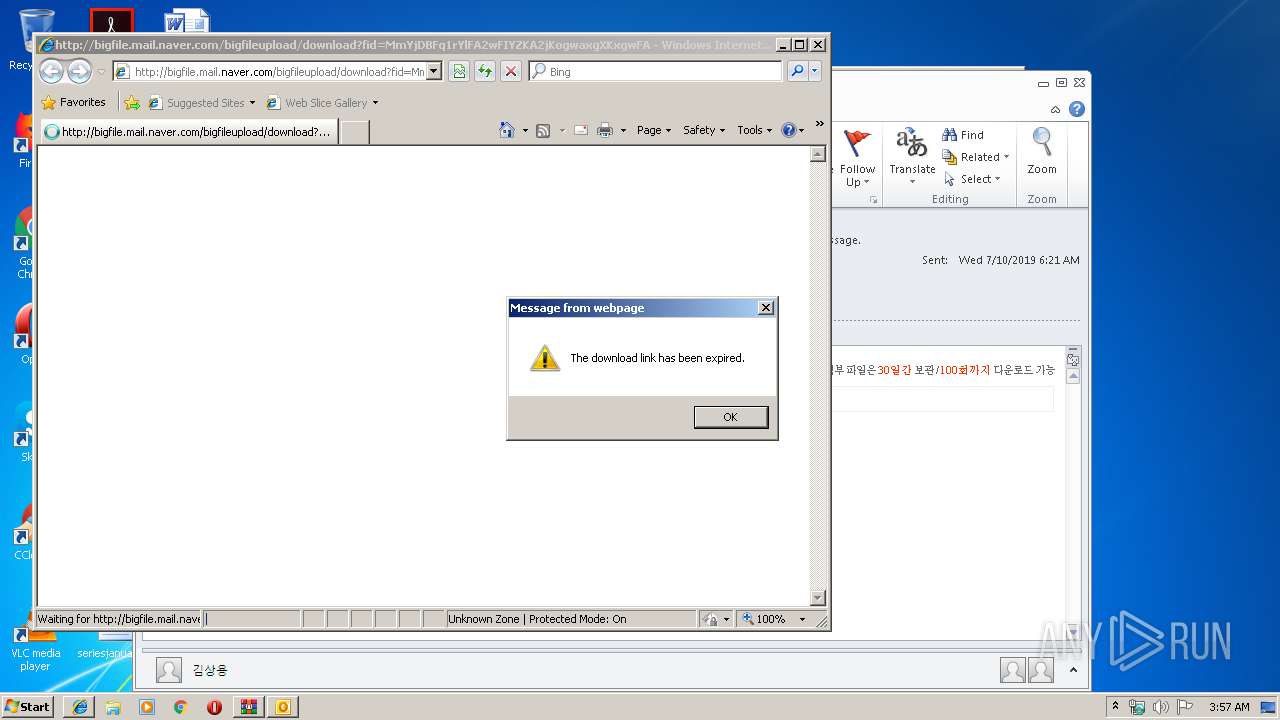
3520 | iexplore.exe | GET | 200 | 125.209.234.99:80 | http://bigfile.mail.naver.com/bigfileupload/download?fid=MmYjDBFq1rYlFA2wFIYZKA2jKogwaxgXKxgwFAUwKAKjKxErFxKrKobla3Ywax34MxU/MrJCM6UqMou/MoiopAtlaxMmM6JSp4i0Mt== | KR | html | 171 b | suspicious |
2840 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3520 | iexplore.exe | 125.209.234.99:80 | bigfile.mail.naver.com | NBP | KR | malicious |
3144 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2840 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
bigfile.mail.naver.com |
| suspicious |
www.bing.com |
| whitelisted |
fuuunlogzz.club |
| unknown |