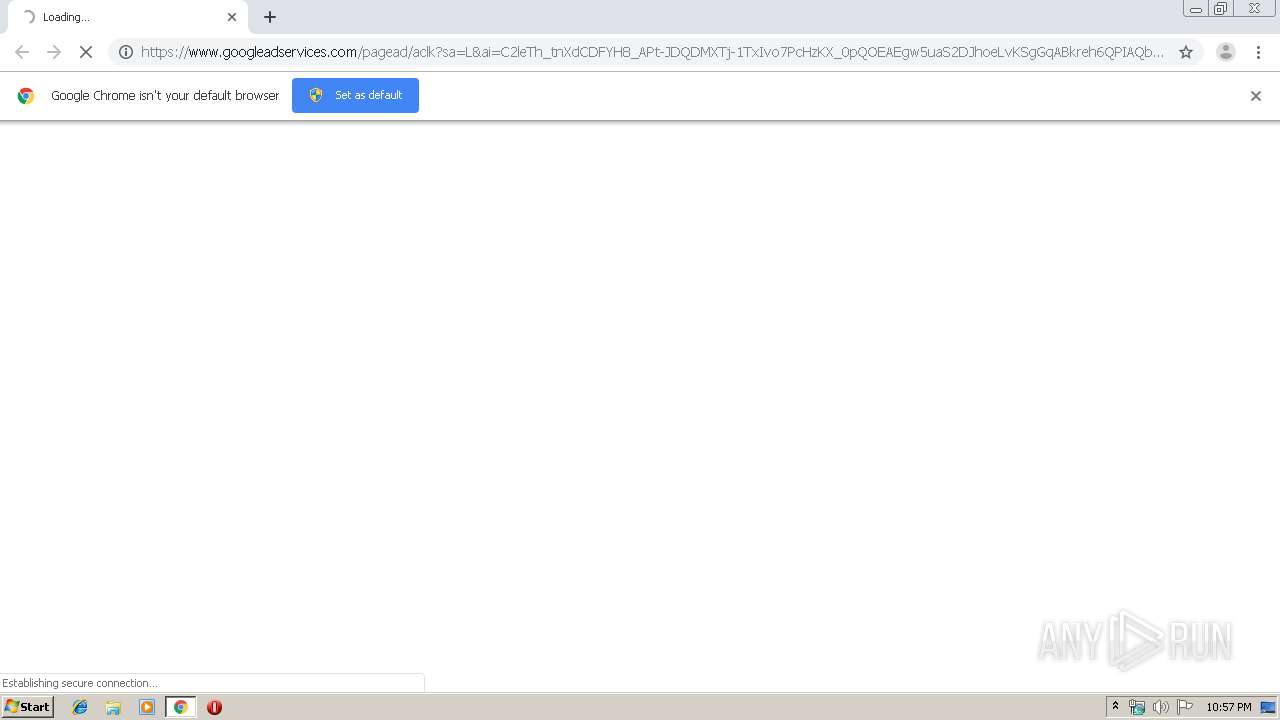
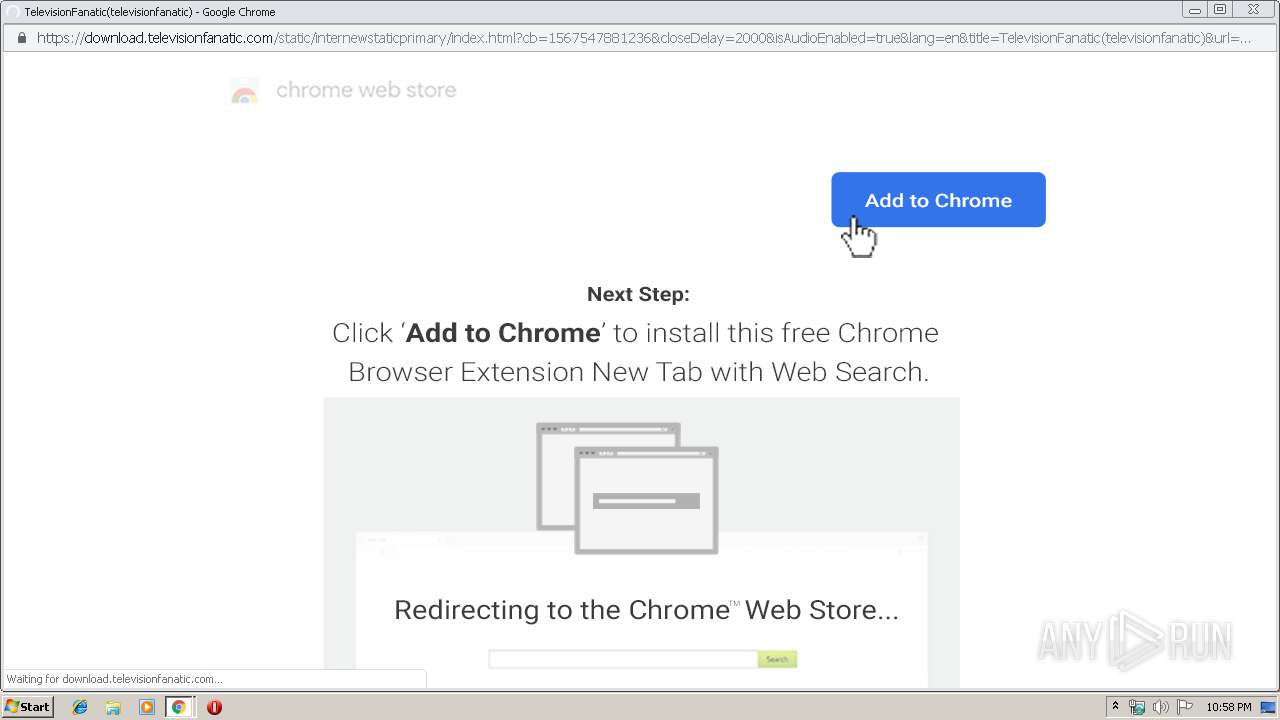
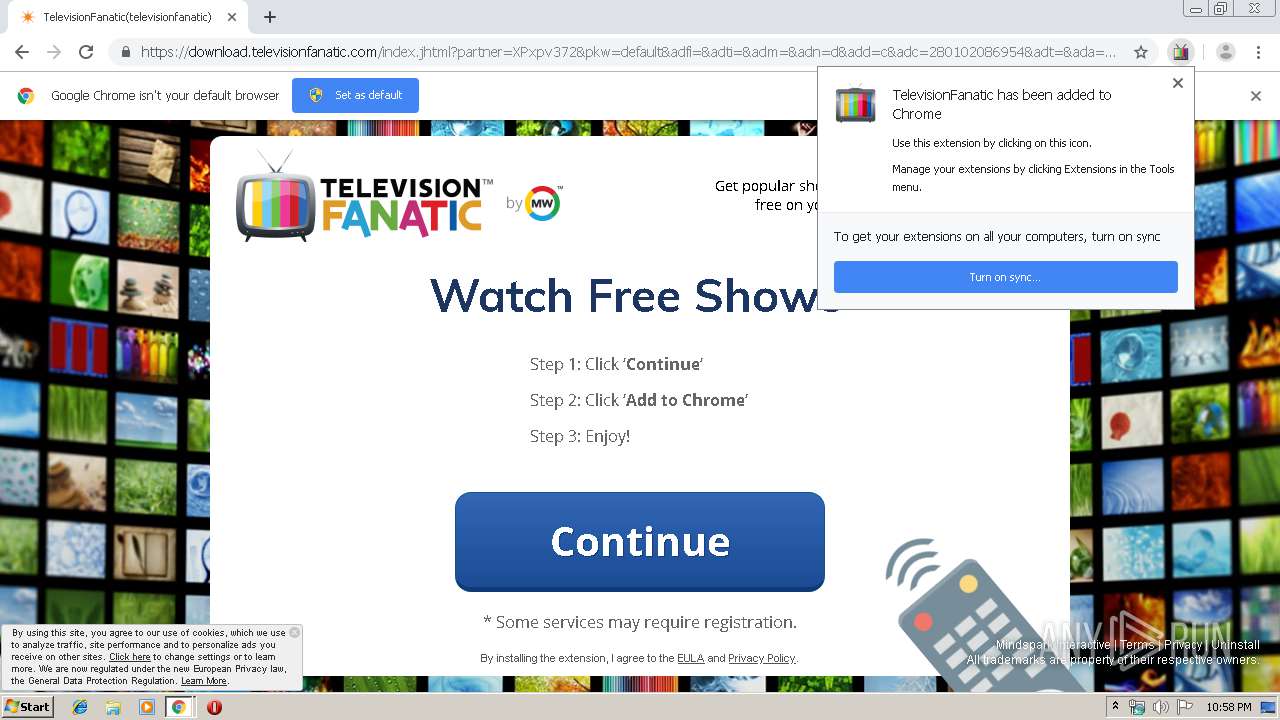
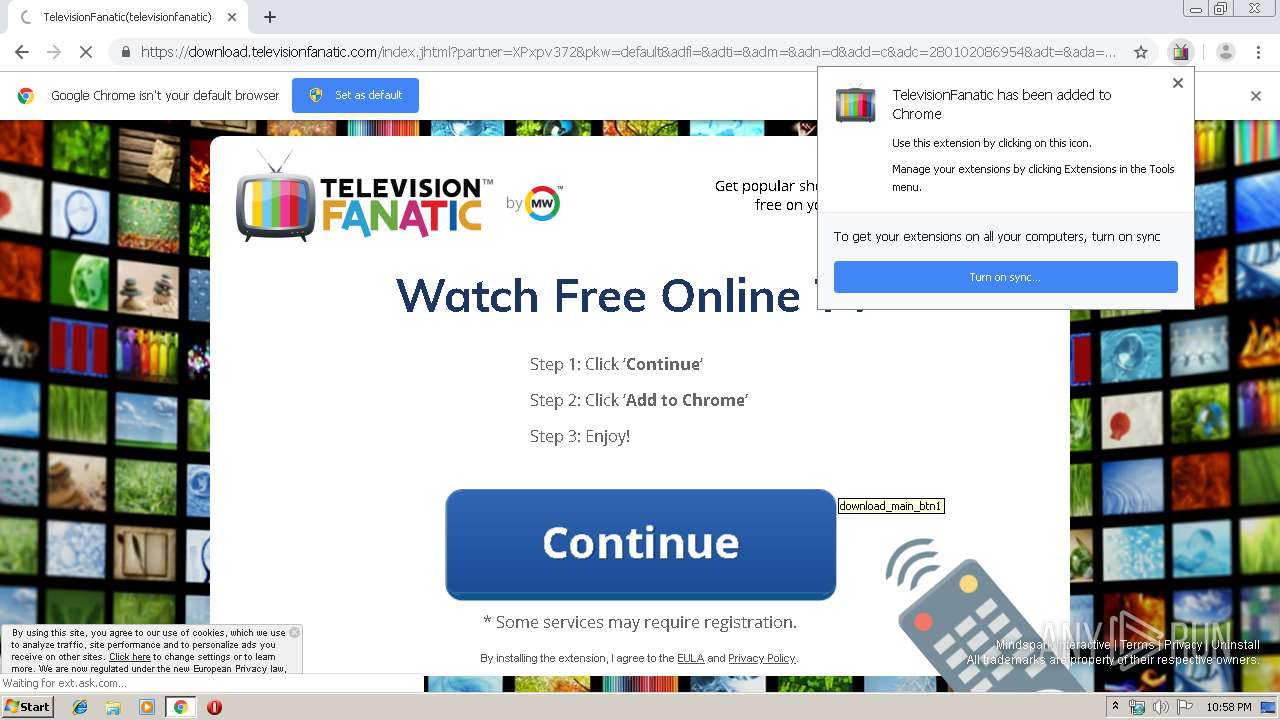
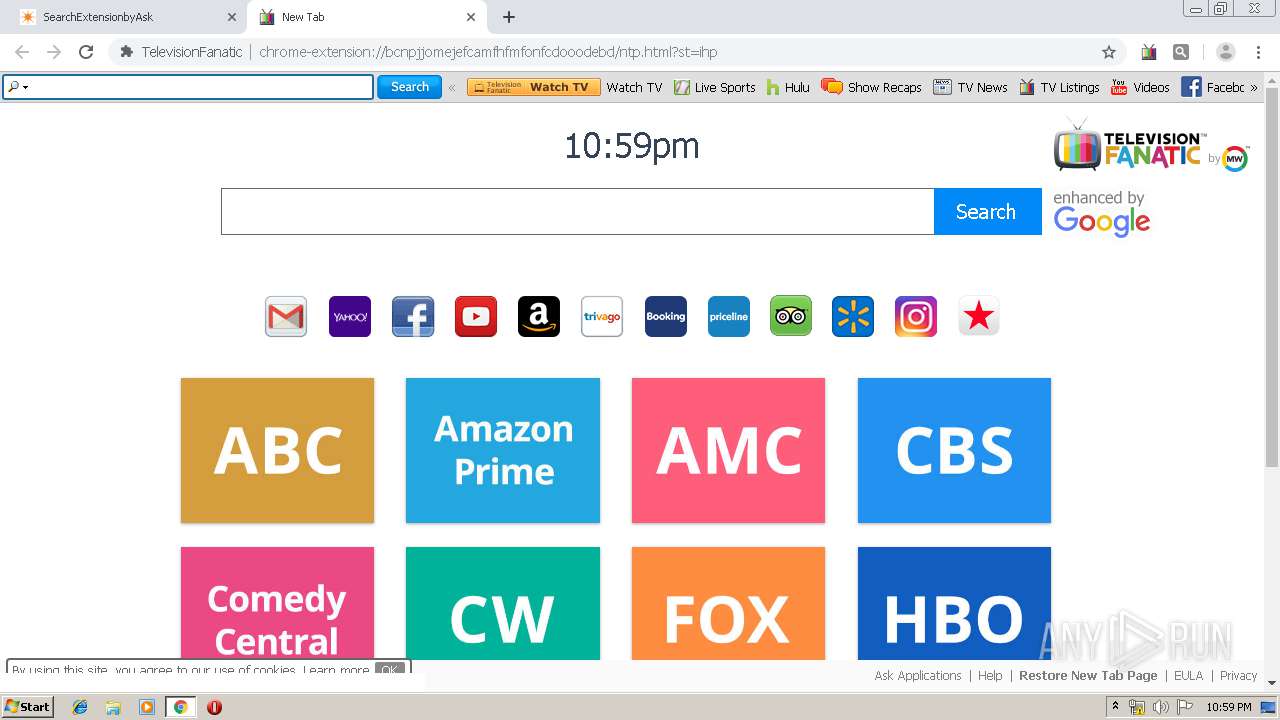
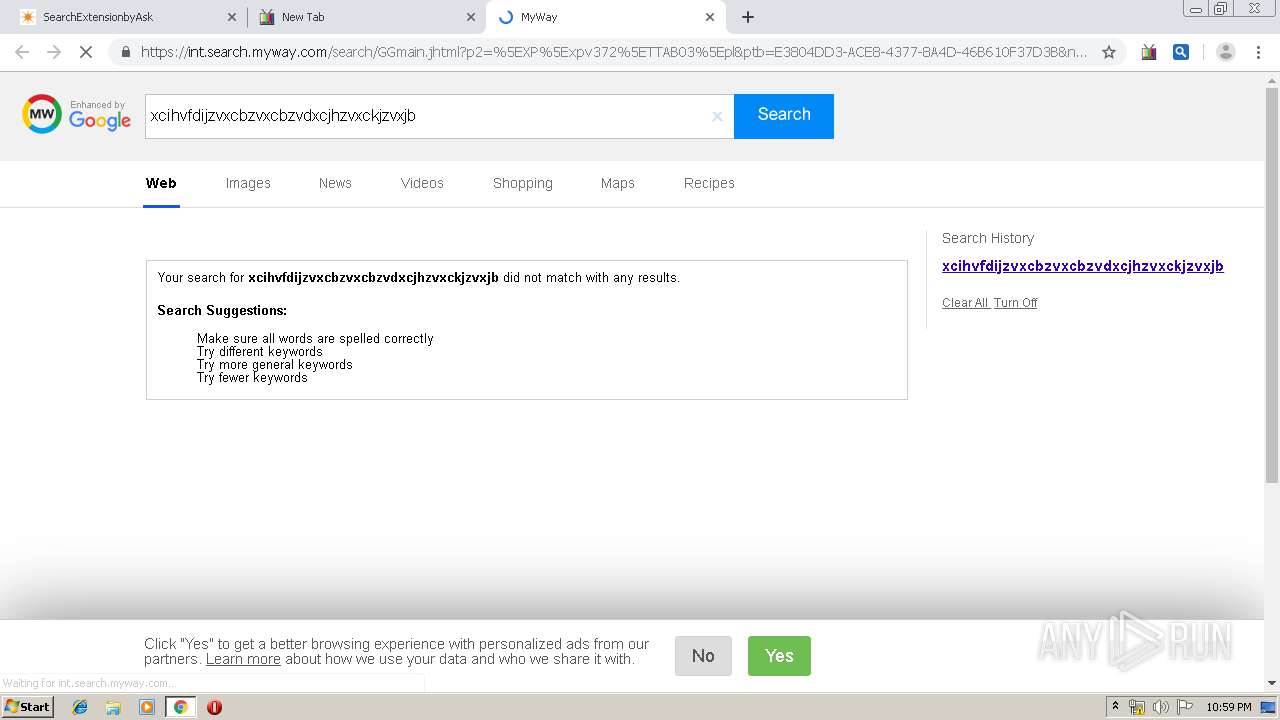
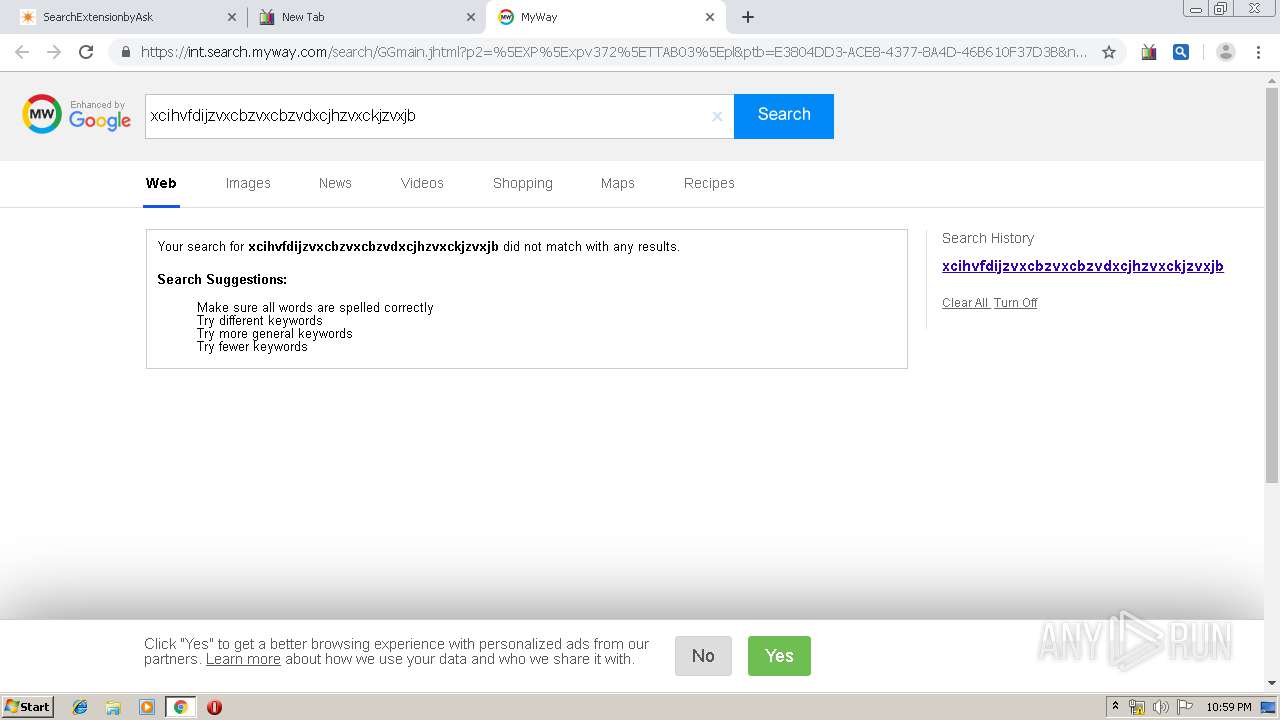
| URL: | https://www.googleadservices.com/pagead/aclk?sa=L&ai=C2leTh_tnXdCDFYH8_APt-JDQDMXTj-1TxIvo7PcHzKX_0pQOEAEgw5uaS2DJhoeLvKSgGqABkreh6QPIAQbgAgCoAwHIA5sEqgSPAk_QTj05AhB4jXAgMCMi-DOhRuJ7jzTlvQlPCAs2BfwKd0izBmlgDUj0xVw_QynQAU6TX4obfyLd_MwToYqOCMsEQaii8RmyAx5NBUv_YFEXv5y34M56ICrICblGdKfWvIDSxX3XUWy7F8oo0idSMkxvynCNO0c1siiKOE3Ej0p4-XqtgYxW-mou7eWvWwsT6eOklBLLc6W4groEGnuAnIMv34IF9wnm8kq7cTWiMdbzhLZIEQiDTBChLgqdLWAseoReTxgYyi7qqVLxFJMv7O6Qd2qfb9oclz08qj5QbgyUYsRsG-R9PGkttFxBuB9d_bQkRRgQ1lROeIf2ldGWJDMP_rlekpTZrLROlMfo7VLgBAGgBjeAB9bI3haoB47OG6gH1ckbqAfB0xuoB4XUG6gHgdQbqAeC1BuoB4bUG6gHhNQbqAeT2BuoB-DTG6gHugaoB9nLG6gHz8wbqAemvhuoB_PRG6gH7NUb2AcB0ggHCIBhEAEYDbEJs4H7xJa3oOWACgPYEww&num=1&cid=CAASEuRoFQDTRF3oumi9Fvd9NPdJHg&sig=AOD64_0zukGvmvZM_fO3hOXRKXkjCMd5oQ&client=ca-pub-1832713758055797&nm=3&nx=212&ny=92&mb=1&nb=9&clkt=111&adurl=http://download.televisionfanatic.com/index.jhtml%3Fpartner%3DXPxpv372%26pkw%3Ddefault%26adfi%3D%26adti%3D%26adm%3D%26adn%3Dd%26add%3Dc%26adc%3D280102086954%26adt%3D%26ada%3D%26adap%3Dnone%26adp%3Dwww.workandmoney.com |
| Full analysis: | https://app.any.run/tasks/aed6a1f0-f392-48a2-a2fb-89029915fd0d |
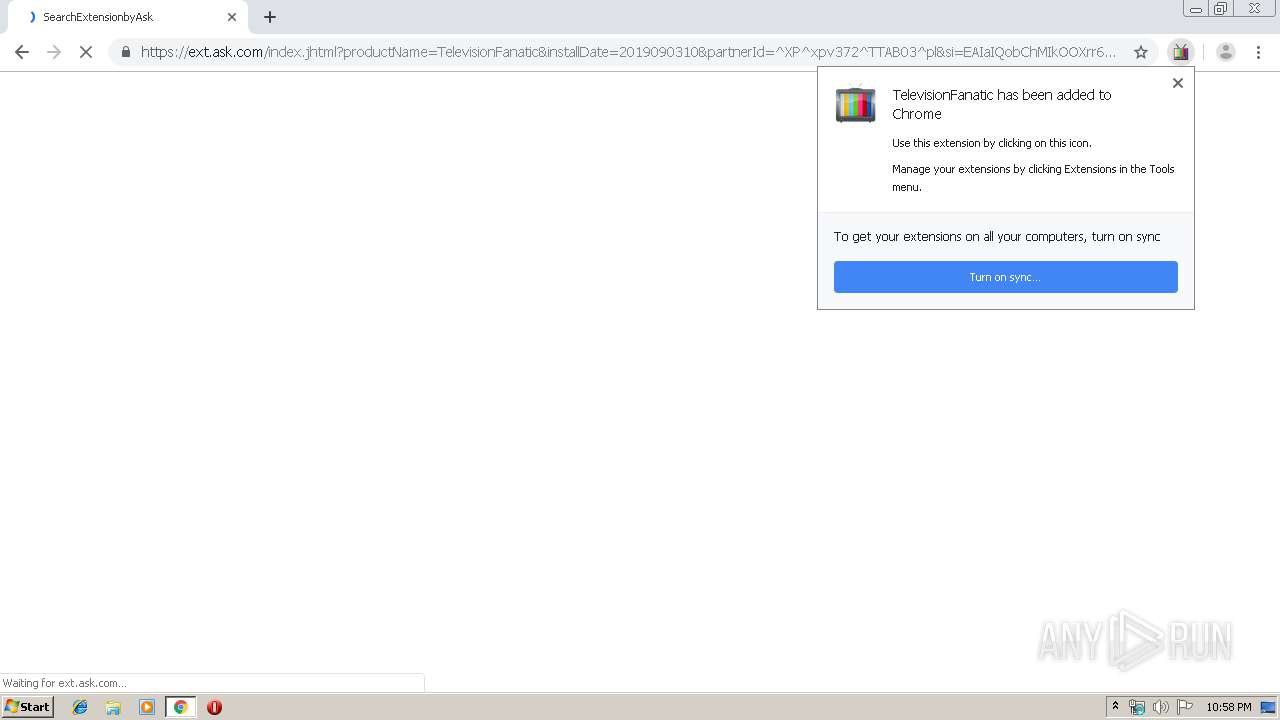
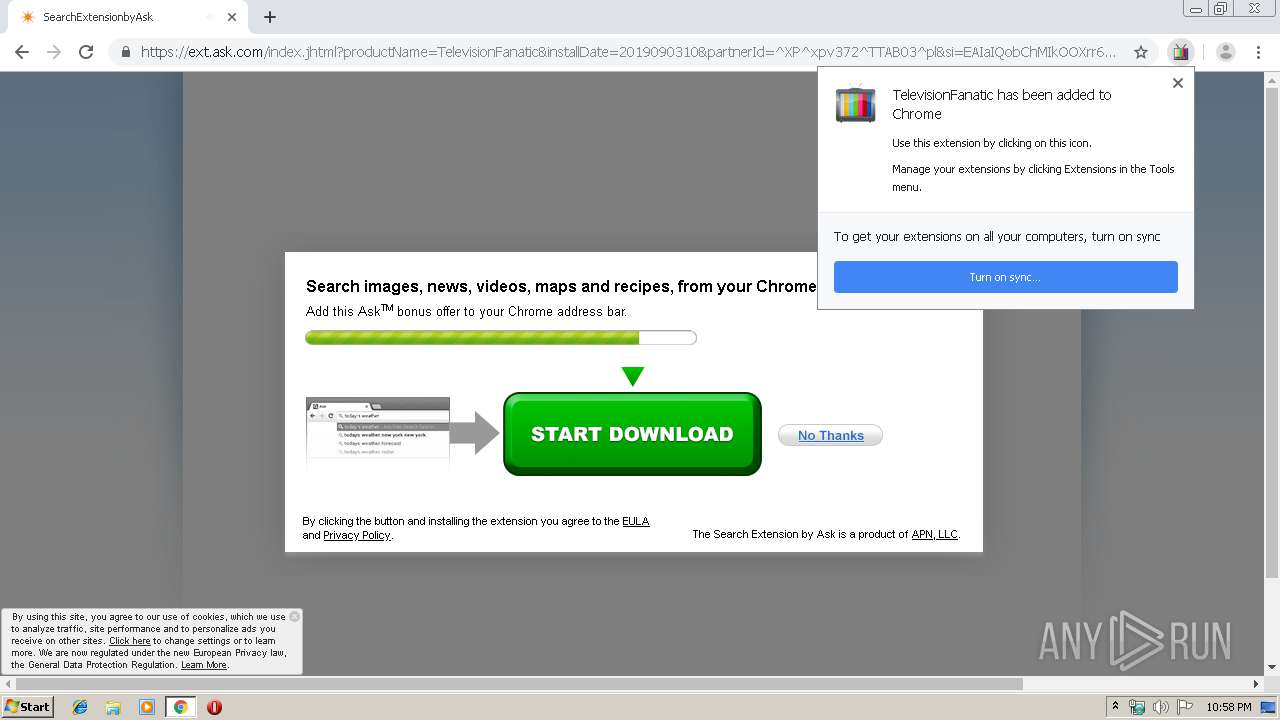
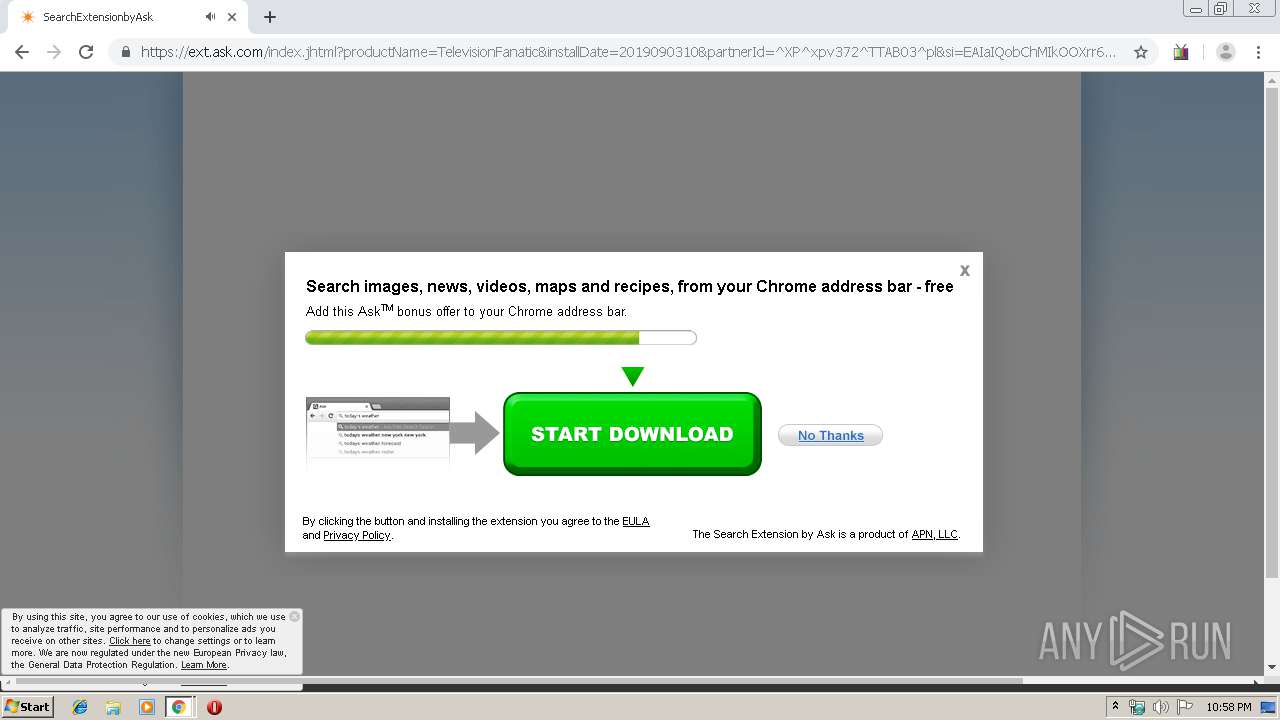
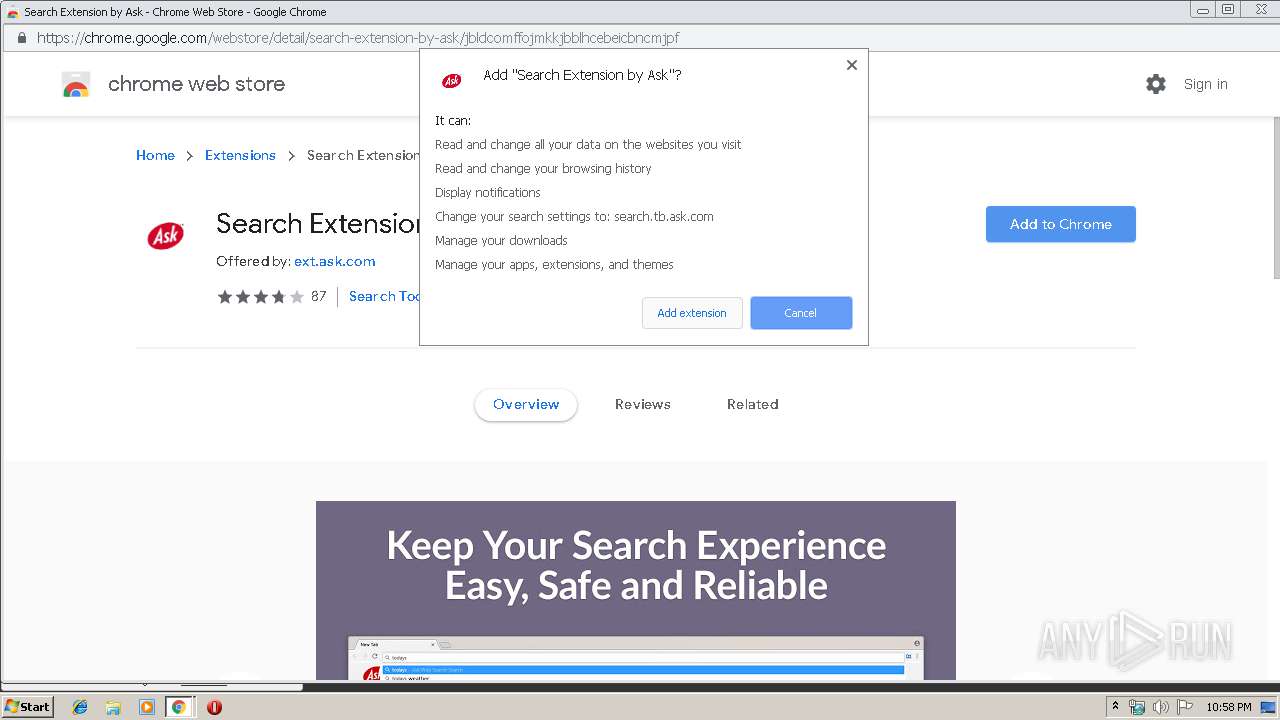
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2019, 21:57:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EB0FCD2798EDAEF66B59E556D2FB7772 |
| SHA1: | 3107442B7F87C0F1A9780E0ED3DB72DF89097505 |
| SHA256: | E418F99F9EEA5826BF69D91F3E9CE852D7115A9D5687FC29AF1C241BBD41365E |
| SSDEEP: | 24:2DGx26Zw0zosMTF6kHD0GFq5nNBUKxPTQwPxdN42:5xVPMFF6kjpQZUSP5v |
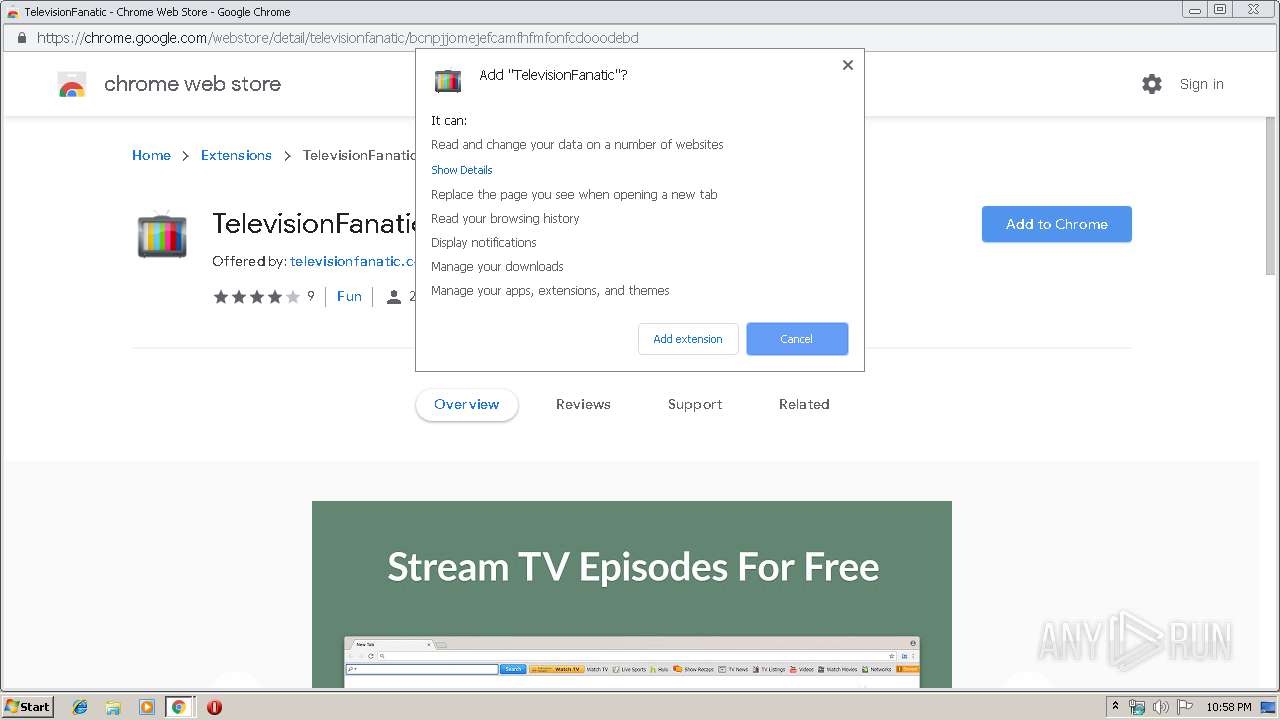
MALICIOUS
No malicious indicators.SUSPICIOUS
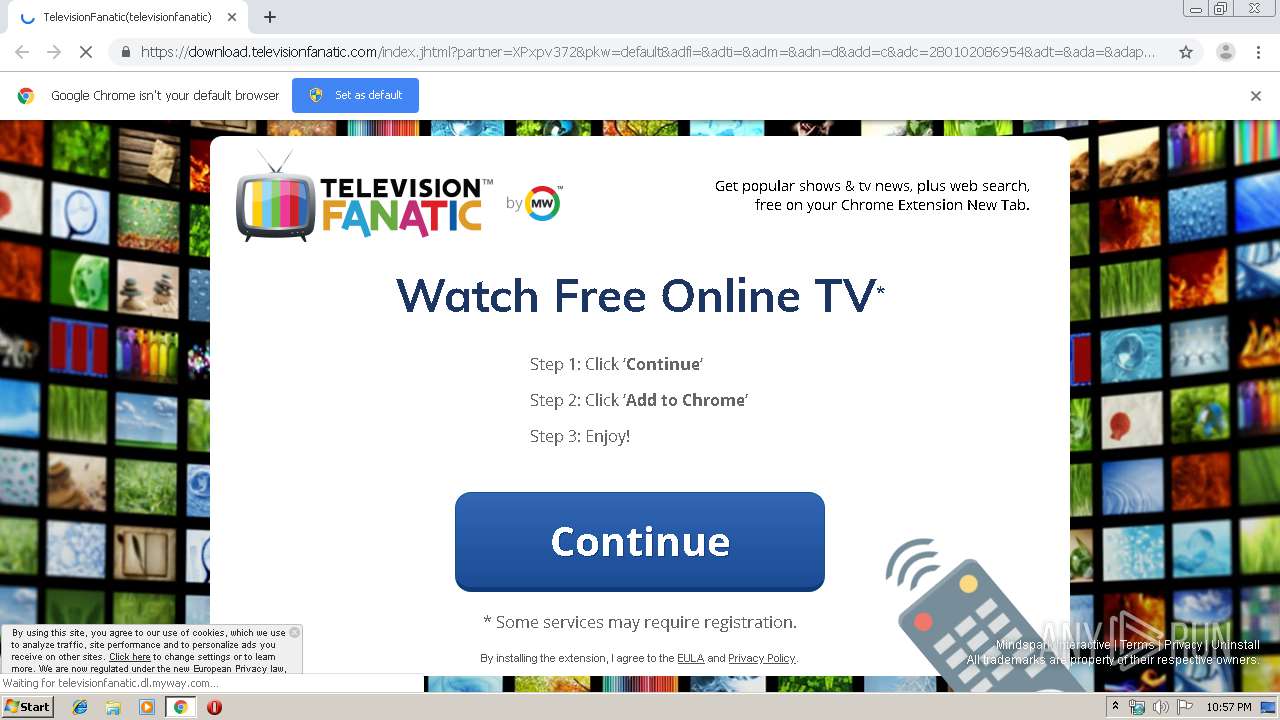
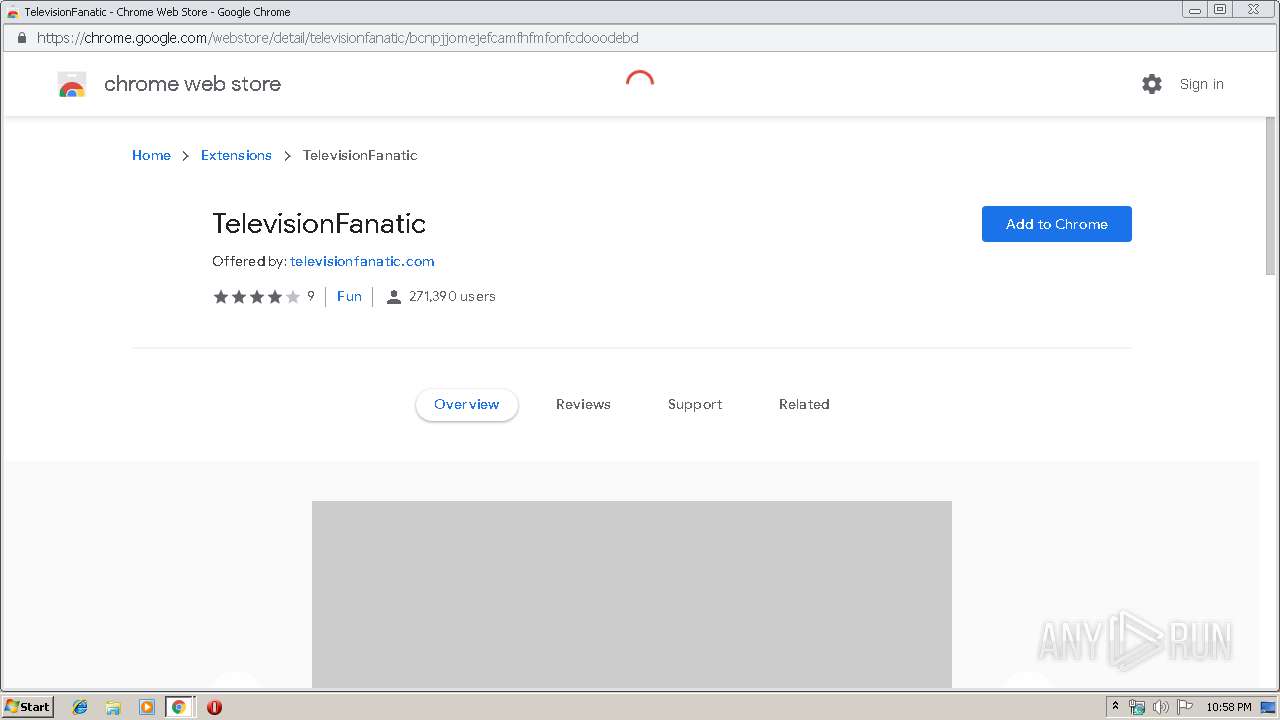
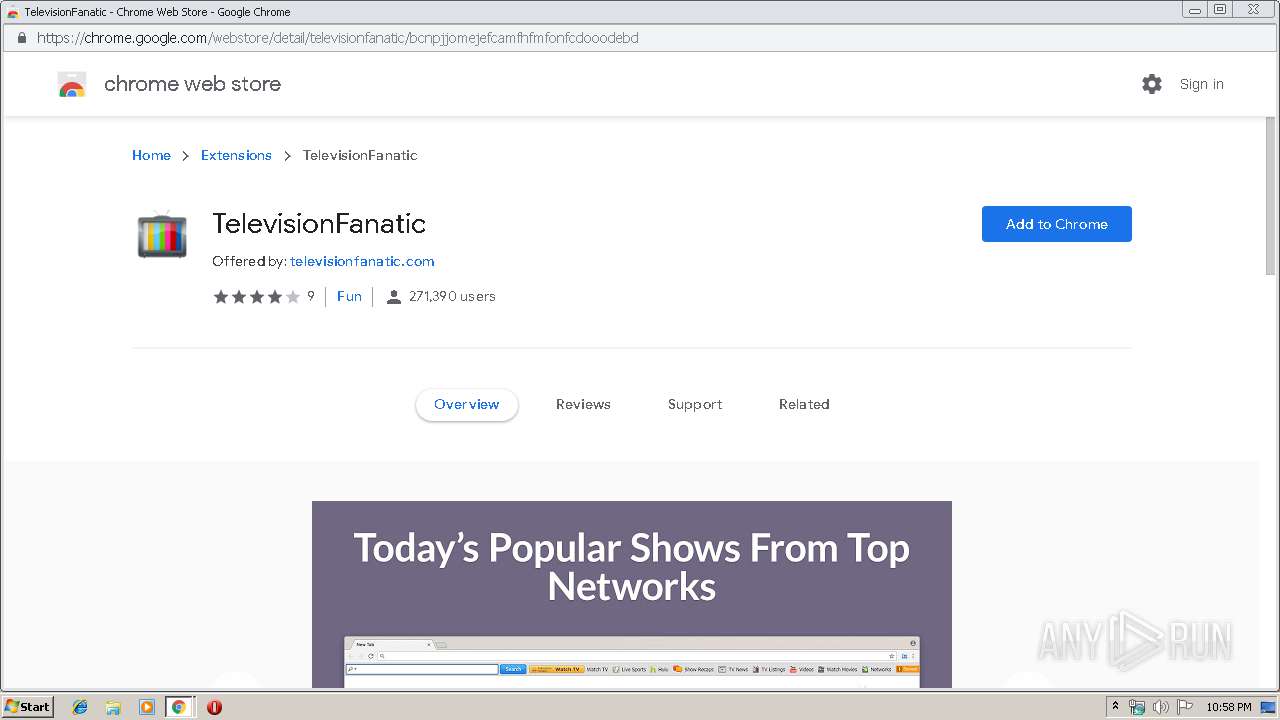
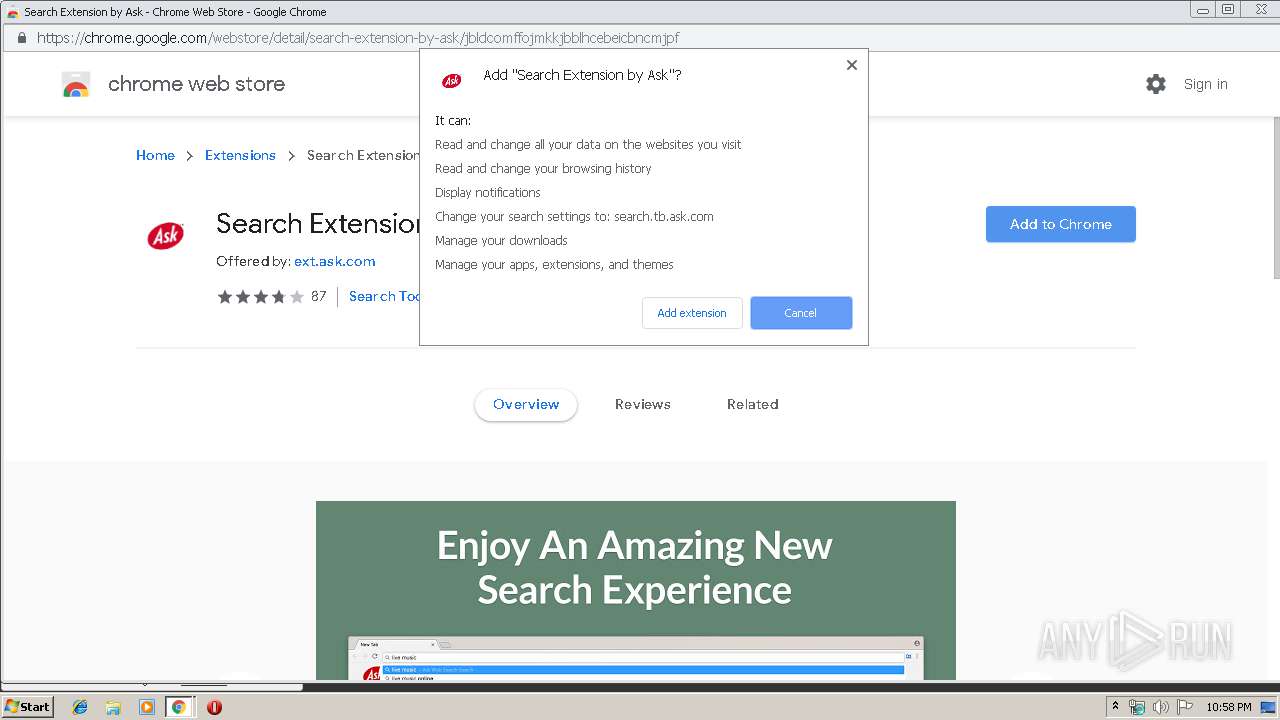
Modifies files in Chrome extension folder
- chrome.exe (PID: 2788)
INFO
Reads the hosts file
- chrome.exe (PID: 2424)
- chrome.exe (PID: 2788)
Application launched itself
- chrome.exe (PID: 2788)
Reads settings of System Certificates
- chrome.exe (PID: 2424)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2788)
Reads Internet Cache Settings
- chrome.exe (PID: 2788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
52
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15412750177739893774 --mojo-platform-channel-handle=5472 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=980,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18427199864753977657 --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4094664020499377095 --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10122901655010032845 --mojo-platform-channel-handle=4304 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7391360573806057156 --renderer-client-id=47 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13082134186713359686 --mojo-platform-channel-handle=4612 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5423916011323301237 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17655968180405429699 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9949364474866991217 --renderer-client-id=44 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1973789719894164968 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5048 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
861
Read events
724
Write events
131
Delete events
6
Modification events
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2788-13212021469948125 |
Value: 259 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
74
Text files
284
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dbf92506-b40b-45d3-a985-c8ccaf5b5e90.tmp | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF16907d.TMP | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
108
DNS requests
61
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2424 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2424 | chrome.exe | GET | 200 | 173.194.150.135:80 | http://r1---sn-f5f7ln7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.222.142&mm=28&mn=sn-f5f7ln7s&ms=nvh&mt=1567547747&mv=u&mvi=0&pl=21&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2424 | chrome.exe | GET | 302 | 172.217.16.194:80 | http://www.googleadservices.com/pagead/conversion/1026055058/?value=0&label=r85WCMaJzQEQkreh6QM&guid=ON&script=0 | US | image | 42 b | whitelisted |
2424 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
2424 | chrome.exe | GET | 302 | 172.217.23.130:80 | http://googleads.g.doubleclick.net/pagead/viewthroughconversion/1026055058/?value=0&label=r85WCMaJzQEQkreh6QM&guid=ON&script=0&ctc_id=CAEVAQAAAB0BAAAA&ct_cookie_present=true&ctc_ai=CYv-OAAAAAACAgICwDwAAxIvo7PcHAKoEBU_Q7NXw&convclickts=1567547872718514&attr_src=1&random=78539240&ssc=ChpDTExkX1BEU3RlUUNGWkhrZHdvZGdrSUtxZxgBQhMIwfStgNO15AIV1wOLCh31Hg33SAFQ1fqtgNO15AI&crd=>d= | US | image | 42 b | whitelisted |
2424 | chrome.exe | GET | 302 | 35.244.218.203:80 | http://download.televisionfanatic.com/index.jhtml?partner=XPxpv372&pkw=default&adfi=&adti=&adm=&adn=d&add=c&adc=280102086954&adt=&ada=&adap=none&adp=www.workandmoney.com&gclid=EAIaIQobChMIkOOXrr6o5AIVAT5_Ch1tPATKEAEYASAAEgKjR_D_BwE | US | — | — | whitelisted |
2424 | chrome.exe | GET | 200 | 13.32.222.126:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2424 | chrome.exe | 216.58.205.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2424 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2424 | chrome.exe | 172.217.16.194:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
2424 | chrome.exe | 35.244.218.203:80 | download.televisionfanatic.com | — | US | whitelisted |
2424 | chrome.exe | 216.58.207.35:443 | www.google.pl | Google Inc. | US | whitelisted |
2424 | chrome.exe | 172.217.23.130:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2424 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2424 | chrome.exe | 185.60.216.35:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
2424 | chrome.exe | 74.113.237.192:443 | anx.mindspark.com | Mindspark Interactive Network, Inc. | US | malicious |
2424 | chrome.exe | 216.58.208.46:443 | chrome.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |
accounts.google.com |
| shared |
download.televisionfanatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ak.imgfarm.com |
| whitelisted |
ak.staticimgfarm.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
akz.imgfarm.com |
| whitelisted |
www.google.com |
| malicious |
Threats
Process | Message |
|---|---|
chrome.exe | Error - |
chrome.exe | Too long restart command line passed |
chrome.exe |