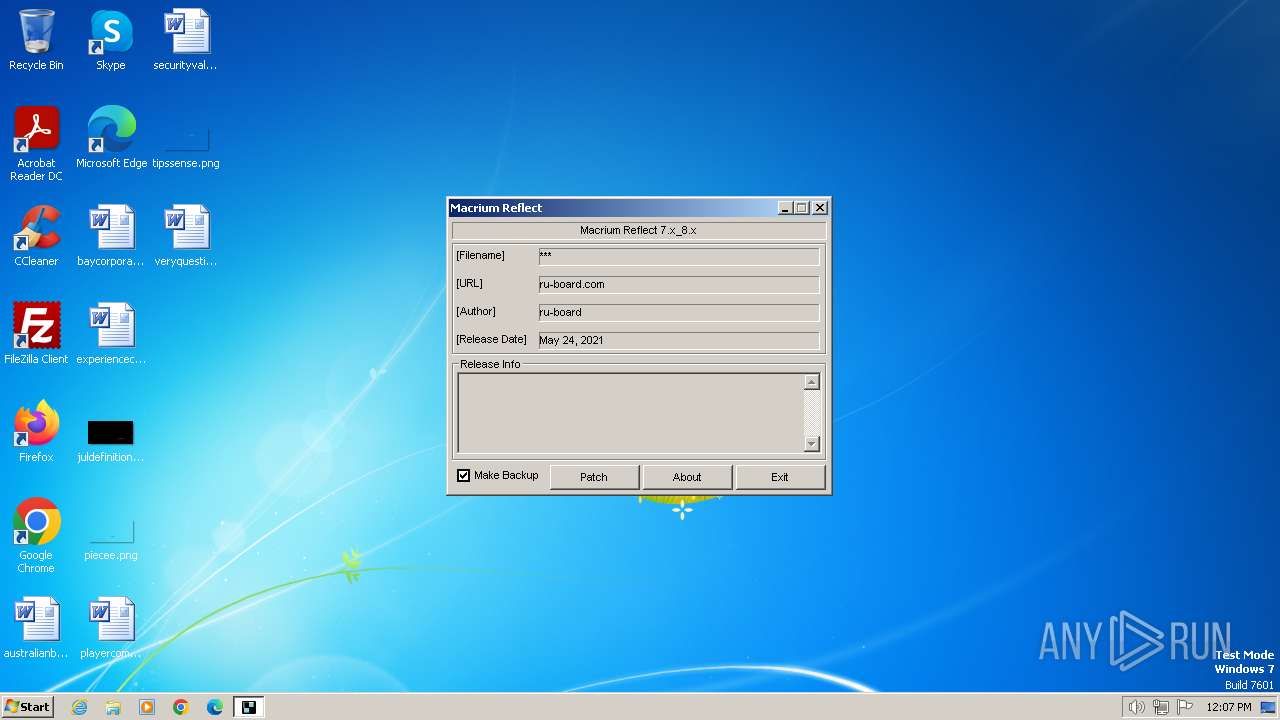
| File name: | Macrium_Reflect-7.x_8.x-patch.exe |
| Full analysis: | https://app.any.run/tasks/3b9c7918-9282-4c6e-b3ec-540104dc9d86 |
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2024, 12:07:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 60F7348C6F666071E3969D16A278711E |
| SHA1: | 5EC5F17E237C1D9991C4AAE56F093372421771B0 |
| SHA256: | E4152620B9C4B5EBB73678D6C8AEDDDD784A41F80412DCD1D89527E3160F756A |
| SSDEEP: | 1536:6TL5Kt5xaXJ/pvGNSlTGBF8y4GubLj03uxfbnxDLv5jQ:6T4WR+N0SX8y4RdFbnhRs |
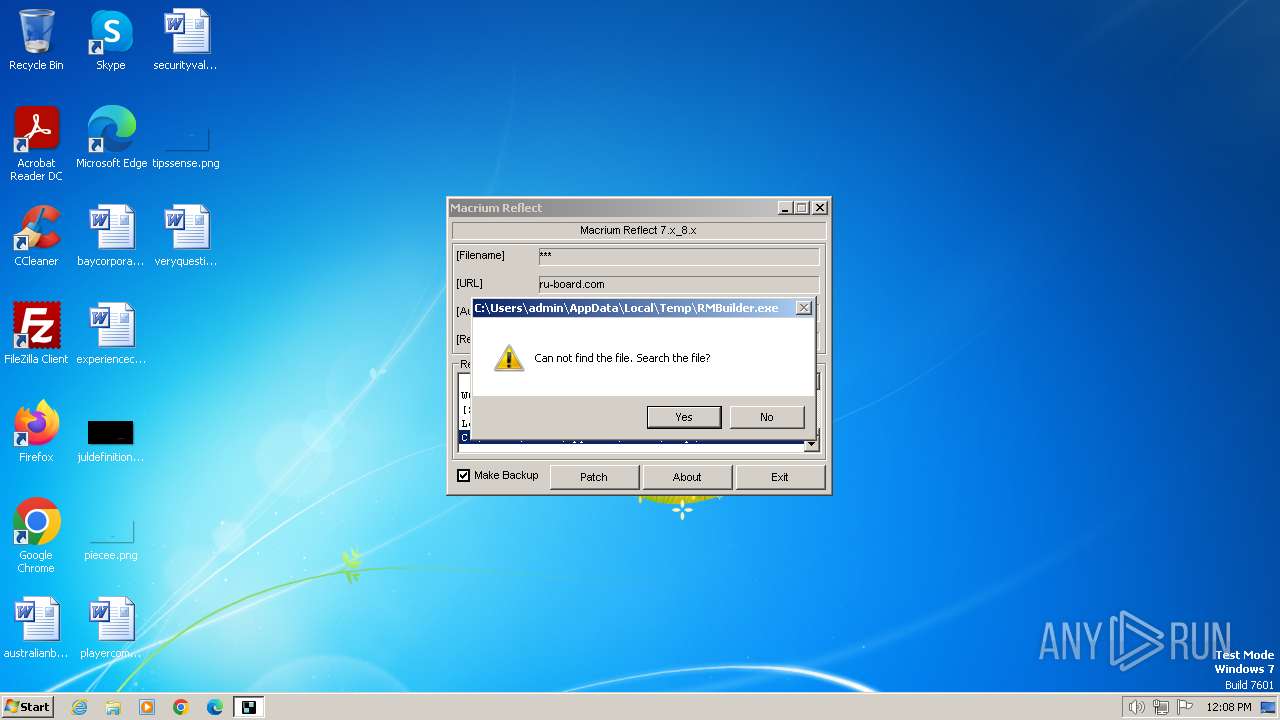
MALICIOUS
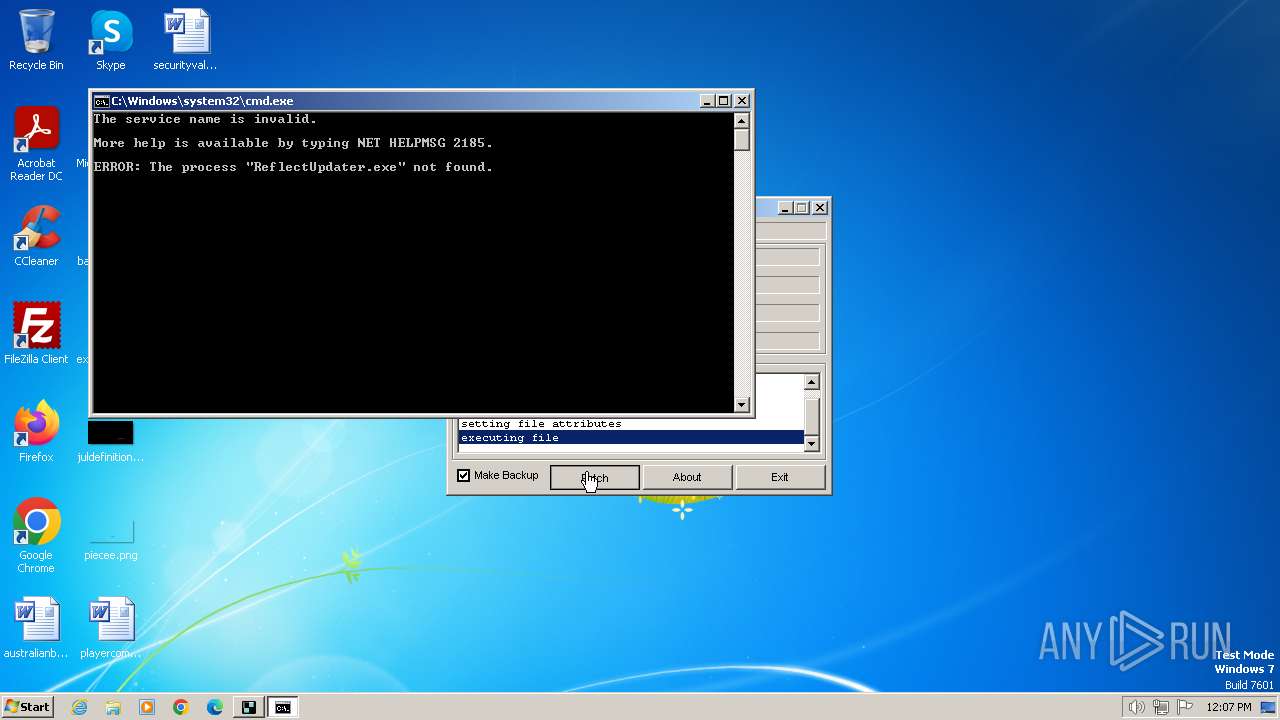
Starts NET.EXE for service management
- cmd.exe (PID: 2100)
- net.exe (PID: 2260)
Drops the executable file immediately after the start
- Macrium_Reflect-7.x_8.x-patch.exe (PID: 876)
SUSPICIOUS
Executing commands from ".cmd" file
- Macrium_Reflect-7.x_8.x-patch.exe (PID: 876)
Starts CMD.EXE for commands execution
- Macrium_Reflect-7.x_8.x-patch.exe (PID: 876)
Uses REG/REGEDIT.EXE to modify registry
- Macrium_Reflect-7.x_8.x-patch.exe (PID: 876)
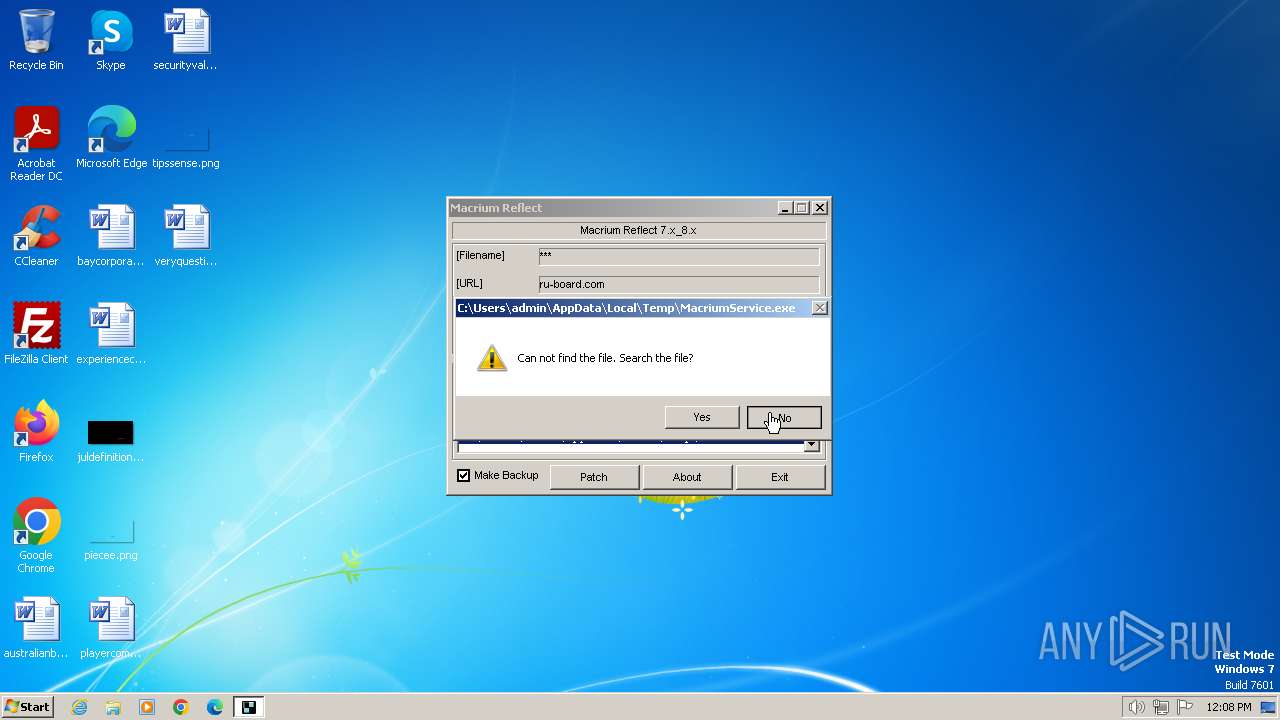
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2100)
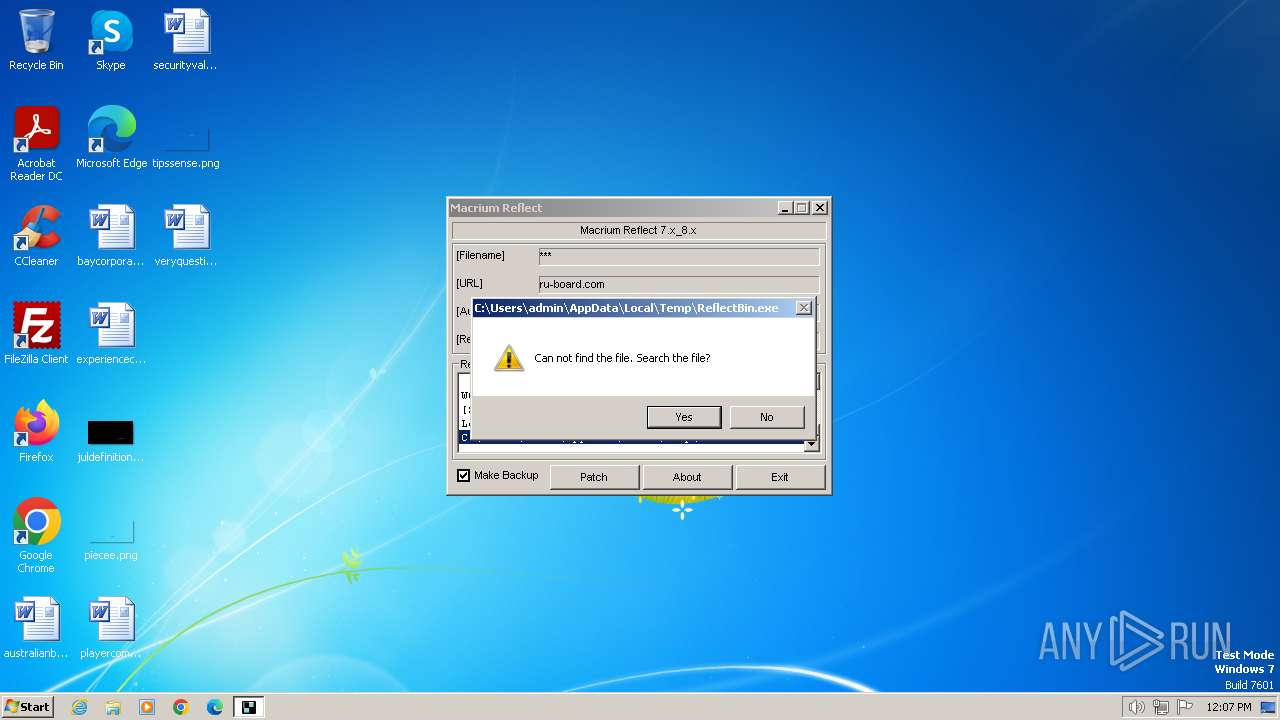
Executable content was dropped or overwritten
- Macrium_Reflect-7.x_8.x-patch.exe (PID: 876)
Reads the Internet Settings
- Macrium_Reflect-7.x_8.x-patch.exe (PID: 876)
INFO
Reads the computer name
- Macrium_Reflect-7.x_8.x-patch.exe (PID: 876)
Checks supported languages
- Macrium_Reflect-7.x_8.x-patch.exe (PID: 876)
Reads the machine GUID from the registry
- Macrium_Reflect-7.x_8.x-patch.exe (PID: 876)
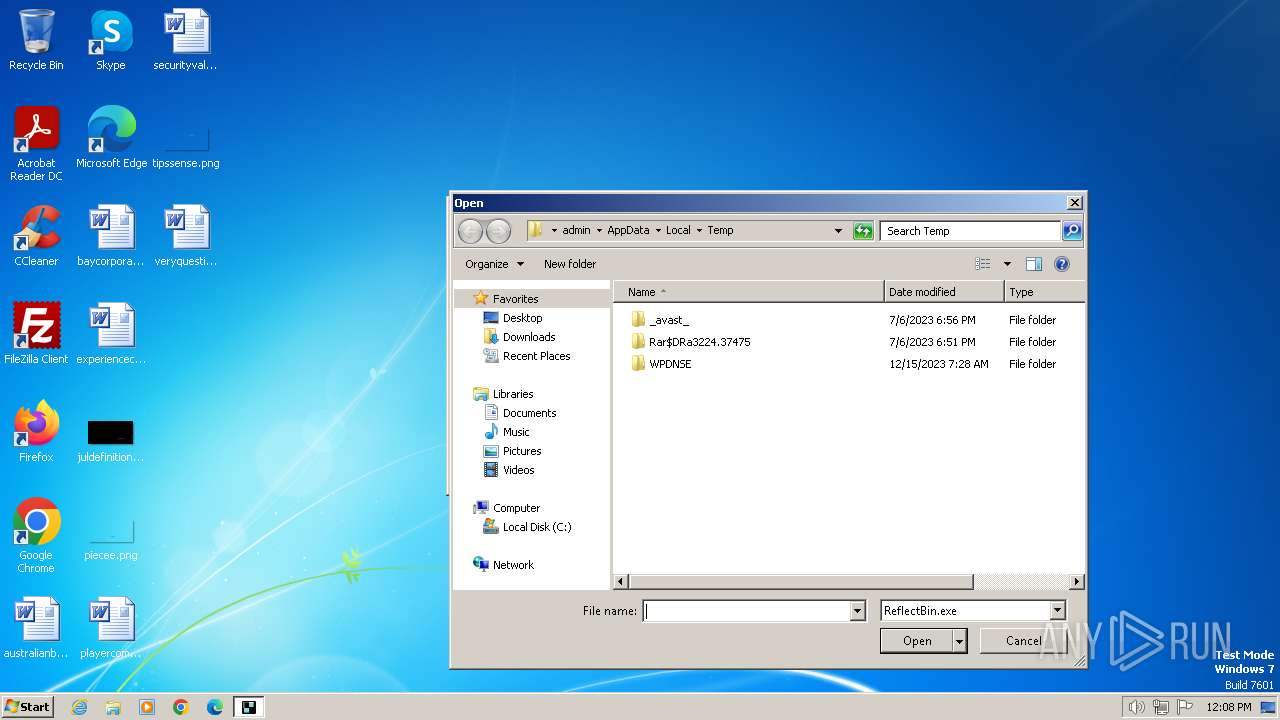
Create files in a temporary directory
- Macrium_Reflect-7.x_8.x-patch.exe (PID: 876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:21 21:59:46+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 512 |
| InitializedDataSize: | 66048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x102b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
59
Monitored processes
18
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 876 | "C:\Users\admin\AppData\Local\Temp\Macrium_Reflect-7.x_8.x-patch.exe" | C:\Users\admin\AppData\Local\Temp\Macrium_Reflect-7.x_8.x-patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1112 | Taskkill /IM RMBuilder.exe /F | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1404 | Taskkill /IM ReflectBin.exe /F | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1408 | net statr MacriumService | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | "C:\Windows\regedit.exe" /s "C:\Users\admin\AppData\Local\Temp\\regpatch.reg" | C:\Windows\regedit.exe | — | Macrium_Reflect-7.x_8.x-patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1556 | C:\Windows\system32\net1 stop MacriumService | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1860 | Taskkill /IM MIGPopup.exe /F | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2072 | C:\Windows\system32\net1 statr MacriumService | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2100 | C:\Windows\system32\cmd.exe /c "C:\Users\admin\AppData\Local\Temp\stop.cmd" | C:\Windows\System32\cmd.exe | — | Macrium_Reflect-7.x_8.x-patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2244 | Taskkill /IM MIGPopup.exe /F | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 614
Read events
4 576
Write events
37
Delete events
1
Modification events
| (PID) Process: | (876) Macrium_Reflect-7.x_8.x-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (876) Macrium_Reflect-7.x_8.x-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (876) Macrium_Reflect-7.x_8.x-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (876) Macrium_Reflect-7.x_8.x-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (876) Macrium_Reflect-7.x_8.x-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (876) Macrium_Reflect-7.x_8.x-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000006000000000000000B00000002000000070000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (876) Macrium_Reflect-7.x_8.x-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 070000000100000006000000000000000B000000020000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (876) Macrium_Reflect-7.x_8.x-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\103\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (876) Macrium_Reflect-7.x_8.x-patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (876) Macrium_Reflect-7.x_8.x-patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | delete value | Name: | 4 |
Value: 4D00610063007200690075006D005F005200650066006C006500630074002D0037002E0078005F0038002E0078002D00700061007400630068002E00650078006500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000C1010000BE000000410400009E020000000000000000000000000000000000000100000000000000 | |||
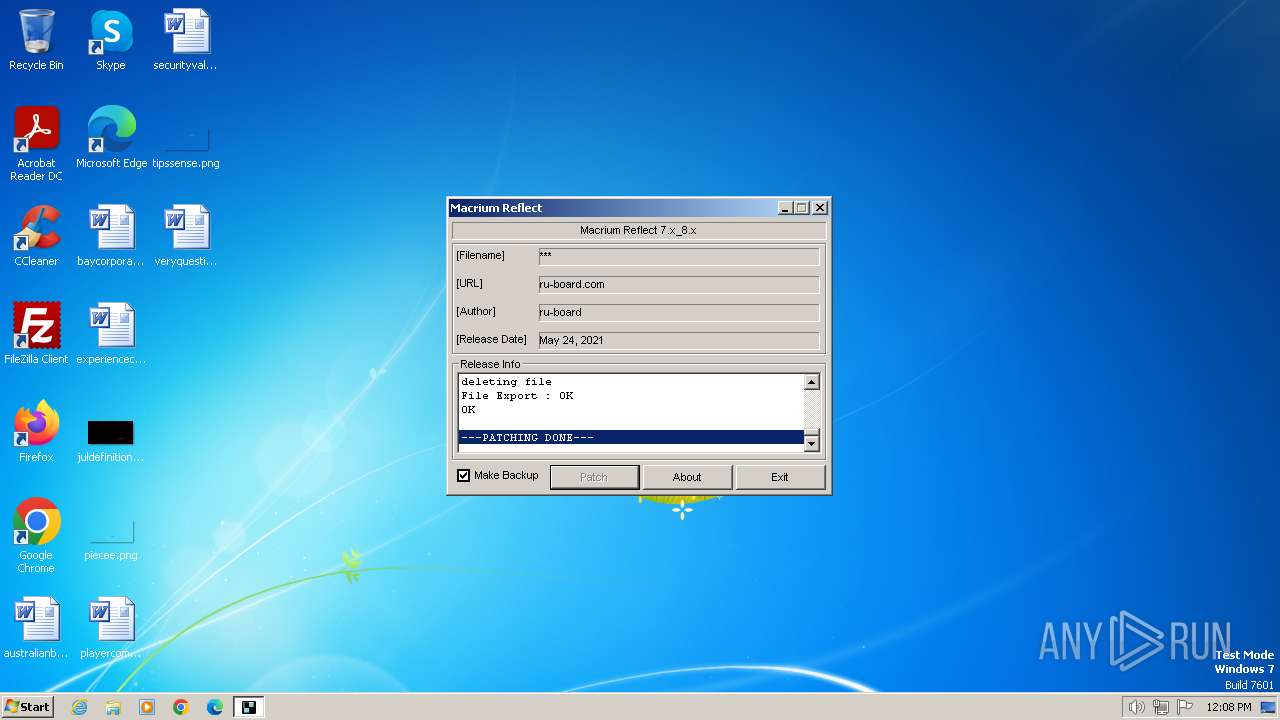
Executable files
1
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 876 | Macrium_Reflect-7.x_8.x-patch.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:468D0760EBA95F83965B9FF4C8488D50 | SHA256:7D0A0EA309BE7A9992E3549F1389CA9E62D5A59EE813A5EE2F6082F2E7C019DA | |||
| 876 | Macrium_Reflect-7.x_8.x-patch.exe | C:\Users\admin\AppData\Local\Temp\regpatch.reg | text | |
MD5:FDB3E2E44195F962A8097A140EB654AF | SHA256:A92D13723F443AD1C4CD673FE6B5FF011A69AEDB71B8316872D8628D62638929 | |||
| 876 | Macrium_Reflect-7.x_8.x-patch.exe | C:\Users\admin\AppData\Local\Temp\stop.cmd | text | |
MD5:74CF949F55980213D14299C55EDDB78E | SHA256:9403F253E790D6FA346B7DF6B0F6CA68612723B13C411B08BB1EB6E0C4AC9A0A | |||
| 876 | Macrium_Reflect-7.x_8.x-patch.exe | C:\Users\admin\AppData\Local\Temp\start.cmd | text | |
MD5:BDC78C33946344832F71E06848B06FA8 | SHA256:6E49C6231EDE9D03FF9BEF6D0D79BBED6262873707E45352F67A67B9E5FAC405 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |