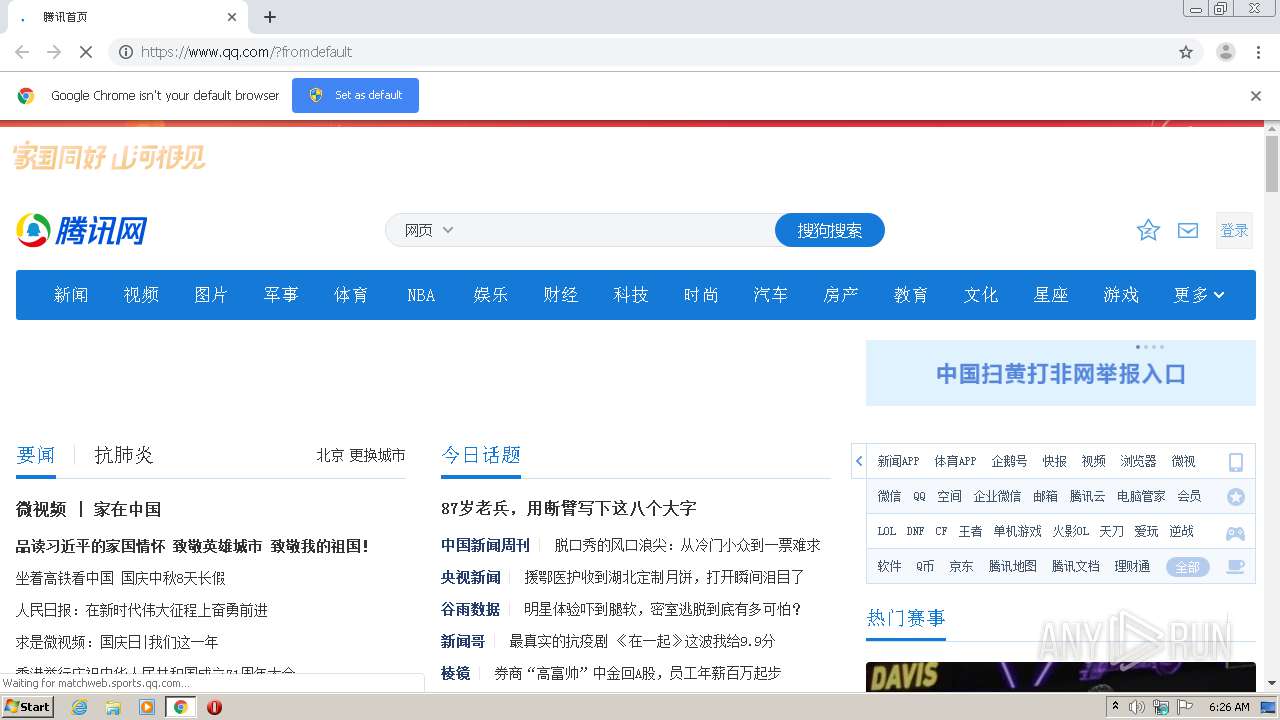
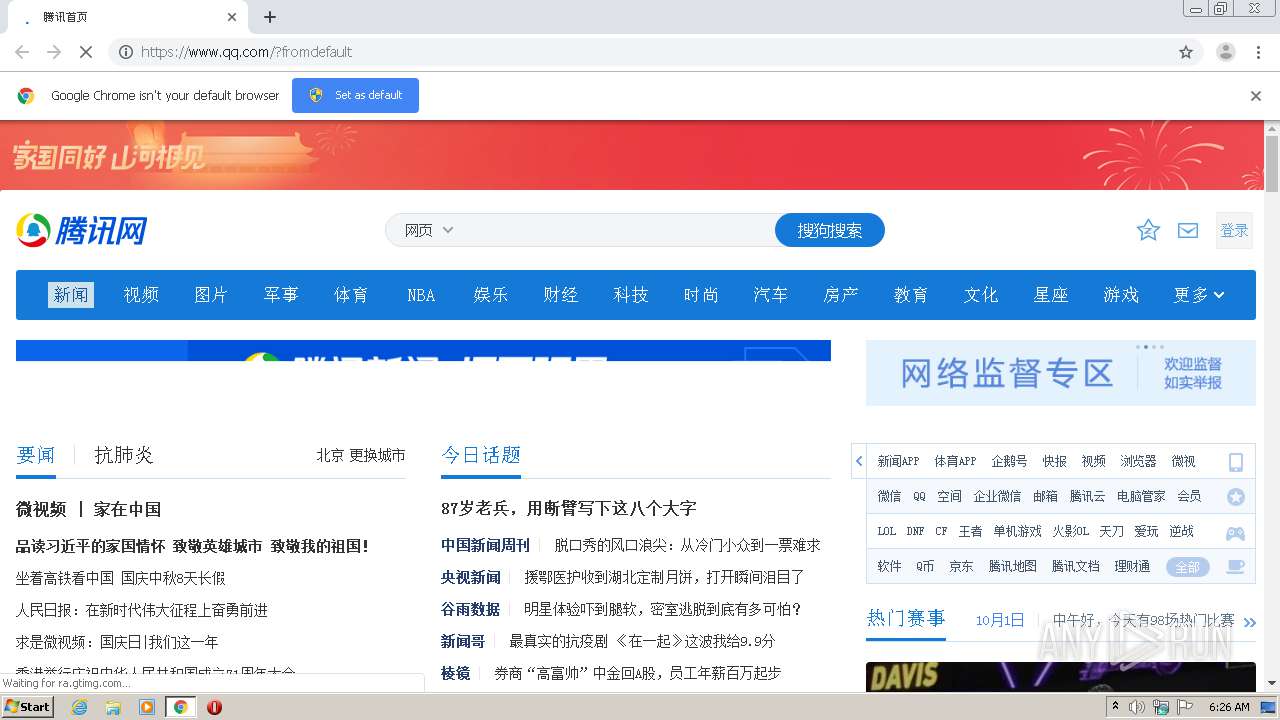
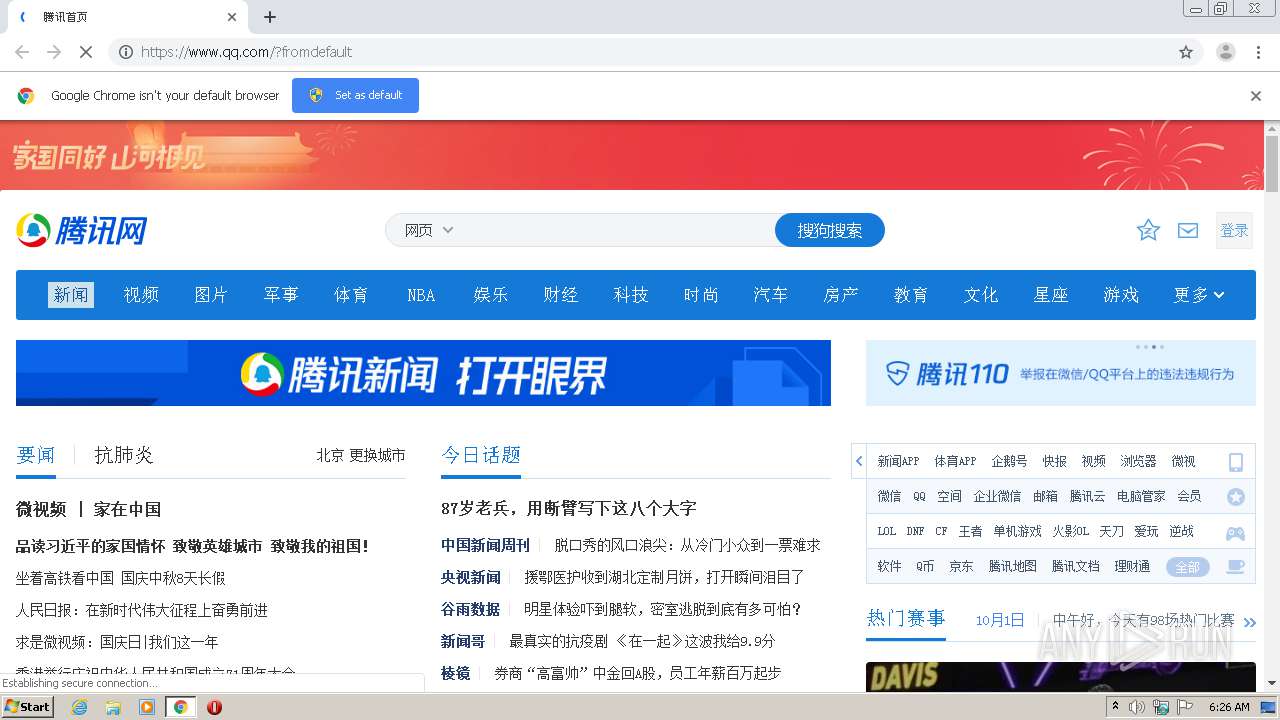
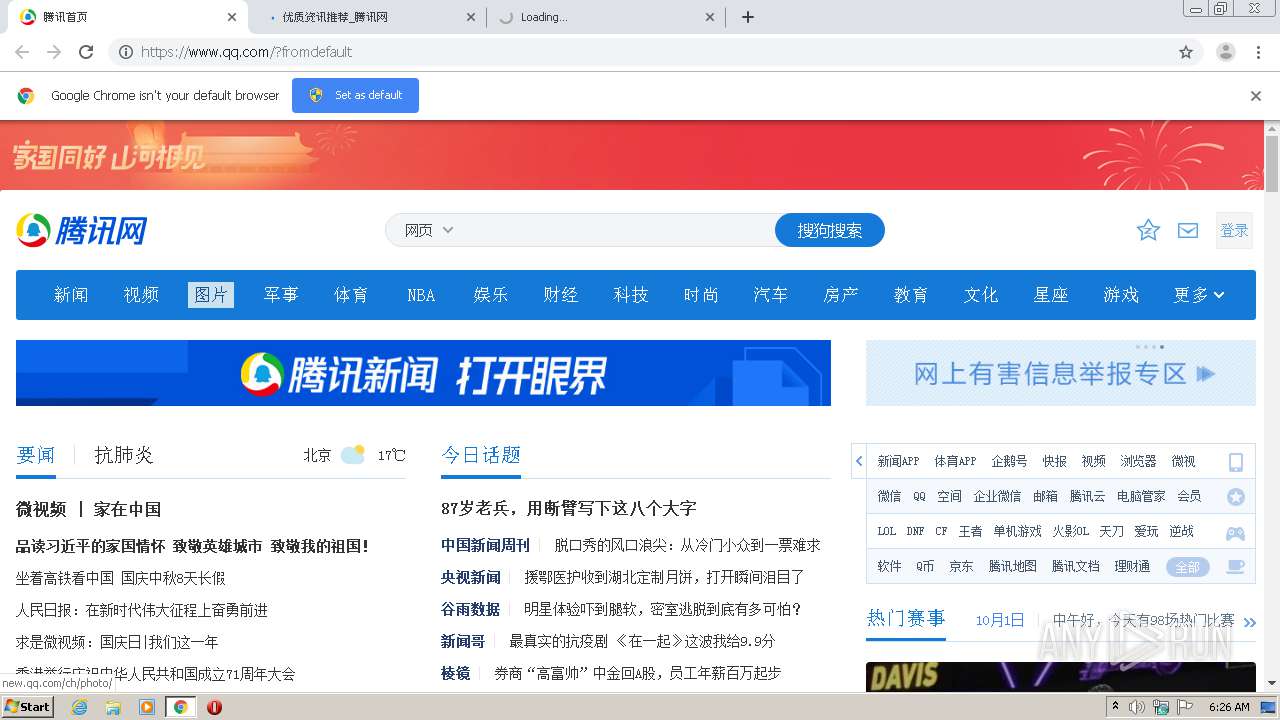
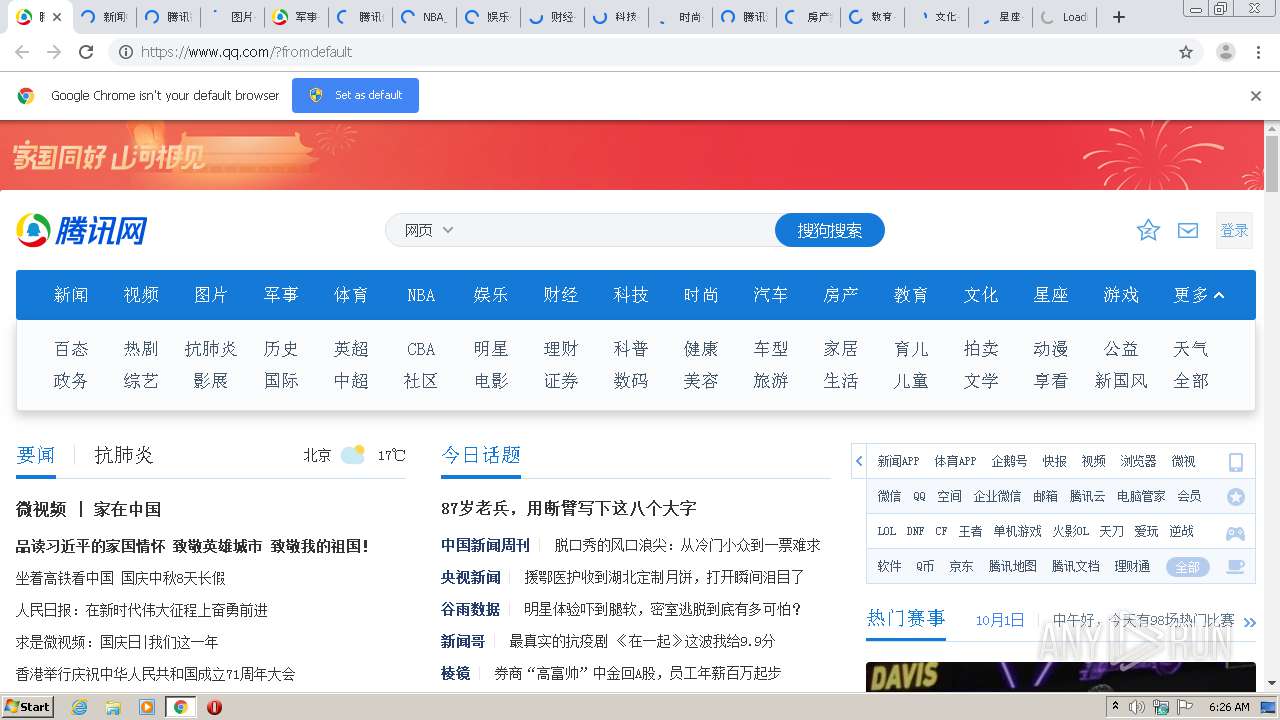
| URL: | https://qq.com |
| Full analysis: | https://app.any.run/tasks/08bf80fb-9108-465a-b6bd-7b17f5eab234 |
| Verdict: | Malicious activity |
| Analysis date: | October 01, 2020, 05:25:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B48B2C7B22B1E29B0547807F3DB1002E |
| SHA1: | 50E24BAF87F167133D78DC3AD11FF9A45CD03188 |
| SHA256: | E4101855725653D7668C30B8321C710FF25C4C59EFAD6B2D0B40AA4A61DA7BAE |
| SSDEEP: | 3:N8DKn:2+n |
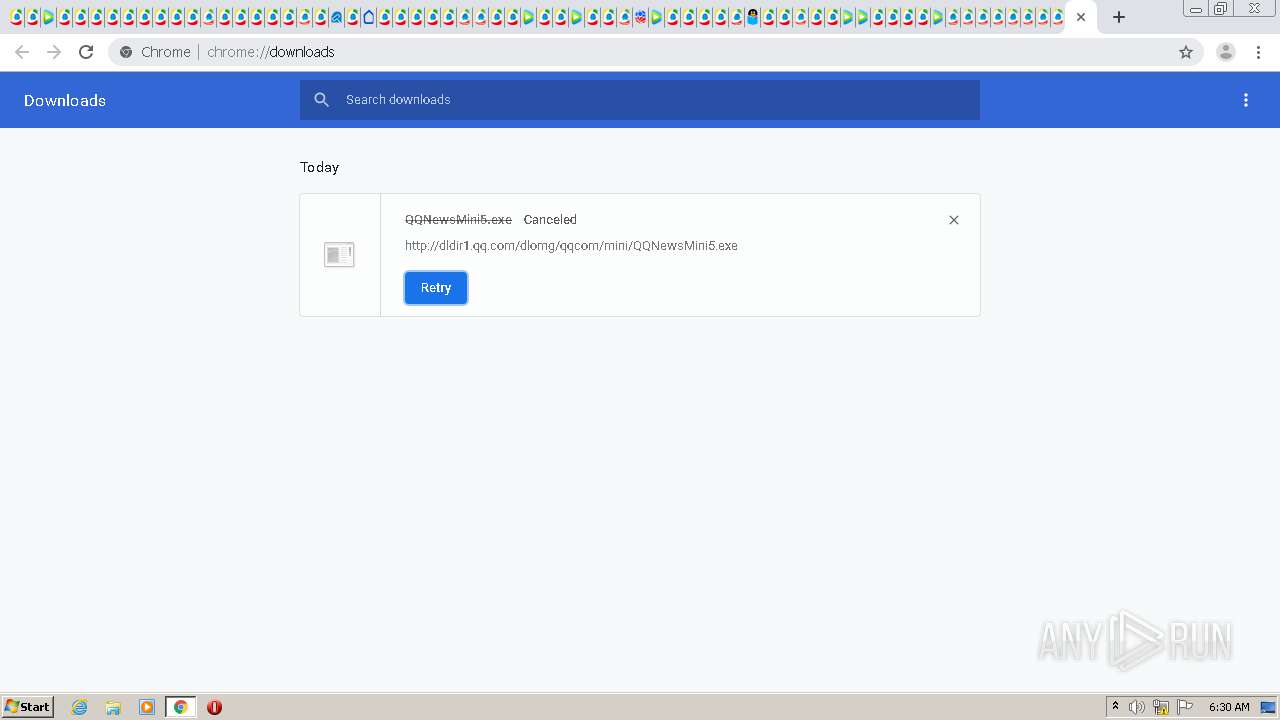
MALICIOUS
No malicious indicators.SUSPICIOUS
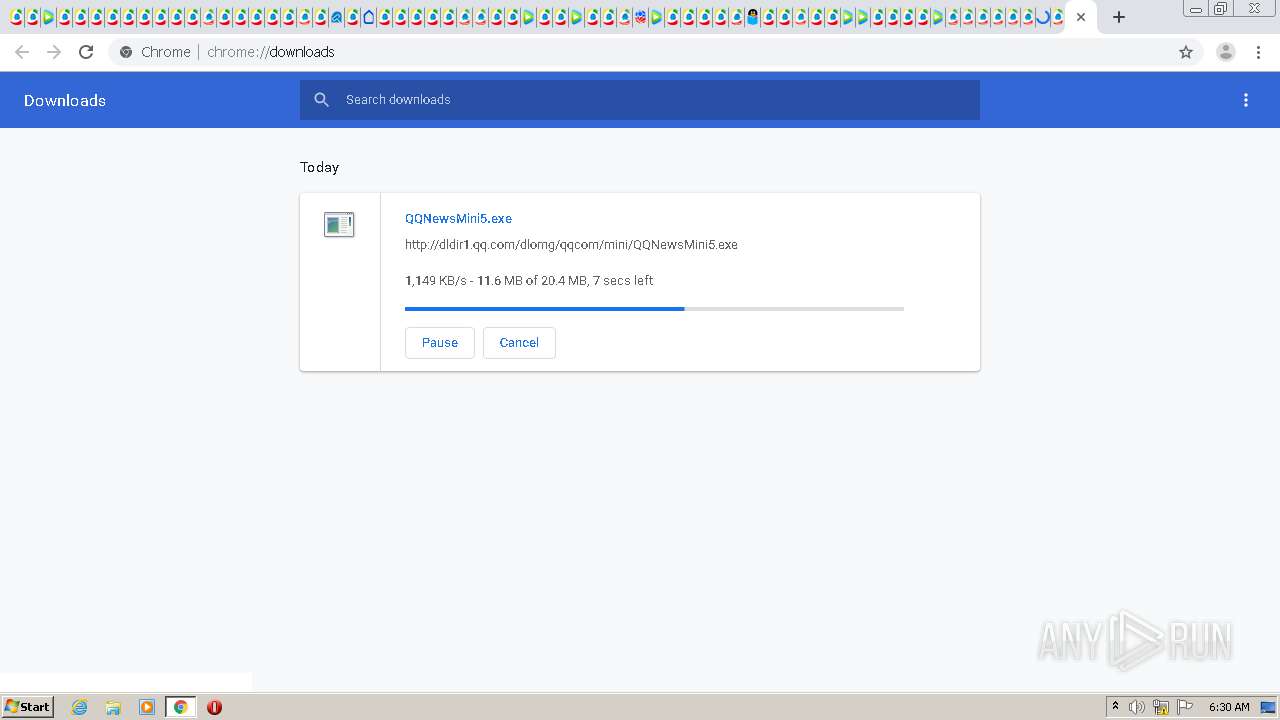
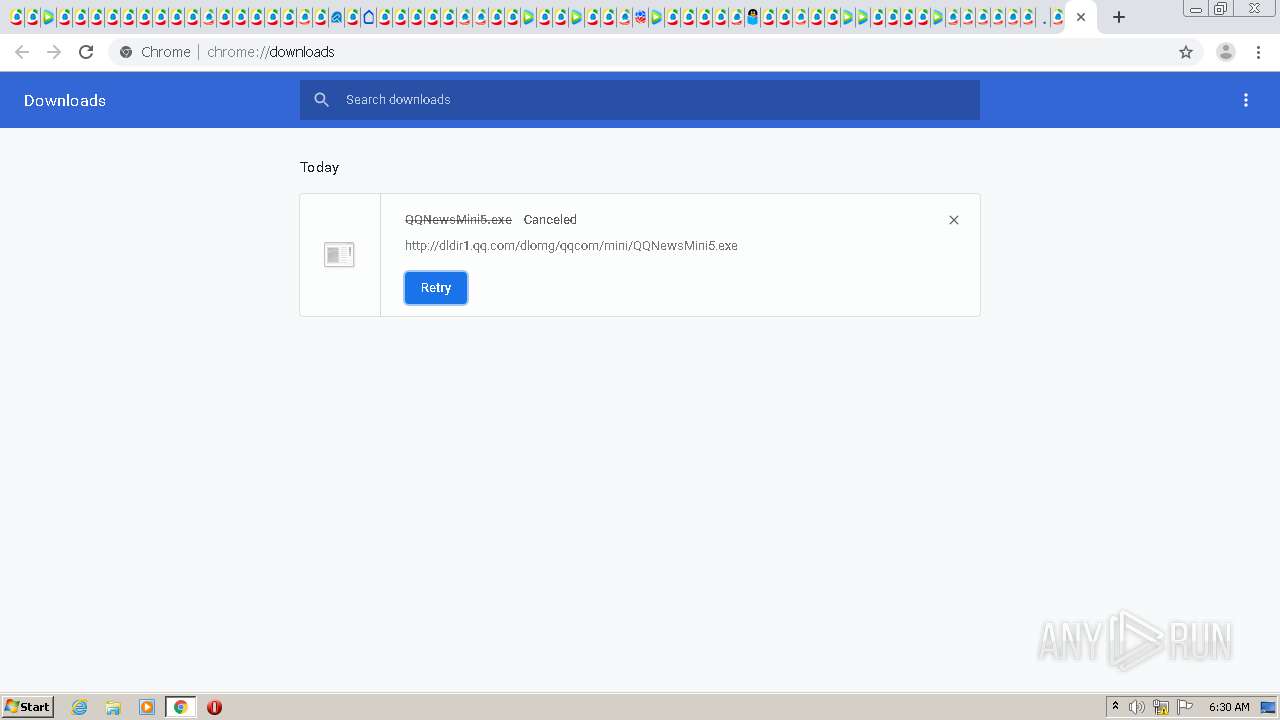
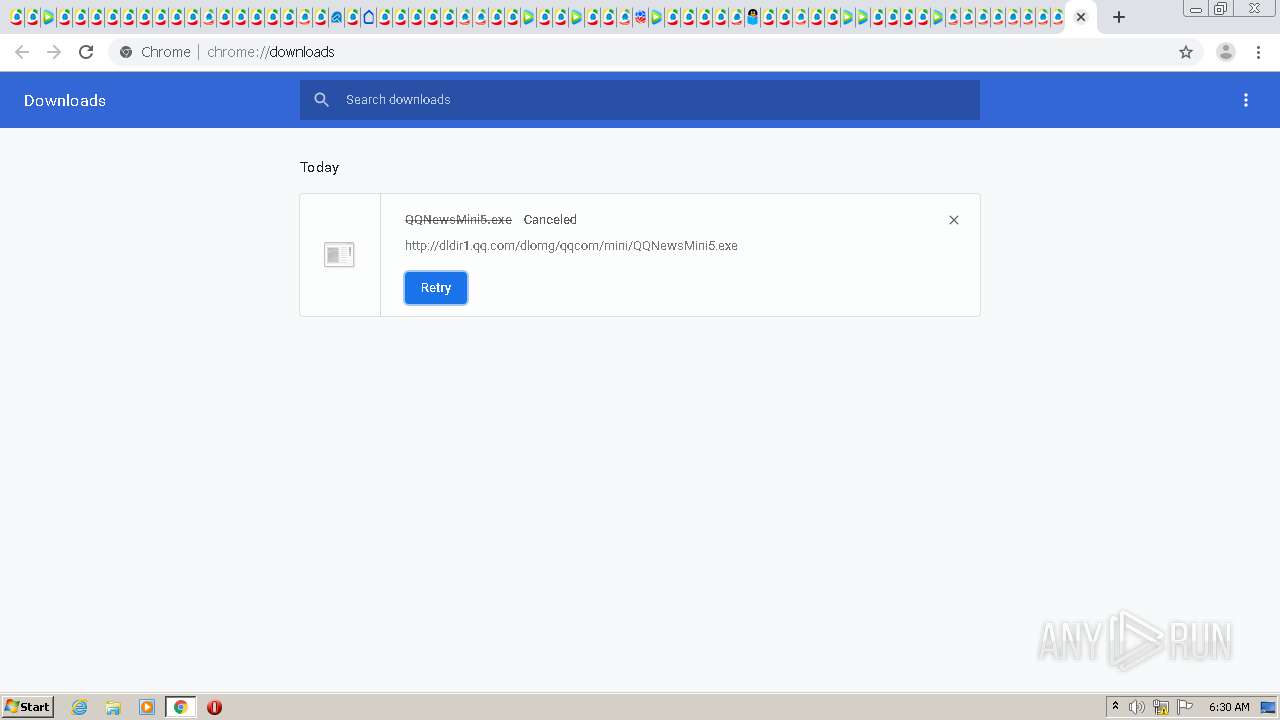
Executable content was dropped or overwritten
- chrome.exe (PID: 2552)
- chrome.exe (PID: 2160)
INFO
Reads the hosts file
- chrome.exe (PID: 2552)
- chrome.exe (PID: 2160)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2552)
Application launched itself
- chrome.exe (PID: 2552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
119
Monitored processes
81
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,10994499680523383493,12715929634606413860,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15483827771945224722 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,10994499680523383493,12715929634606413860,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15568579178437693337 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,10994499680523383493,12715929634606413860,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15600544959735678950 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,10994499680523383493,12715929634606413860,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1967211755054016193 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3688 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,10994499680523383493,12715929634606413860,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8302234466614829382 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3868 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,10994499680523383493,12715929634606413860,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1053116555927639619 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,10994499680523383493,12715929634606413860,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15981518950941266702 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,10994499680523383493,12715929634606413860,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6194692229926216481 --mojo-platform-channel-handle=1060 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,10994499680523383493,12715929634606413860,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9821348704917027210 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,10994499680523383493,12715929634606413860,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=cdm --service-request-channel-token=5806297033677868962 --mojo-platform-channel-handle=5620 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 083
Read events
913
Write events
166
Delete events
4
Modification events
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2552-13246003560569375 |
Value: 259 | |||
Executable files
3
Suspicious files
880
Text files
2 195
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F756869-9F8.pma | — | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\aad431bc-8d6f-49fb-b0a7-f796b5f105fd.tmp | — | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF227a7a.TMP | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF227a5a.TMP | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF227ae7.TMP | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2552 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF227a1c.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 248
TCP/UDP connections
591
DNS requests
345
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2160 | chrome.exe | GET | 301 | 104.111.239.81:80 | http://news.qq.com/ | NL | — | — | whitelisted |
2160 | chrome.exe | GET | 200 | 104.111.239.81:80 | http://img1.gtimg.com/ninja/2/2018/10/ninja153907290259802.png | NL | image | 8.34 Kb | whitelisted |
2160 | chrome.exe | GET | 200 | 104.111.239.81:80 | http://inews.gtimg.com/newsapp_ls/0/12550859173_640330/0 | NL | image | 15.9 Kb | whitelisted |
2160 | chrome.exe | GET | 200 | 104.111.239.81:80 | http://inews.gtimg.com/newsapp_ls/0/12550756219_640330/0 | NL | image | 13.1 Kb | whitelisted |
2160 | chrome.exe | GET | 200 | 104.111.239.81:80 | http://inews.gtimg.com/newsapp_ls/0/12550842234_640330/0 | NL | image | 26.2 Kb | whitelisted |
2160 | chrome.exe | GET | 200 | 104.111.239.81:80 | http://inews.gtimg.com/newsapp_ls/0/12550843930_640330/0 | NL | image | 21.2 Kb | whitelisted |
2160 | chrome.exe | GET | 200 | 104.111.239.81:80 | http://inews.gtimg.com/newsapp_ls/0/12550437963_640330/0 | NL | image | 10.2 Kb | whitelisted |
2160 | chrome.exe | GET | 200 | 104.111.239.81:80 | http://inews.gtimg.com/newsapp_ls/0/12550818124_640330/0 | NL | image | 21.9 Kb | whitelisted |
2160 | chrome.exe | GET | 200 | 104.111.239.81:80 | http://inews.gtimg.com/newsapp_ls/0/12547351408_640330/0 | NL | image | 17.9 Kb | whitelisted |
2160 | chrome.exe | GET | 200 | 104.111.239.81:80 | http://inews.gtimg.com/newsapp_ls/0/12548182759_640330/0 | NL | image | 36.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
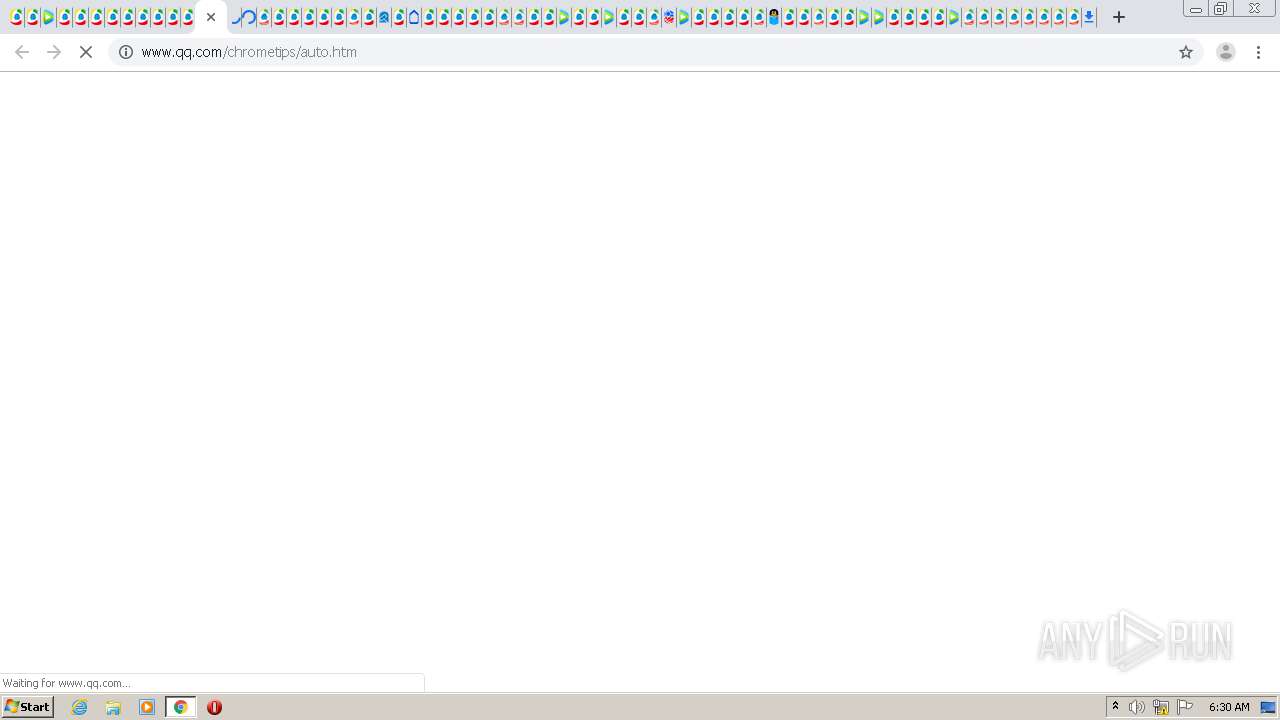
2160 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2160 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2160 | chrome.exe | 104.111.239.81:443 | www.qq.com | Akamai International B.V. | NL | unknown |
2160 | chrome.exe | 104.111.239.81:80 | www.qq.com | Akamai International B.V. | NL | unknown |
2160 | chrome.exe | 211.152.136.120:443 | mat1.gtimg.com | — | CN | unknown |
2160 | chrome.exe | 104.111.215.42:443 | vm.gtimg.cn | Akamai International B.V. | NL | whitelisted |
2160 | chrome.exe | 211.152.136.120:80 | mat1.gtimg.com | — | CN | unknown |
2160 | chrome.exe | 203.205.137.232:443 | ra.gtimg.com | Tencent Building, Kejizhongyi Avenue | CN | unknown |
2160 | chrome.exe | 203.205.255.191:443 | trace.qq.com | — | CN | suspicious |
2160 | chrome.exe | 2.18.234.88:443 | matchweb.sports.qq.com | Akamai International B.V. | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
qq.com |
| malicious |
accounts.google.com |
| shared |
www.qq.com |
| whitelisted |
mat1.gtimg.com |
| whitelisted |
img1.gtimg.com |
| whitelisted |
inews.gtimg.com |
| unknown |
vm.gtimg.cn |
| whitelisted |
imgcache.qq.com |
| whitelisted |
ra.gtimg.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2160 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
2160 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
2160 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
2160 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
2160 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
2160 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
2160 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
2160 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
2160 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |
2160 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pwd= in cleartext |