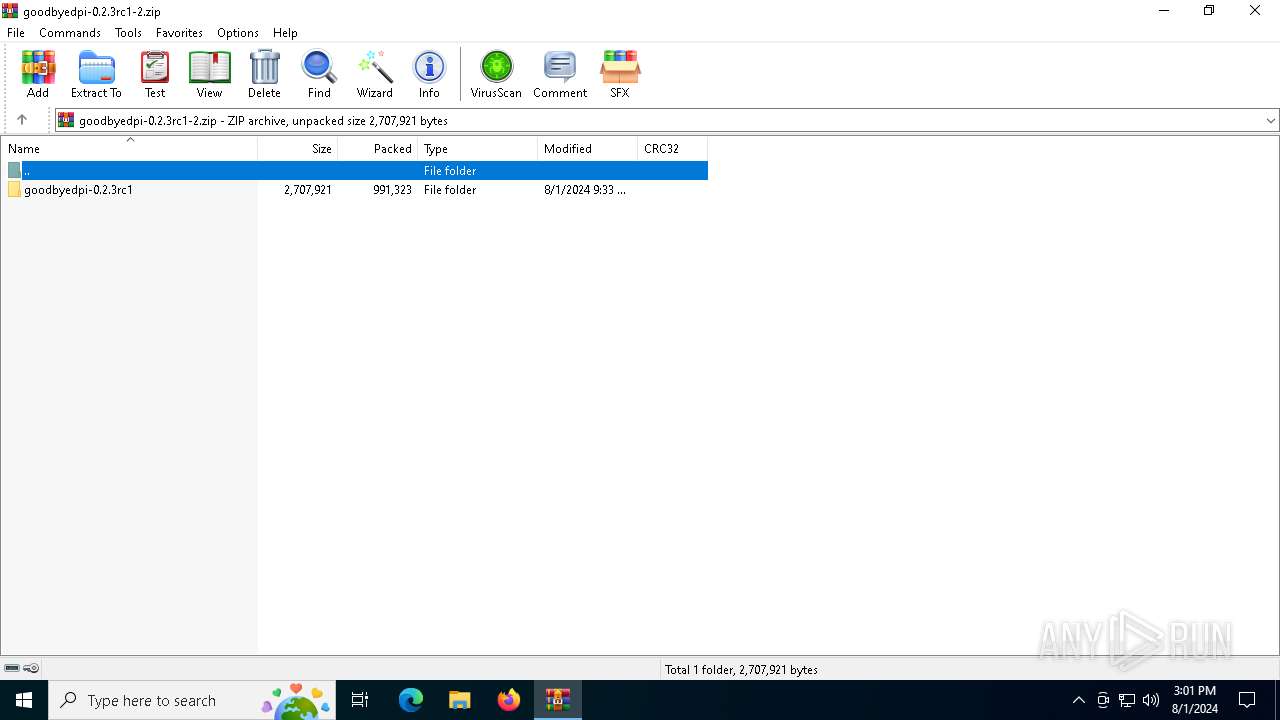
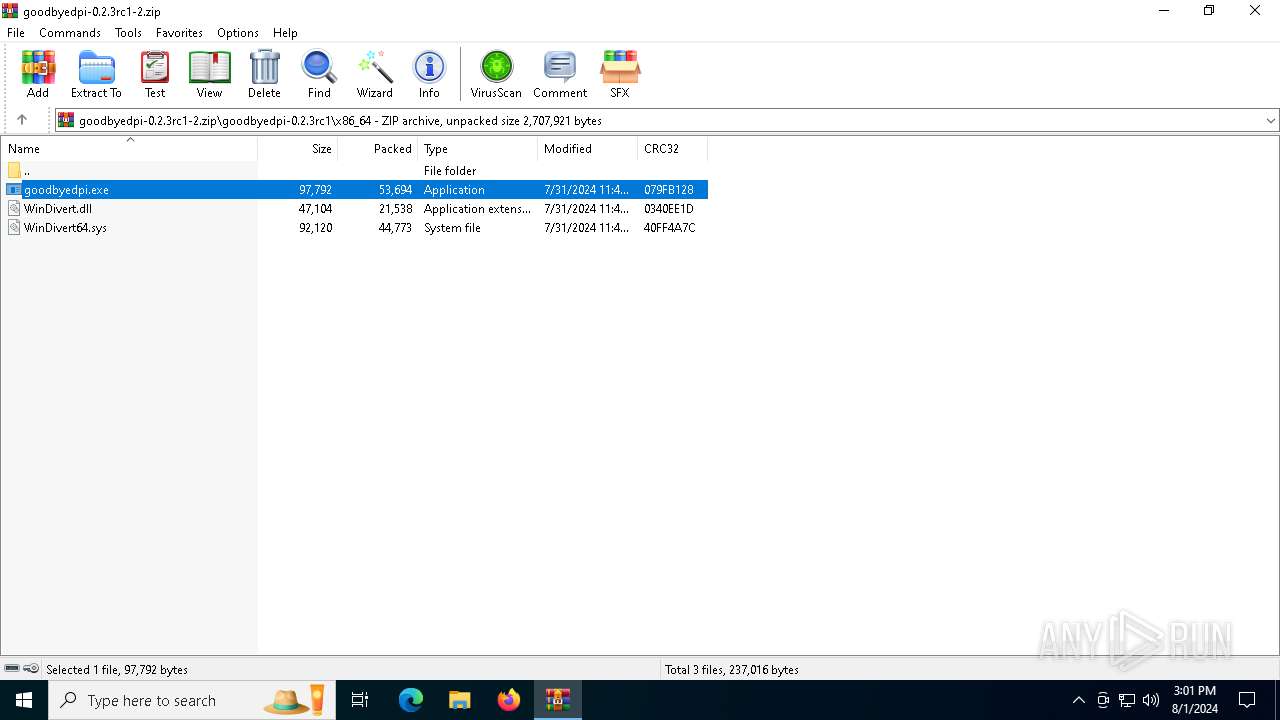
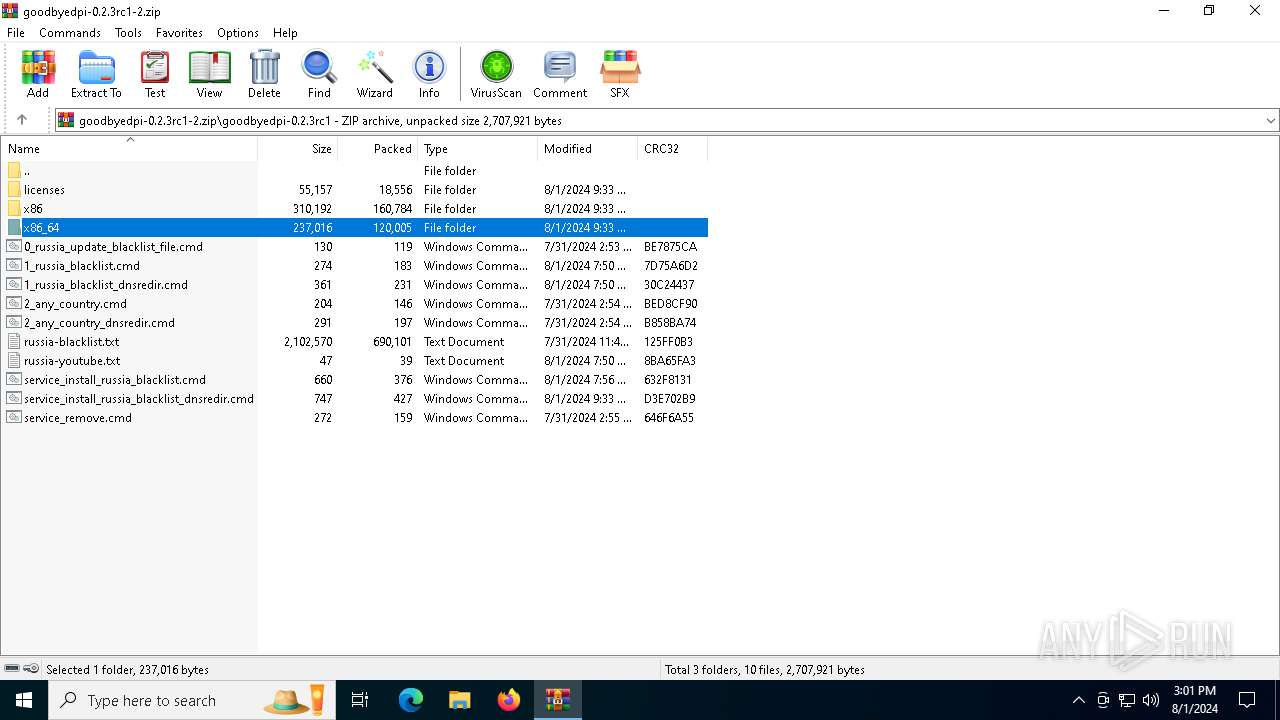
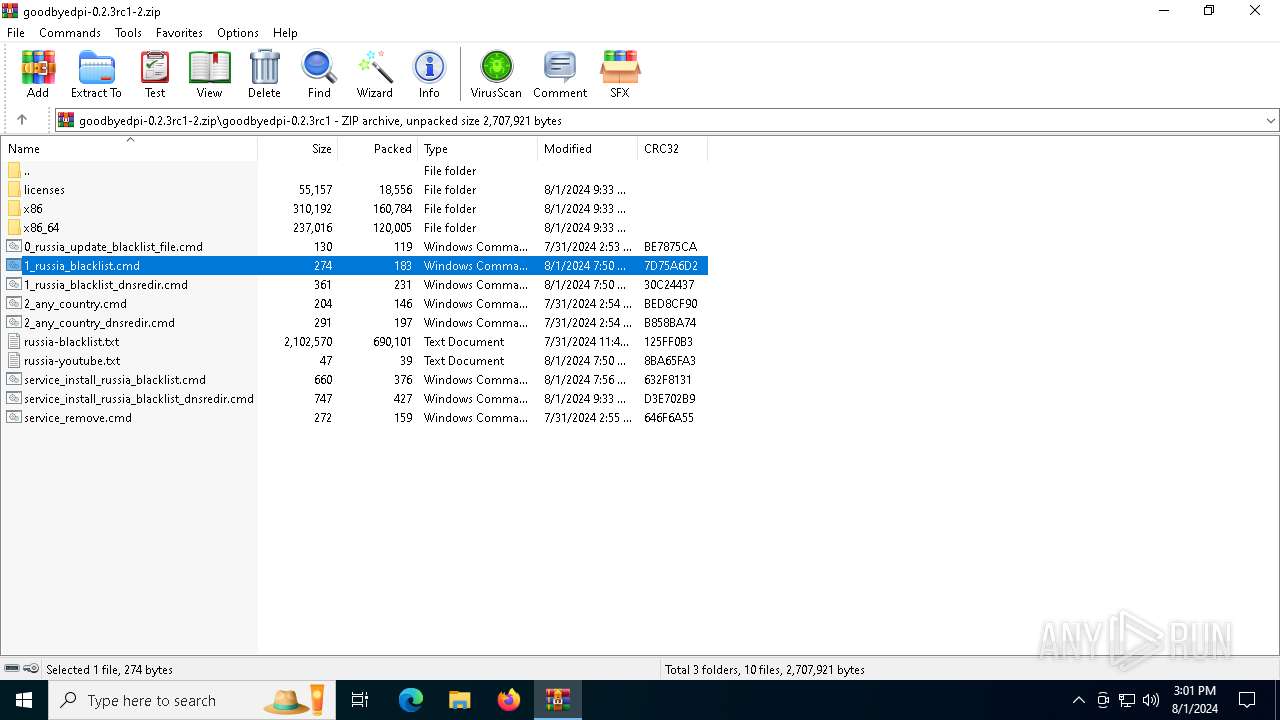
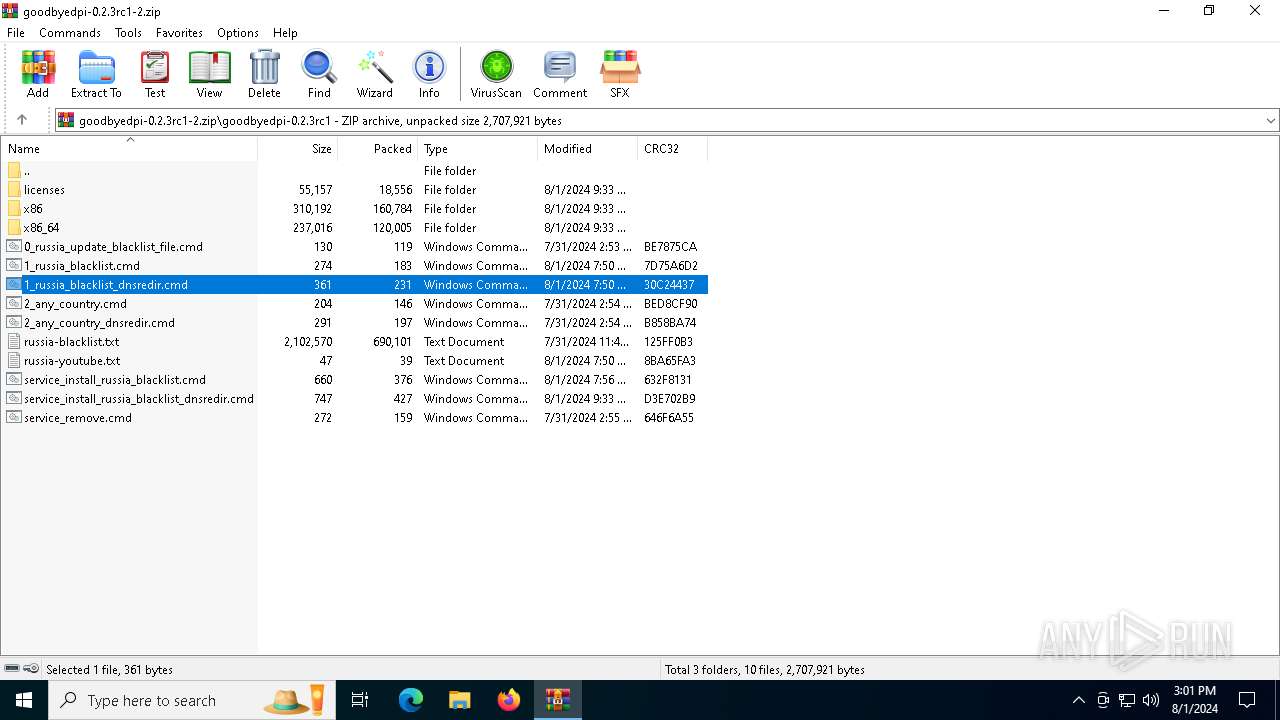
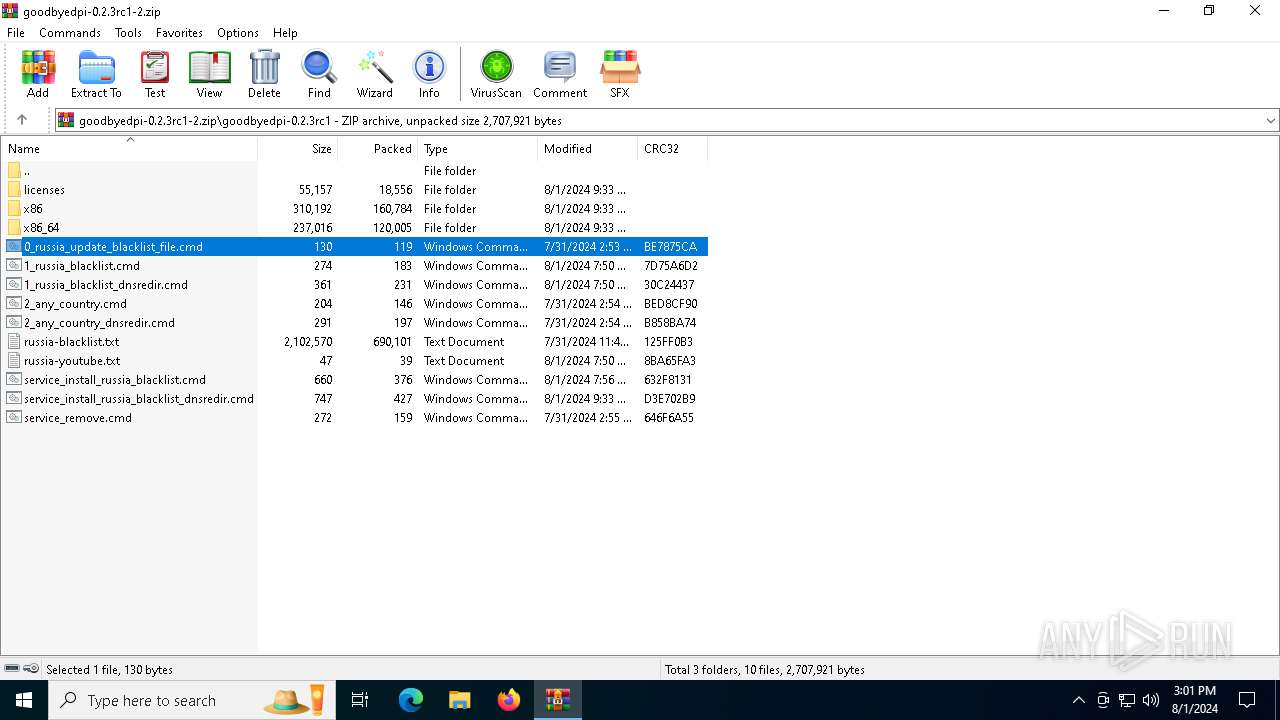
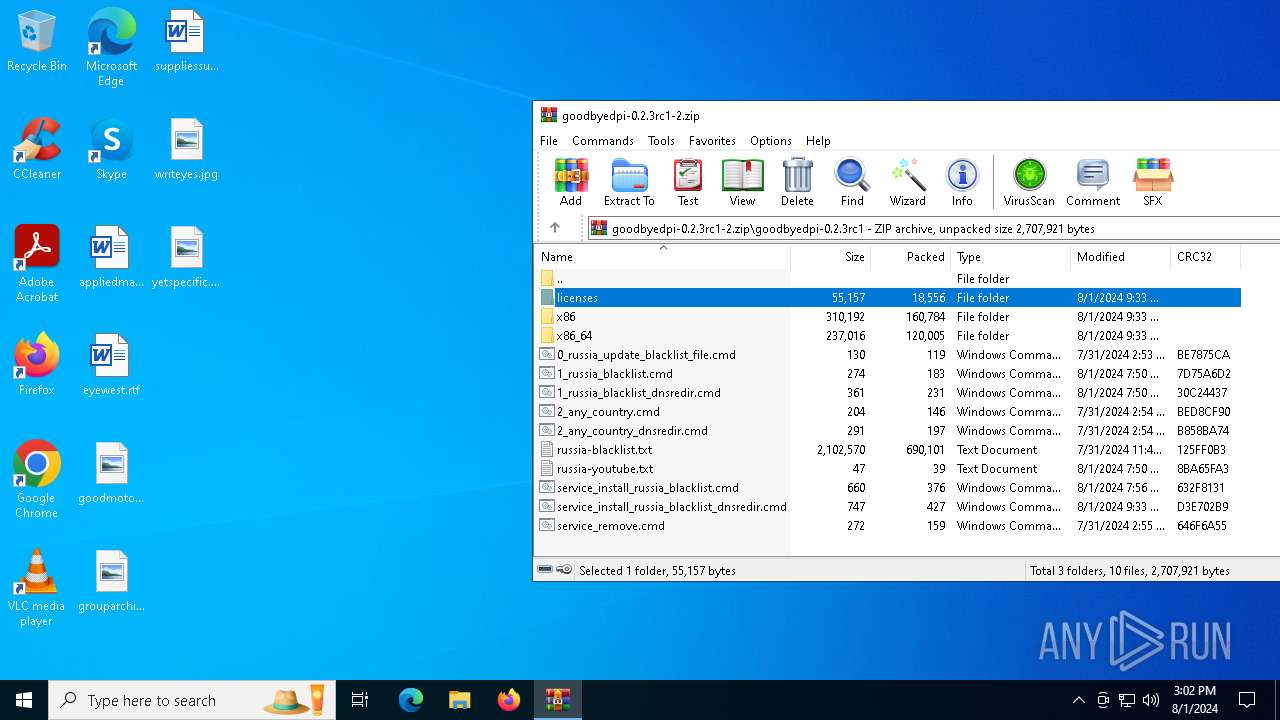
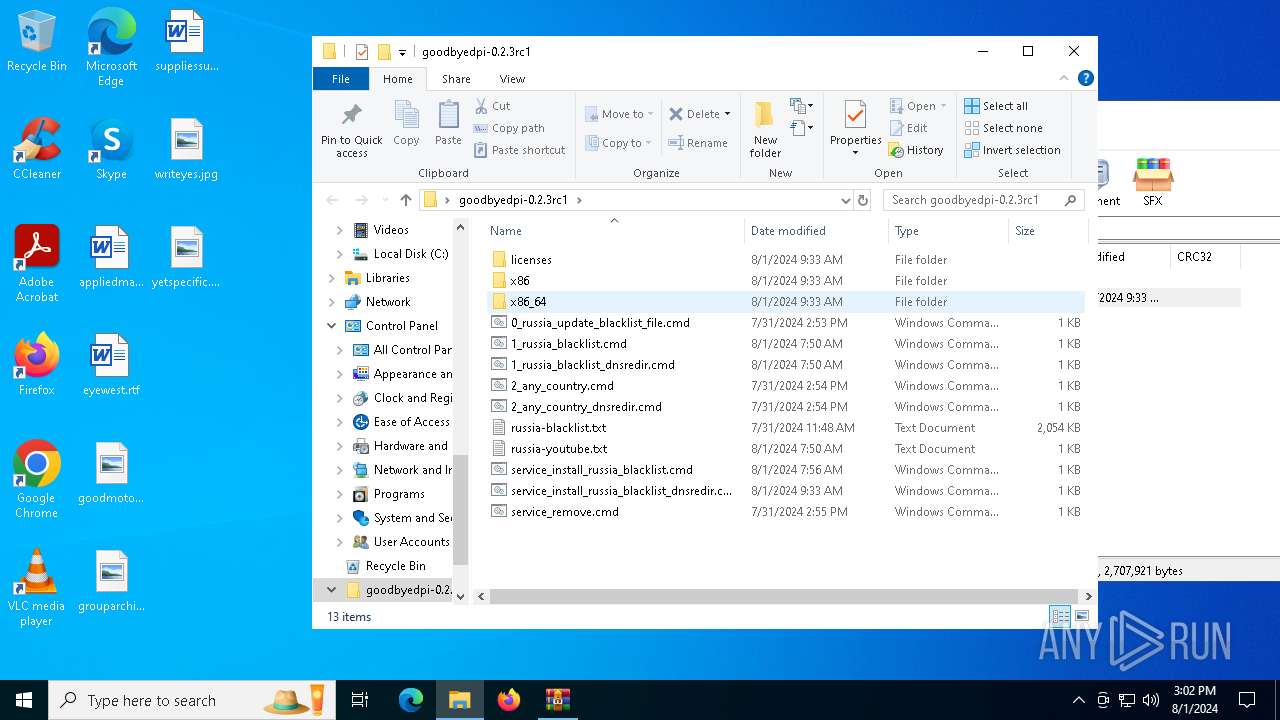
| File name: | goodbyedpi-0.2.3rc1-2.zip |
| Full analysis: | https://app.any.run/tasks/fbec67d3-951b-42aa-87ea-a3cd2ebdaf32 |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2024, 15:01:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 41938D1256F900CDACA626A152BA5E95 |
| SHA1: | DBAFC9A75213D46B19E8FD7A330B87BFD8C0B562 |
| SHA256: | E3FF0DE76A44978EBD02B890F66BE6F3F4320C99F8B443DE1877D4E16A4A5443 |
| SSDEEP: | 49152:0AJn6dfL7XeDJmJS57XeLoMd1ZeGdZtQdrK/DFam2pkAUZq+KrqhOe+6wADOE7LU:VN6dfL7uDJp57u0UZN8BKbUTKNts6wA6 |
MALICIOUS
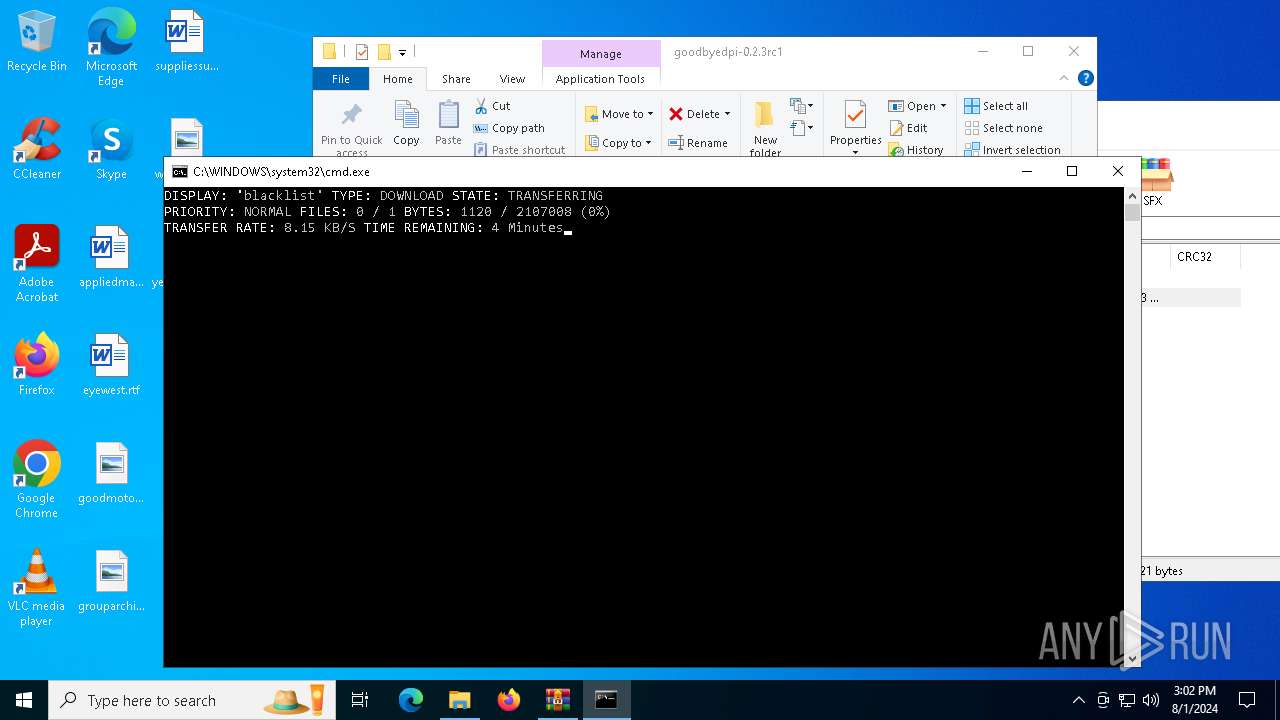
Downloads files via BITSADMIN.EXE
- cmd.exe (PID: 2136)
- cmd.exe (PID: 6680)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6284)
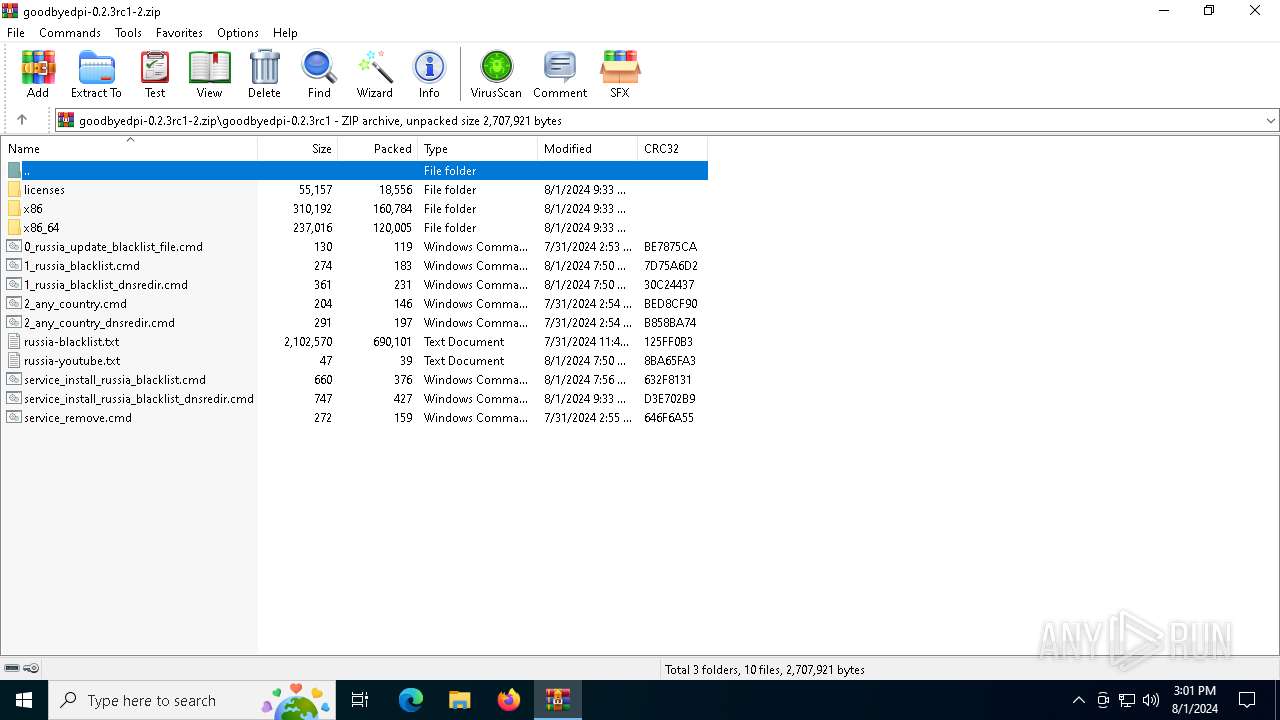
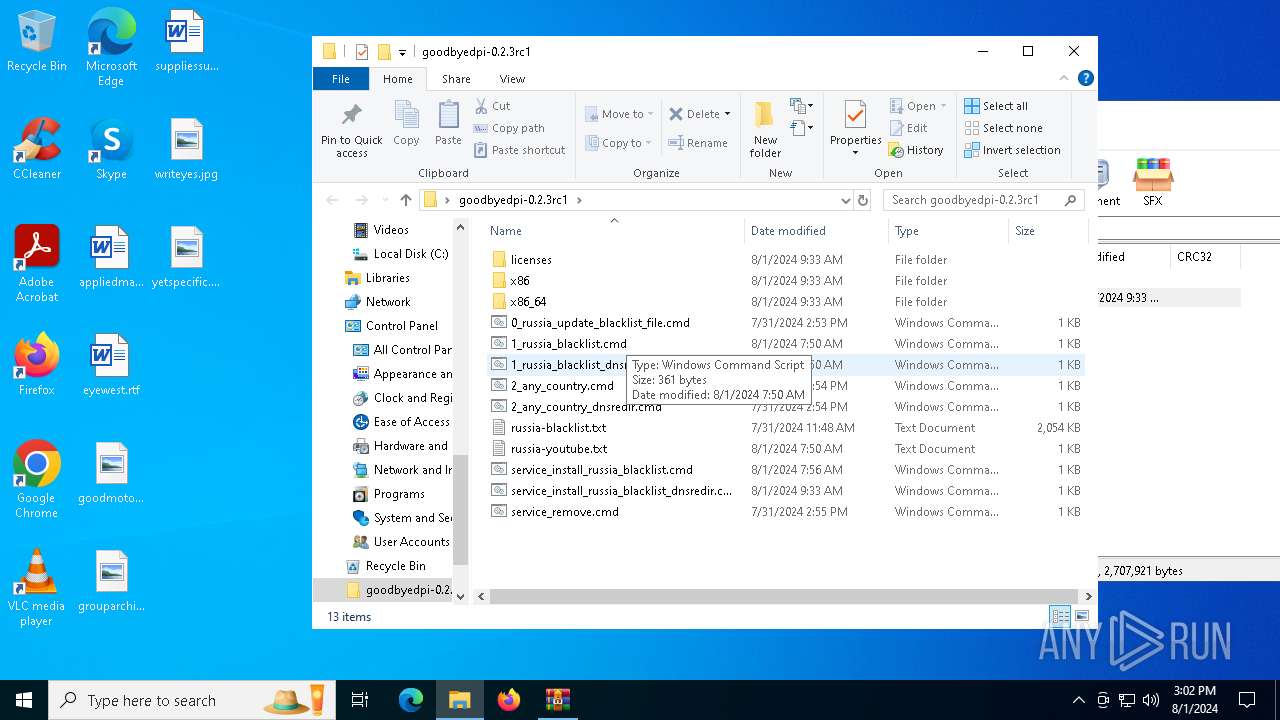
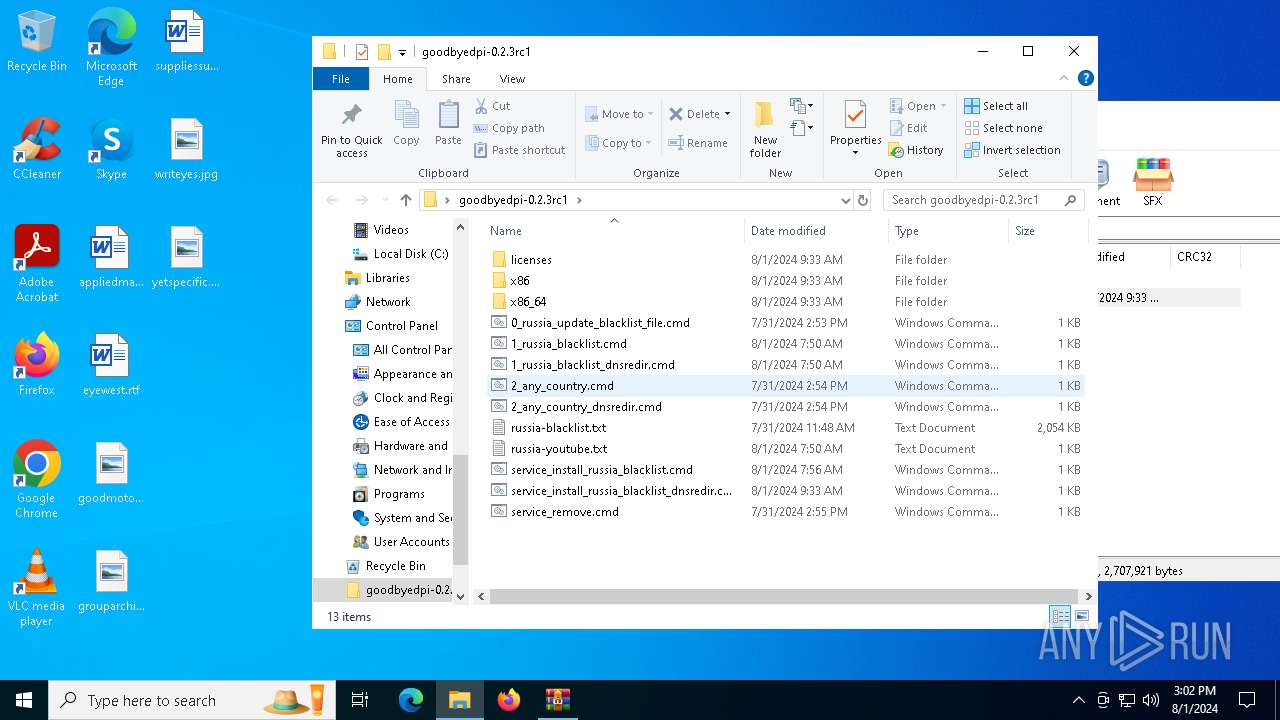
Executing commands from ".cmd" file
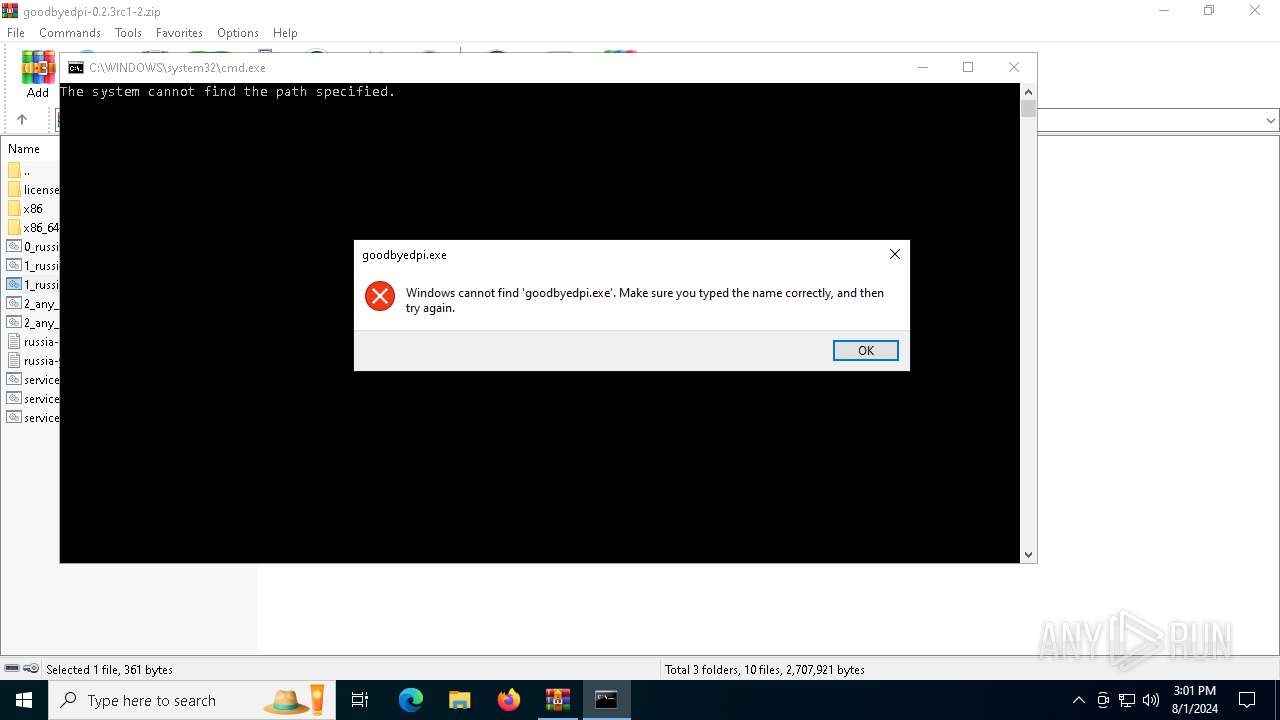
- WinRAR.exe (PID: 6284)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 6284)
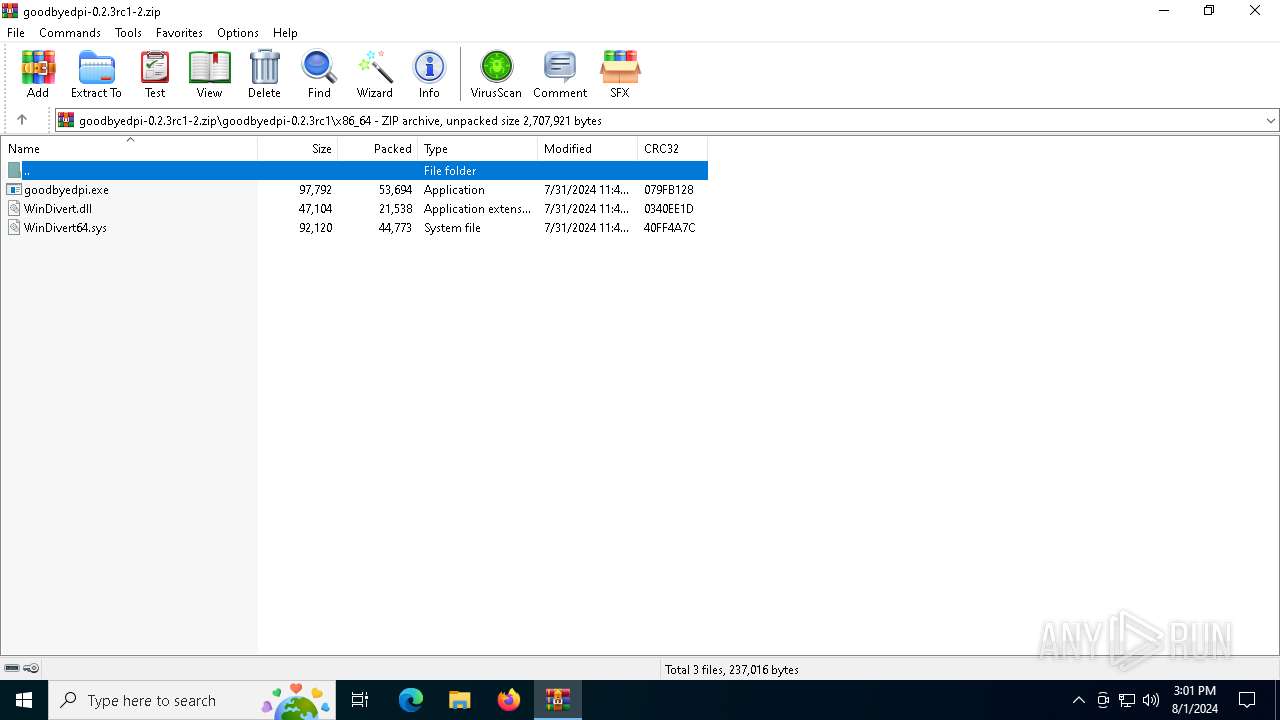
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6284)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6284)
Reads the computer name
- goodbyedpi.exe (PID: 6628)
Checks supported languages
- goodbyedpi.exe (PID: 6628)
Reads the machine GUID from the registry
- goodbyedpi.exe (PID: 6628)
Manual execution by a user
- cmd.exe (PID: 6680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:08:01 09:33:12 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | goodbyedpi-0.2.3rc1/ |
Total processes
151
Monitored processes
15
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
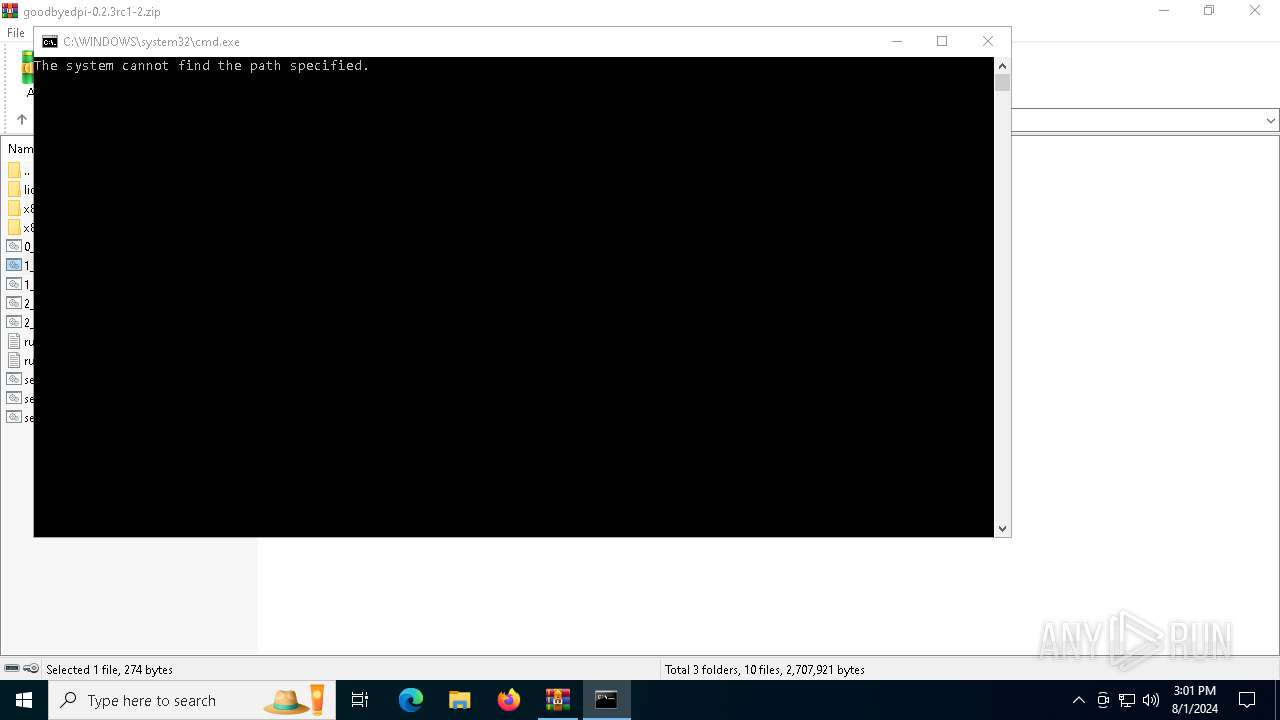
| 1168 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa6284.32084\1_russia_blacklist.cmd" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
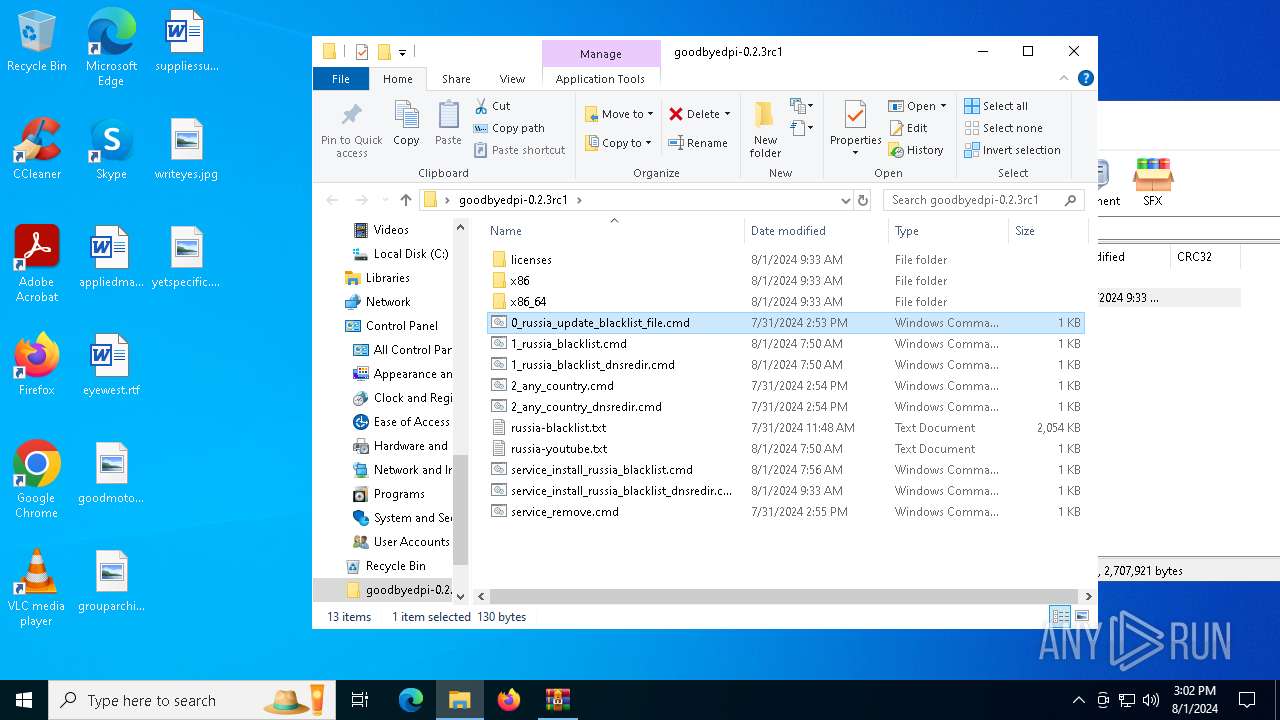
| 2136 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa6284.32653\0_russia_update_blacklist_file.cmd" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2336 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa6284.32398\1_russia_blacklist_dnsredir.cmd" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2396 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4544 | bitsadmin /transfer blacklist https://p.thenewone.lol/domains-export.txt "C:\Users\admin\Desktop\goodbyedpi-0.2.3rc1\russia-blacklist.txt" | C:\Windows\System32\bitsadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BITS administration utility Version: 7.8.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6244 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6284 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Downloads\goodbyedpi-0.2.3rc1-2.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
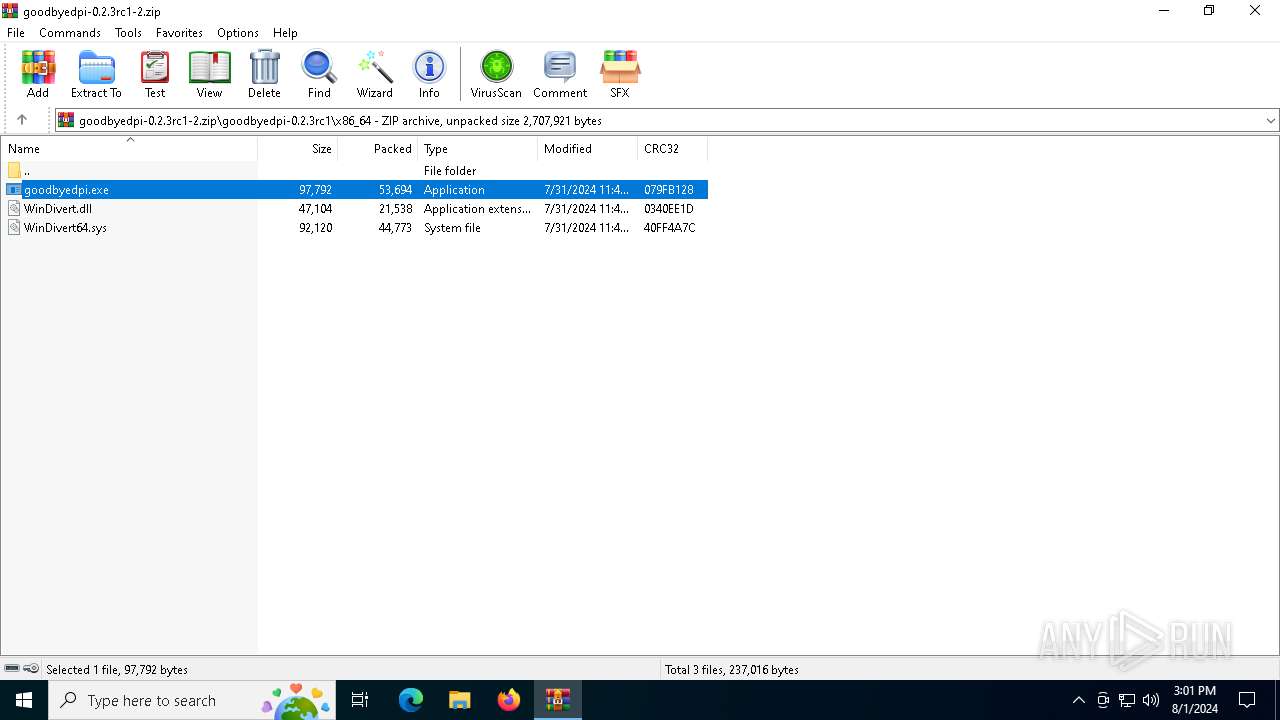
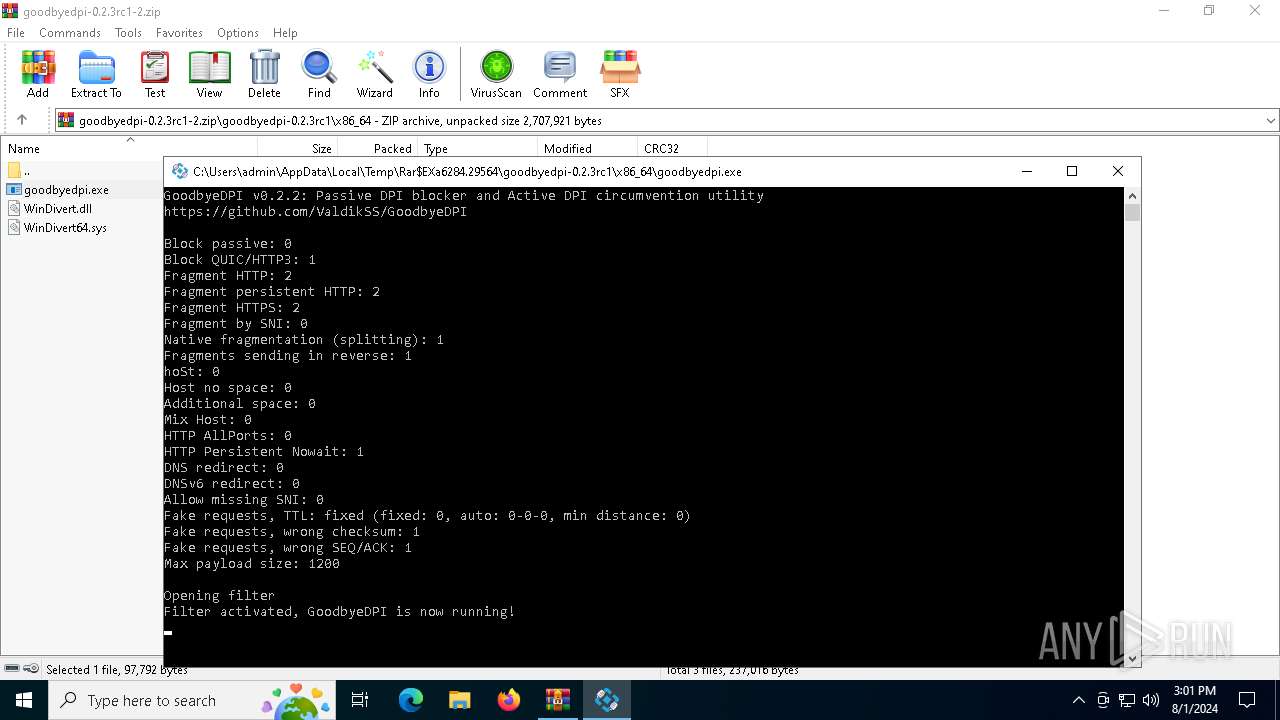
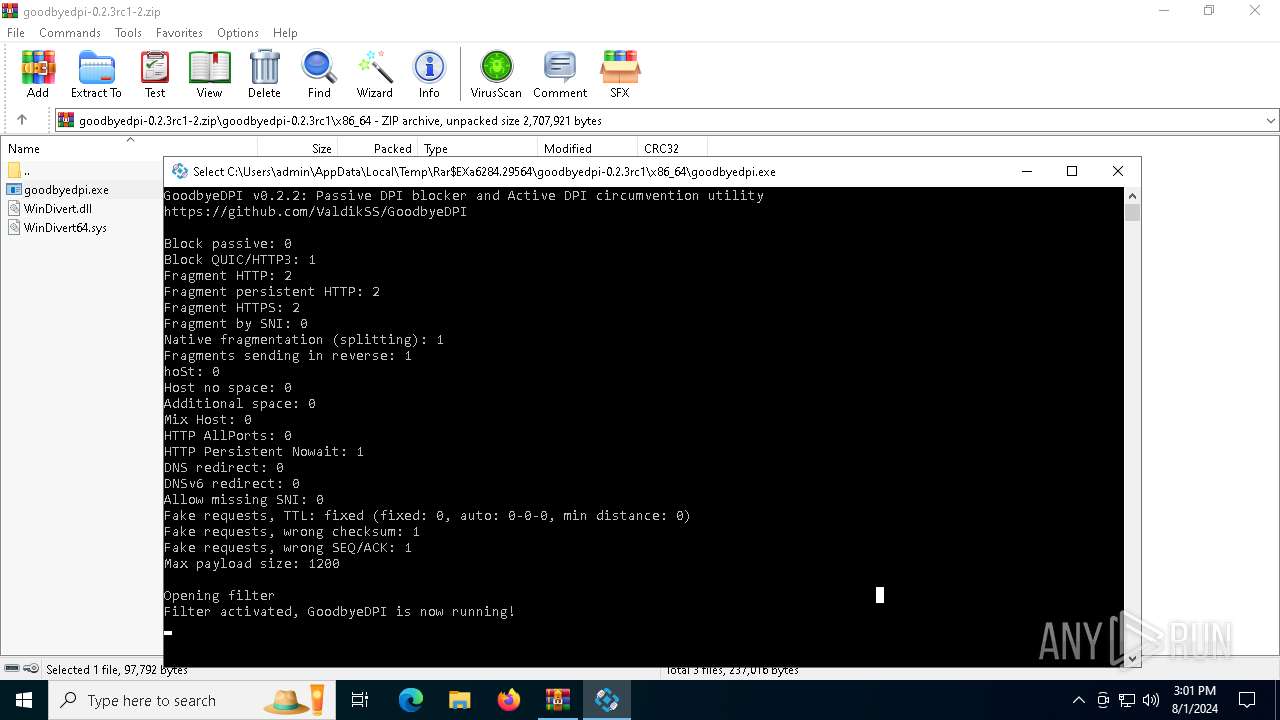
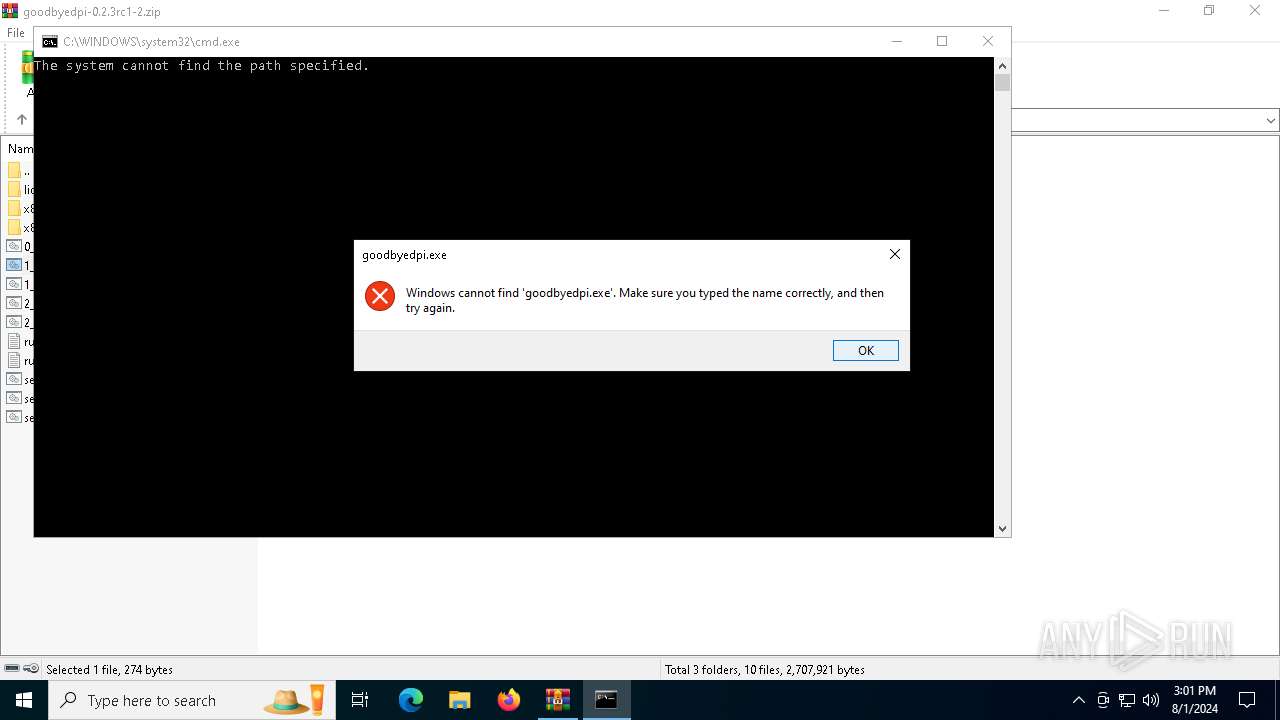
| 6572 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6284.29564\goodbyedpi-0.2.3rc1\x86_64\goodbyedpi.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6284.29564\goodbyedpi-0.2.3rc1\x86_64\goodbyedpi.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
7 256
Read events
7 236
Write events
20
Delete events
0
Modification events
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\goodbyedpi-0.2.3rc1-2.zip | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\System32\acppage.dll,-6003 |
Value: Windows Command Script | |||
| (PID) Process: | (6284) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
14
Suspicious files
0
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6284.29564\goodbyedpi-0.2.3rc1\licenses\LICENSE-getline.txt | text | |
MD5:3A7EDEBC3612BCEA2306F73B92342A44 | SHA256:EC5F8E03FCCB3842CC62AD79EA5F6F6058988E2721A3E6566E8FB72786D485C4 | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6284.29564\goodbyedpi-0.2.3rc1\x86\WinDivert.dll | executable | |
MD5:1CB0EFD60883B5637B31BF46C34AE199 | SHA256:625FFDD95BFABFF32D0E8A95BEABCD303C01C8BBA73B90402D4E84D6E15DD8E5 | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6284.29564\goodbyedpi-0.2.3rc1\licenses\LICENSE-windivert.txt | text | |
MD5:B864FBB188A7C3A11CEF80F3EE902D77 | SHA256:E5453B2E71E4C4DCDB89A2539655ADD3A63202521CF3012B768E8BFEDA199312 | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6284.29564\goodbyedpi-0.2.3rc1\x86\WinDivert32.sys | executable | |
MD5:CD477EE96FF05CACDA8AC3C0E9316D7A | SHA256:29CA5CEB59C9C6993A349E82B1FD46078E6F8A302764153AB84FA22E382FCDCA | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6284.29564\goodbyedpi-0.2.3rc1\licenses\LICENSE-uthash.txt | text | |
MD5:5CC1F1E4C71F19F580458586756C02B4 | SHA256:D3C6556E48104C31E3E0C62238C749C2A09CA79EE87DA50B9CD29C6C9027D57D | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6284.29564\goodbyedpi-0.2.3rc1\x86\goodbyedpi.exe | executable | |
MD5:92A6C37A997FBA11F9E26995925CBEE6 | SHA256:DA0884D6B282FF934C0D7392A50EFCA03C65943B6E2B6254E14E81420F0EBB5F | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6284.29564\goodbyedpi-0.2.3rc1\x86_64\goodbyedpi.exe | executable | |
MD5:FD680538C2A80DC54C63AE39C3563FBD | SHA256:FA9A32AE6EB24E2290941EA60F80E914168E1F84E900293BFFD4393FB9A8FAE2 | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6284.29564\goodbyedpi-0.2.3rc1\x86_64\WinDivert.dll | executable | |
MD5:88E1C19B978436258F7C938013408A8A | SHA256:6110BFA44667405179C3E15E12AF1B62037E447ED59B054B19042032995E6C7E | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6284.29564\goodbyedpi-0.2.3rc1\1_russia_blacklist_dnsredir.cmd | text | |
MD5:06018C5958CDDD1D0CF3135762AEB2EB | SHA256:472D9BD4F0366BB9478B6CD61302F12BF6CFFBED038508A67087250BF610E355 | |||
| 6284 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6284.29564\goodbyedpi-0.2.3rc1\2_any_country.cmd | text | |
MD5:72103C58F2ED536EBC07E19FD00FA2F0 | SHA256:17A3D7B8B1E1340F67D3687CE9162199C0A25025941D23954880808403487D07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
46
DNS requests
18
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://www.w3.org/ | US | — | 471 b | whitelisted |
4 | System | GET | 200 | 192.229.221.95:80 | http://www.w3.org/ | US | — | 471 b | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://www.w3.org/ | US | — | 313 b | whitelisted |
4 | System | GET | 200 | 192.229.221.95:80 | http://www.w3.org/ | US | — | 471 b | whitelisted |
4192 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://www.w3.org/ | US | — | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
876 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
5040 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
5336 | SearchApp.exe | 2.23.209.191:443 | www.bing.com | Akamai International B.V. | GB | unknown |
4 | System | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | unknown |
4 | System | 2.23.209.130:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 2.23.209.130:443 | www.bing.com | Akamai International B.V. | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
google.com |
| unknown |
www.bing.com |
| unknown |
ocsp.digicert.com |
| unknown |
th.bing.com |
| unknown |
r.bing.com |
| unknown |
browser.pipe.aria.microsoft.com |
| unknown |
login.live.com |
| unknown |
client.wns.windows.com |
| unknown |
fd.api.iris.microsoft.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5336 | SearchApp.exe | Generic Protocol Command Decode | SURICATA TLS handshake invalid length |
5336 | SearchApp.exe | Generic Protocol Command Decode | SURICATA TLS handshake invalid length |
5336 | SearchApp.exe | Generic Protocol Command Decode | SURICATA TLS handshake invalid length |
5336 | SearchApp.exe | Generic Protocol Command Decode | SURICATA TLS handshake invalid length |
4 | System | Generic Protocol Command Decode | SURICATA TLS handshake invalid length |
4 | System | Generic Protocol Command Decode | SURICATA TLS handshake invalid length |
5336 | SearchApp.exe | Generic Protocol Command Decode | SURICATA TLS handshake invalid length |
5336 | SearchApp.exe | Generic Protocol Command Decode | SURICATA TLS handshake invalid length |
4192 | backgroundTaskHost.exe | Generic Protocol Command Decode | SURICATA TLS handshake invalid length |
4192 | backgroundTaskHost.exe | Generic Protocol Command Decode | SURICATA TLS handshake invalid length |