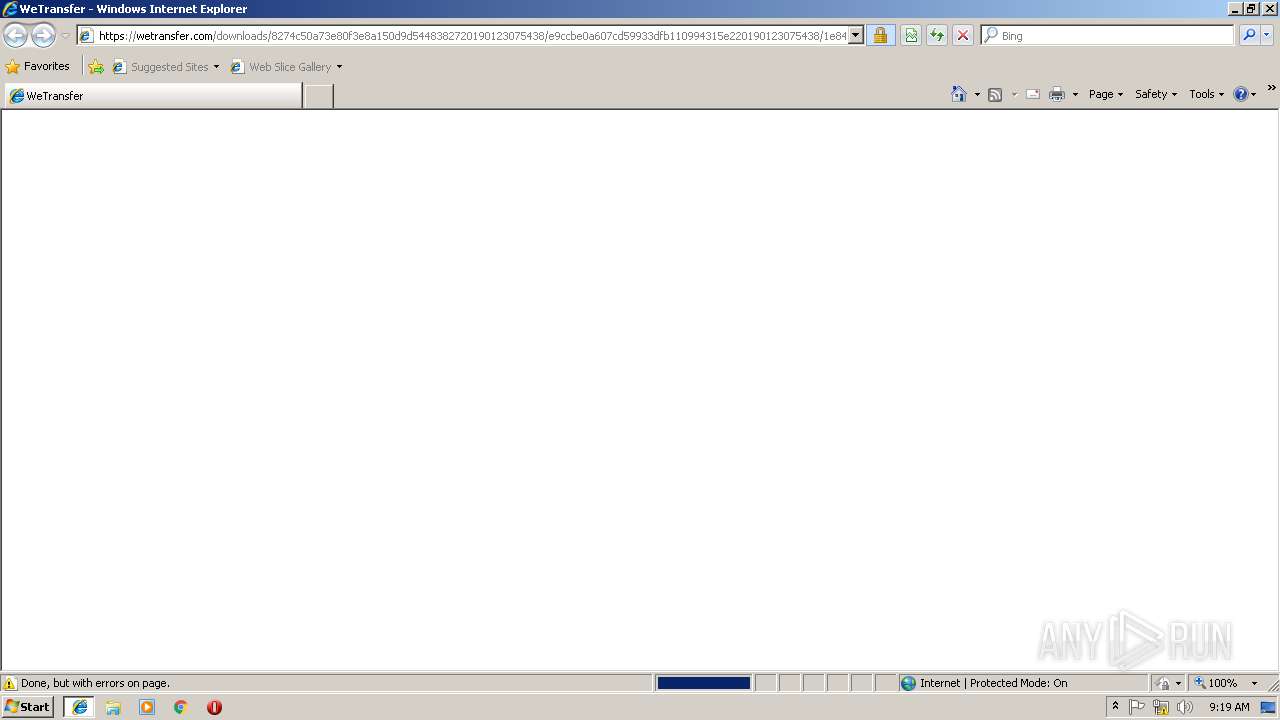
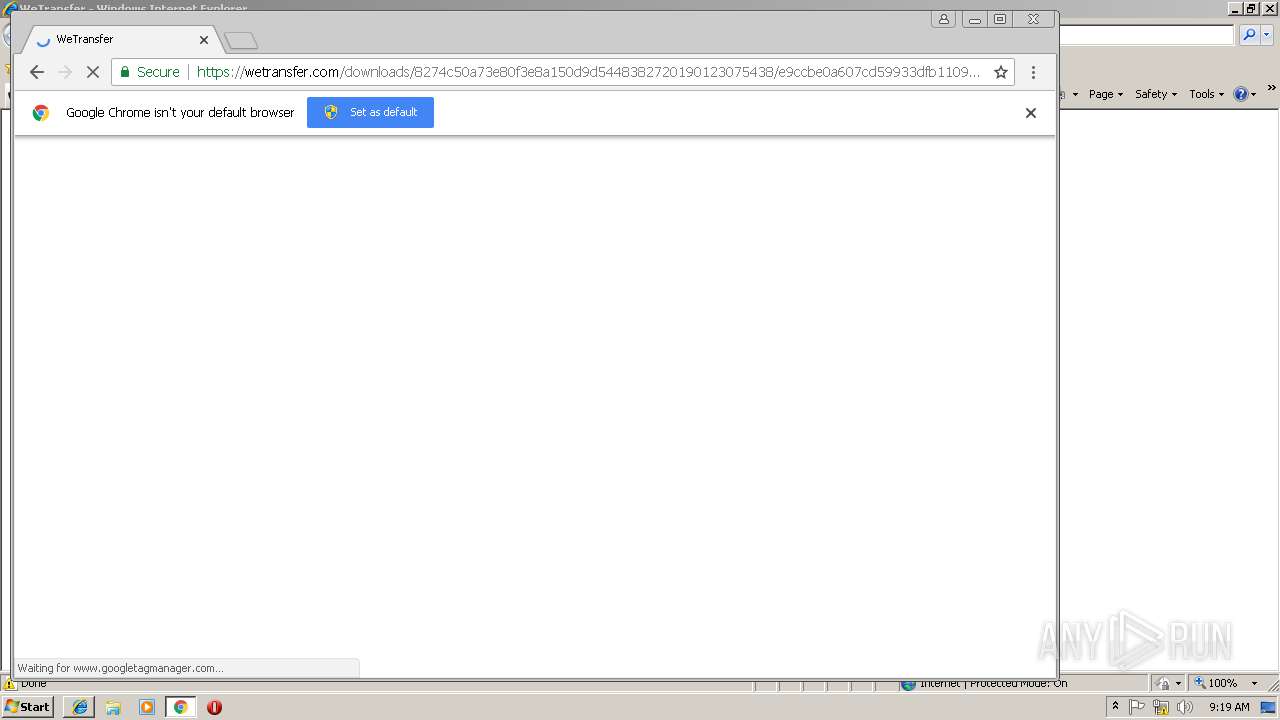
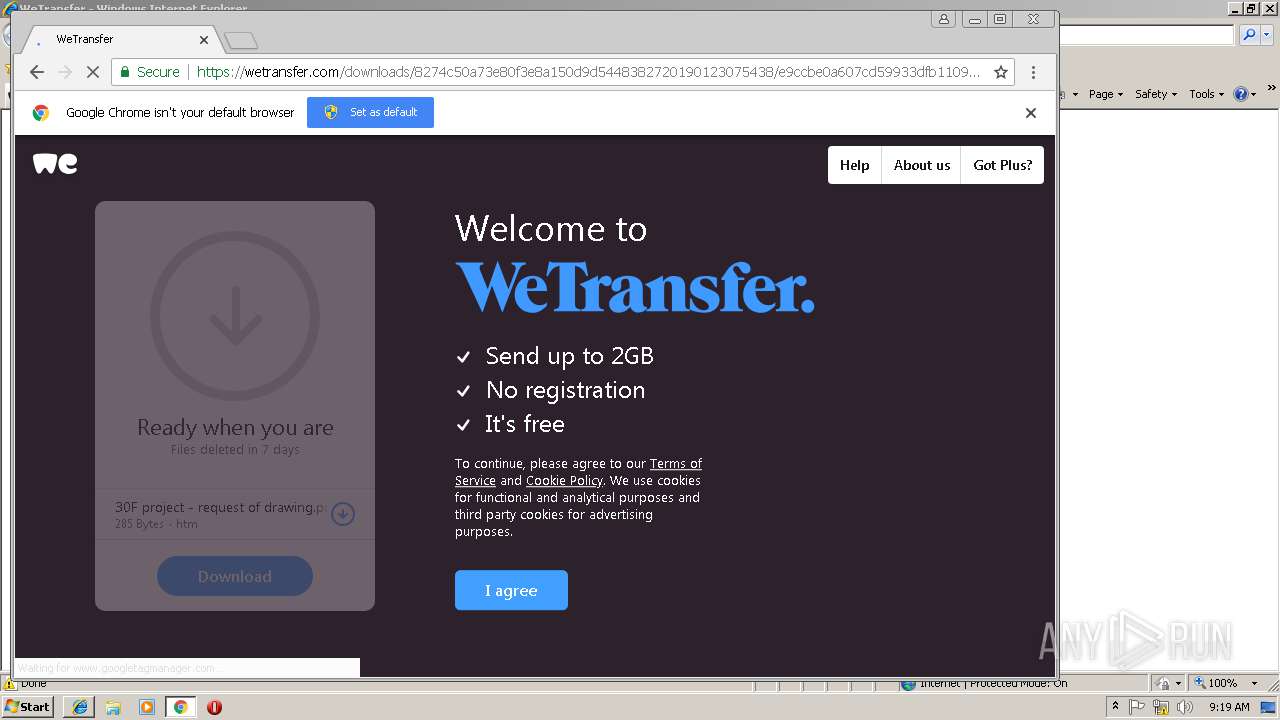
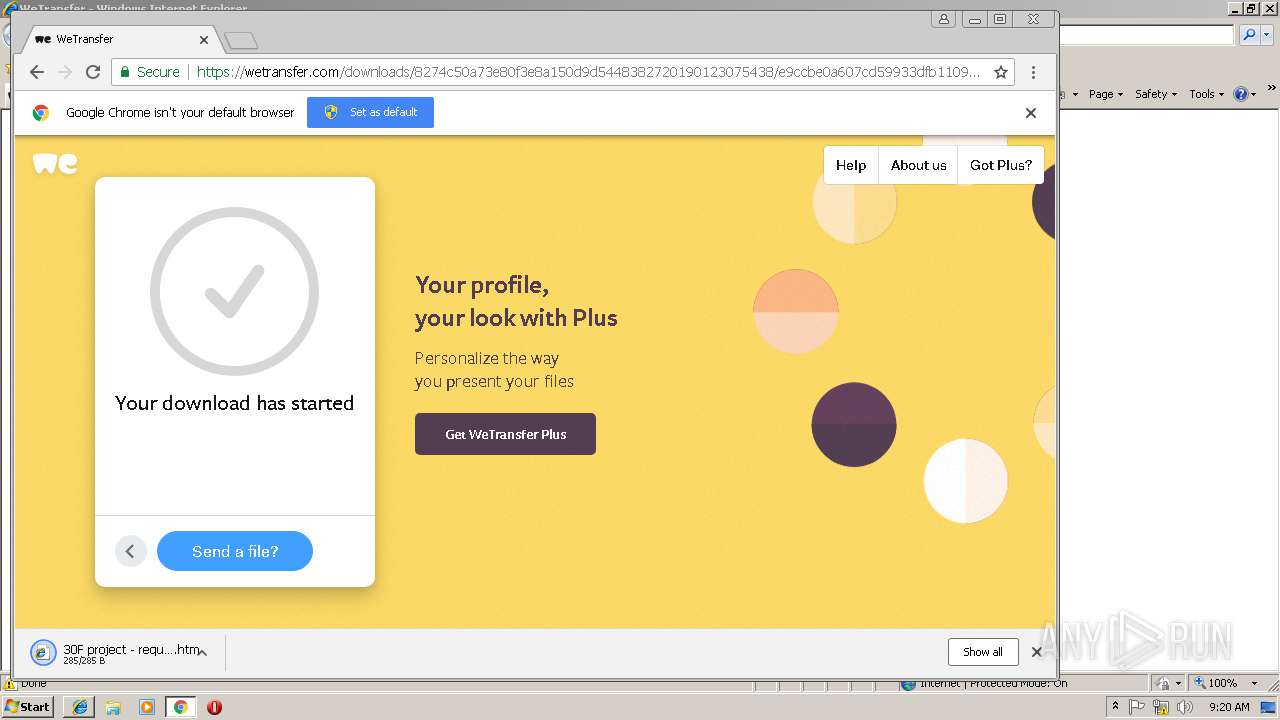
| URL: | https://wetransfer.com/downloads/8274c50a73e80f3e8a150d9d5448382720190123075438/e9ccbe0a607cd59933dfb110994315e220190123075438/1e8474?utm_campaign=WT_email_tracking&utm_content=general&utm_medium=download_button&utm_source=notify_recipient_email |
| Full analysis: | https://app.any.run/tasks/f8d0e510-b803-4c3f-af14-e9502002dc9e |
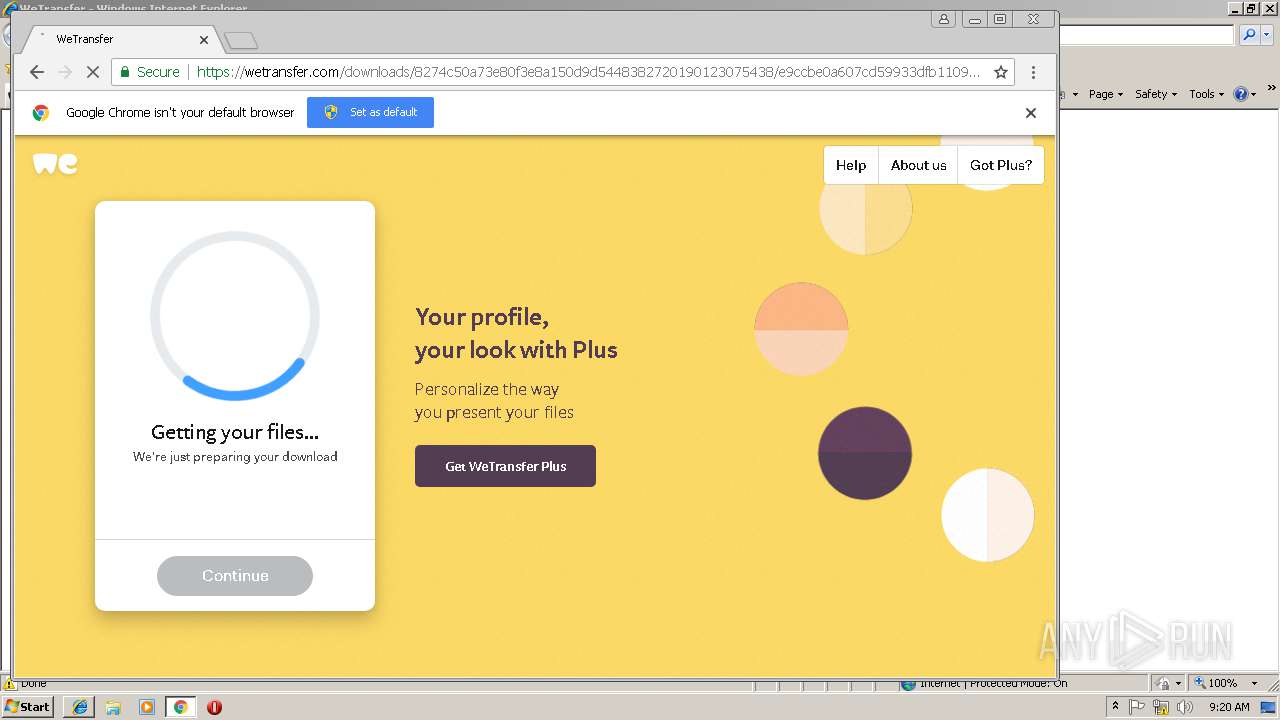
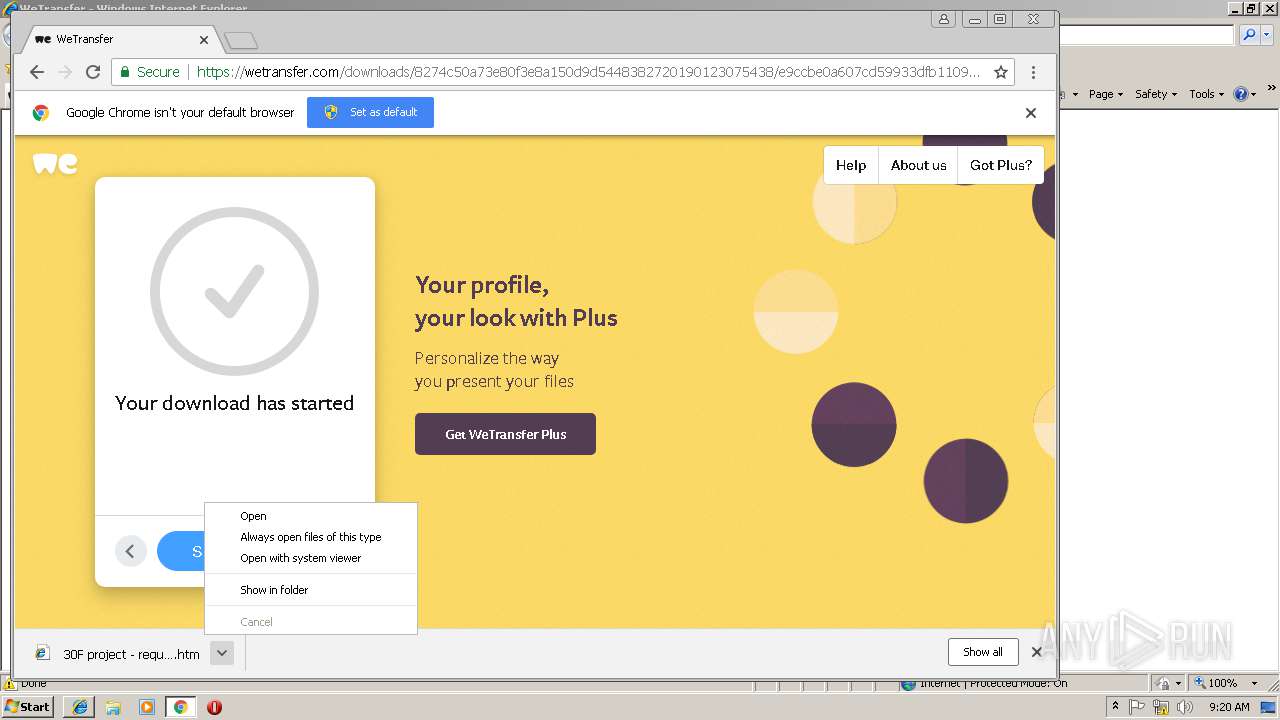
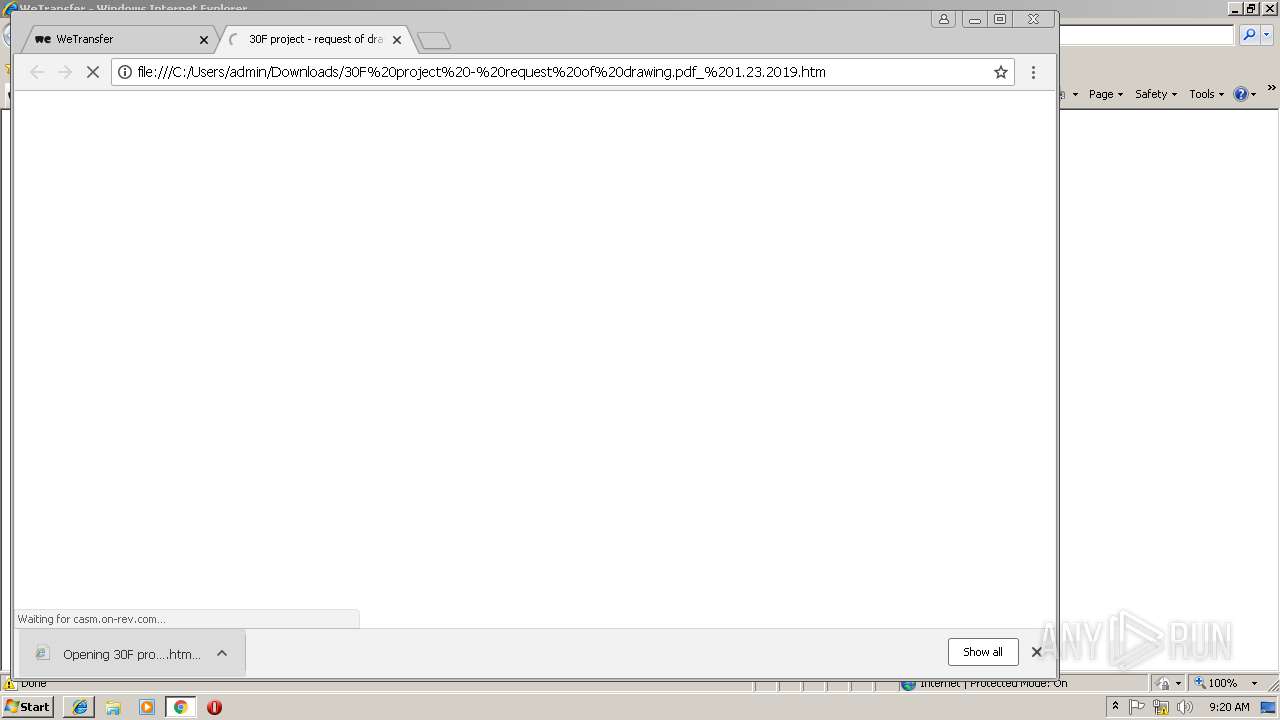
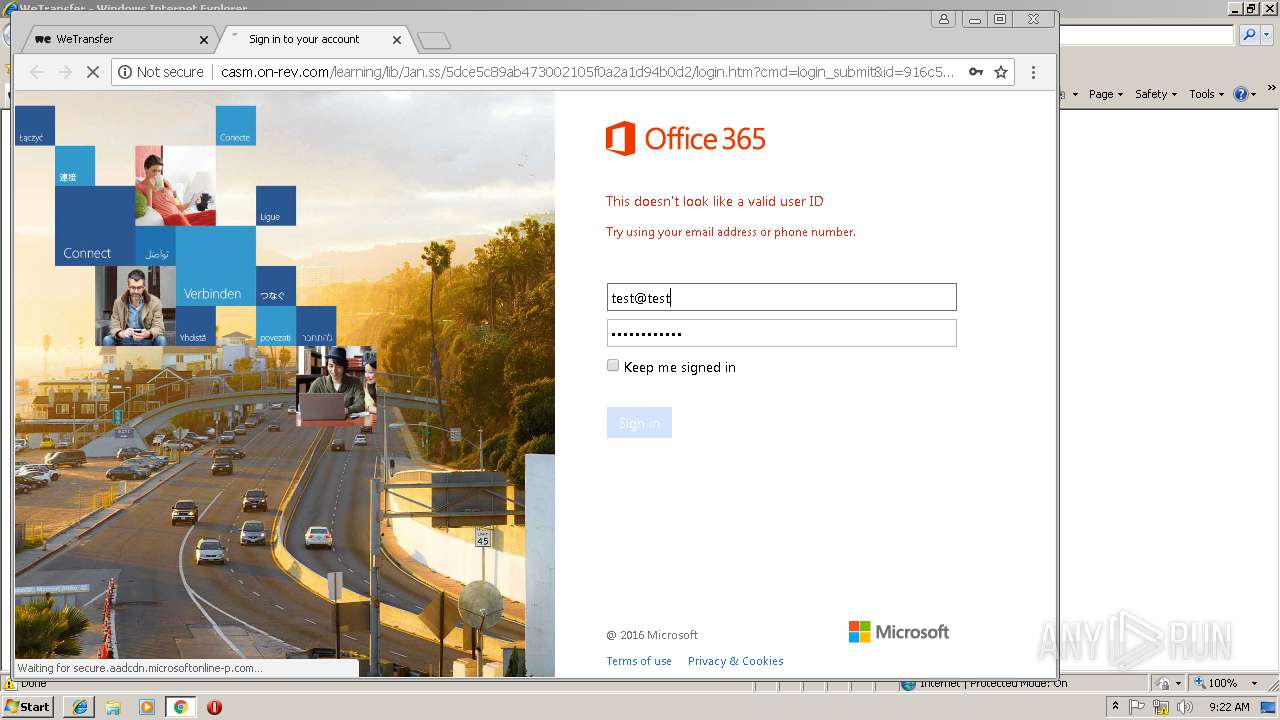
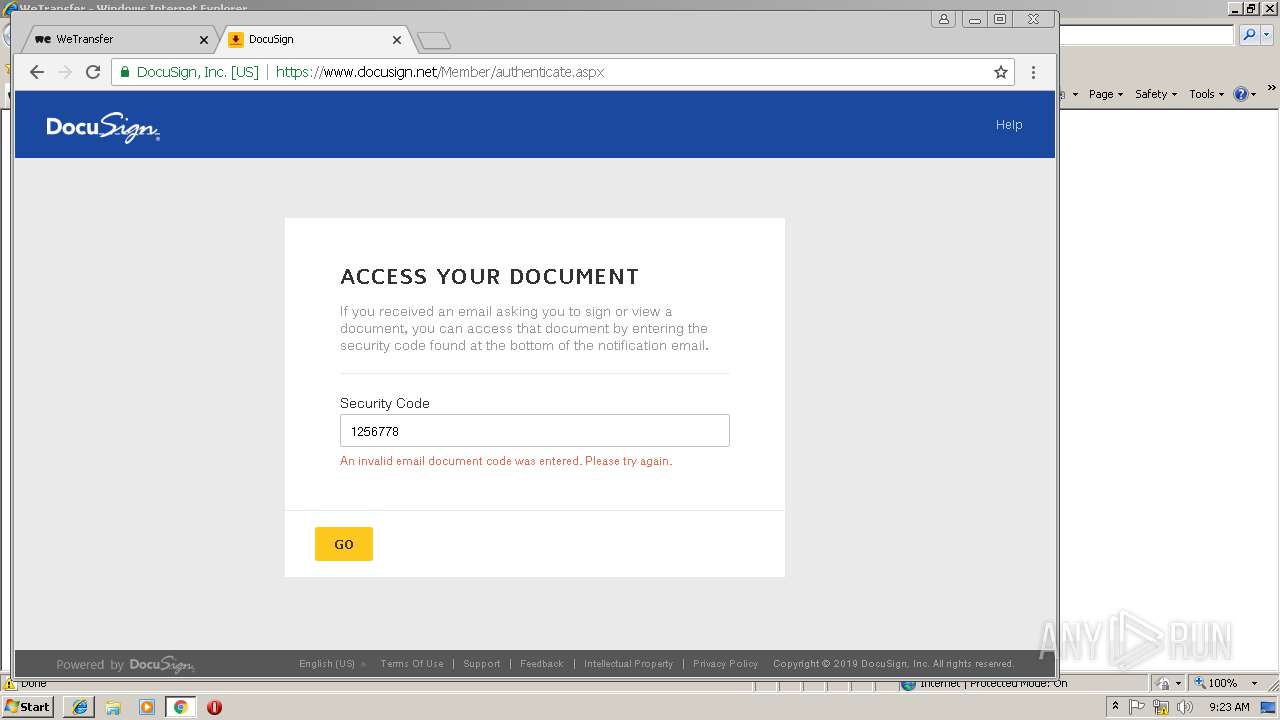
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2019, 09:17:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F8408D7B6011EDD5C9091BC5A8E9C3C3 |
| SHA1: | 727D93D1DBCDD17A4AC880F8ABD05BE96E2ECC1E |
| SHA256: | E3FC384939B64D90514547FB7865B9FE4FB252E42A400878298313B26A32D8B3 |
| SSDEEP: | 6:2EYNaRuAoe+/YQtdh8oE/SmEtl0xEZLX2uH1SEq4CWVXMVITn:2EYNsuADstduoVm7CF2GAEq4SITn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
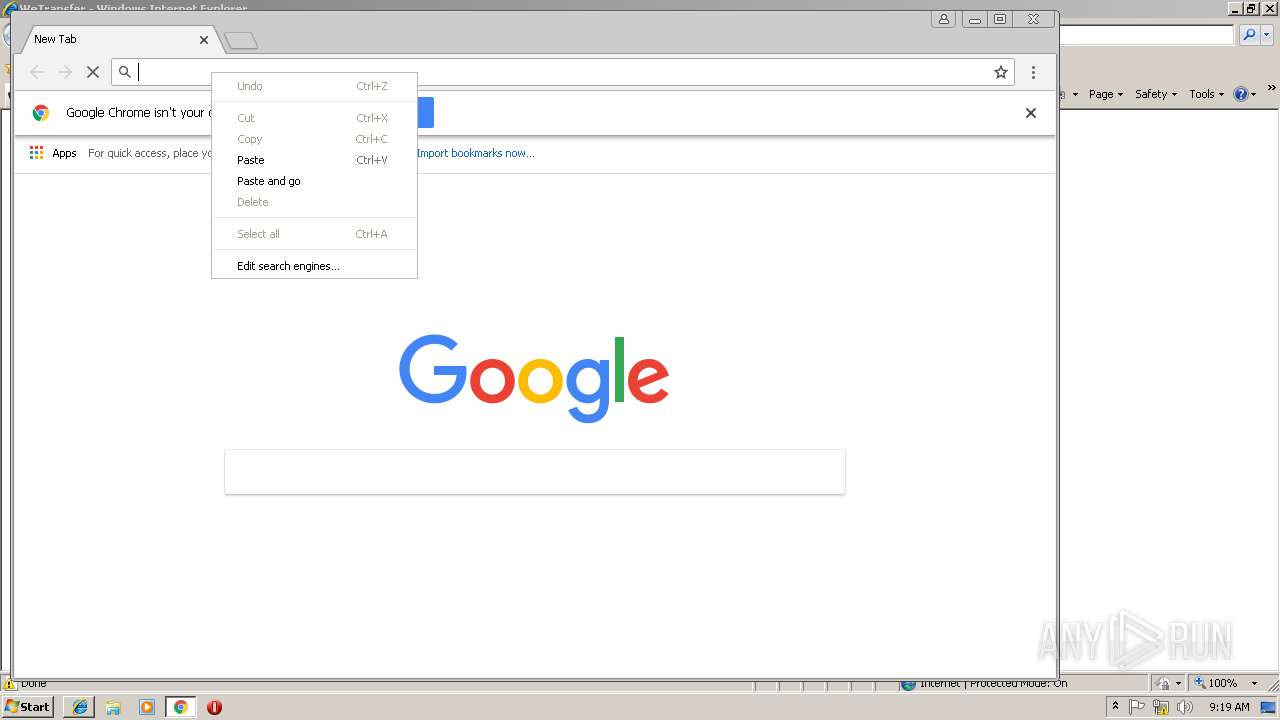
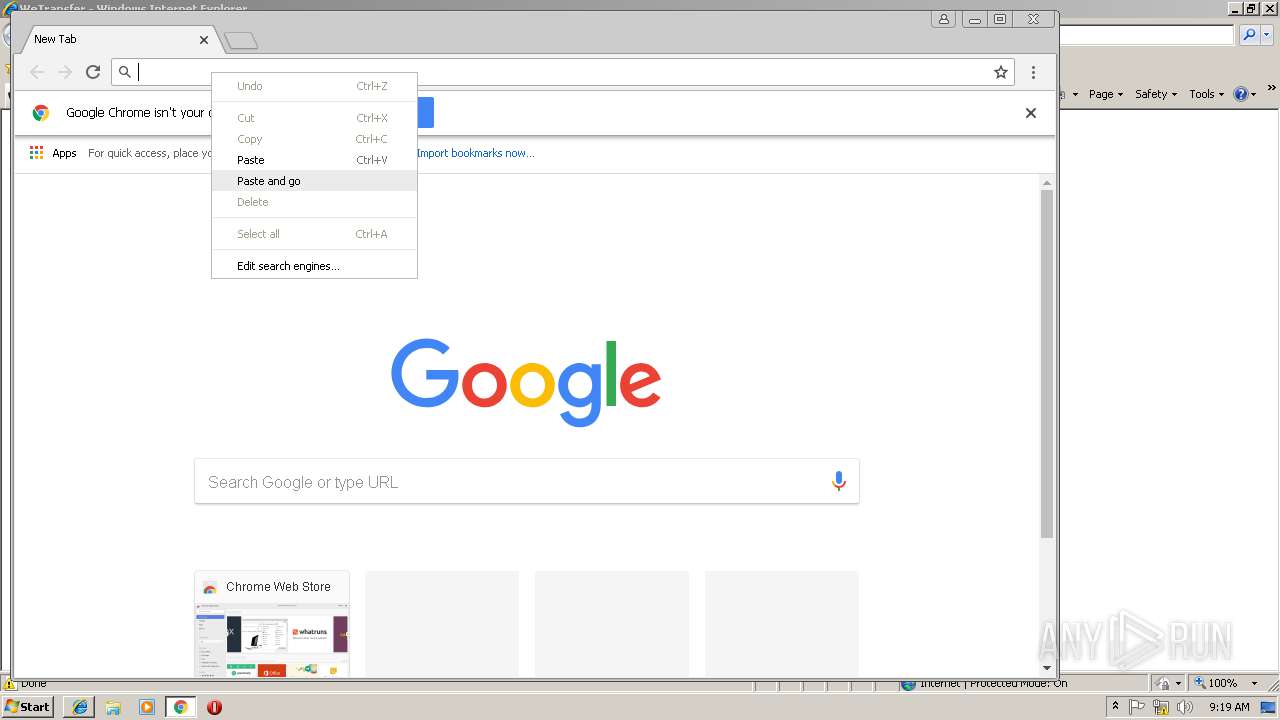
Application launched itself
- iexplore.exe (PID: 2952)
- chrome.exe (PID: 2440)
Changes internet zones settings
- iexplore.exe (PID: 2952)
Reads internet explorer settings
- iexplore.exe (PID: 3216)
Changes settings of System certificates
- iexplore.exe (PID: 2952)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2952)
Reads Internet Cache Settings
- iexplore.exe (PID: 3216)
- chrome.exe (PID: 2440)
Reads settings of System Certificates
- iexplore.exe (PID: 2952)
Reads Microsoft Office registry keys
- chrome.exe (PID: 2440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,16461188365549878769,10264223950986526040,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6DAEC106E106B2FEC046059517D2EB3B --mojo-platform-channel-handle=1124 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2444 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,16461188365549878769,10264223950986526040,131072 --enable-features=PasswordImport --service-pipe-token=2FD733B6BF924A28CB9A3BAC89CFF2CF --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2FD733B6BF924A28CB9A3BAC89CFF2CF --renderer-client-id=3 --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,16461188365549878769,10264223950986526040,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C9A0AD6F4E44C2539E305BEC0F89C54D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C9A0AD6F4E44C2539E305BEC0F89C54D --renderer-client-id=11 --mojo-platform-channel-handle=2176 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2952 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3216 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2952 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6e8b00b0,0x6e8b00c0,0x6e8b00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,16461188365549878769,10264223950986526040,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=C726BEAF43F5CFD0E1FC671A0E83BCCA --mojo-platform-channel-handle=3876 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,16461188365549878769,10264223950986526040,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=DAB99FD33408E8CC5383C68994DEF7D9 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=DAB99FD33408E8CC5383C68994DEF7D9 --renderer-client-id=7 --mojo-platform-channel-handle=3748 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
947
Read events
824
Write events
117
Delete events
6
Modification events
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {D5C4C3D3-1EEF-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307010003001700090012001900AF03 | |||
Executable files
0
Suspicious files
77
Text files
124
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar967A.tmp | — | |
MD5:— | SHA256:— | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab969B.tmp | — | |
MD5:— | SHA256:— | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar969C.tmp | — | |
MD5:— | SHA256:— | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9777.tmp | — | |
MD5:— | SHA256:— | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9778.tmp | — | |
MD5:— | SHA256:— | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\1e8474[1].txt | — | |
MD5:— | SHA256:— | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
| 3216 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\070E0202839D9D67350CD2613E78E416 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
90
DNS requests
52
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
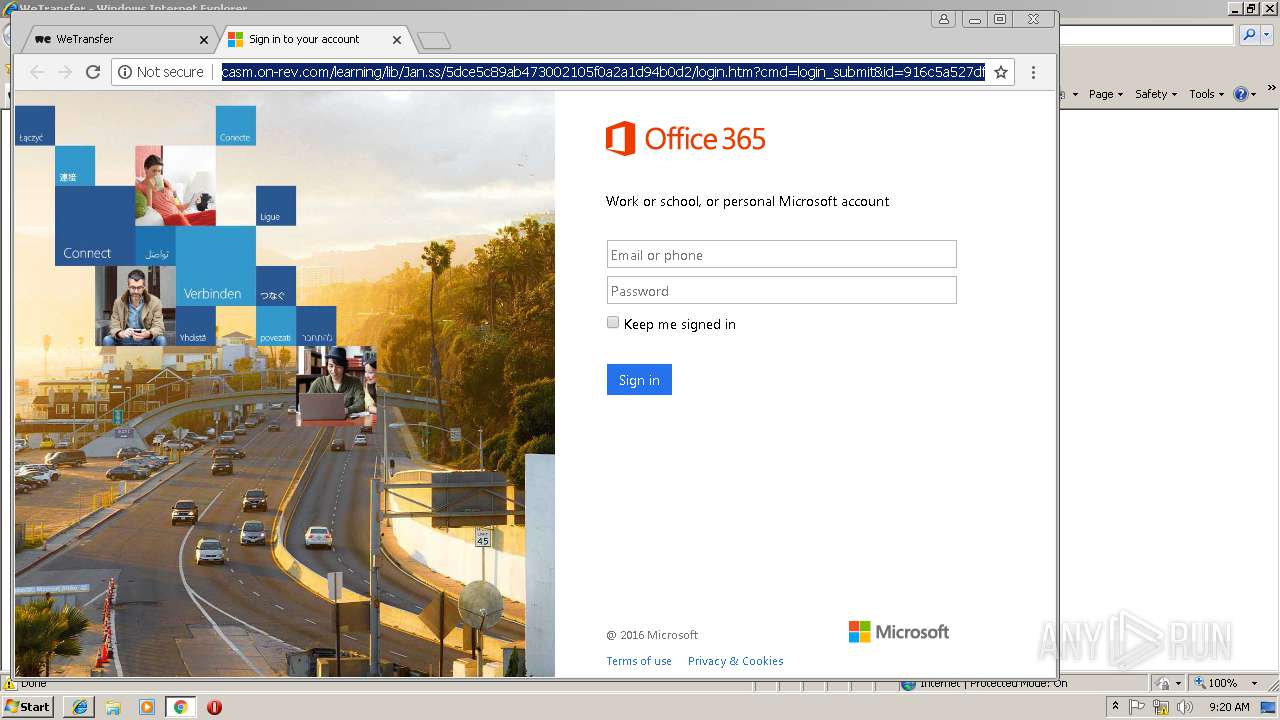
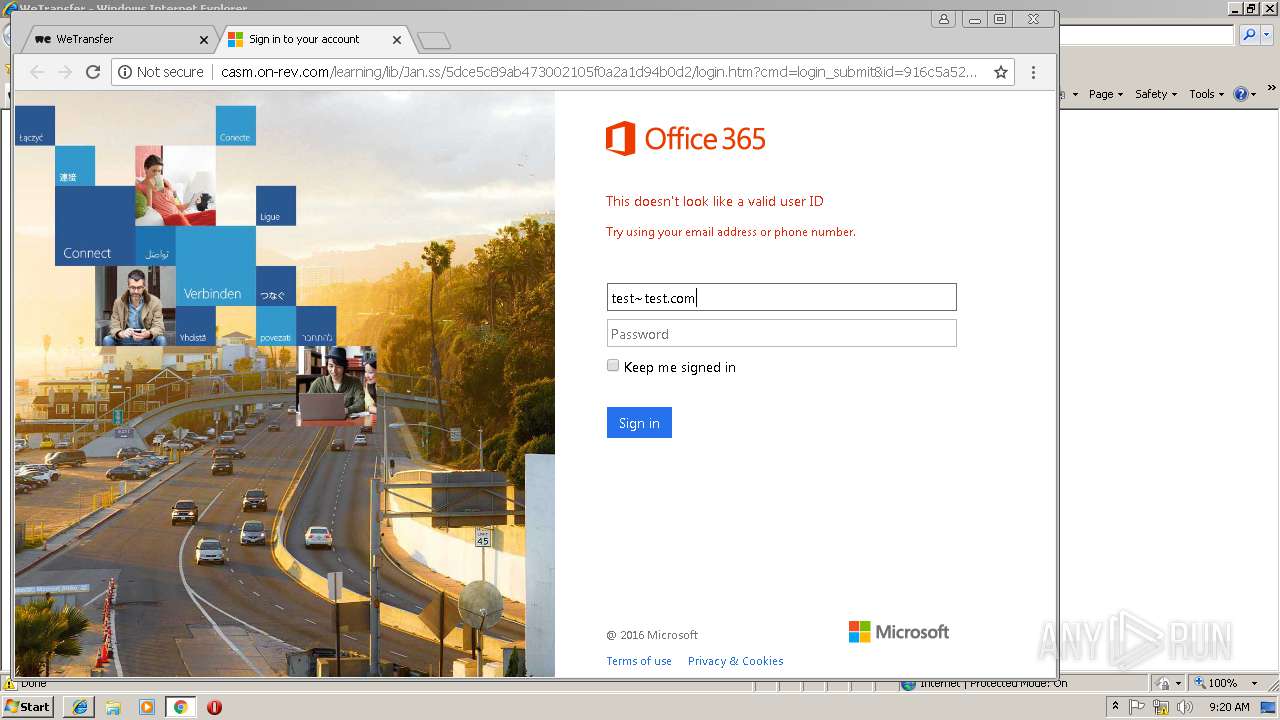
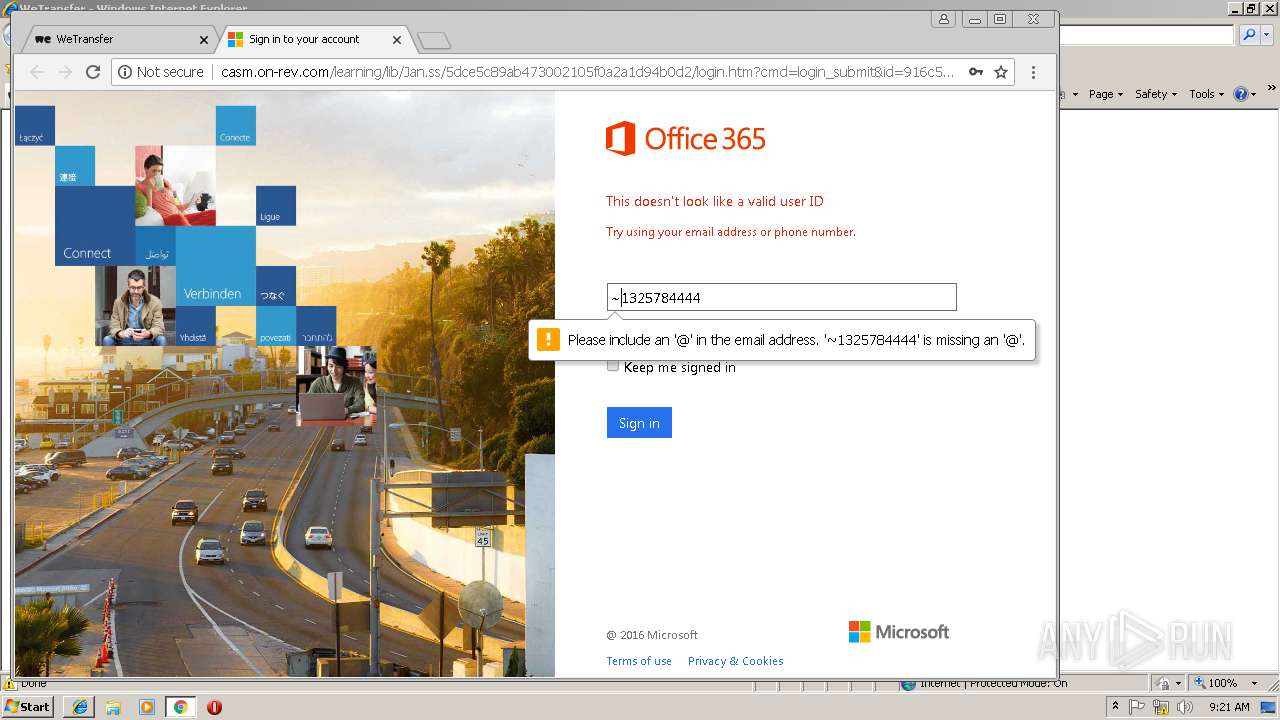
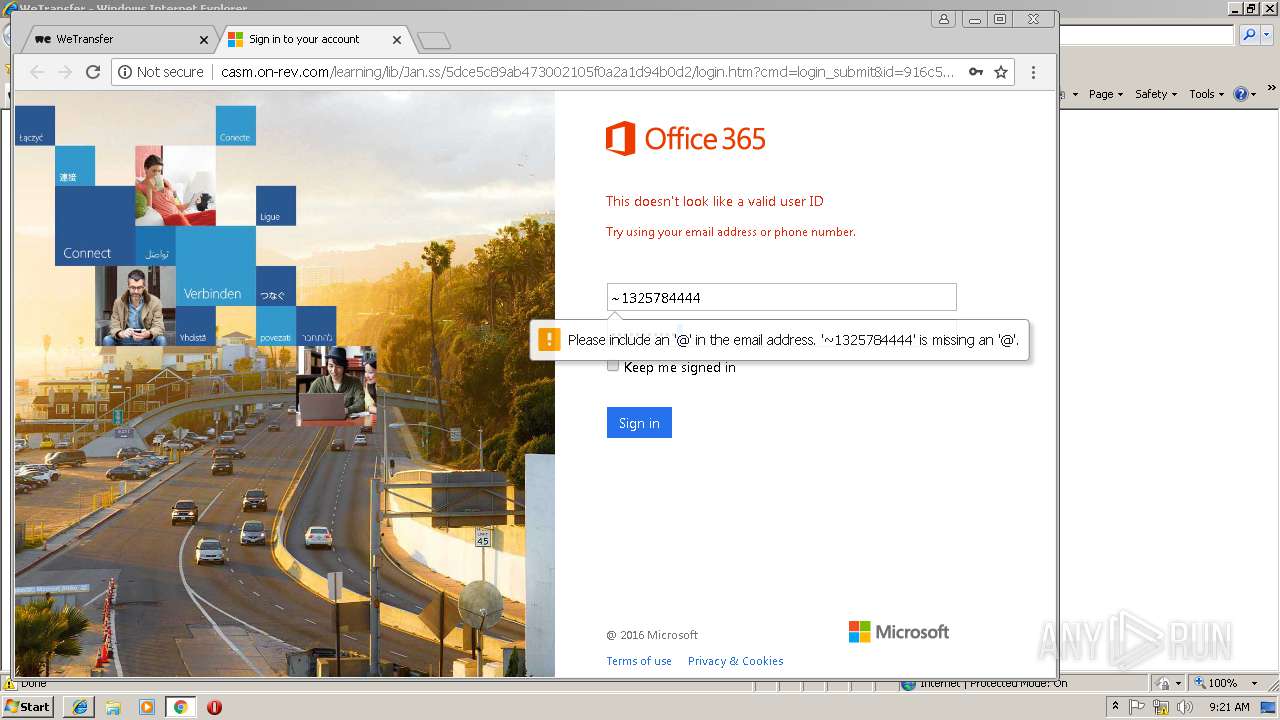
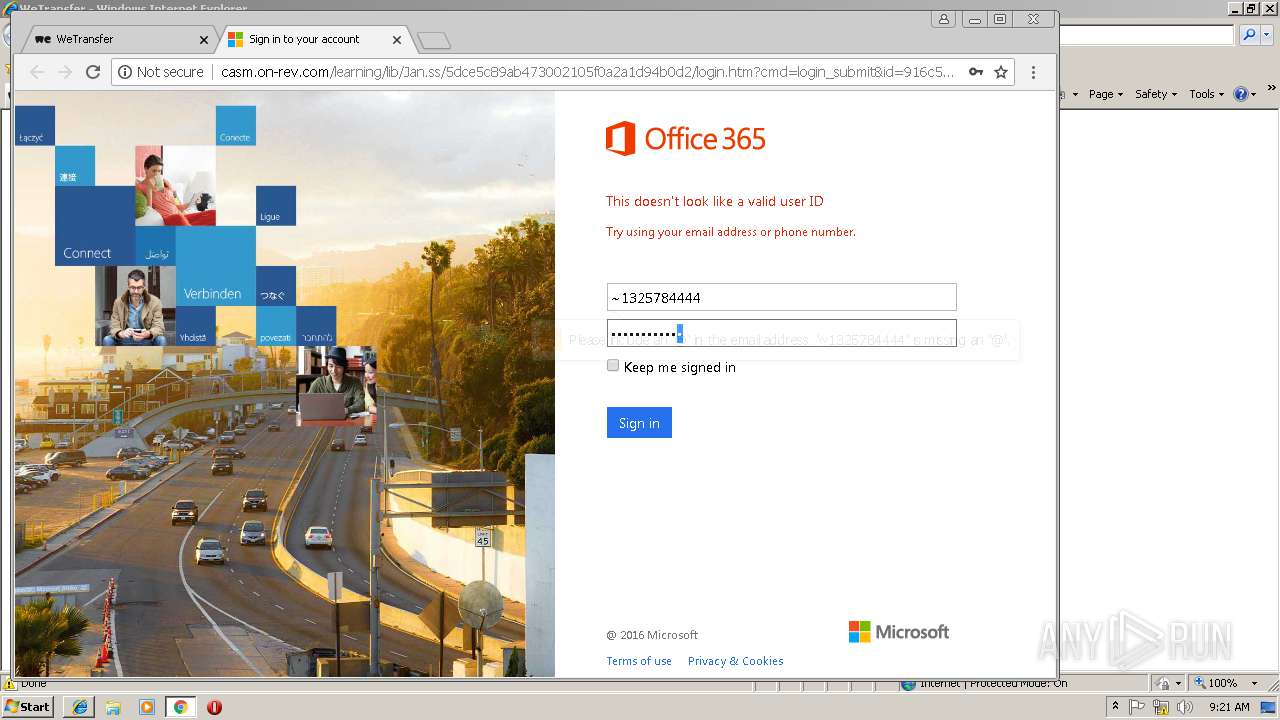
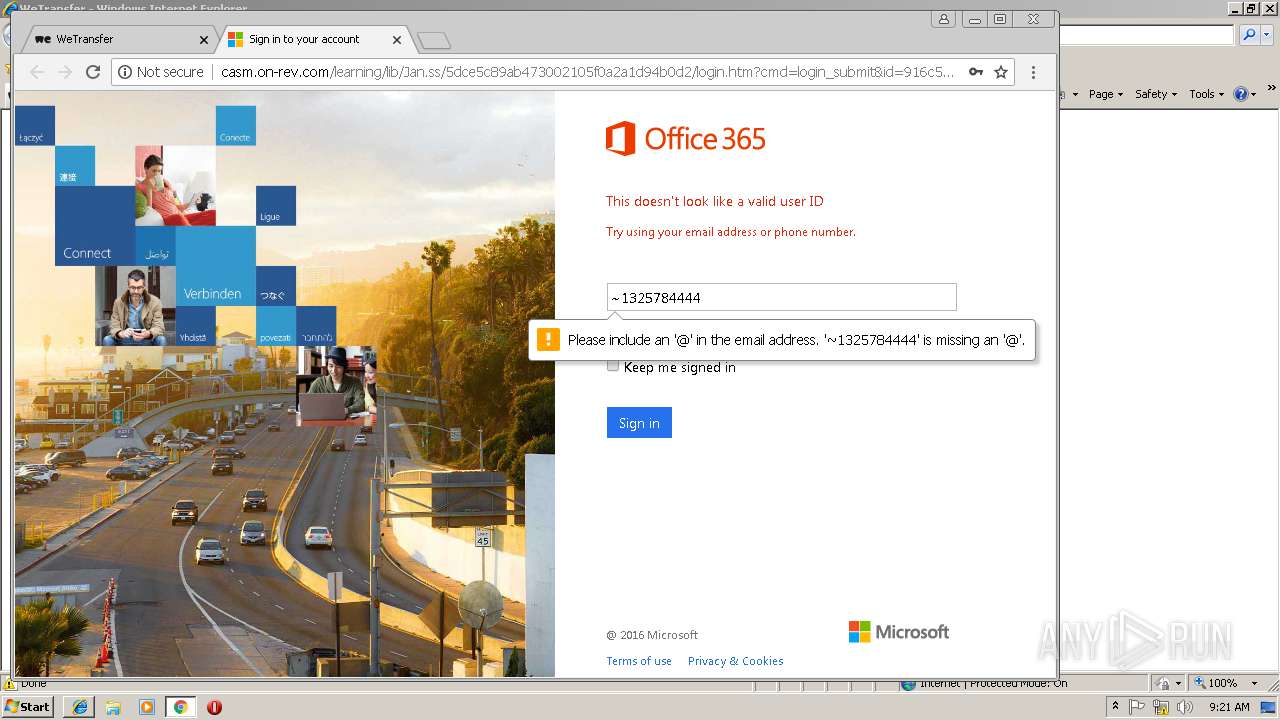
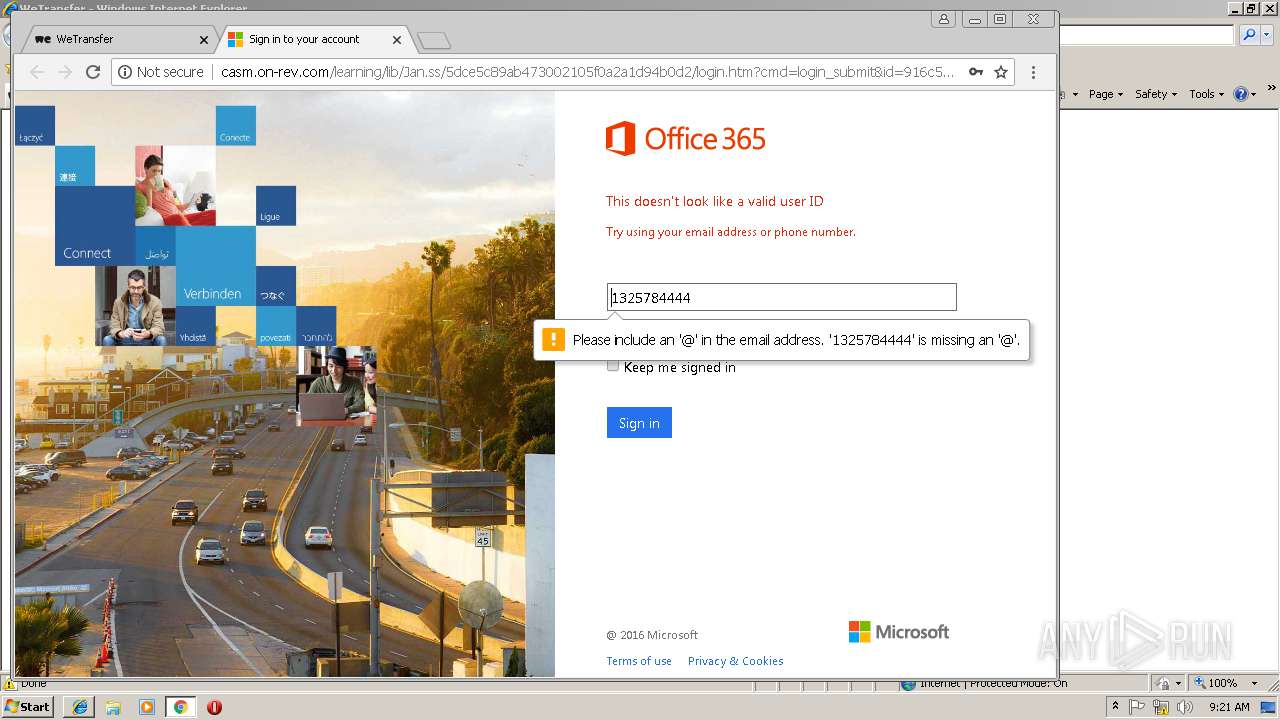
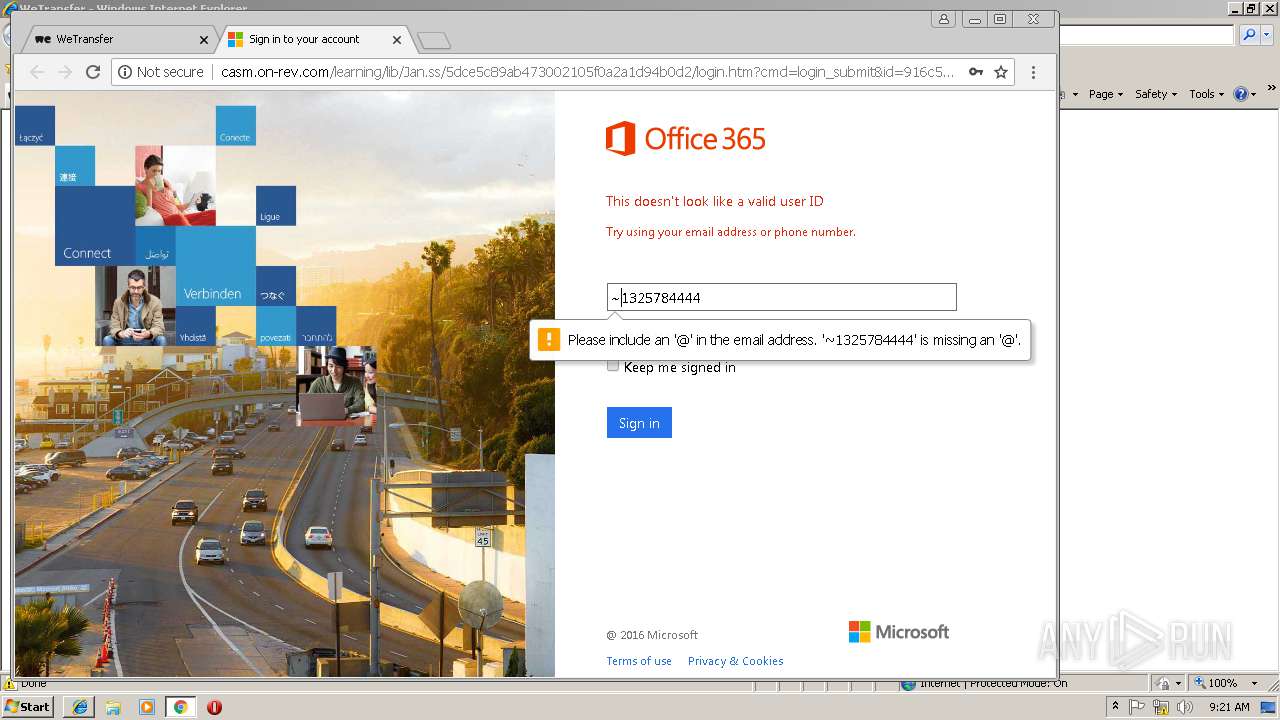
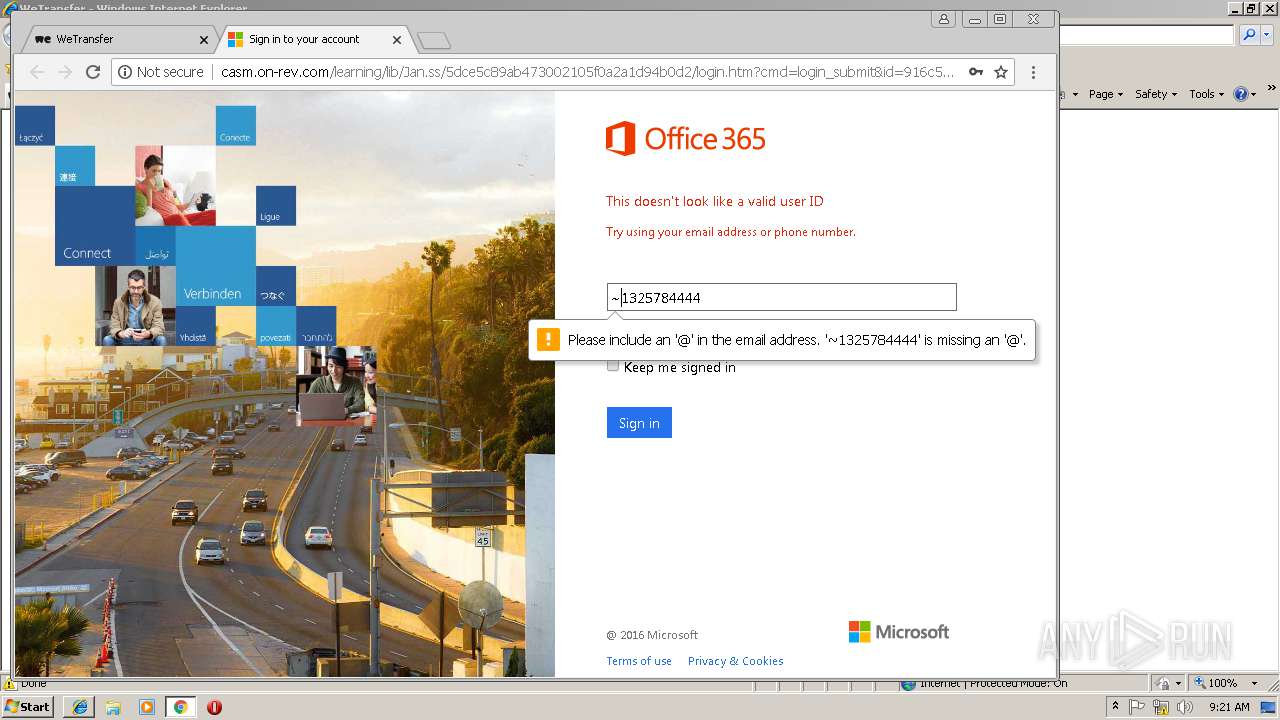
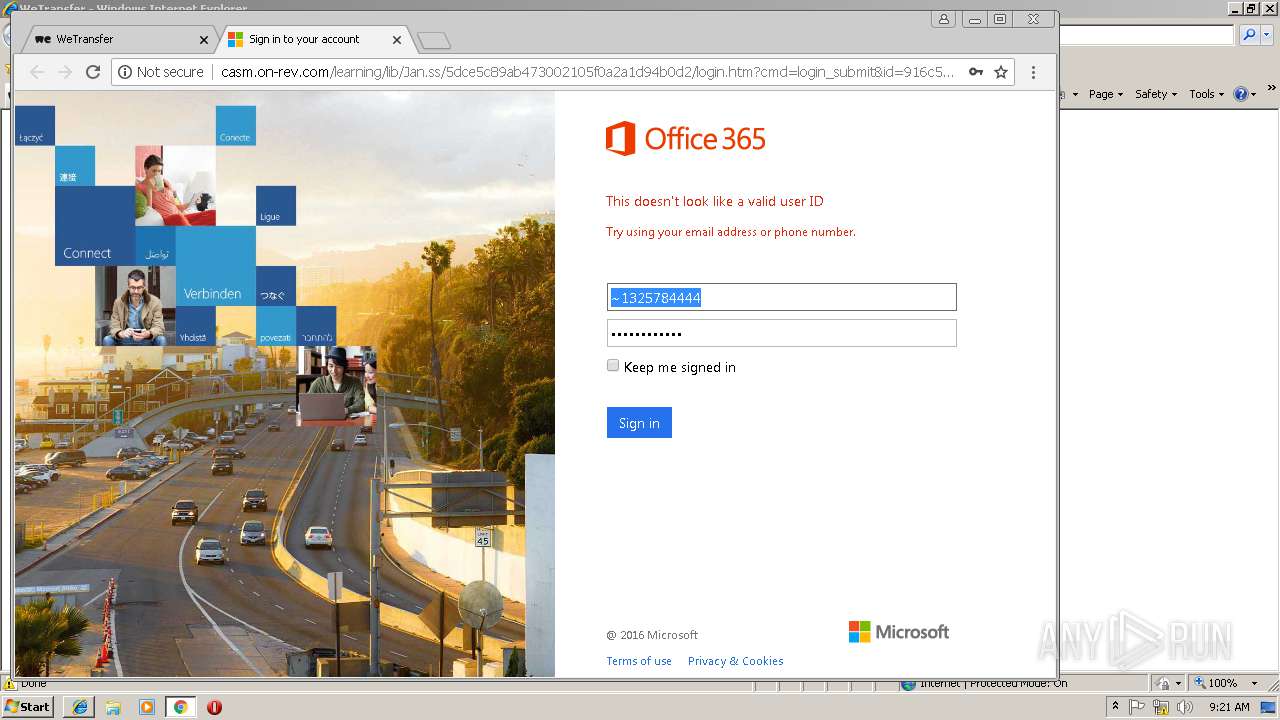
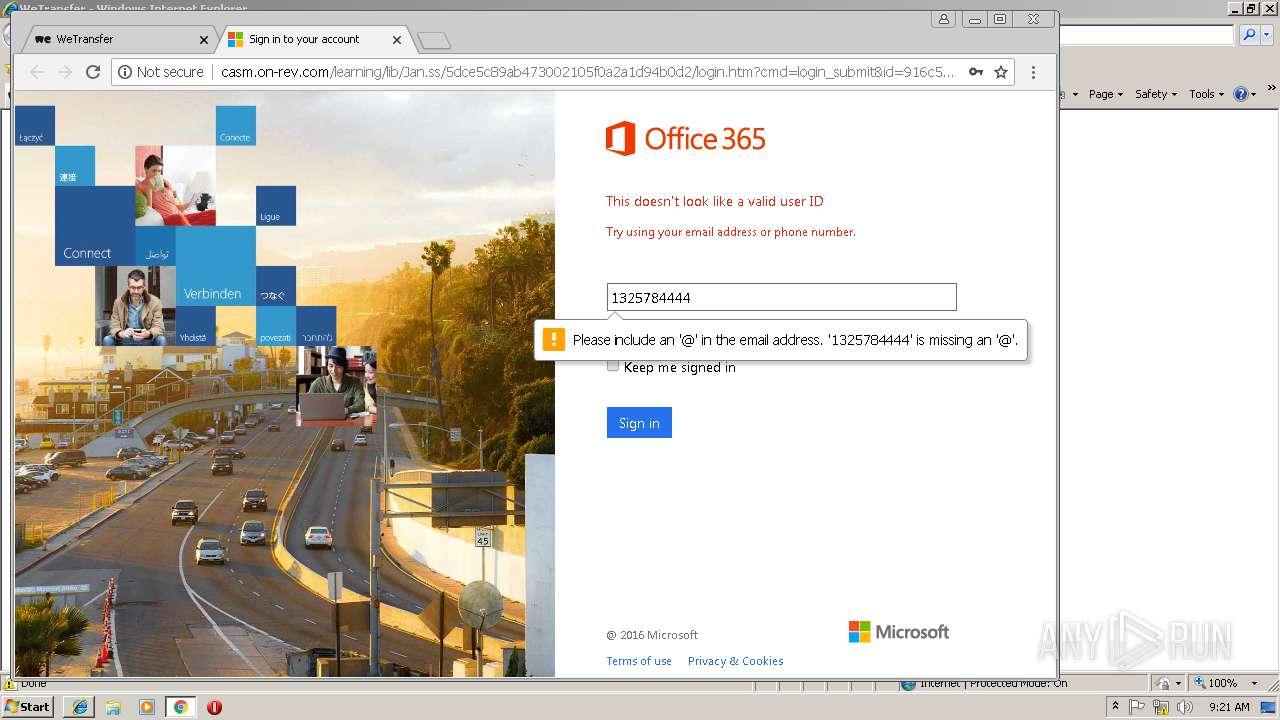
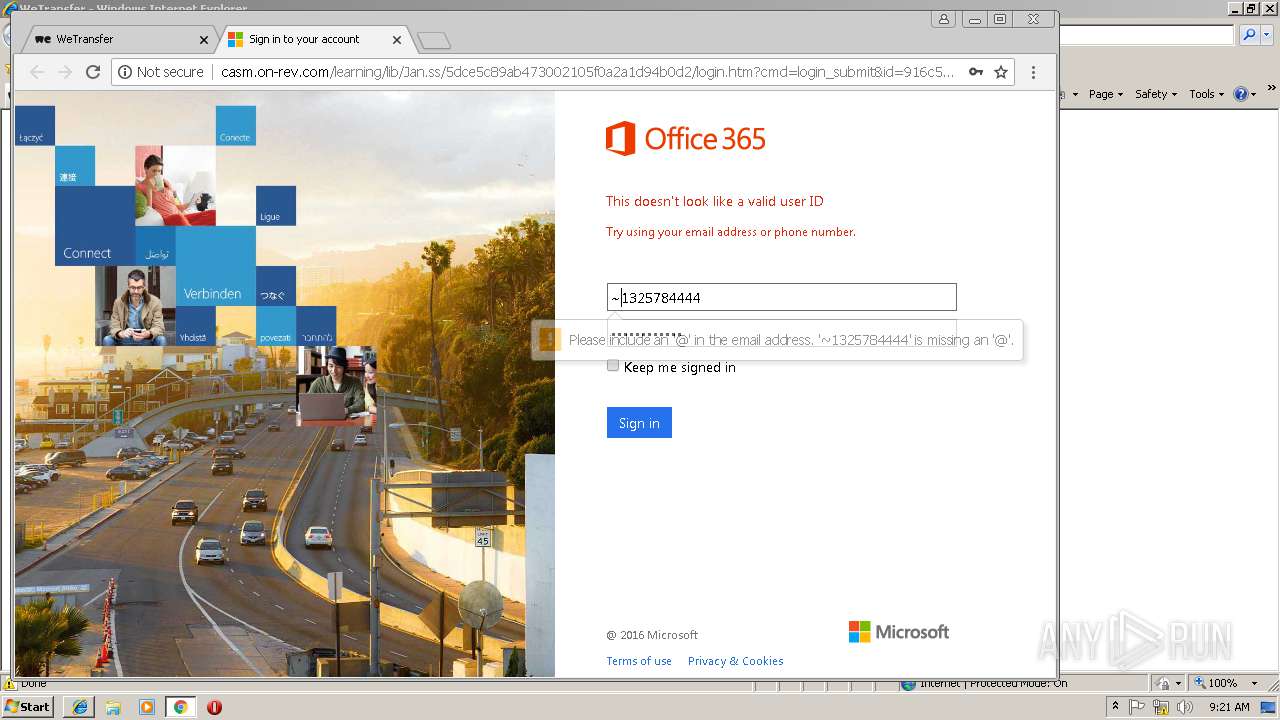
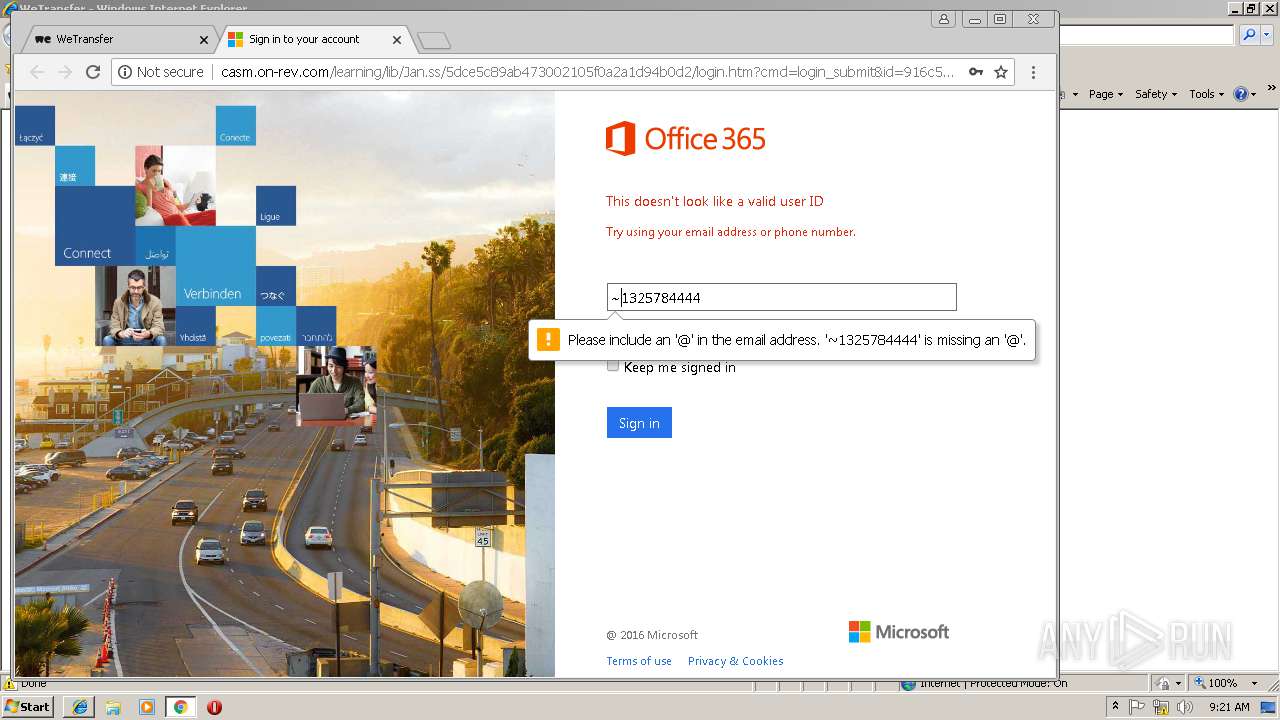
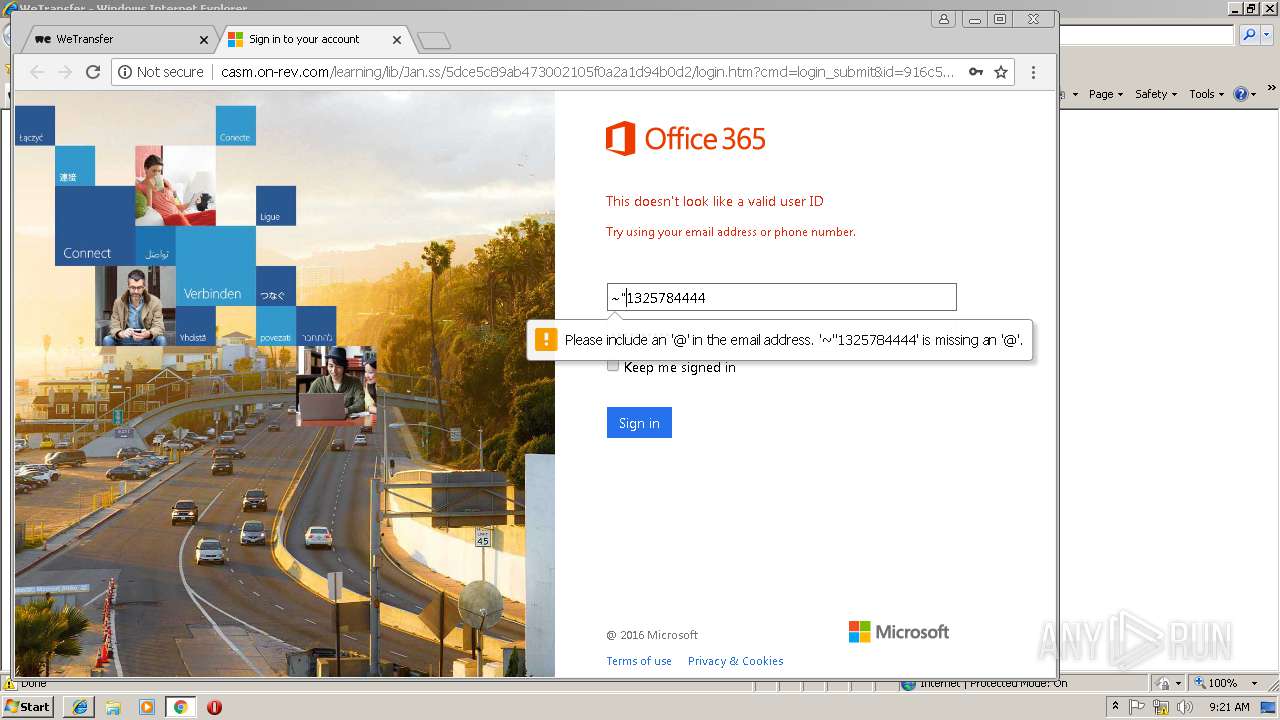
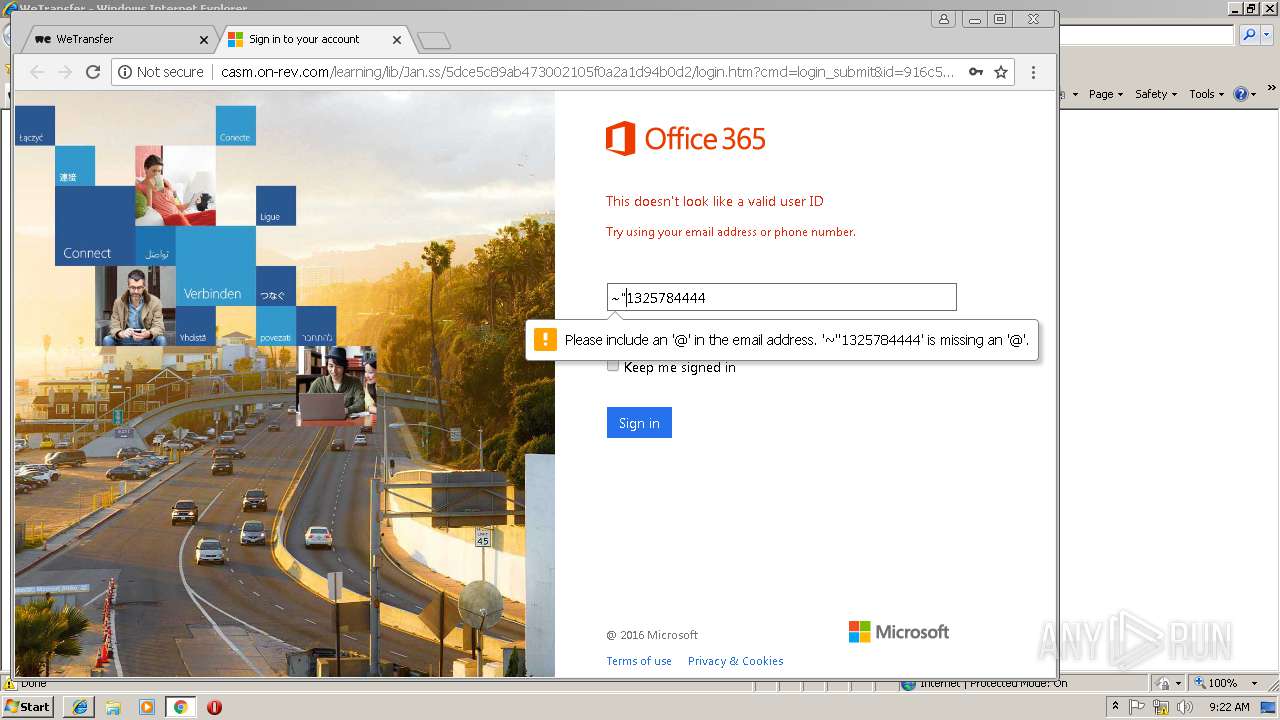
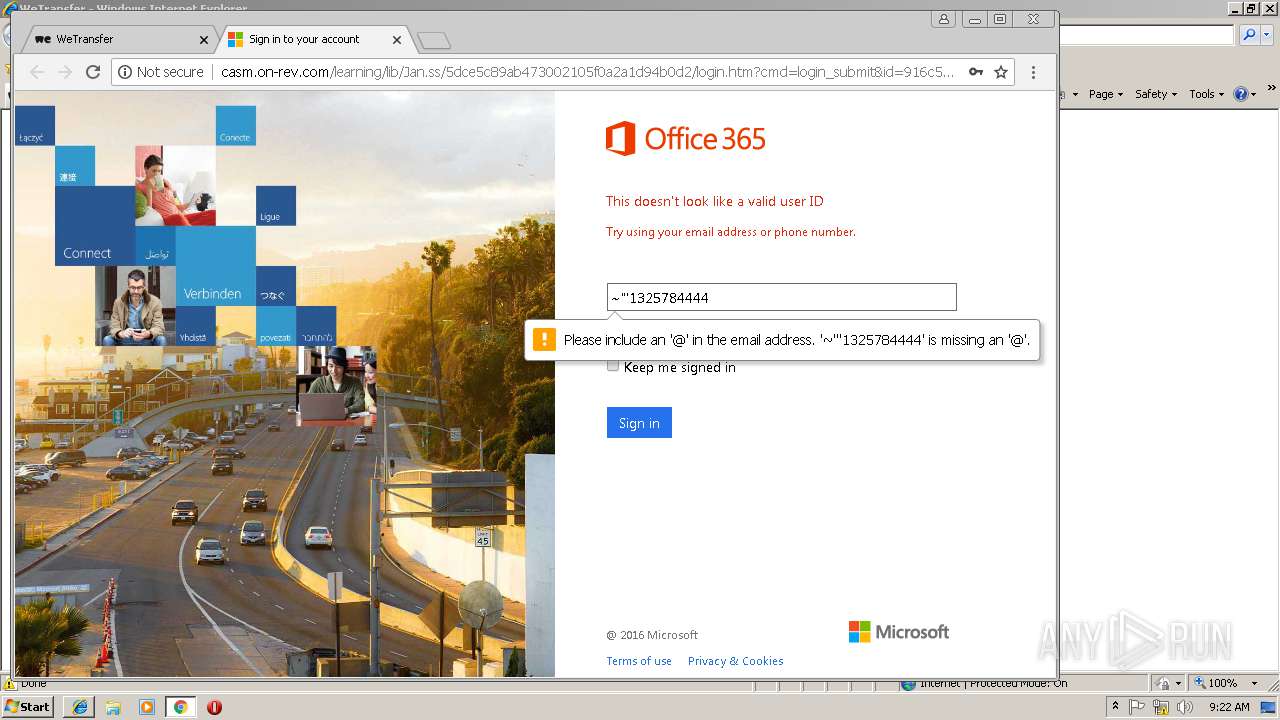
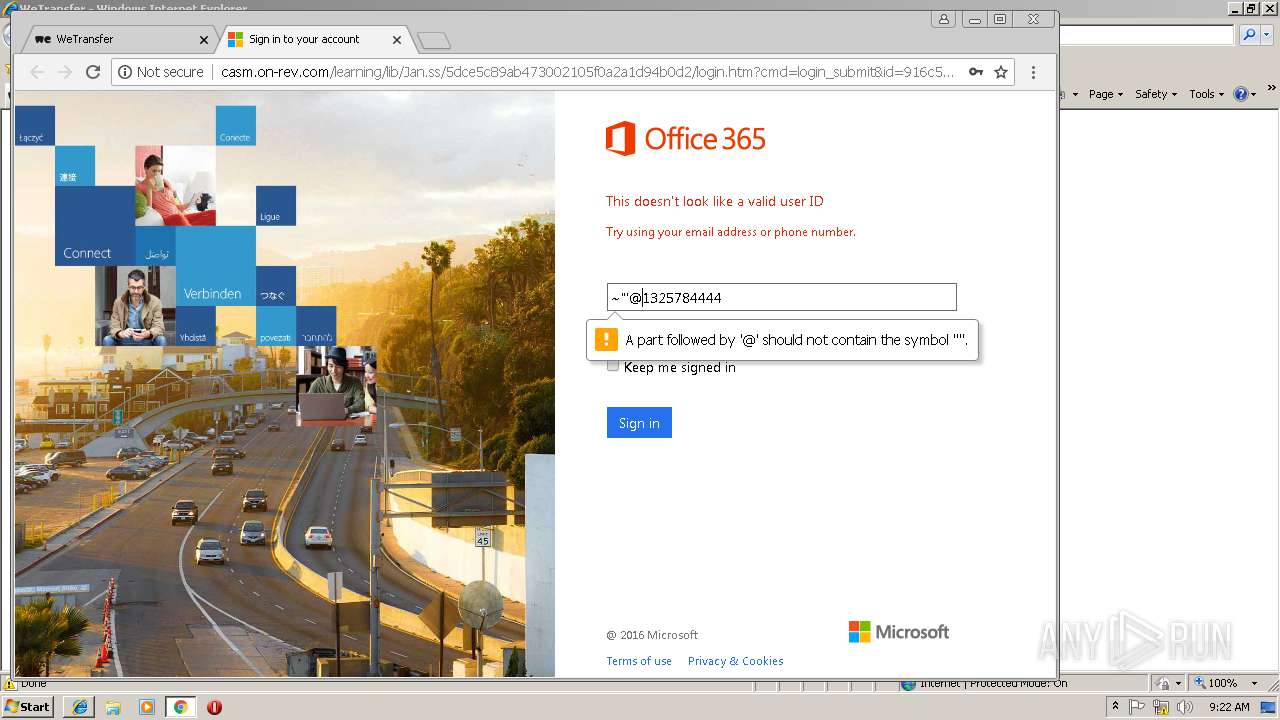
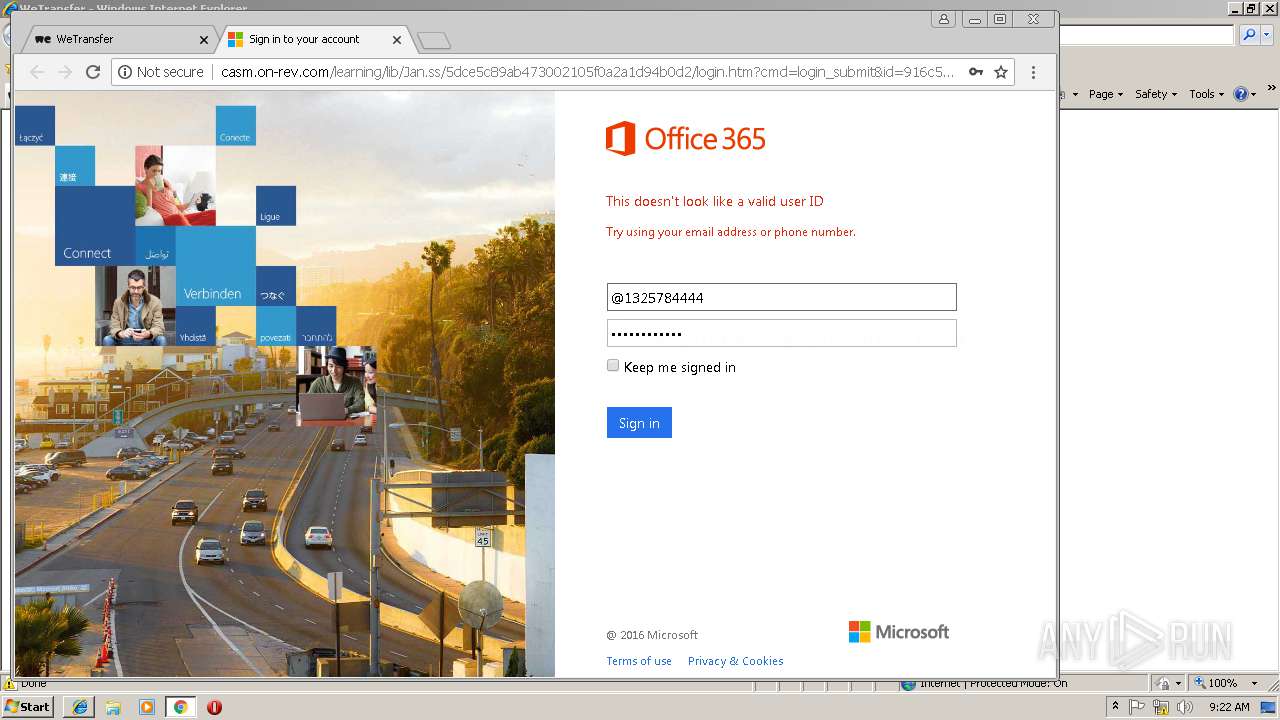
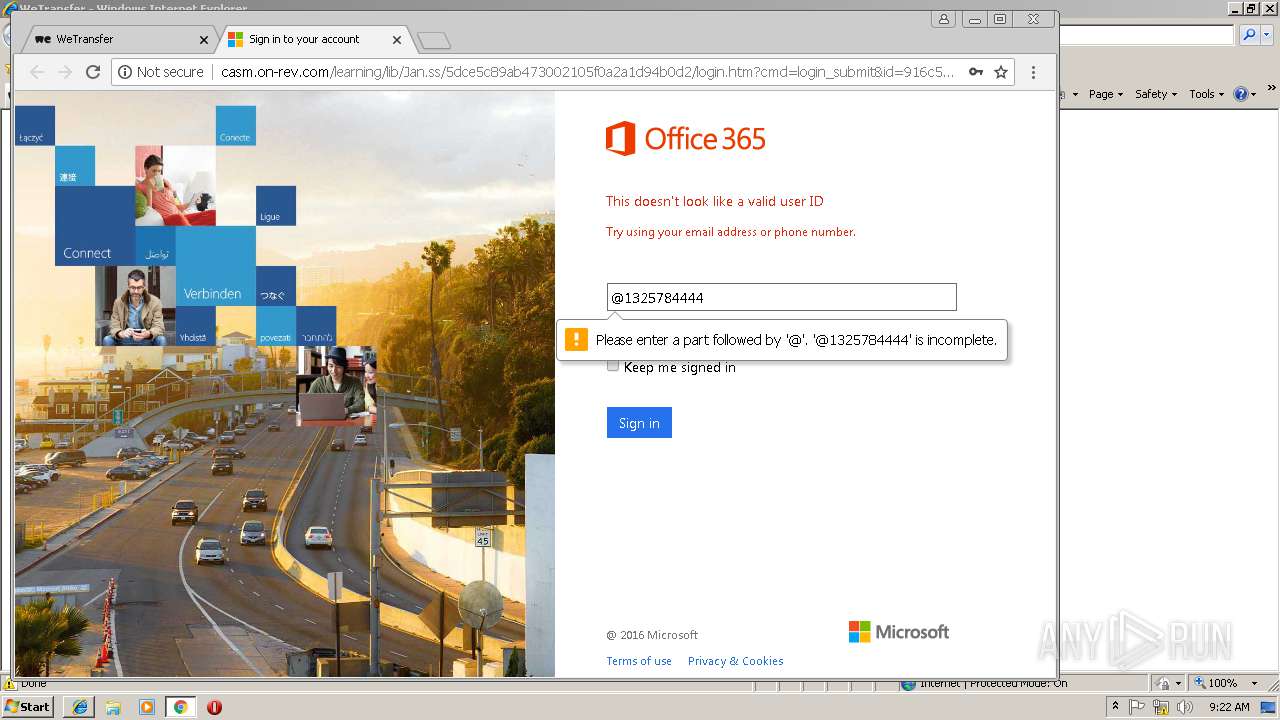
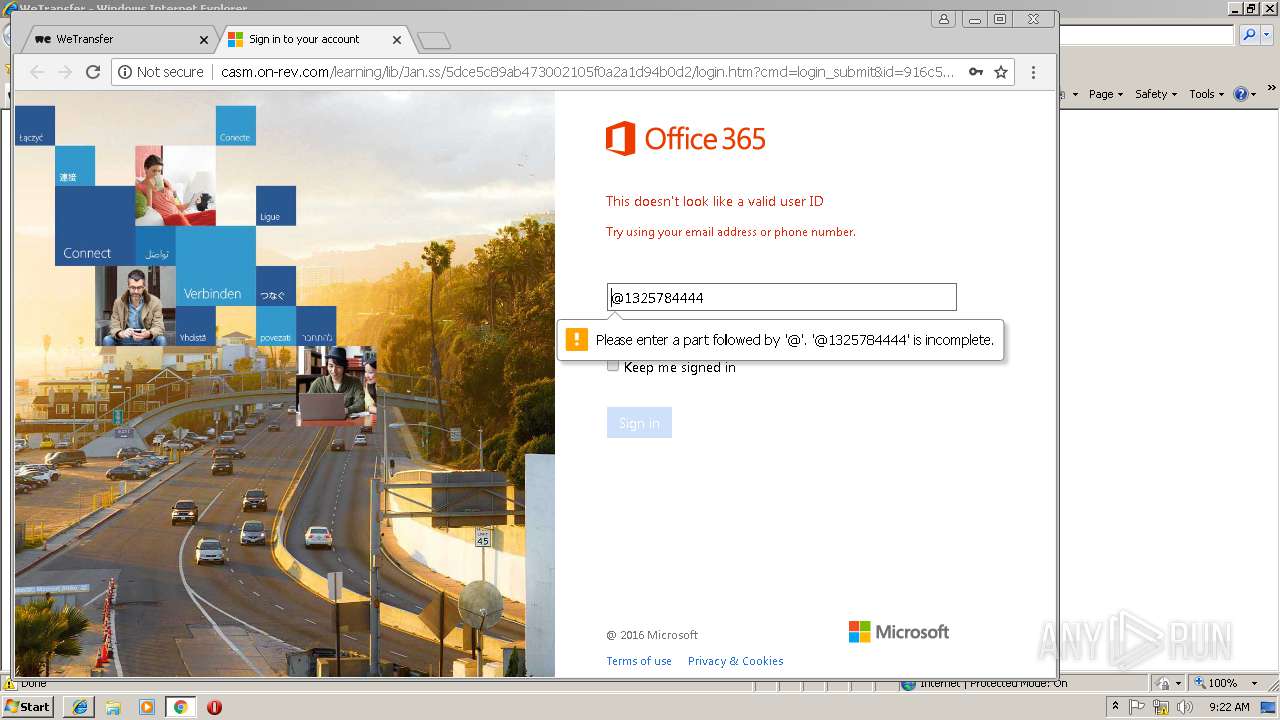
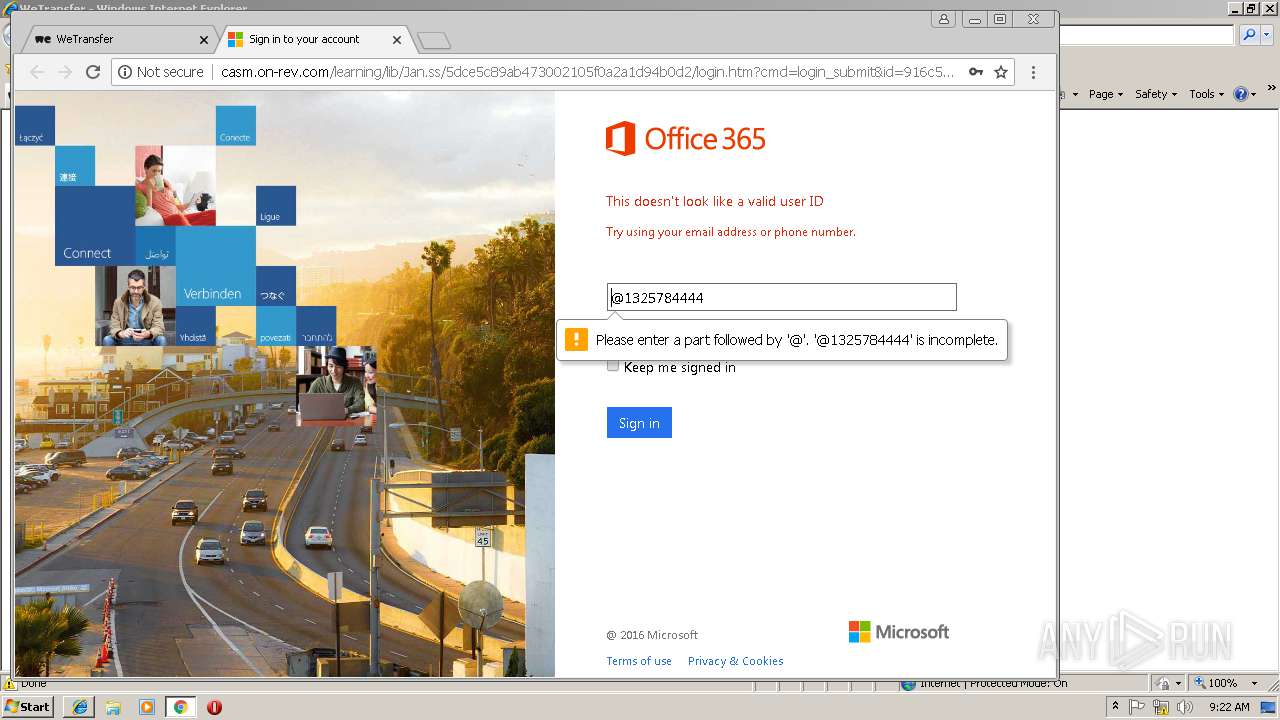
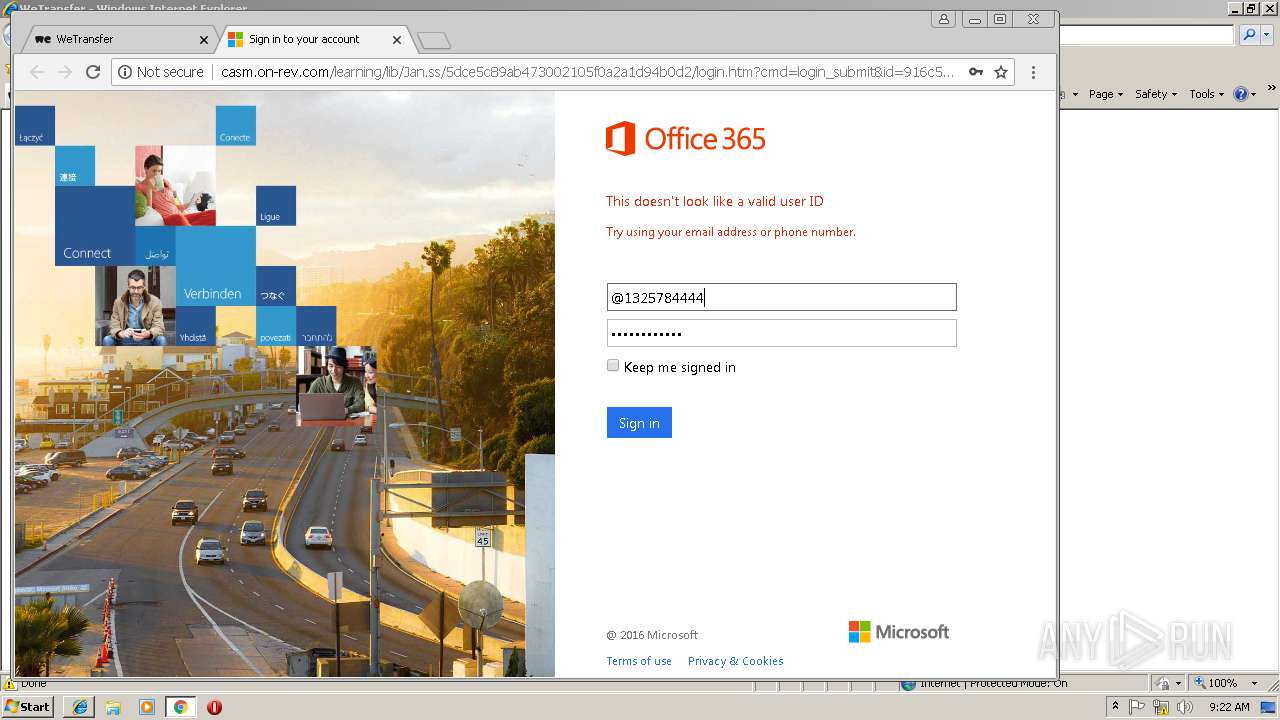
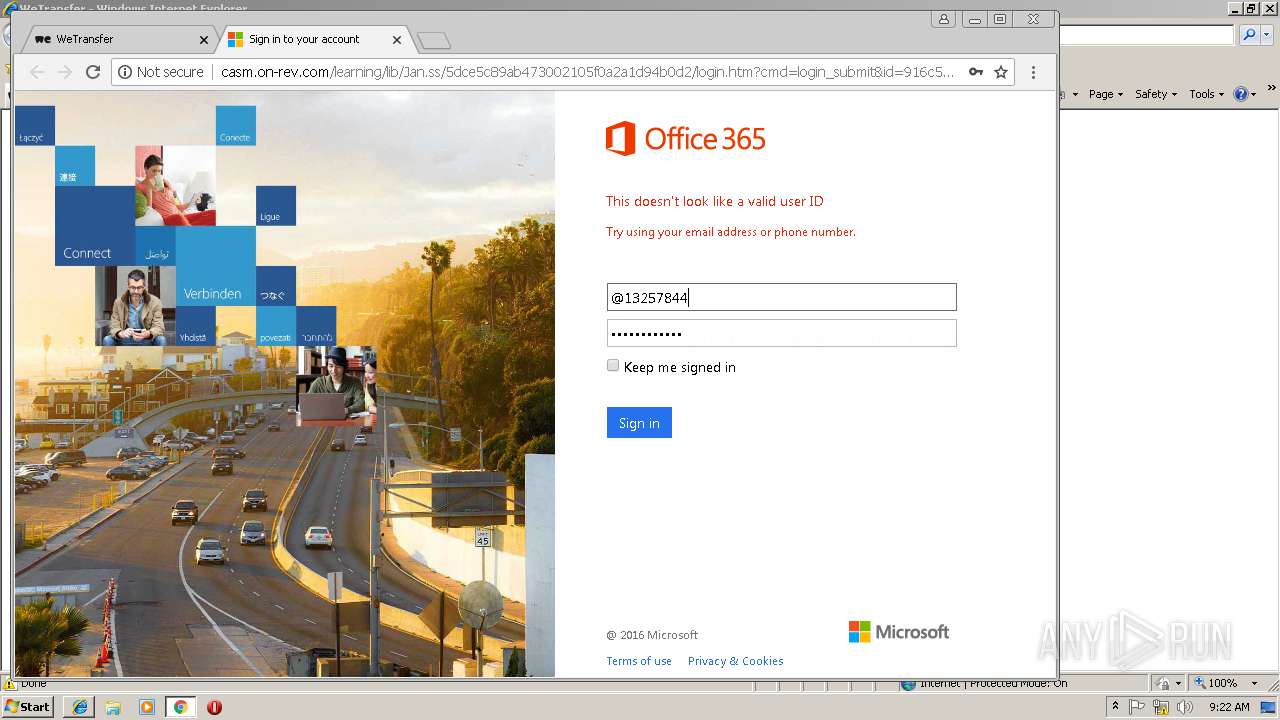
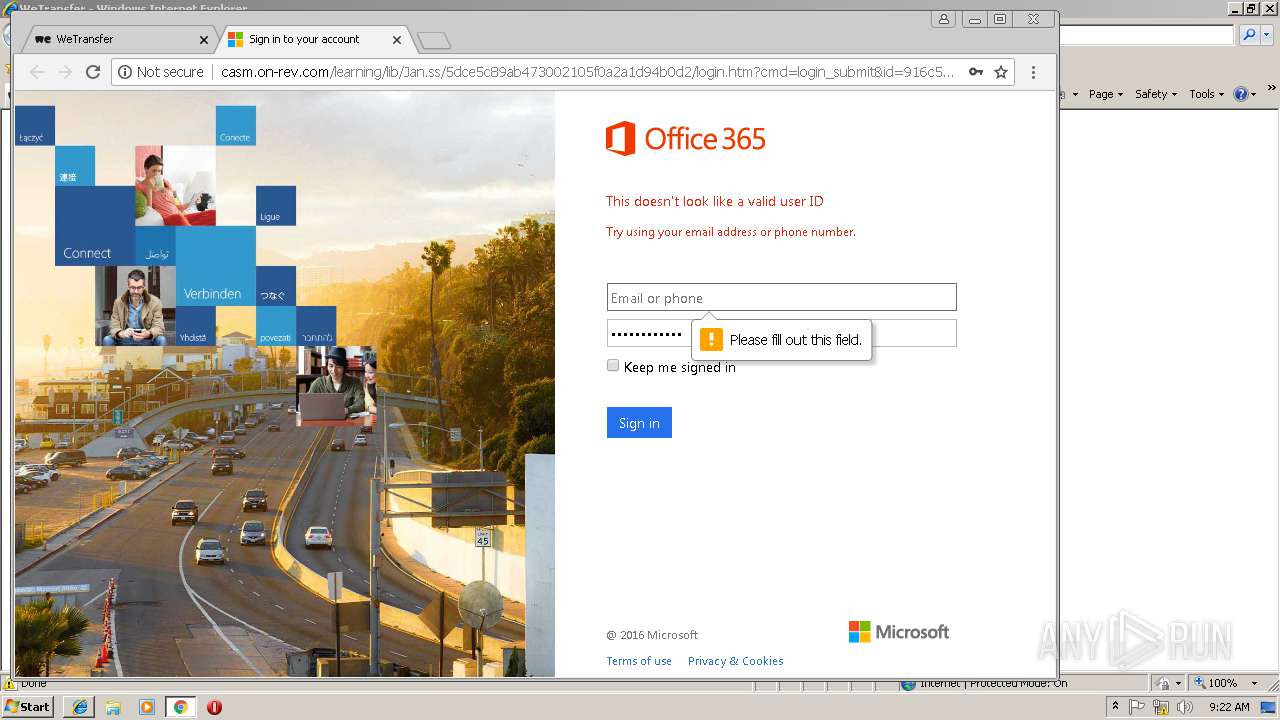
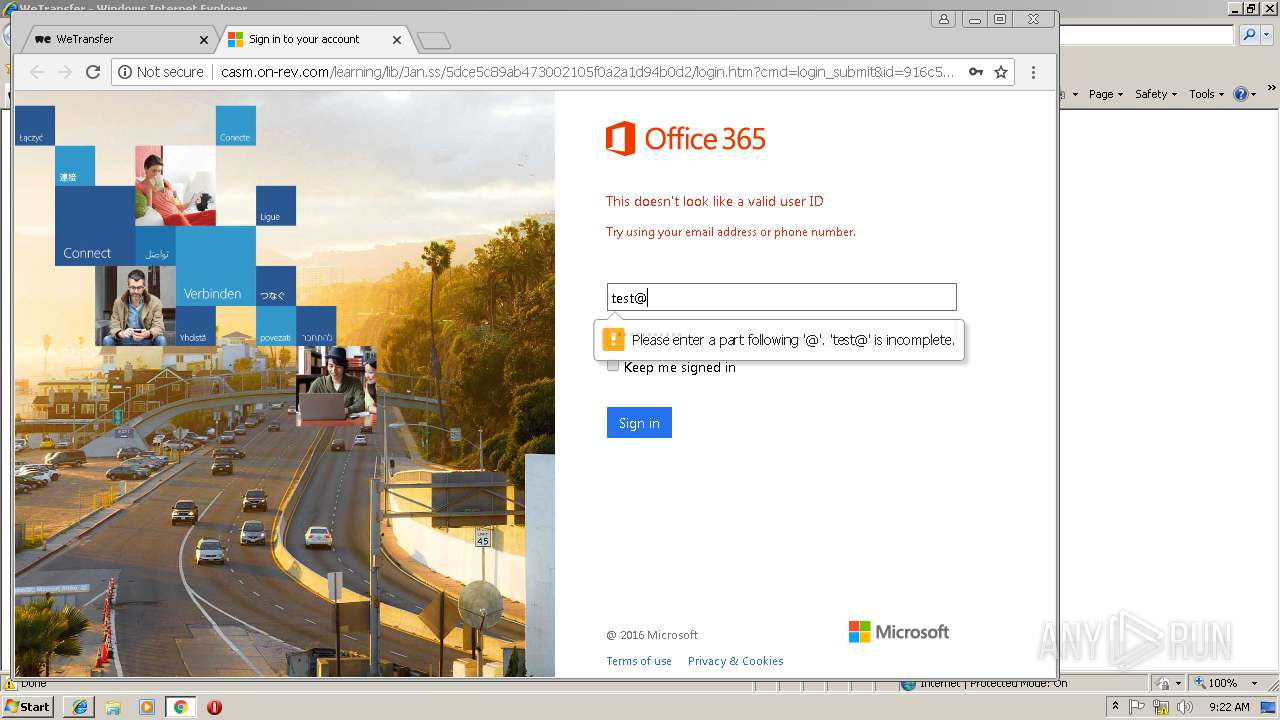
— | — | GET | — | 50.28.38.69:80 | http://casm.on-rev.com/learning/lib/Jan.ss/5dce5c89ab473002105f0a2a1d94b0d2/ | US | — | — | suspicious |
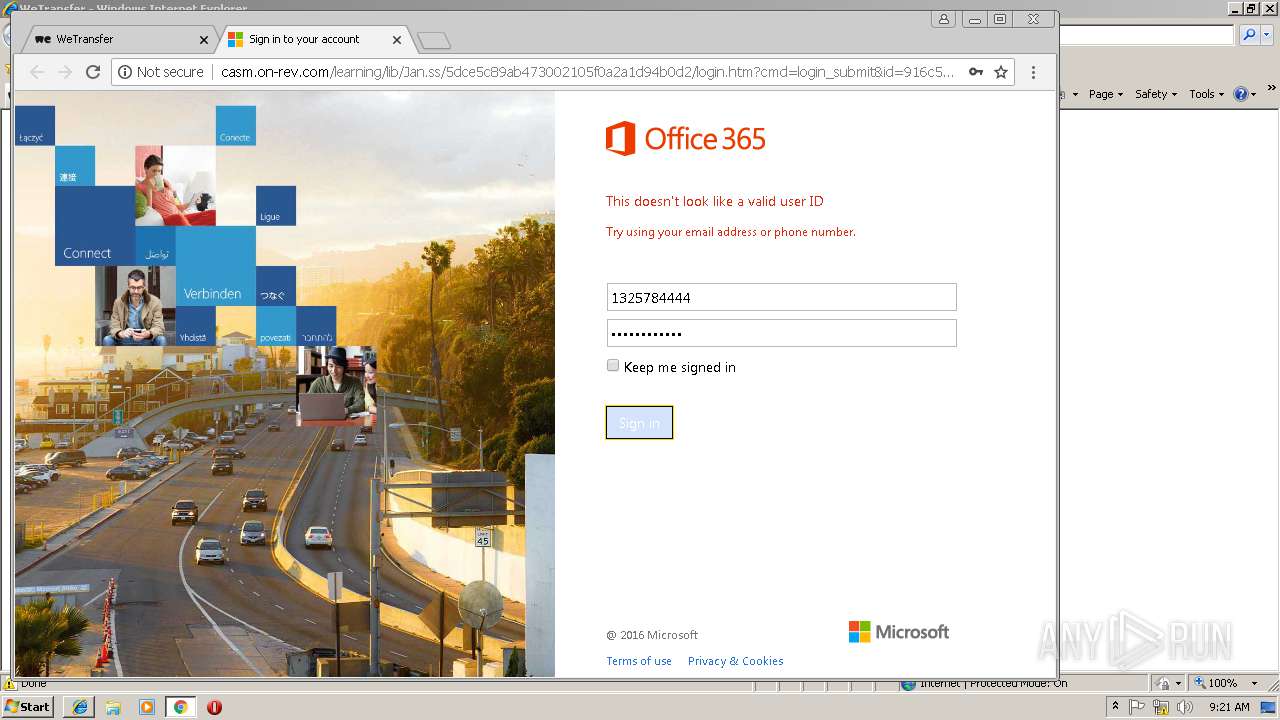
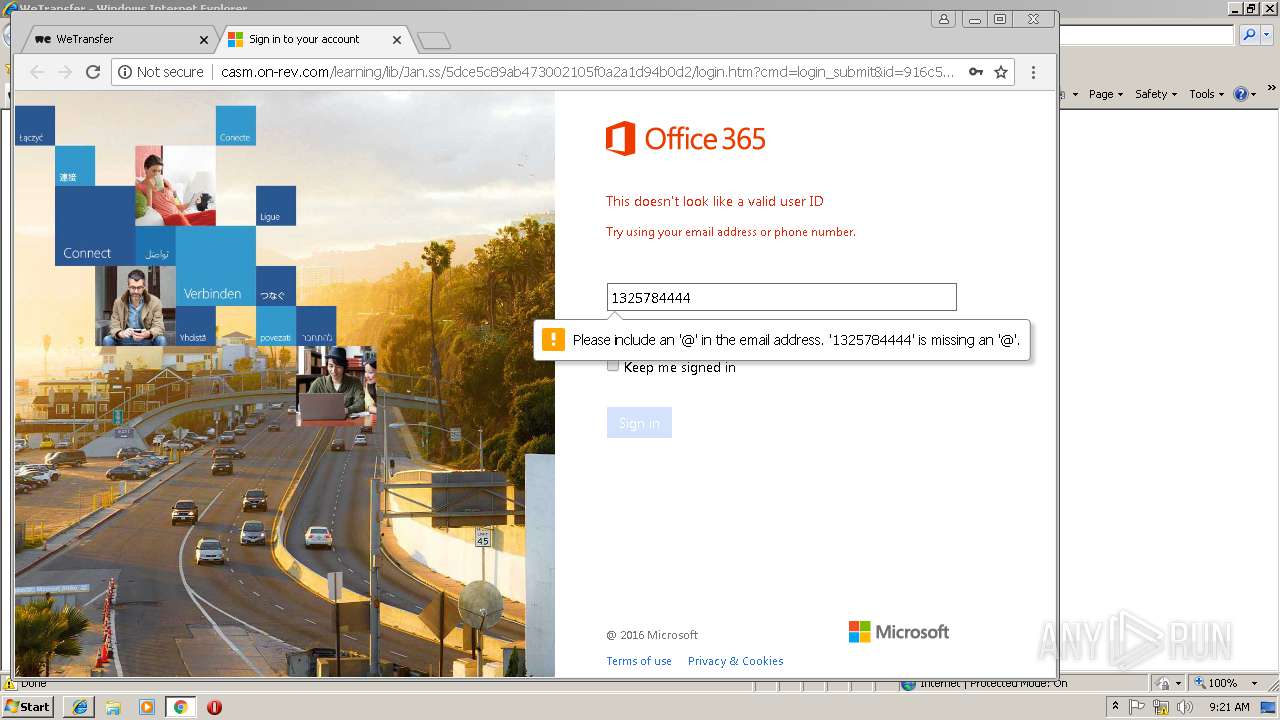
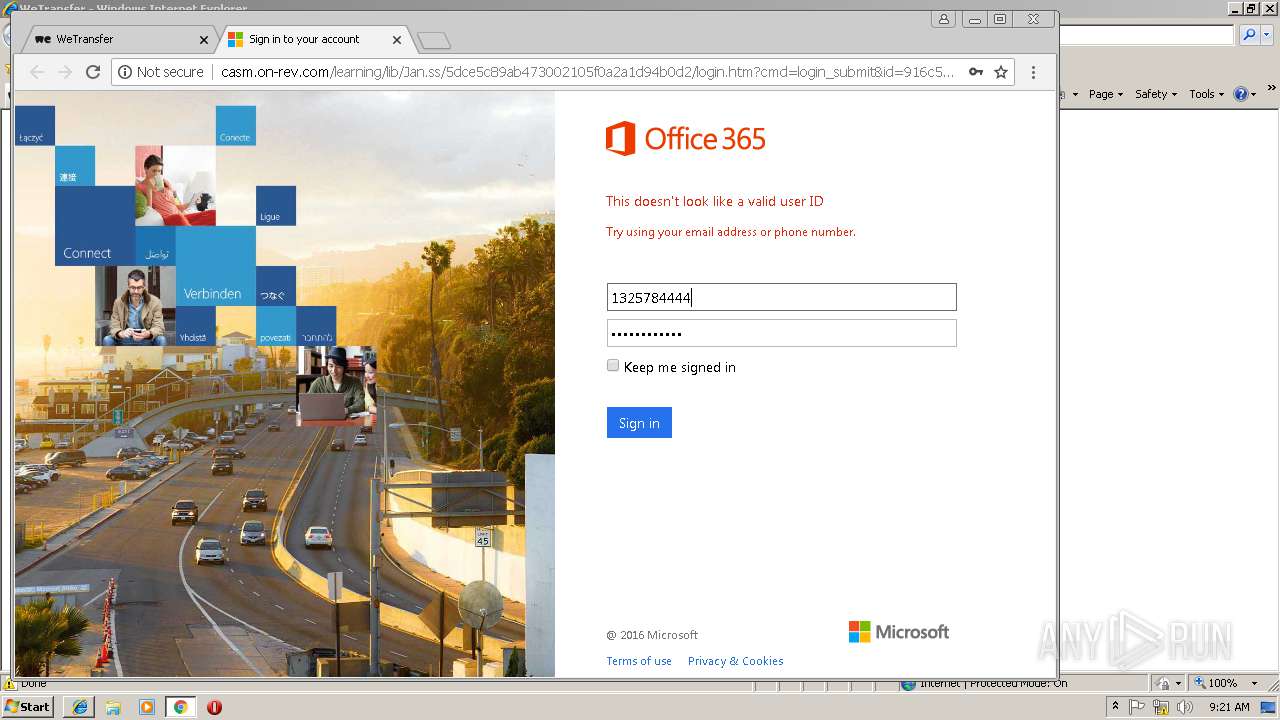
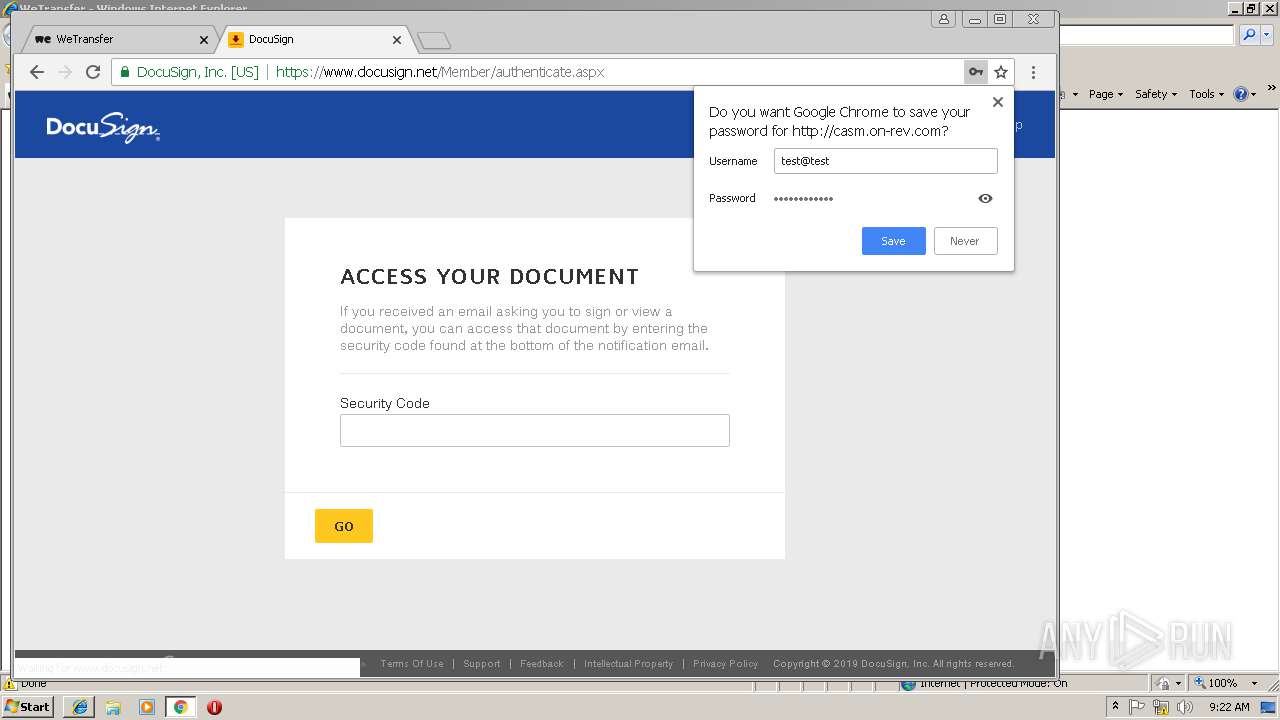
2440 | chrome.exe | GET | — | 50.28.38.69:80 | http://casm.on-rev.com/learning/lib/Jan.ss/5dce5c89ab473002105f0a2a1d94b0d2/login.htm?cmd=login_submit&id=916c5a527dffc11b2e4c227ab0110eb8916c5a527dffc11b2e4c227ab0110eb8&session=916c5a527dffc11b2e4c227ab0110eb8916c5a527dffc11b2e4c227ab0110eb8 | US | — | — | suspicious |
2440 | chrome.exe | GET | — | 50.28.38.69:80 | http://casm.on-rev.com/learning/lib/Jan.ss/ | US | — | — | suspicious |
2440 | chrome.exe | GET | 301 | 50.28.38.69:80 | http://casm.on-rev.com/learning/lib/Jan.ss/5dce5c89ab473002105f0a2a1d94b0d2 | US | html | 284 b | suspicious |
2440 | chrome.exe | POST | — | 50.28.38.69:80 | http://casm.on-rev.com/learning/lib/Jan.ss/5dce5c89ab473002105f0a2a1d94b0d2/login.php | US | — | — | suspicious |
2440 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAo5%2BOXHvlBoK3dClV8T7p4%3D | US | der | 471 b | whitelisted |
2440 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3216 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
3216 | iexplore.exe | GET | 200 | 52.85.182.15:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2440 | chrome.exe | 172.217.21.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2440 | chrome.exe | 172.217.16.163:443 | www.google.de | Google Inc. | US | whitelisted |
2952 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3216 | iexplore.exe | 52.17.181.56:443 | wetransfer.com | Amazon.com, Inc. | IE | unknown |
3216 | iexplore.exe | 52.85.182.15:80 | x.ss2.us | Amazon.com, Inc. | US | whitelisted |
3216 | iexplore.exe | 54.230.202.216:443 | prod-cdn.wetransfer.net | Amazon.com, Inc. | US | unknown |
3216 | iexplore.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3216 | iexplore.exe | 172.217.18.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2440 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2440 | chrome.exe | 34.243.235.206:443 | wtplus.wetransfer.com | Amazon.com, Inc. | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
wetransfer.com |
| shared |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
prod-cdn.wetransfer.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
d19ptbnuzhibkh.cloudfront.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
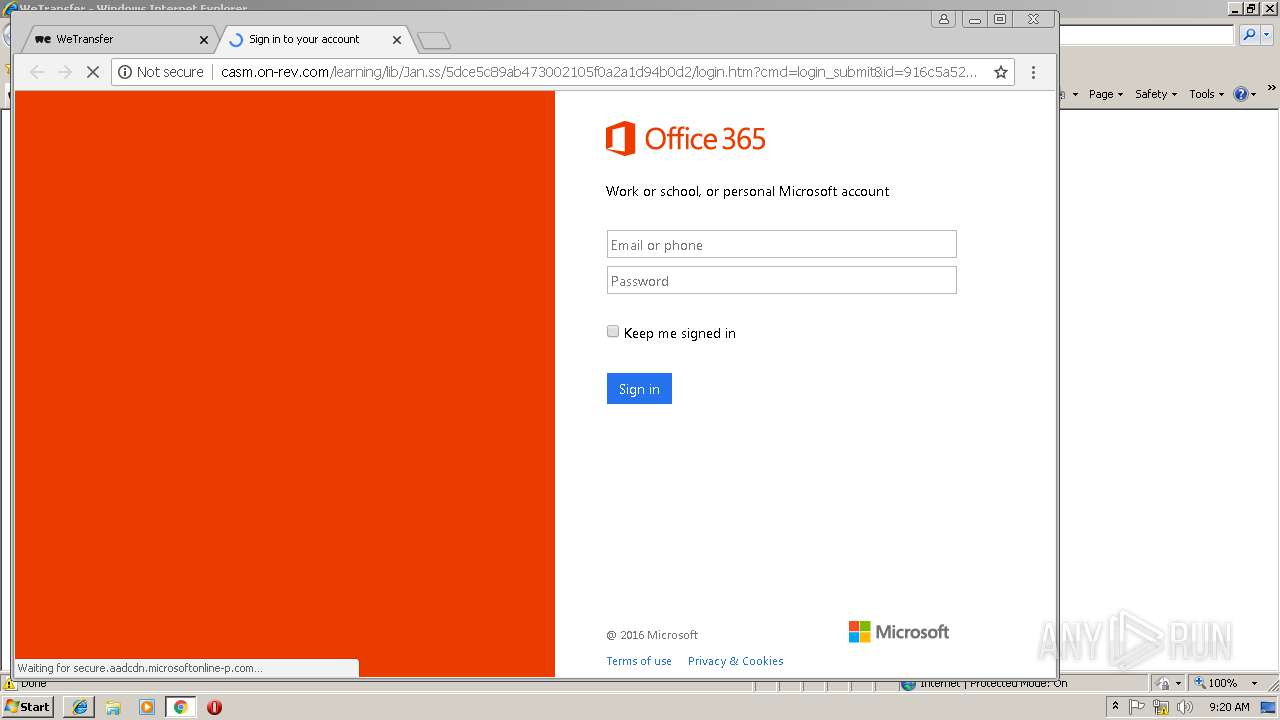
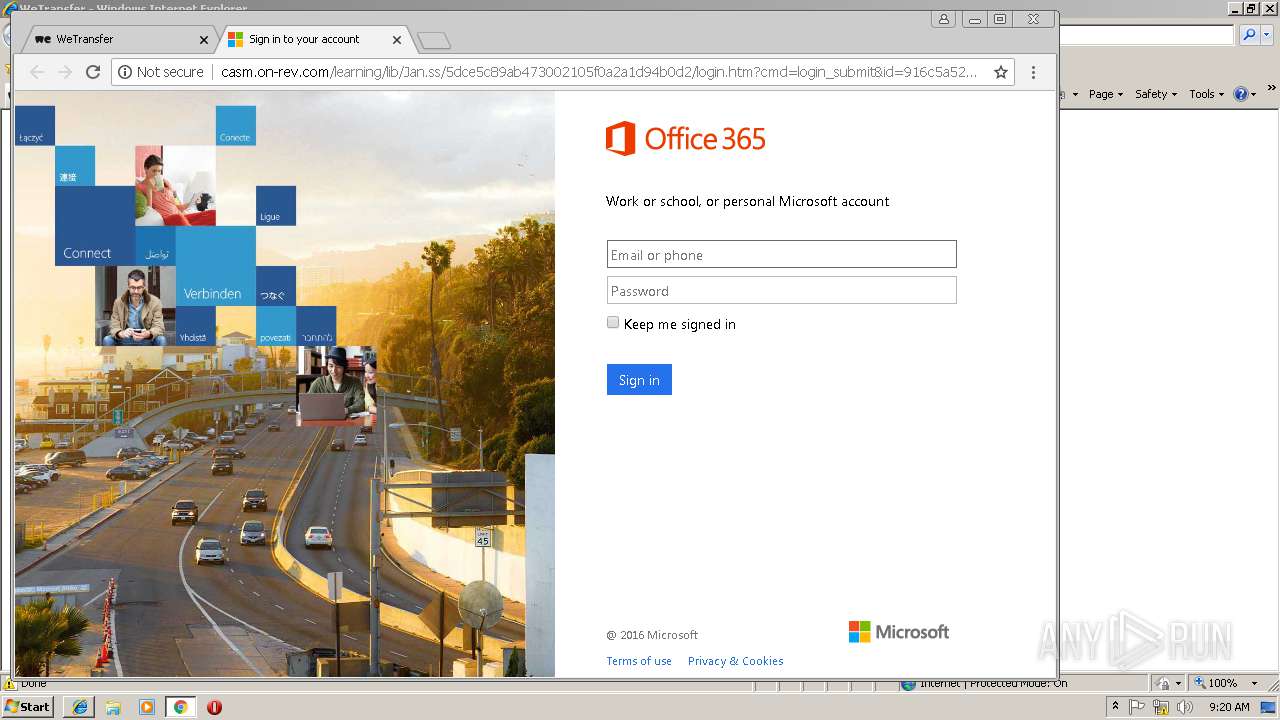
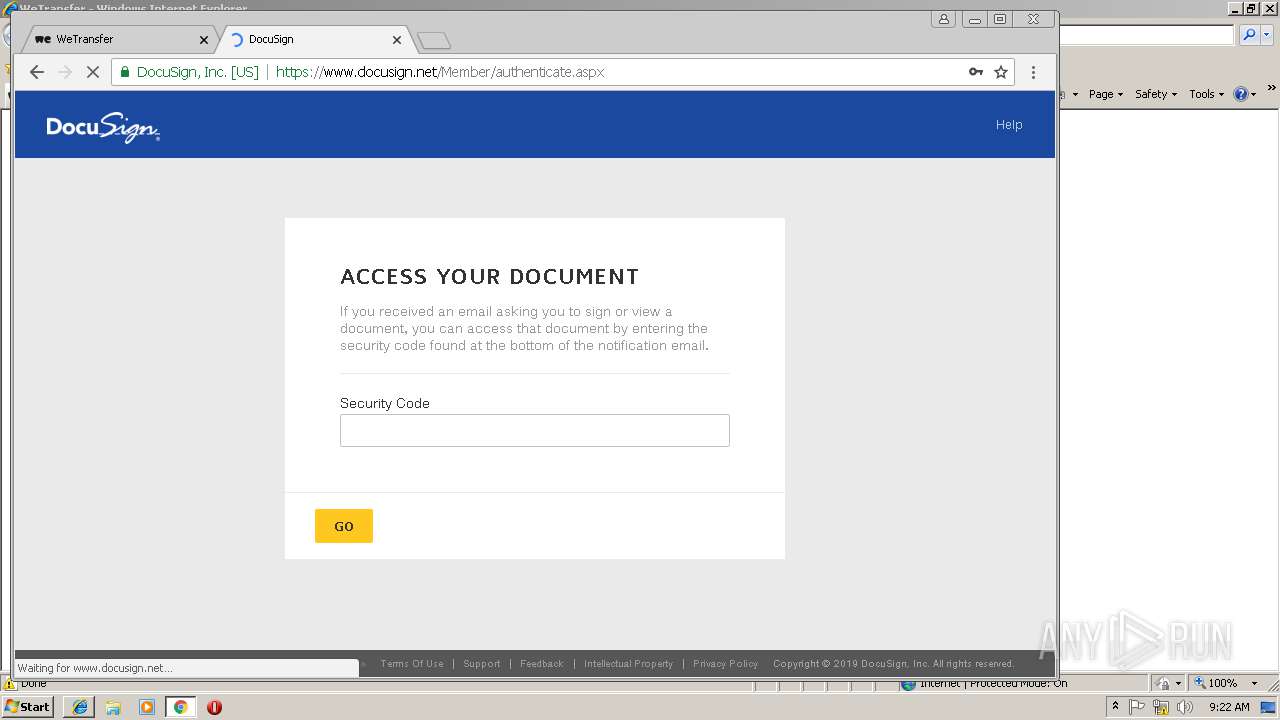
2440 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Phishing Redirect Feb 09 2016 |
2440 | chrome.exe | A Network Trojan was detected | SC PHISHING PDF/Phishing - unknown malware |
2440 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Office 365 Phishing Landing Aug 24 2016 |
2440 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Phishing Redirect Feb 09 2016 |
2440 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
3 ETPRO signatures available at the full report