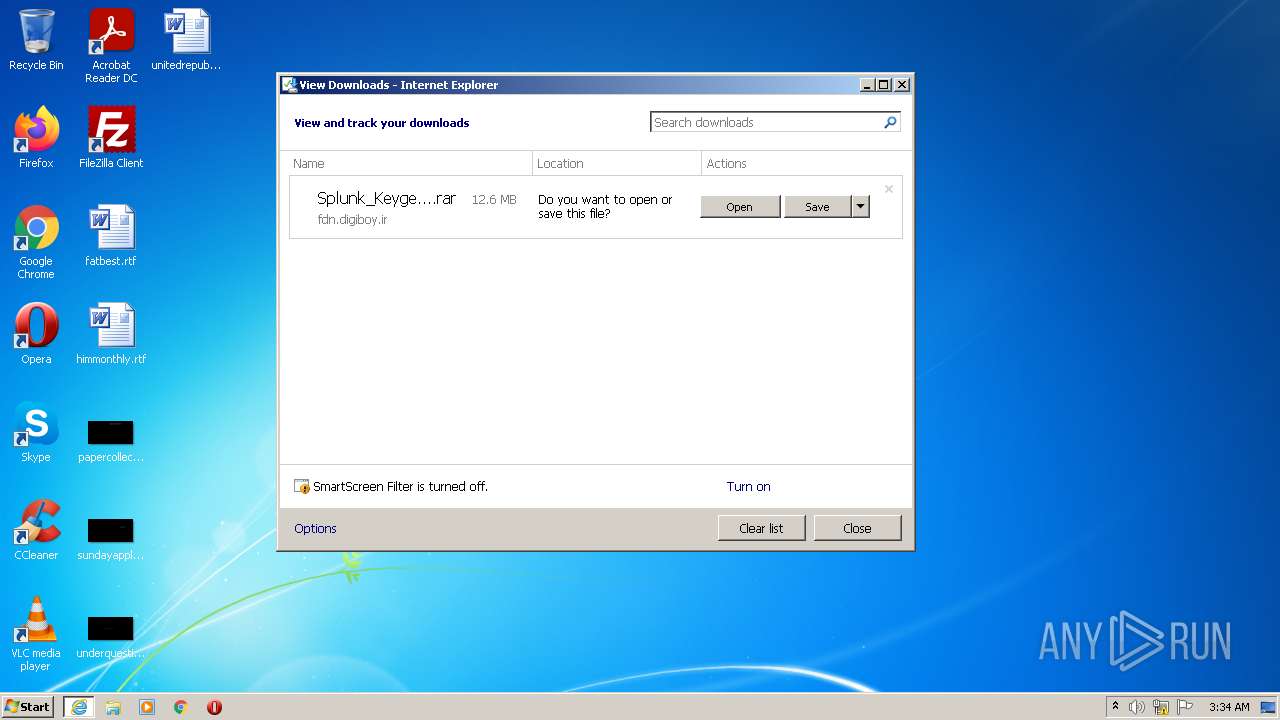
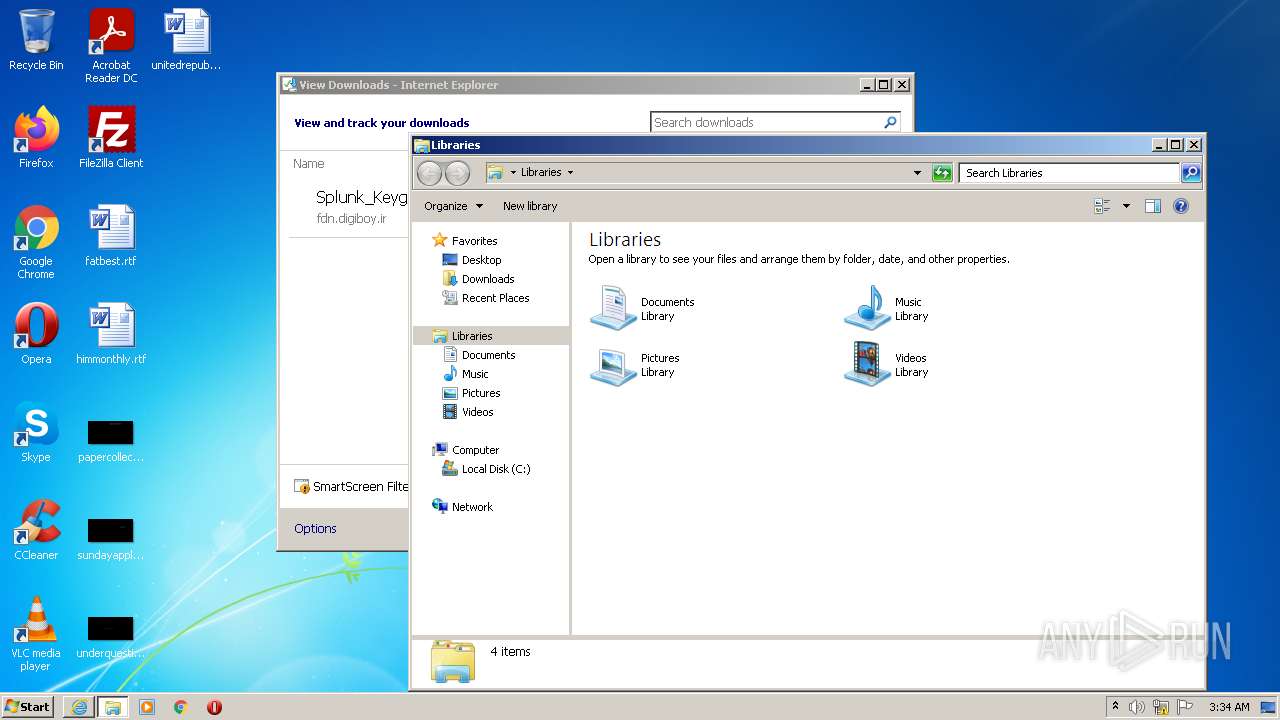
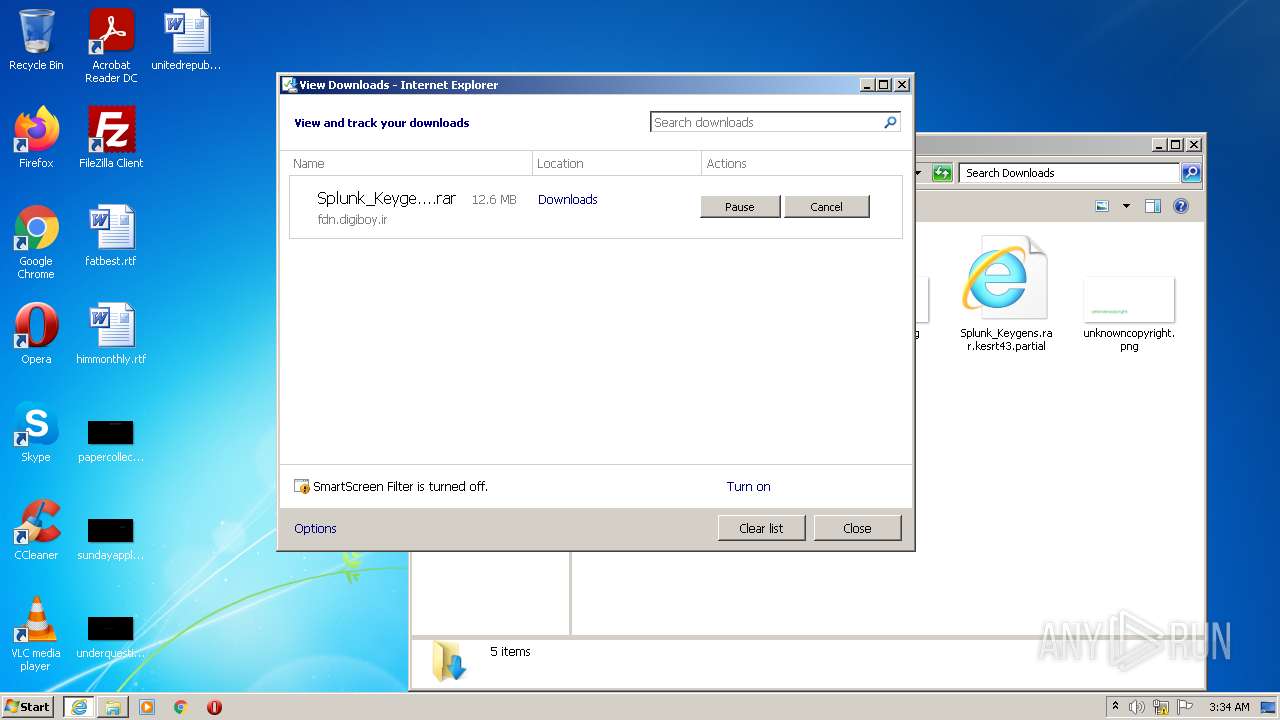
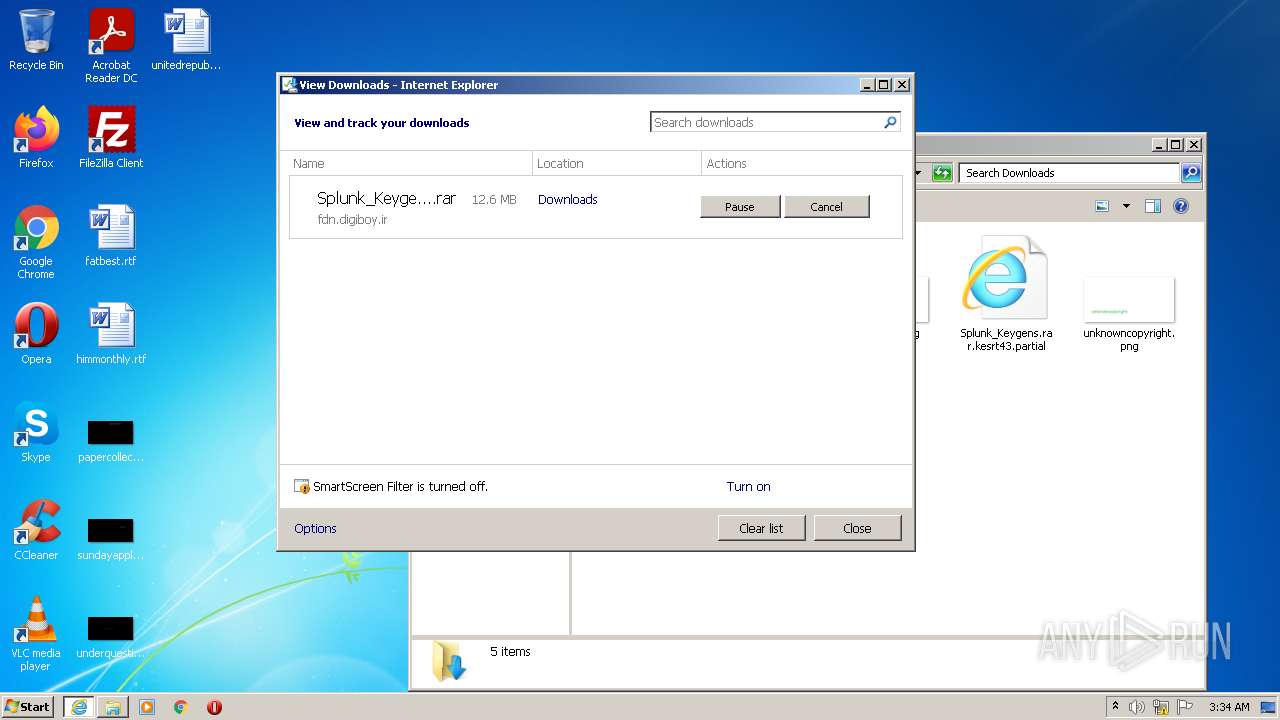
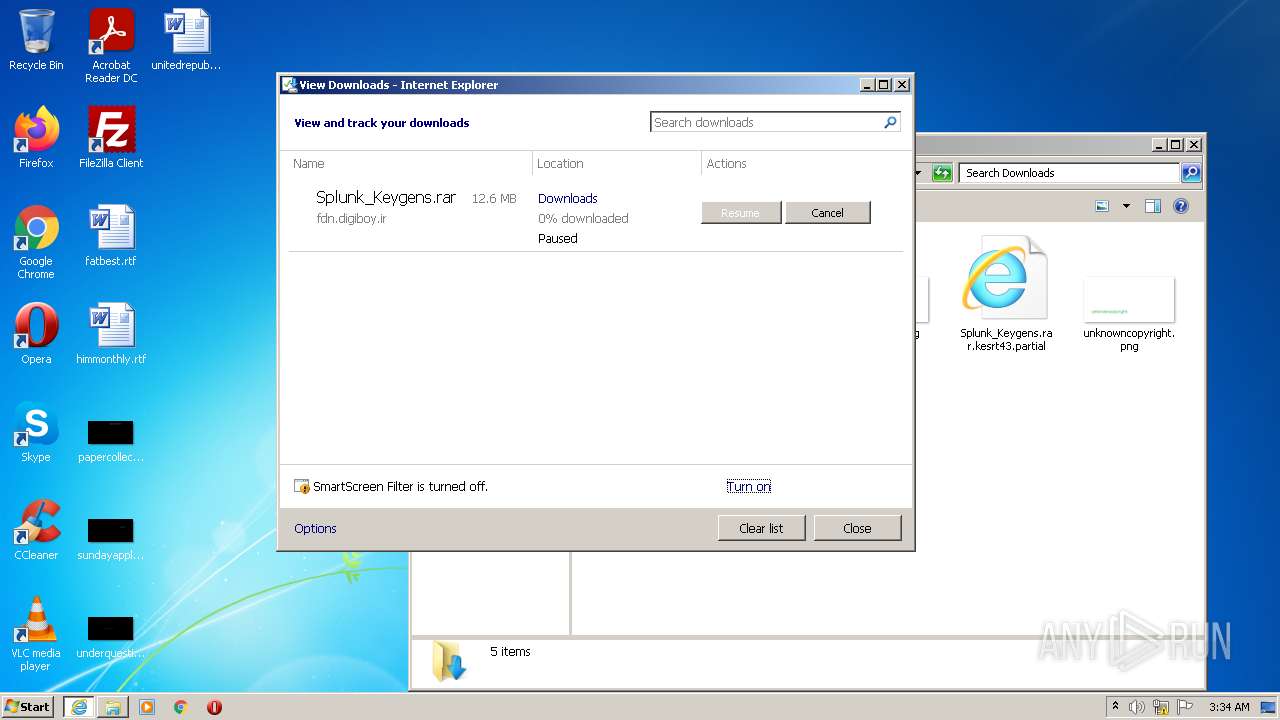
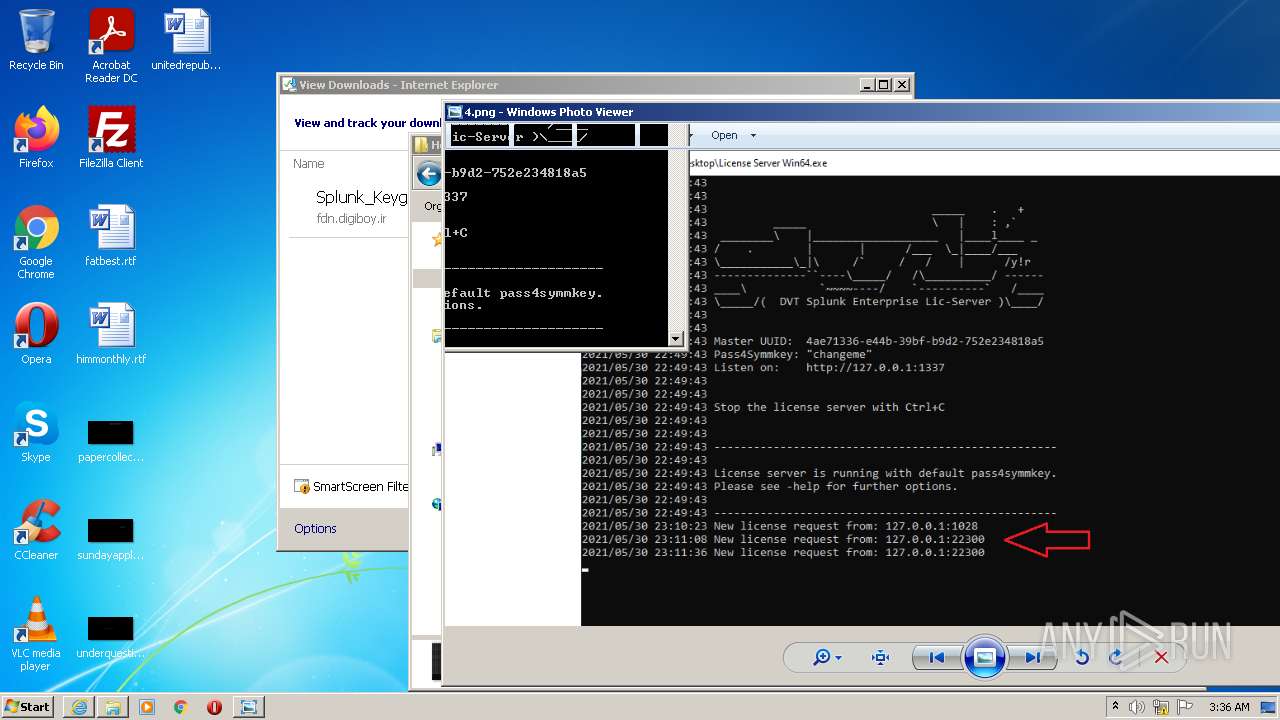
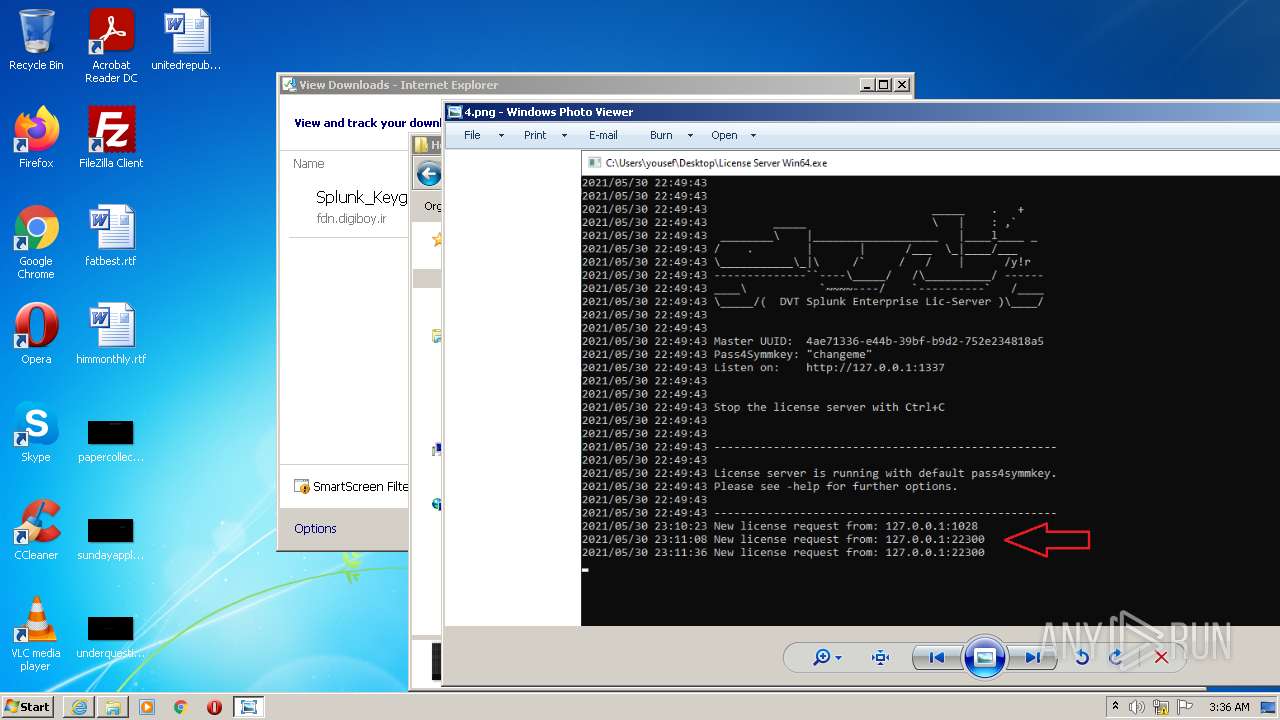
| URL: | https://fdn.digiboy.ir/dlir-s3/Splunk_Keygens.rar |
| Full analysis: | https://app.any.run/tasks/26673a72-addc-4d06-98bd-148a806eed9b |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2022, 02:34:15 |
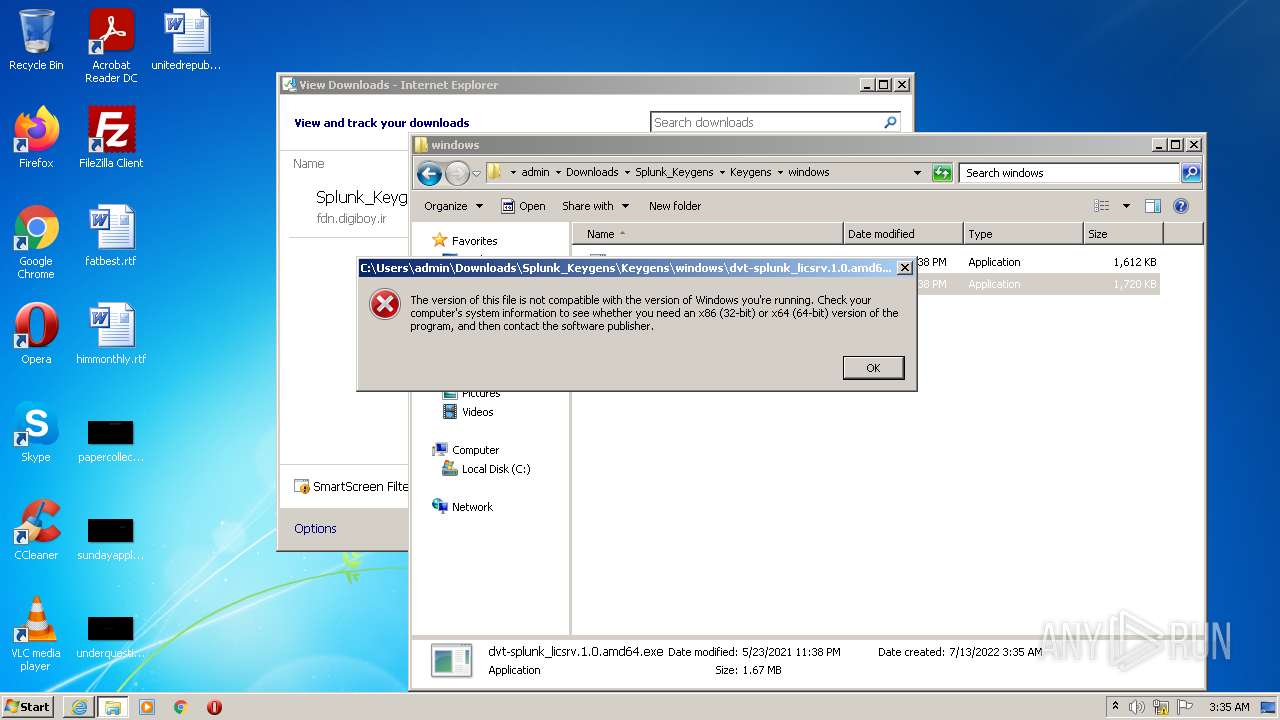
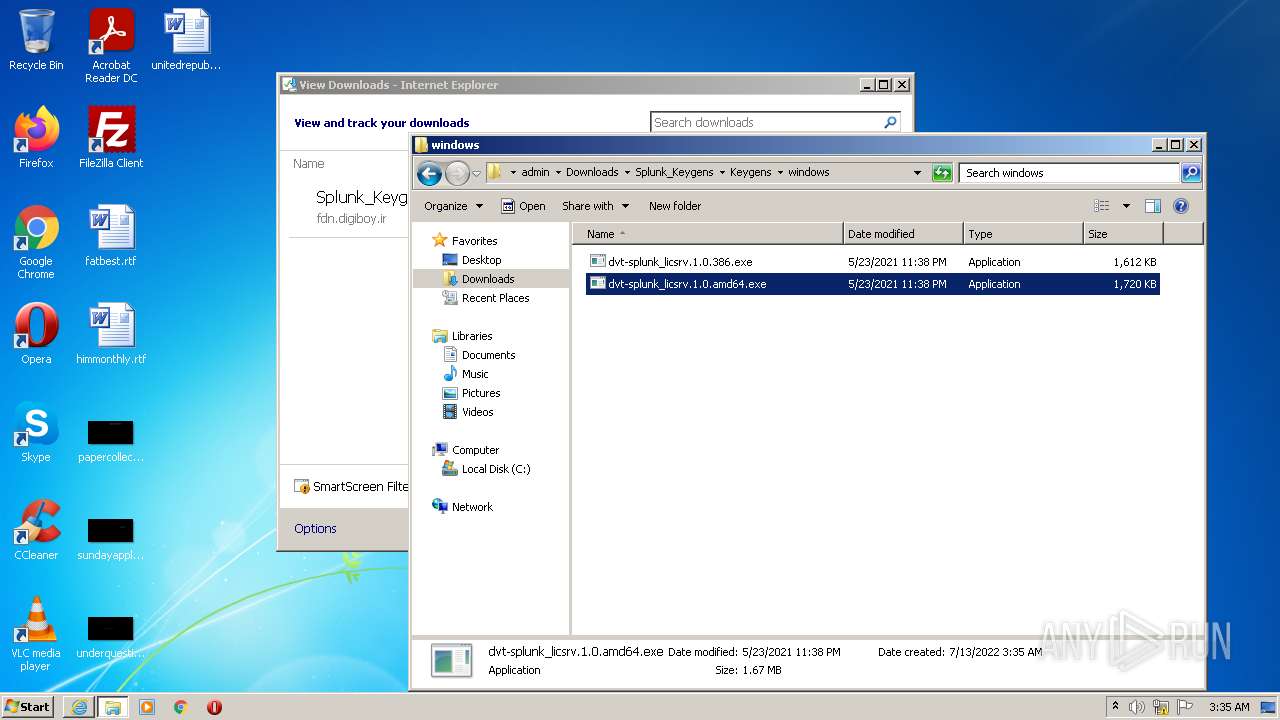
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 49F8D1ABD5E36B670107E0398F6941B2 |
| SHA1: | 3051DA6F790218E0E862109787C528D76B616A16 |
| SHA256: | E3EE2FB4D05748D8C5E8D9E5AD08D141589AB6989E25D61EB34CF2150131E792 |
| SSDEEP: | 3:N8niE52s6FxLWj+n:2n3osoWj+n |
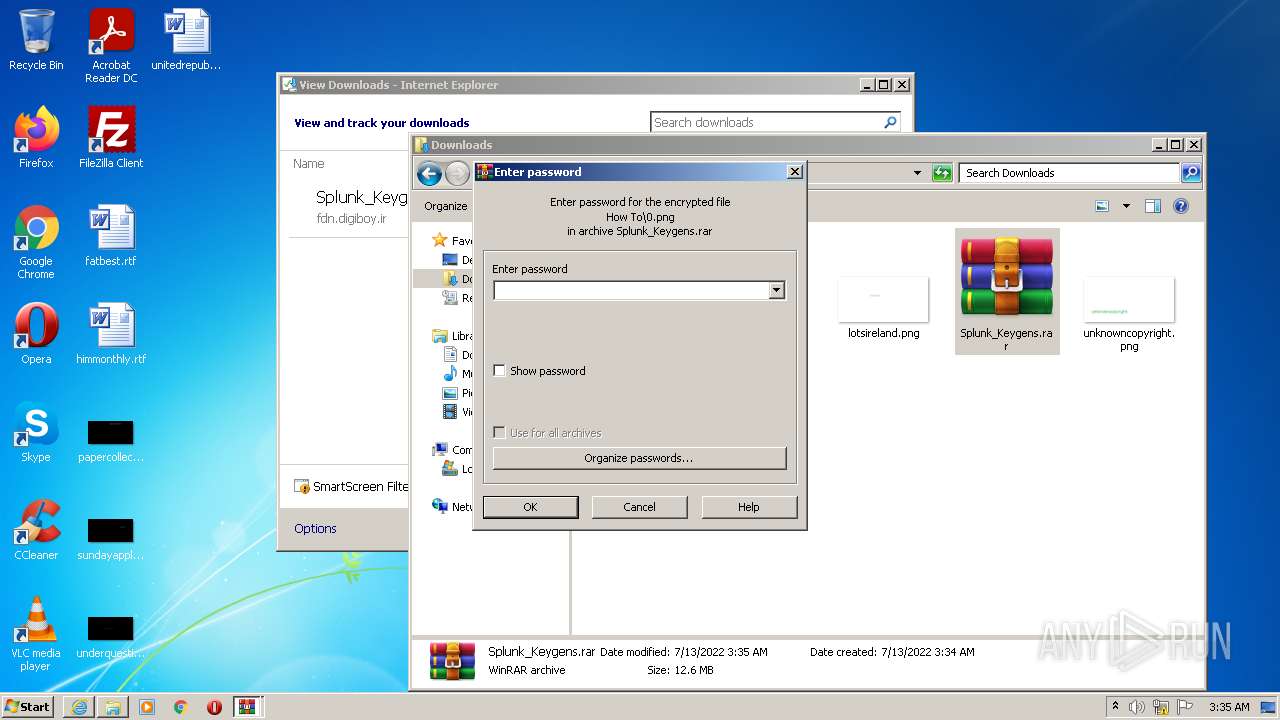
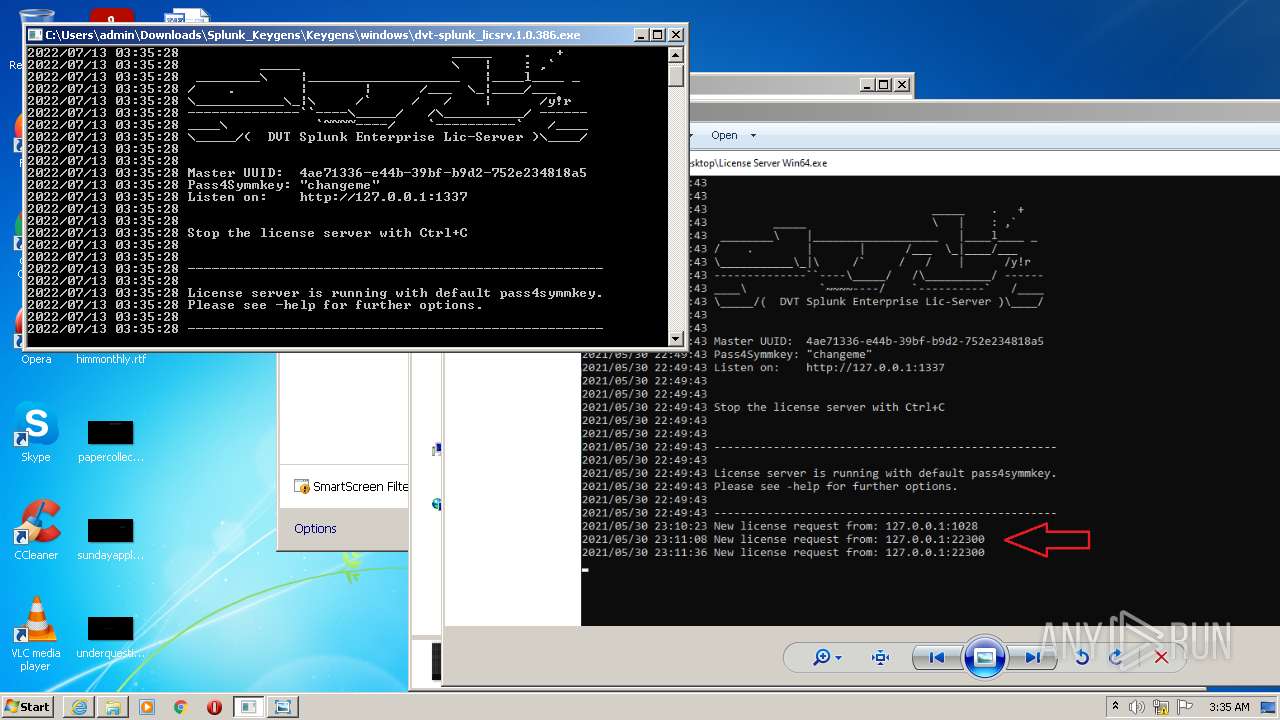
MALICIOUS
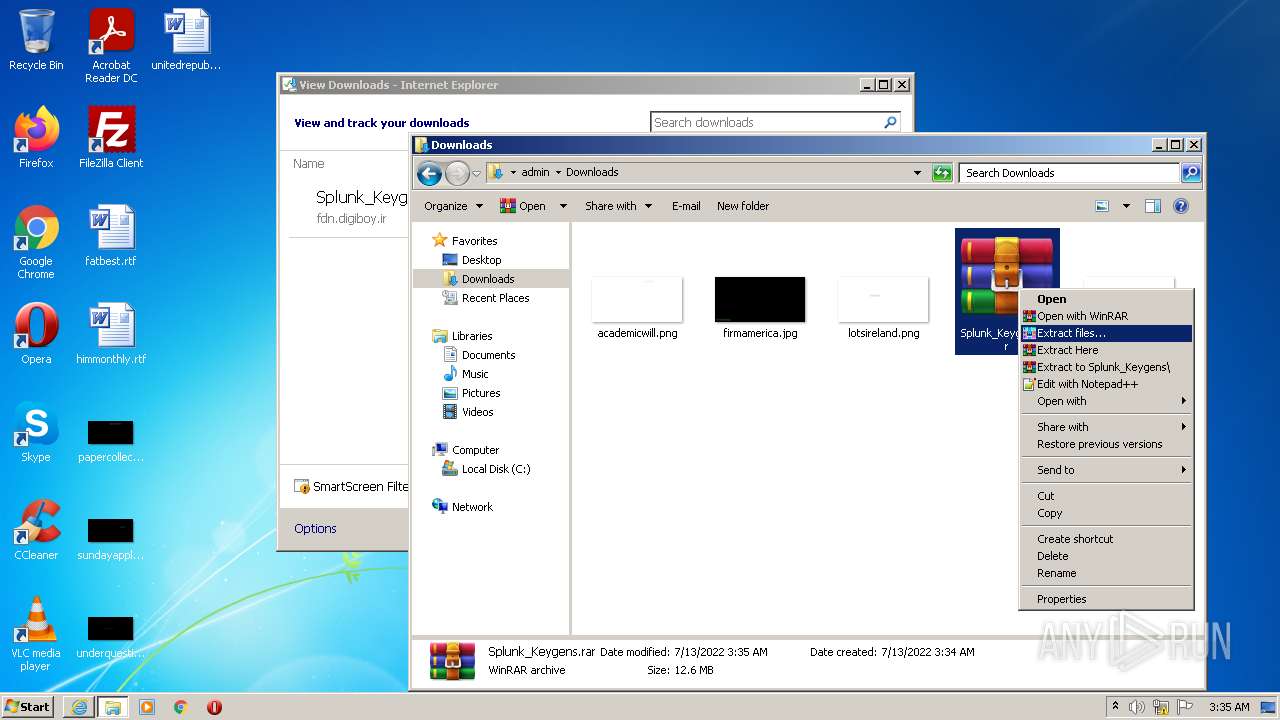
Drops executable file immediately after starts
- WinRAR.exe (PID: 2936)
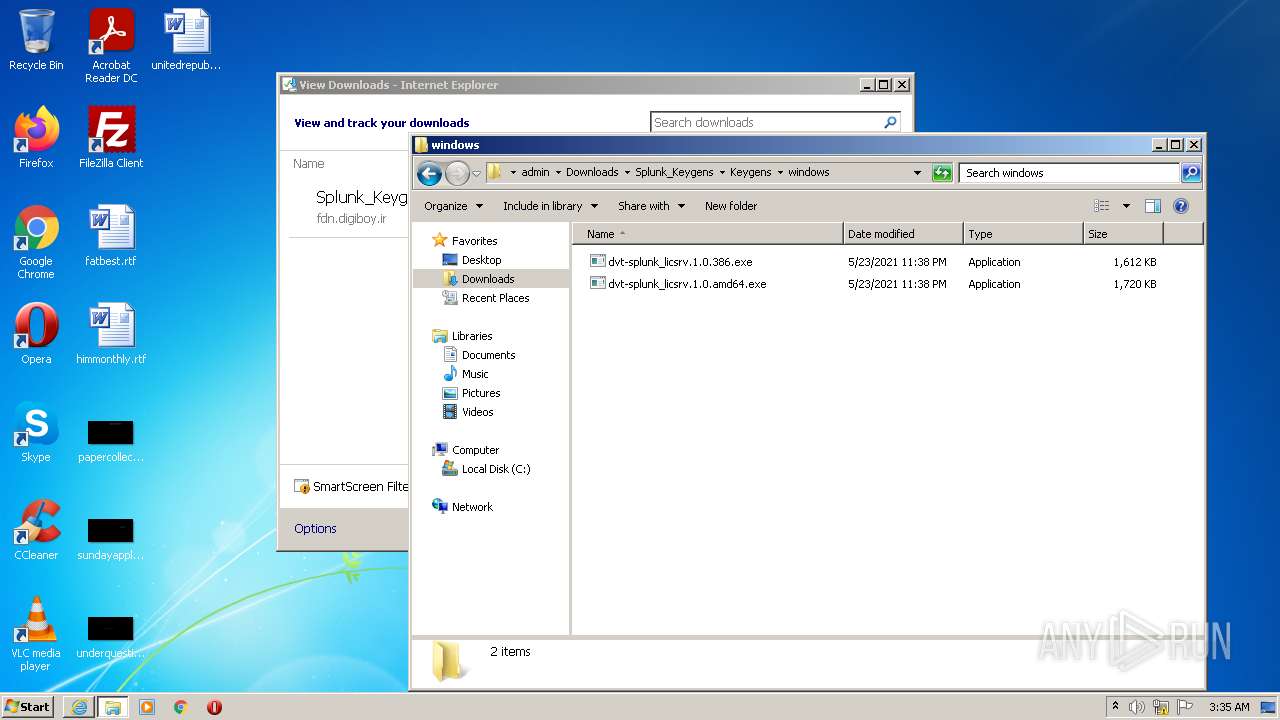
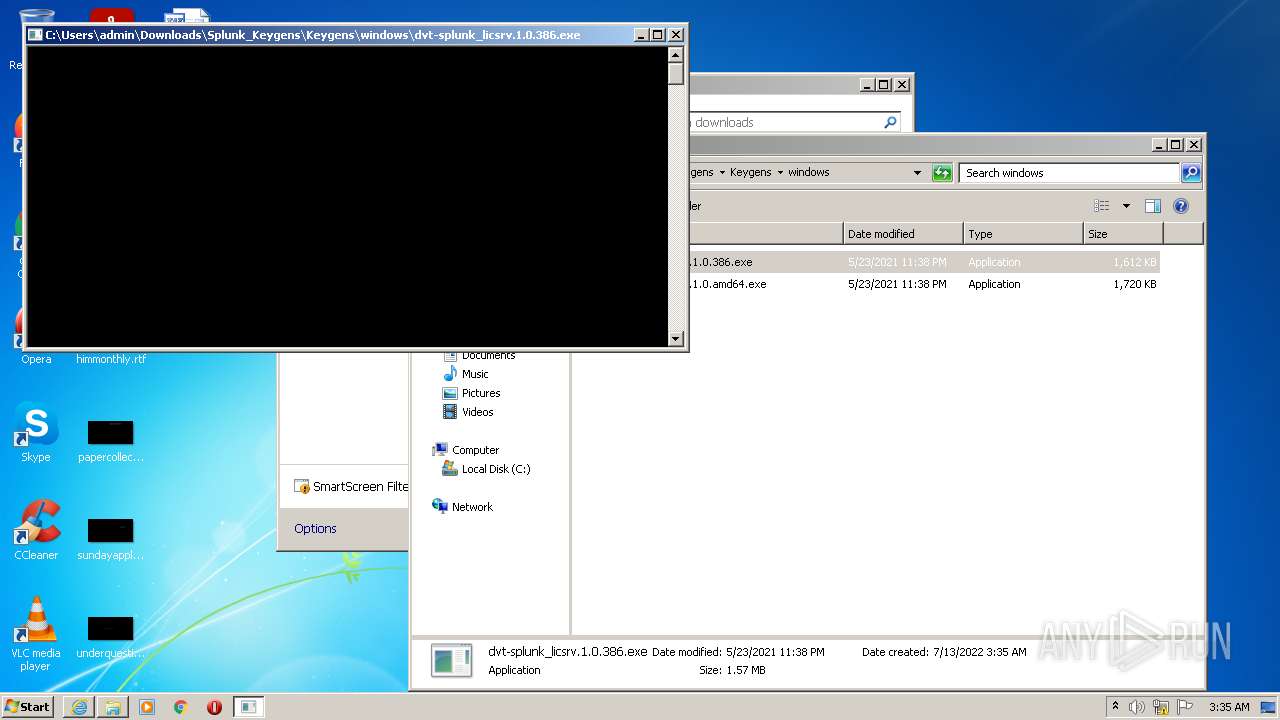
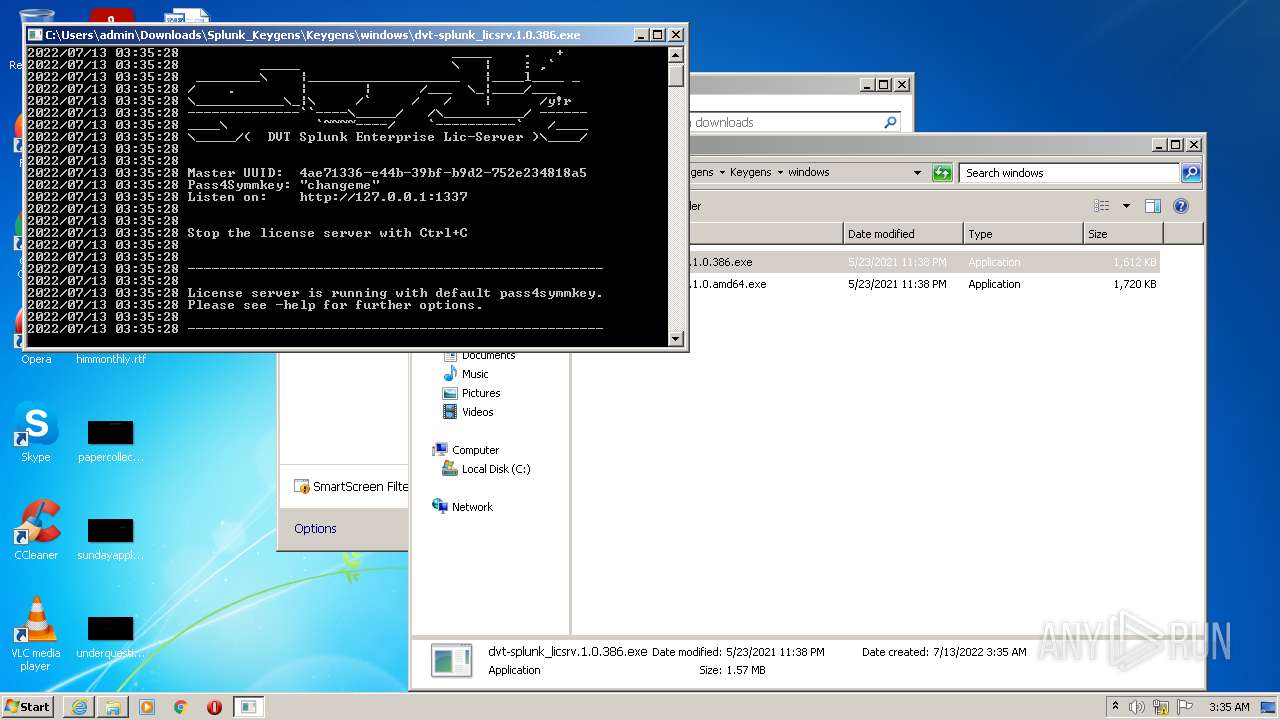
Application was dropped or rewritten from another process
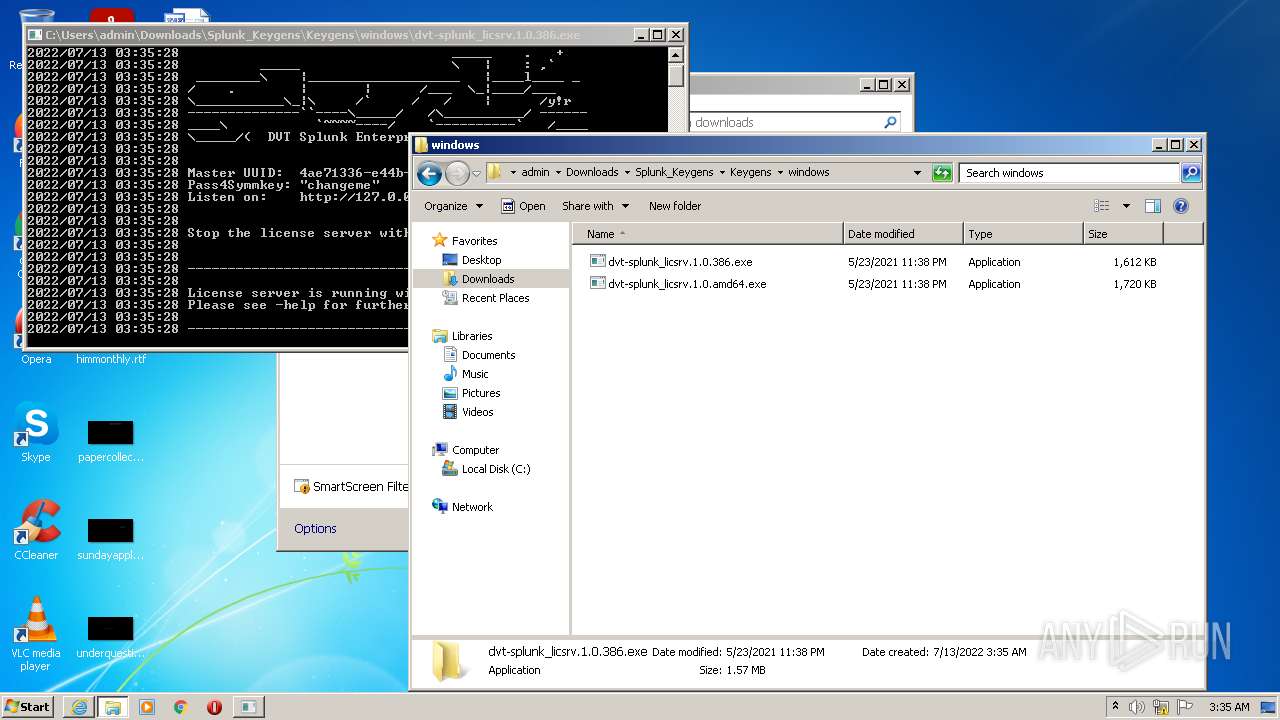
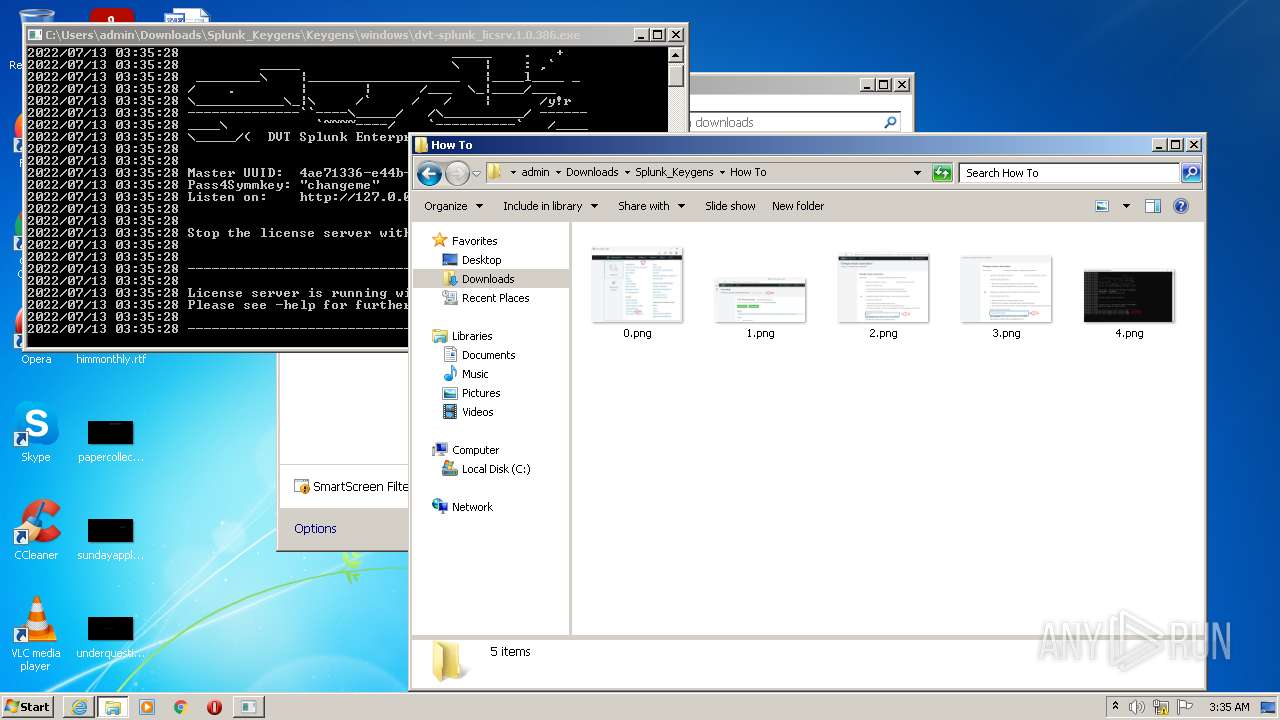
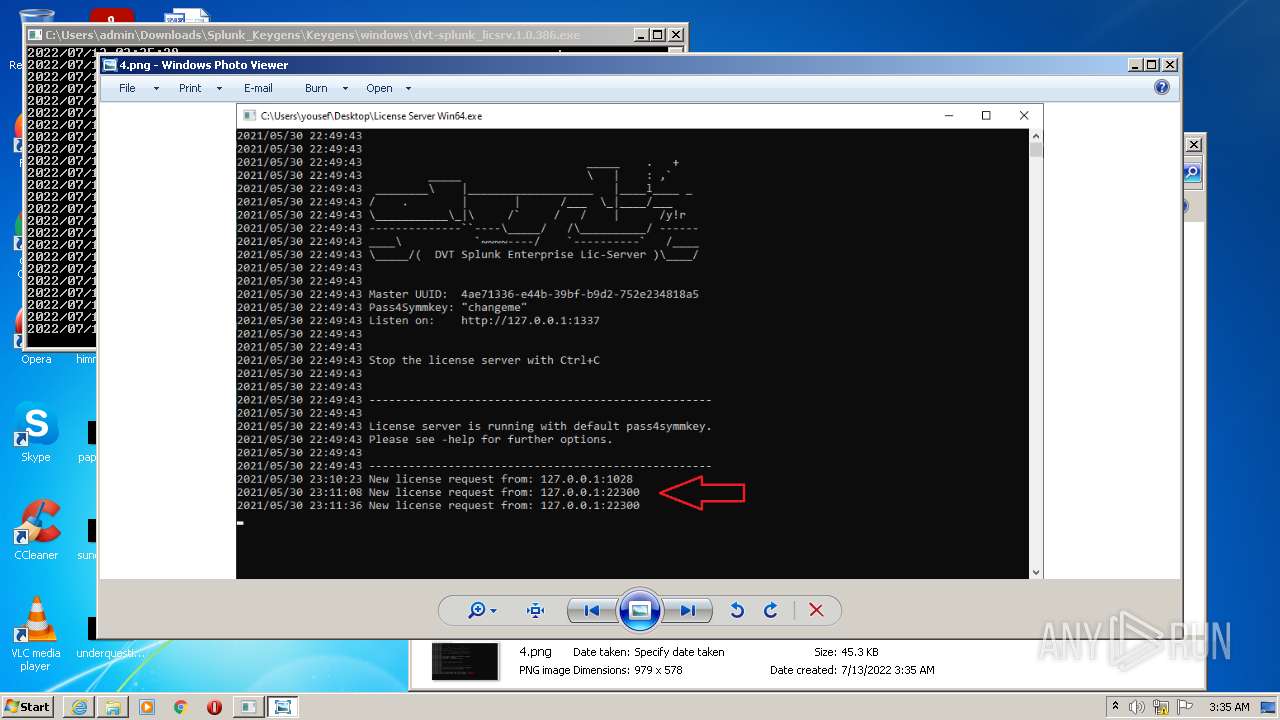
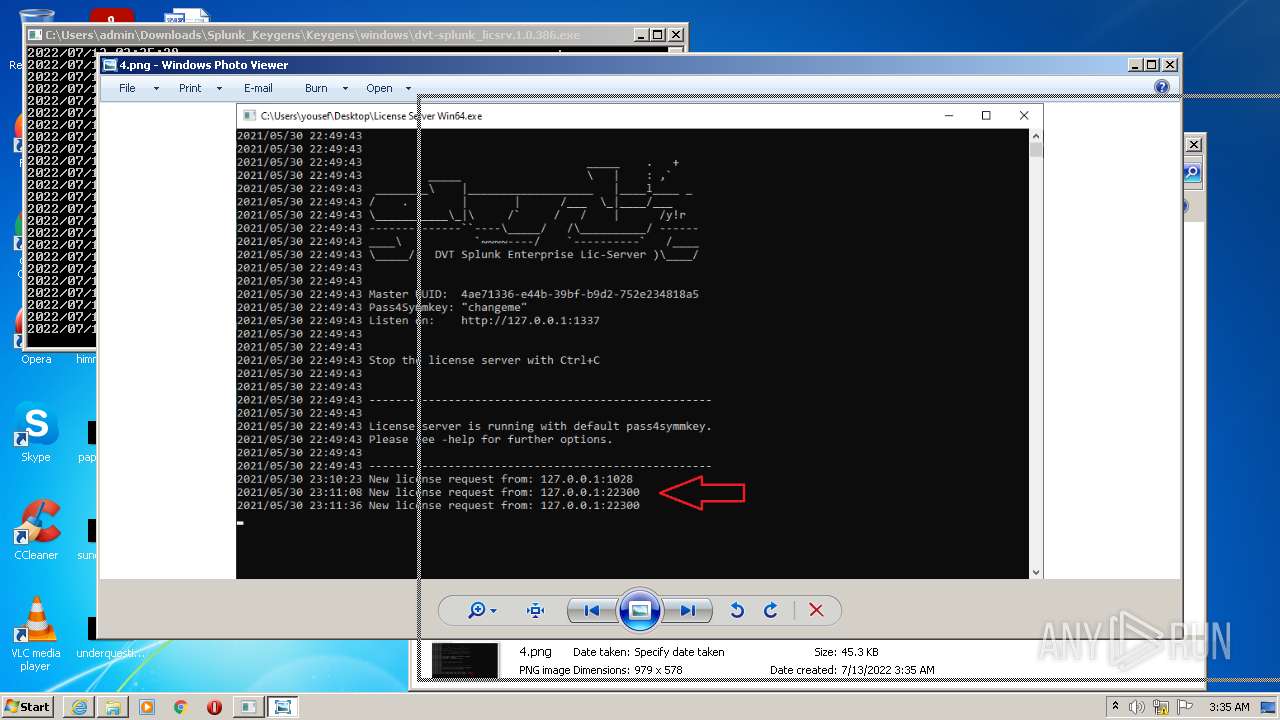
- dvt-splunk_licsrv.1.0.386.exe (PID: 3244)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3492)
Checks supported languages
- WinRAR.exe (PID: 2936)
- dvt-splunk_licsrv.1.0.386.exe (PID: 3244)
Reads the computer name
- WinRAR.exe (PID: 2936)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2936)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2936)
Executed via COM
- DllHost.exe (PID: 2784)
INFO
Checks supported languages
- iexplore.exe (PID: 3096)
- iexplore.exe (PID: 3492)
- explorer.exe (PID: 3700)
- DllHost.exe (PID: 2784)
Changes internet zones settings
- iexplore.exe (PID: 3096)
Reads the computer name
- iexplore.exe (PID: 3096)
- iexplore.exe (PID: 3492)
- explorer.exe (PID: 3700)
- DllHost.exe (PID: 2784)
Application launched itself
- iexplore.exe (PID: 3096)
Checks Windows Trust Settings
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 3096)
Reads settings of System Certificates
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 3096)
Reads the date of Windows installation
- iexplore.exe (PID: 3096)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3096)
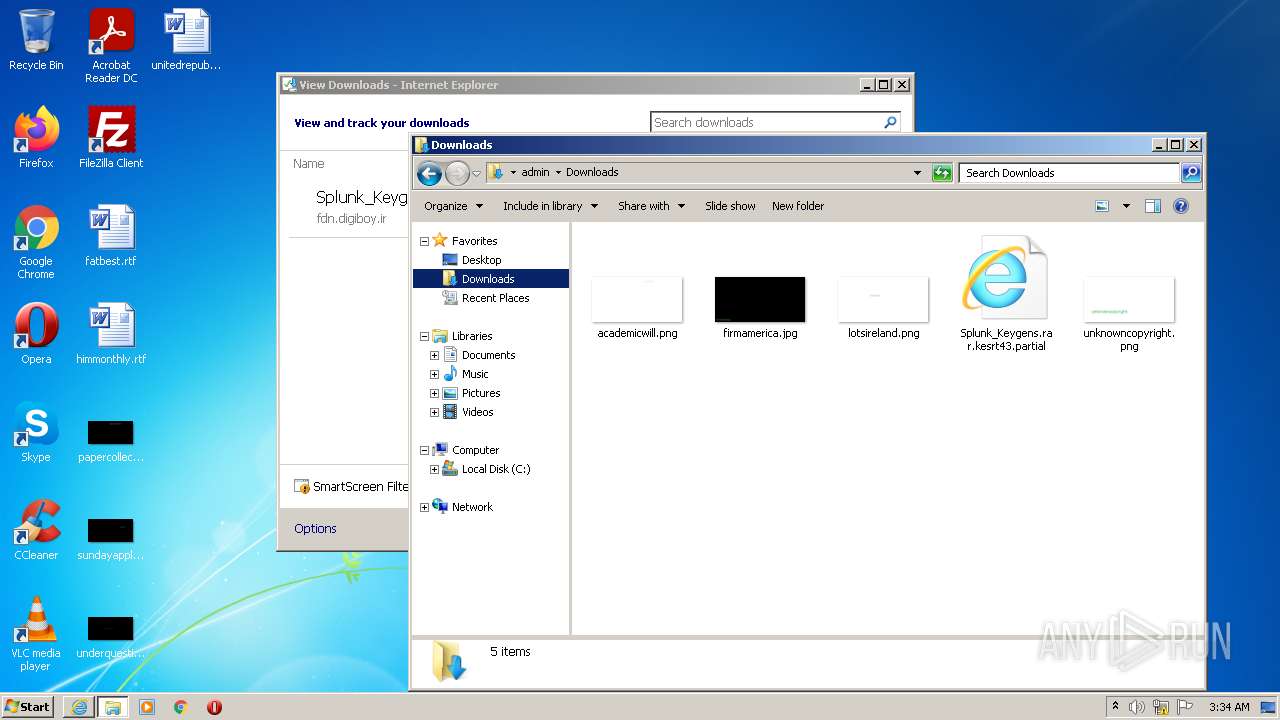
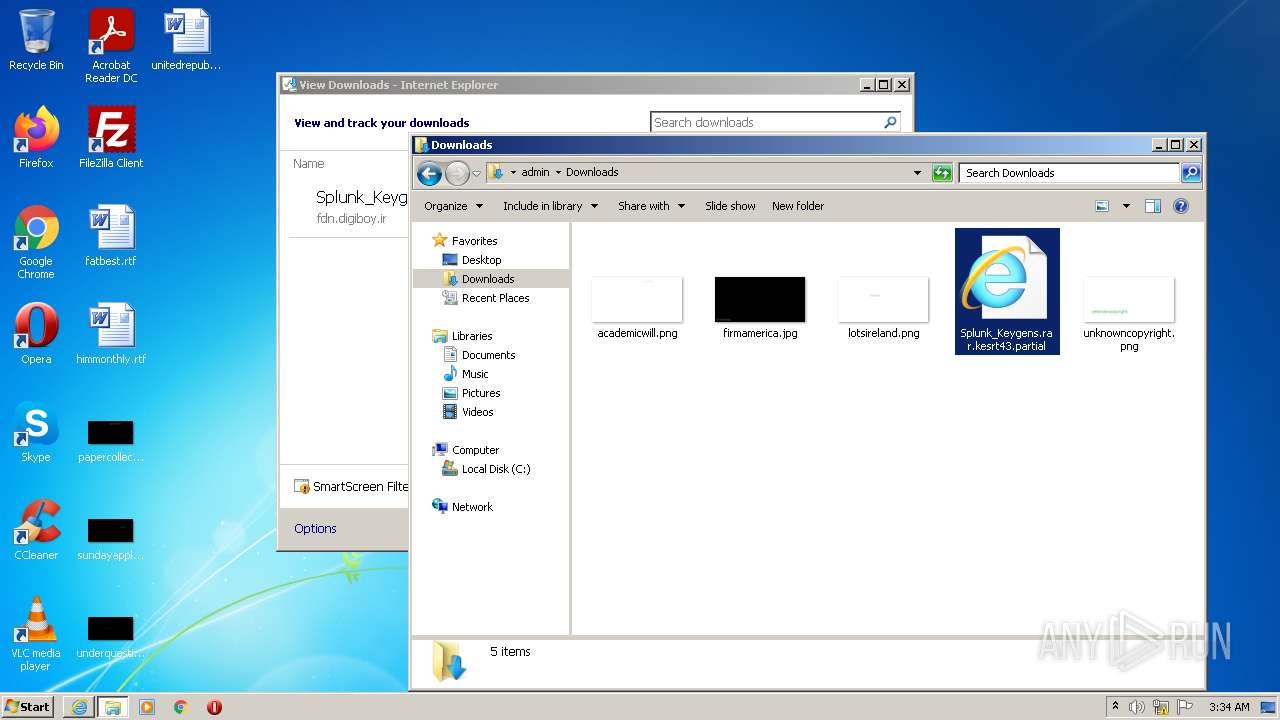
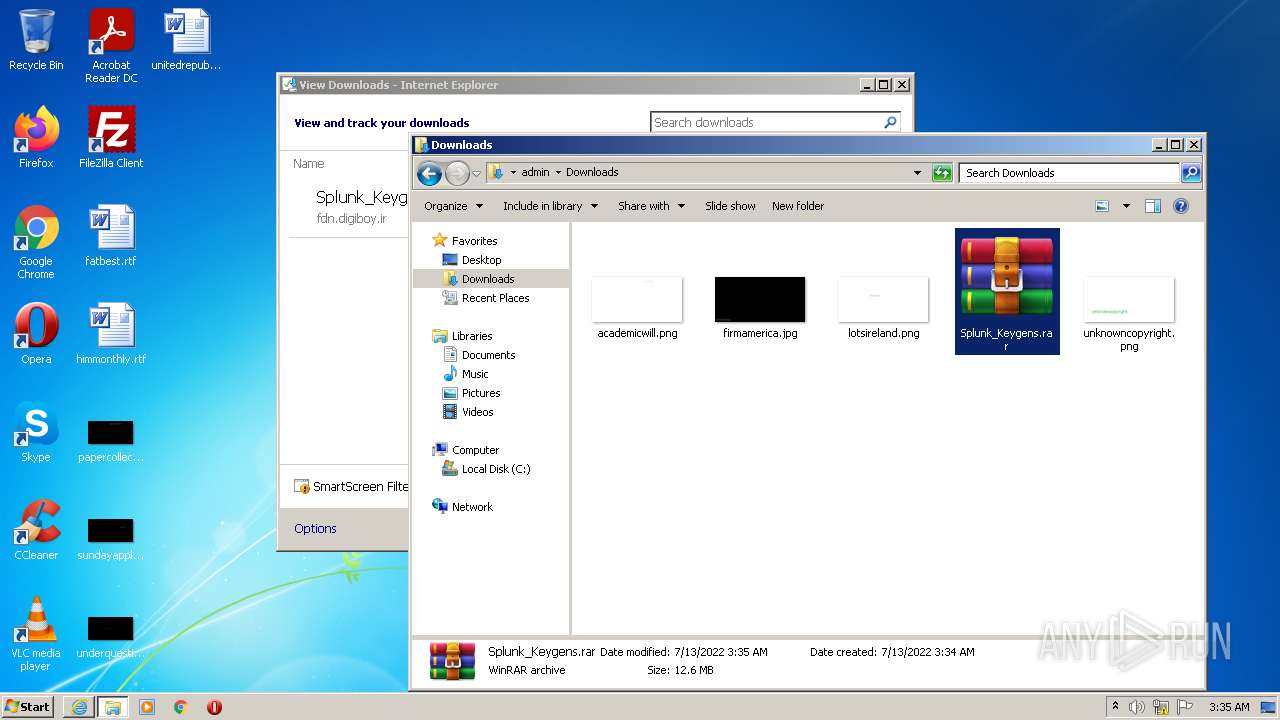
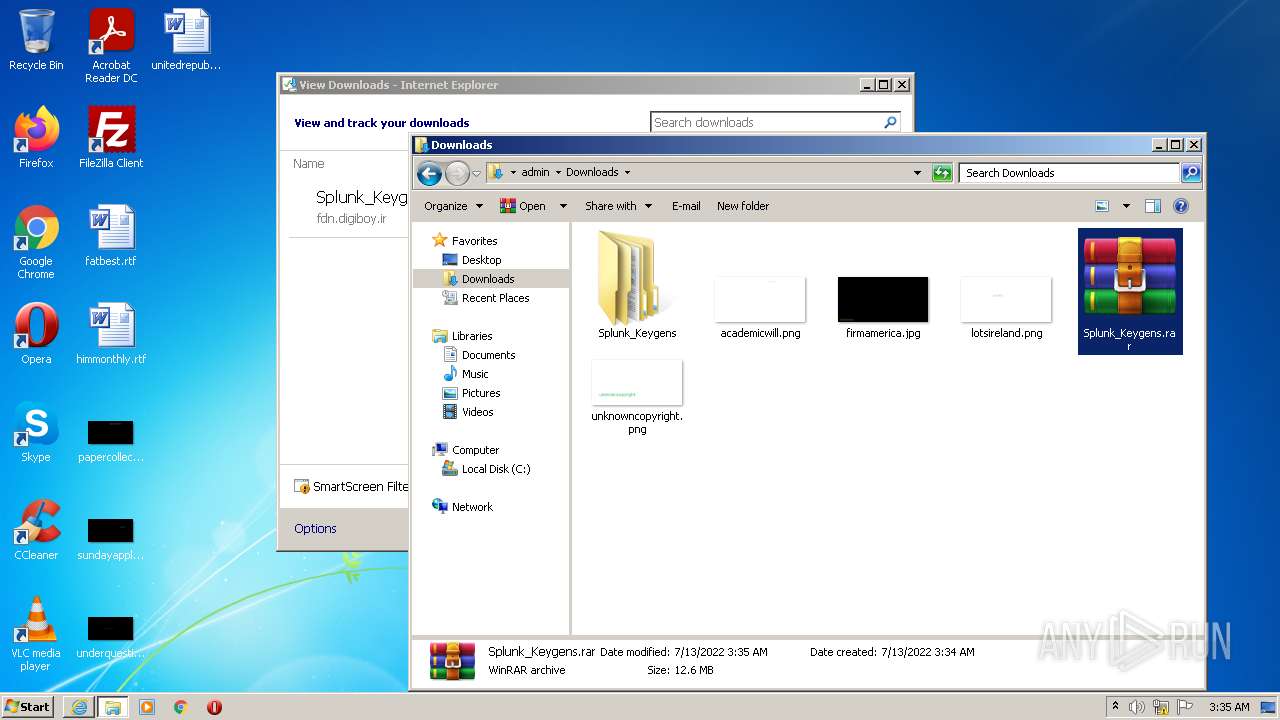
Manual execution by user
- explorer.exe (PID: 3700)
- WinRAR.exe (PID: 2936)
- dvt-splunk_licsrv.1.0.386.exe (PID: 3244)
Creates files in the user directory
- iexplore.exe (PID: 3096)
Changes settings of System certificates
- iexplore.exe (PID: 3096)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2784 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
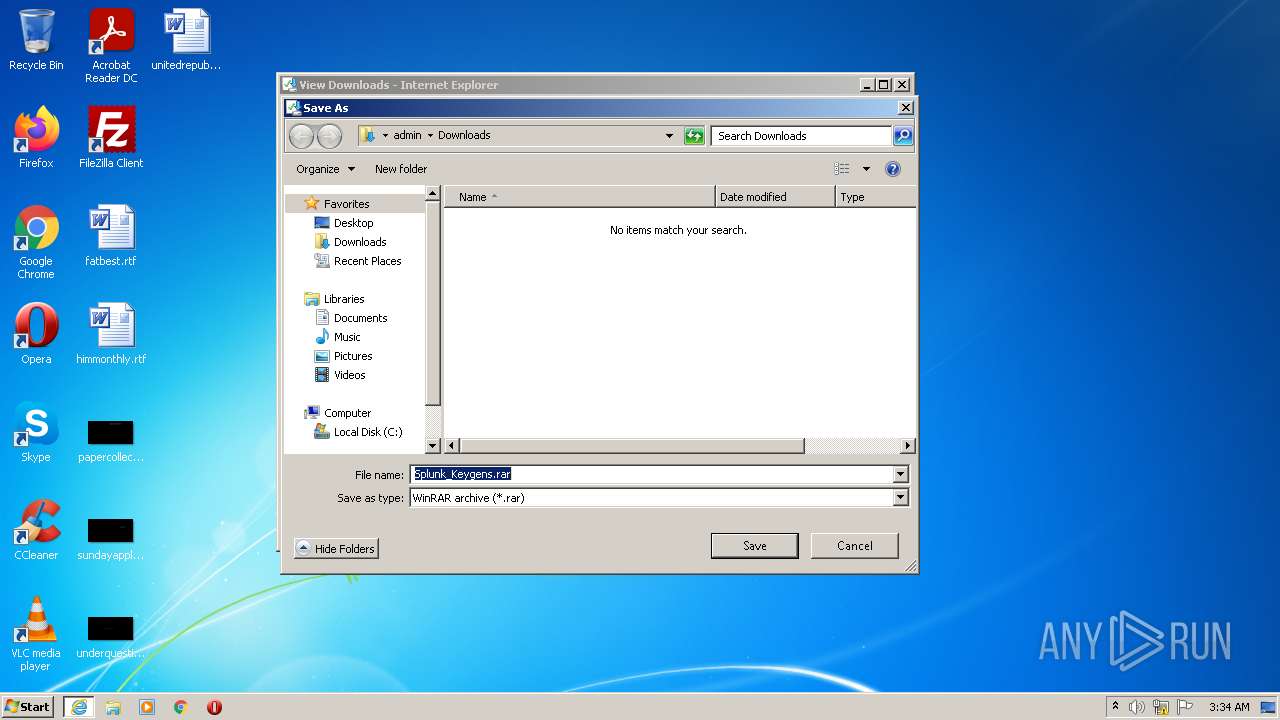
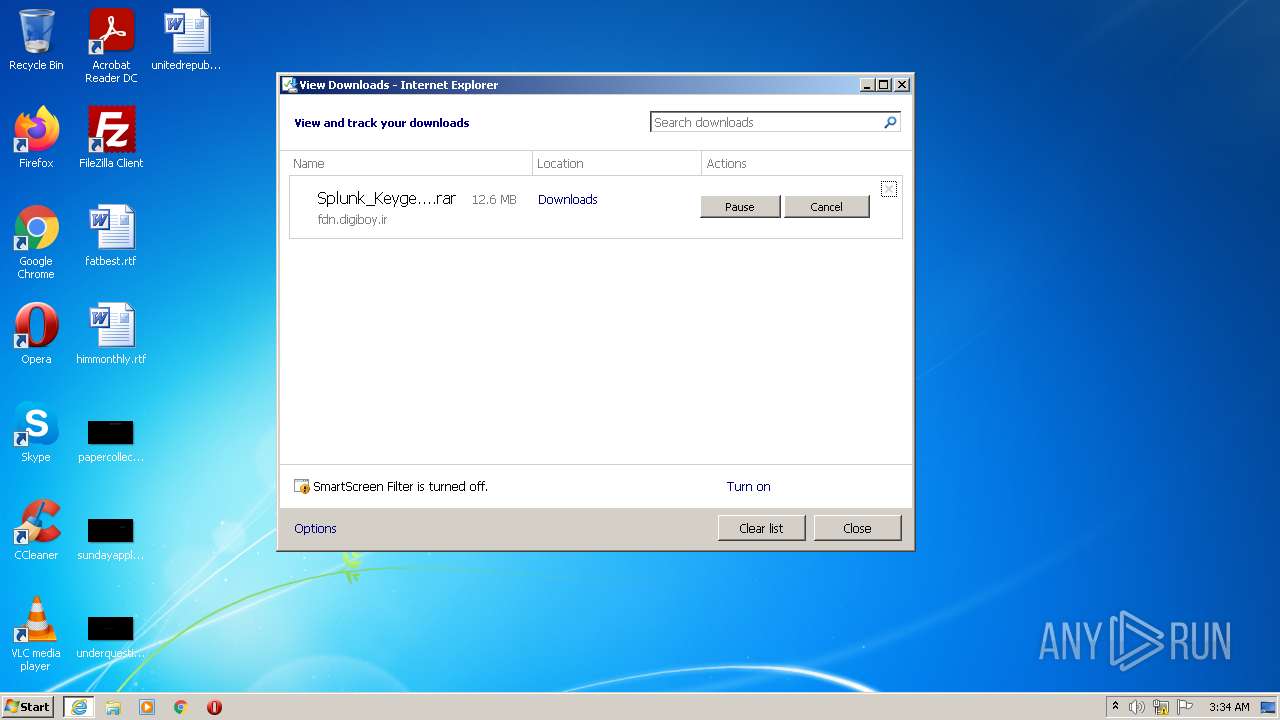
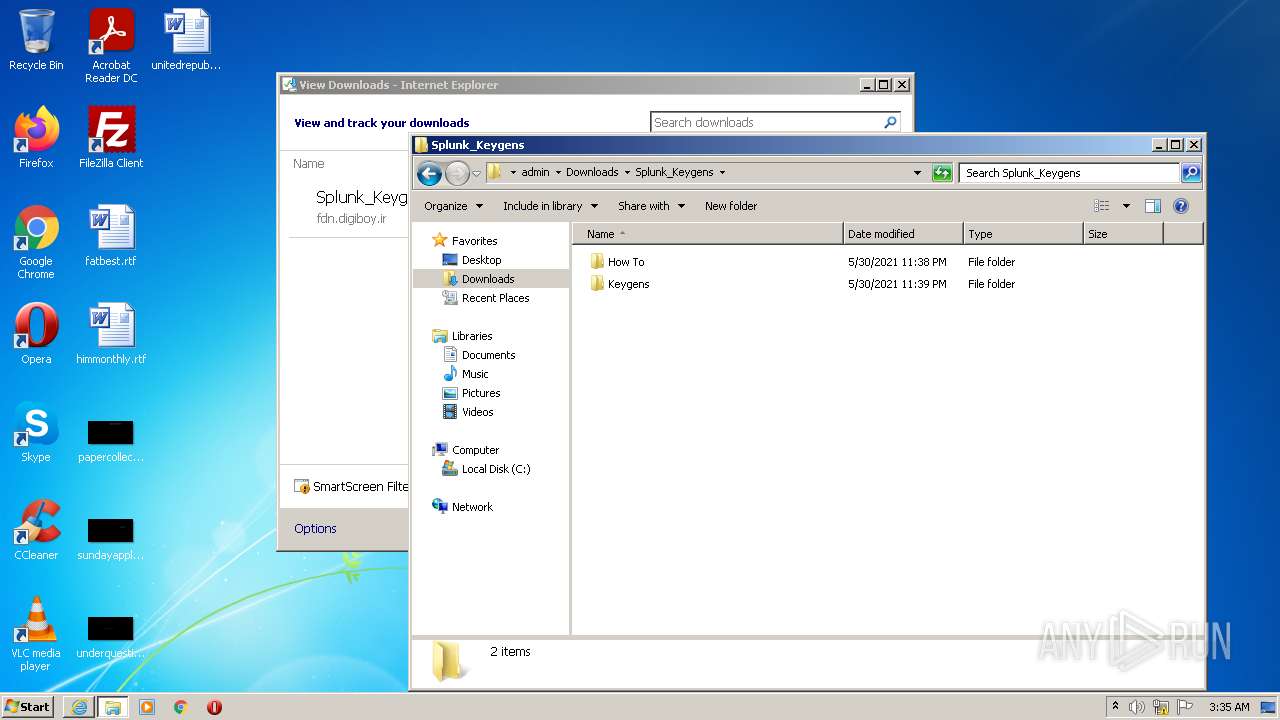
| 2936 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Splunk_Keygens.rar" C:\Users\admin\Downloads\Splunk_Keygens\ | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3096 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://fdn.digiboy.ir/dlir-s3/Splunk_Keygens.rar" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3244 | "C:\Users\admin\Downloads\Splunk_Keygens\Keygens\windows\dvt-splunk_licsrv.1.0.386.exe" | C:\Users\admin\Downloads\Splunk_Keygens\Keygens\windows\dvt-splunk_licsrv.1.0.386.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3492 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3096 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3700 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
16 263
Read events
16 095
Write events
164
Delete events
4
Modification events
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 227396256 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30971489 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 527398756 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30971489 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3096) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
13
Text files
23
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07DB822C3548410165E7DFA39F71BDE_9BFC800125F38451AB582976D3D9439B | der | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F07DB822C3548410165E7DFA39F71BDE_9BFC800125F38451AB582976D3D9439B | binary | |
MD5:— | SHA256:— | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3096 | iexplore.exe | C:\Users\admin\Downloads\Splunk_Keygens.rar | — | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\68FAF71AF355126BCA00CE2E73CC7374_123B8BA19C64CE9A8B3EAC32000FAF3E | binary | |
MD5:— | SHA256:— | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1F4BA66CDBFEC85A20E11BF729AF23_AA85F8F9DAFF33153B5AEC2E983B94B6 | der | |
MD5:— | SHA256:— | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF768A690CD87F4B02.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
31
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3492 | iexplore.exe | GET | 200 | 23.36.162.85:80 | http://dvcasha2.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNcCPjJ499lHmfPUvPsRjzr1YchwQU5TGtvzoRlvSDvFA81LeQm5Du3iUCEH4vKKFDC%2FiQnE2d3p7MkiE%3D | NL | der | 1.56 Kb | whitelisted |
3096 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
3492 | iexplore.exe | GET | 200 | 23.36.162.85:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | NL | der | 1.50 Kb | whitelisted |
3096 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3096 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3492 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0b6d6166d7faefa6 | US | compressed | 4.70 Kb | whitelisted |
3492 | iexplore.exe | GET | 200 | 23.36.162.85:80 | http://subca.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCECbd0itGycRNWmlNOYB%2Bcq0%3D | NL | der | 1.54 Kb | whitelisted |
3492 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3532958fcf14e750 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3096 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3492 | iexplore.exe | 23.36.162.85:80 | subca.ocsp-certum.com | CW Vodafone Group PLC | NL | suspicious |
3096 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3096 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3096 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
3096 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3096 | iexplore.exe | 104.92.93.19:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | unknown |
3096 | iexplore.exe | 20.25.53.147:443 | query.prod.cms.msn.com | — | US | unknown |
3492 | iexplore.exe | 5.144.134.6:443 | fdn.digiboy.ir | Noavaran Shabakeh Sabz Mehregan Company Limited | IR | unknown |
3492 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fdn.digiboy.ir |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
subca.ocsp-certum.com |
| whitelisted |
dvcasha2.ocsp-certum.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |