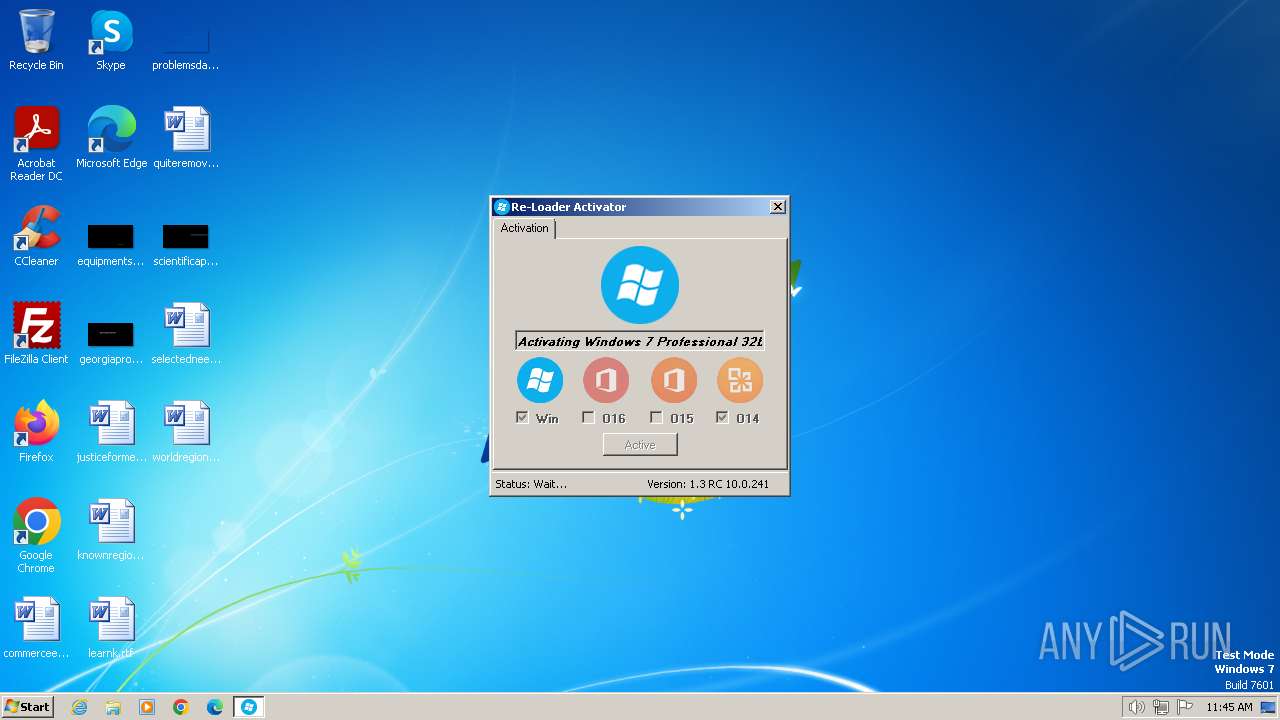
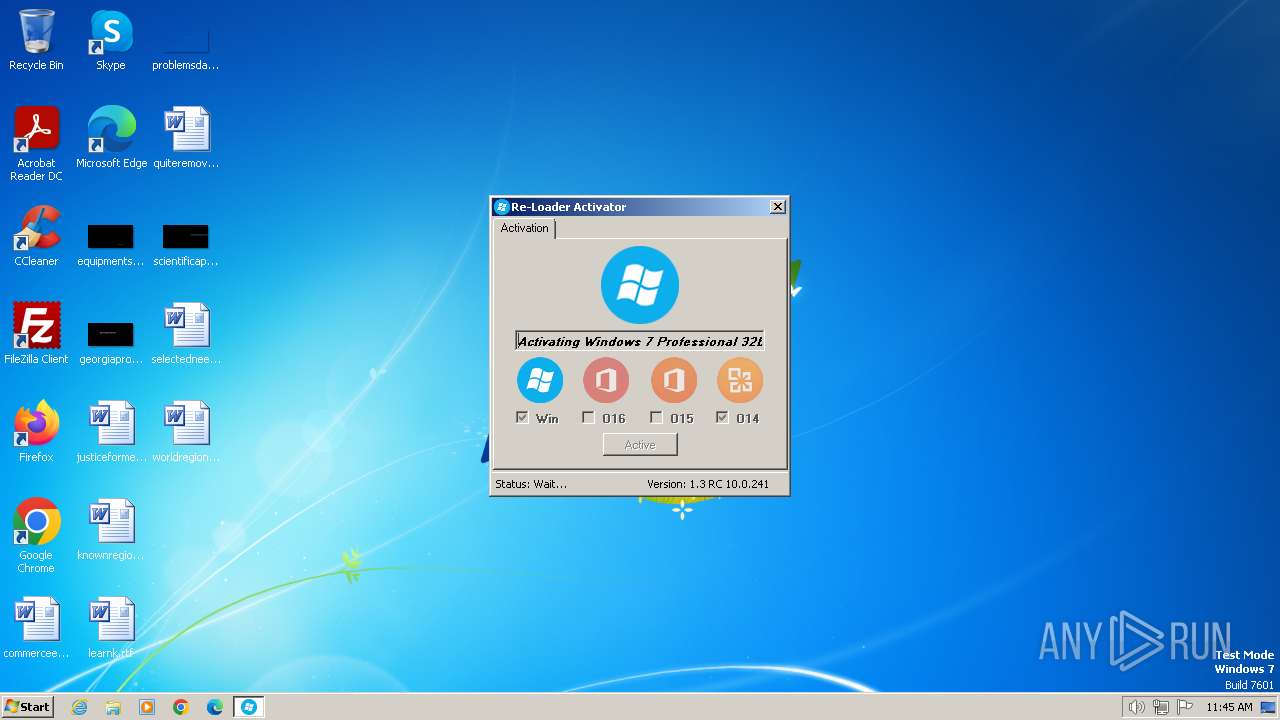
| File name: | Re-Loader.exe |
| Full analysis: | https://app.any.run/tasks/f7ab8876-1022-42f9-9c31-e9676c66dd64 |
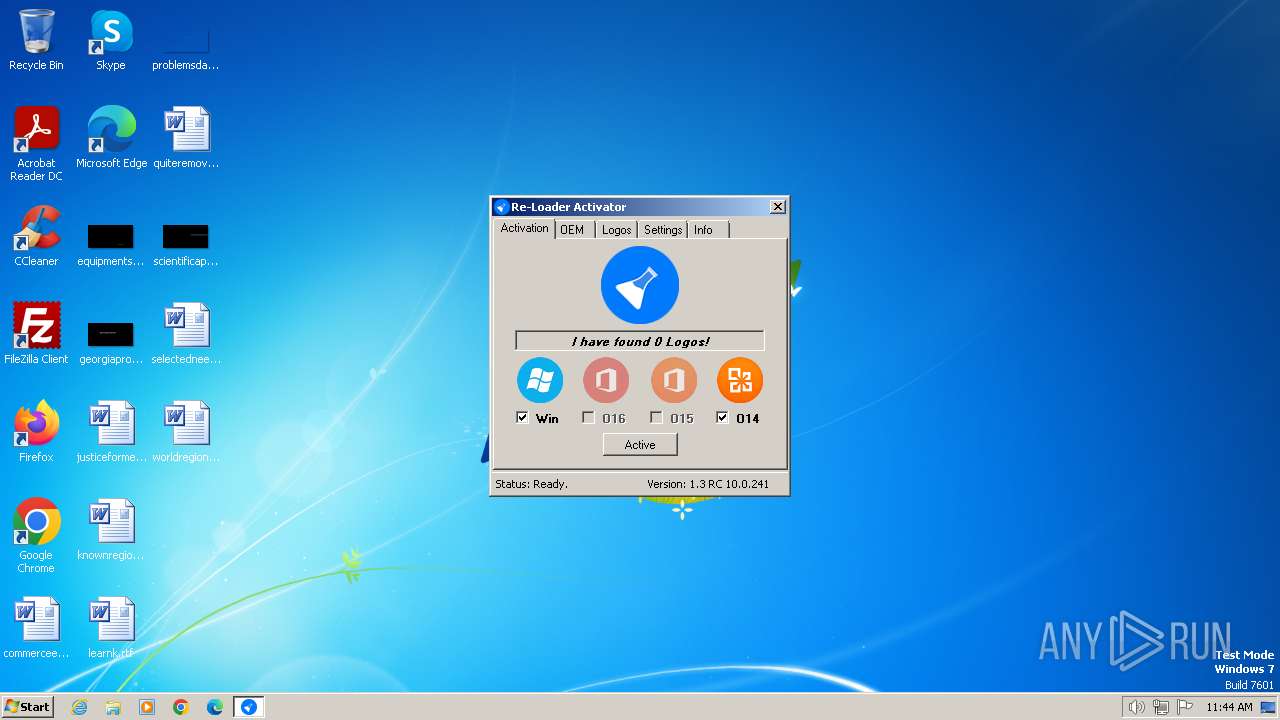
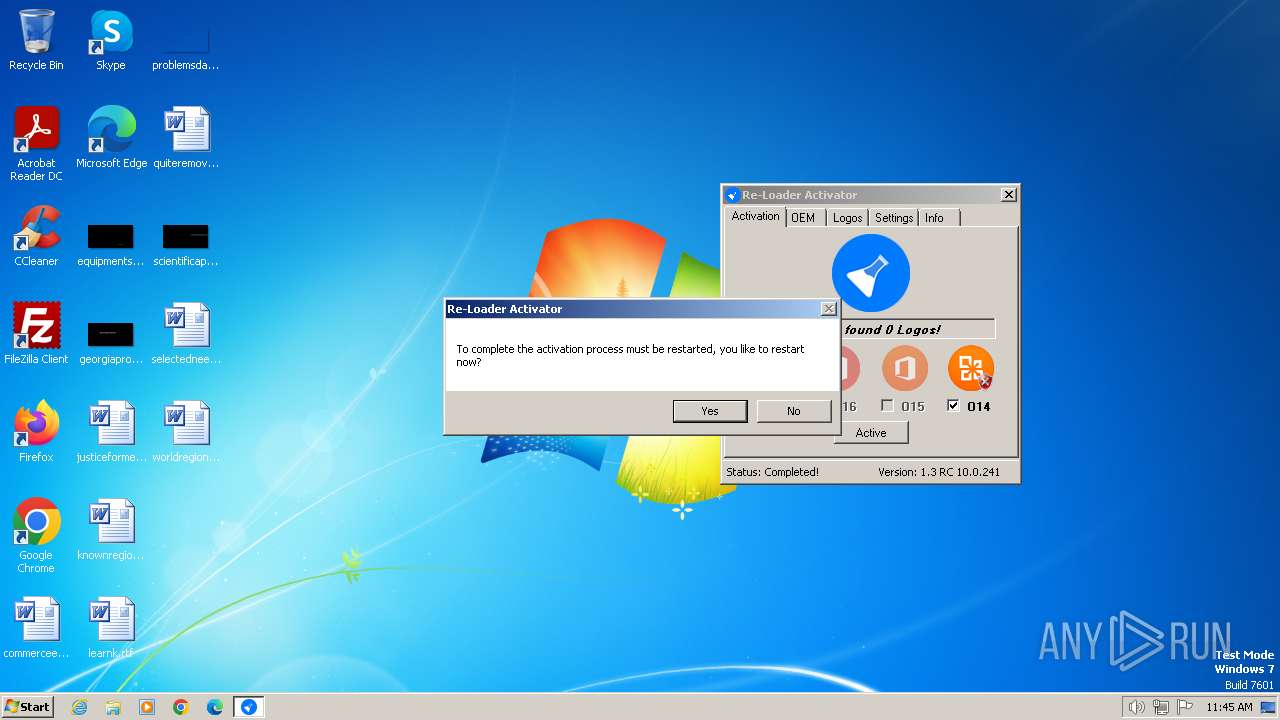
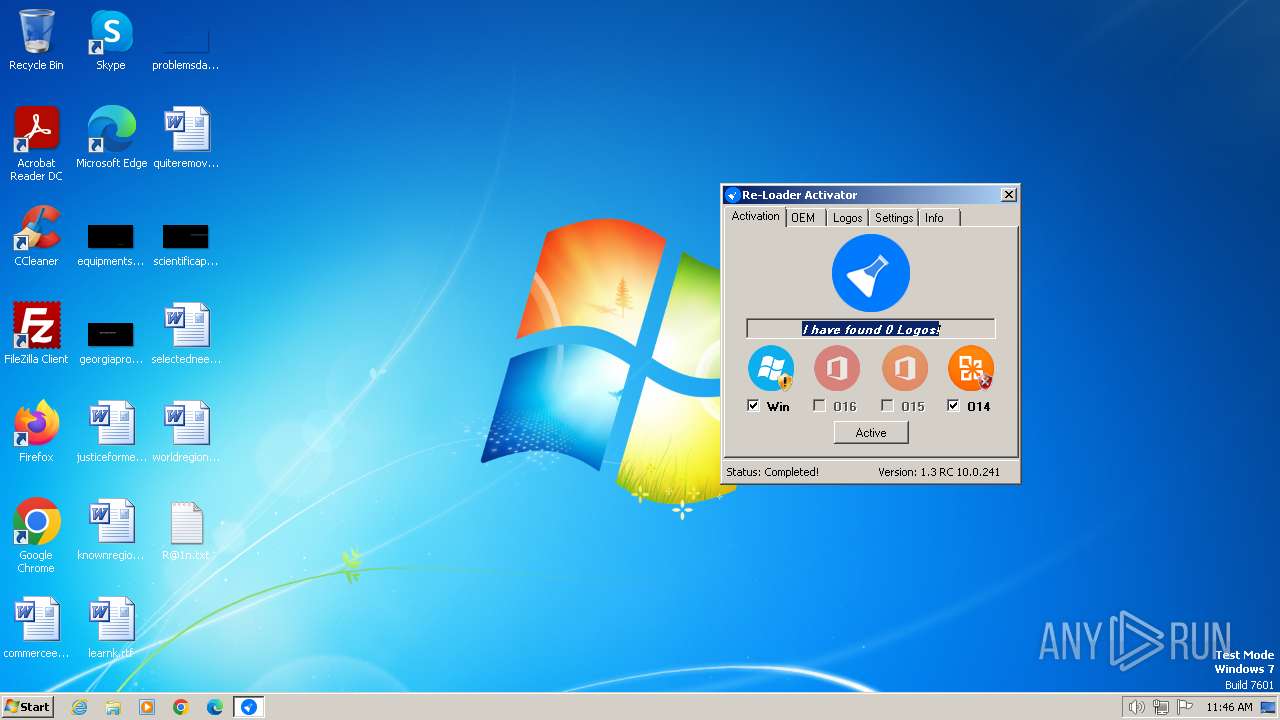
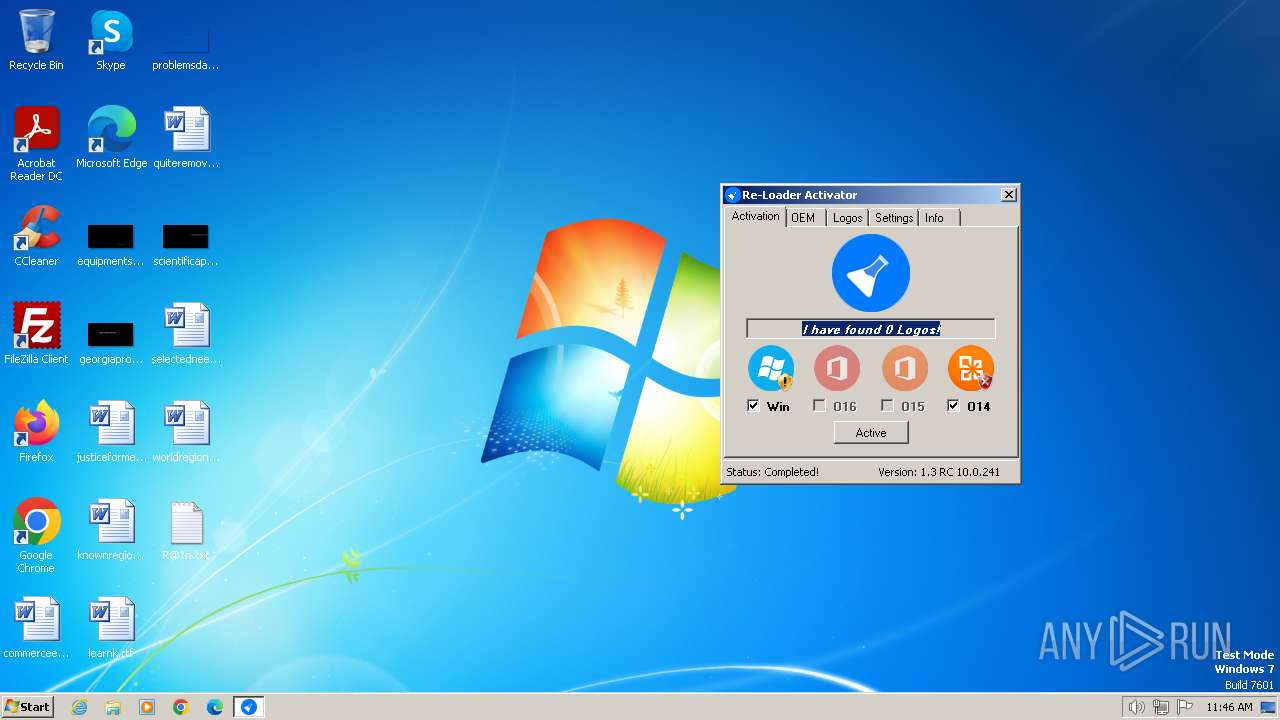
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2024, 11:44:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, MZ for MS-DOS |
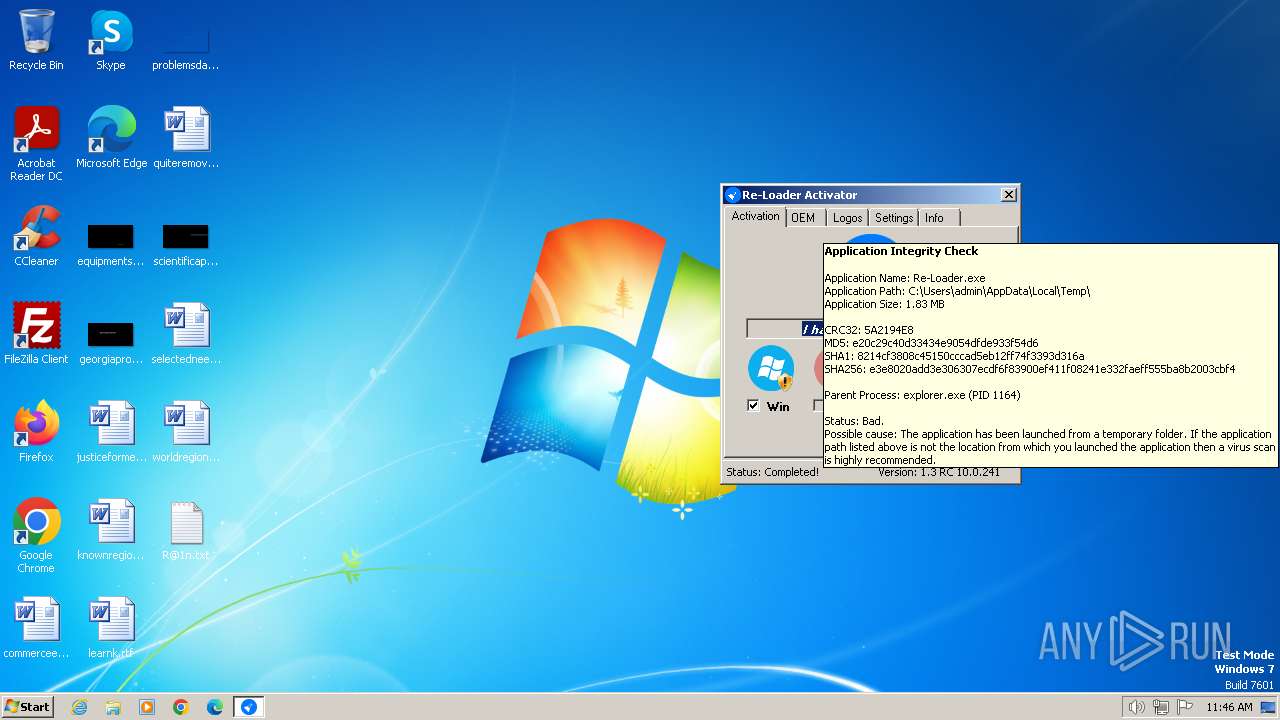
| MD5: | E20C29C40D33434E9054DFDE933F54D6 |
| SHA1: | 8214CF3808C45150CCCAD5EB12FF74F3393D316A |
| SHA256: | E3E8020ADD3E306307ECDF6F83900EF411F08241E332FAEFF555BA8B2003CBF4 |
| SSDEEP: | 98304:ndT5aCpbtKV8pjWNdhoYTekrLUspCjGT1IilEw78x84z3VSUaMcf8PauNzpLuRL2:Tp5 |
MALICIOUS
Drops the executable file immediately after the start
- Re-Loader.exe (PID: 2036)
SUSPICIOUS
Reads the Internet Settings
- Re-Loader.exe (PID: 2036)
Reads security settings of Internet Explorer
- Re-Loader.exe (PID: 2036)
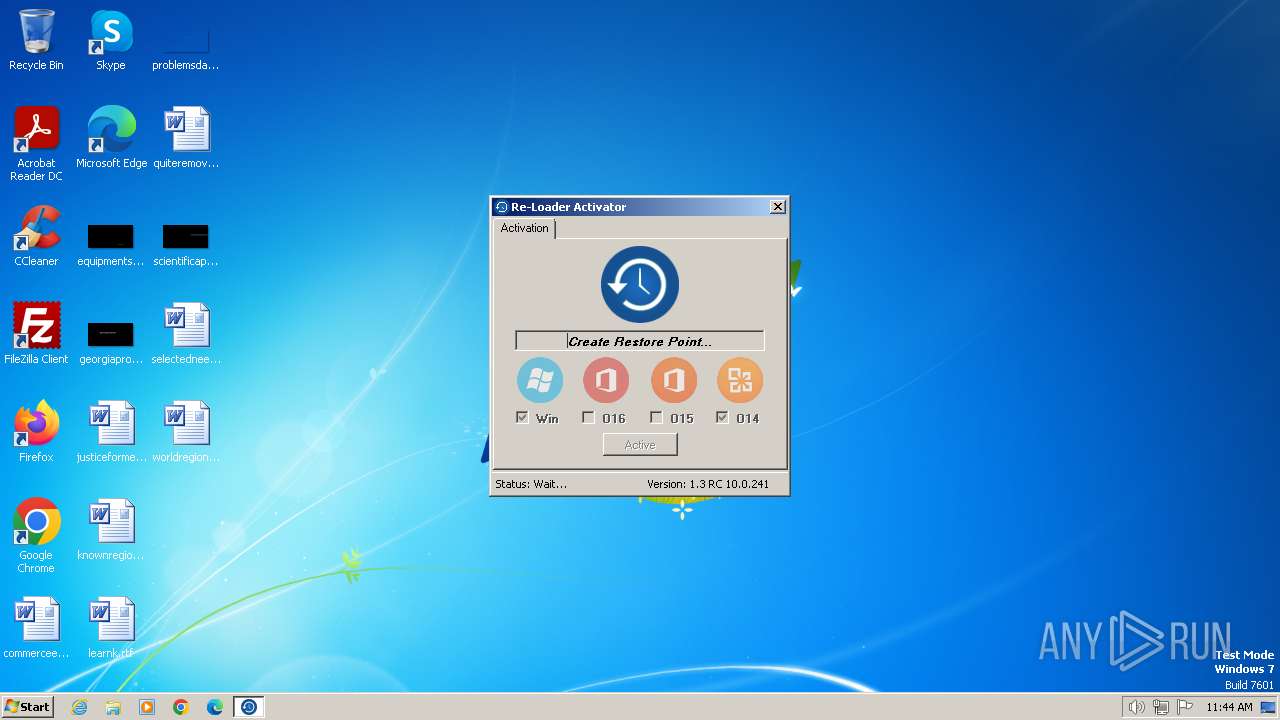
Executes as Windows Service
- VSSVC.exe (PID: 1972)
Searches for installed software
- dllhost.exe (PID: 956)
Executable content was dropped or overwritten
- Re-Loader.exe (PID: 2036)
Process drops legitimate windows executable
- Re-Loader.exe (PID: 2036)
Starts a Microsoft application from unusual location
- bootinst.exe (PID: 2728)
- bootinst.exe (PID: 1556)
Likely accesses (executes) a file from the Public directory
- notepad.exe (PID: 2020)
INFO
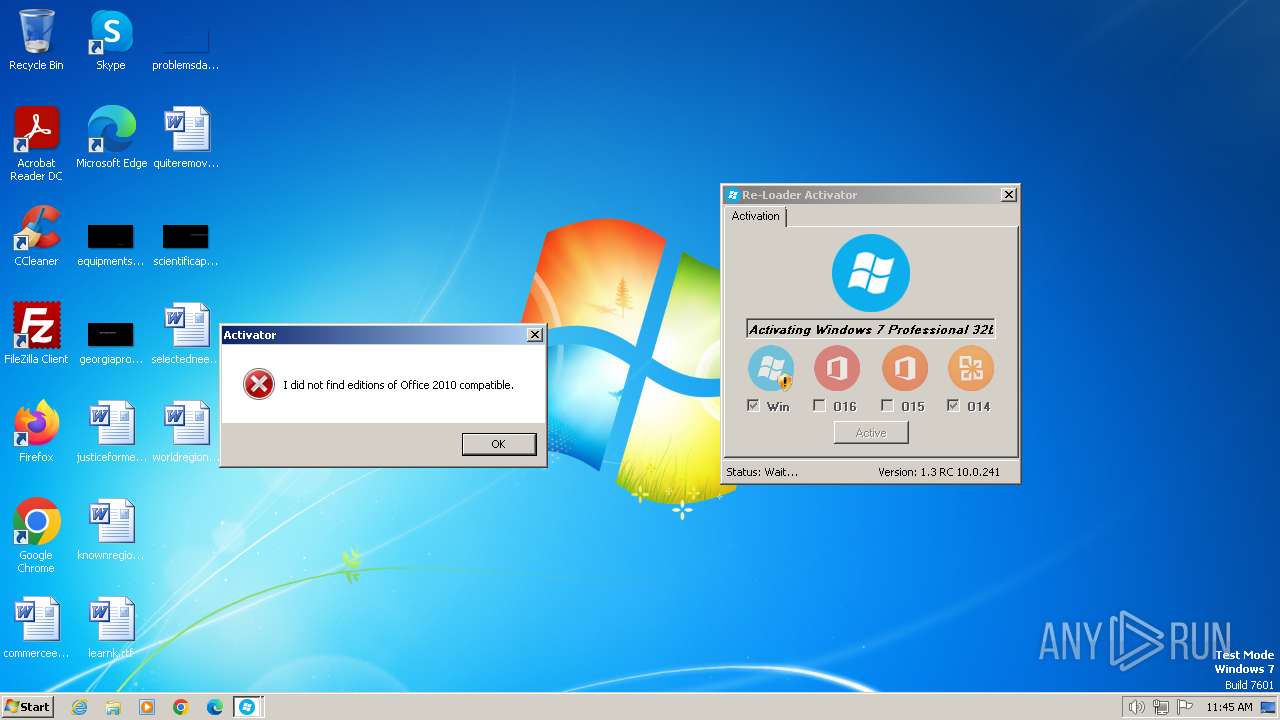
Reads Microsoft Office registry keys
- Re-Loader.exe (PID: 2036)
Reads the computer name
- Re-Loader.exe (PID: 2036)
Checks supported languages
- Re-Loader.exe (PID: 2036)
- bootinst.exe (PID: 2728)
- bootinst.exe (PID: 1556)
Reads the machine GUID from the registry
- Re-Loader.exe (PID: 2036)
Reads Environment values
- Re-Loader.exe (PID: 2036)
Create files in a temporary directory
- Re-Loader.exe (PID: 2036)
Reads product name
- Re-Loader.exe (PID: 2036)
Creates files or folders in the user directory
- Re-Loader.exe (PID: 2036)
Manual execution by a user
- notepad.exe (PID: 2020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:12:09 18:58:13+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 4096 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.2.10 |
| ProductVersionNumber: | 1.3.2.10 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
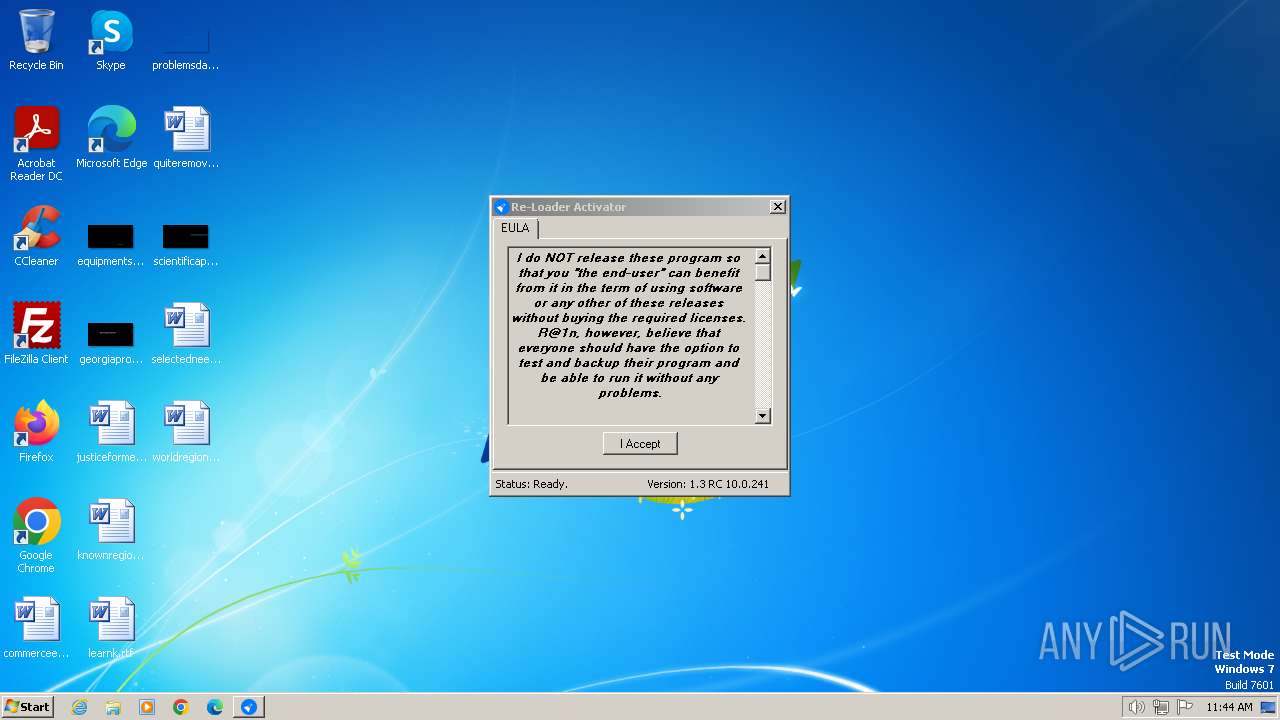
| FileDescription: | Activator |
| FileVersion: | 1.3.2.10 |
| InternalName: | Activator.exe |
| LegalCopyright: | Copyright © By R@1n 2015 |
| LegalTrademarks: | - |
| OriginalFileName: | Activator.exe |
| ProductName: | Re-Loader By R@1n |
| ProductVersion: | 1.3.2.10 |
| AssemblyVersion: | 1.3.2.10 |
Total processes
52
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1556 | "C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\boot\bootinst.exe" /nt60 SYS /force | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\boot\bootinst.exe | — | Re-Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Sector Manipulation Tool Exit code: 0 Version: 6.0.6001.18000 (longhorn_rtm.080118-1840) Modules
| |||||||||||||||
| 1972 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
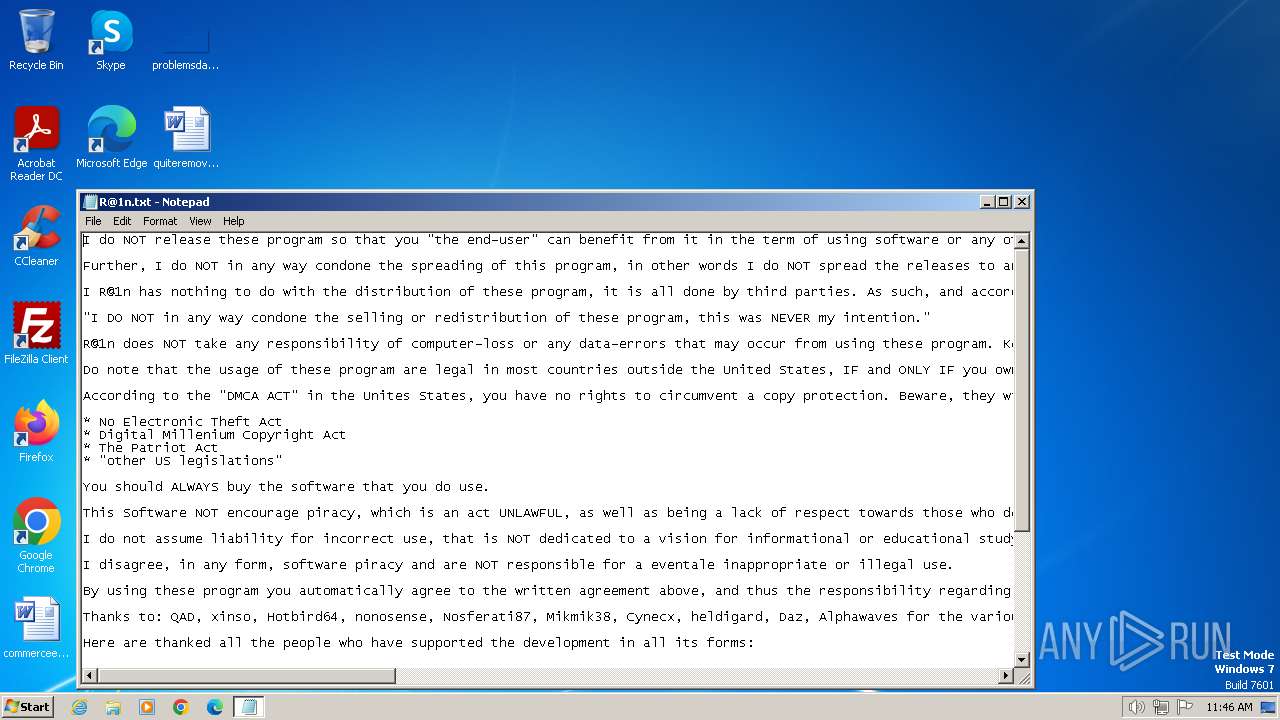
| 2020 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\Public\Desktop\R@1n.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2036 | "C:\Users\admin\AppData\Local\Temp\Re-Loader.exe" | C:\Users\admin\AppData\Local\Temp\Re-Loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Activator Exit code: 0 Version: 1.3.2.10 Modules
| |||||||||||||||
| 2728 | "C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\boot\bootinst.exe" /nt60 SYS /force | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\boot\bootinst.exe | — | Re-Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Sector Manipulation Tool Exit code: 0 Version: 6.0.6001.18000 (longhorn_rtm.080118-1840) Modules
| |||||||||||||||
| 3672 | "C:\Users\admin\AppData\Local\Temp\Re-Loader.exe" | C:\Users\admin\AppData\Local\Temp\Re-Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Activator Exit code: 3221226540 Version: 1.3.2.10 Modules
| |||||||||||||||
Total events
2 178
Read events
2 036
Write events
142
Delete events
0
Modification events
| (PID) Process: | (2036) Re-Loader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2036) Re-Loader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2036) Re-Loader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2036) Re-Loader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (956) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000020A818DF8470DA01BC030000D8050000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (956) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 75 | |||
| (PID) Process: | (956) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000F0BA2BDF8470DA01BC030000D8050000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (956) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000FEE132DF8470DA01BC0300008C0E0000E8030000010000000000000000000000B444F5DFBEB8594089212679314797AD0000000000000000 | |||
| (PID) Process: | (1972) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C0CD3EDF8470DA01B4070000800A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1972) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C0CD3EDF8470DA01B4070000EC020000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
4
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 956 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2728 | bootinst.exe | \Device\HarddiskVolume1 | — | |
MD5:— | SHA256:— | |||
| 1556 | bootinst.exe | \Device\HarddiskVolume1 | — | |
MD5:— | SHA256:— | |||
| 2036 | Re-Loader.exe | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\CustomSLIC\grldr | binary | |
MD5:4908E7A4441A380EF07E30D5F0AC48D1 | SHA256:D8A3ECD656EF4901CBEB822CDFB71A46D707331C60166DBF53DA2FFB2FBA1326 | |||
| 2036 | Re-Loader.exe | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\boot\bootinst.exe | executable | |
MD5:2C44C79619C51B4FA0E0B1F1982AC944 | SHA256:4E927F83F15FDFA810A65D83FC274AD016BFF7C60976A8F680B5EC2F96EC839C | |||
| 2036 | Re-Loader.exe | C:\Users\admin\AppData\Local\Temp\Re-Loader\DEFAULT.XRM-MS | xml | |
MD5:18B1E45BF56F40C3C4BBE65831178216 | SHA256:D072A059D3ED3E75C98B85B41E4319E8D5CFAE0E0C239B62436A3AD34003AB4A | |||
| 2036 | Re-Loader.exe | C:\Users\admin\AppData\Local\mpress\Re-Loader.exe_Url_nznajbrvfzvkyhckvf4h15egvndzrf0b\1.3.2.10\bqnug01i.newcfg | xml | |
MD5:9DAA433406ACF472F1448EF7A81FA023 | SHA256:51BF902526D075A8893133436271FD430C8EC83A51AF3045F33CCE8C47EE7EF2 | |||
| 2036 | Re-Loader.exe | C:\Users\admin\AppData\Local\mpress\Re-Loader.exe_Url_nznajbrvfzvkyhckvf4h15egvndzrf0b\1.3.2.10\user.config | xml | |
MD5:9DAA433406ACF472F1448EF7A81FA023 | SHA256:51BF902526D075A8893133436271FD430C8EC83A51AF3045F33CCE8C47EE7EF2 | |||
| 2036 | Re-Loader.exe | C:\Users\Public\Desktop\R@1n.txt | text | |
MD5:6C202CC547CD5327F5BEE652B20D734B | SHA256:21A853B1CF1962DA8056CDFA9651D340D1F1212083B687EC42F623F8590C6FF4 | |||
| 2036 | Re-Loader.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963}\grldr | binary | |
MD5:FF4D5B0E83F7902816D6381B543E10A7 | SHA256:DF3219C575A4063A4C50799B9B761E58129A33A443904DDAD527C0E72A380757 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |