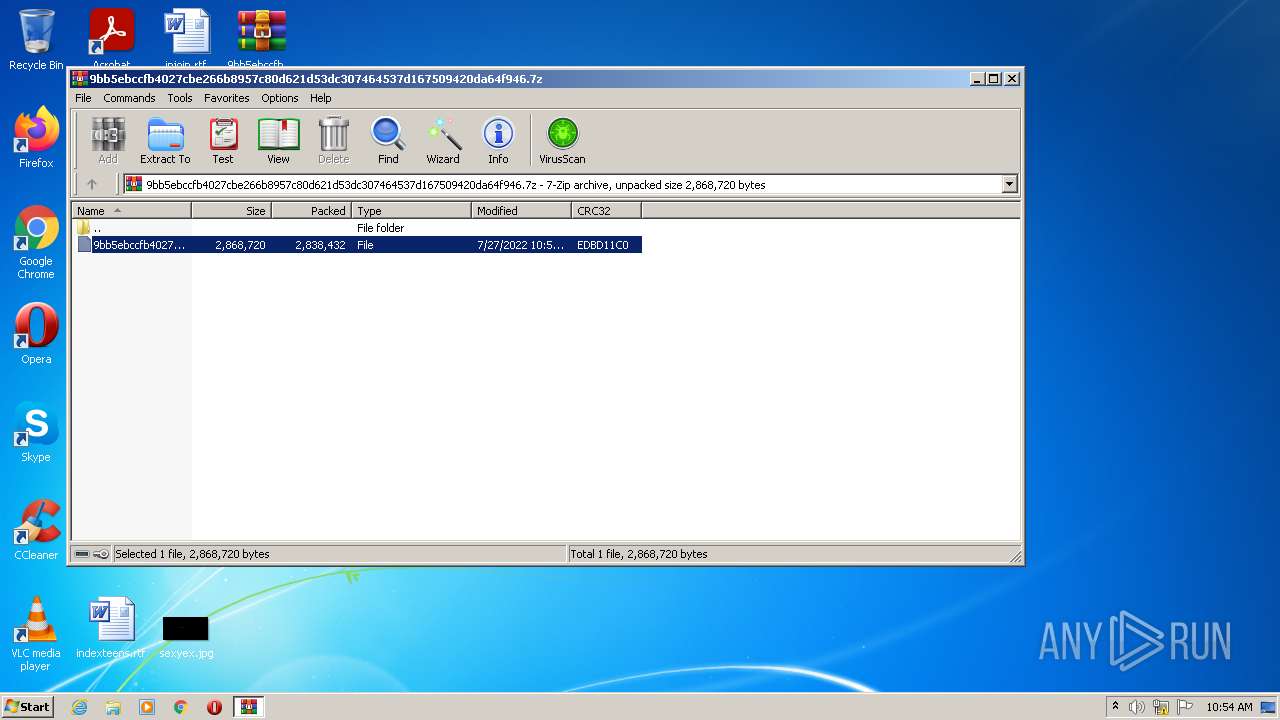
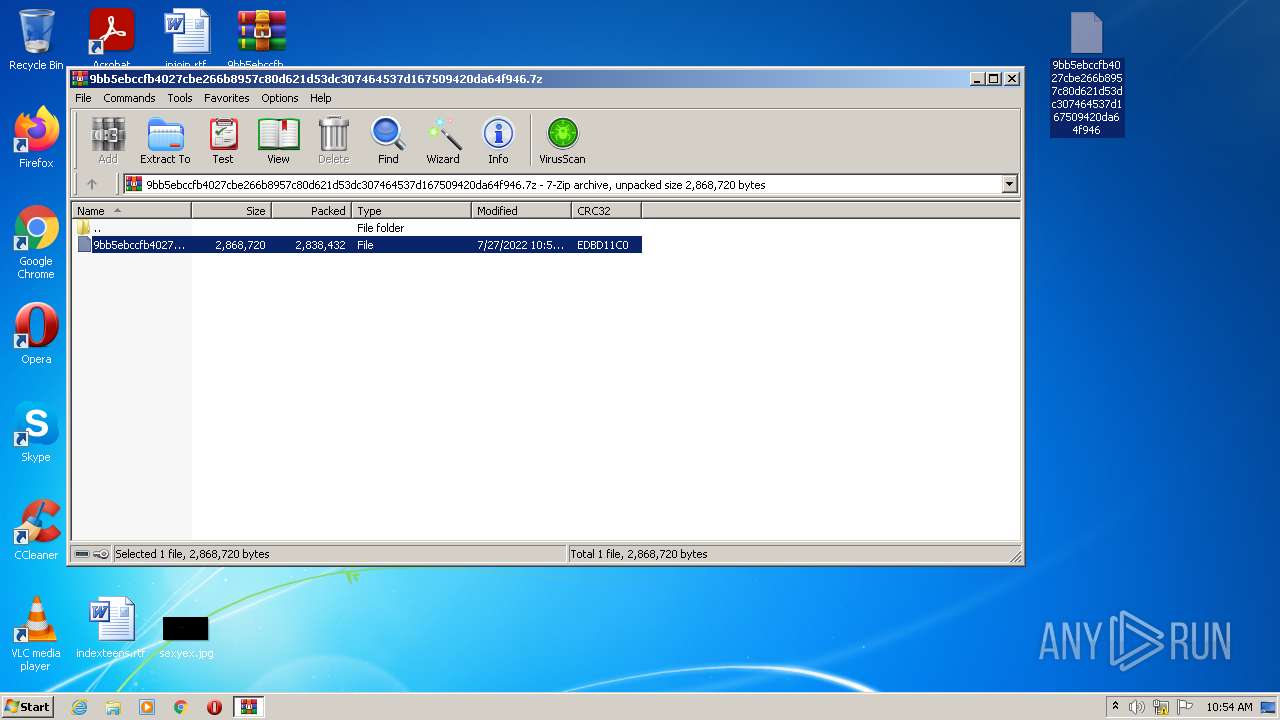
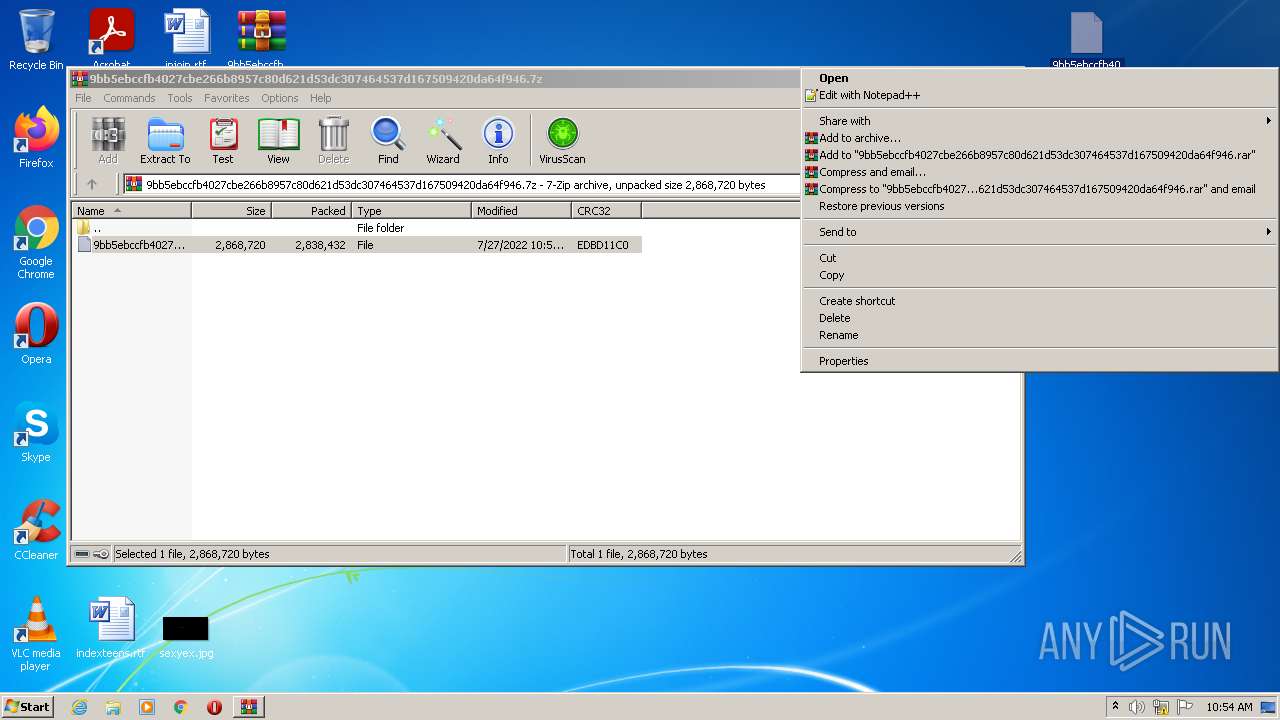
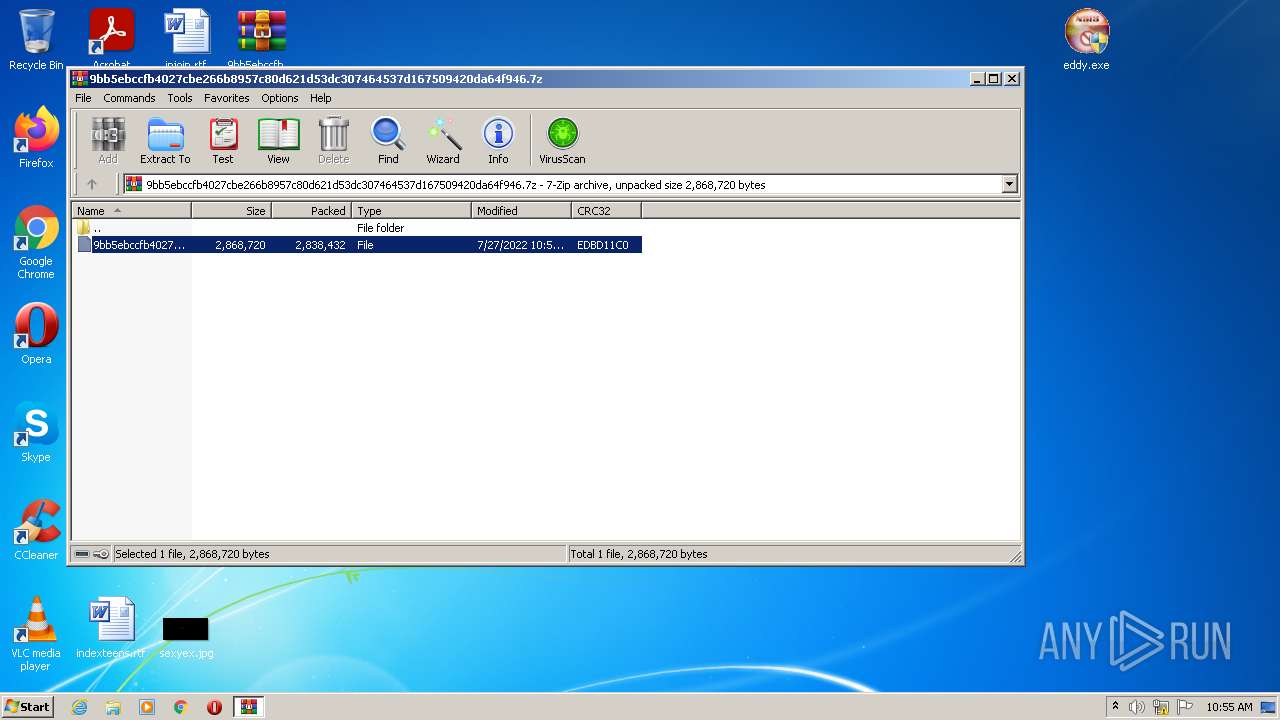
| File name: | 9bb5ebccfb4027cbe266b8957c80d621d53dc307464537d167509420da64f946.7z |
| Full analysis: | https://app.any.run/tasks/6f4f3202-5602-4443-ae62-eb01cbac650b |
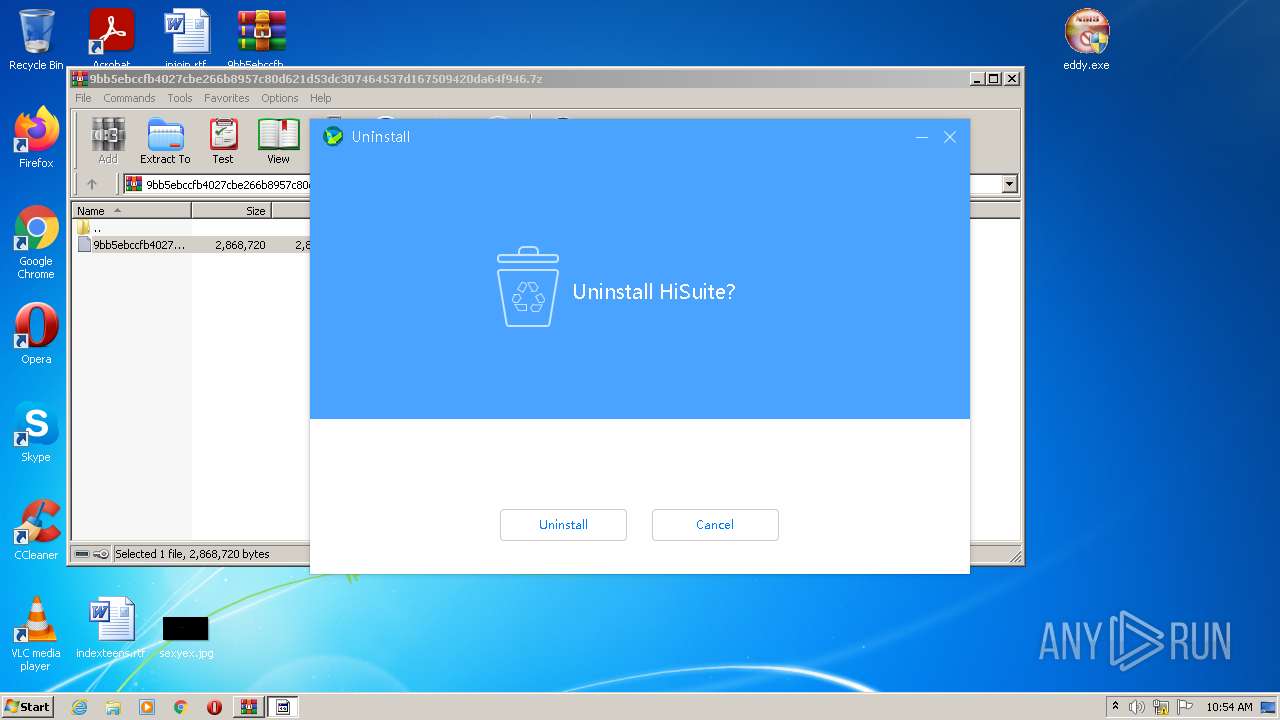
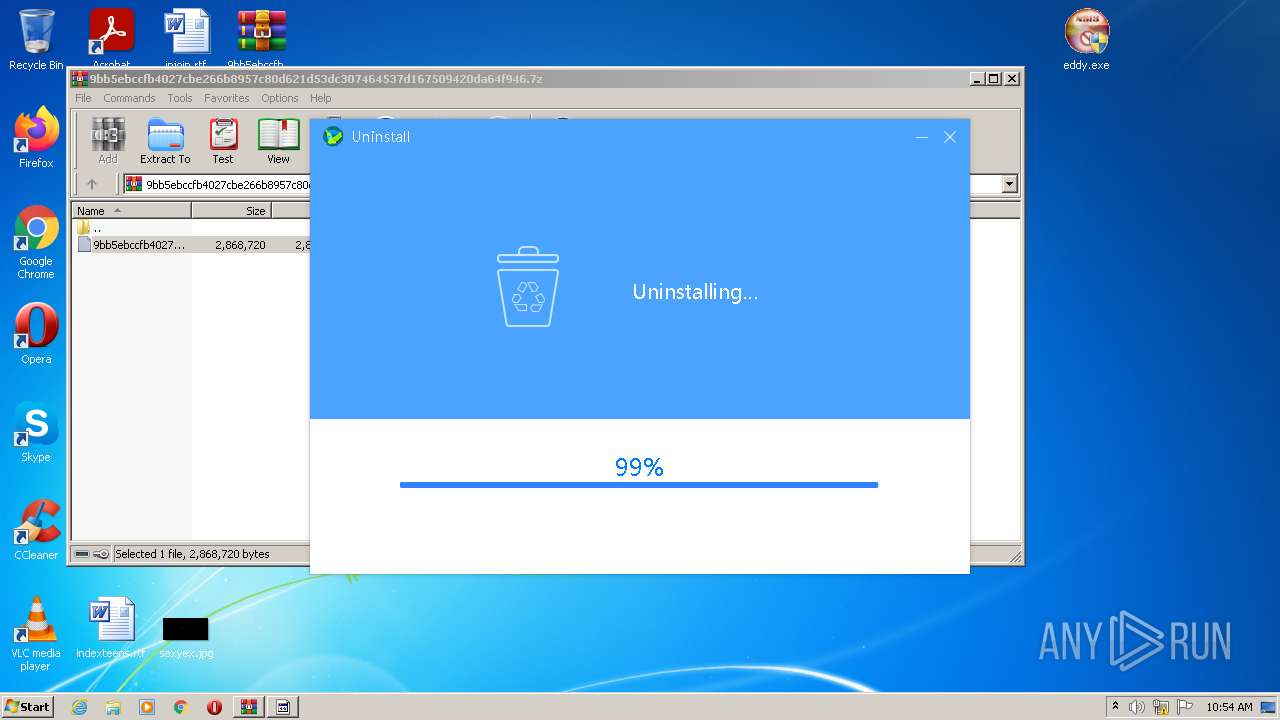
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2022, 09:54:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 6E687E428139C9F38BDA1B61340F7D46 |
| SHA1: | 47283BAFFC31D238D2C840A71E1A10EE88944A90 |
| SHA256: | E3DBE4C8429F7E603C2A6199190498B543D9FBDB6BF41E3ABE3449E74FFD5A00 |
| SSDEEP: | 49152:r780WiVFurYRQLu2I596y70pi3zdxHa09xkrhz9sD/CqJz4NBnkhw6:rgp3YRkuv6y70czvHrLAc7cIl |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 3396)
- eddy.exe (PID: 1744)
- Un_A.exe (PID: 3196)
Application was dropped or rewritten from another process
- eddy.exe (PID: 2896)
- eddy.exe (PID: 1744)
- Un_A.exe (PID: 3196)
Loads dropped or rewritten executable
- Un_A.exe (PID: 3196)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 3396)
- eddy.exe (PID: 1744)
- Un_A.exe (PID: 3196)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3396)
- eddy.exe (PID: 1744)
- Un_A.exe (PID: 3196)
Checks supported languages
- WinRAR.exe (PID: 3396)
- eddy.exe (PID: 1744)
- Un_A.exe (PID: 3196)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3396)
- eddy.exe (PID: 1744)
- Un_A.exe (PID: 3196)
Starts itself from another location
- eddy.exe (PID: 1744)
Reads Environment values
- Un_A.exe (PID: 3196)
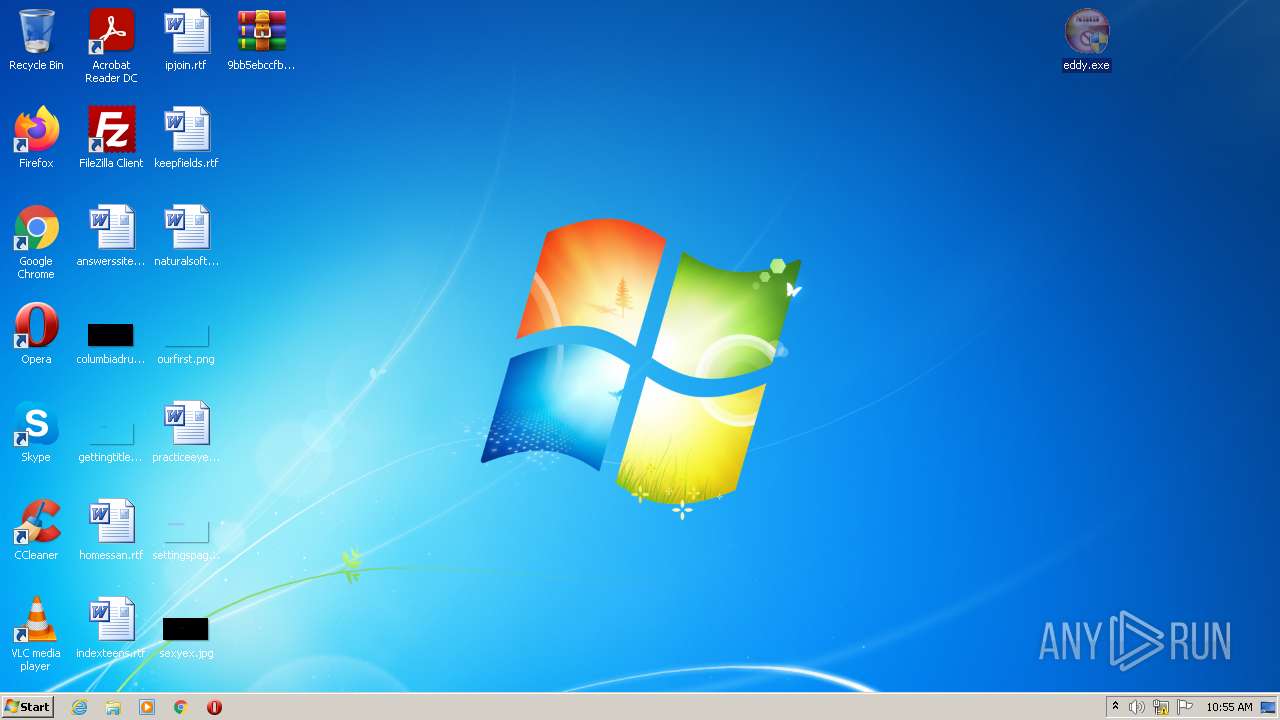
INFO
Manual execution by user
- eddy.exe (PID: 2896)
- eddy.exe (PID: 1744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
43
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1744 | "C:\Users\admin\Desktop\eddy.exe" | C:\Users\admin\Desktop\eddy.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2896 | "C:\Users\admin\Desktop\eddy.exe" | C:\Users\admin\Desktop\eddy.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3196 | "C:\Users\admin\AppData\Local\Temp\~nsuA.tmp\Un_A.exe" _?=C:\Users\admin\Desktop\ | C:\Users\admin\AppData\Local\Temp\~nsuA.tmp\Un_A.exe | eddy.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
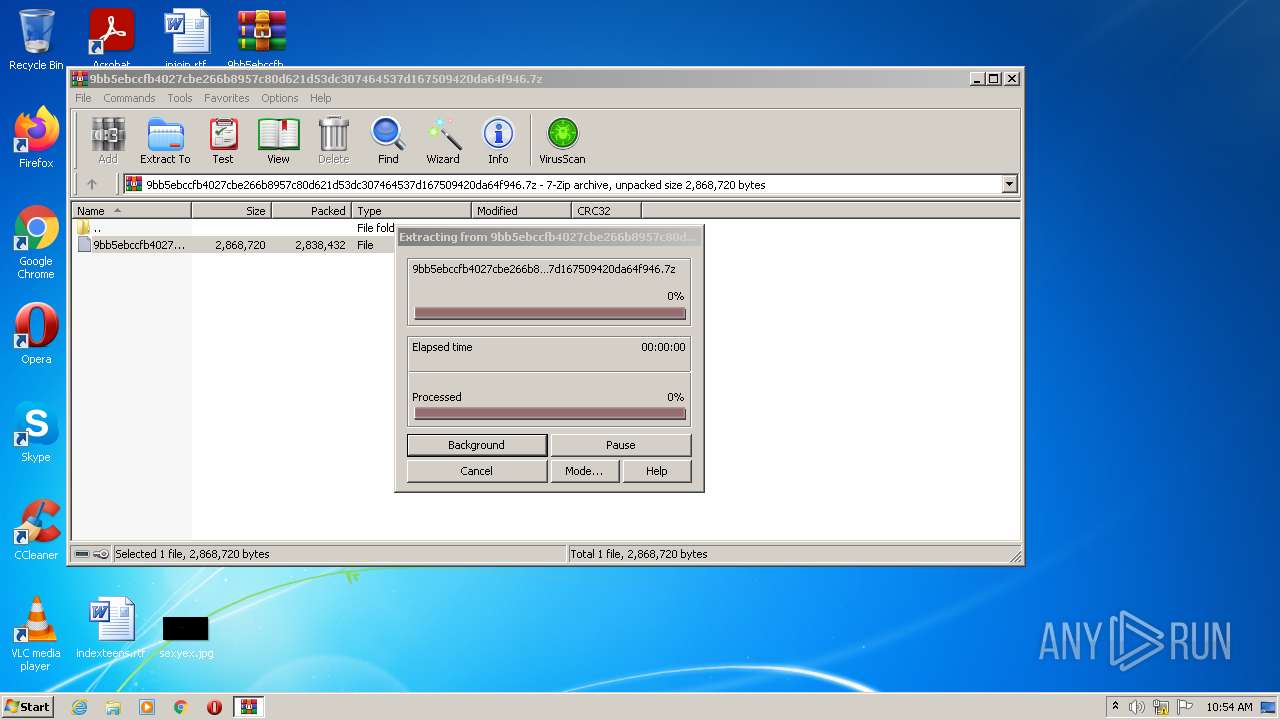
| 3396 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\9bb5ebccfb4027cbe266b8957c80d621d53dc307464537d167509420da64f946.7z" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
1 539
Read events
1 494
Write events
45
Delete events
0
Modification events
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\9bb5ebccfb4027cbe266b8957c80d621d53dc307464537d167509420da64f946.7z | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
56
Suspicious files
0
Text files
182
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
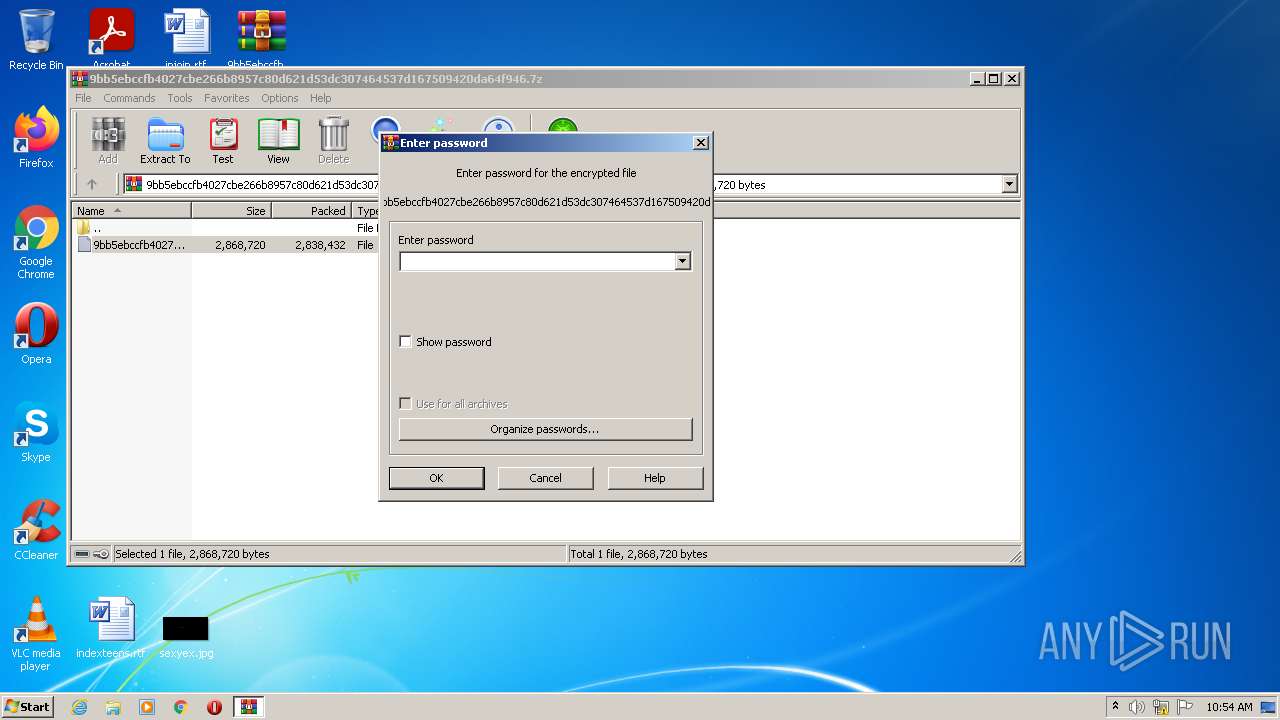
| 3396 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3396.33376\9bb5ebccfb4027cbe266b8957c80d621d53dc307464537d167509420da64f946 | executable | |
MD5:— | SHA256:— | |||
| 1744 | eddy.exe | C:\Users\admin\AppData\Local\Temp\nsx9C06.tmp | obj | |
MD5:— | SHA256:— | |||
| 1744 | eddy.exe | C:\Users\admin\AppData\Local\Temp\~nsuA.tmp\Un_A.exe | executable | |
MD5:— | SHA256:— | |||
| 3196 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nss9CD2.tmp\api_ms_win_core_file_l1_2_0.dll | executable | |
MD5:907384847A4E3002C9C9D621CABF2508 | SHA256:F144D246F27EEE4EC942B6CCFAE54C261B2D60E311D7F6C145A0E49CAF402FC6 | |||
| 3196 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nss9CD2.tmp\api_ms_win_core_console_l1_1_0.dll | executable | |
MD5:316B785B14A36AE34FBE8DFBE0C43944 | SHA256:622D879D3F03CF36FAEBFF42195674F540C30C36AD496C3B77F6C89C651D4448 | |||
| 3196 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nss9CD2.tmp\System.dll | executable | |
MD5:564BB0373067E1785CBA7E4C24AAB4BF | SHA256:7A9DDEE34562CD3703F1502B5C70E99CD5BBA15DE2B6845A3555033D7F6CB2A5 | |||
| 3196 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nss9CD2.tmp\api_ms_win_core_debug_l1_1_0.dll | executable | |
MD5:B16EDD687D38AF6921D0F3872E7C5915 | SHA256:6DA76FF6D4D97C6DB5897FF9FC5FC30D4F2FD9D917A39792C4A7231816F8C08E | |||
| 3196 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nss9CD2.tmp\api_ms_win_core_errorhandling_l1_1_0.dll | executable | |
MD5:53CA7B998409BFC859301F816B7FBD6E | SHA256:7E4130CBFBAF8E3C126535B91764C4EBA5250AC5E517F2EB6B04C366BBDE1DC6 | |||
| 3196 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nss9CD2.tmp\api_ms_win_core_file_l2_1_0.dll | executable | |
MD5:0A140E3610D15EA1B408266DD54331F2 | SHA256:B8AE54D4CC2848E26BEB5C03901AB5097D273D2144B0A0CCA24517E4BBBBF78A | |||
| 3196 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nss9CD2.tmp\api_ms_win_core_handle_l1_1_0.dll | executable | |
MD5:E670B5CC9DC3C4E74DD7033F83E1080B | SHA256:B06ED70AEA63630A0E2E09E3F6C1750ADAD3674426A30CE00D4751786C744250 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report