| File name: | YandexPackSetup.exe |
| Full analysis: | https://app.any.run/tasks/17e465f5-f4cc-4d28-ab60-f7a302e97c1c |
| Verdict: | Malicious activity |
| Analysis date: | August 03, 2020, 17:38:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B7D0B4FC8380567A0327D2FFE40005F1 |
| SHA1: | 63CE50778CF2C2A7AF9B26175DE0CE52264F3680 |
| SHA256: | E3DA1762FBC858737D343FC8F94C3E5669AB2CAF16CBBFC7A91D683EF13F5E34 |
| SSDEEP: | 196608:ezzoF/uD9jckrCFsu3iqo/U0/YIBjWrqufezvnUH:eHOeCz0/YojW2uGz/UH |
MALICIOUS
Application was dropped or rewritten from another process
- lite_installer.exe (PID: 1420)
- seederexe.exe (PID: 3388)
- sender.exe (PID: 2160)
Actions looks like stealing of personal data
- seederexe.exe (PID: 3388)
- lite_installer.exe (PID: 1420)
SUSPICIOUS
Reads Environment values
- MsiExec.exe (PID: 316)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1756)
- MsiExec.exe (PID: 316)
Creates files in the user directory
- seederexe.exe (PID: 3388)
INFO
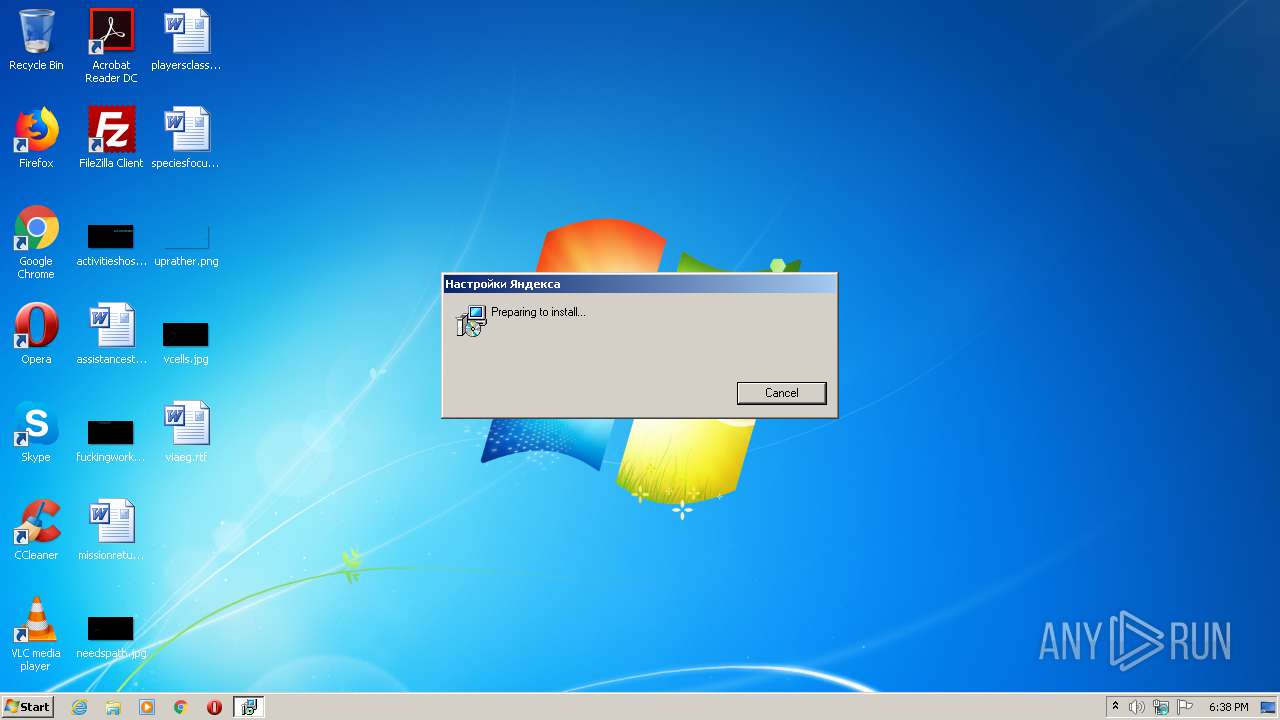
Application launched itself
- msiexec.exe (PID: 1756)
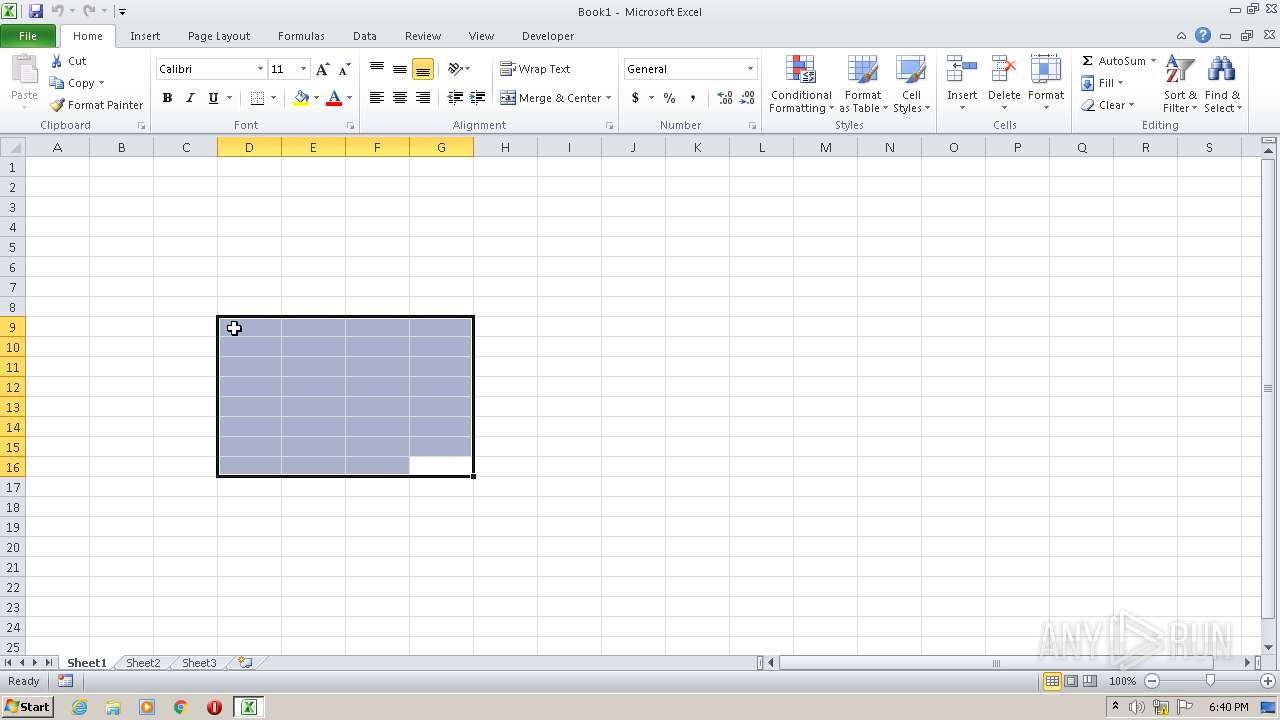
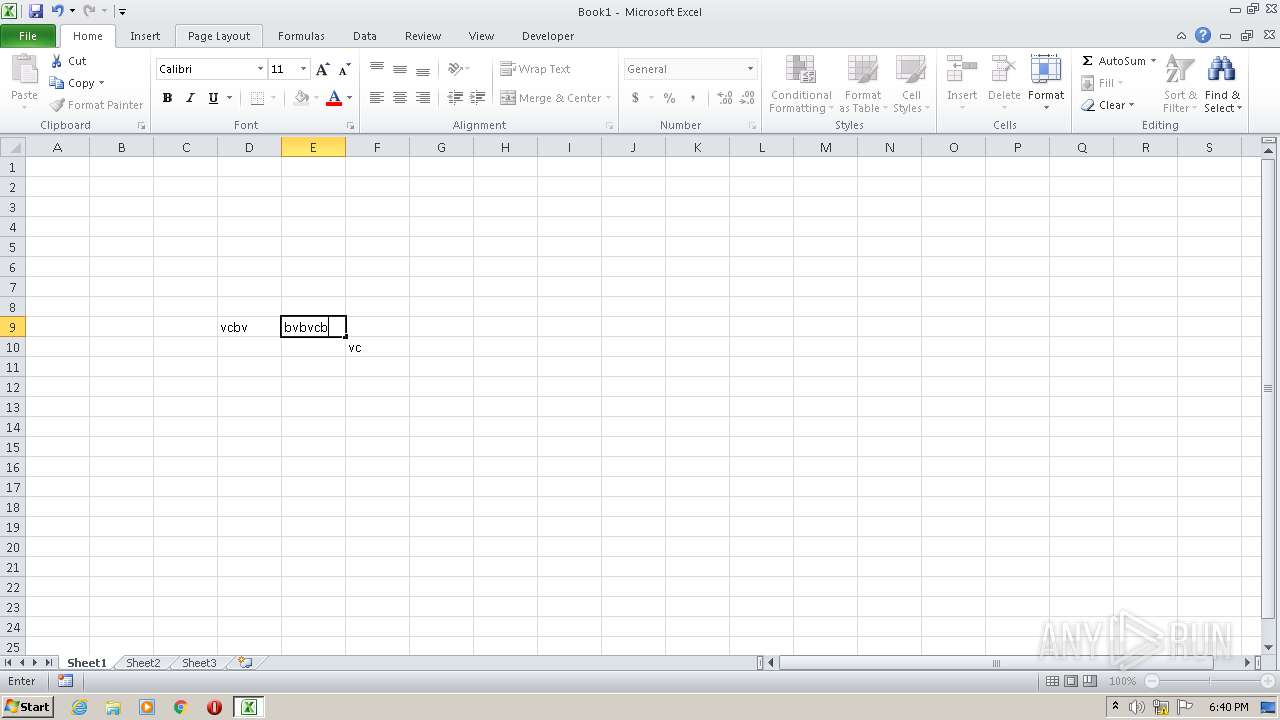
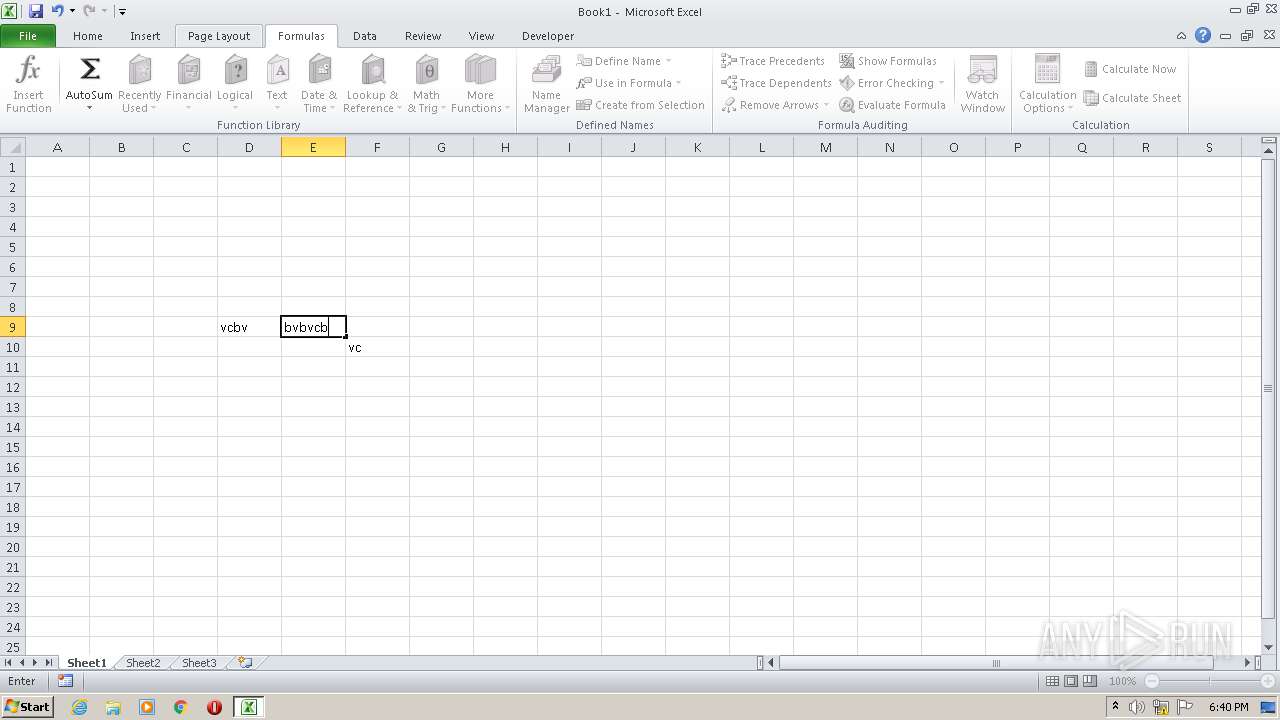
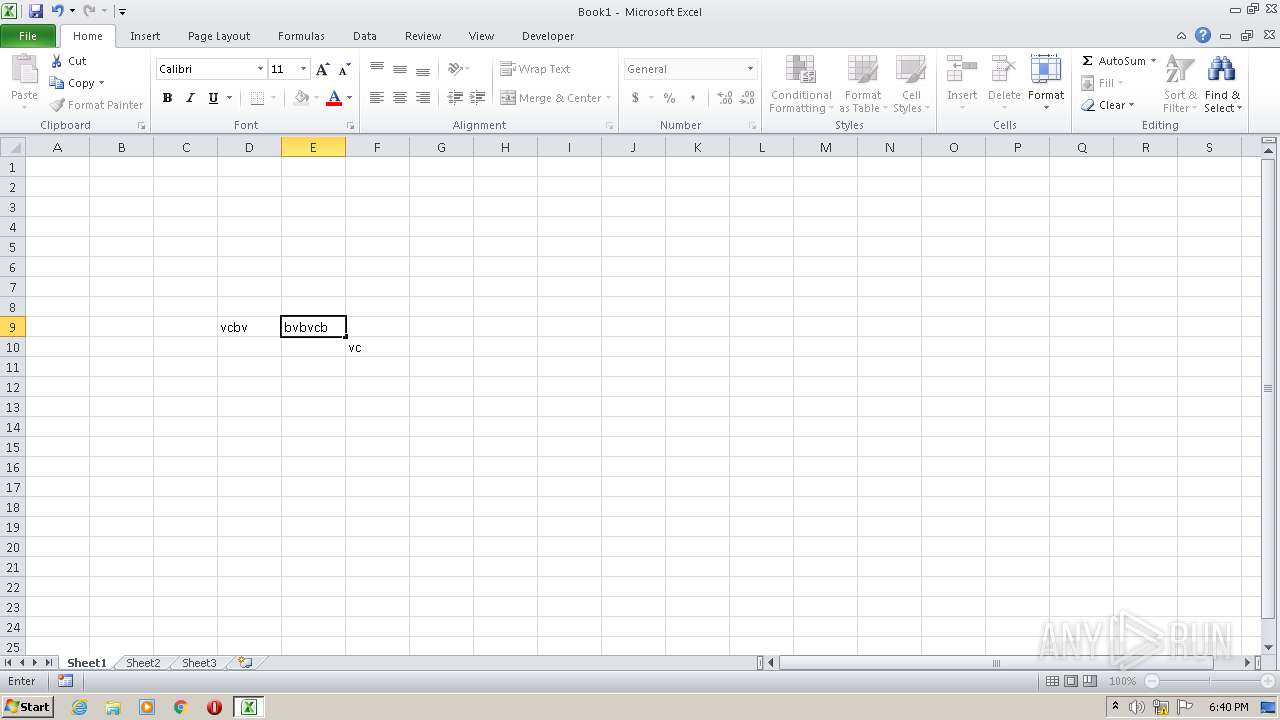
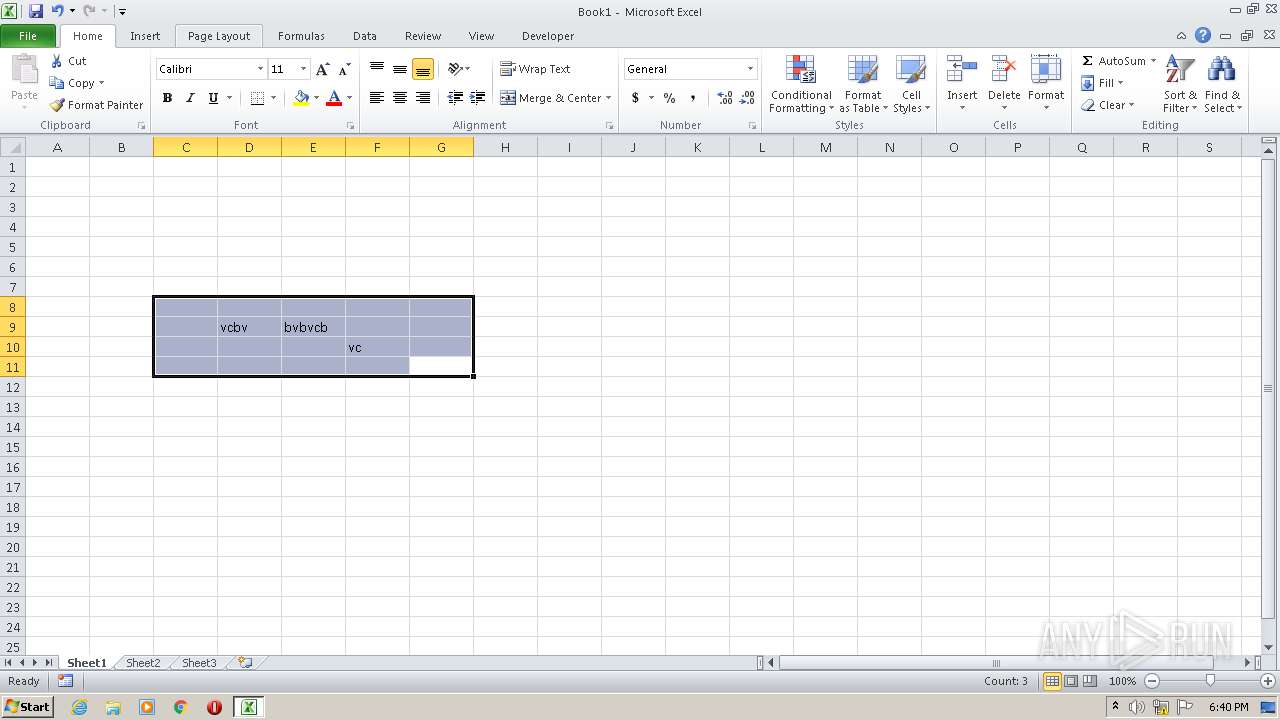
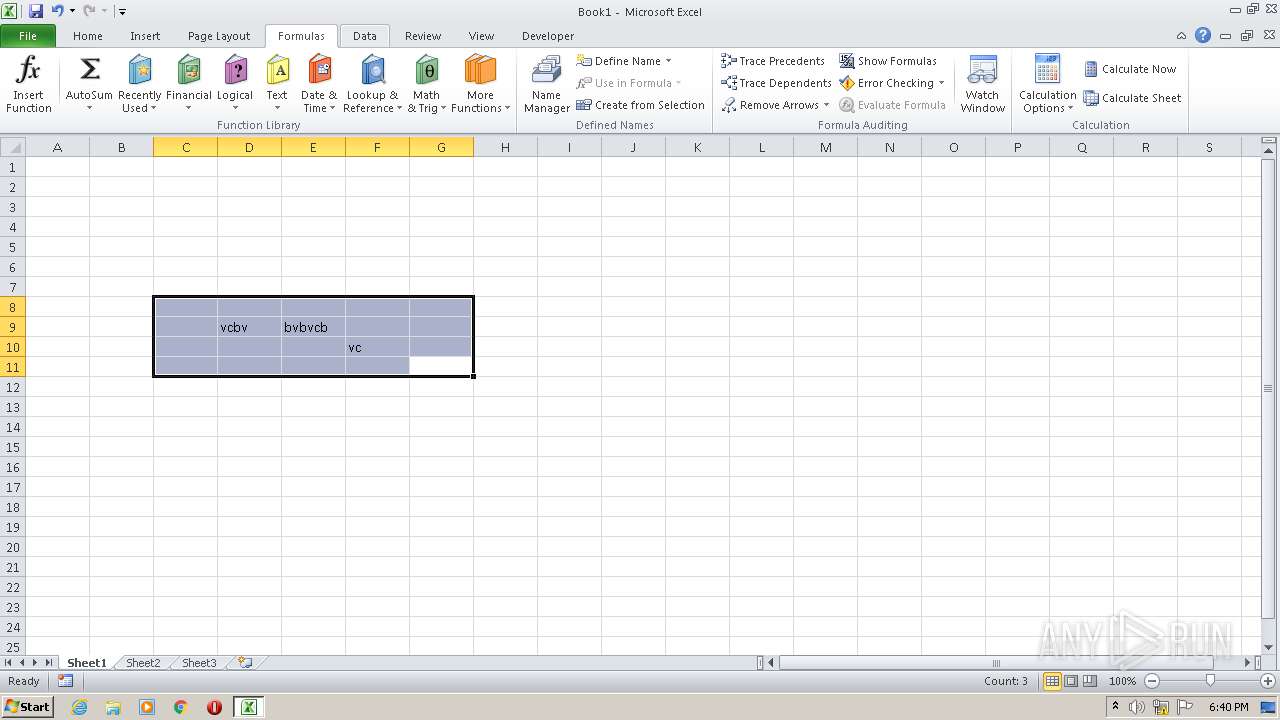
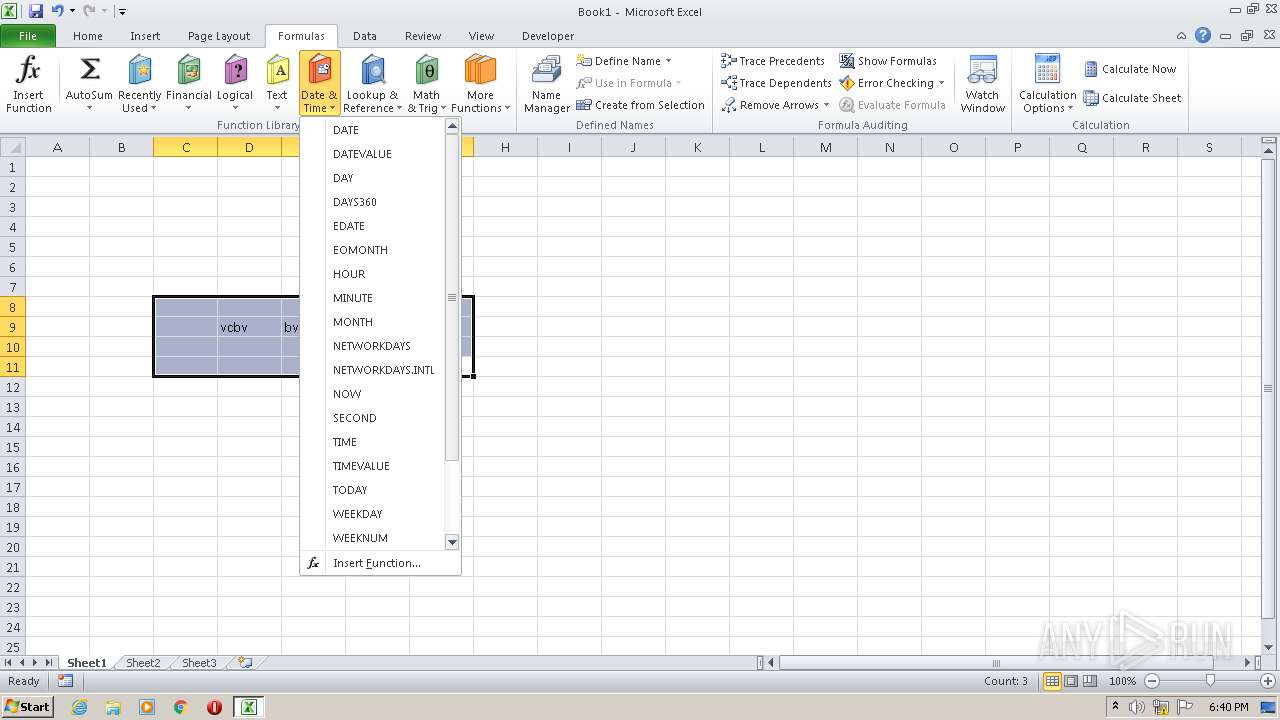
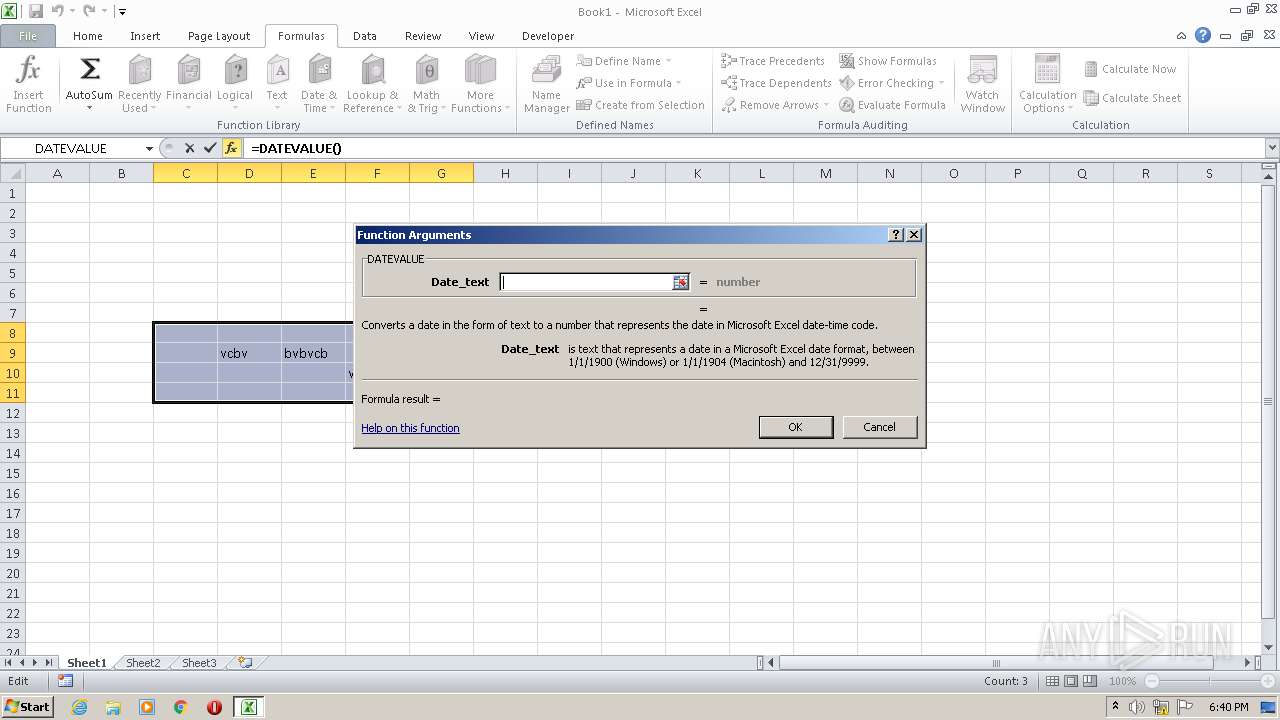
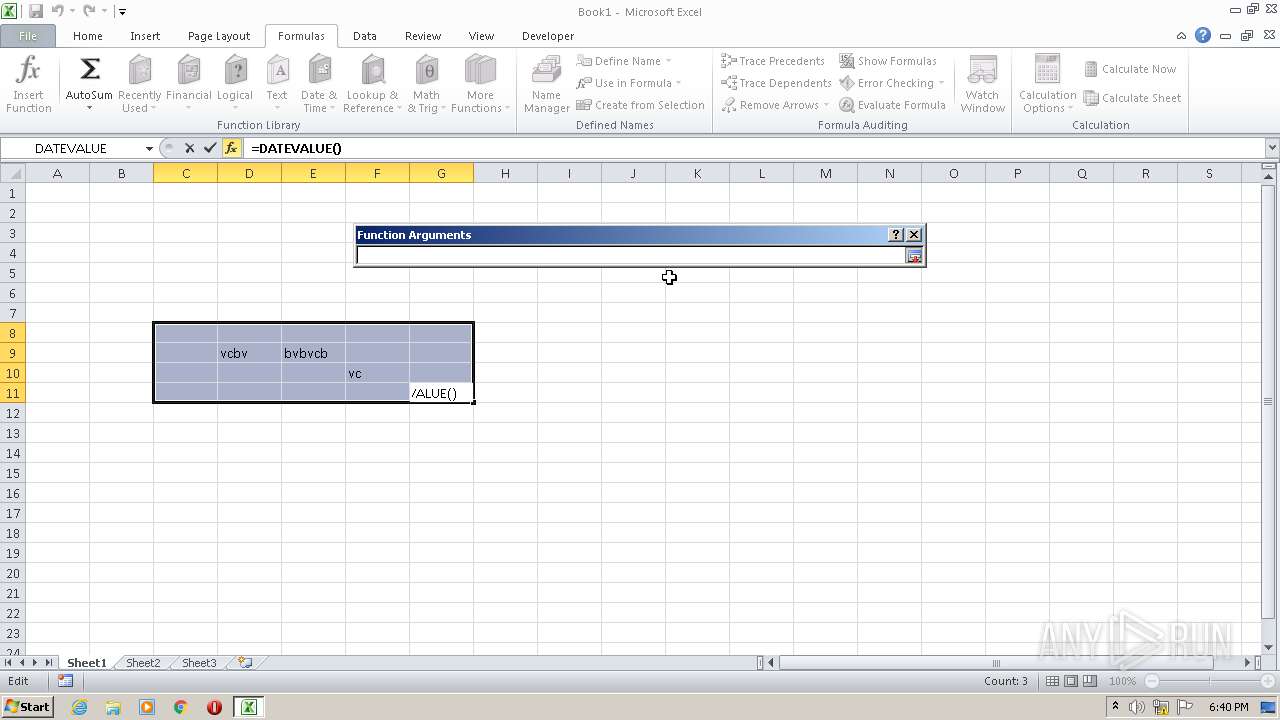
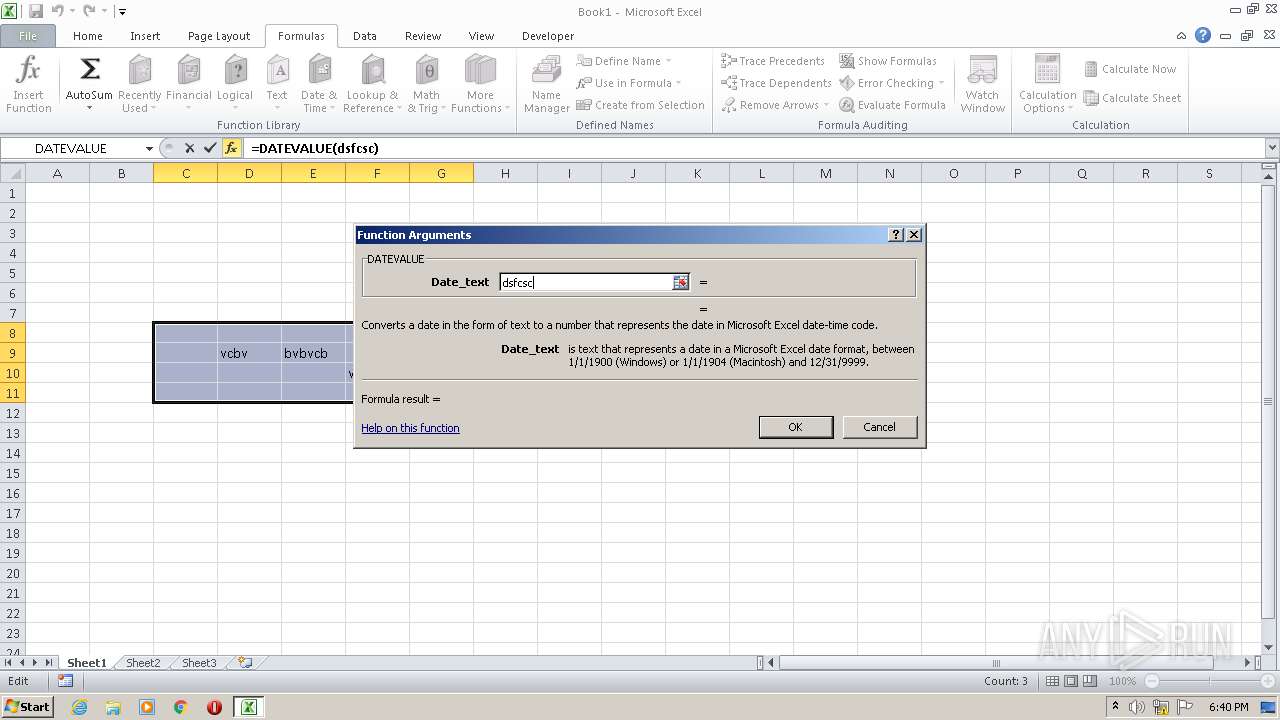
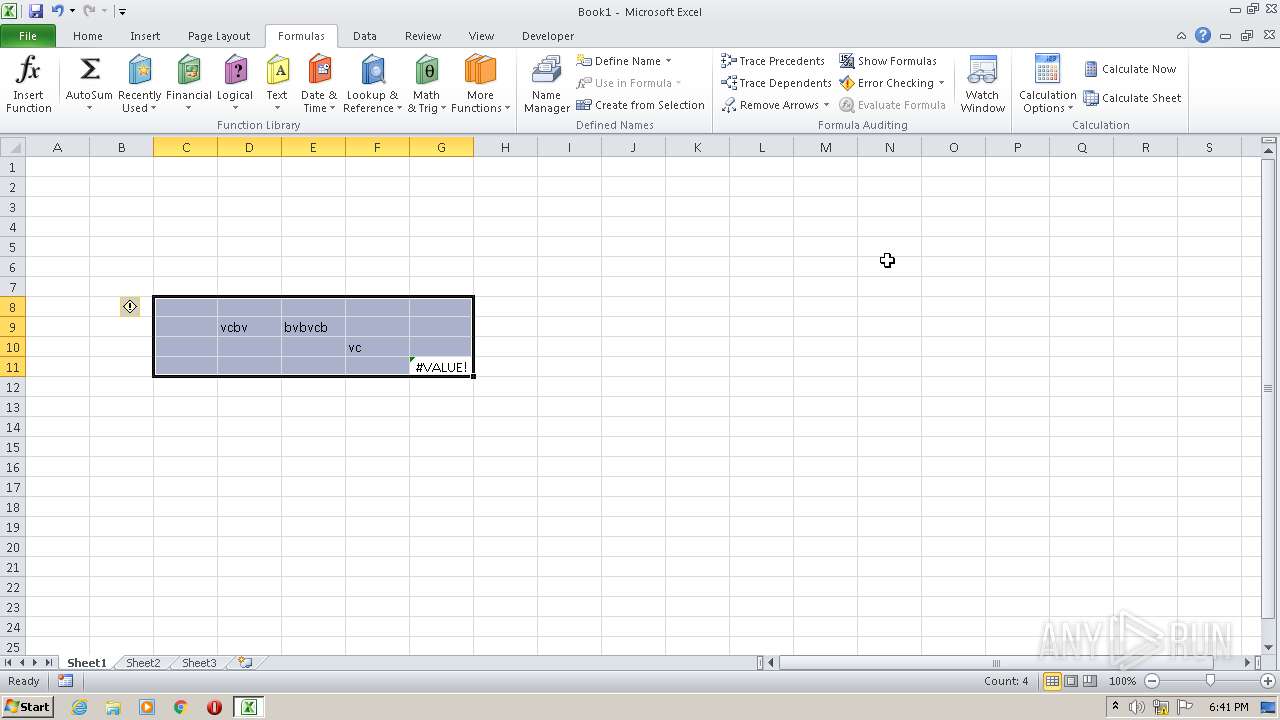
Manual execution by user
- EXCEL.EXE (PID: 3176)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:21 09:50:25+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 189952 |
| InitializedDataSize: | 9515008 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x10d6e |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.5419.0 |
| ProductVersionNumber: | 3.0.5419.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Software Installer |
| FileVersion: | 3.0.5419.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| LegalTrademarks1: | Microsoft® is a registered trademark of Microsoft Corporation. |
| LegalTrademarks2: | Windows® is a registered trademark of Microsoft Corporation. |
| OriginalFileName: | setup.exe |
| ProductName: | Windows Installer XML |
| ProductVersion: | 3.0.5419.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Nov-2018 08:50:25 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Software Installer |
| FileVersion: | 3.0.5419.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| LegalTrademarks1: | Microsoft® is a registered trademark of Microsoft Corporation. |
| LegalTrademarks2: | Windows® is a registered trademark of Microsoft Corporation. |
| OriginalFilename: | setup.exe |
| ProductName: | Windows Installer XML |
| ProductVersion: | 3.0.5419.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 21-Nov-2018 08:50:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E5B3 | 0x0002E600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60856 |
.rdata | 0x00030000 | 0x000106FC | 0x00010800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.45925 |
.data | 0x00041000 | 0x00001B18 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.07872 |
.rsrc | 0x00043000 | 0x00901854 | 0x00901A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.24009 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31079 | 1242 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 1.53973 | 9832 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 1.54324 | 4392 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 1.70751 | 2488 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 1.78405 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 3.25417 | 528 | Latin 1 / Western European | English - United States | RT_DIALOG |
102 | 2.64638 | 76 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
126 | 3.16391 | 2004 | Latin 1 / Western European | English - United States | RT_STRING |
3188 | 1.18832 | 46 | Latin 1 / Western European | English - United States | RT_STRING |
51003 | 0.197212 | 52232 | Latin 1 / Western European | English - United States | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.dll |
KERNEL32.dll |
PSAPI.DLL |
SHELL32.dll |
Secur32.dll |
USER32.dll |
WTSAPI32.dll |
msi.dll |
ole32.dll |
Total processes
42
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | C:\Windows\system32\MsiExec.exe -Embedding 71856381A486D9F803C0B04653B2A71C | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1420 | "C:\Users\admin\AppData\Local\Temp\BB510928-80A7-4121-95CC-886754DEF61D\lite_installer.exe" --use-user-default-locale --silent --cumtom-welcome-page=https://browser.yandex.ru/promo/welcome_com/5/ | C:\Users\admin\AppData\Local\Temp\BB510928-80A7-4121-95CC-886754DEF61D\lite_installer.exe | MsiExec.exe | ||||||||||||
User: admin Company: Yandex Integrity Level: MEDIUM Description: YandexBrowserDownloader Exit code: 0 Version: 1.0.1.88 Modules
| |||||||||||||||
| 1756 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2160 | C:\Users\admin\AppData\Local\Temp\32900D97-A3BC-4350-9BDA-039AF6E57D62\sender.exe --send "/status.xml?clid=2254945&uuid=66bc087c-3994-43d2-85d5-b3850e203dfc&vnt=Windows 7x32&file-no=6%0A15%0A16%0A25%0A38%0A45%0A58%0A59%0A102%0A106%0A108%0A111%0A121%0A125%0A129%0A" | C:\Users\admin\AppData\Local\Temp\32900D97-A3BC-4350-9BDA-039AF6E57D62\sender.exe | seederexe.exe | ||||||||||||
User: admin Company: Yandex Integrity Level: MEDIUM Description: Yandex Statistics Exit code: 0 Version: 0.0.2.14 Modules
| |||||||||||||||
| 2540 | "C:\Users\admin\AppData\Local\Temp\YandexPackSetup.exe" | C:\Users\admin\AppData\Local\Temp\YandexPackSetup.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Software Installer Exit code: 0 Version: 3.0.5419.0 Modules
| |||||||||||||||
| 3176 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3388 | "C:\Users\admin\AppData\Local\Temp\C1683BCD-3706-4781-8AE5-81CF7F3A4E4B\seederexe.exe" "--yqs=" "--yhp=" "--ilight=" "--oem=" "--nopin=n" "--pin_custom=n" "--pin_desktop=n" "--pin_taskbar=y" "--locale=us" "--browser=" "--browser_default=" "--yabm=" "--loglevel=trace" "--ess=" "--clids=C:\Users\admin\AppData\Local\Temp\clids-yasearch.xml" "--sender=C:\Users\admin\AppData\Local\Temp\32900D97-A3BC-4350-9BDA-039AF6E57D62\sender.exe" "--is_elevated=no" "--ui_level=5" "--good_token=x" | C:\Users\admin\AppData\Local\Temp\C1683BCD-3706-4781-8AE5-81CF7F3A4E4B\seederexe.exe | MsiExec.exe | ||||||||||||
User: admin Company: Yandex Integrity Level: MEDIUM Description: Browser Integration Module Exit code: 0 Version: 3.7.1.123 Modules
| |||||||||||||||
Total events
1 100
Read events
1 024
Write events
61
Delete events
15
Modification events
| (PID) Process: | (2540) YandexPackSetup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1756) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\132\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1756) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: DC060000D8E170F4BC69D601 | |||
| (PID) Process: | (1756) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 735722E79A889373A4DF671FB12AE2C9491FF829E98A2EB168EC79D368C58315 | |||
| (PID) Process: | (1756) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1756) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | (default) |
Value: C:\Windows\Installer\d782f.ipi | |||
| (PID) Process: | (1756) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (1756) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\d7830.rbs |
Value: 30828997 | |||
| (PID) Process: | (1756) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\d7830.rbsLow |
Value: 1462887888 | |||
| (PID) Process: | (1756) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\132\52C64B7E |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
5
Suspicious files
6
Text files
88
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2540 | YandexPackSetup.exe | C:\Users\admin\AppData\Local\Temp\{5B964E0E-B9A3-4276-9ED9-4D5A5720747A}\YandexSearch.msi | — | |
MD5:— | SHA256:— | |||
| 1756 | msiexec.exe | C:\Windows\Installer\d782e.msi | — | |
MD5:— | SHA256:— | |||
| 1756 | msiexec.exe | C:\Windows\Installer\MSI7947.tmp | — | |
MD5:— | SHA256:— | |||
| 316 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\vendor00000.xml | — | |
MD5:— | SHA256:— | |||
| 1756 | msiexec.exe | C:\Windows\Installer\MSI7A24.tmp | — | |
MD5:— | SHA256:— | |||
| 1756 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF144118F9457AFB9B.TMP | — | |
MD5:— | SHA256:— | |||
| 1756 | msiexec.exe | C:\Windows\Installer\MSI7AC1.tmp | — | |
MD5:— | SHA256:— | |||
| 1756 | msiexec.exe | C:\Windows\Installer\MSI7AD2.tmp | — | |
MD5:— | SHA256:— | |||
| 1756 | msiexec.exe | C:\Windows\Installer\MSI7AF2.tmp | — | |
MD5:— | SHA256:— | |||
| 1756 | msiexec.exe | C:\Windows\Installer\MSI7B32.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3388 | seederexe.exe | GET | 200 | 213.180.204.14:80 | http://clck.yandex.ru/click/dtype=stred/pid=198/cid=73068/path=3_7_1_123/GoogleChromeBeta=0/anti=0/antiNames=/browser=iexplore/clid=2254945/ff=0/gc=0/goodToken=x/googlin=0/ie=0/init=0/mlru=0/op=0/op64=0/ui=%7B66bc087c-3994-43d2-85d5-b3850e203dfc%7D/yabro=0/%2A | RU | image | 43 b | whitelisted |
2160 | sender.exe | GET | 200 | 87.250.250.33:80 | http://soft.export.yandex.ru/status.xml?clid=2254945&uuid=66bc087c-3994-43d2-85d5-b3850e203dfc&vnt=Windows%207x32&file-no=6%0A15%0A16%0A25%0A38%0A45%0A58%0A59%0A102%0A106%0A108%0A111%0A121%0A125%0A129 | RU | xml | 64 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1420 | lite_installer.exe | 213.180.204.14:80 | clck.yandex.ru | YANDEX LLC | RU | whitelisted |
3388 | seederexe.exe | 213.180.204.14:80 | clck.yandex.ru | YANDEX LLC | RU | whitelisted |
2160 | sender.exe | 87.250.250.33:80 | soft.export.yandex.ru | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clck.yandex.ru |
| whitelisted |
soft.export.yandex.ru |
| whitelisted |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
YandexPackSetup.exe | IsAlreadyRun() In
|
YandexPackSetup.exe | IsAlreadyRun() Out : ret (BOOL) = 0
|
YandexPackSetup.exe | IsMSISrvFree() Out ret = 1
|
YandexPackSetup.exe | IsMSISrvFree() In |
YandexPackSetup.exe | IsMSISrvFree() : OpenMutex() err ret = 2
|
YandexPackSetup.exe | GetSidFromEnumSess(): LsaEnumerateLogonSessions() lpszSid = S-1-5-21-1302019708-1500728564-335382590-1000
|
YandexPackSetup.exe | GetLoggedCreds_WTSSessionInfo(): szUserName = admin, szDomain = USER-PC, dwSessionId = 1
|
YandexPackSetup.exe | GetSidFromEnumSess(): LsaGetLogonSessionData(0) err = 5
|
YandexPackSetup.exe | GetSidFromEnumSess(): ProfileImagePath(1) = C:\Users\admin
|
YandexPackSetup.exe | GetSidFromEnumSess(): LsaEnumerateLogonSessions() lpszSid = S-1-5-21-1302019708-1500728564-335382590-1000
|