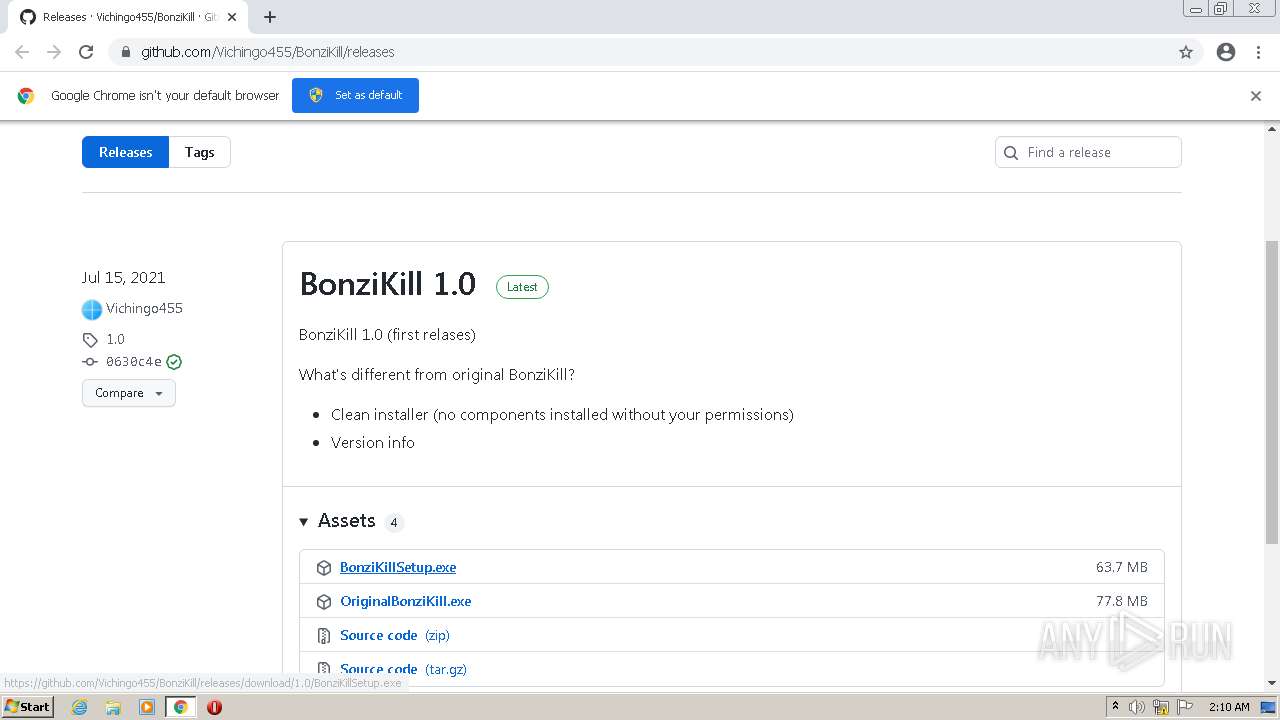
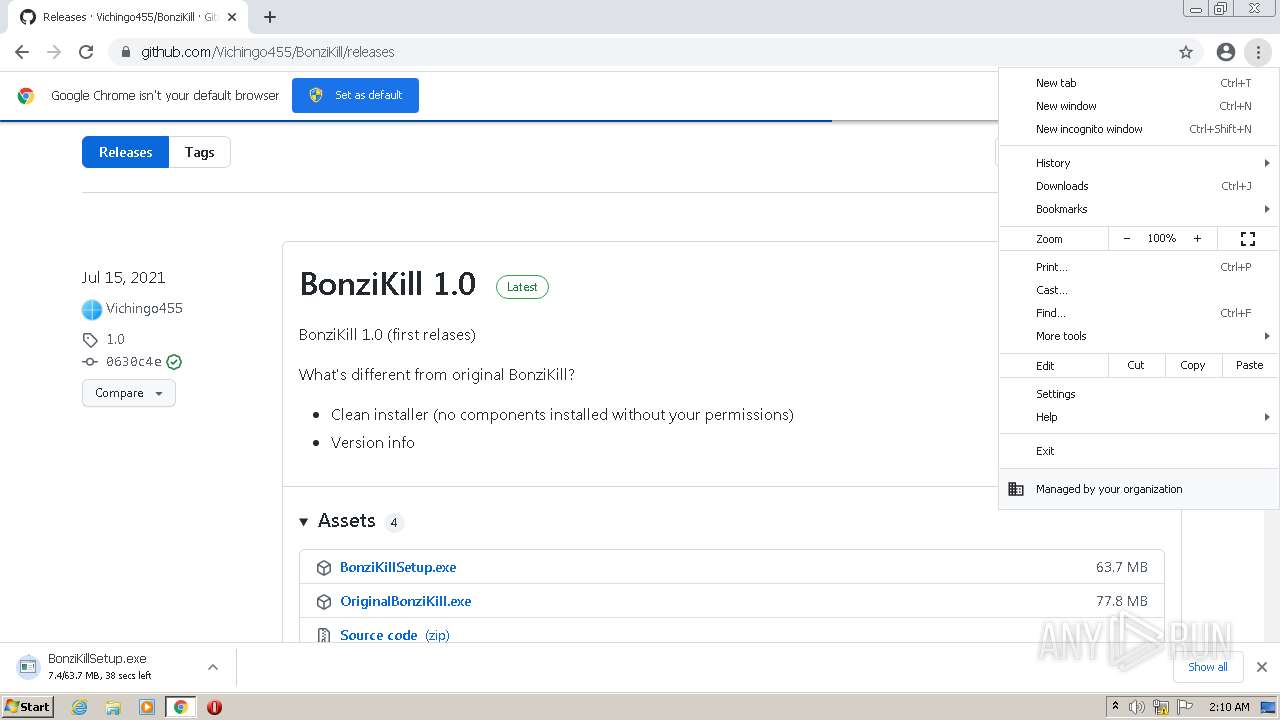
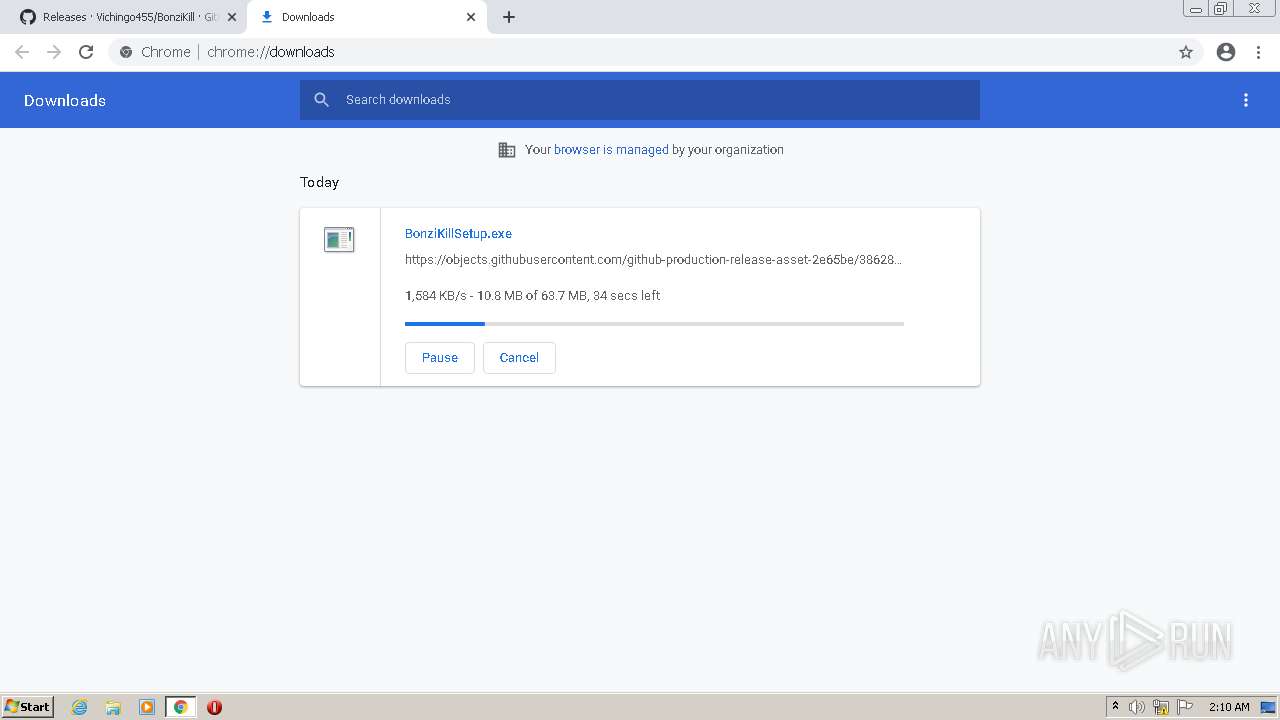
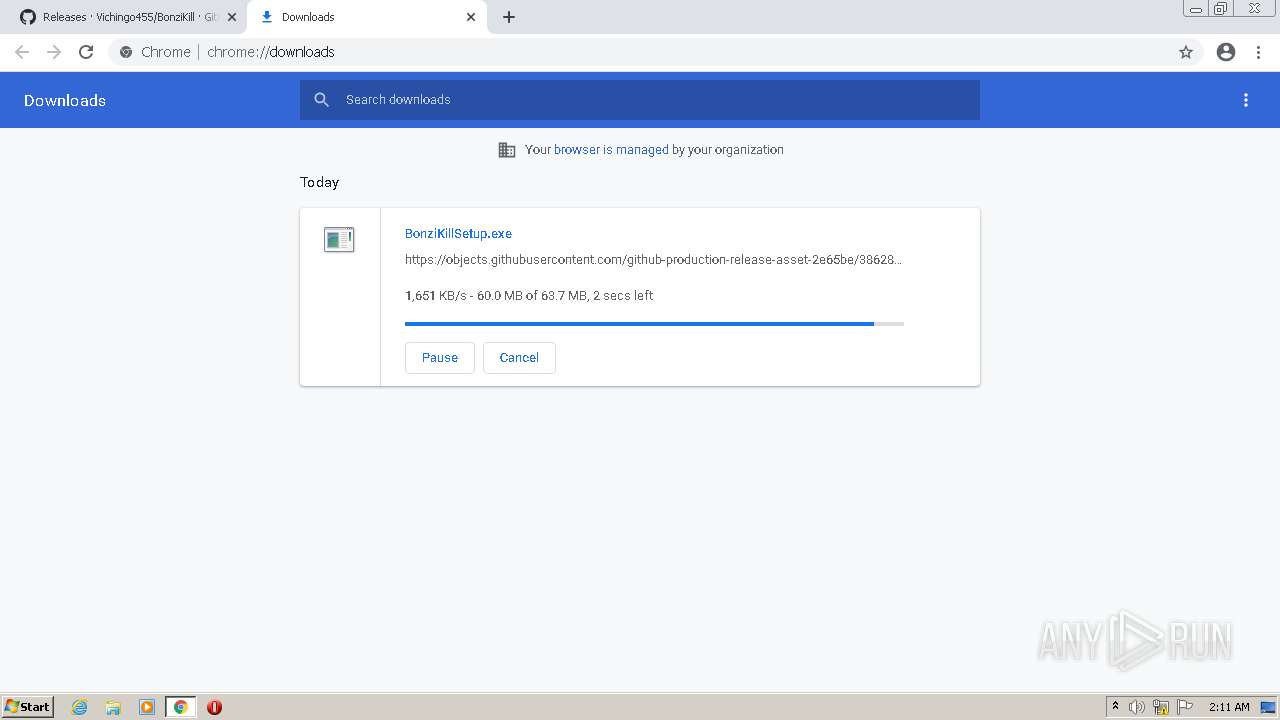
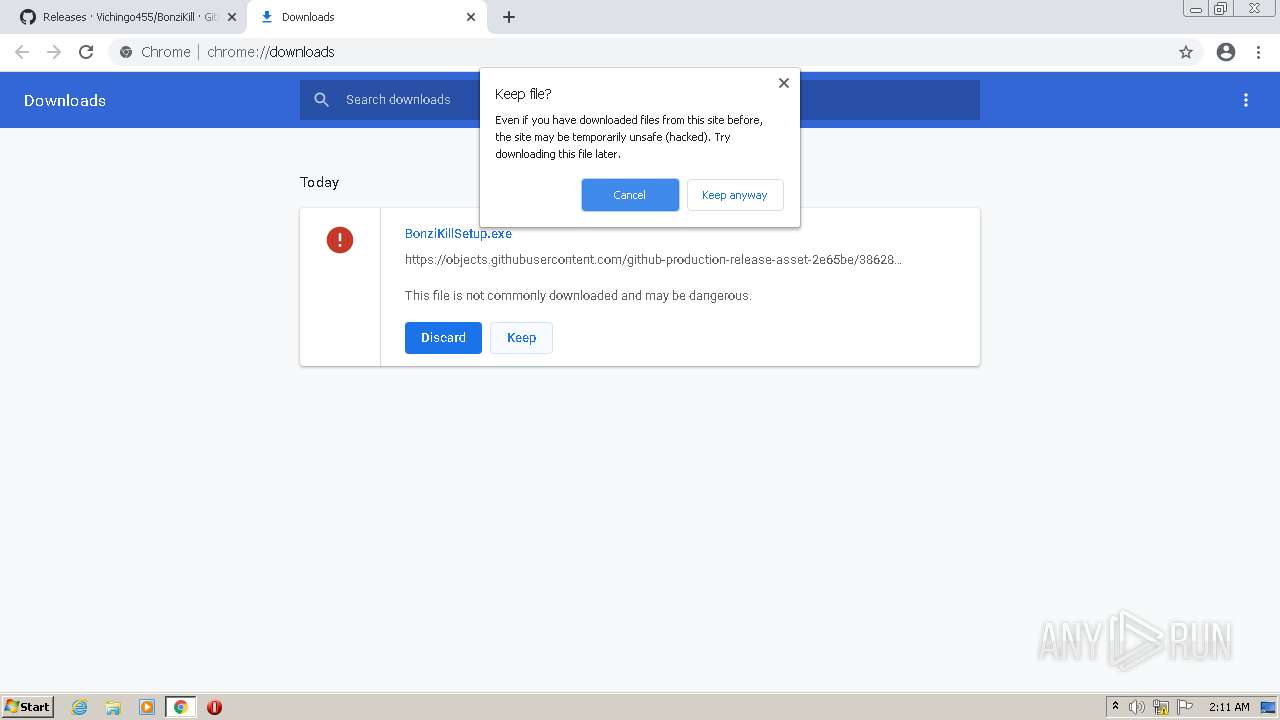
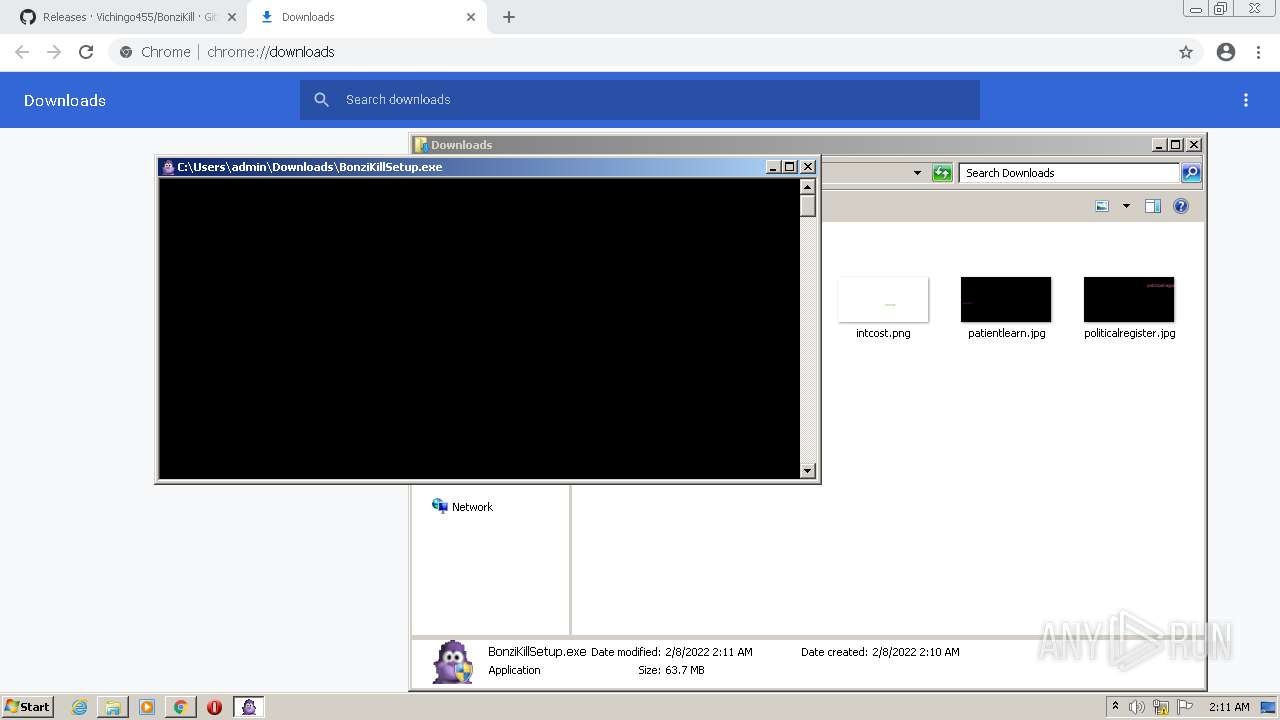
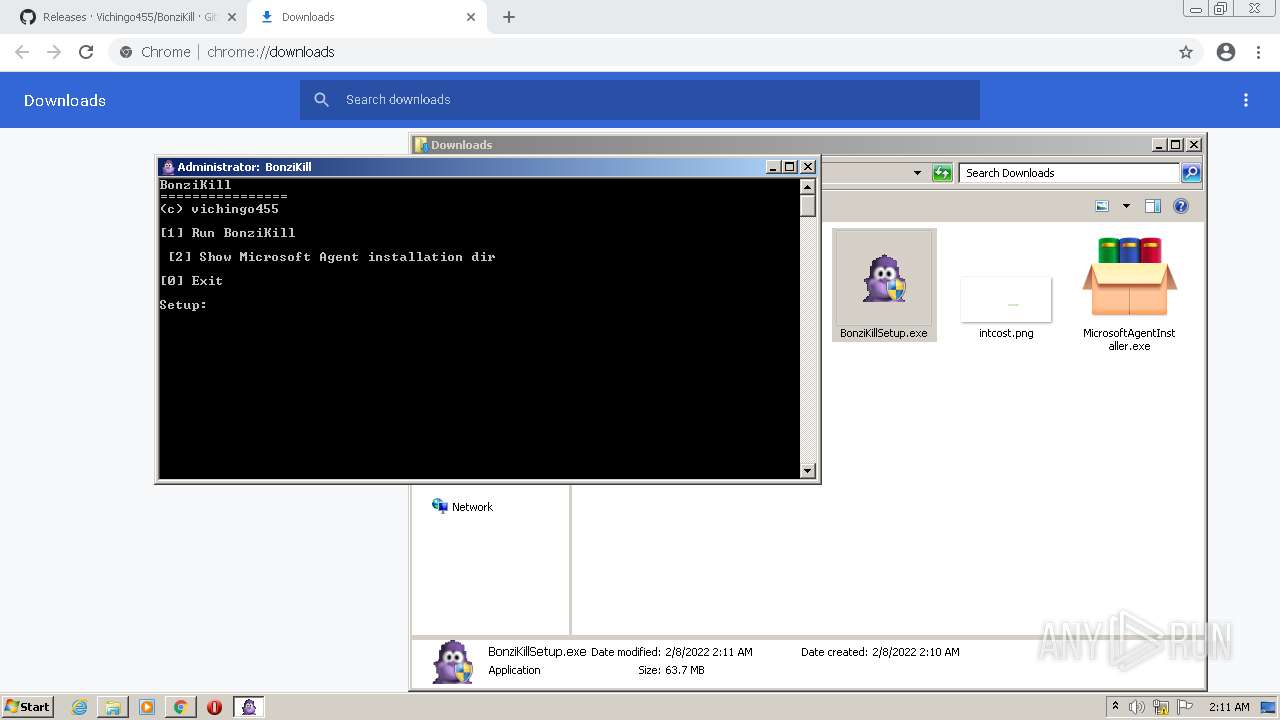
| URL: | https://github.com/Vichingo455/BonziKill/releases |
| Full analysis: | https://app.any.run/tasks/1527733a-a397-459c-b78a-1740142f9e4f |
| Verdict: | Malicious activity |
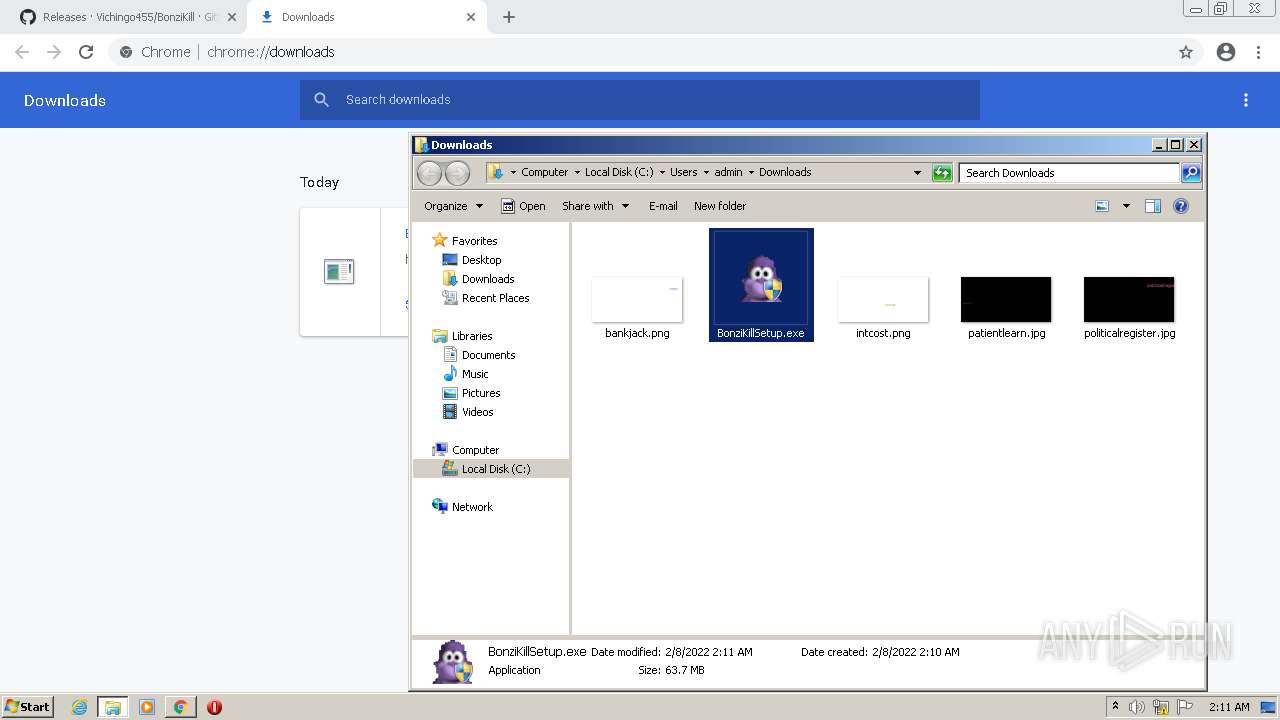
| Analysis date: | February 08, 2022, 02:10:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5E91D2110187441FAE7953B63F3069B3 |
| SHA1: | 16DED6849FE6F3590948EC9D74A9C03BCFA24355 |
| SHA256: | E3B3D4EF6E3E98DAC551E9AC1A6BD71CEC44F41DE3C151C71D12D7043E1E338F |
| SSDEEP: | 3:N8tEdQaM2KQQKnKrv0MAJArn:2umHjQQKnKcIrn |
MALICIOUS
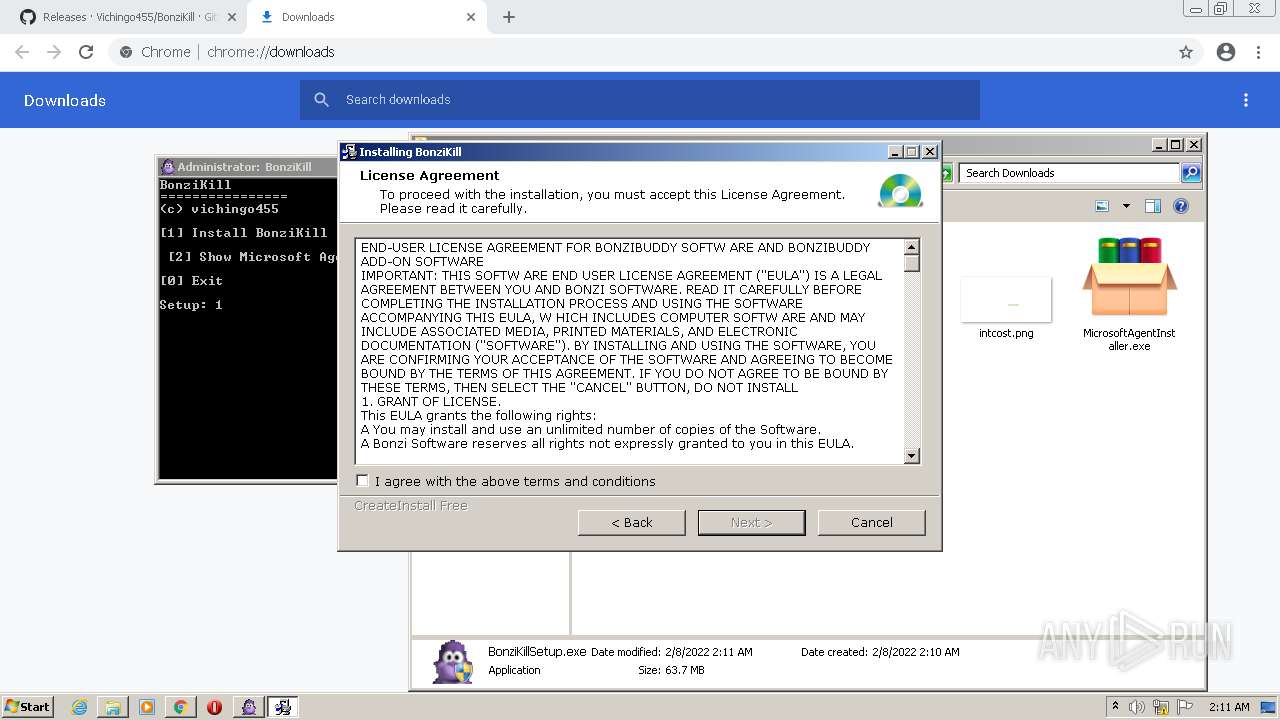
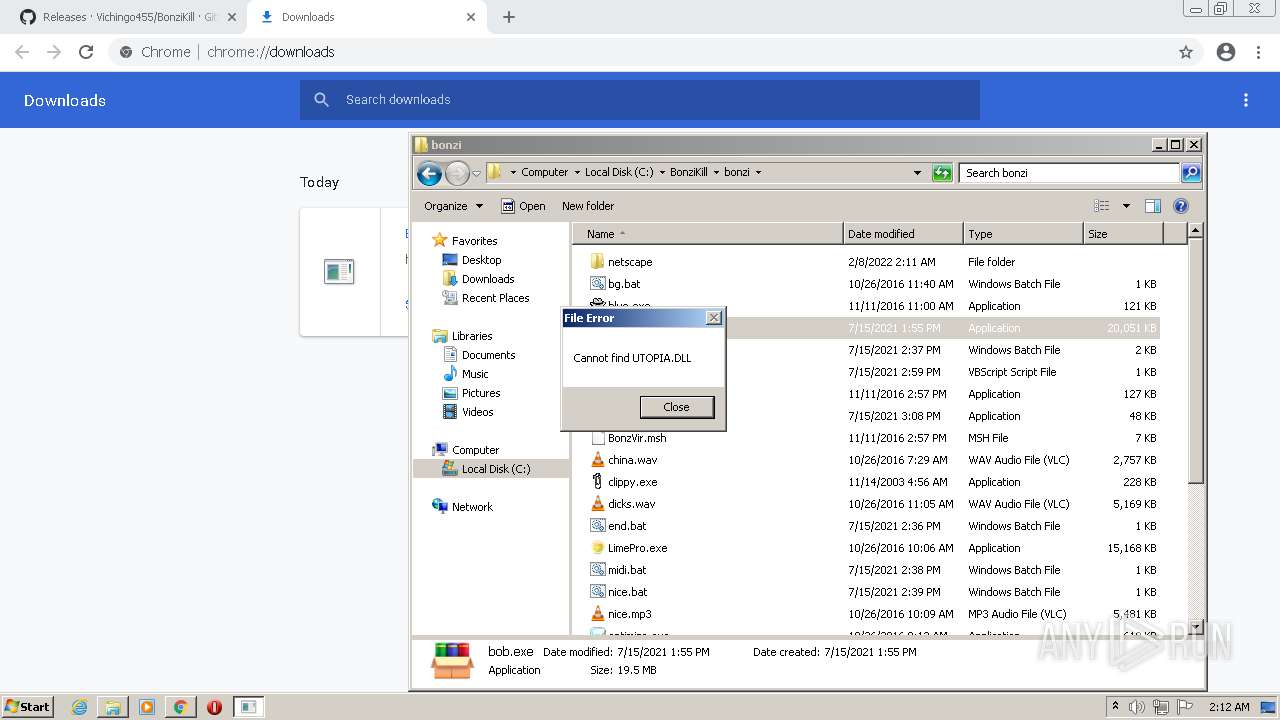
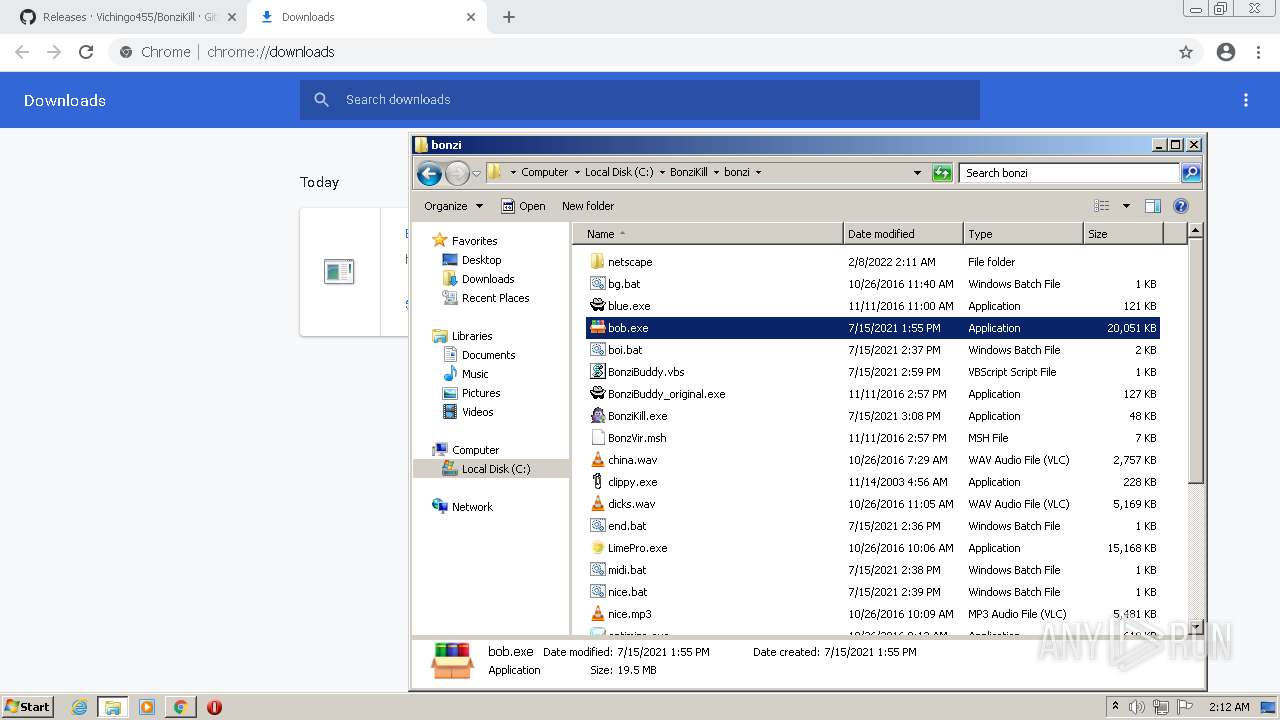
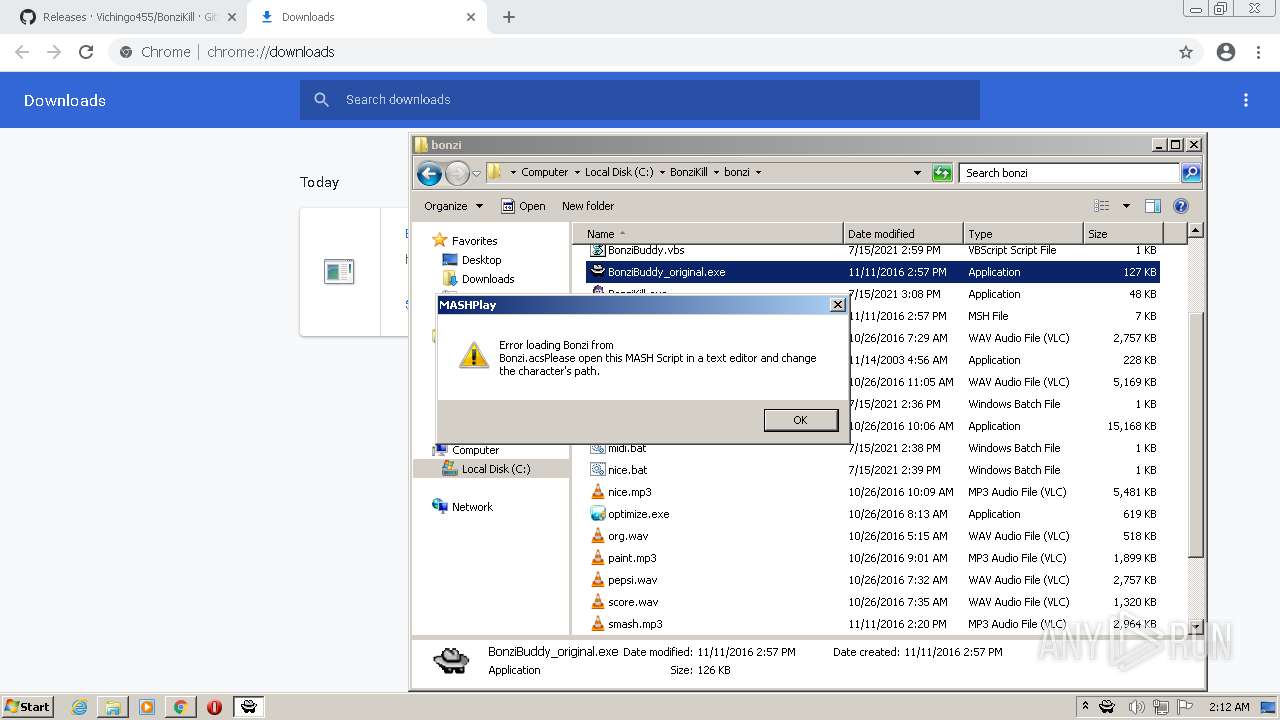
Application was dropped or rewritten from another process
- MicrosoftAgentInstaller.exe (PID: 3252)
- bob.exe (PID: 572)
- BonziBuddy_original.exe (PID: 3476)
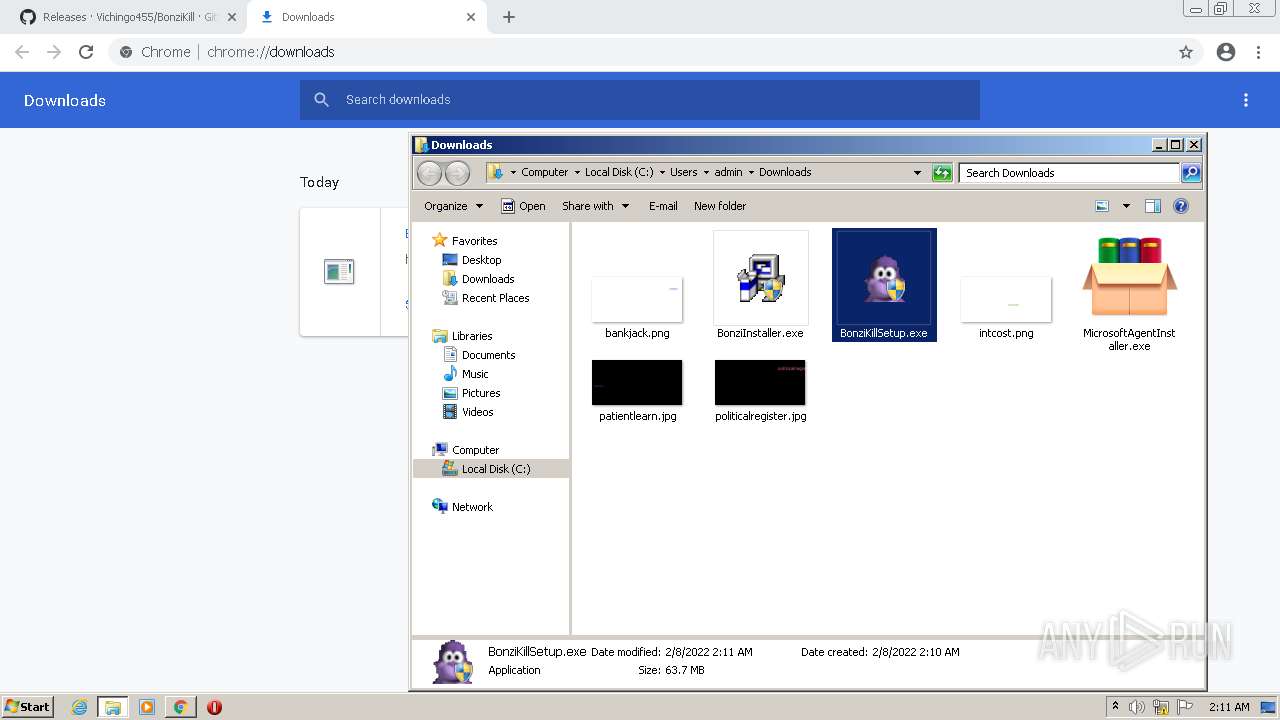
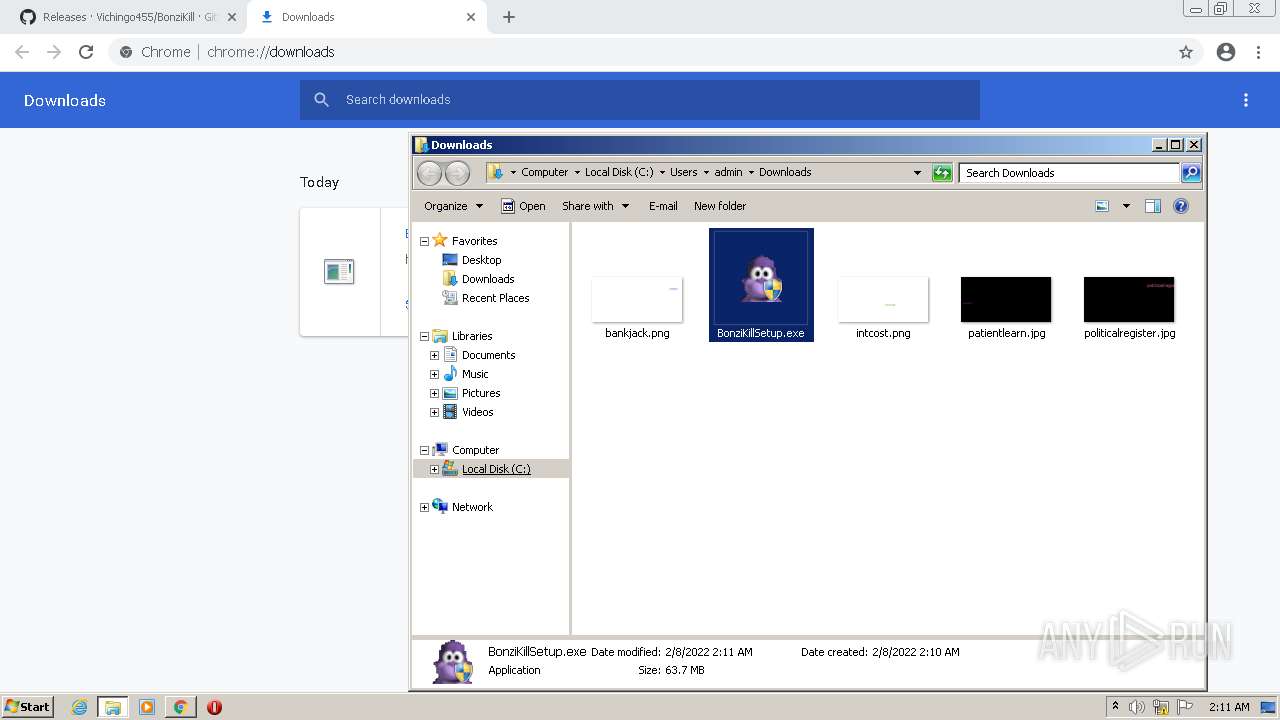
Drops executable file immediately after starts
- MicrosoftAgentInstaller.exe (PID: 3252)
- BonziInstaller.exe (PID: 2240)
Loads dropped or rewritten executable
- BonziInstaller.exe (PID: 2240)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3652)
- BonziKillSetup.exe (PID: 2056)
- MicrosoftAgentInstaller.exe (PID: 3252)
- BonziInstaller.exe (PID: 2240)
- (PID: 1820)
Drops a file that was compiled in debug mode
- BonziKillSetup.exe (PID: 2056)
- MicrosoftAgentInstaller.exe (PID: 3252)
- BonziInstaller.exe (PID: 2240)
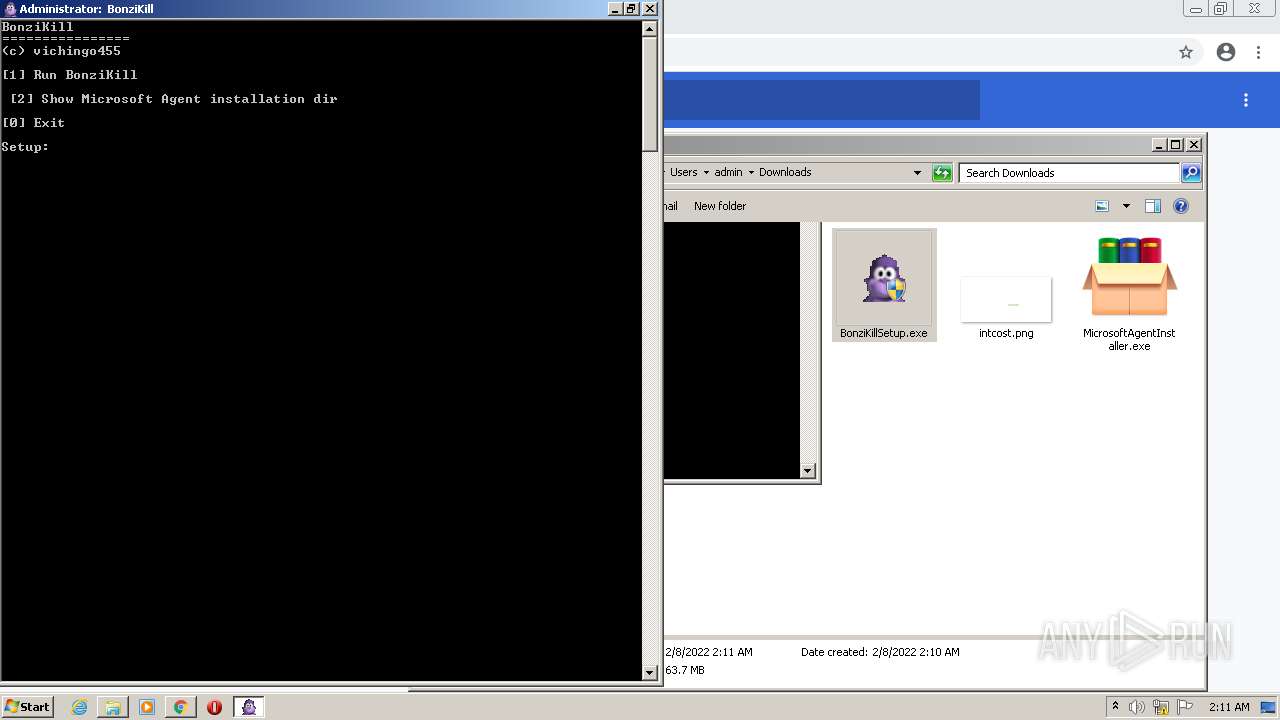
Starts CMD.EXE for commands execution
- BonziKillSetup.exe (PID: 2056)
- BonziInstaller.exe (PID: 2240)
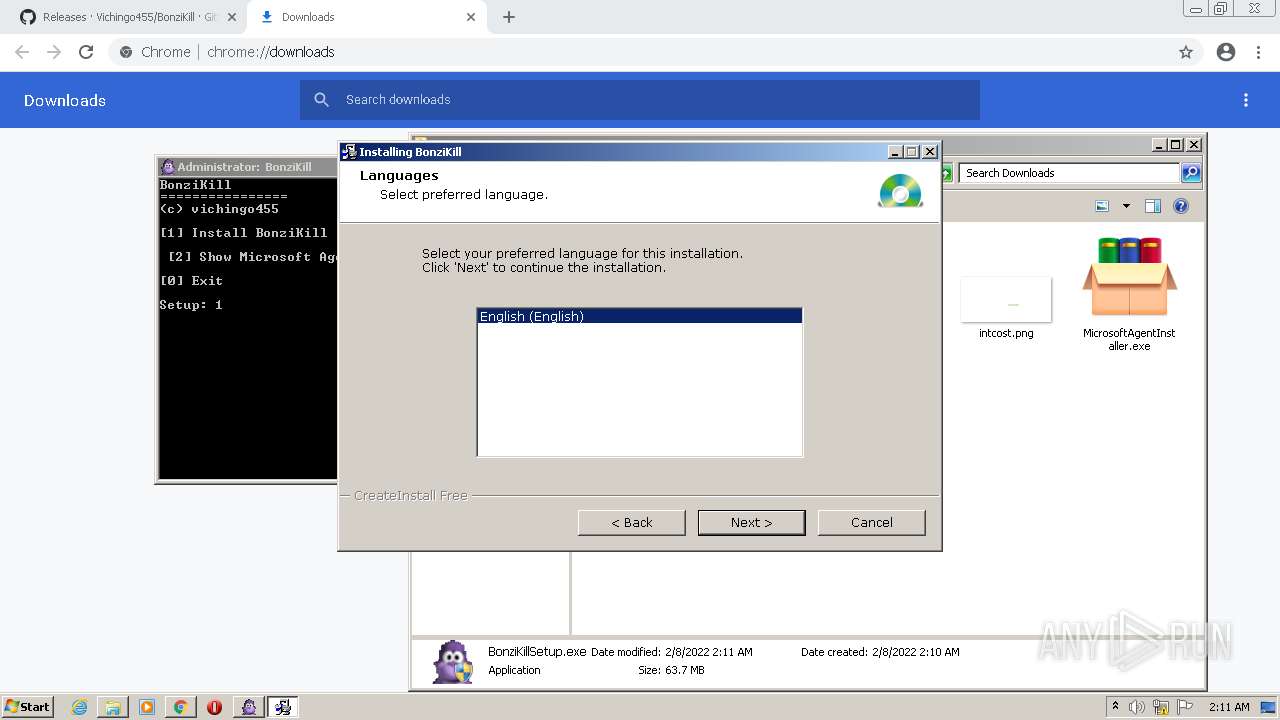
Checks supported languages
- BonziKillSetup.exe (PID: 2056)
- cmd.exe (PID: 3708)
- MicrosoftAgentInstaller.exe (PID: 3252)
- BonziInstaller.exe (PID: 2240)
- bob.exe (PID: 572)
- (PID: 1820)
- bob.exe (PID: 2732)
- cmd.exe (PID: 2236)
- BonziBuddy_original.exe (PID: 3476)
Removes files from Windows directory
- MicrosoftAgentInstaller.exe (PID: 3252)
Reads the computer name
- MicrosoftAgentInstaller.exe (PID: 3252)
- BonziInstaller.exe (PID: 2240)
- bob.exe (PID: 572)
- bob.exe (PID: 2732)
- (PID: 1820)
- BonziBuddy_original.exe (PID: 3476)
Drops a file with too old compile date
- MicrosoftAgentInstaller.exe (PID: 3252)
- BonziInstaller.exe (PID: 2240)
Creates files in the Windows directory
- MicrosoftAgentInstaller.exe (PID: 3252)
Reads the Windows organization settings
- BonziInstaller.exe (PID: 2240)
Reads Windows owner or organization settings
- BonziInstaller.exe (PID: 2240)
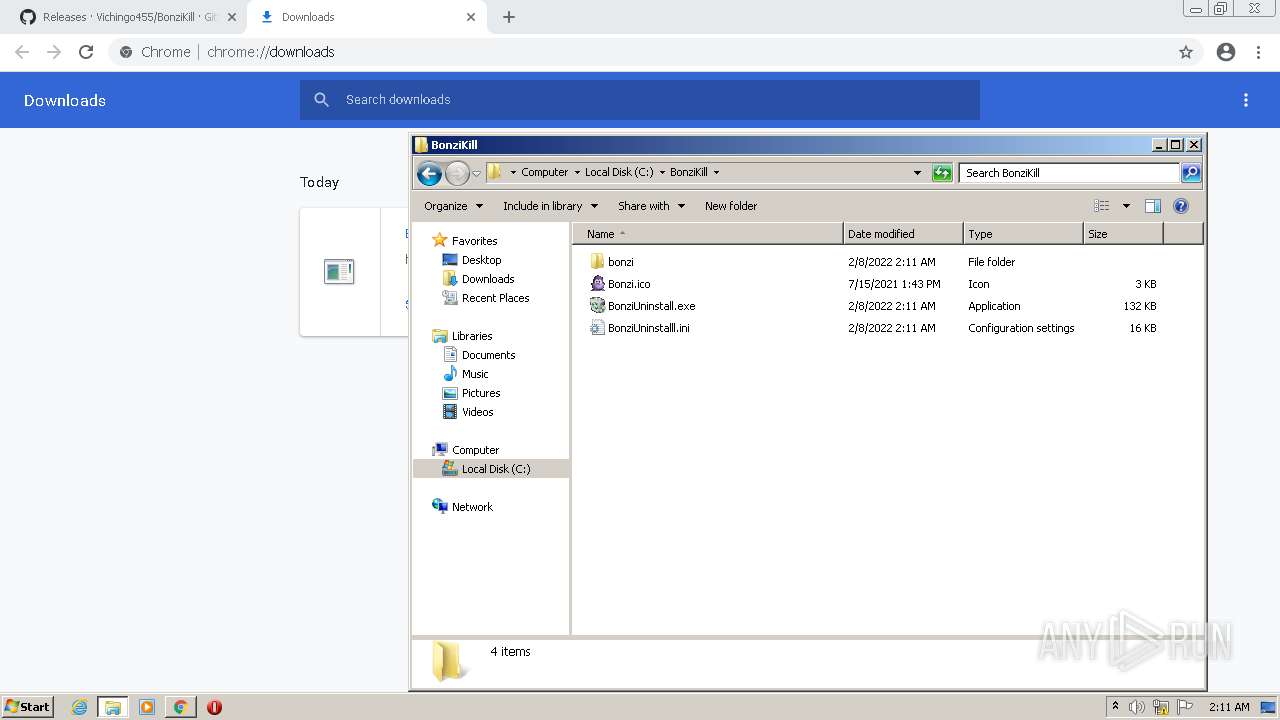
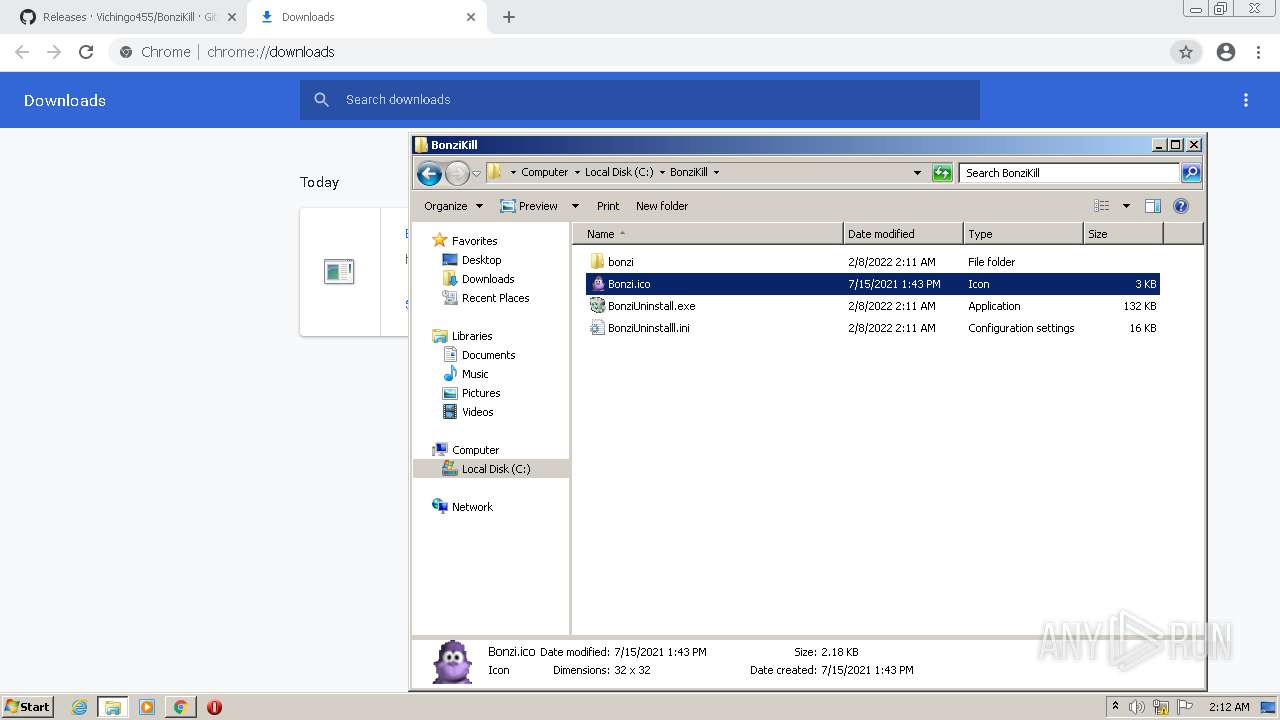
Creates a directory in Program Files
- BonziInstaller.exe (PID: 2240)
Creates files in the user directory
- BonziInstaller.exe (PID: 2240)
- bob.exe (PID: 2732)
- (PID: 1820)
Creates a software uninstall entry
- BonziInstaller.exe (PID: 2240)
Executed via COM
- DllHost.exe (PID: 4044)
Starts application with an unusual extension
- bob.exe (PID: 2732)
Drops a file with a compile date too recent
- (PID: 1820)
INFO
Reads the computer name
- chrome.exe (PID: 1536)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3316)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 592)
- chrome.exe (PID: 1580)
- chrome.exe (PID: 776)
- chrome.exe (PID: 3516)
- chrome.exe (PID: 3692)
- DllHost.exe (PID: 4044)
Checks supported languages
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 1536)
- chrome.exe (PID: 3864)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2356)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3316)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 592)
- chrome.exe (PID: 2788)
- chrome.exe (PID: 856)
- chrome.exe (PID: 3148)
- chrome.exe (PID: 1580)
- chrome.exe (PID: 776)
- chrome.exe (PID: 3516)
- chrome.exe (PID: 1480)
- chrome.exe (PID: 3424)
- chrome.exe (PID: 3692)
- DllHost.exe (PID: 4044)
- chrome.exe (PID: 1536)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 2028)
Reads the date of Windows installation
- chrome.exe (PID: 2248)
Reads the hosts file
- chrome.exe (PID: 3972)
- chrome.exe (PID: 3652)
Reads settings of System Certificates
- chrome.exe (PID: 3972)
Application launched itself
- chrome.exe (PID: 3652)
Checks Windows Trust Settings
- chrome.exe (PID: 3652)
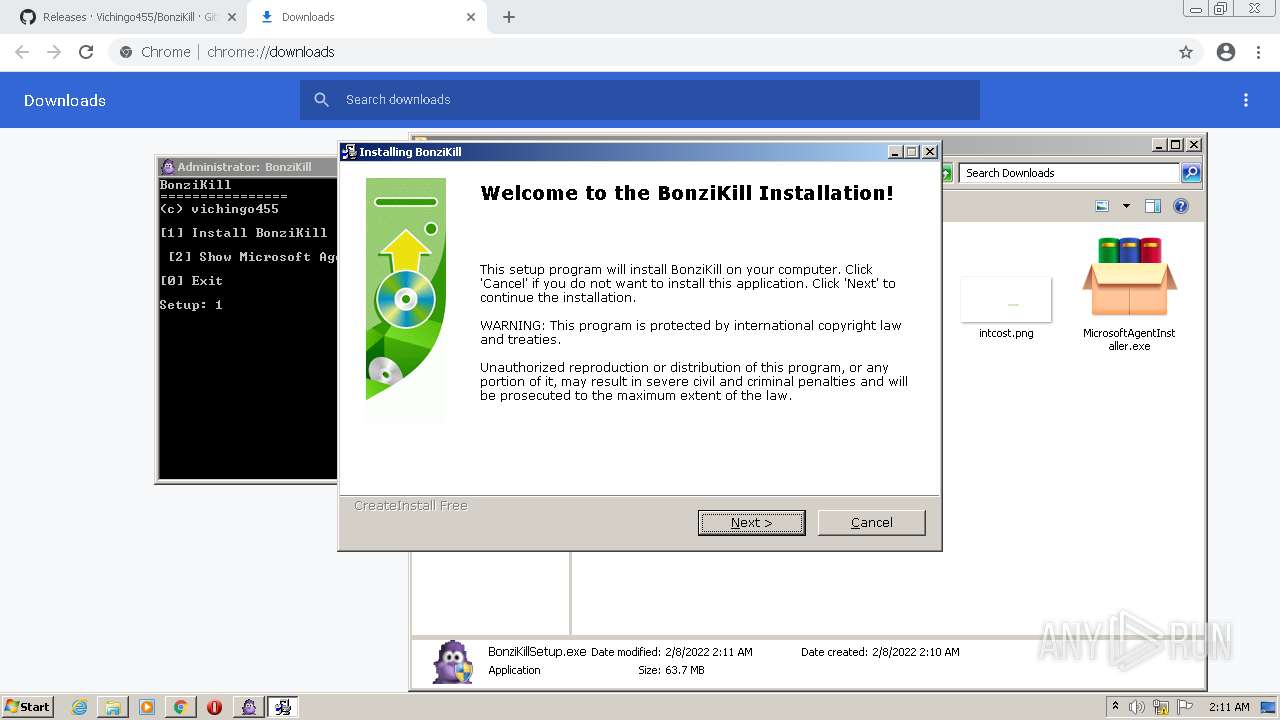
Manual execution by user
- BonziKillSetup.exe (PID: 2056)
- bob.exe (PID: 572)
- BonziBuddy_original.exe (PID: 3476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
33
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 572 | "C:\BonziKill\bonzi\bob.exe" | C:\BonziKill\bonzi\bob.exe | — | Explorer.EXE |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2680 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1016,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=932 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3088 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1016,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2864 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1068 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1016,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2916 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1016,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2960 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 1820 | bob.exe | |||
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1016,11895710382425917550,4173502547325726186,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1736 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
73
Suspicious files
50
Text files
249
Unknown types
14
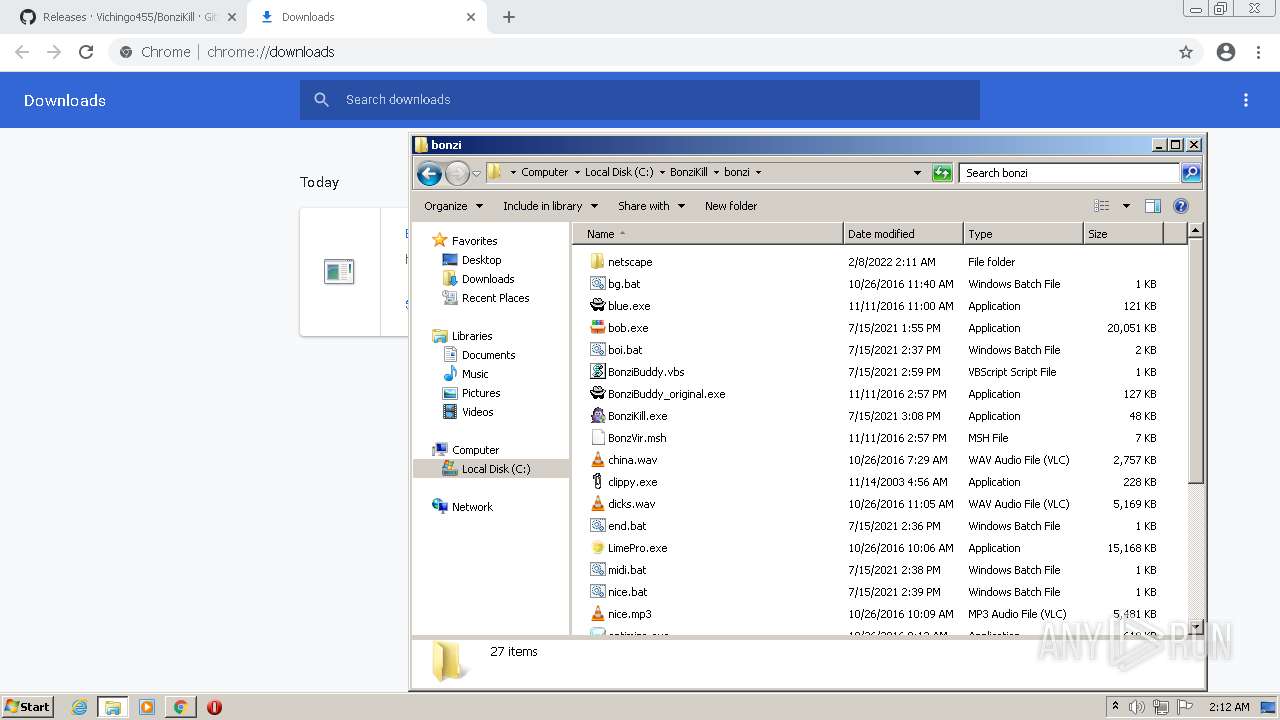
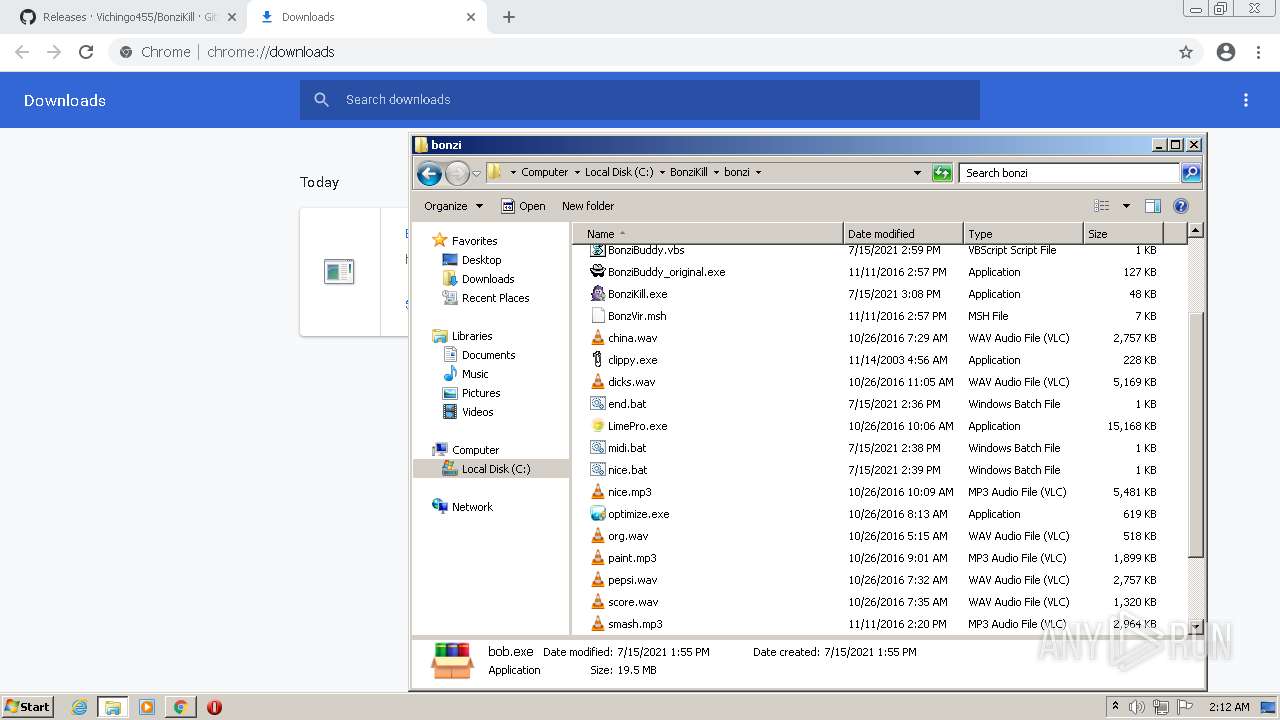
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6201D111-E44.pma | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:5B13520FC584EB3711C21709510AF306 | SHA256:1804BD6DF7BE5335BA08BFF624F3E0CA5D39BE2EE3A02A84AF6318BBE3332B9F | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\800c5636-e801-4bdd-b432-743c2b1984a2.tmp | text | |
MD5:5B13520FC584EB3711C21709510AF306 | SHA256:1804BD6DF7BE5335BA08BFF624F3E0CA5D39BE2EE3A02A84AF6318BBE3332B9F | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF12ca5d.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12c943.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF12c953.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3b501ddf-df34-44a5-889f-7a0d74a98c0f.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:CDB4EE2AEA69CC6A83331BBE96DC2CAA9A299D21329EFB0336FC02A82E1839A8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
32
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
872 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 5.64 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 9.69 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 43.4 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 9.69 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 358 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 88.4 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 20.9 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 178 Kb | whitelisted |
872 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 718 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3972 | chrome.exe | 142.250.185.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 142.250.184.237:443 | accounts.google.com | Google Inc. | US | suspicious |
3972 | chrome.exe | 185.199.108.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
3972 | chrome.exe | 140.82.121.4:443 | github.com | — | US | malicious |
3972 | chrome.exe | 185.199.111.133:443 | avatars.githubusercontent.com | GitHub, Inc. | NL | suspicious |
3972 | chrome.exe | 172.217.16.138:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 140.82.112.22:443 | collector.github.com | — | US | suspicious |
3972 | chrome.exe | 140.82.121.6:443 | api.github.com | — | US | suspicious |
3972 | chrome.exe | 142.250.184.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3972 | chrome.exe | 142.250.186.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
collector.github.com |
| whitelisted |
api.github.com |
| whitelisted |
Threats
Process | Message |
|---|---|
bob.exe | <?dml?>#1 p=2732/AACh t=2780/ADCh: <link cmd=".reload /f boot_loader.exe=0x66200000">Reload</link> <b>boot_loader.exe</b> 0x66200000
|
bob.exe | <?dml?>#2 p=2732/AACh t=2780/ADCh: Loading packaged nt0_dll.dll...
|
bob.exe | <?dml?>#3 p=2732/AACh t=2780/ADCh: <link cmd=".reload /f nt0_dll.dll=0x7FDD0000">Reload</link> <b>nt0_dll.dll</b> 0x7FDD0000 packaged
|
bob.exe | <?dml?>#1 p=2732/AACh t=2780/ADCh: <link cmd=".reload /f nt0_dll.dll=0x7FDC0000">Reload</link> <b>nt0_dll.dll</b> 0x7FDC0000 <b>mapped to pid=0/0h</b>
|