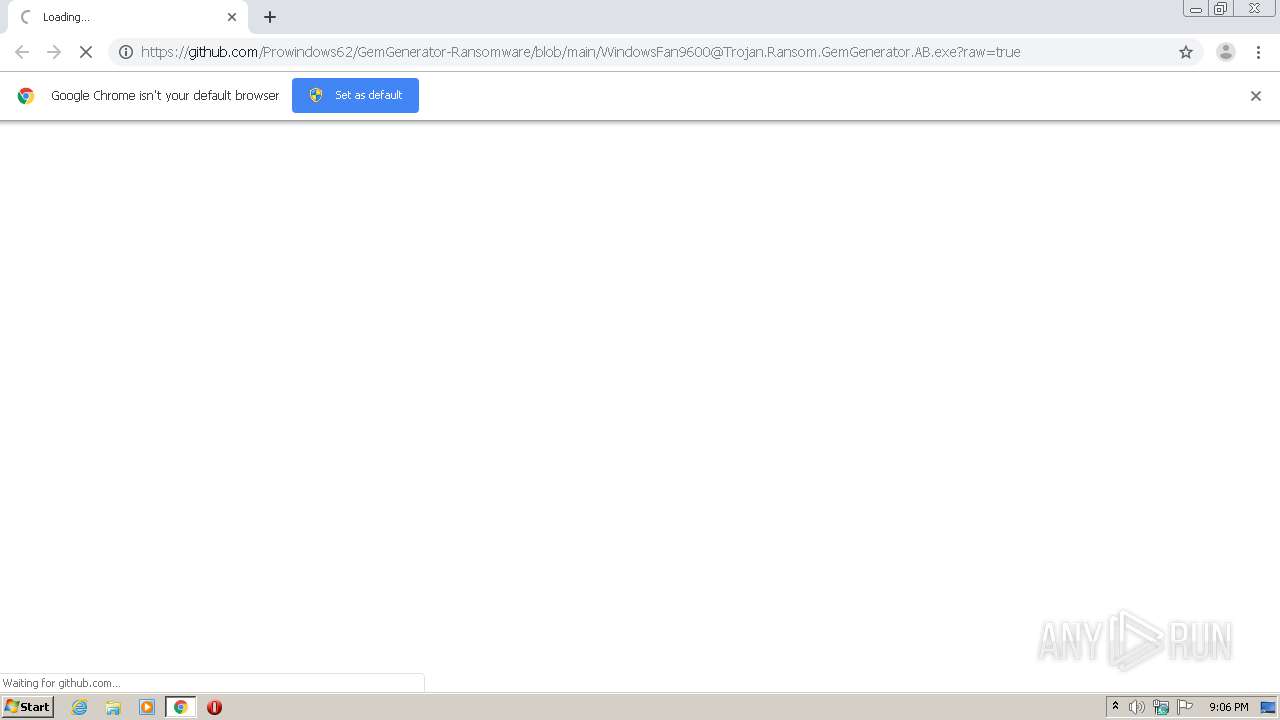
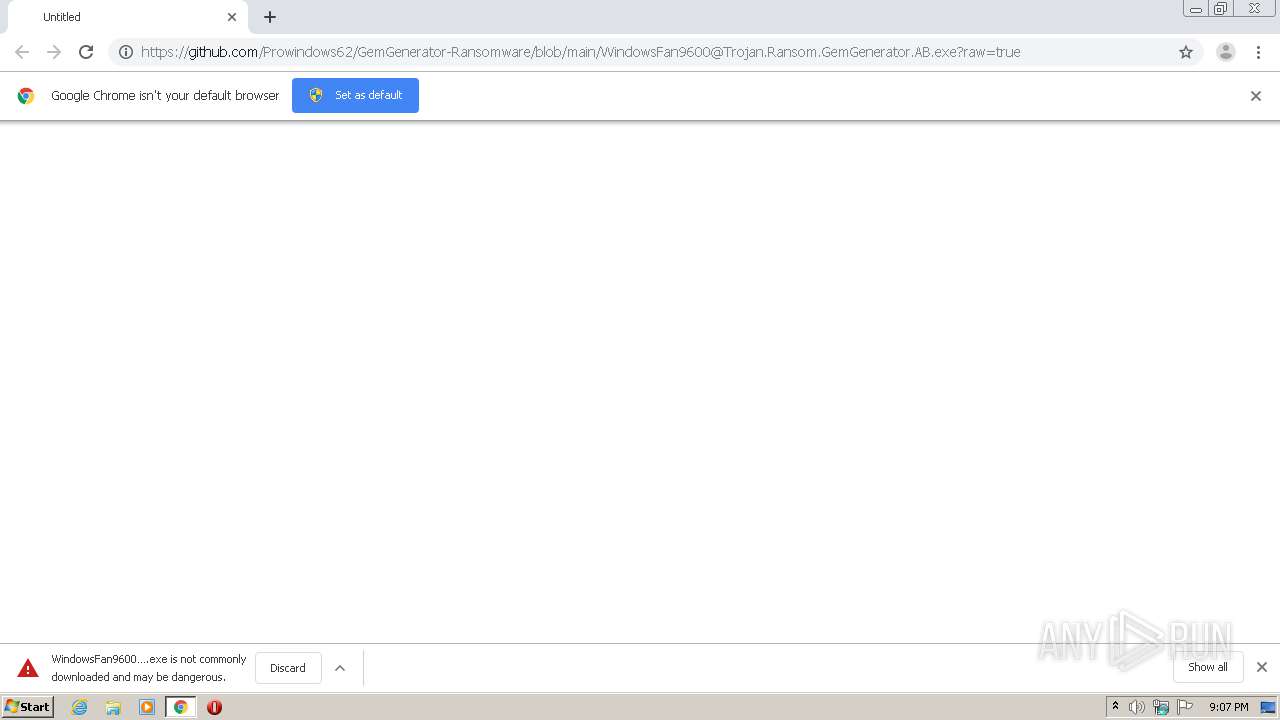
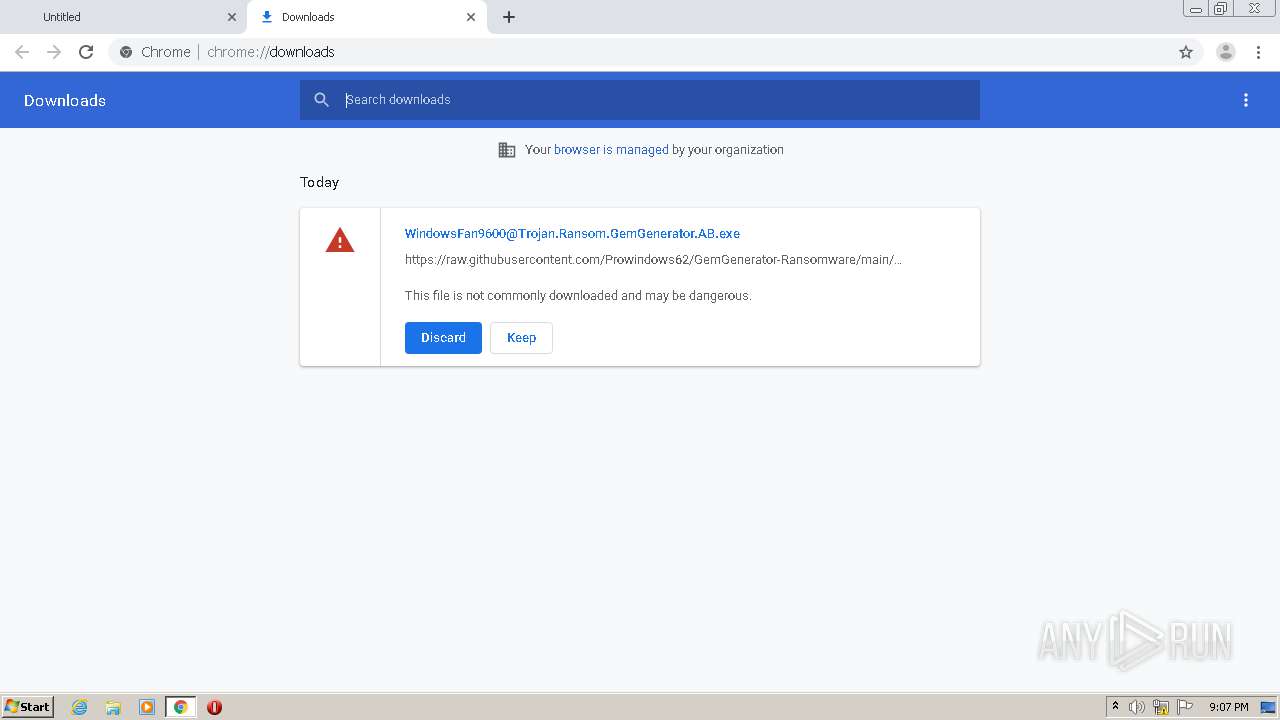
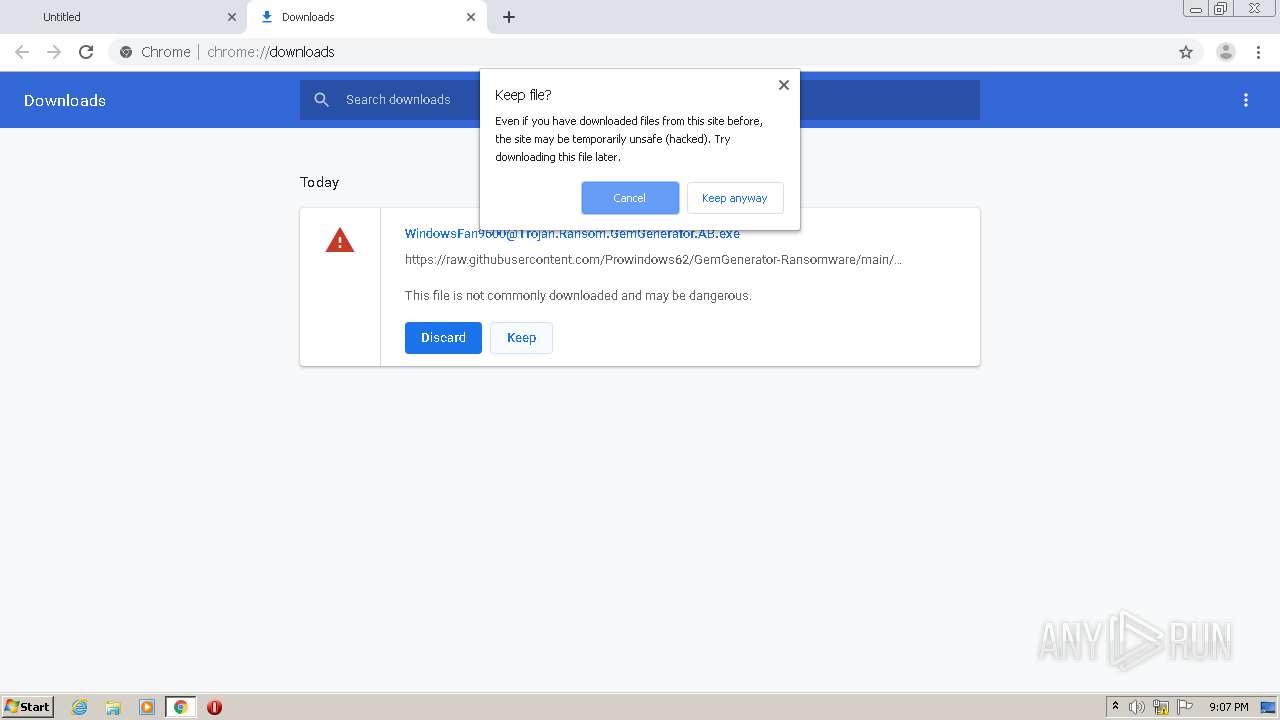
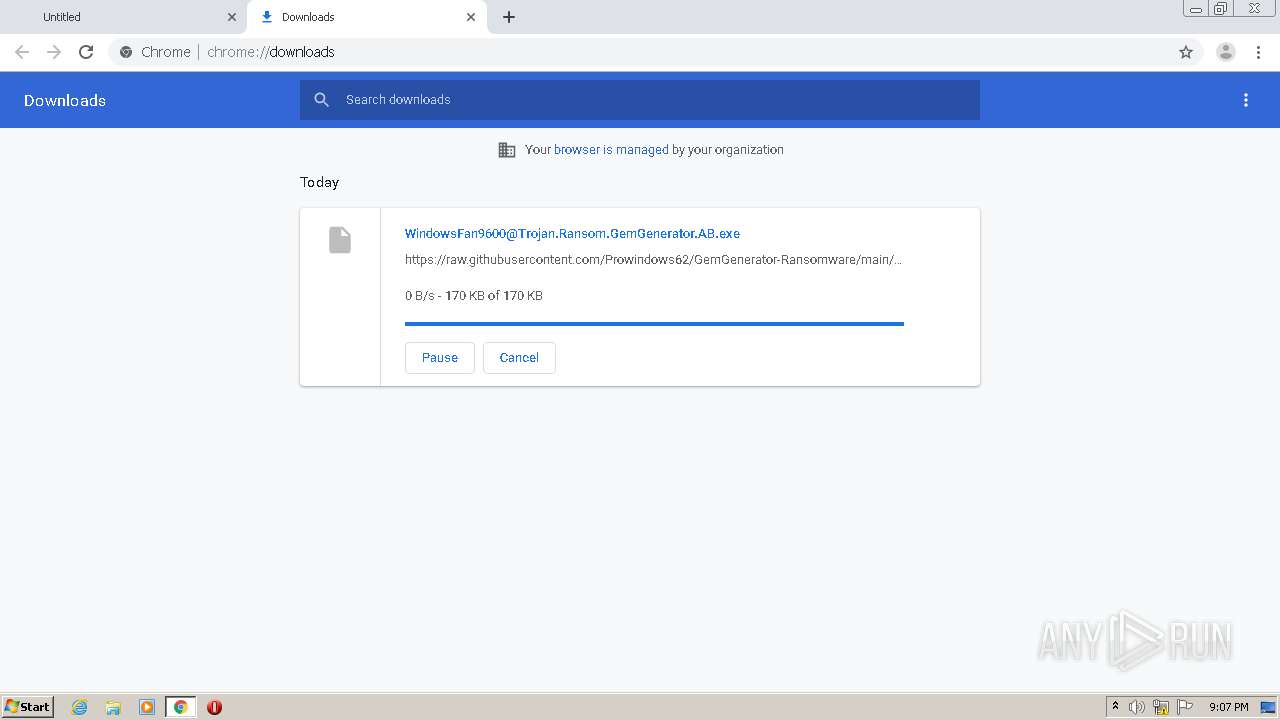
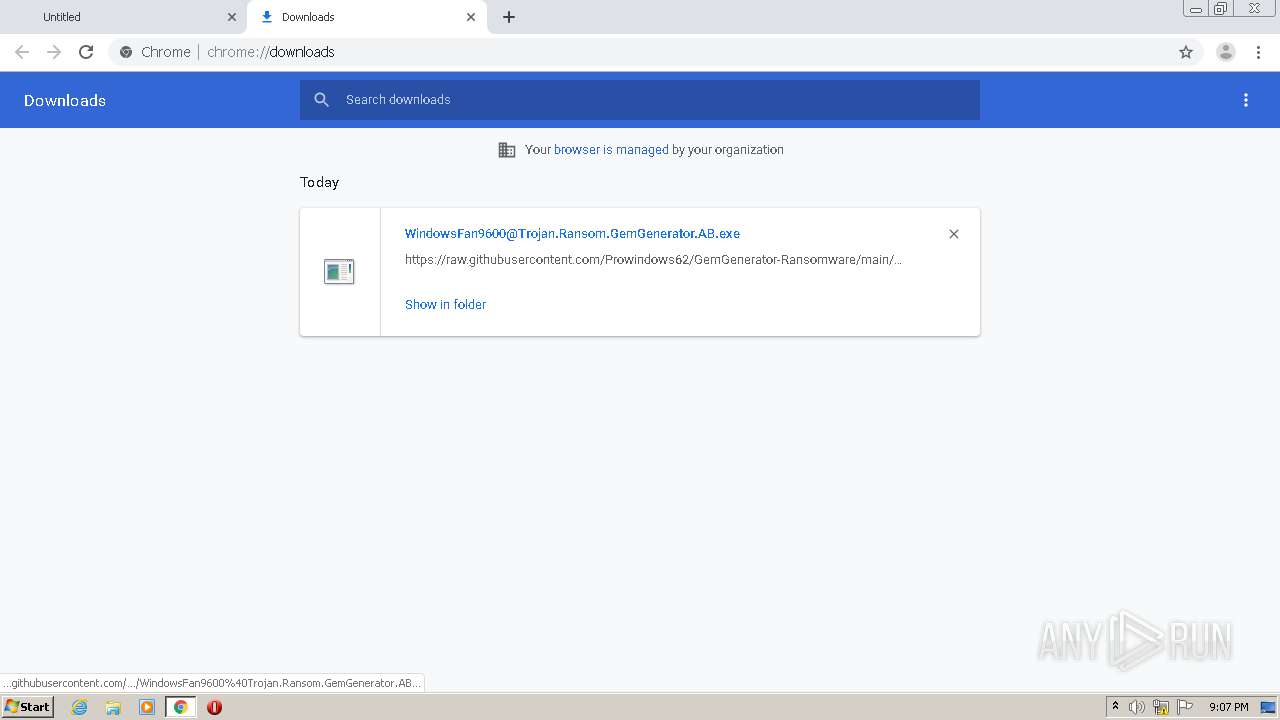
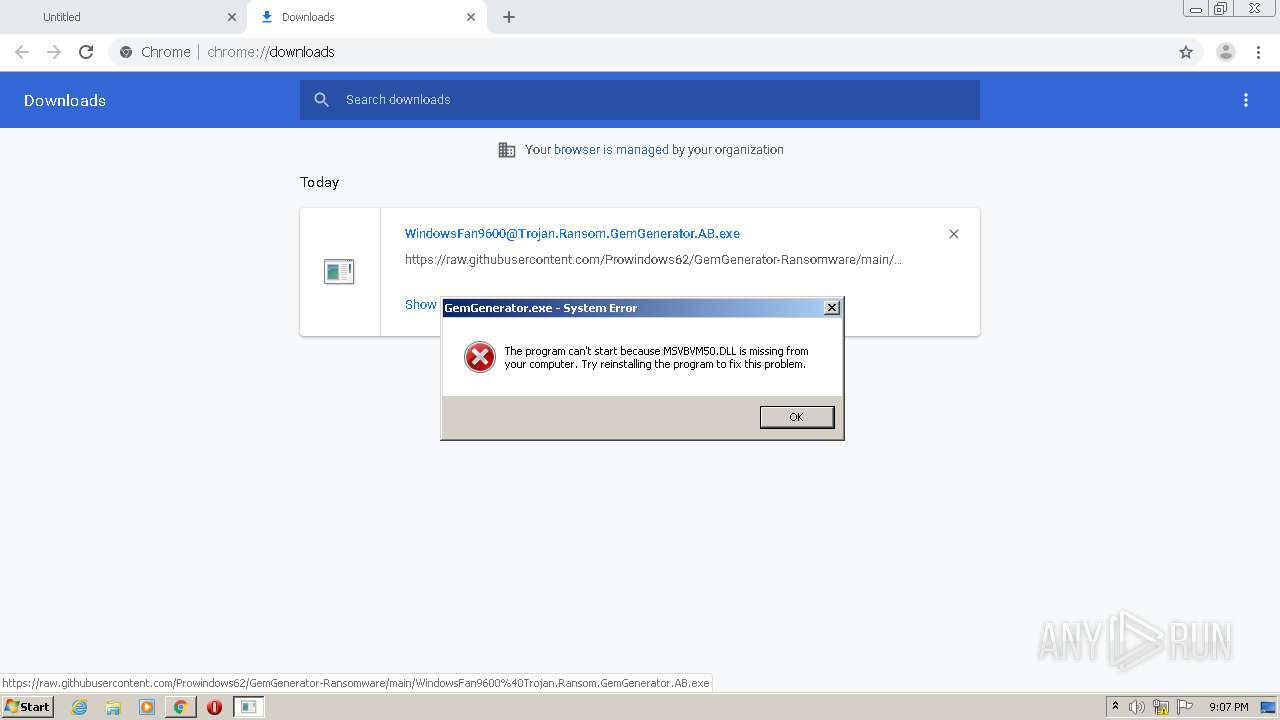
| URL: | https://github.com/Prowindows62/GemGenerator-Ransomware/blob/main/WindowsFan9600@Trojan.Ransom.GemGenerator.AB.exe?raw=true |
| Full analysis: | https://app.any.run/tasks/729403cb-9381-43af-af00-ba170b3dabf8 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2021, 21:06:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0CF59107B5281F04E5CA10CEE71FE11B |
| SHA1: | 401E14350F733C9905B9F4CF5C242BB1F6F22BE7 |
| SHA256: | E3AFA4F317E70DB06DA86A5F1A00D902A3090FDAB61C444DA403CFA903581AF9 |
| SSDEEP: | 3:N8tEdfMAZeIiALtTnhcTER9KSEV31KFt3NL4srH:2udMAZeIiutz6s9KSEnKj3NL4srH |
MALICIOUS
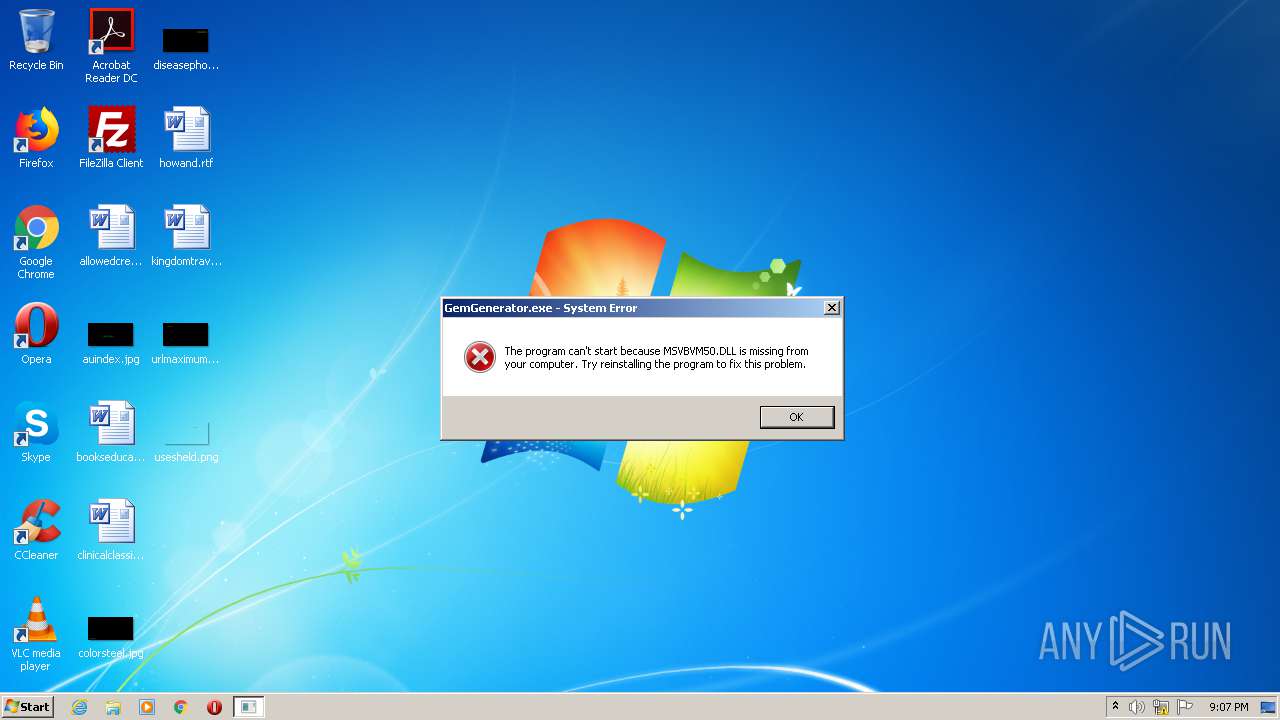
Application was dropped or rewritten from another process
- WindowsFan9600@Trojan.Ransom.GemGenerator.AB.exe (PID: 1764)
- WindowsFan9600@Trojan.Ransom.GemGenerator.AB.exe (PID: 3352)
- GemGenerator.exe (PID: 3928)
Drops executable file immediately after starts
- WindowsFan9600@Trojan.Ransom.GemGenerator.AB.exe (PID: 3352)
- cmd.exe (PID: 1404)
Changes Image File Execution Options
- reg.exe (PID: 1720)
- reg.exe (PID: 1360)
- reg.exe (PID: 1924)
- reg.exe (PID: 3480)
- reg.exe (PID: 3188)
- reg.exe (PID: 3004)
- reg.exe (PID: 1916)
- reg.exe (PID: 2648)
- reg.exe (PID: 2236)
- reg.exe (PID: 2588)
- reg.exe (PID: 1736)
Changes the autorun value in the registry
- reg.exe (PID: 2696)
- reg.exe (PID: 3504)
Renames files like Ransomware
- cmd.exe (PID: 1404)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 1404)
SUSPICIOUS
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1404)
Drops a file with too old compile date
- WindowsFan9600@Trojan.Ransom.GemGenerator.AB.exe (PID: 3352)
- cmd.exe (PID: 1404)
Executable content was dropped or overwritten
- chrome.exe (PID: 2384)
- WindowsFan9600@Trojan.Ransom.GemGenerator.AB.exe (PID: 3352)
- cmd.exe (PID: 1404)
Creates files in the Windows directory
- cmd.exe (PID: 1404)
Starts CMD.EXE for commands execution
- WindowsFan9600@Trojan.Ransom.GemGenerator.AB.exe (PID: 3352)
Drops a file with a compile date too recent
- WindowsFan9600@Trojan.Ransom.GemGenerator.AB.exe (PID: 3352)
- cmd.exe (PID: 1404)
INFO
Reads the hosts file
- chrome.exe (PID: 2384)
- chrome.exe (PID: 3924)
Application launched itself
- chrome.exe (PID: 2384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
77
Monitored processes
33
Malicious processes
4
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2548 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1360 | REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\regedit.exe" /v Debugger /t REG_SZ /d "C:\WINDOWS\Uninstaller.exe" /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1404 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\89AE.tmp\89AF.tmp\89B0.bat C:\Users\admin\Downloads\WindowsFan9600@Trojan.Ransom.GemGenerator.AB.exe" | C:\Windows\system32\cmd.exe | WindowsFan9600@Trojan.Ransom.GemGenerator.AB.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,10082183291116629357,12427503547483685030,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7289912988889129690 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,10082183291116629357,12427503547483685030,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16703808467849233488 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\taskmgr.exe" /v Debugger /t REG_SZ /d "C:\WINDOWS\Uninstaller.exe" /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1736 | REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exe" /v Debugger /t REG_SZ /d "C:\WINDOWS\Uninstaller.exe" /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,10082183291116629357,12427503547483685030,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4363827131234887478 --mojo-platform-channel-handle=3408 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1764 | "C:\Users\admin\Downloads\WindowsFan9600@Trojan.Ransom.GemGenerator.AB.exe" | C:\Users\admin\Downloads\WindowsFan9600@Trojan.Ransom.GemGenerator.AB.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1916 | REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\iexplore.exe" /v Debugger /t REG_SZ /d "C:\WINDOWS\Uninstaller.exe" /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
991
Read events
911
Write events
77
Delete events
3
Modification events
| (PID) Process: | (956) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2384-13261180007800750 |
Value: 259 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2384) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
13
Suspicious files
18
Text files
116
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-605CFB68-950.pma | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\746eb660-e2e4-4a32-9da8-815a051ab22f.tmp | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFd8d9a.TMP | text | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFd8f9e.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
11
DNS requests
7
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3924 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3924 | chrome.exe | 185.199.111.133:443 | raw.githubusercontent.com | GitHub, Inc. | NL | suspicious |
3924 | chrome.exe | 216.58.214.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3924 | chrome.exe | 142.250.185.78:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
3924 | chrome.exe | 172.217.20.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3924 | chrome.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
accounts.google.com |
| shared |
raw.githubusercontent.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
safebrowsing.google.com |
| whitelisted |