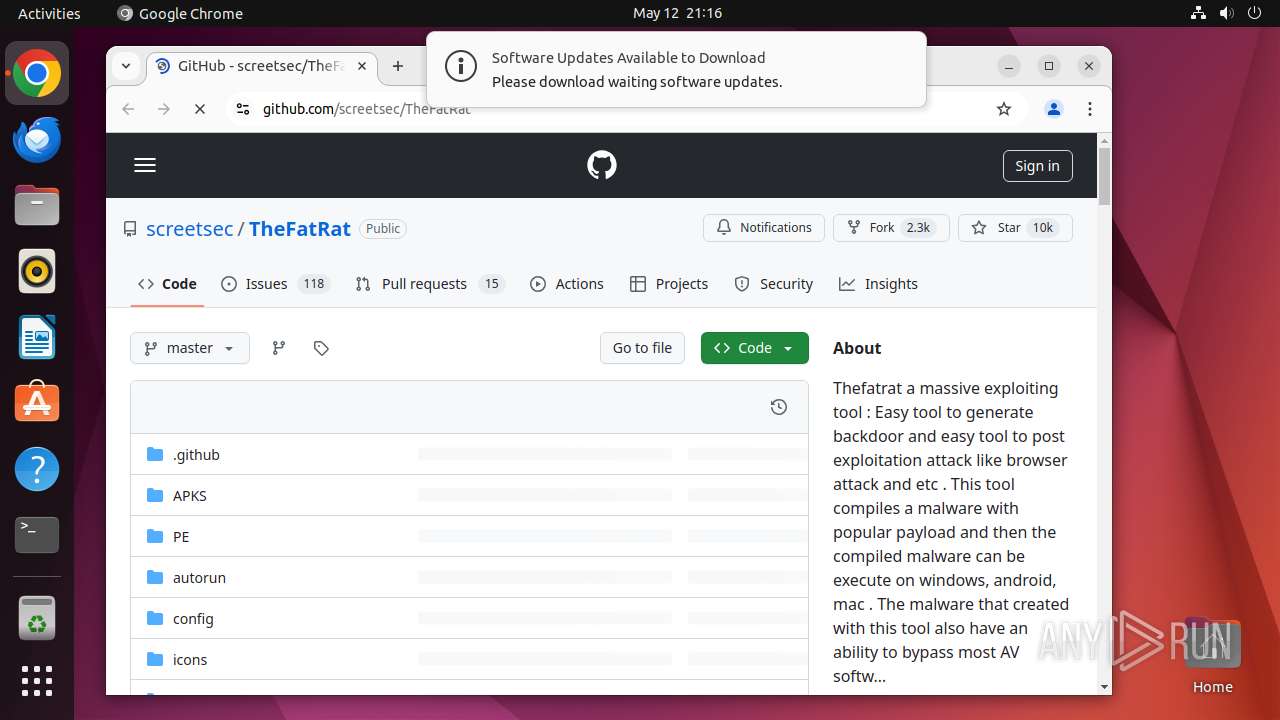
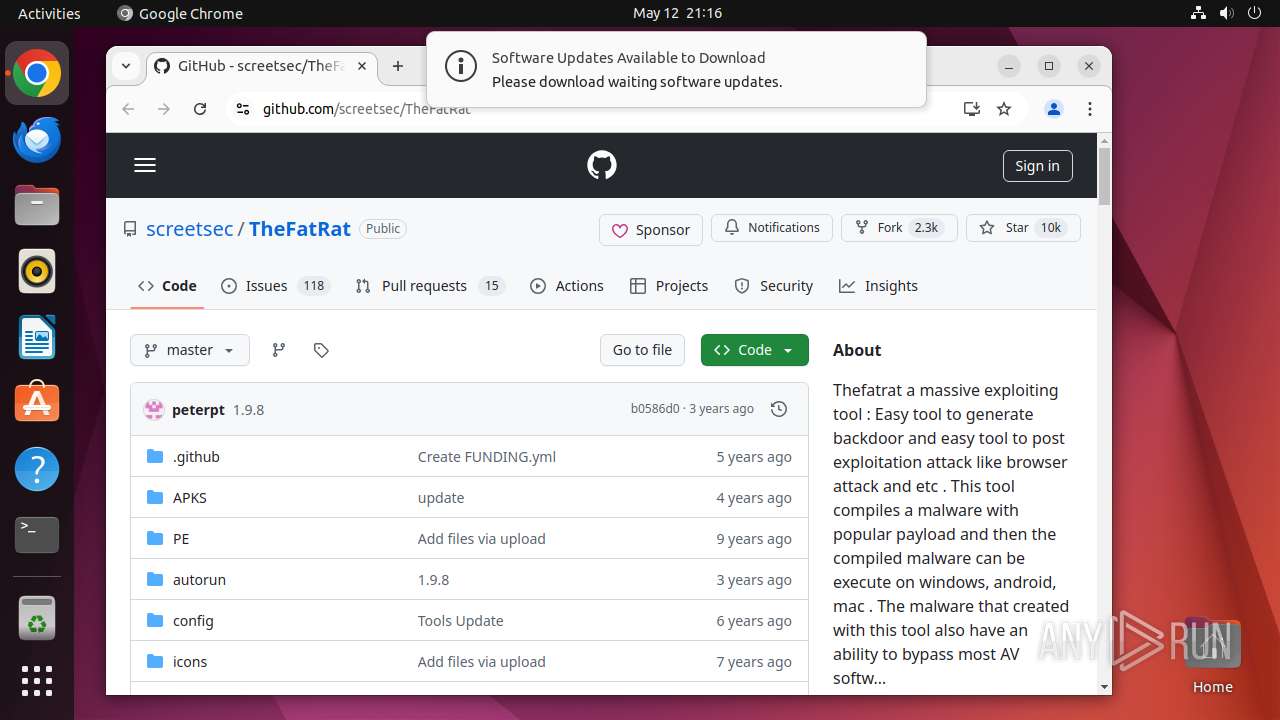
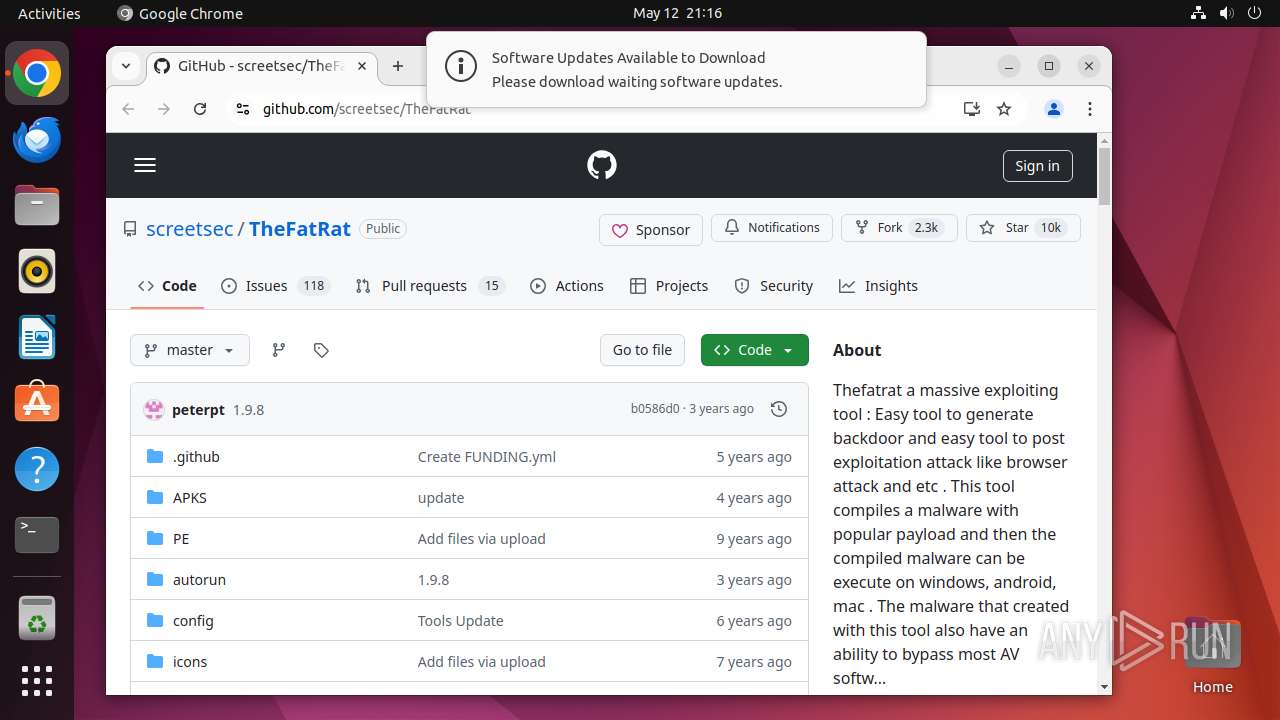
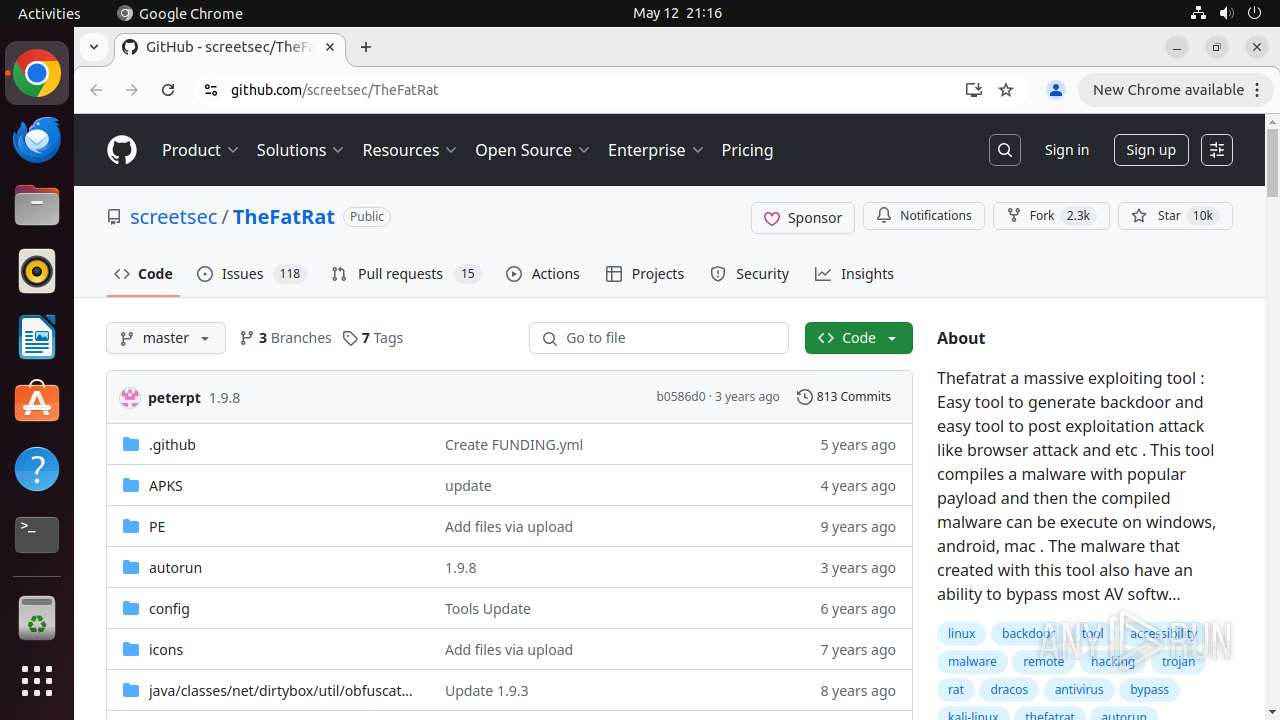
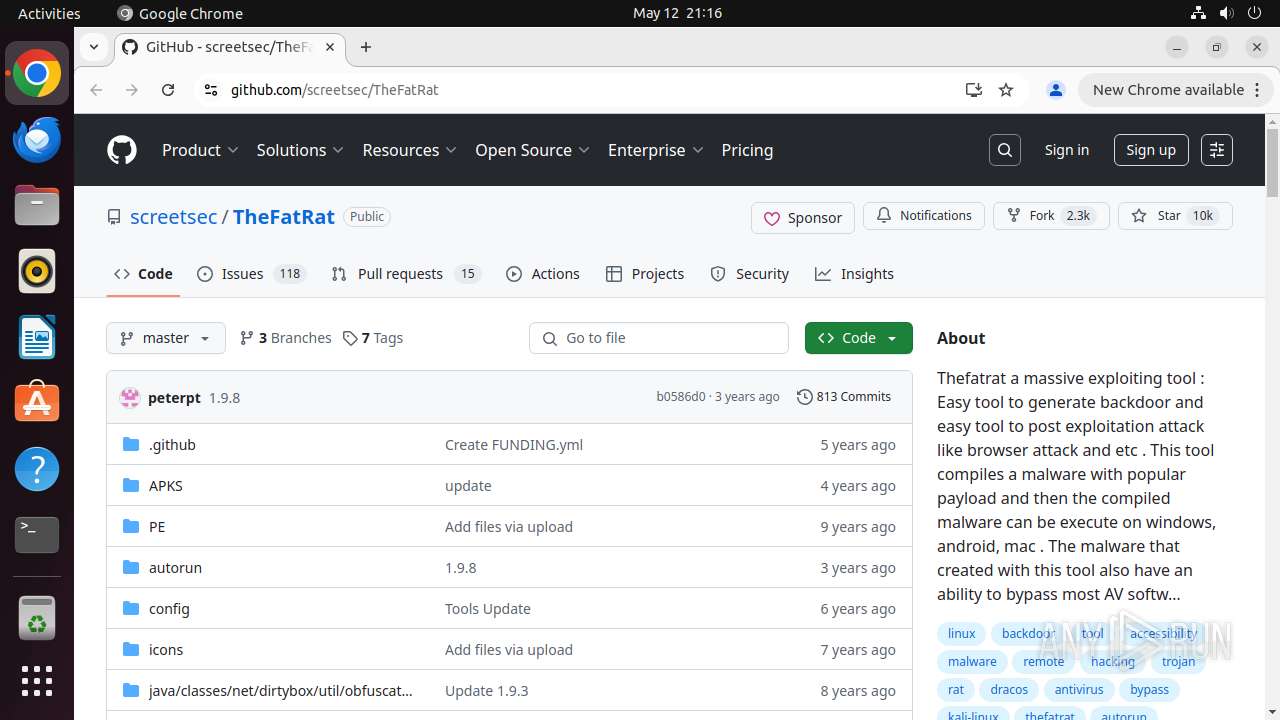
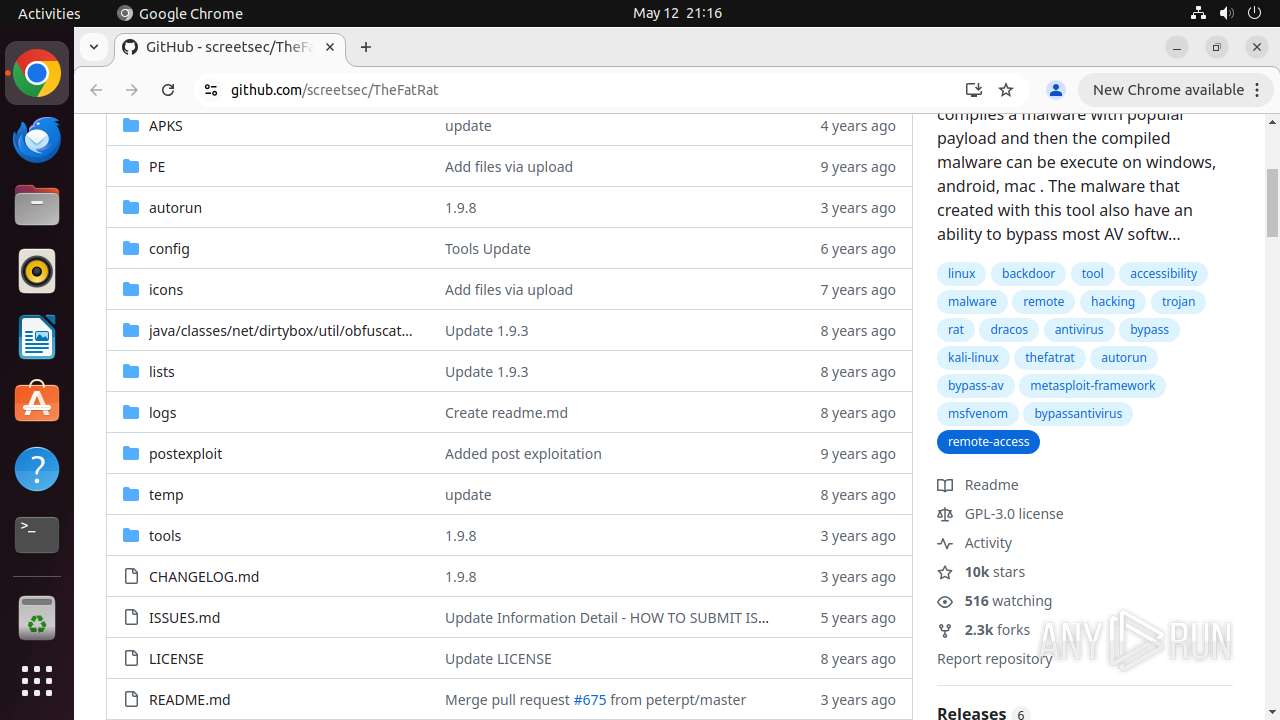
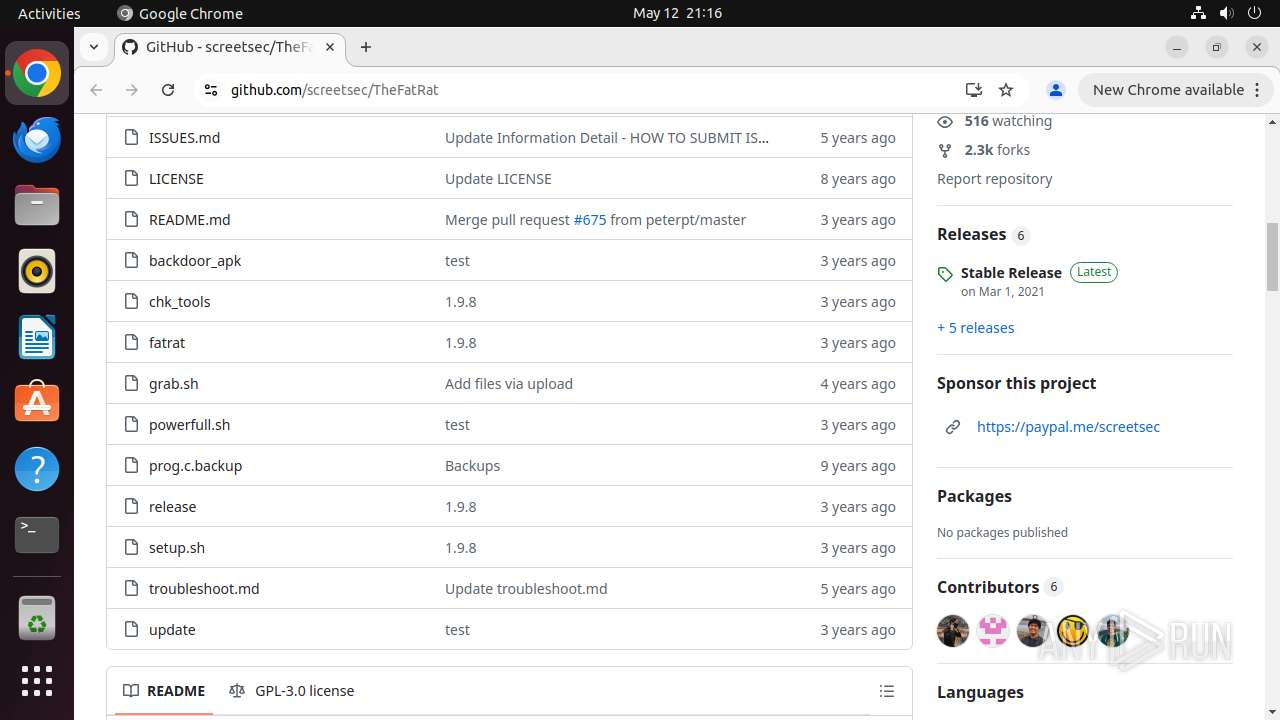
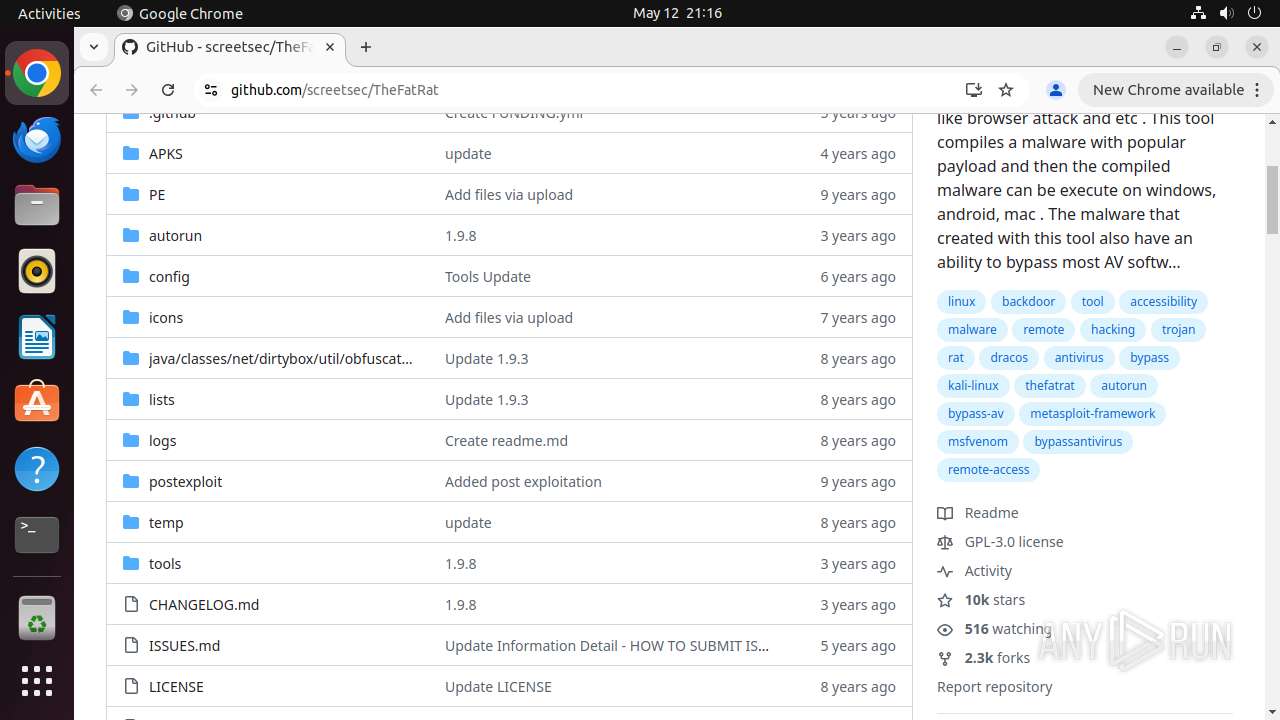
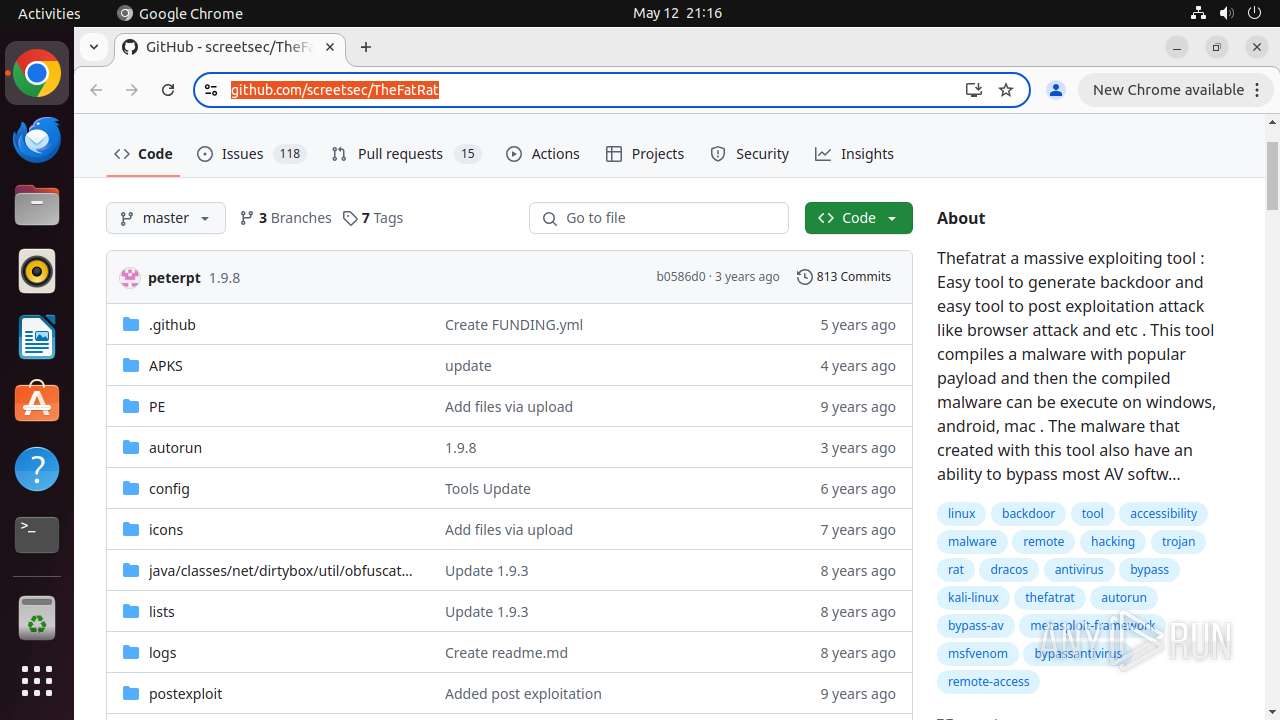
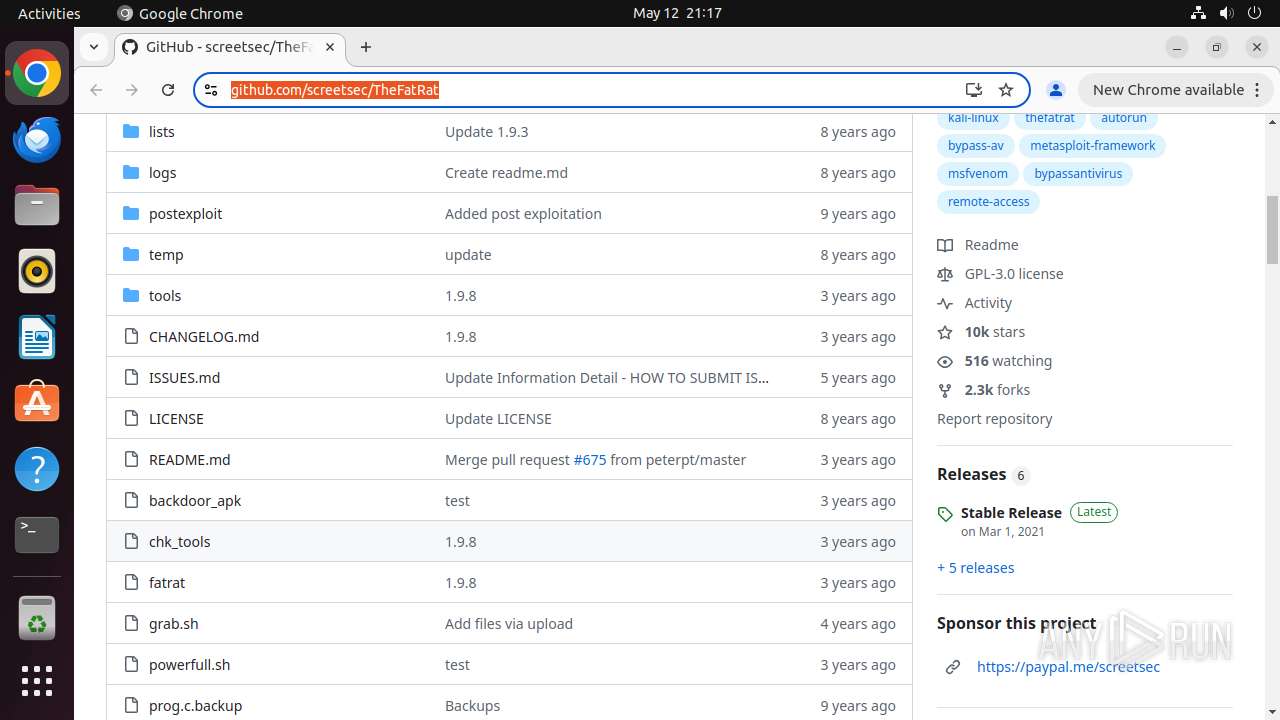
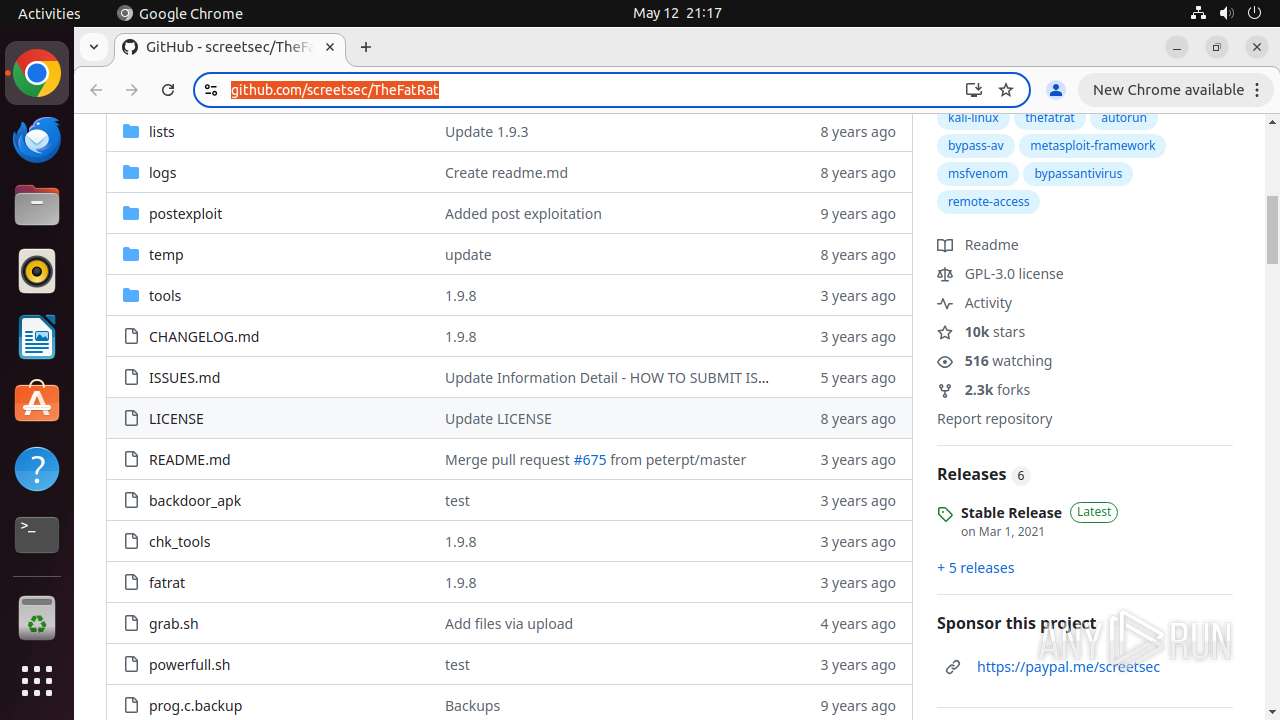
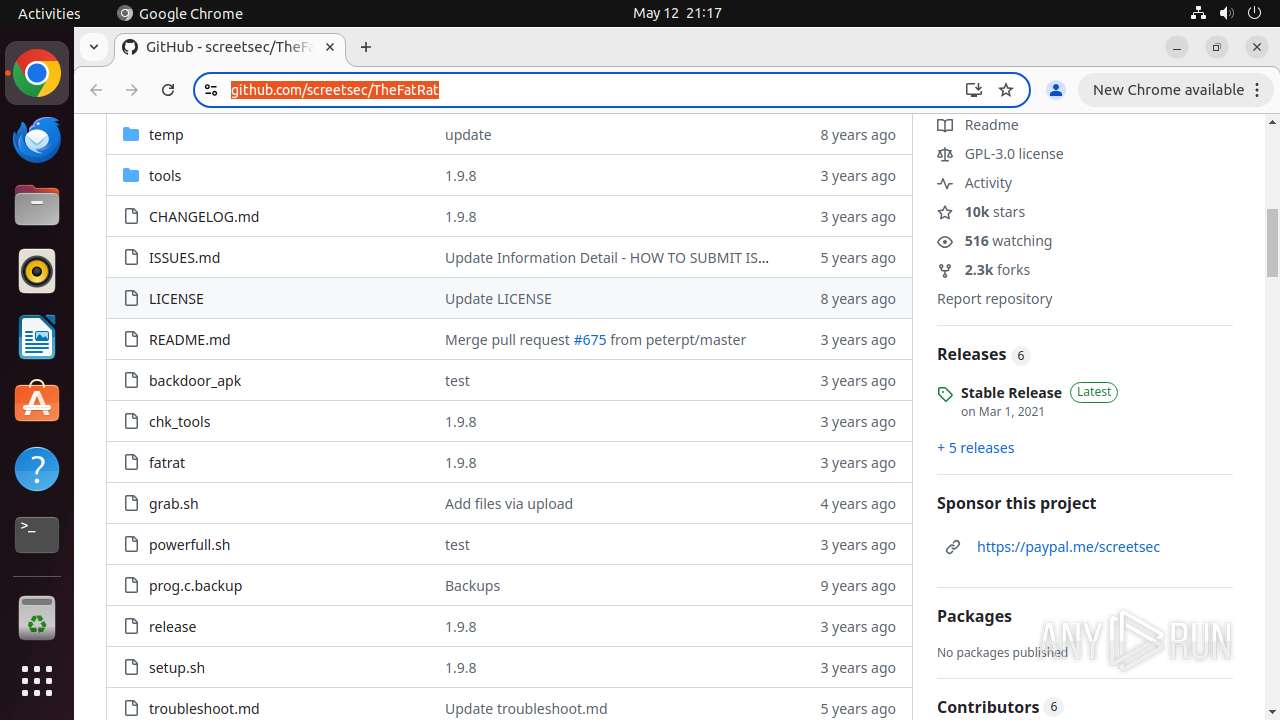
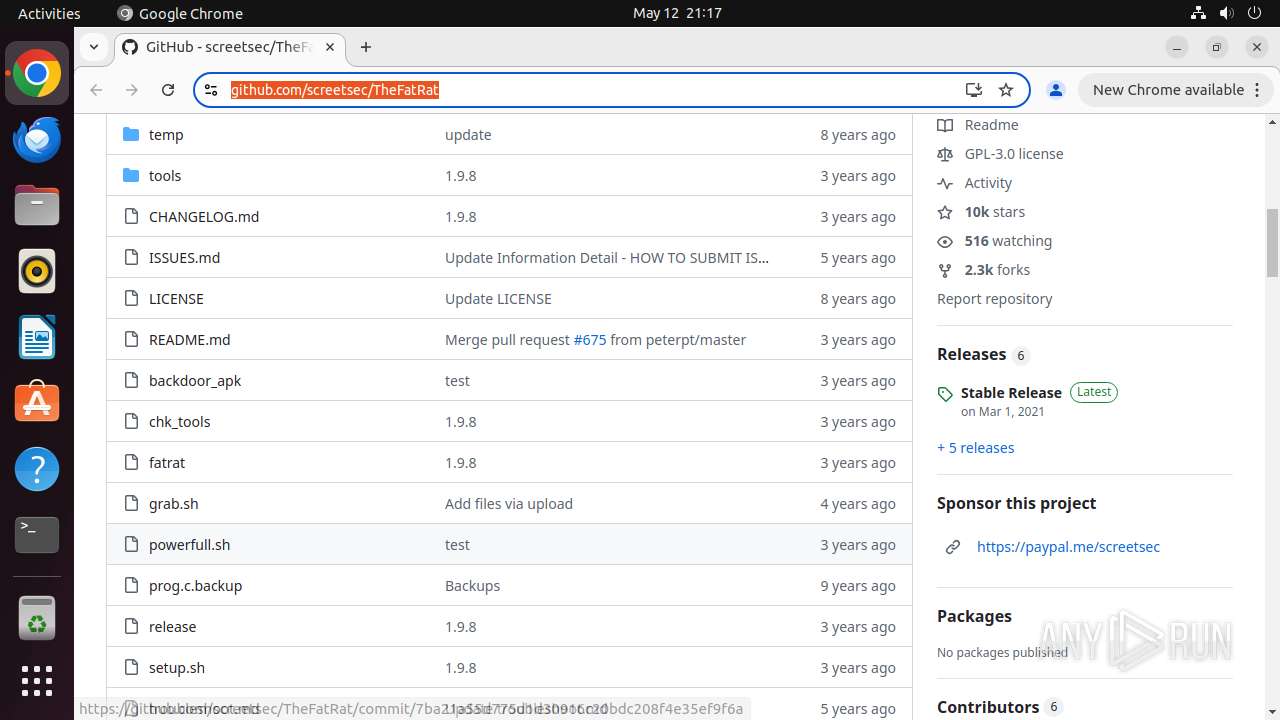
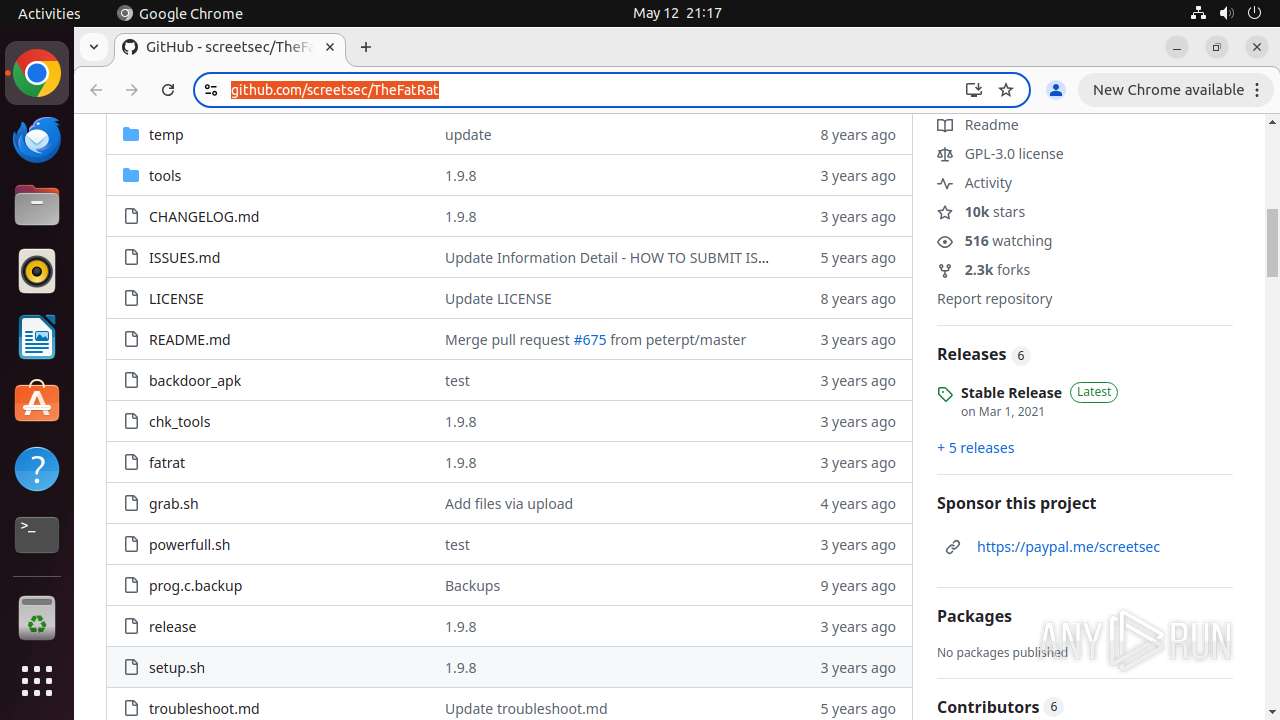
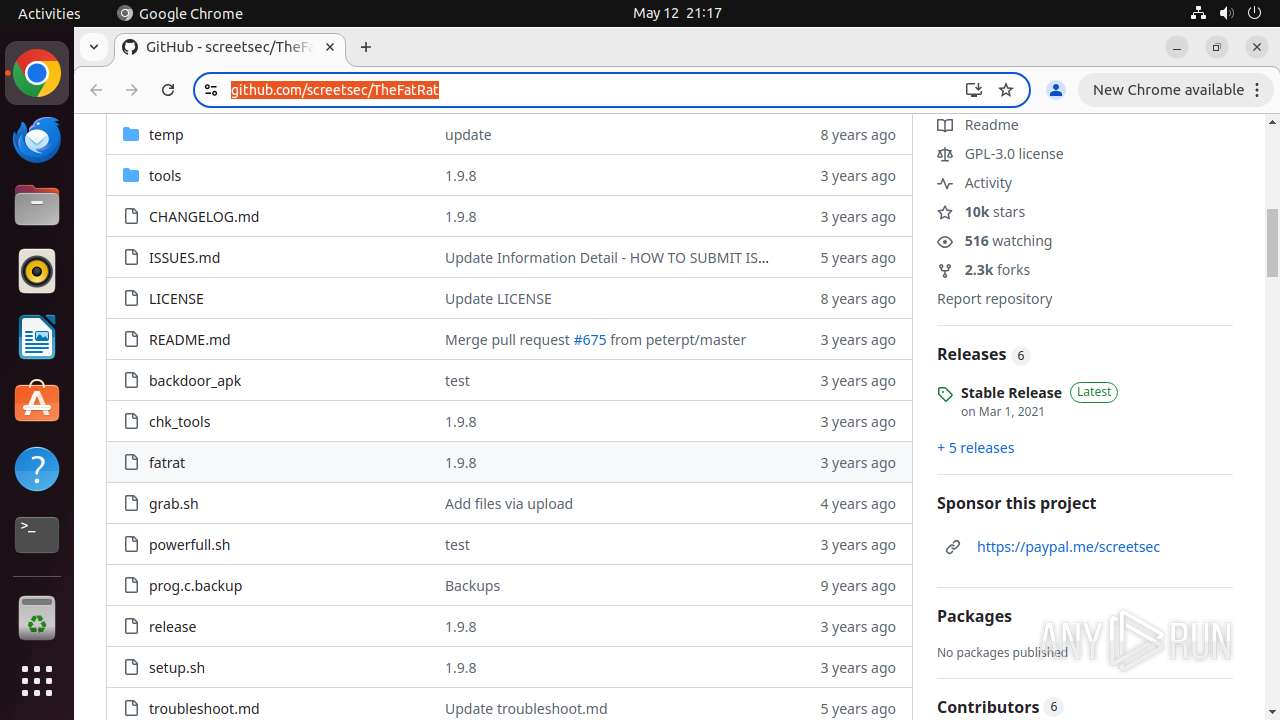
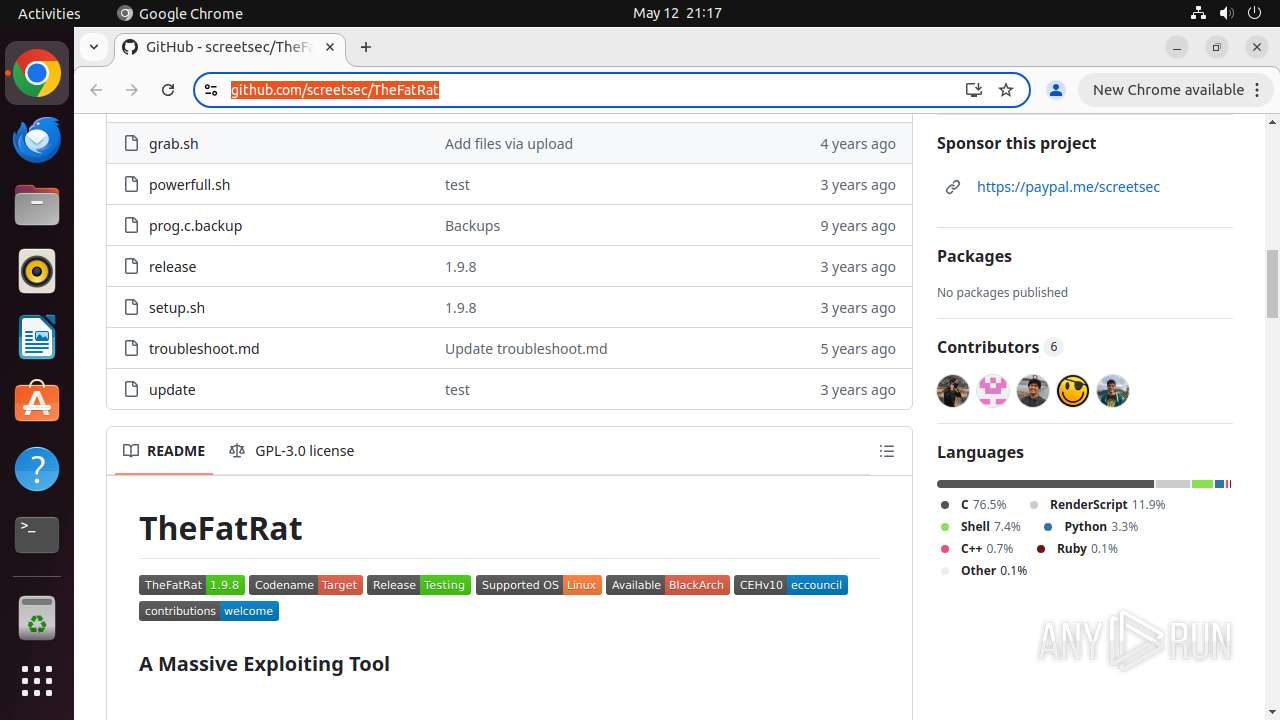
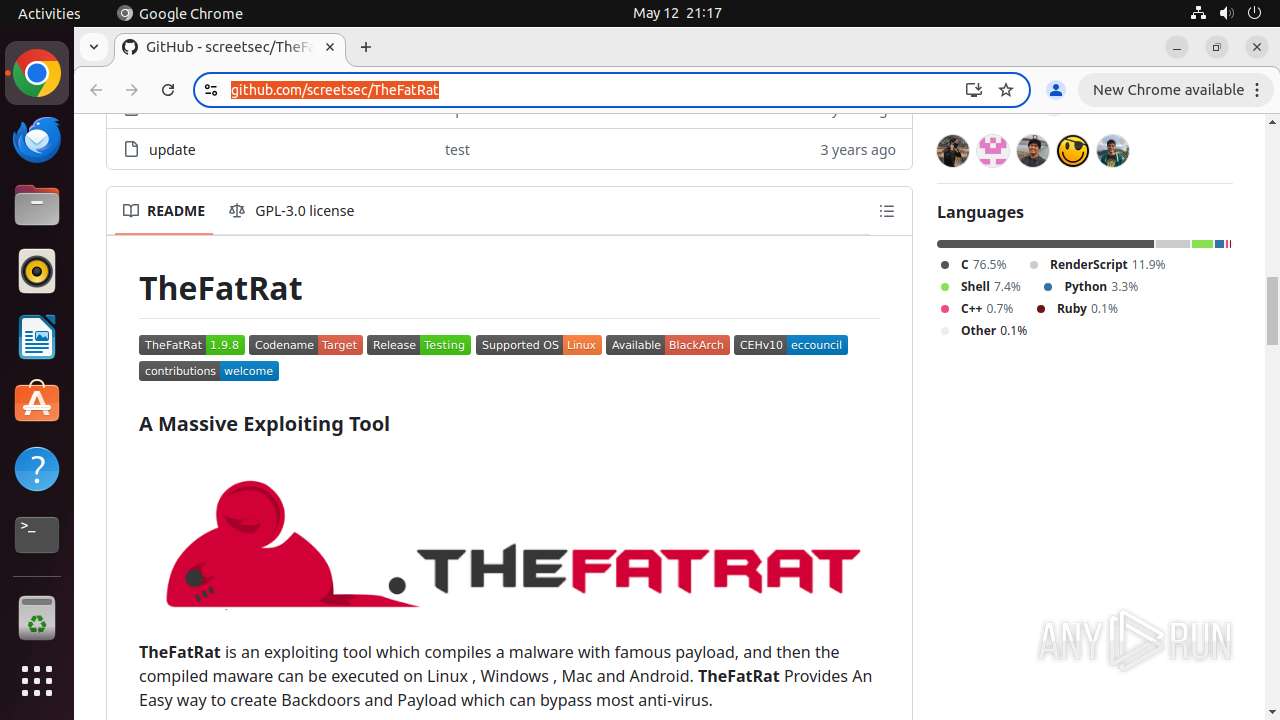
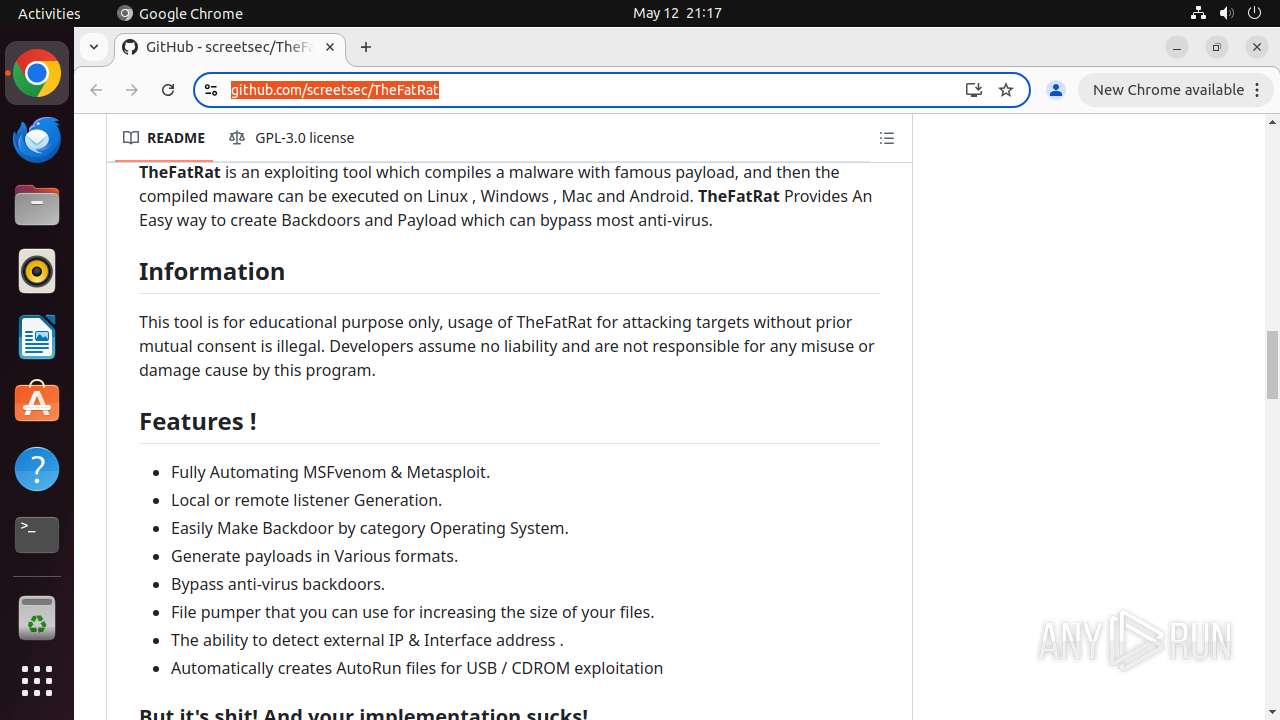
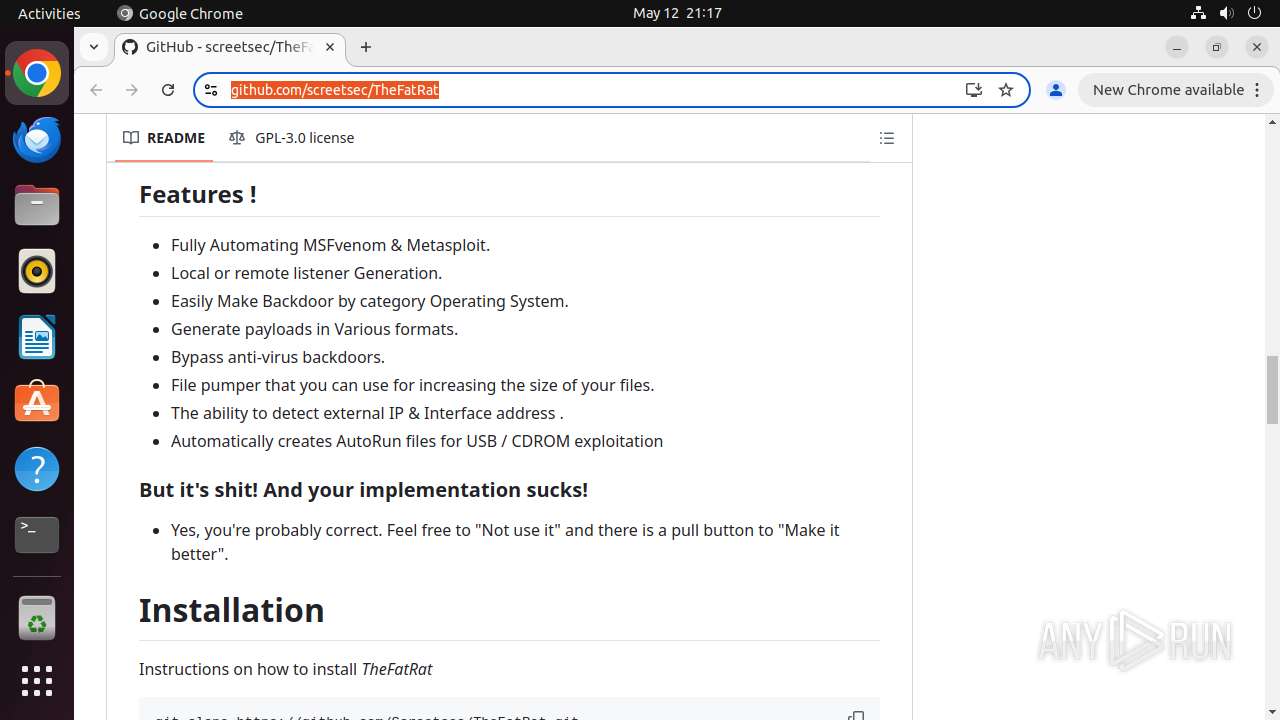
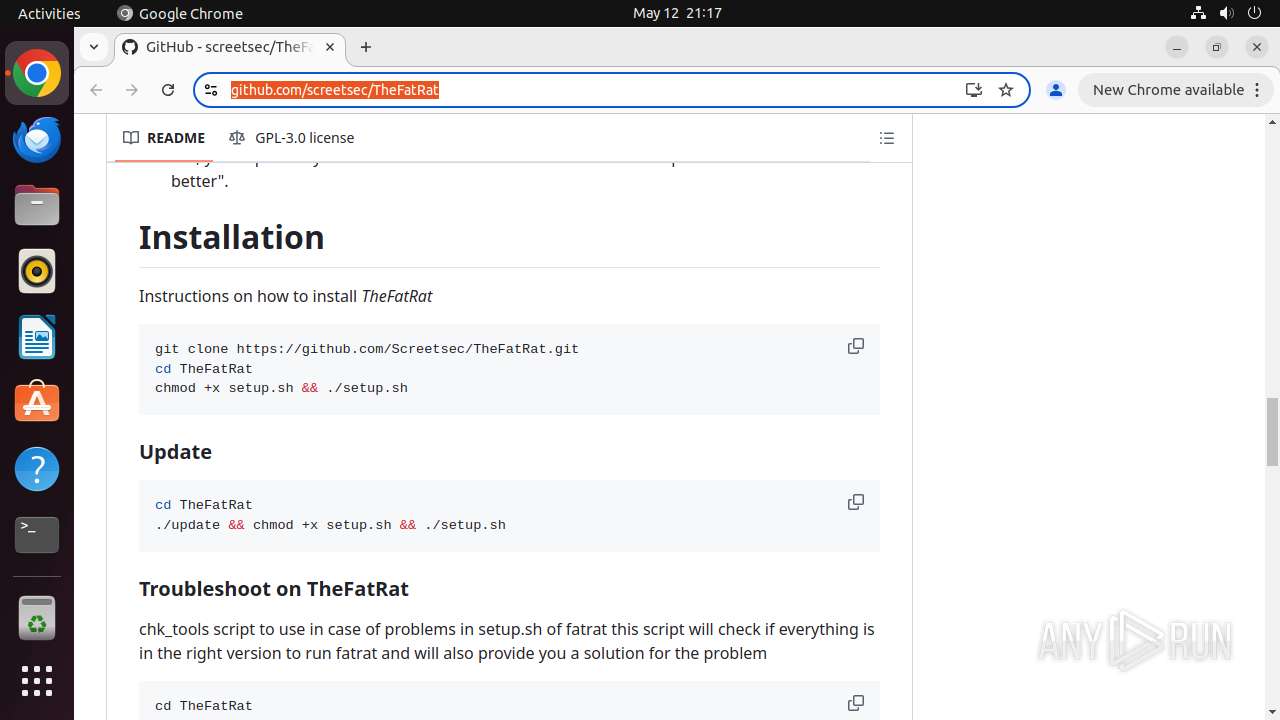
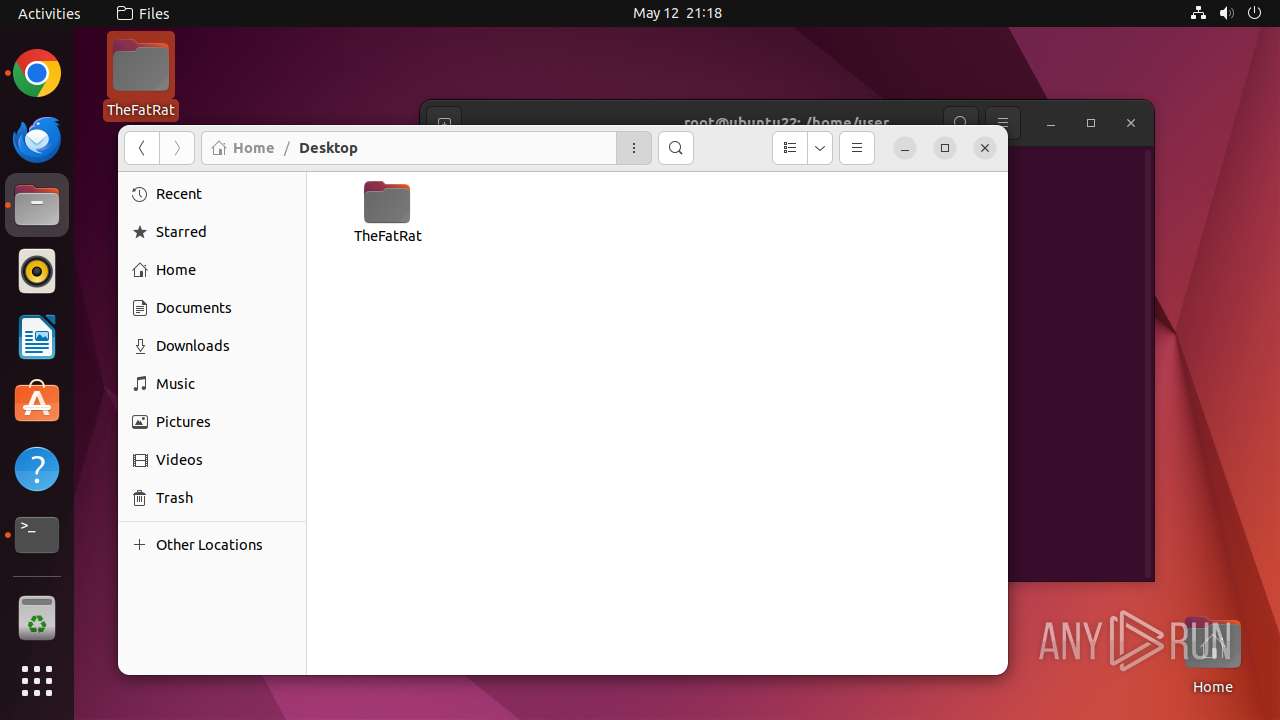
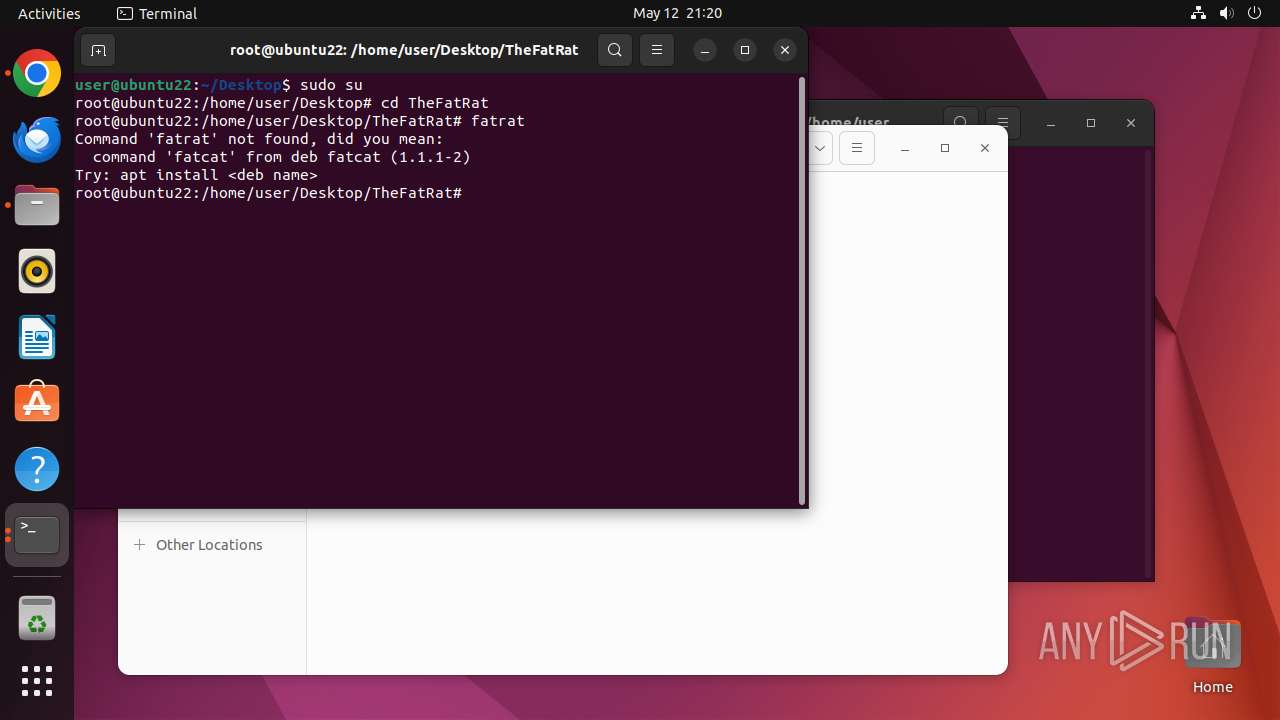
| URL: | https://github.com/screetsec/TheFatRat |
| Full analysis: | https://app.any.run/tasks/18e093ff-21a1-416a-ae80-59c69db66967 |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2025, 20:16:32 |
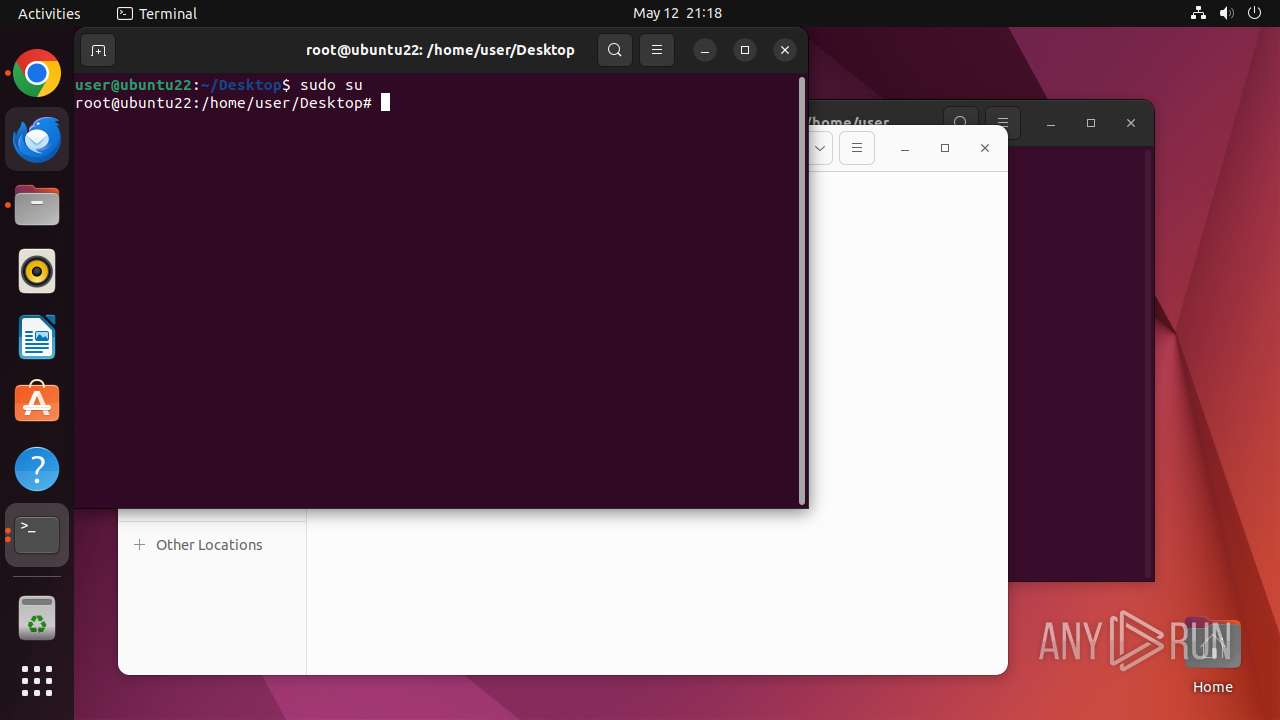
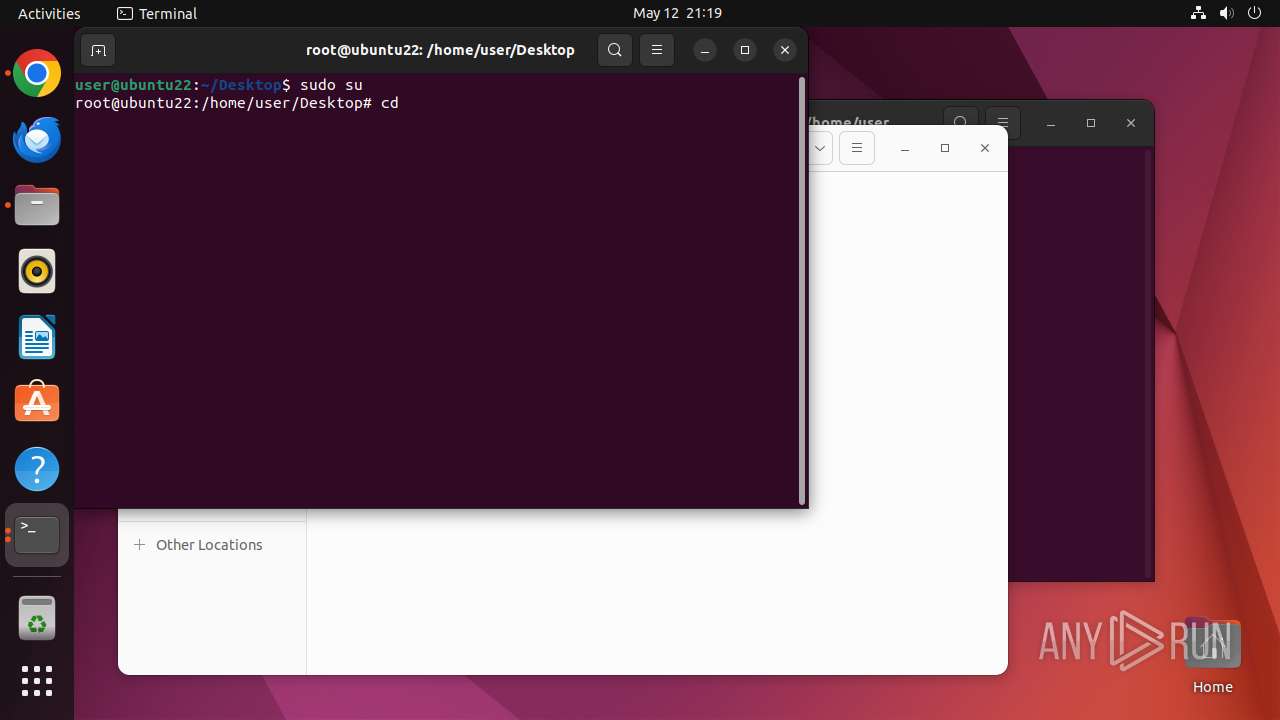
| OS: | Ubuntu 22.04.2 |
| MD5: | 1F0CBB072C0DB09E623A96BB6D267F3C |
| SHA1: | 4218A746F174681030BFFFC7A86A409739C4D721 |
| SHA256: | E3AA5489A35387AF8A316BE79ED4BF03334B9305EEE343A73579CE2B6B5396B2 |
| SSDEEP: | 3:N8tEdmGVwj2TRo:2uwdjd |
MALICIOUS
No malicious indicators.SUSPICIOUS
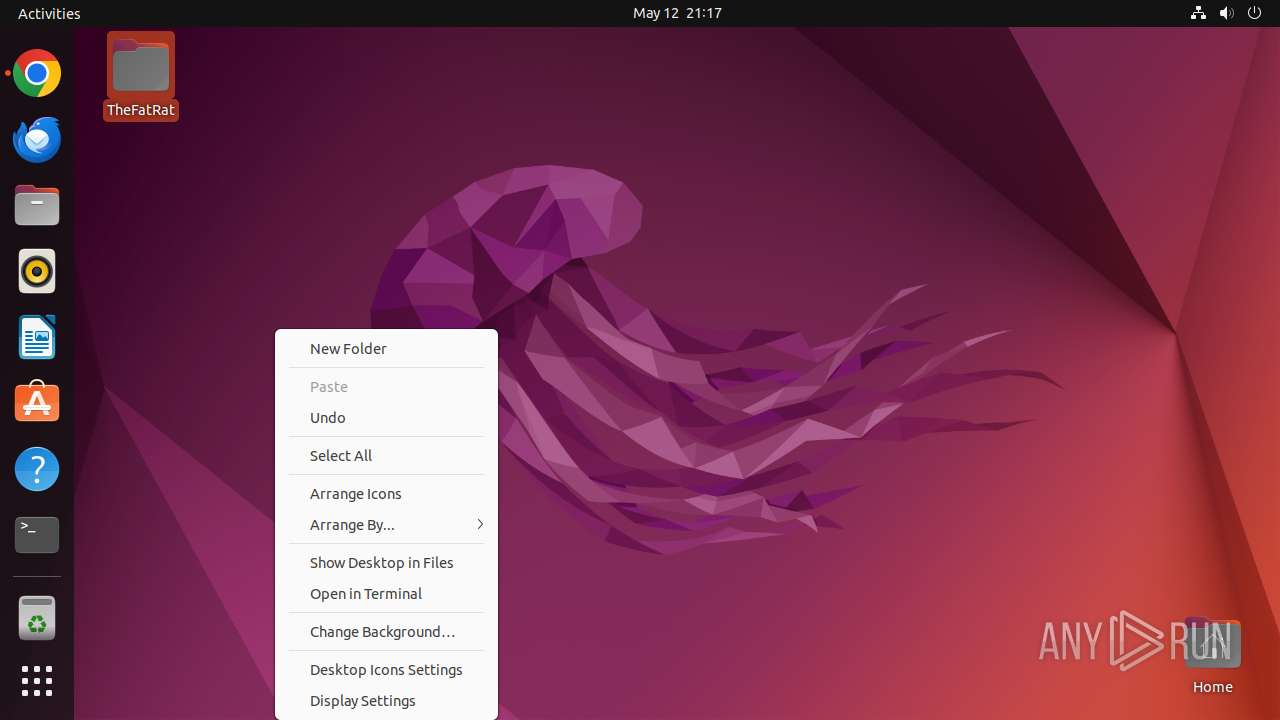
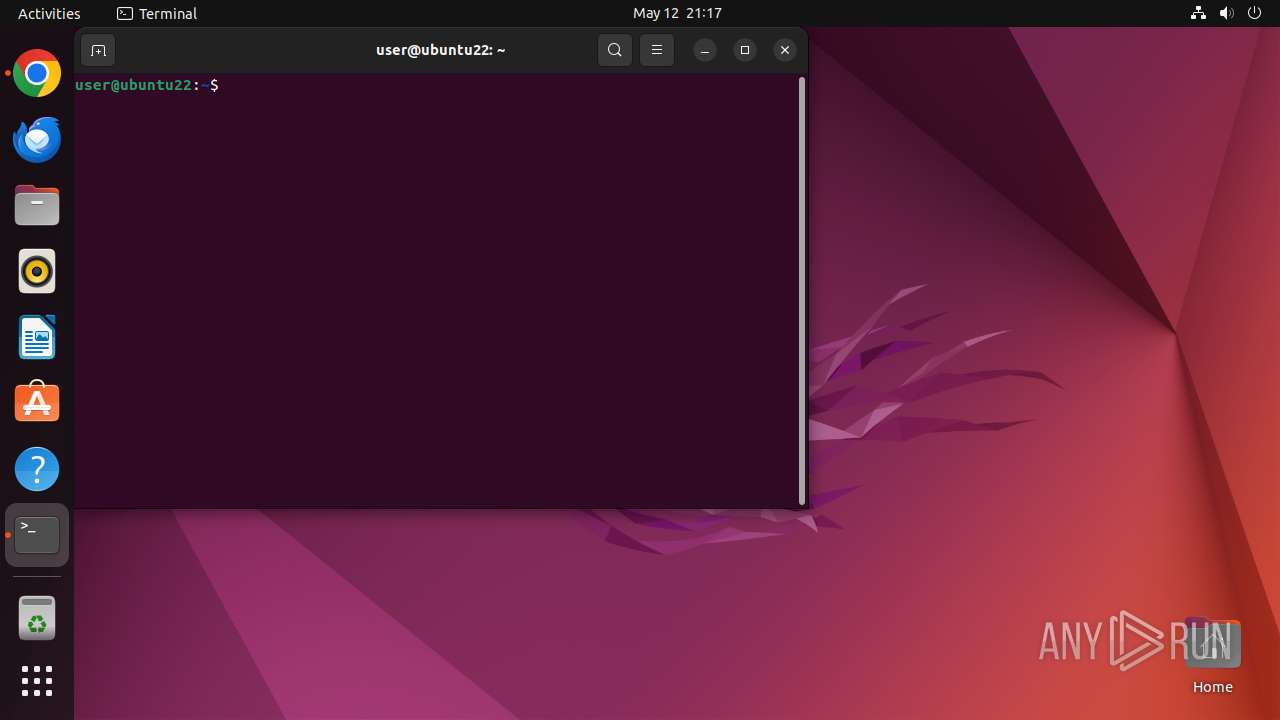
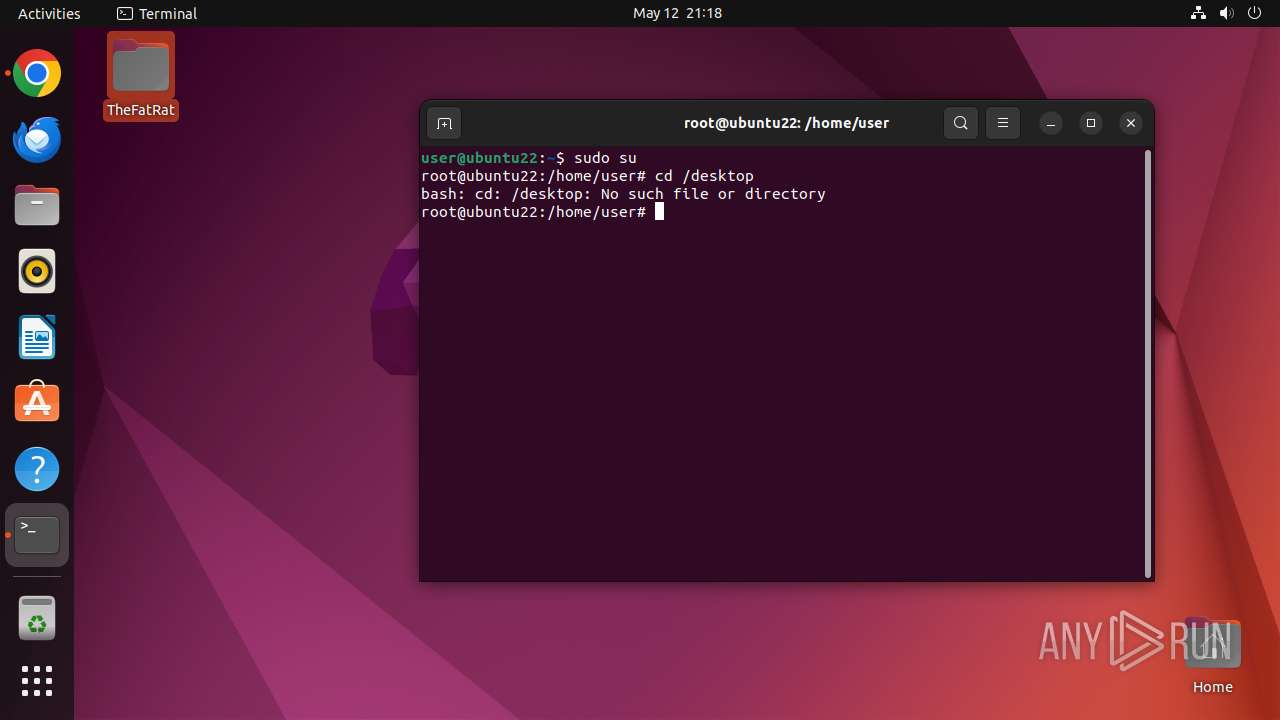
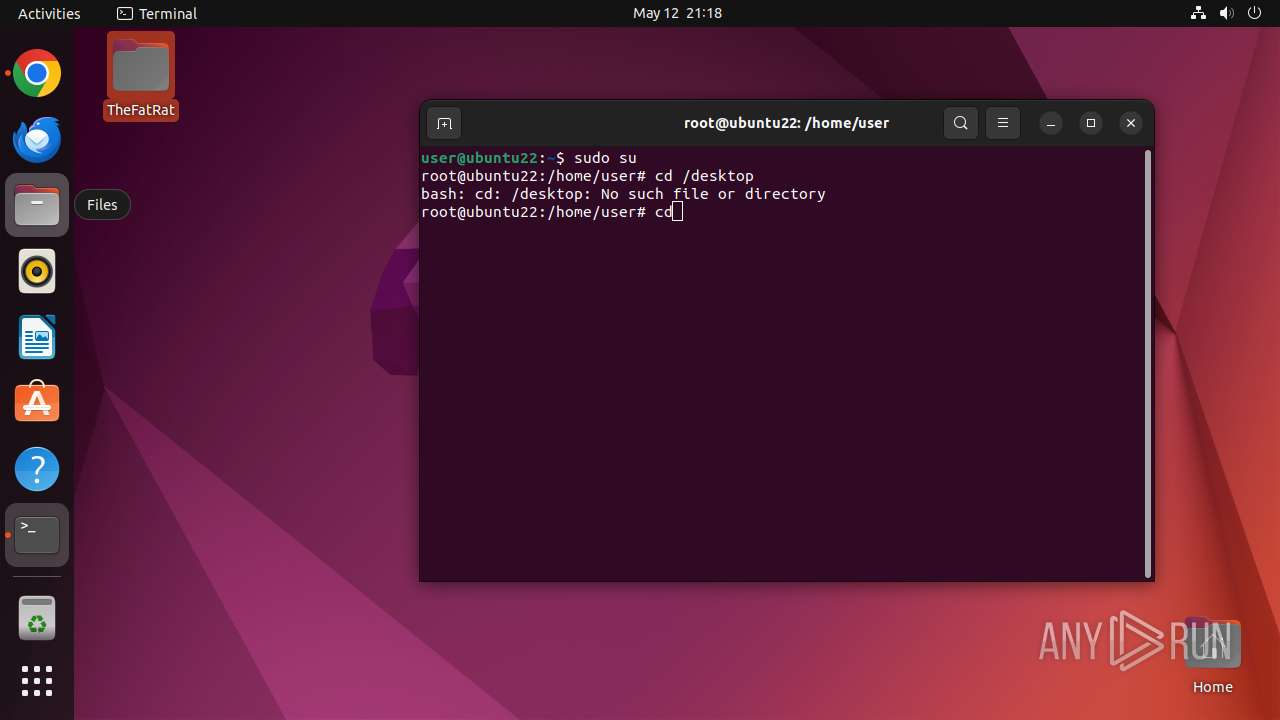
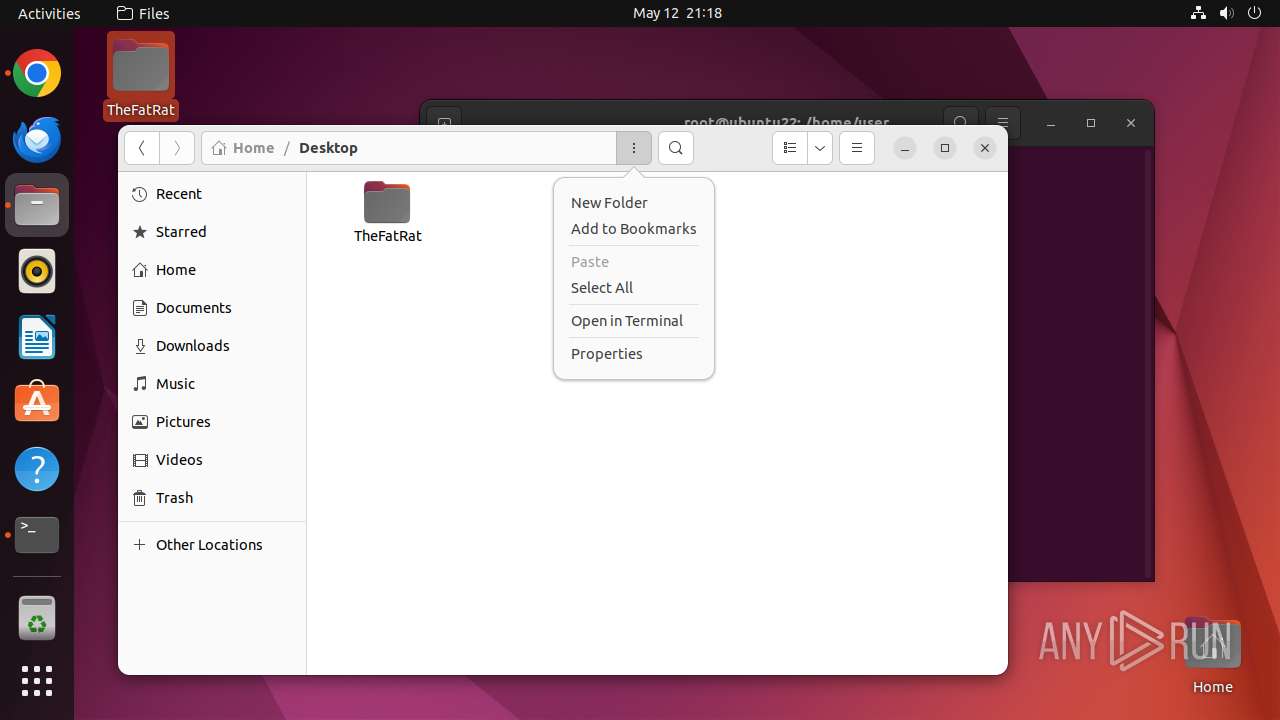
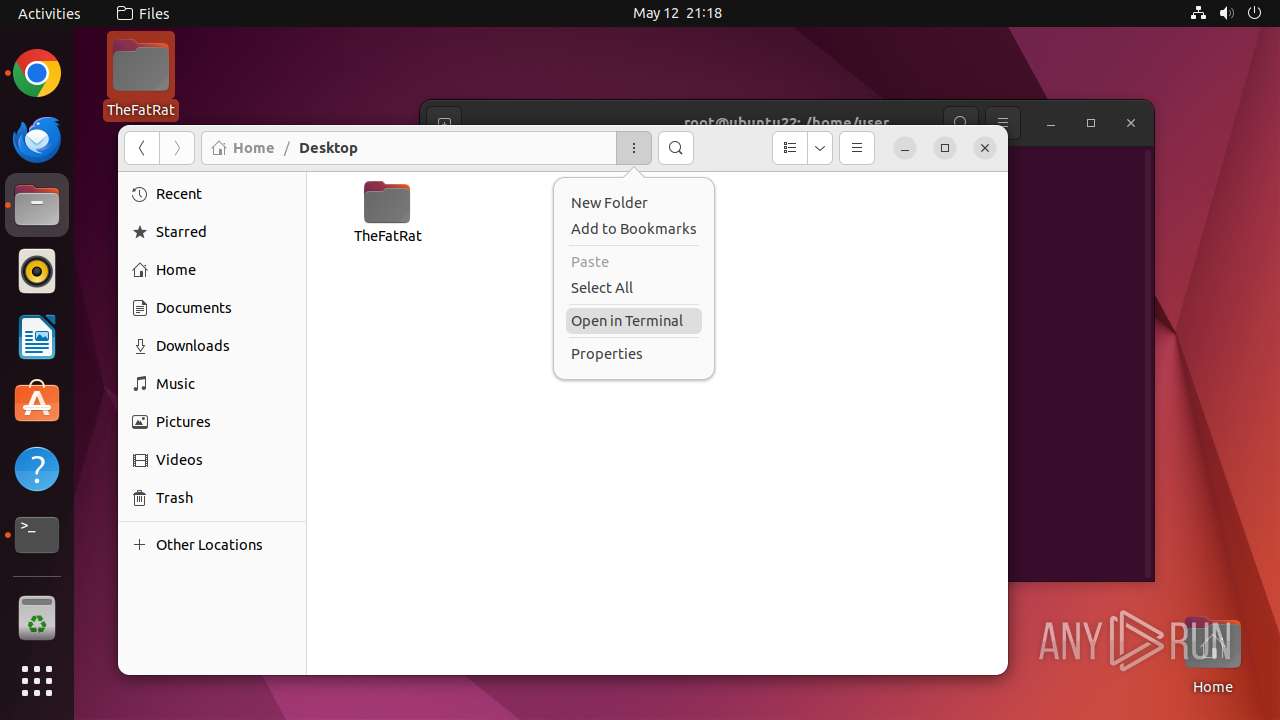
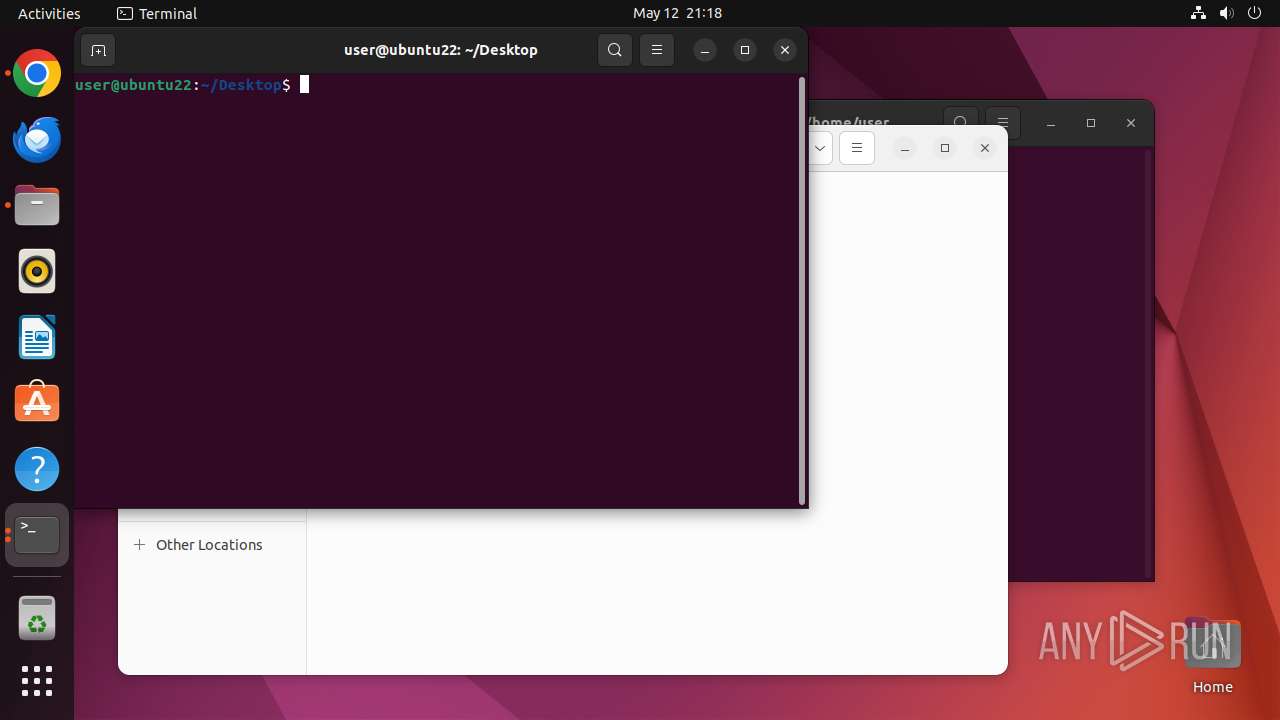
Executes commands using command-line interpreter
- chrome (PID: 40658)
- sudo (PID: 40656)
- gnome-terminal-server (PID: 40952)
- su (PID: 41108)
- su (PID: 40995)
Reads passwd file
- su (PID: 41108)
- su (PID: 40995)
INFO
Checks timezone
- chrome (PID: 40658)
- su (PID: 41108)
- python3.10 (PID: 40945)
- su (PID: 40995)
- python3.10 (PID: 41118)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
363
Monitored processes
142
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 40655 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://github\.com/screetsec/TheFatRat " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 40656 | sudo -iu user google-chrome https://github.com/screetsec/TheFatRat | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 40657 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40658 | /usr/bin/google-chrome https://github.com/screetsec/TheFatRat | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 40659 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40660 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40661 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40662 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40663 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 40664 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
Executable files
13
Suspicious files
359
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 40925 | nautilus | /home/user/.local/share/nautilus/tags/meta.db | binary | |
MD5:— | SHA256:— | |||
| 40658 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40658 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40658 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40658 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40658 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40658 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40705 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 41118 | python3.10 | /var/lib/command-not-found/commands.db | binary | |
MD5:— | SHA256:— | |||
| 40658 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
53
DNS requests
57
Threats
32
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.96:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
40707 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ack5uggbk52xbbpamivut3hdp5lq_2025.5.12.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2025.05.12.01_all_acaacxxkg6wl6bml346gkcq2gtxq.crx3 | unknown | — | — | whitelisted |
40707 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aclxnidwwkj5di3vduduj2gqpgpq_4.10.2891.0/oimompecagnajdejgnnjijobebaeigek_4.10.2891.0_linux_b4hin3q5s66ws2322cyyfp35lu.crx3 | unknown | — | — | whitelisted |
40707 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aevtvjsxpcrwhjvp5w32fej6zq_9.56.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.56.0_all_acq3rupi4ymeq53so4pzqroatfea.crx3 | unknown | — | — | whitelisted |
40707 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/avtaypr7qxkbxa4ziskdkuquki_507/lmelglejhemejginpboagddgdfbepgmp_507_all_ZZ_acsofxfb65zjxy76u2gu7rzkbdhq.crx3 | unknown | — | — | whitelisted |
40707 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aca4j7naijrf65juvpzj5lv43una_2025.4.30.0/niikhdgajlphfehepabhhblakbdgeefj_2025.04.30.00_all_pi2vwi5t776kda42vjlunrgh5u.crx3 | unknown | — | — | whitelisted |
40707 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ktyagi2aeozubwzo2hlk3u6dni_1313/efniojlnjndmcbiieegkicadnoecjjef_1313_all_p4rv2wtycprx24knn2sn7g2ag4.crx3 | unknown | — | — | whitelisted |
40707 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/f36rcgpz7pmcle3g47jginux54_9780/hfnkpimlhhgieaddgfemjhofmfblmnib_9780_all_act7gxtrnrcb72dyqt2fnb74lheq.crx3 | unknown | — | — | whitelisted |
40707 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/h26xvwhuftpziwnfucve6pheoe_3069/jflookgnkcckhobaglndicnbbgbonegd_3069_all_jd5jon3opnt3ka3niwggalpawu.crx3 | unknown | — | — | whitelisted |
40707 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adchl7wjwtq6n322xjkik2i7vfaa_20250424.754192769.14/obedbbhbpmojnkanicioggnmelmoomoc_20250424.754192769.14_all_ENGB500000_ad77ur2hlt5pkhj4pv534qpf4seq.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 91.189.91.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 185.125.190.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 37.19.194.80:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 185.125.188.57:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40707 | chrome | 216.58.212.170:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
40707 | chrome | 142.250.185.67:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
40707 | chrome | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
40707 | chrome | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
github.com |
| whitelisted |
accounts.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
40707 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40707 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40707 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40707 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40707 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40707 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40707 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40707 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40707 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
40707 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |