| download: | openlink.exe |
| Full analysis: | https://app.any.run/tasks/b8a2a9ca-3573-4734-b34d-dbb38ed6bcef |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2020, 06:49:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 0DE19D334AE0A47397419D86DEEAFF7C |
| SHA1: | E5F0C71E4DC8E0088C35A552D873013B3055B66C |
| SHA256: | E3872E08F6D10DF5FE661979422C000ACE02DDB8604D782A8DFC6098C11CA2B0 |
| SSDEEP: | 3072:zMUWAHrRW60Ag/dTC4/Hd7ilq3kjca+TjecjMUCqT/0uf:zMGHrRWBTCW+U3k9GjR/X |
MALICIOUS
No malicious indicators.SUSPICIOUS
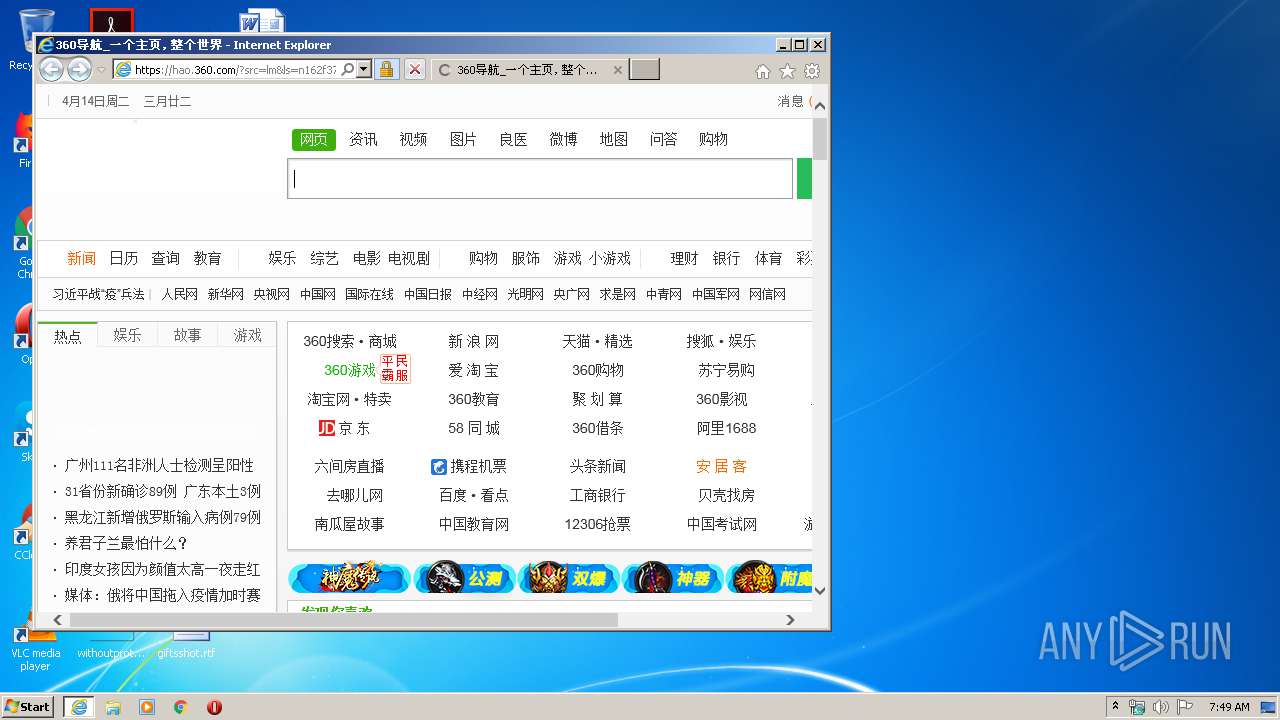
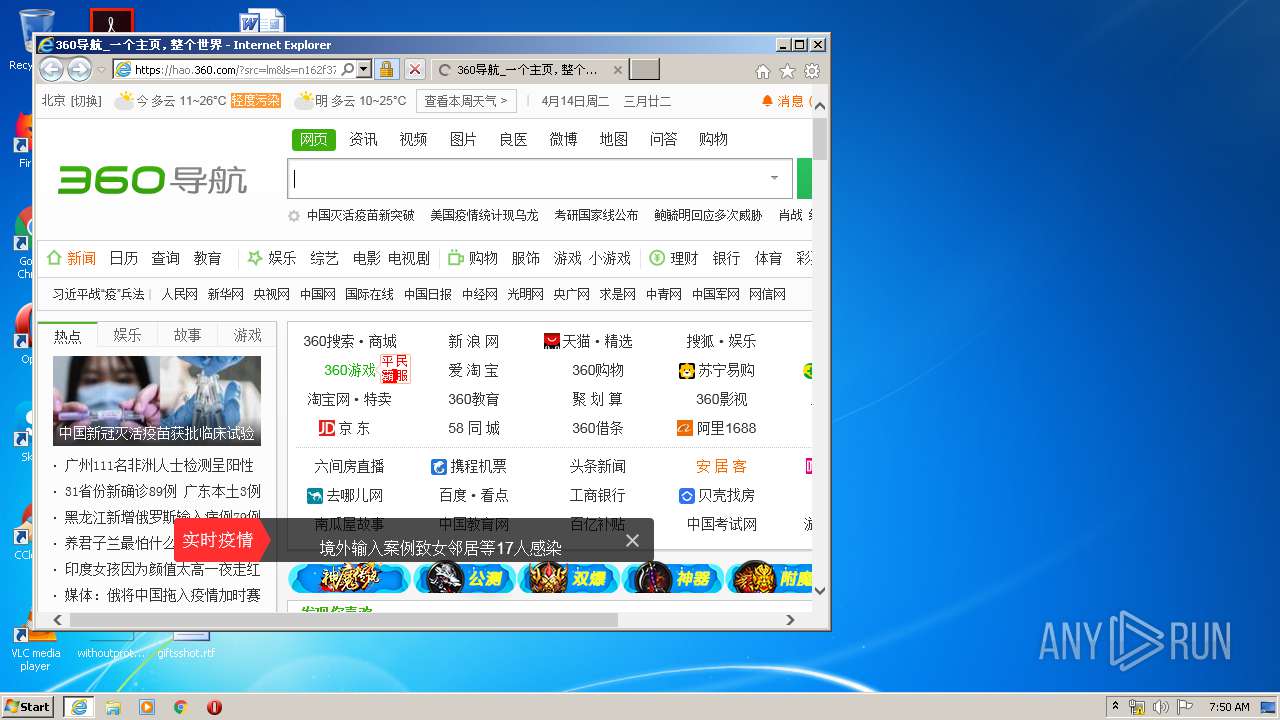
Starts Internet Explorer
- openlink.exe (PID: 2356)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2504)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3056)
- iexplore.exe (PID: 3792)
Changes internet zones settings
- iexplore.exe (PID: 3056)
Application launched itself
- iexplore.exe (PID: 3056)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2504)
- iexplore.exe (PID: 3792)
Reads internet explorer settings
- iexplore.exe (PID: 3792)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:04:01 08:06:24+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 73728 |
| InitializedDataSize: | 86016 |
| UninitializedDataSize: | 225280 |
| EntryPoint: | 0x49150 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | - |
| FileDescription: | 访问互联网 |
| FileVersion: | - |
| InternalName: | - |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Apr-2017 06:06:24 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | 访问互联网 |
| FileVersion: | - |
| InternalName: | - |
| LegalCopyright: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Apr-2017 06:06:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00037000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00038000 | 0x00012000 | 0x00011400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9058 |
.rsrc | 0x0004A000 | 0x00015000 | 0x00014C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.83932 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.22926 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 5.75932 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 6.17195 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 2.89005 | 744 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 2.54353 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 2.02749 | 68 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.17501 | 2216 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
9 | 3.47748 | 1384 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
10 | 2.83156 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
WINSPOOL.DRV |
Total processes
39
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2356 | "C:\Users\admin\Desktop\openlink.exe" | C:\Users\admin\Desktop\openlink.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 访问互联网 Exit code: 0 Modules
| |||||||||||||||
| 2504 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 3056 | "C:\Program Files\Internet Explorer\iexplore.exe" https://hao.360.cn/?src=lm&ls=n162f37fb94 | C:\Program Files\Internet Explorer\iexplore.exe | openlink.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3792 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3056 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
640
Read events
544
Write events
96
Delete events
0
Modification events
| (PID) Process: | (2356) openlink.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000C699C3DD2812D601 | |||
| (PID) Process: | (3056) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 4022771122 | |||
| (PID) Process: | (3056) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30806568 | |||
| (PID) Process: | (3056) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3056) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3056) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3056) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3056) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3056) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3056) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
58
Text files
302
Unknown types
48
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFE6D.tmp | — | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFE6E.tmp | — | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\IJXD2LB9.txt | text | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C18B7A4A1C49A0D62FB269C7C94152C2_D348AC65641F62DB6CB48240267534F8 | der | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\P3I1QO9U.htm | html | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\ZFL8Y069.js | text | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C18B7A4A1C49A0D62FB269C7C94152C2_D348AC65641F62DB6CB48240267534F8 | binary | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\3d01aba13832e3b4[1].js | text | |
MD5:— | SHA256:— | |||
| 3792 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\e0f211ae7629636a[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
258
DNS requests
71
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3792 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://wotrus-ovca.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBROB68uPCabixs381BzpJxWVlED2AQUasBJGVKf6gFeRQyx8A9%2BoF9tj%2BUCEHLgAqoQiAZYnsEJIe4MG6o%3D | US | der | 1.50 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
3792 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3792 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://wotrus-ovca.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBROB68uPCabixs381BzpJxWVlED2AQUasBJGVKf6gFeRQyx8A9%2BoF9tj%2BUCEF7eHE83SHtZC0McQClx9kw%3D | US | der | 1.50 Kb | whitelisted |
3792 | iexplore.exe | GET | 200 | 123.59.118.38:80 | http://ocsp.crlocsp.cn/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRgH%2FPN%2F2KBN5Fec0GB96MNB1kxHgQUmZst9ovwo9uJ1J775XQvaNKQT%2BQCEQDl4LMz%2BDALlI5yCWlhELkT | CN | der | 472 b | suspicious |
3792 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEQDVbiRslO1jq7FG78GWtk%2Bw | US | der | 728 b | whitelisted |
3792 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEDwQTwm9nF7lMh9ExemdswQ%3D | US | der | 727 b | whitelisted |
3792 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 727 b | whitelisted |
— | — | GET | 200 | 151.139.128.14:80 | http://wotrus.ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR%2BkL4%2FxS4enxU71eA1P6WTAMenqAQUDUnJDz6x3zIDtZLbJaVtdOxZIssCEFN9rWMOrDrrQK95s0H1c8k%3D | US | der | 471 b | whitelisted |
3792 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.62 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3792 | iexplore.exe | 36.110.236.68:443 | hao.360.cn | IDC, China Telecommunications Corporation | CN | unknown |
3792 | iexplore.exe | 151.139.236.246:80 | subca.ocsp-certum.com | netDNA | US | unknown |
3056 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3792 | iexplore.exe | 180.153.199.213:443 | hao1.qhimg.com | China Telecom (Group) | CN | unknown |
3792 | iexplore.exe | 143.204.97.14:443 | s1.ssl.qhimg.com | — | US | unknown |
3792 | iexplore.exe | 58.222.38.25:443 | hao1.qhimg.com | No.31,Jin-rong Street | CN | unknown |
3792 | iexplore.exe | 13.225.73.100:443 | p0.ssl.qhimgs4.com | — | US | unknown |
3792 | iexplore.exe | 104.192.110.245:443 | s3m.mediav.com | Beijing Qihu Technology Company Limited | US | suspicious |
3792 | iexplore.exe | 117.91.191.253:443 | hao1.qhimg.com | No.31,Jin-rong Street | CN | unknown |
3792 | iexplore.exe | 218.93.202.6:443 | hao1.qhimg.com | No.31,Jin-rong Street | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hao.360.cn |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
subca.ocsp-certum.com |
| whitelisted |
hao.360.com |
| unknown |
s1.ssl.qhimg.com |
| whitelisted |
s0.ssl.qhimg.com |
| whitelisted |
hao1.qhimg.com |
| malicious |
hao2.qhimg.com |
| suspicious |
hao3.qhimg.com |
| malicious |