| File name: | uTorrent.exe |
| Full analysis: | https://app.any.run/tasks/e00cd5c6-7a76-4fd9-81d2-af750b61dd34 |
| Verdict: | Suspicious activity |
| Analysis date: | July 19, 2018, 09:36:45 |
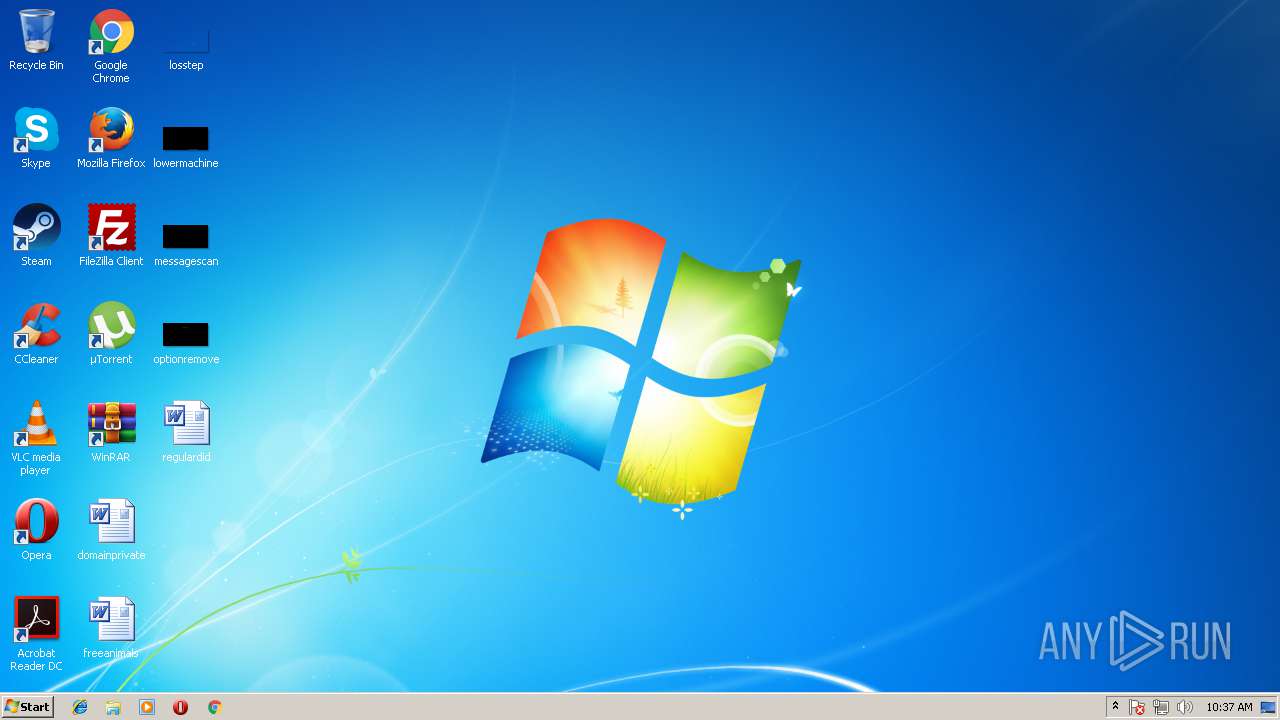
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | AD876376DB78E4A59A8DFEE0A0D83A71 |
| SHA1: | F87B26B4F1B6487668ACAB618A8E45F6C7B662A3 |
| SHA256: | E3794A03DBC6FEAB50896BC5BA6E32C12B09E32D40CC38B0A1C13266FA0C29B5 |
| SSDEEP: | 49152:86o7Uv0GyxGKceAgH1rRZUg7Yu0+DSvjrwW:zowvdQLceAgVVHwHz |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes scripts
- mshta.exe (PID: 2980)
Application launched itself
- uTorrent.exe (PID: 3300)
Creates files in the user directory
- uTorrent.exe (PID: 3300)
- uTorrent.exe (PID: 2312)
Starts MSHTA.EXE for opening HTA or HTMLS files
- uTorrent.exe (PID: 2312)
Checks for external IP
- mshta.exe (PID: 2980)
INFO
Dropped object may contain URL's
- uTorrent.exe (PID: 3300)
Reads internet explorer settings
- mshta.exe (PID: 2980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:15 02:55:06+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 2121728 |
| InitializedDataSize: | 126976 |
| UninitializedDataSize: | 3977216 |
| EntryPoint: | 0x5d1310 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
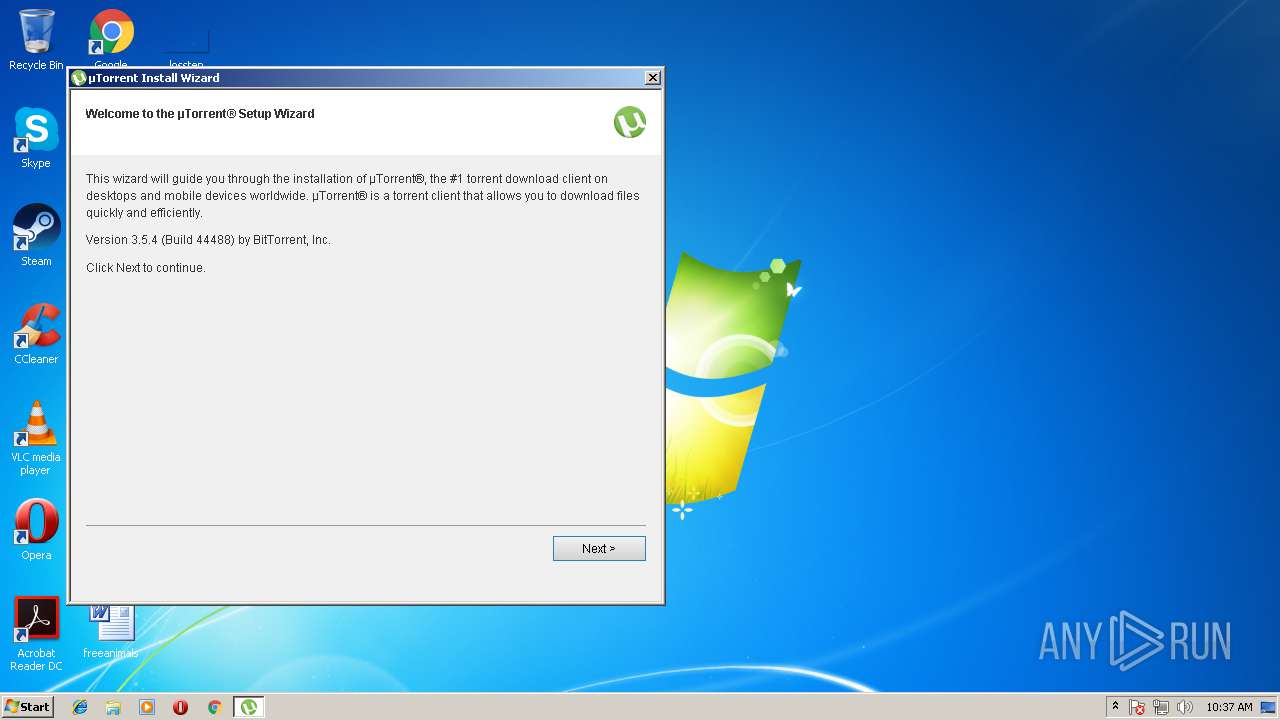
| FileVersionNumber: | 3.5.4.44488 |
| ProductVersionNumber: | 3.5.4.44488 |
| FileFlagsMask: | 0x002b |
| FileFlags: | Special build |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | BitTorrent Inc. |
| FileDescription: | µTorrent |
| FileVersion: | 3.5.4.44488 |
| InternalName: | uTorrent.exe |
| OriginalFileName: | uTorrent.exe |
| LegalCopyright: | ©2018 BitTorrent, Inc. All Rights Reserved. |
| ProductName: | µTorrent |
| ProductVersion: | 3.5.4.44488 |
| SpecialBuild: | release |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jun-2018 00:55:06 |
| Detected languages: |
|
| CompanyName: | BitTorrent Inc. |
| FileDescription: | µTorrent |
| FileVersion: | 3.5.4.44488 |
| InternalName: | uTorrent.exe |
| OriginalFilename: | uTorrent.exe |
| LegalCopyright: | ©2018 BitTorrent, Inc. All Rights Reserved. |
| ProductName: | µTorrent |
| ProductVersion: | 3.5.4.44488 |
| SpecialBuild: | release |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000148 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 15-Jun-2018 00:55:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x003CB000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x003CC000 | 0x00206000 | 0x00206000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99989 |
.rsrc | 0x005D2000 | 0x0001F000 | 0x0001EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.03854 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11079 | 1835 | Latin 1 / Western European | Swedish - Sweden | RT_MANIFEST |
2 | 7.79637 | 1003 | Latin 1 / Western European | Swedish - Sweden | RT_HTML |
3 | 5.68396 | 62 | Latin 1 / Western European | Swedish - Sweden | RT_GROUP_ICON |
4 | 7.98236 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.32193 | 20 | Latin 1 / Western European | Swedish - Sweden | RT_GROUP_ICON |
6 | 7.9769 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 7.98167 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 7.98085 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.98064 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 6.38105 | 114 | Latin 1 / Western European | Swedish - Sweden | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
DNSAPI.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSIMG32.dll |
OLEAUT32.dll |
PSAPI.DLL |
Total processes
42
Monitored processes
6
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | "C:\Windows\System32\PING.EXE" 8.8.8.8 -n 2 -w 500 | C:\Windows\System32\PING.EXE | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2312 | "C:\Users\admin\AppData\Local\Temp\uTorrent.exe" /HYDRA_PERMISSIONS_RESTART /HYDRA_LOG "C:\Users\admin\AppData\Local\Temp\HYDAFD0.tmp.1531993049\index.hta.log" /HYDRA_HTADIR "C:\Users\admin\AppData\Local\Temp\HYDAFD0.tmp.1531993049\HTA" | C:\Users\admin\AppData\Local\Temp\uTorrent.exe | uTorrent.exe | ||||||||||||
User: admin Company: BitTorrent Inc. Integrity Level: HIGH Description: µTorrent Exit code: 0 Version: 3.5.4.44488 Modules
| |||||||||||||||
| 2316 | "C:\Windows\System32\cscript.exe" "shell_scripts/check_if_cscript_is_working.js" | C:\Windows\System32\cscript.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 99 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2980 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\AppData\Local\Temp\HYDAFD0.tmp.1531993049\HTA\index.hta?utorrent" "C:\Users\admin\AppData\Local\Temp\uTorrent.exe" /LOG "C:\Users\admin\AppData\Local\Temp\HYDAFD0.tmp.1531993049\index.hta.log" /PID "2312" /CID "P-6naYMO2gvdMZkz" /VERSION "111717832" /BUCKET "1" /SSB "267030" /COUNTRY "US" /OS "6.1" /BROWSERS "\"C:\Program Files\Mozilla Firefox\firefox.exe\",\"C:\Program Files\Google\Chrome\Application\chrome.exe\",C:\Program Files\Internet Explorer\iexplore.exe,\"C:\Program Files\Opera\Opera.exe\"" /ARCHITECTURE "32" /LANG "en" /USERNAME "admin" /SID "S-1-5-21-1302019708-1500728564-335382590-1000" /CLIENT "utorrent" | C:\Windows\System32\mshta.exe | uTorrent.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3300 | "C:\Users\admin\AppData\Local\Temp\uTorrent.exe" | C:\Users\admin\AppData\Local\Temp\uTorrent.exe | explorer.exe | ||||||||||||
User: admin Company: BitTorrent Inc. Integrity Level: MEDIUM Description: µTorrent Exit code: 0 Version: 3.5.4.44488 Modules
| |||||||||||||||
| 4020 | "C:\Windows\System32\cscript.exe" shell_scripts/shell_ping_after_close.js "http://i-50.b-000.XYZ.bench.utorrent.com/e?i=50&e=eyJldmVudE5hbWUiOiJoeWRyYTEiLCJhY3Rpb24iOiJodGFiZWdpbiIsInBpZCI6IjIzMTIiLCJoIjoiUC02bmFZTU8yZ3ZkTVpreiIsInYiOiIxMTE3MTc4MzIiLCJiIjo0NDQ4OCwiY2wiOiJ1VG9ycmVudCIsIm9zYSI6IjMyIiwic2xuZyI6ImVuIiwiZGIiOiJXaW5kb3dzIEludGVybmV0IEV4cGxvcmVyIiwiZGJ2IjoiOC4wIiwiaWJyIjpbeyJuYW1lIjoiRmlyZWZveCIsInZlcnNpb24iOiI1NS4wIiwiZXhlTmFtZSI6ImZpcmVmb3gifSx7Im5hbWUiOiJHb29nbGUgQ2hyb21lIiwidmVyc2lvbiI6IjYxLjAiLCJleGVOYW1lIjoiY2hyb21lIn0seyJuYW1lIjoiV2luZG93cyBJbnRlcm5ldCBFeHBsb3JlciIsInZlcnNpb24iOiI4LjAiLCJleGVOYW1lIjoiaWV4cGxvcmUifSx7Im5hbWUiOiJPcGVyYSBJbnRlcm5ldCBCcm93c2VyIiwidmVyc2lvbiI6IjEyLjE1IiwiZXhlTmFtZSI6Im9wZXJhIn1dLCJpcCI6IjM3LjQ4LjExOS4xMjkiLCJjbiI6Ik5ldGhlcmxhbmRzIiwicGFja2lkIjoiZGVmYXVsdCJ9" | C:\Windows\System32\cscript.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
639
Read events
614
Write events
25
Delete events
0
Modification events
| (PID) Process: | (2980) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2980) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2980) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mshta_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2980) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mshta_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2980) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mshta_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2980) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mshta_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2980) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mshta_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2980) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mshta_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2980) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mshta_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2980) mshta.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mshta_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
5
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3300 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\uttAF14.tmp | — | |
MD5:— | SHA256:— | |||
| 3300 | uTorrent.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@localhost[1].txt | text | |
MD5:— | SHA256:— | |||
| 3300 | uTorrent.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\c1477c1f926a3dfc3f9fba24fc5470d6_90059c37-1320-41a4-b58d-2b75a9850d2f | binary | |
MD5:— | SHA256:— | |||
| 3300 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\HYDAFD0.tmp.1531993049\HTA\install.1531993049.zip | compressed | |
MD5:— | SHA256:— | |||
| 3300 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\HYDAFD0.tmp.1531993049\HTA\i18n\pt.json | html | |
MD5:FB63D52AC25CD3D272365FA75F74C279 | SHA256:E39D6A57D2F16E60C4075D07741DADD6A2742A85ACEB250083D7AB103279F737 | |||
| 3300 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\HYDAFD0.tmp.1531993049\index.hta.log | text | |
MD5:2B632A88AF93F552846FDBF6890E8613 | SHA256:2B1D8F74B6B7EF3811B62E9320953577A736ED64AB9DD5C3E2390D994A10D234 | |||
| 3300 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\HYDAFD0.tmp.1531993049\HTA\i18n\ru.json | html | |
MD5:3C40E2B9A731D84C5A7CFE218139B4C9 | SHA256:960ECC28726D25AB8F9D8A2C342534E1B42C2C8B6D2937C3B4A4C85A6F15948C | |||
| 3300 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\HYDAFD0.tmp.1531993049\HTA\i18n\es.json | html | |
MD5:D208BD6553A40136D75A78D5C0E11F52 | SHA256:AAC630FBE06486BACE04D05DA5E12CC96715B263CB3CAE8F246E630B6166DE41 | |||
| 3300 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\HYDAFD0.tmp.1531993049\HTA\i18n\br.json | html | |
MD5:F12764DFC1ADE6DB8FBAC38762A53911 | SHA256:968738E0C8C5413C4CD516E04D2FC43F9FB6449C1BF44B2010E84176E462514A | |||
| 3300 | uTorrent.exe | C:\Users\admin\AppData\Local\Temp\HYDAFD0.tmp.1531993049\HTA\i18n\ko.json | html | |
MD5:F9FEB32431F5064F711B87C31CCC8AC0 | SHA256:6CCE352F8426A6CB2D41D5D108658CFA1244F0142D6F60BC96E3C4C2904913C3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
11
DNS requests
7
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3300 | uTorrent.exe | GET | — | 67.215.238.66:80 | http://download-lb.utorrent.com/endpoint/hydra-ut/os/win7/track/beta/cc-tag/290/browser/ie/os-region/US/os-lang/en/os-ver/6.1/enc-ver/111717832/ | US | — | — | whitelisted |
3300 | uTorrent.exe | POST | — | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | — | — | whitelisted |
3300 | uTorrent.exe | POST | — | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | — | — | whitelisted |
2980 | mshta.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json?callback=jQuery19102351469418154467_1531993053713&_=1531993053714 | DE | text | 394 b | malicious |
3300 | uTorrent.exe | POST | 200 | 107.20.217.71:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
3300 | uTorrent.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
4020 | cscript.exe | GET | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50&e=eyJldmVudE5hbWUiOiJoeWRyYTEiLCJhY3Rpb24iOiJodGFiZWdpbiIsInBpZCI6IjIzMTIiLCJoIjoiUC02bmFZTU8yZ3ZkTVpreiIsInYiOiIxMTE3MTc4MzIiLCJiIjo0NDQ4OCwiY2wiOiJ1VG9ycmVudCIsIm9zYSI6IjMyIiwic2xuZyI6ImVuIiwiZGIiOiJXaW5kb3dzIEludGVybmV0IEV4cGxvcmVyIiwiZGJ2IjoiOC4wIiwiaWJyIjpbeyJuYW1lIjoiRmlyZWZveCIsInZlcnNpb24iOiI1NS4wIiwiZXhlTmFtZSI6ImZpcmVmb3gifSx7Im5hbWUiOiJHb29nbGUgQ2hyb21lIiwidmVyc2lvbiI6IjYxLjAiLCJleGVOYW1lIjoiY2hyb21lIn0seyJuYW1lIjoiV2luZG93cyBJbnRlcm5ldCBFeHBsb3JlciIsInZlcnNpb24iOiI4LjAiLCJleGVOYW1lIjoiaWV4cGxvcmUifSx7Im5hbWUiOiJPcGVyYSBJbnRlcm5ldCBCcm93c2VyIiwidmVyc2lvbiI6IjEyLjE1IiwiZXhlTmFtZSI6Im9wZXJhIn1dLCJpcCI6IjM3LjQ4LjExOS4xMjkiLCJjbiI6Ik5ldGhlcmxhbmRzIiwicGFja2lkIjoiZGVmYXVsdCJ9 | US | text | 21 b | whitelisted |
2980 | mshta.exe | GET | 200 | 67.215.246.203:80 | http://update.utorrent.com/featuredcontent.php?w=6.1 | US | text | 21 b | whitelisted |
2312 | uTorrent.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
2312 | uTorrent.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3300 | uTorrent.exe | 67.215.238.66:80 | download-lb.utorrent.com | QuadraNet, Inc | US | suspicious |
2312 | uTorrent.exe | 23.21.43.186:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | malicious |
2980 | mshta.exe | 67.215.246.203:80 | update.utorrent.com | QuadraNet, Inc | US | suspicious |
2980 | mshta.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
4020 | cscript.exe | 23.21.43.186:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | malicious |
3300 | uTorrent.exe | 107.20.217.71:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | suspicious |
3300 | uTorrent.exe | 23.21.43.186:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
router.bittorrent.com |
| shared |
router.utorrent.com |
| whitelisted |
i-50.b-000.xyz.bench.utorrent.com |
| whitelisted |
download-lb.utorrent.com |
| whitelisted |
ip-api.com |
| malicious |
update.utorrent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2312 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client POST JSON |
2312 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client response_code |
3300 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client POST JSON |
3300 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client POST JSON |
3300 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client POST JSON |
3300 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client response_code |
3300 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client POST JSON |
3300 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client POST JSON |
3300 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client response_code |
3300 | uTorrent.exe | Misc activity | POLICY [PTsecurity] uTorrent Hydra Client response_code |