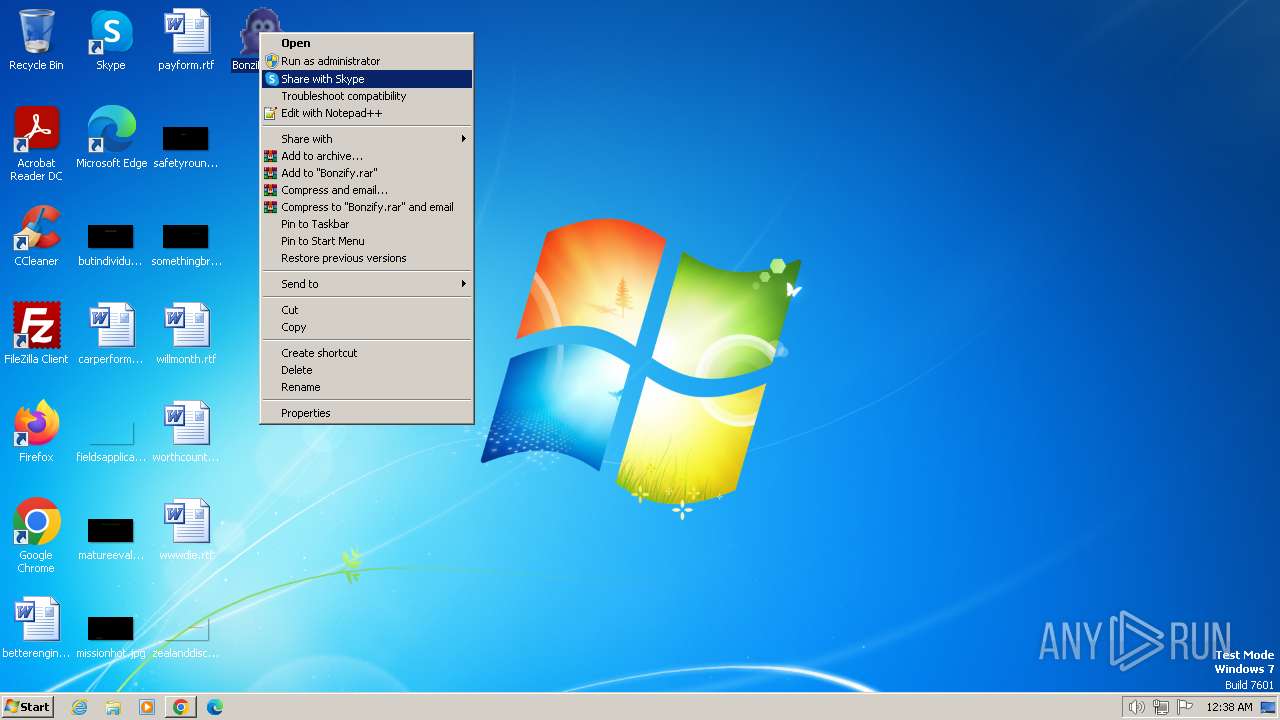
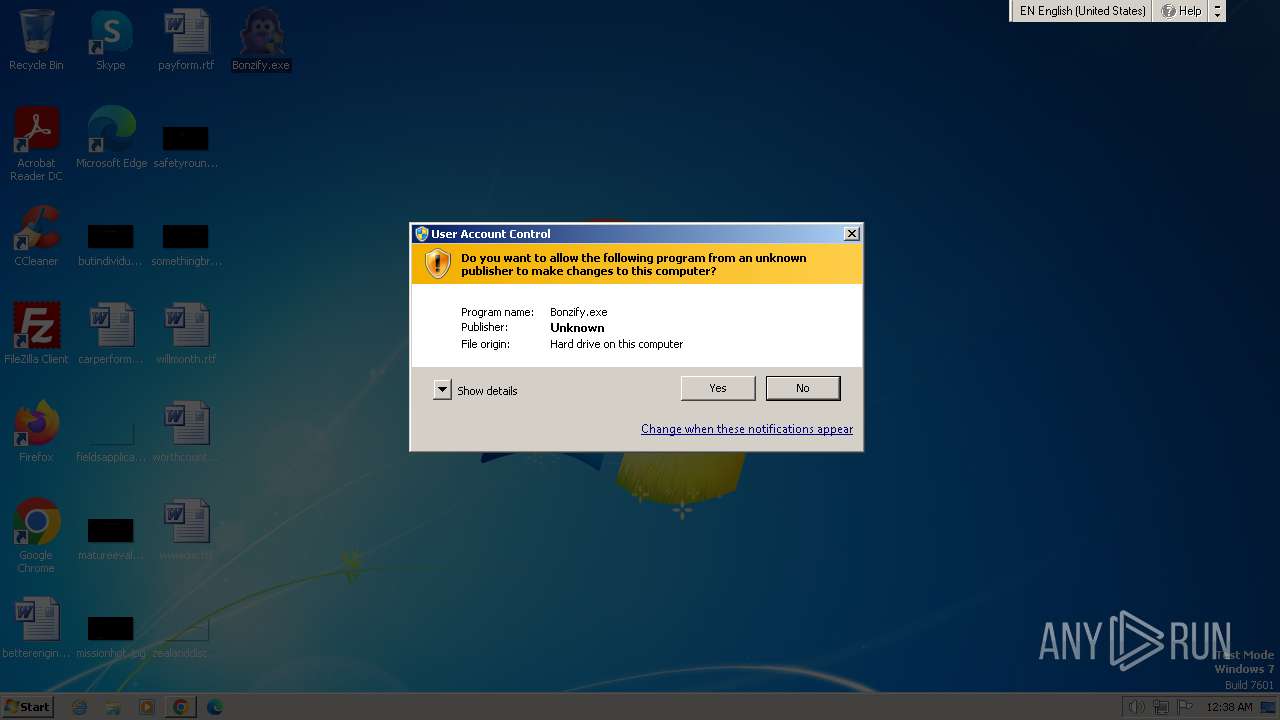
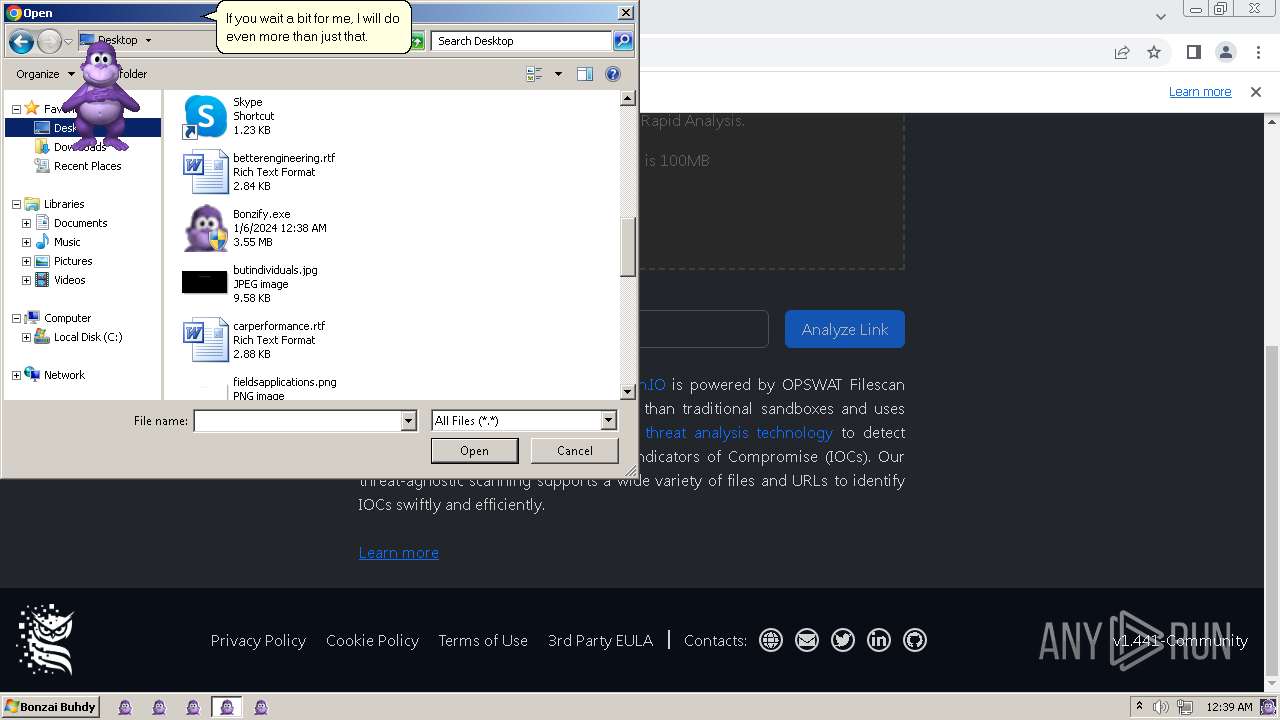
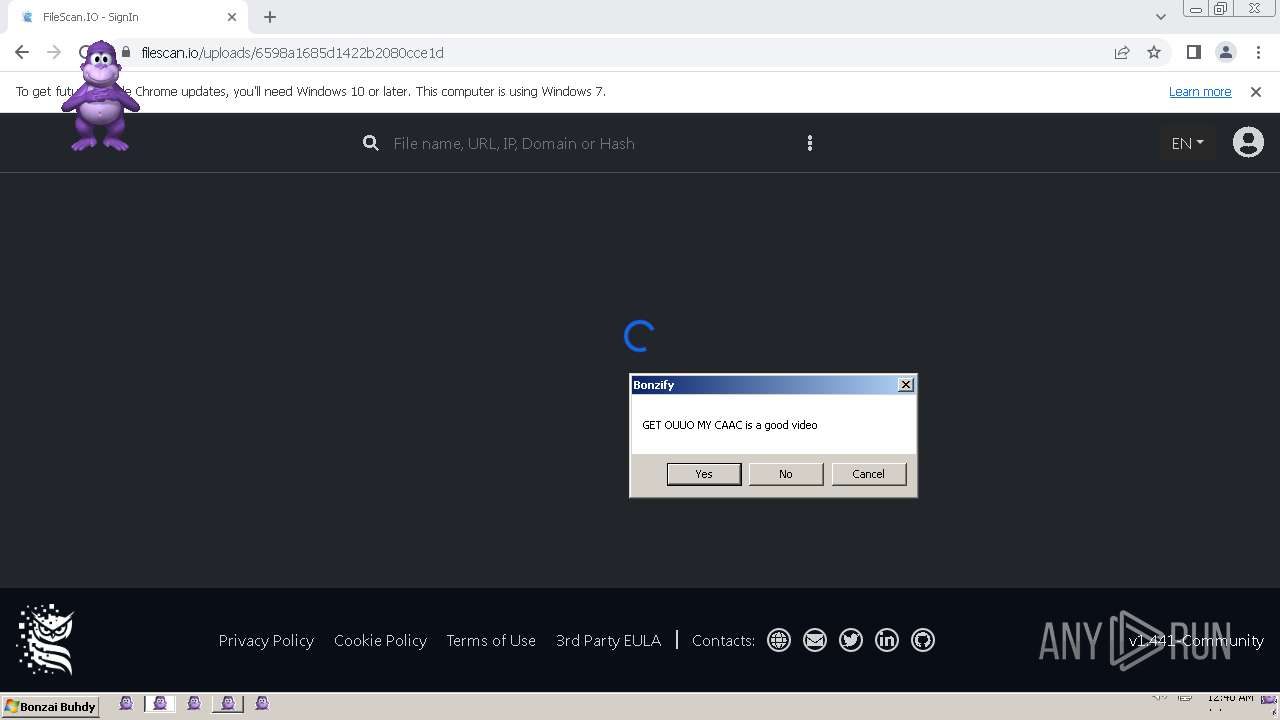
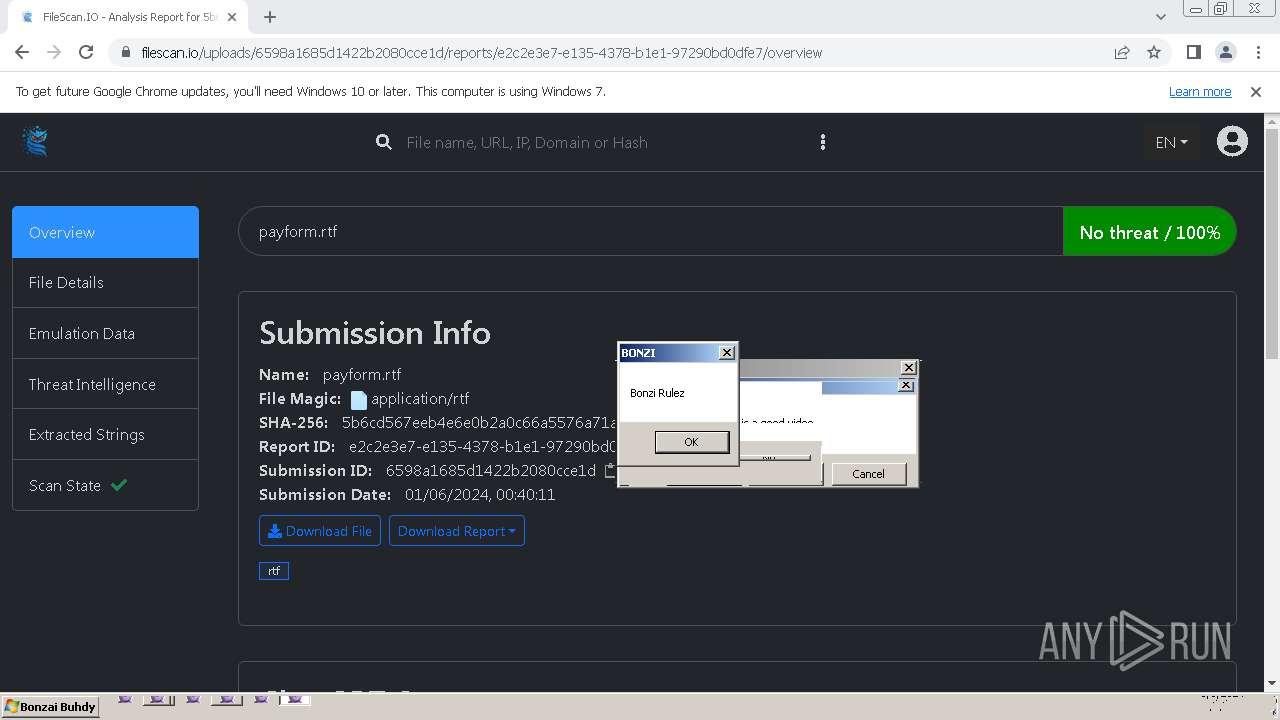
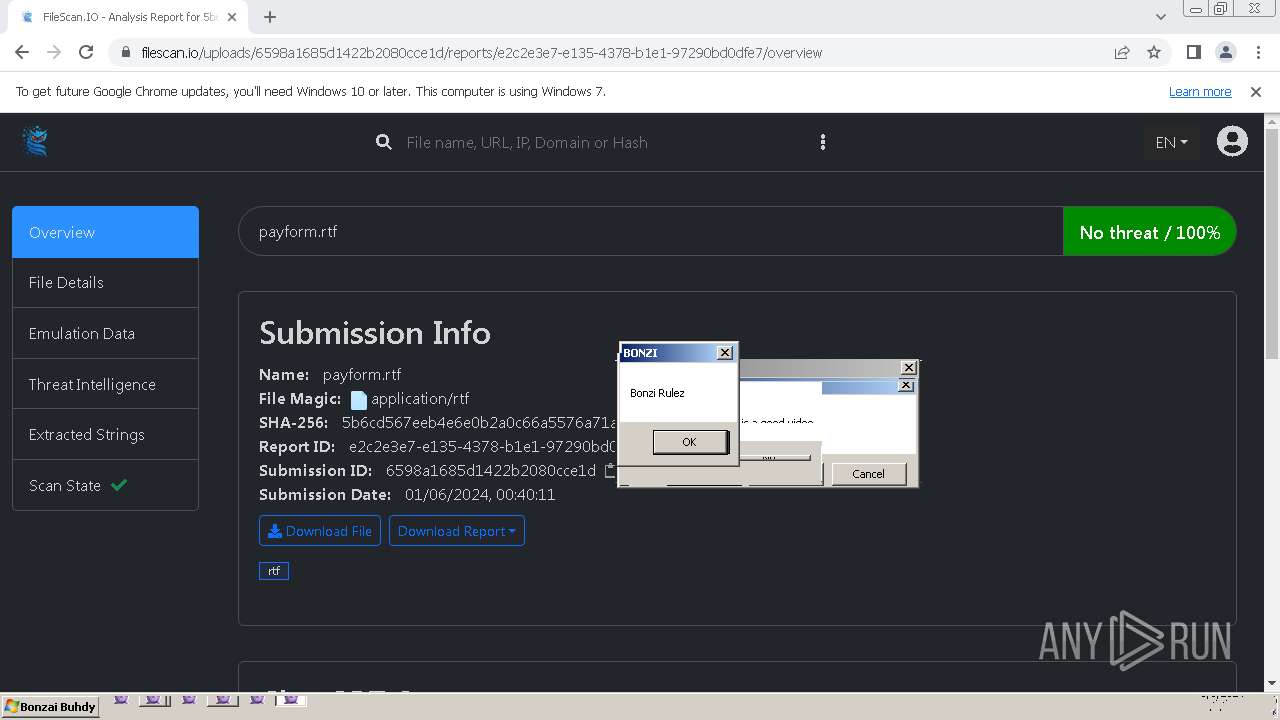
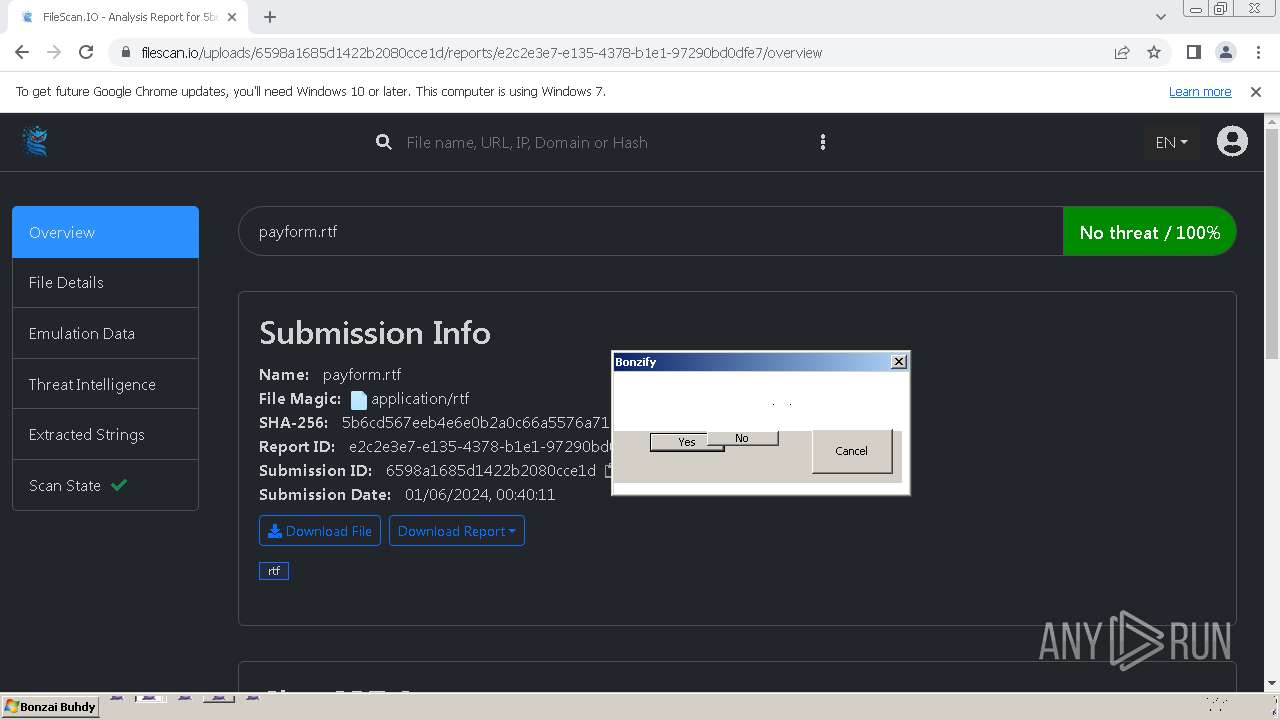
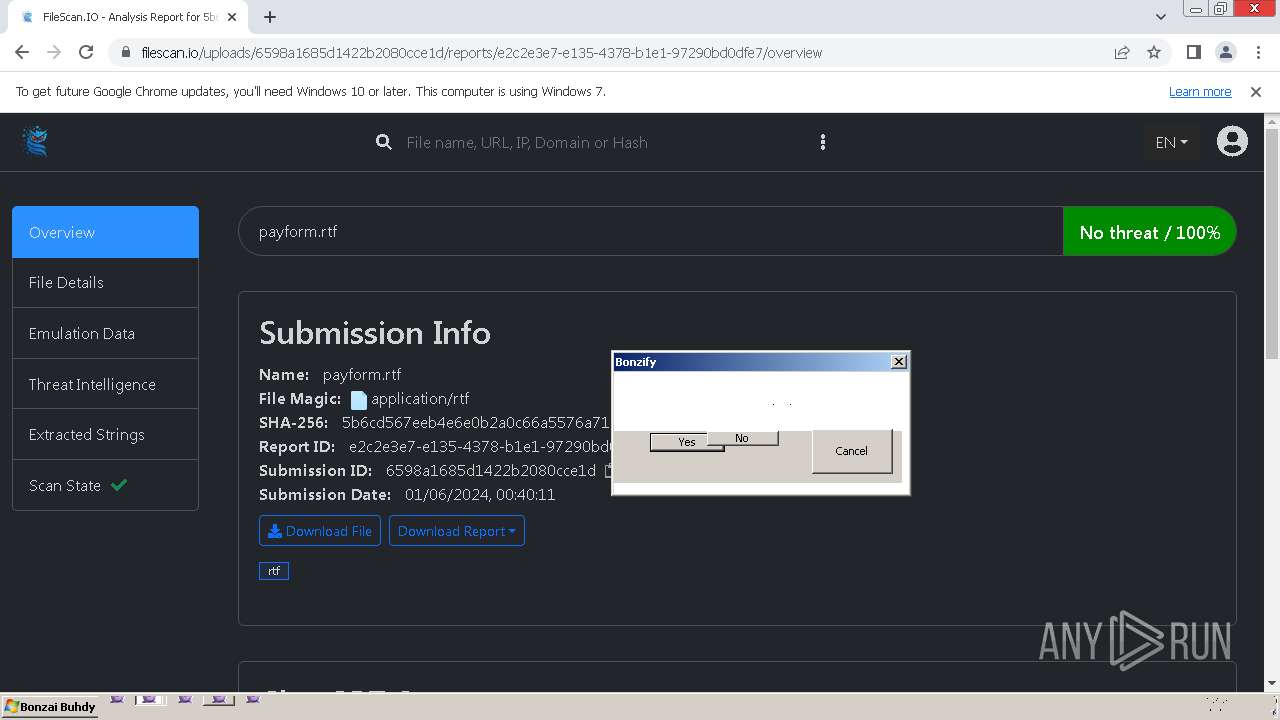
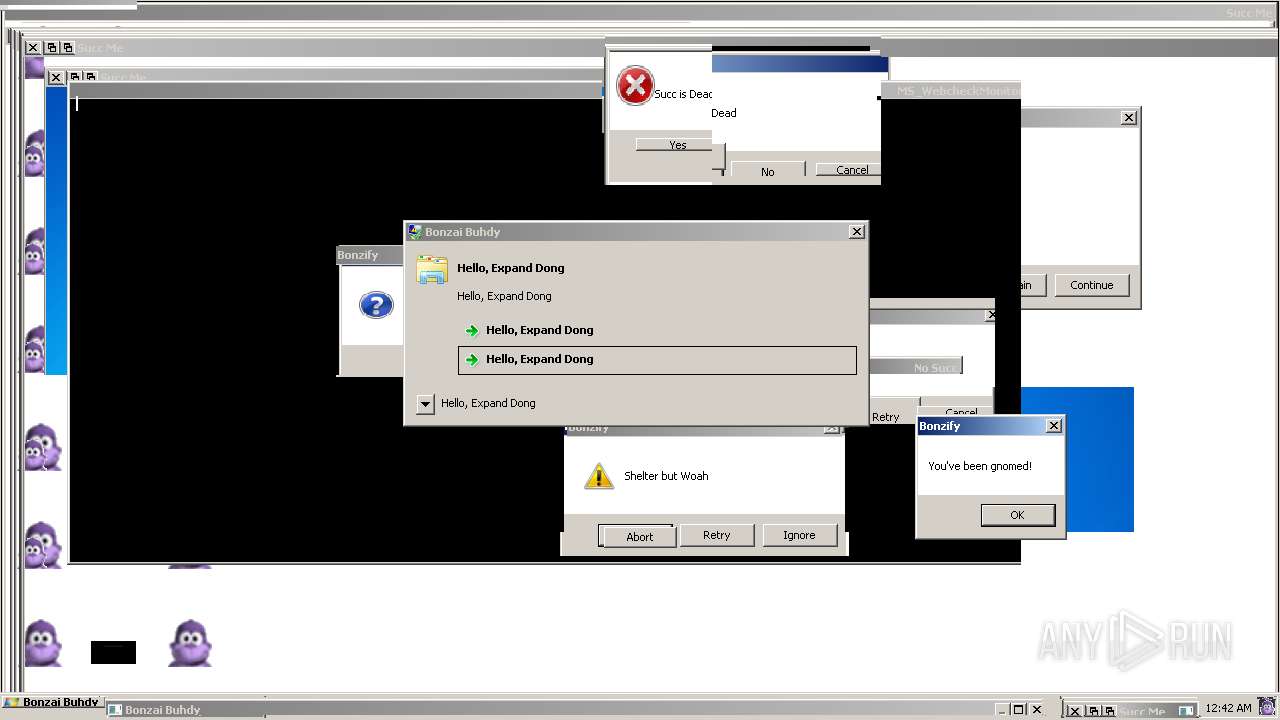
| File name: | Bonzify.exe |
| Full analysis: | https://app.any.run/tasks/8ea347ba-7af8-4f01-86b9-cb9e15c743d5 |
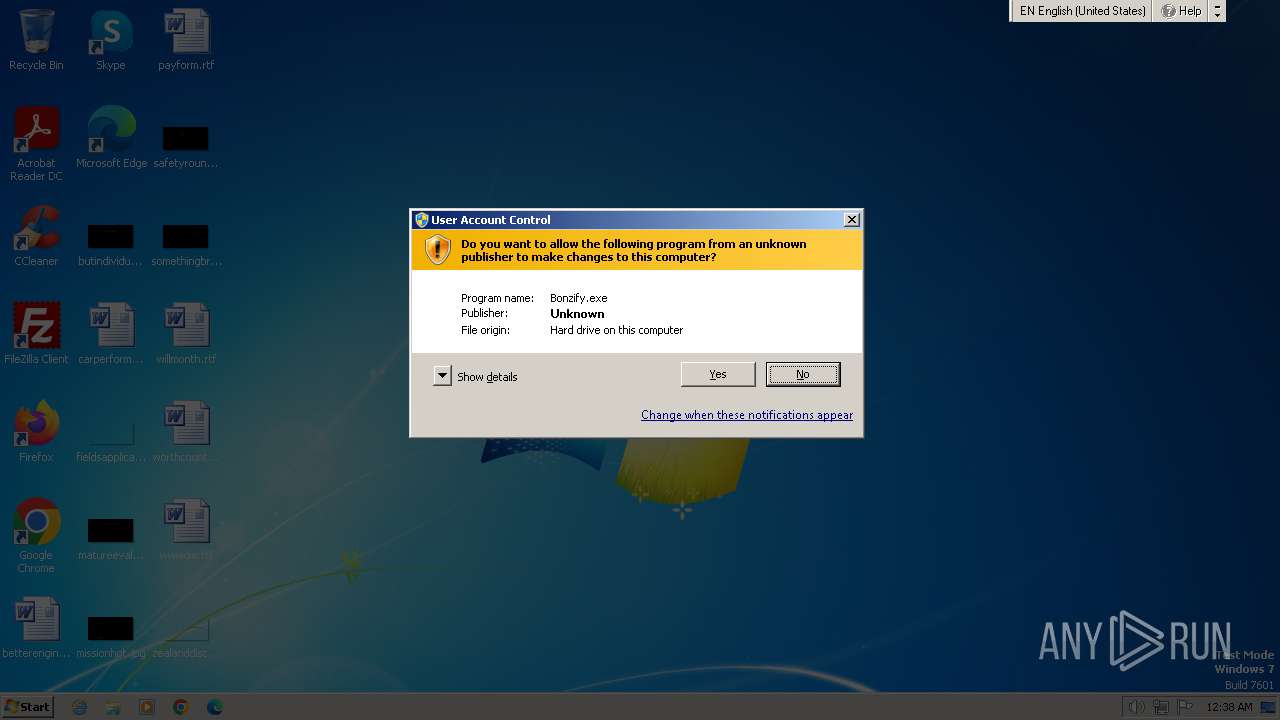
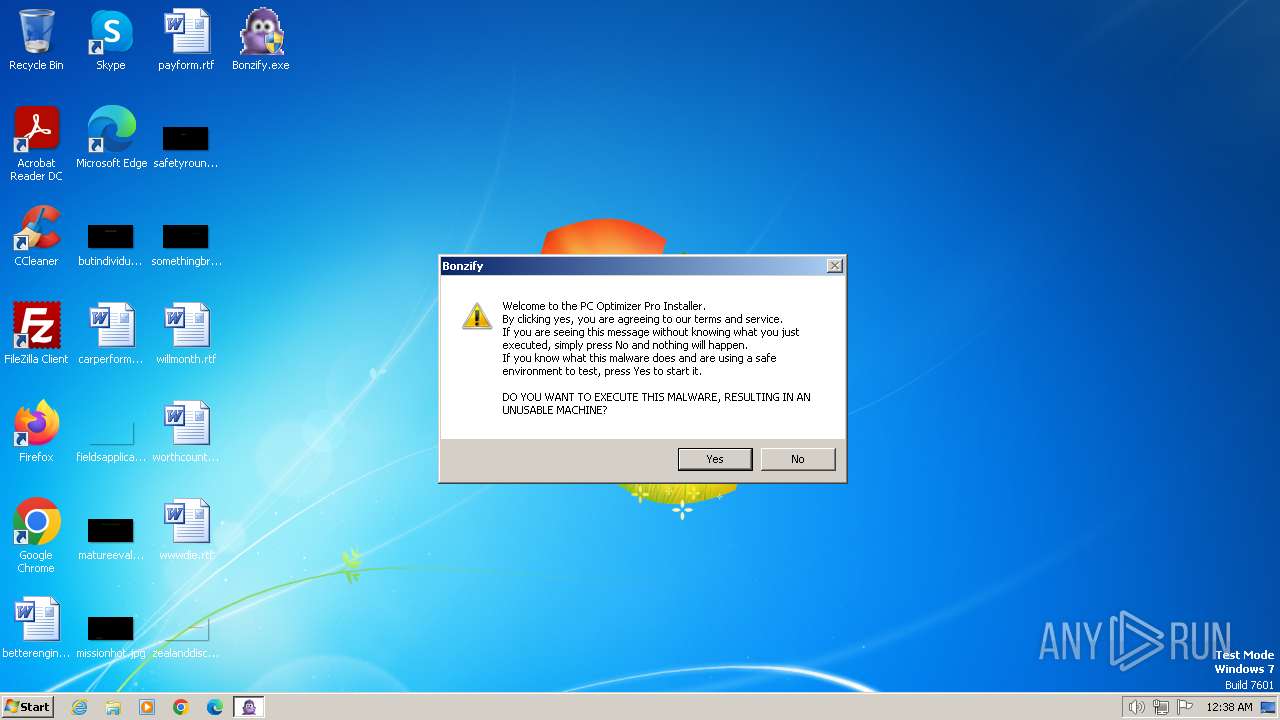
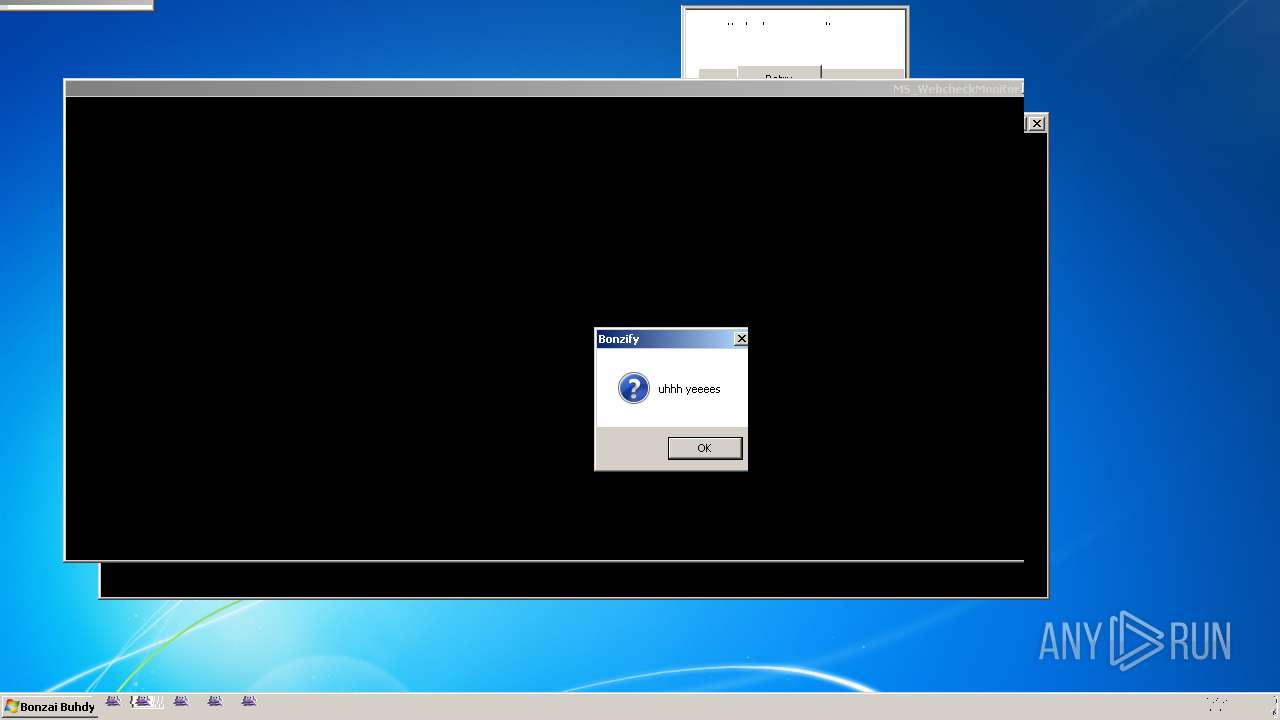
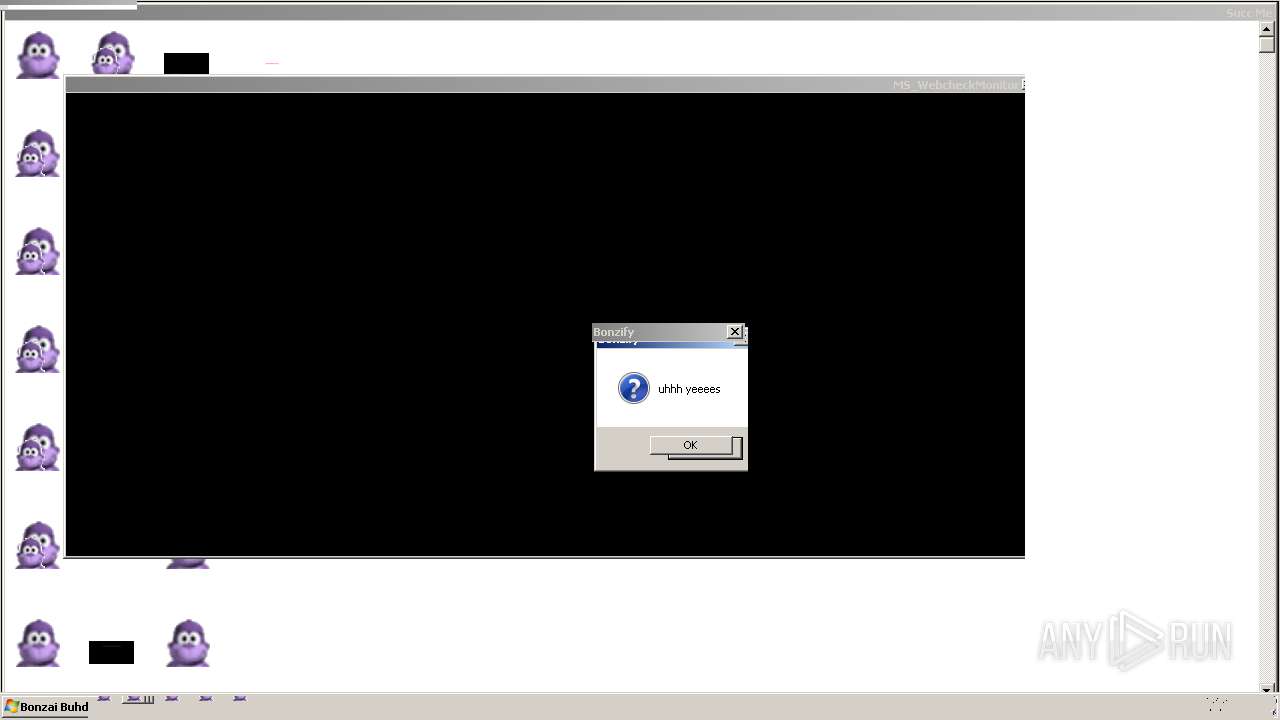
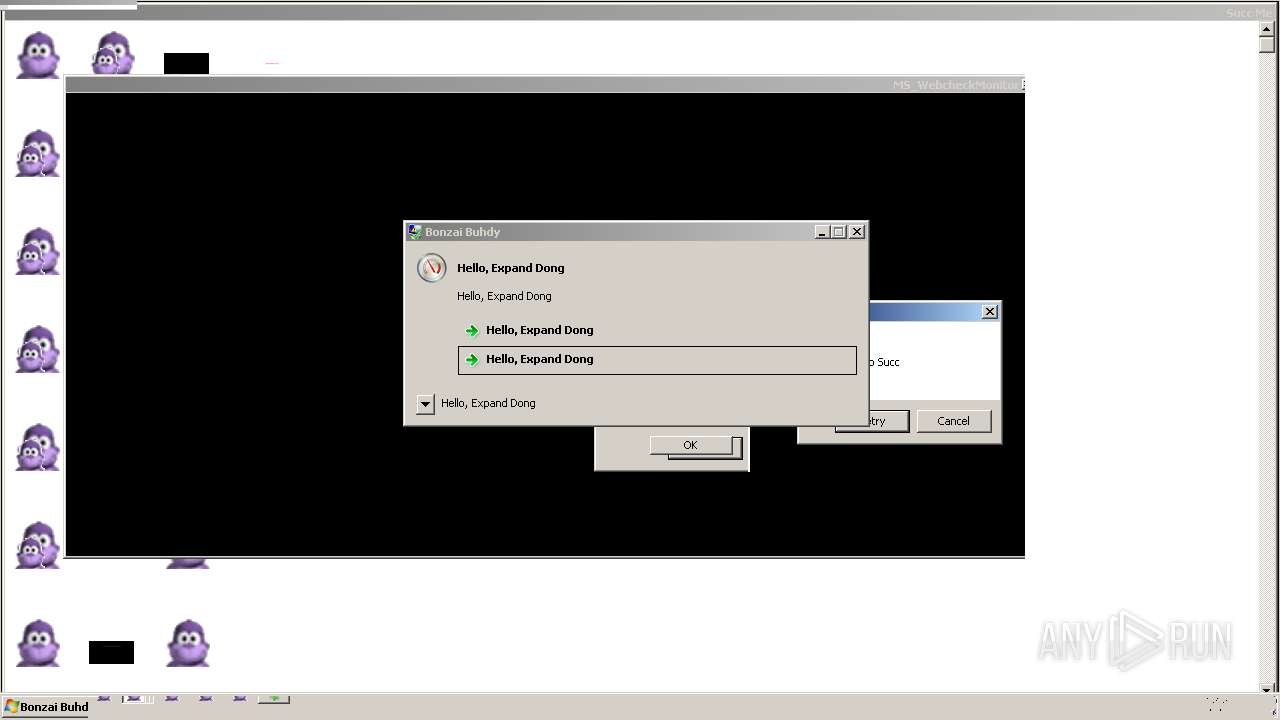
| Verdict: | Malicious activity |
| Analysis date: | January 06, 2024, 00:37:54 |
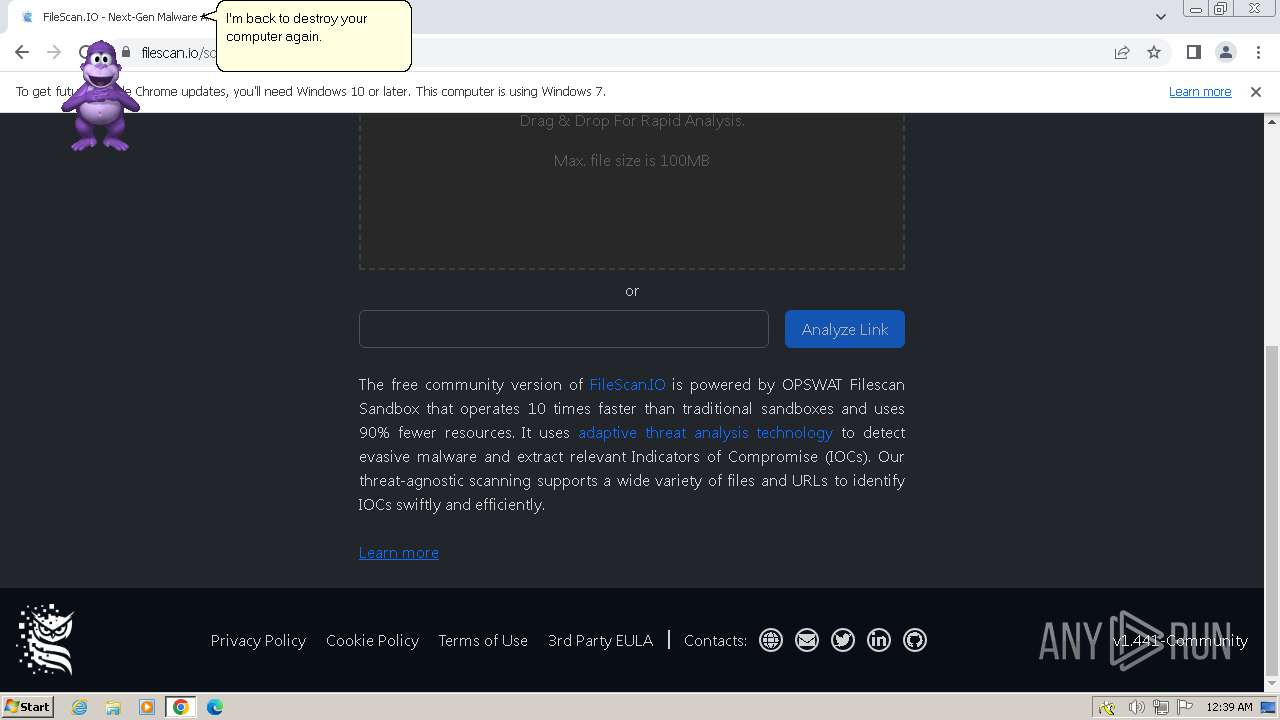
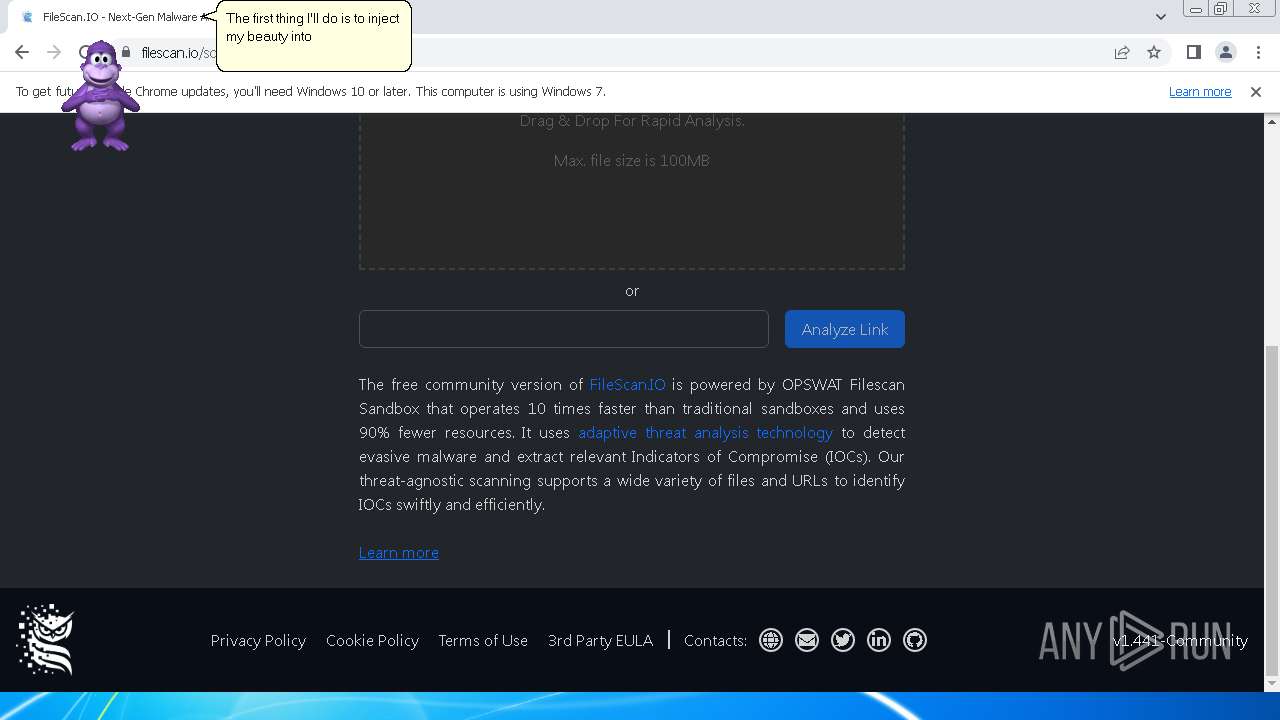
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7E5FBEA7EE5A03D2C6DEE20854DEED2E |
| SHA1: | E3D6D23BACC182E8036FB5E38D9E8FD26830045C |
| SHA256: | E369B688C86695960657DCF3CF63626C8C47095832C4A85E2D317E31AB8EF497 |
| SSDEEP: | 98304:5YFIsQd4i6QcdsbjxHqi/iXrPFt4BZkHj+Ml8TV9EFvxiKJT+7L51fo6bxHKrDWt:5yQ8nQqClXF |
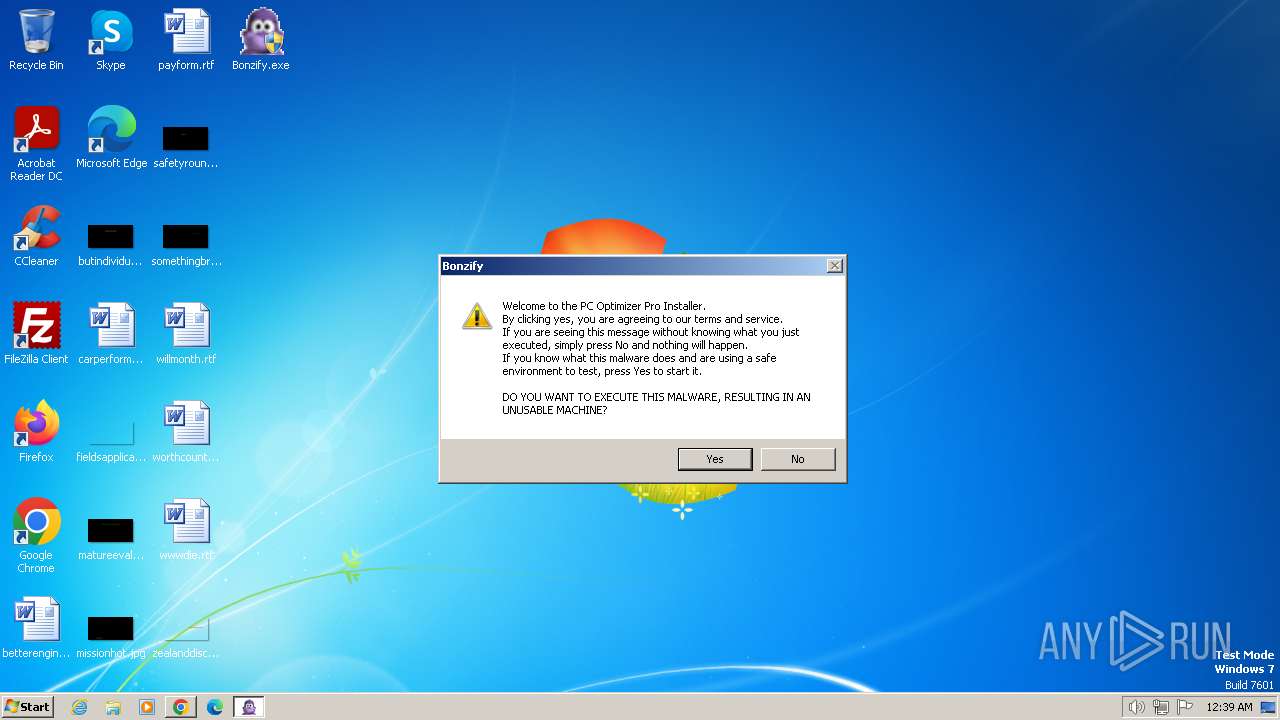
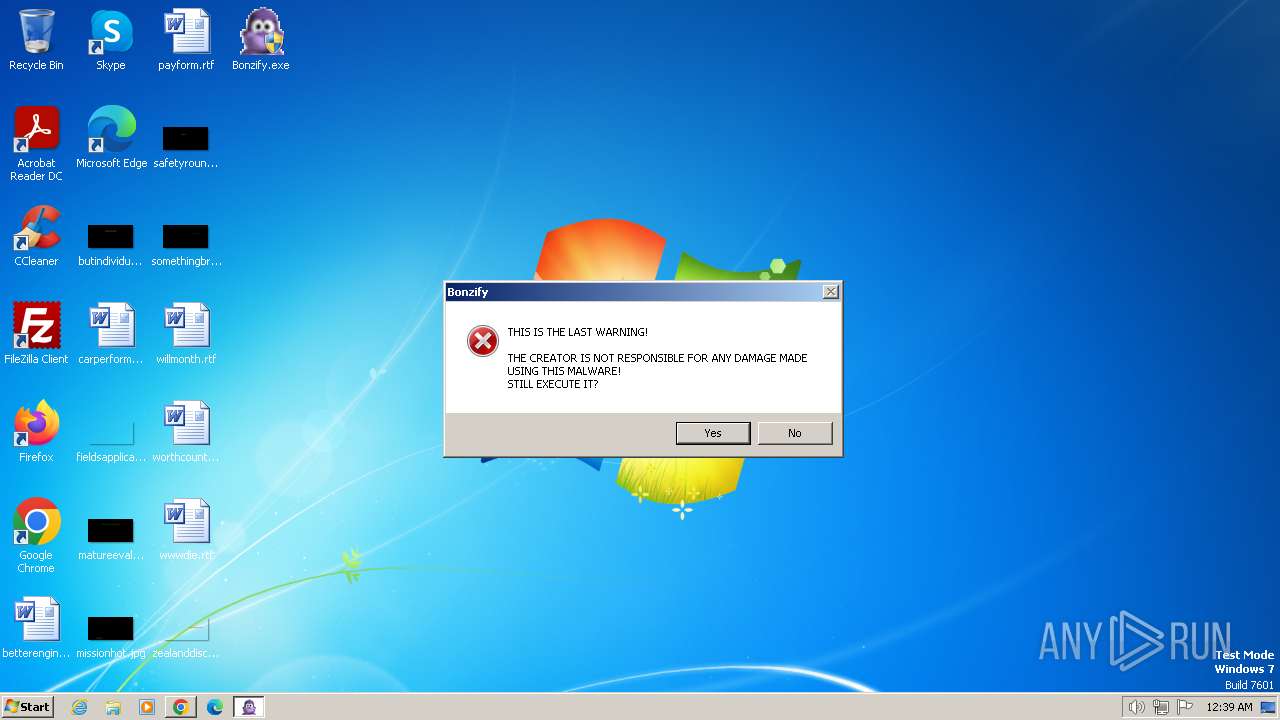
MALICIOUS
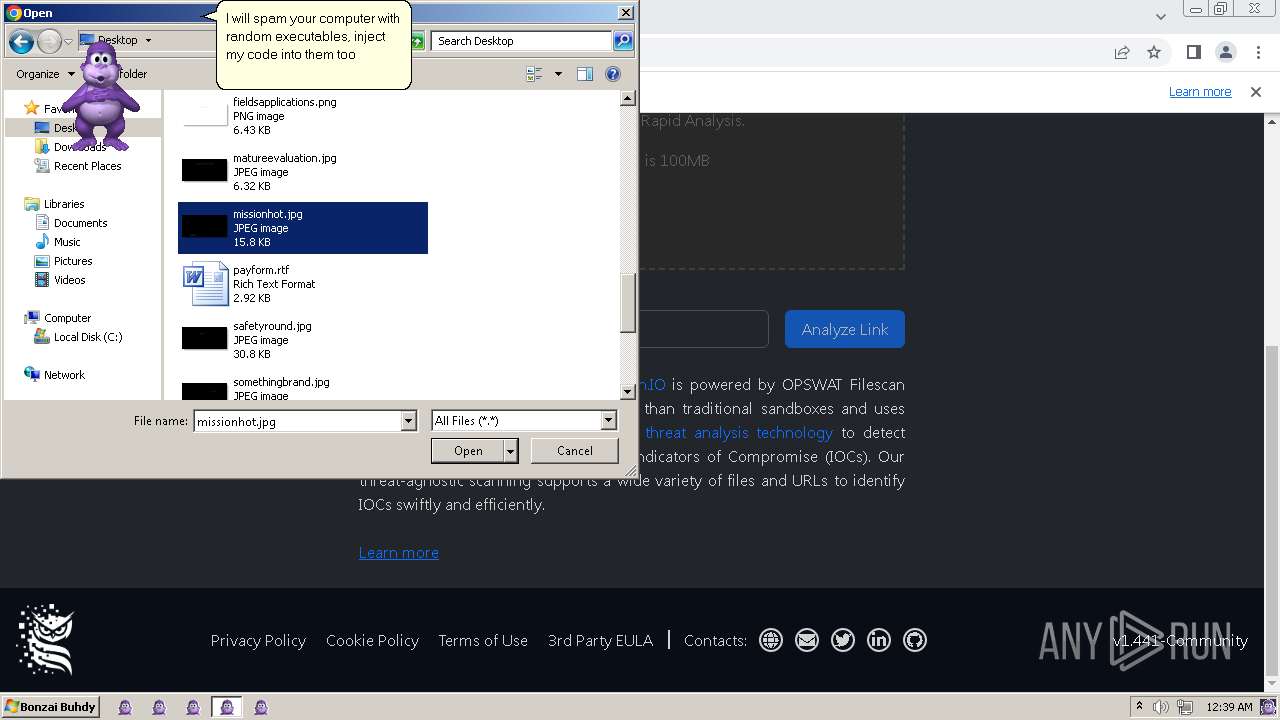
Registers / Runs the DLL via REGSVR32.EXE
- INSTALLER.exe (PID: 3368)
- INSTALLER.exe (PID: 3692)
Creates a writable file in the system directory
- INSTALLER.exe (PID: 3692)
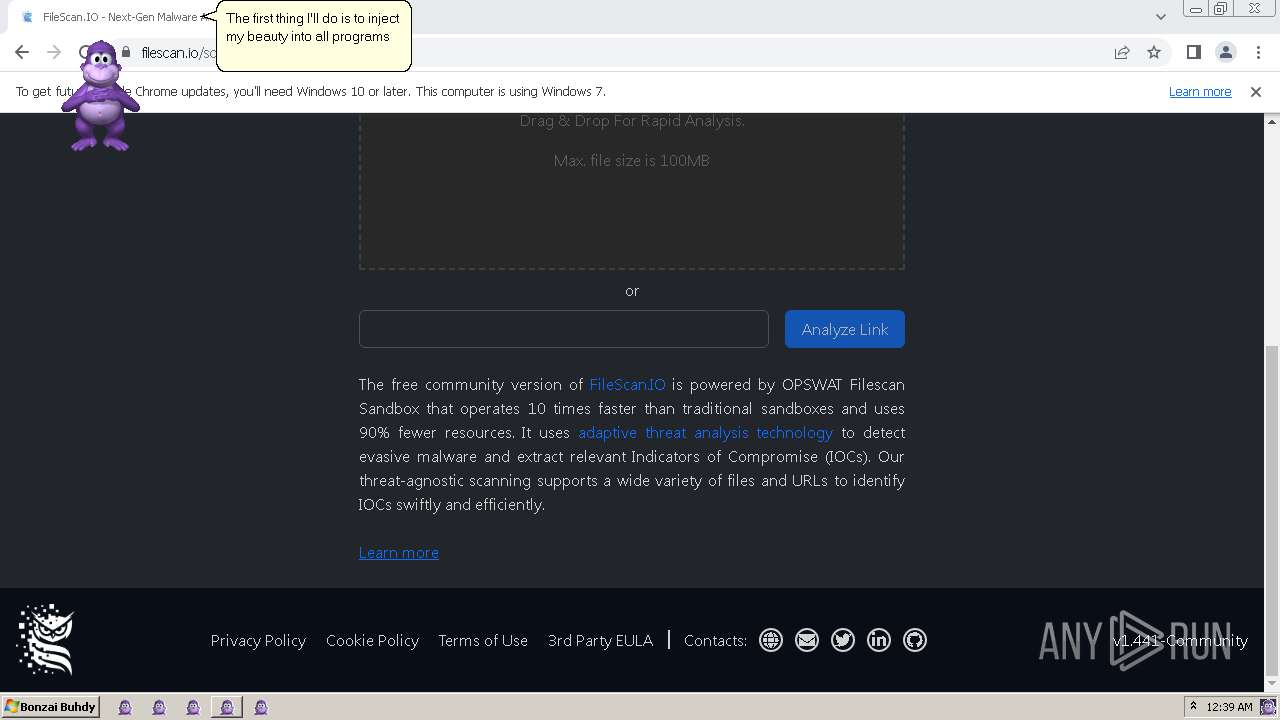
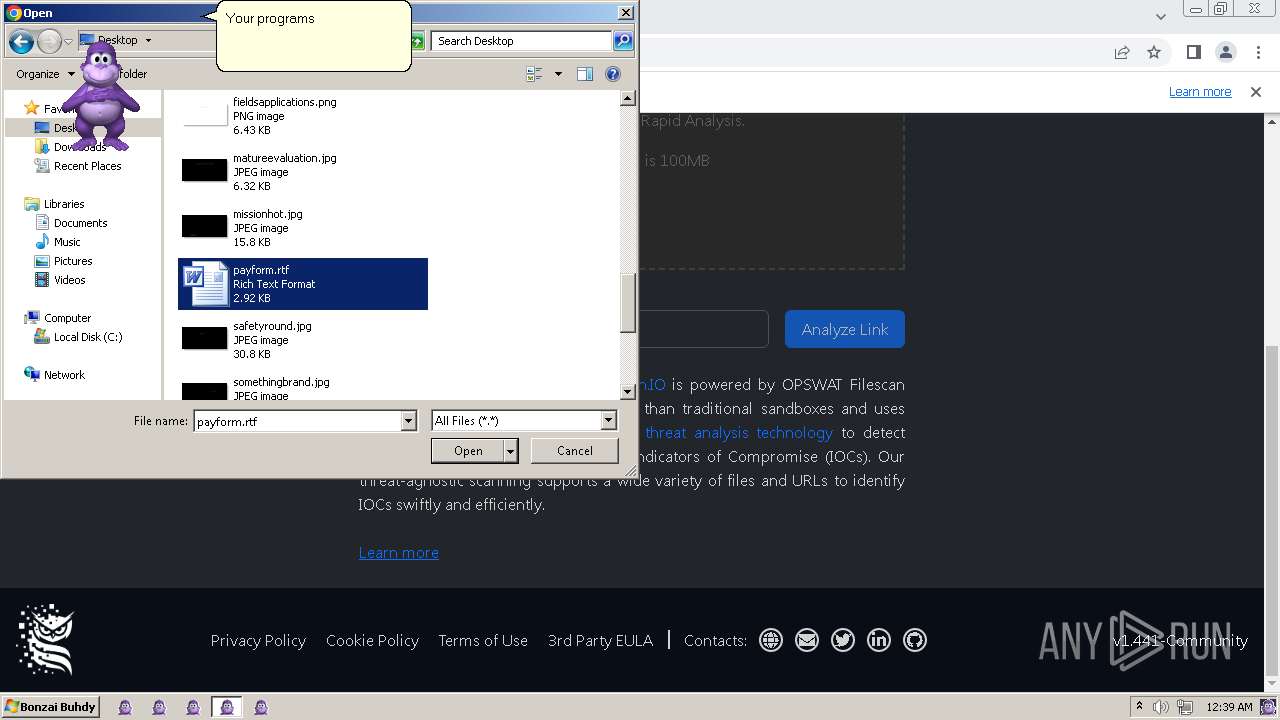
Changes the AppInit_DLLs value (autorun option)
- Bonzify.exe (PID: 3096)
Changes the autorun value in the registry
- FlashUtil32_32_0_0_453_pepper.exe (PID: 2660)
Changes Windows Error Reporting flag
- FlashUtil32_32_0_0_453_pepper.exe (PID: 2660)
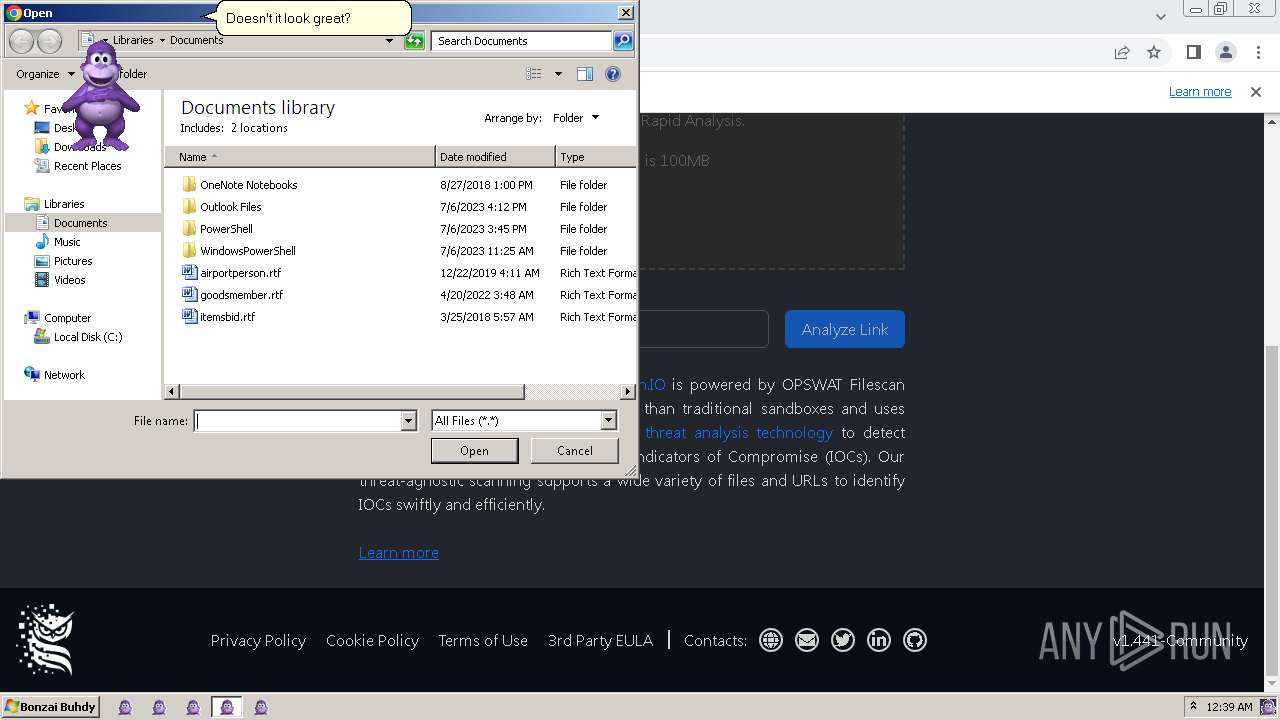
The DLL Hijacking
- ONENOTE.EXE (PID: 552)
SUSPICIOUS
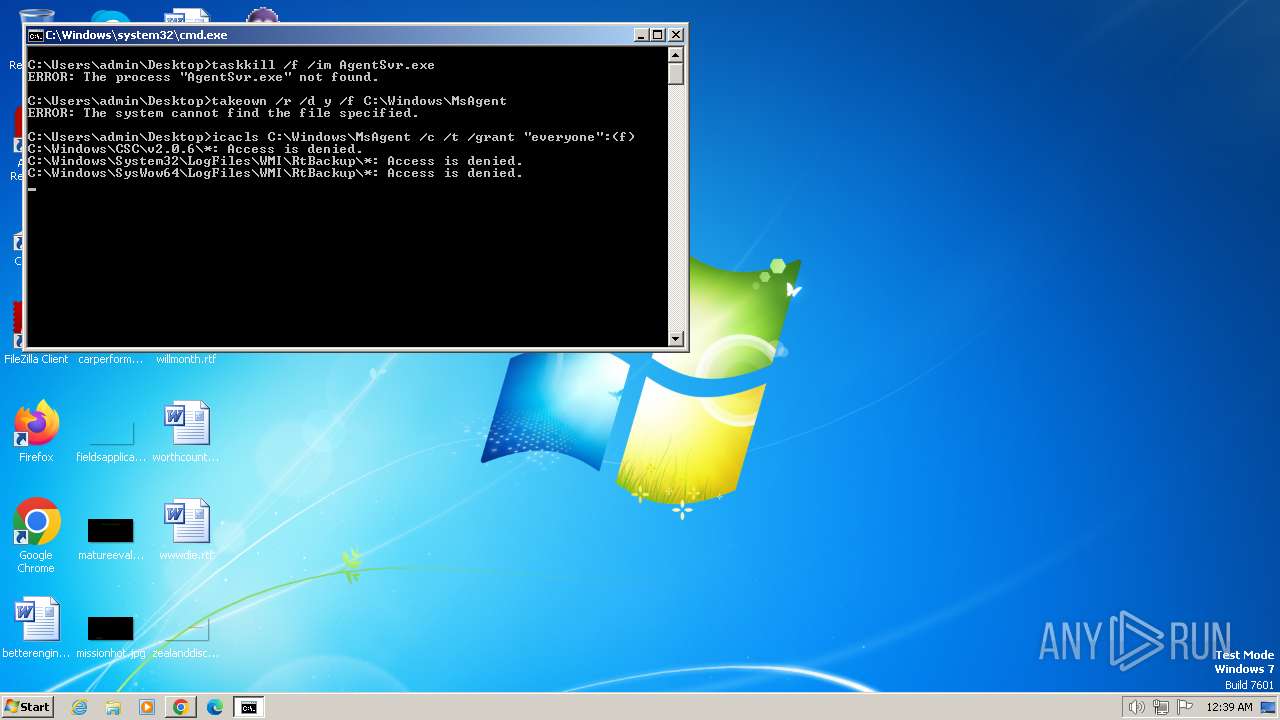
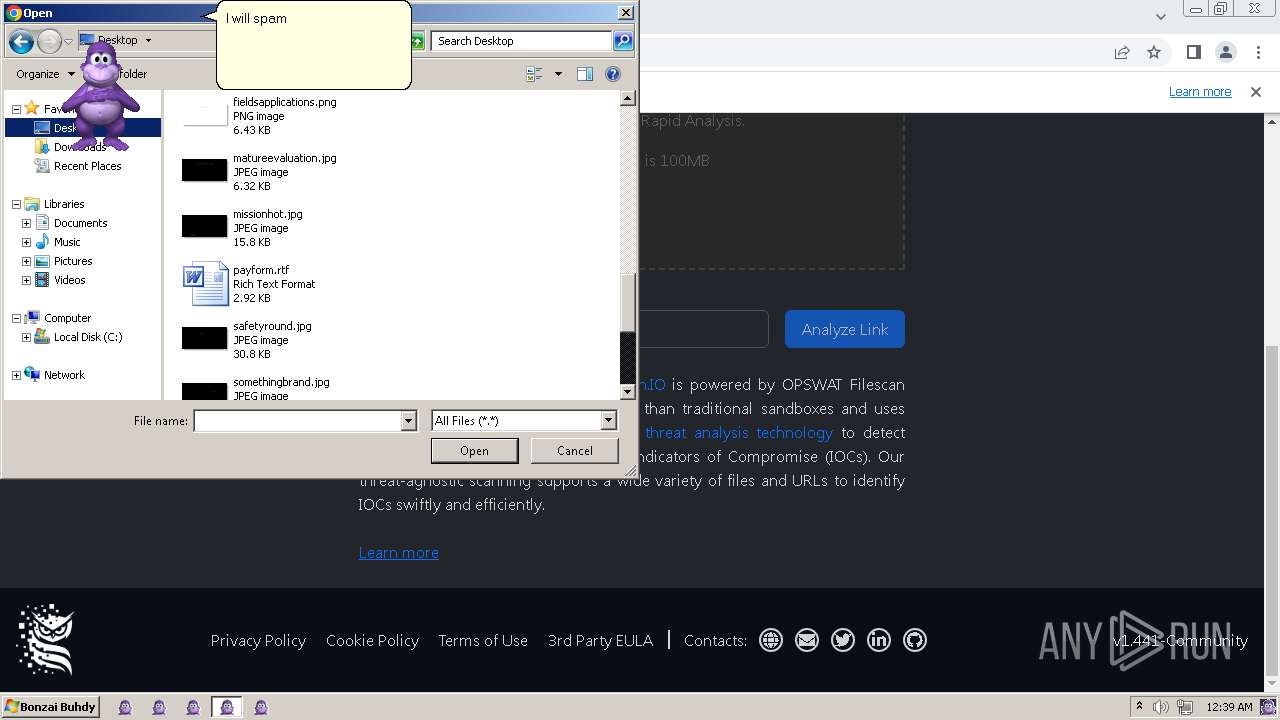
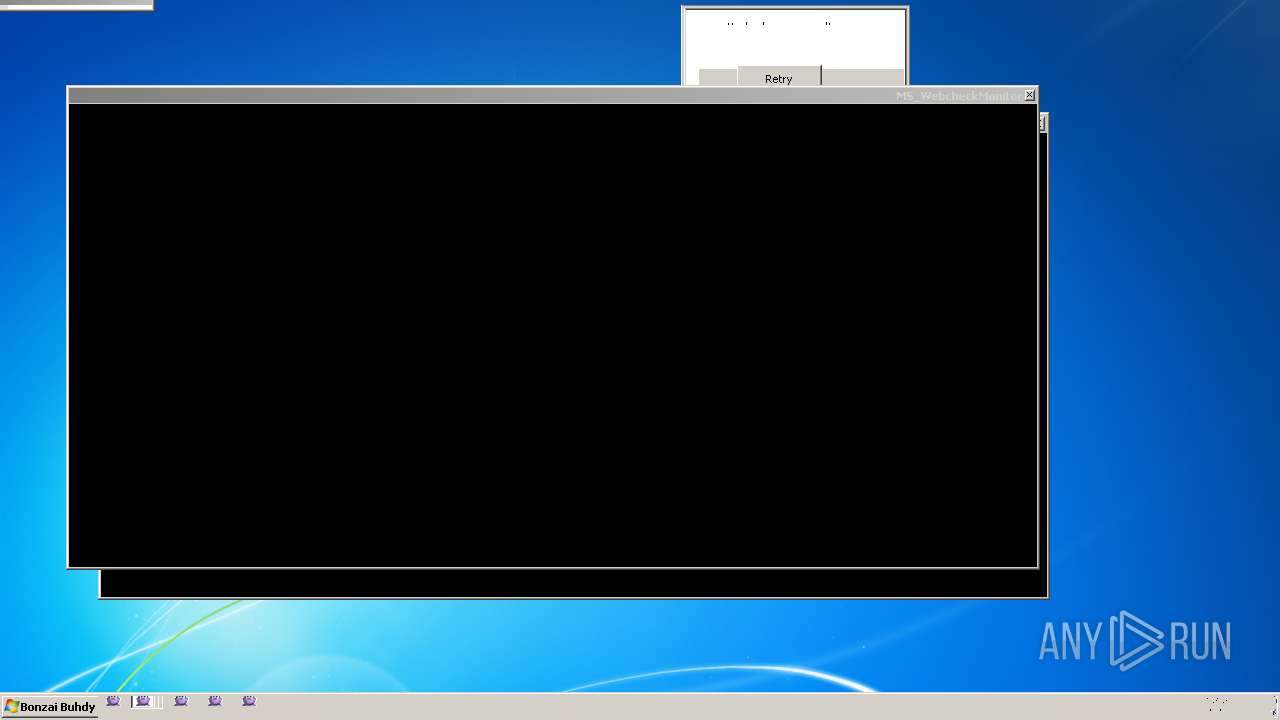
Starts CMD.EXE for commands execution
- Bonzify.exe (PID: 3096)
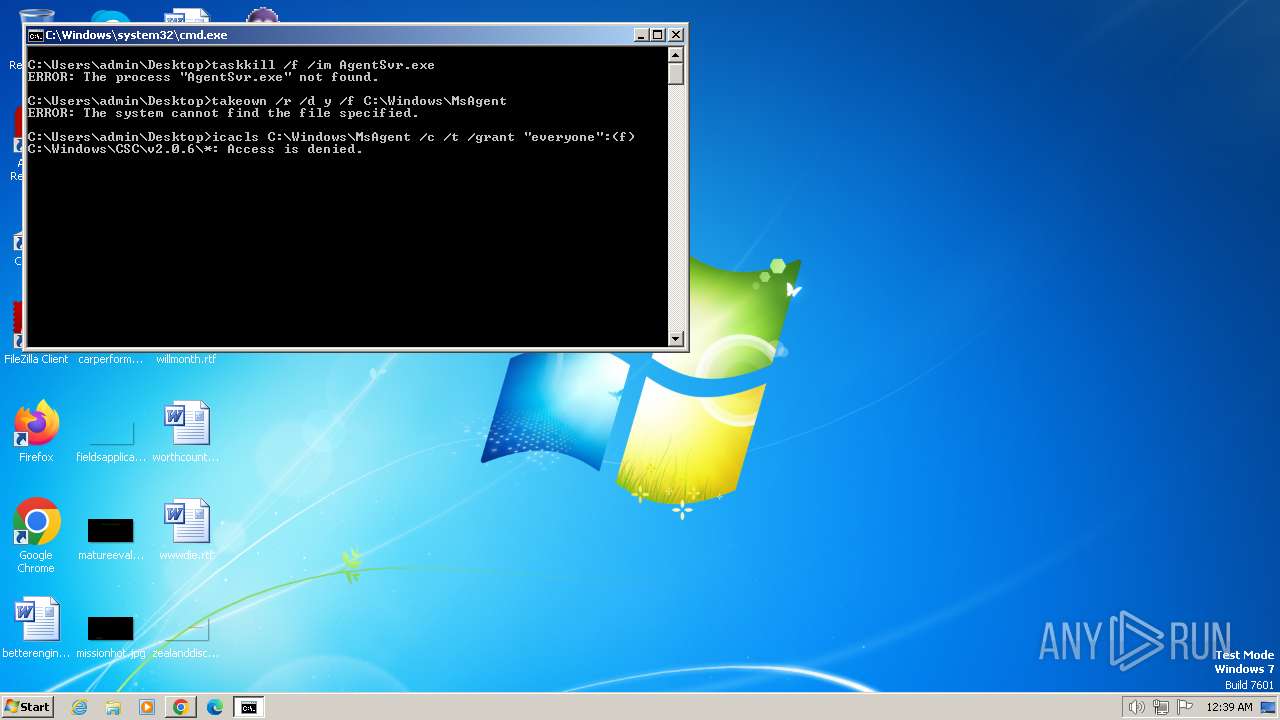
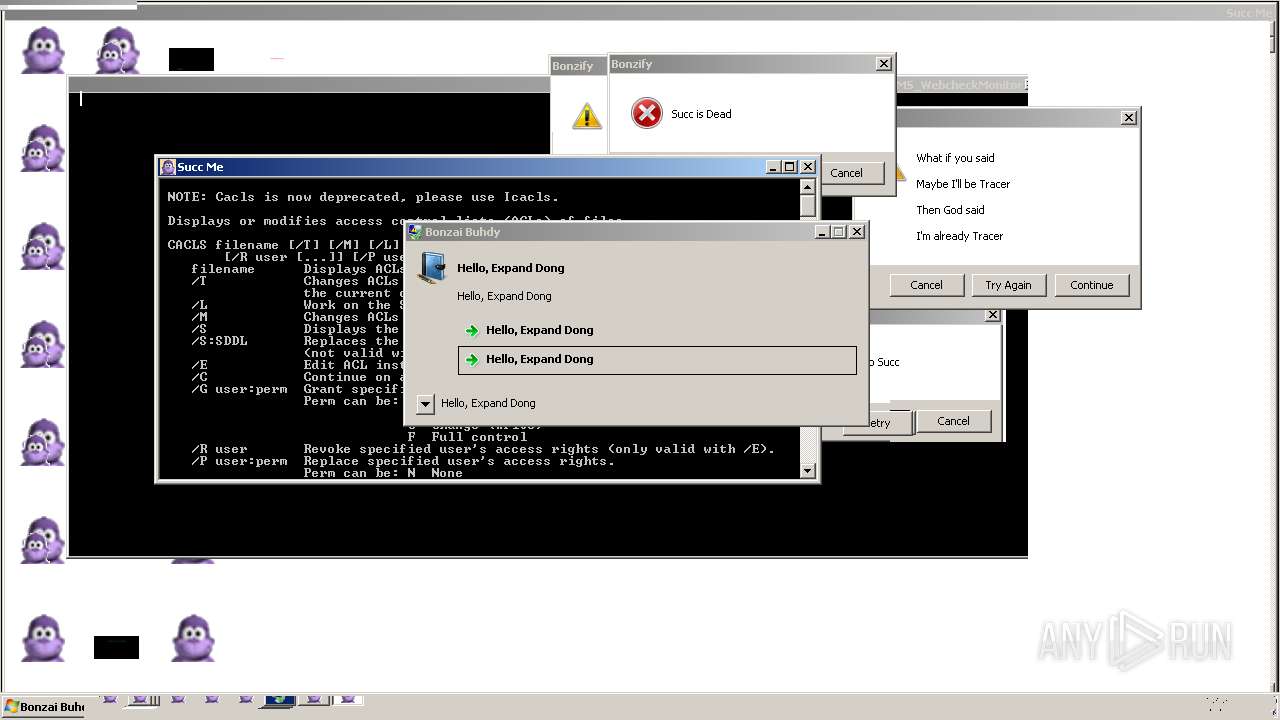
Takes ownership (TAKEOWN.EXE)
- cmd.exe (PID: 3248)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3248)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 3248)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3428)
Reads the Internet Settings
- resmon.exe (PID: 3652)
Changes internet zones settings
- FlashUtil32_32_0_0_453_pepper.exe (PID: 2660)
Executing commands from a ".bat" file
- Bonzify.exe (PID: 3096)
INFO
Drops the executable file immediately after the start
- Bonzify.exe (PID: 1592)
- Bonzify.exe (PID: 3096)
- INSTALLER.exe (PID: 3368)
- INSTALLER.exe (PID: 3692)
Checks supported languages
- Bonzify.exe (PID: 1592)
- INSTALLER.exe (PID: 3692)
- AgentSvr.exe (PID: 3492)
- AgentSvr.exe (PID: 3864)
- wmpnscfg.exe (PID: 3216)
- aspnet_wp.exe (PID: 2836)
- wmpnscfg.exe (PID: 2676)
- rundll32.exe (PID: 3000)
- FlashUtil32_32_0_0_453_pepper.exe (PID: 2660)
- resmon.exe (PID: 3652)
- appidcertstorecheck.exe (PID: 568)
- drvinst.exe (PID: 2412)
- ONENOTE.EXE (PID: 552)
- Bonzify.exe (PID: 3096)
- INSTALLER.exe (PID: 3368)
Create files in a temporary directory
- INSTALLER.exe (PID: 3368)
- INSTALLER.exe (PID: 3692)
- Bonzify.exe (PID: 3096)
Process drops legitimate windows executable
- INSTALLER.exe (PID: 3368)
- Bonzify.exe (PID: 3096)
- INSTALLER.exe (PID: 3692)
Reads the computer name
- INSTALLER.exe (PID: 3368)
- INSTALLER.exe (PID: 3692)
- Bonzify.exe (PID: 3096)
- AgentSvr.exe (PID: 3864)
- wmpnscfg.exe (PID: 3216)
- wmpnscfg.exe (PID: 2676)
- resmon.exe (PID: 3652)
- ONENOTE.EXE (PID: 552)
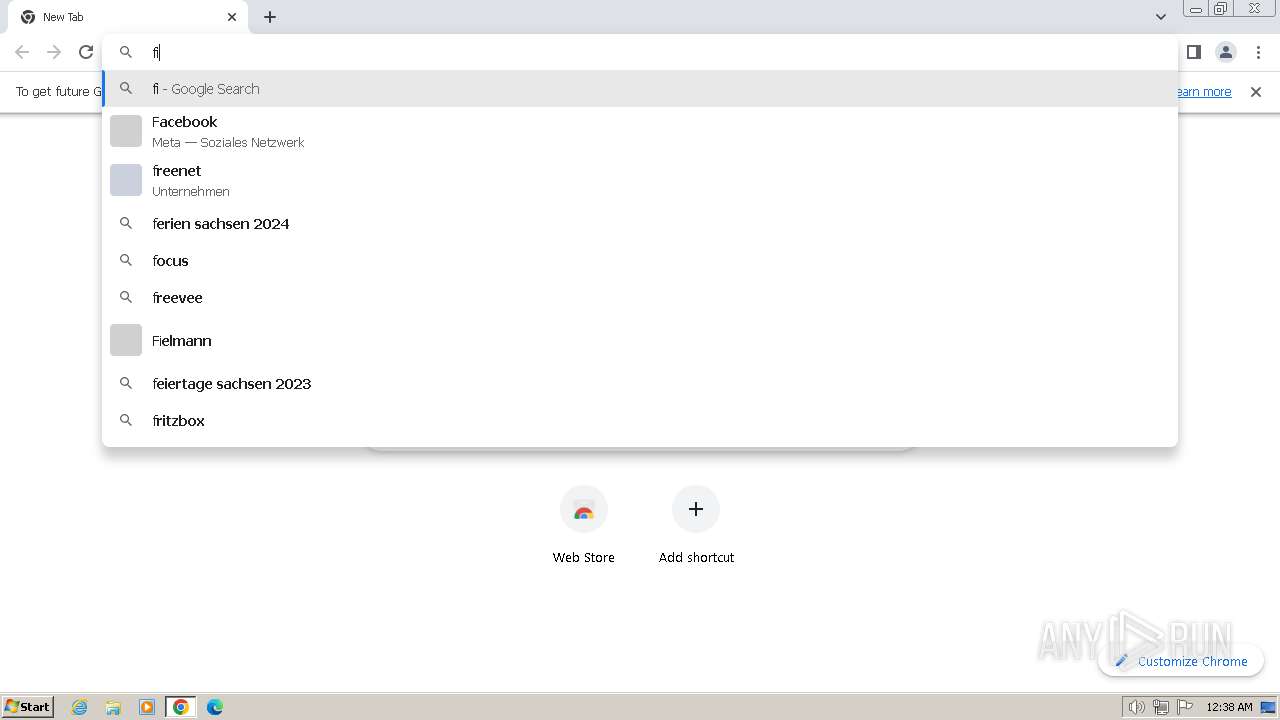
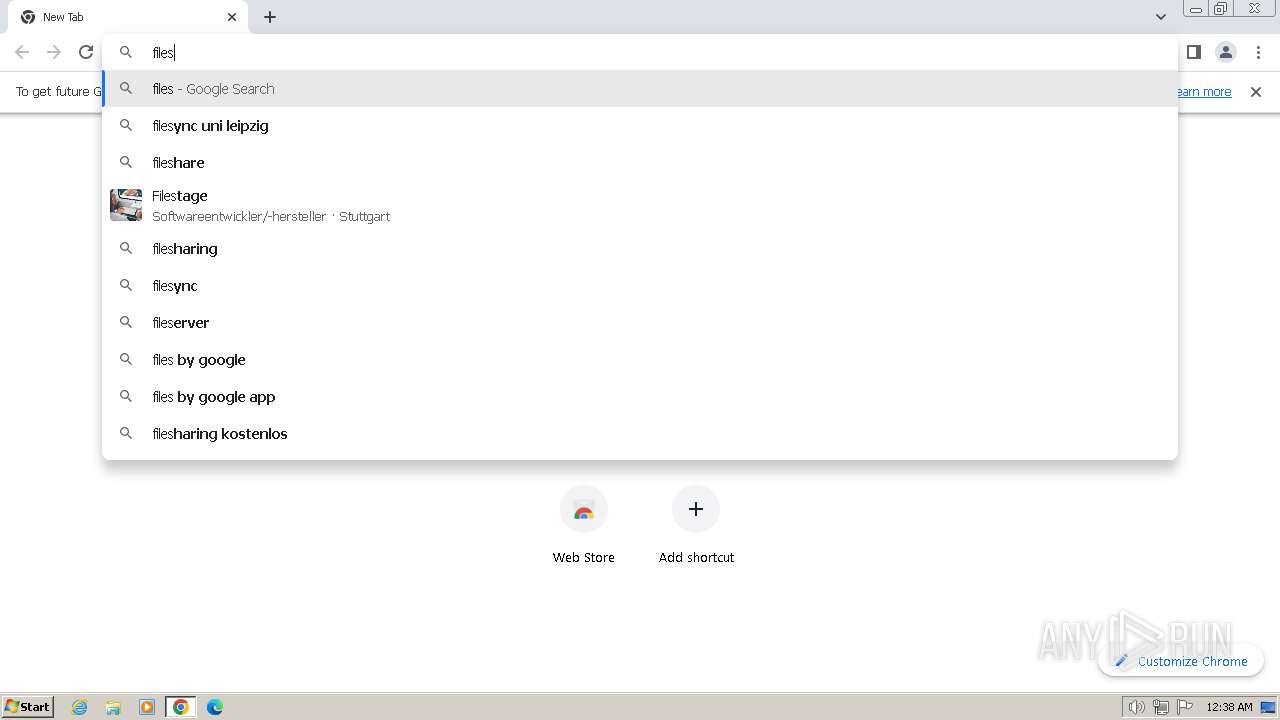
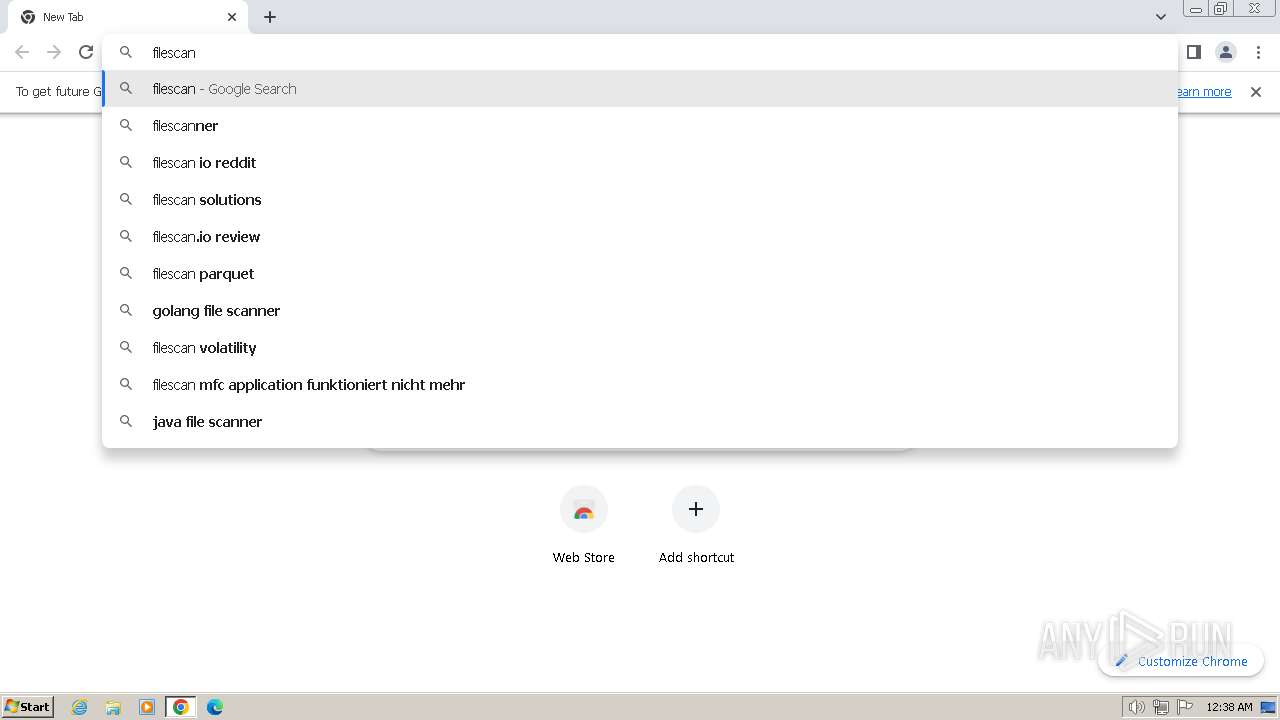
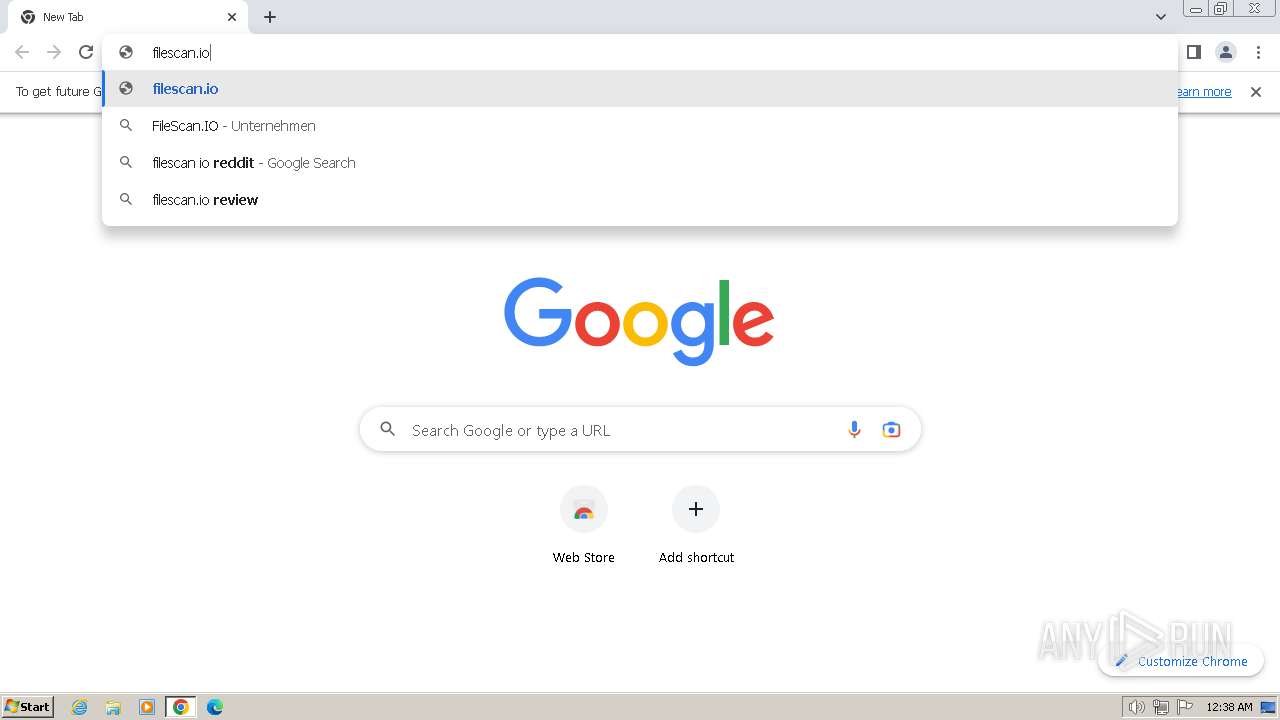
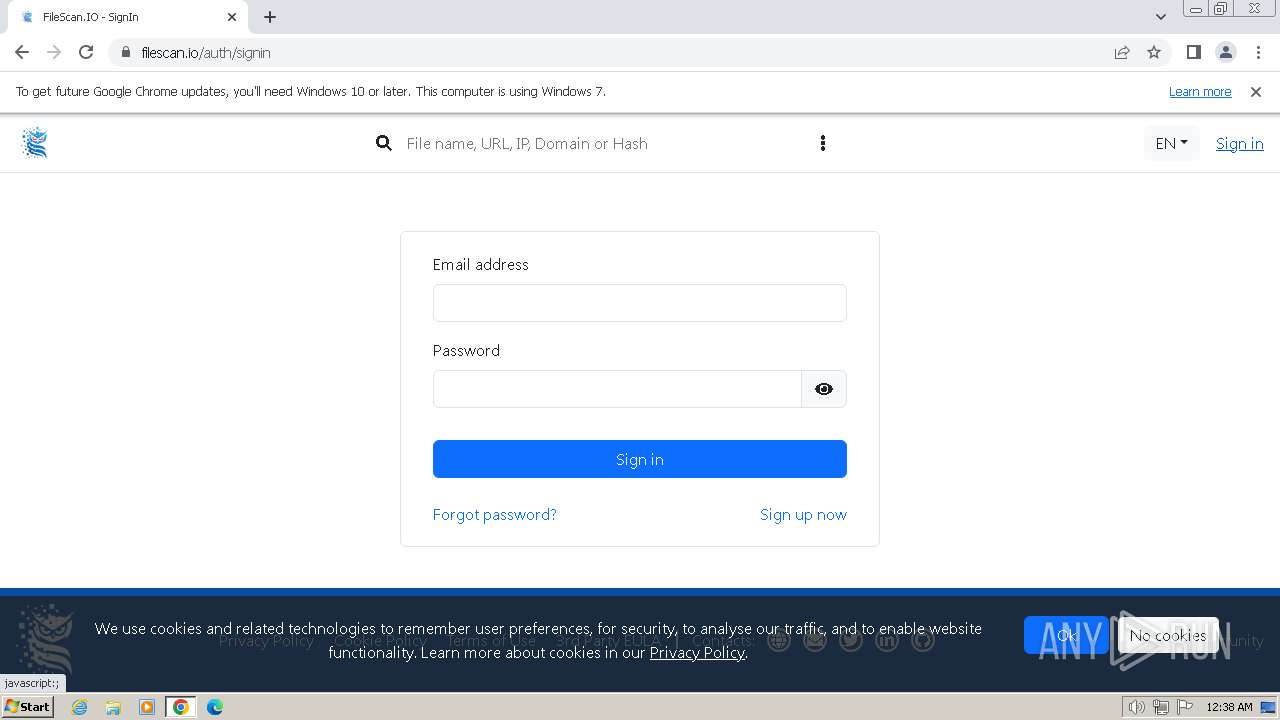
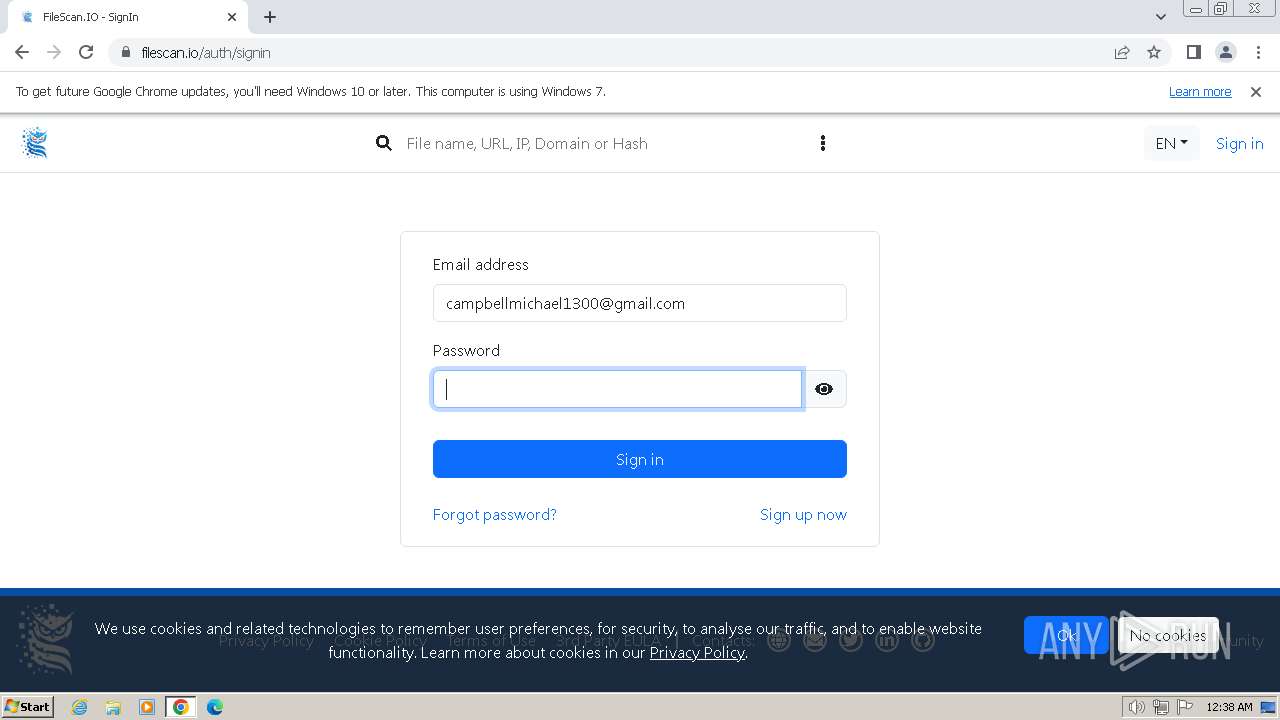
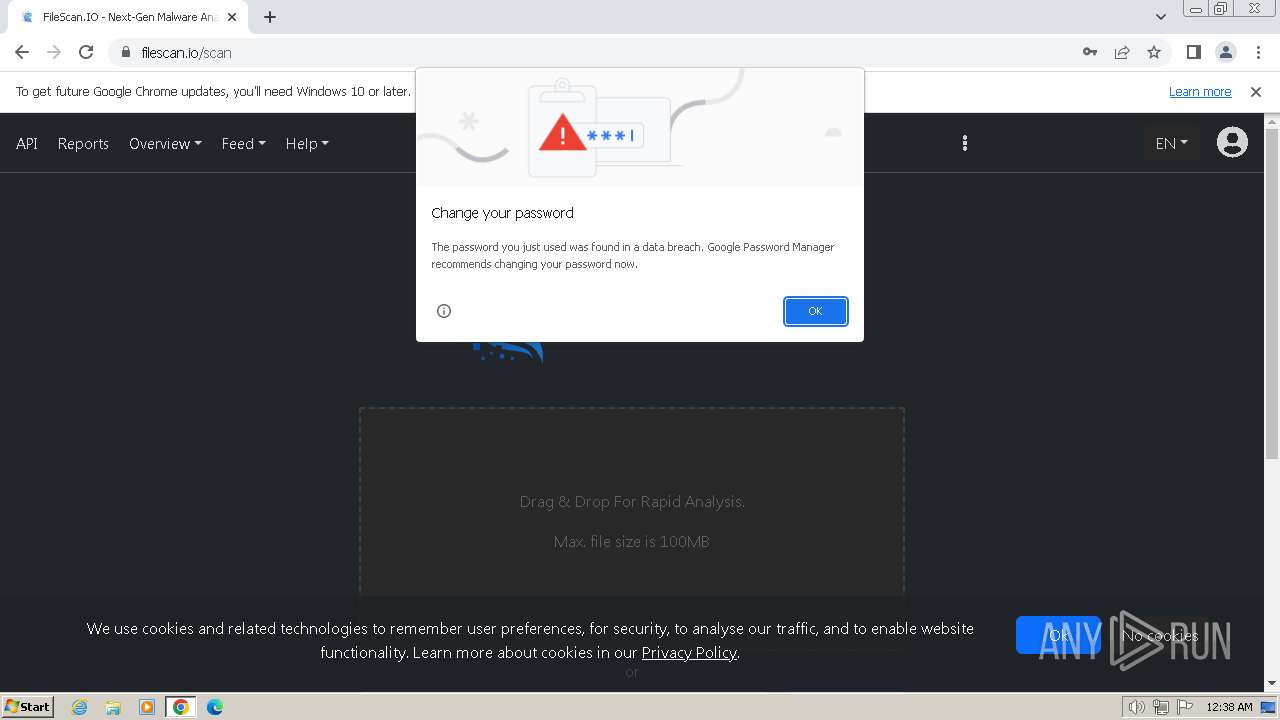
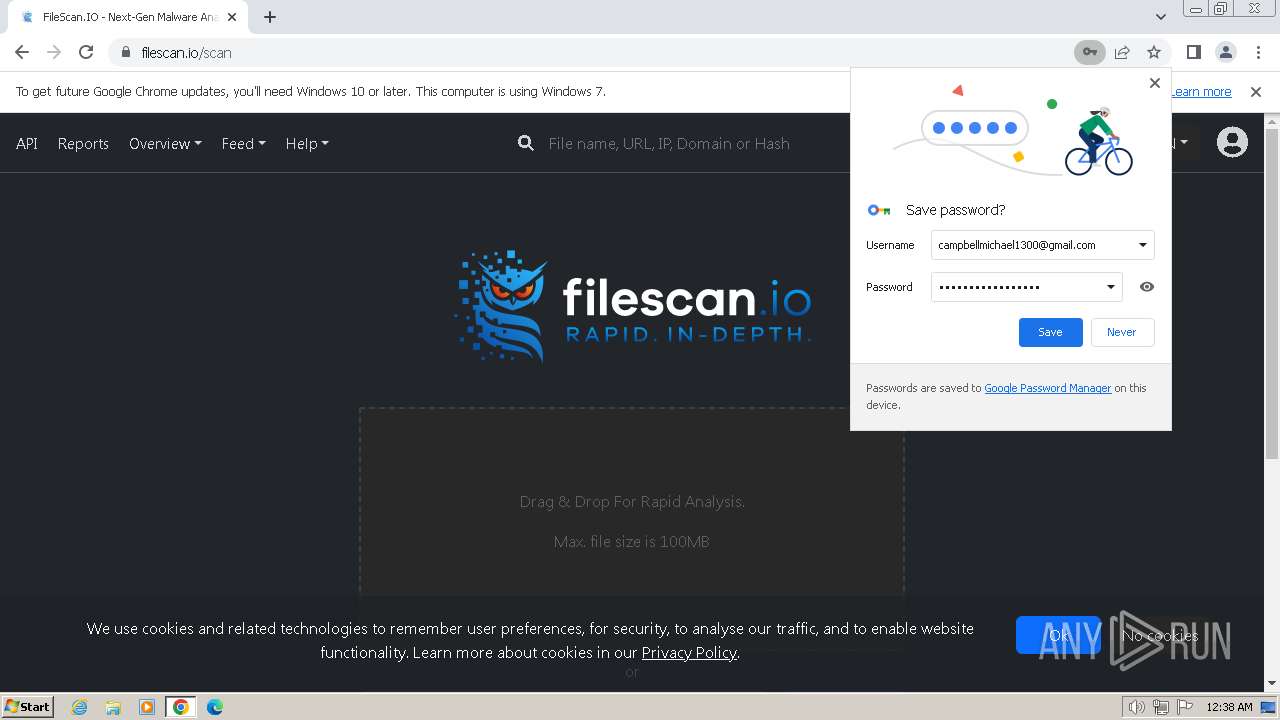
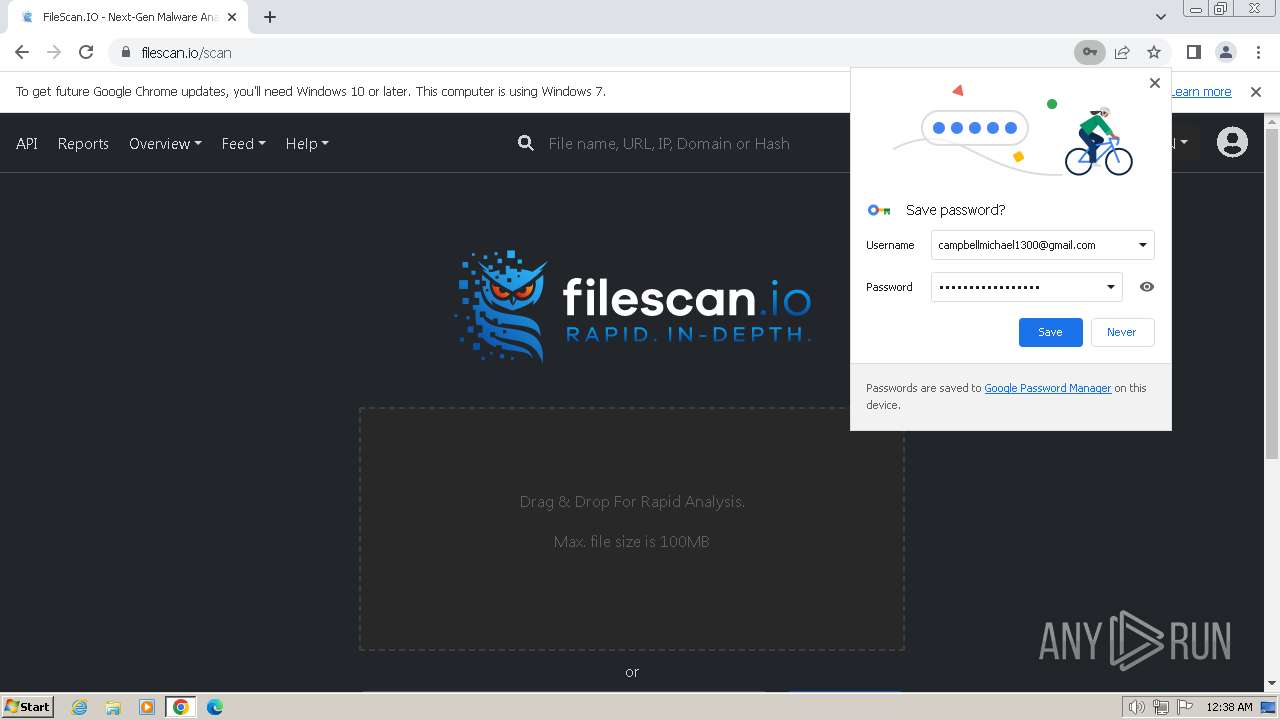
Manual execution by a user
- chrome.exe (PID: 1792)
- wmpnscfg.exe (PID: 2676)
- wmpnscfg.exe (PID: 3216)
- aspnet_wp.exe (PID: 2836)
- rundll32.exe (PID: 3000)
- MigSetup.exe (PID: 3556)
- TRACERT.EXE (PID: 3196)
- FlashUtil32_32_0_0_453_pepper.exe (PID: 2660)
- appidcertstorecheck.exe (PID: 568)
- spinstall.exe (PID: 3552)
- resmon.exe (PID: 3652)
- evntwin.exe (PID: 3944)
- smss.exe (PID: 3516)
- autochk.exe (PID: 1924)
- ONENOTE.EXE (PID: 552)
- wusa.exe (PID: 3084)
- rrinstaller.exe (PID: 2176)
- cacls.exe (PID: 3464)
- secinit.exe (PID: 1596)
- drvinst.exe (PID: 2412)
- ocsetup.exe (PID: 2672)
- IMEPADSV.EXE (PID: 3708)
- RmClient.exe (PID: 1740)
- mstsc.exe (PID: 748)
- rstrui.exe (PID: 3456)
- VaultSysUi.exe (PID: 3944)
- ntoskrnl.exe (PID: 2732)
- Bonzify.exe (PID: 3096)
- MultiDigiMon.exe (PID: 1804)
Application launched itself
- chrome.exe (PID: 1792)
Reads the machine GUID from the registry
- Bonzify.exe (PID: 3096)
- AgentSvr.exe (PID: 3864)
- FlashUtil32_32_0_0_453_pepper.exe (PID: 2660)
- resmon.exe (PID: 3652)
- ONENOTE.EXE (PID: 552)
Reads Microsoft Office registry keys
- ONENOTE.EXE (PID: 552)
Reads Environment values
- ONENOTE.EXE (PID: 552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 MS Cabinet Self-Extractor (WExtract stub) (80.4) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (8.2) |
| .exe | | | Win64 Executable (generic) (7.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.7) |
| .exe | | | Win32 Executable (generic) (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:07 19:29:20+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 4096 |
| InitializedDataSize: | 3719680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16b0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
262
Monitored processes
69
Malicious processes
4
Suspicious processes
1
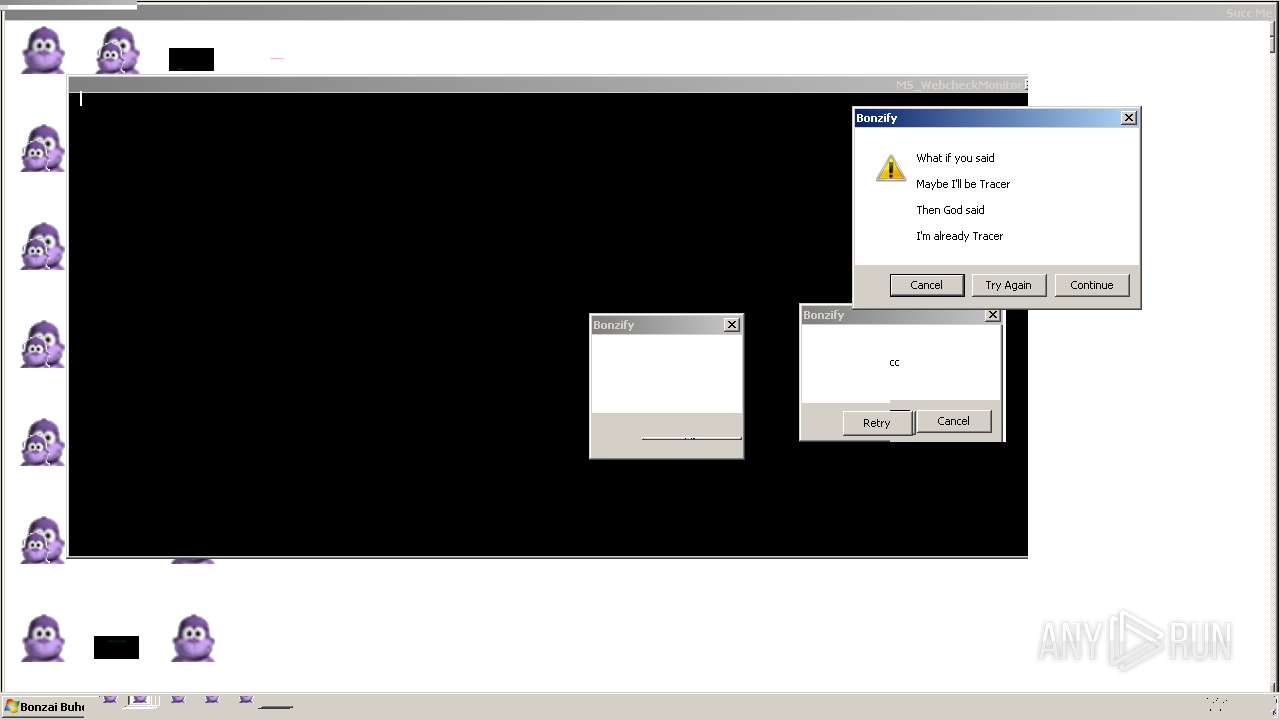
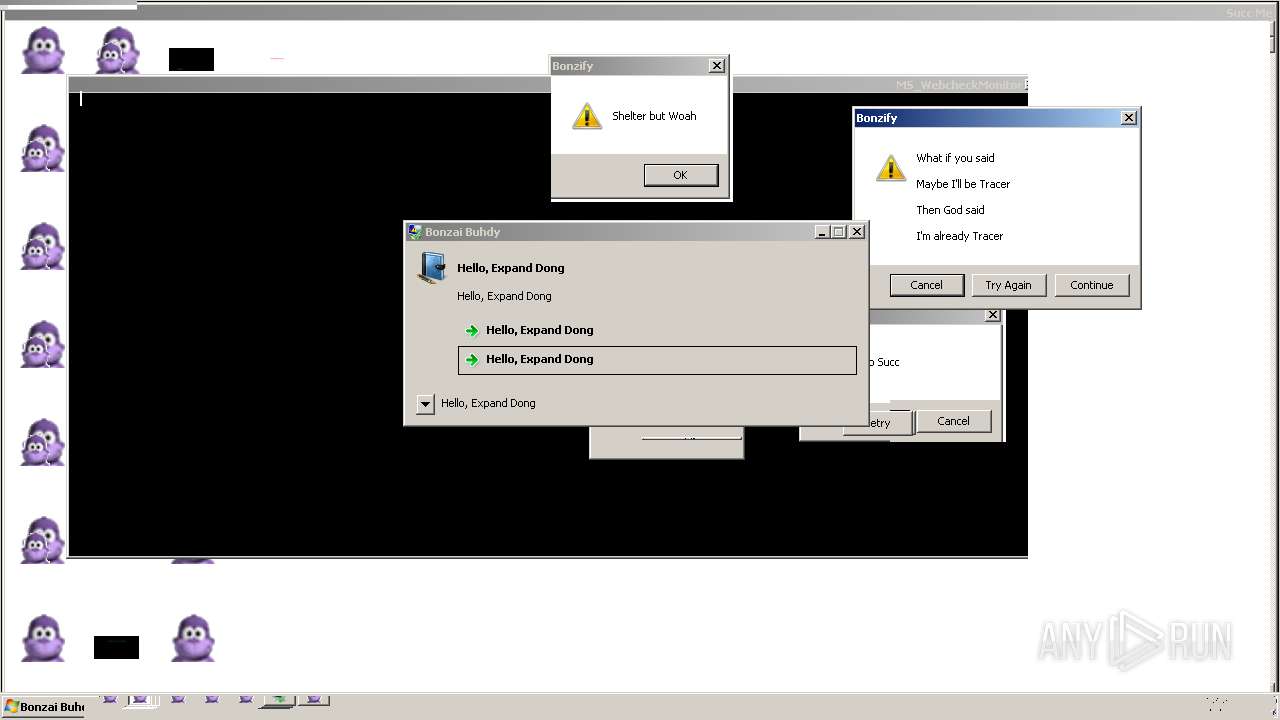
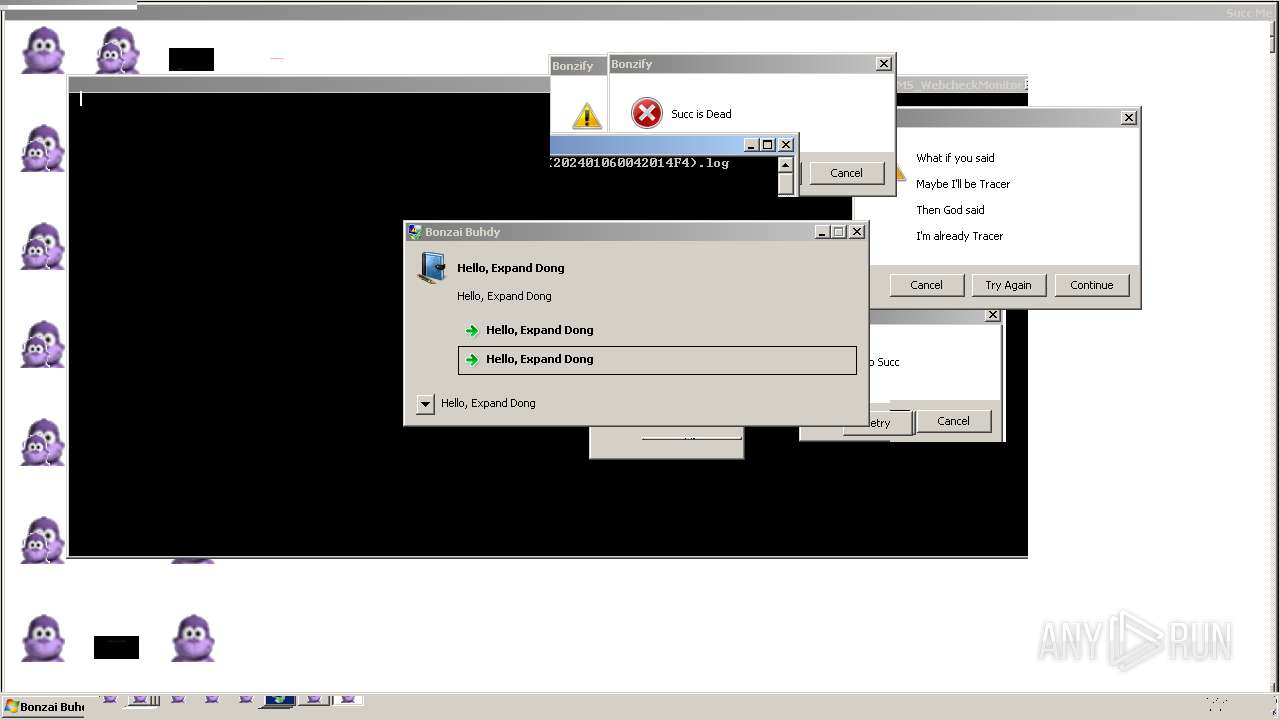
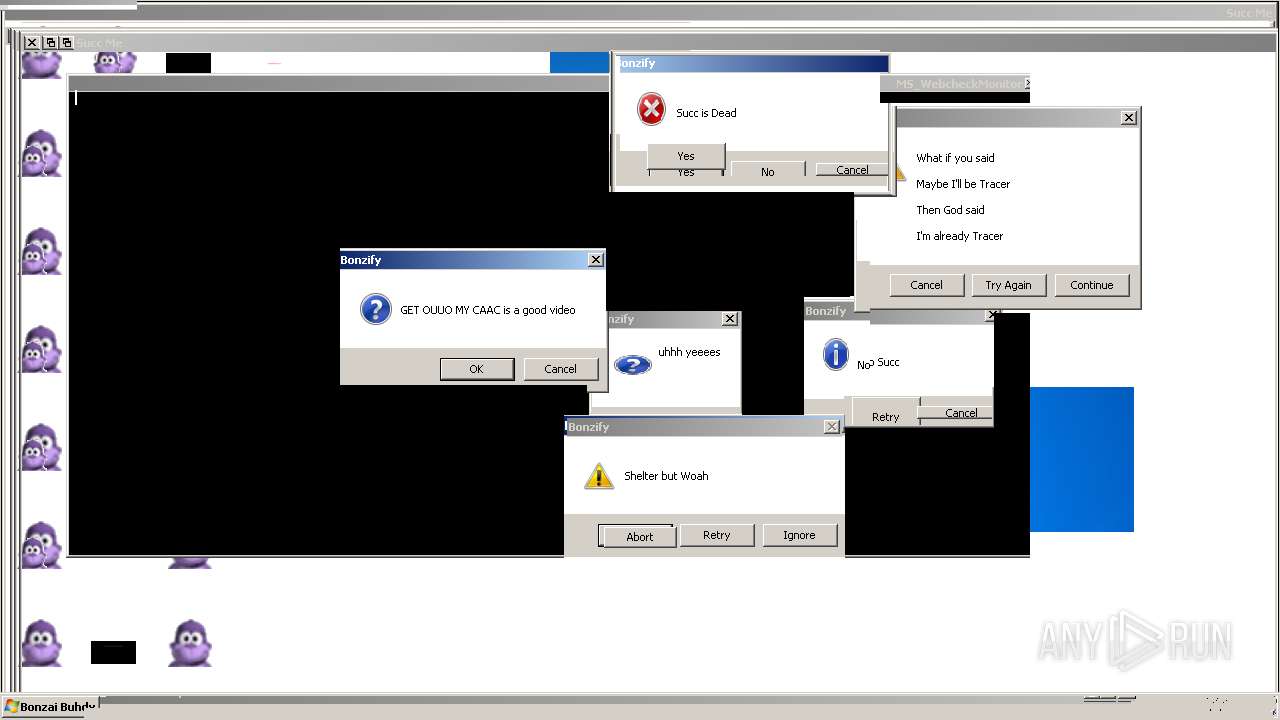
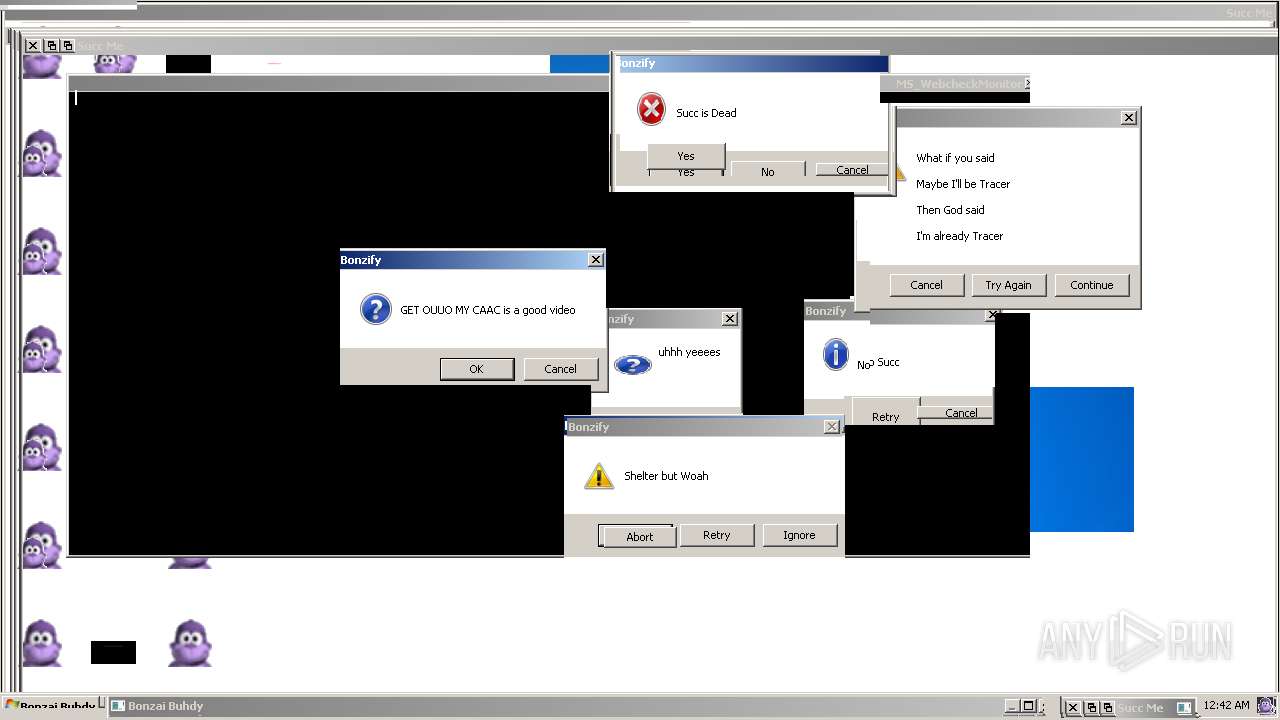
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1140 --field-trial-handle=1132,i,16395484461639713926,16942646810409423376,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 292 | takeown /r /d y /f C:\Windows\MsAgent | C:\Windows\System32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | "C:\Windows\Installer\$PatchCache$\Managed\00004109D30000000000000000F01FEC\14.0.4763\ONENOTE.EXE" | C:\Windows\Installer\$PatchCache$\Managed\00004109D30000000000000000F01FEC\14.0.4763\ONENOTE.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Exit code: 0 Version: 14.0.4763.1000 Modules
| |||||||||||||||
| 568 | "C:\Windows\winsxs\x86_microsoft-windows-appid_31bf3856ad364e35_6.1.7601.24545_none_59bd614a299ec1c1\appidcertstorecheck.exe" | C:\Windows\winsxs\x86_microsoft-windows-appid_31bf3856ad364e35_6.1.7601.24545_none_59bd614a299ec1c1\appidcertstorecheck.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AppID Certificate Store Verification Task Exit code: 5 Version: 6.1.7601.24545 (win7sp1_ldr_escrow.200102-1707) Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1960 --field-trial-handle=1132,i,16395484461639713926,16942646810409423376,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 1 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 748 | "C:\Windows\winsxs\x86_microsoft-windows-t..minalservicesclient_31bf3856ad364e35_6.1.7601.22252_none_503ff5a79899aaee\mstsc.exe" | C:\Windows\winsxs\x86_microsoft-windows-t..minalservicesclient_31bf3856ad364e35_6.1.7601.22252_none_503ff5a79899aaee\mstsc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Remote Desktop Connection Exit code: 0 Version: 6.1.7601.22252 (win7sp1_ldr.130214-1432) Modules
| |||||||||||||||
| 844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6d798b38,0x6d798b48,0x6d798b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1056 | "C:\Windows\System32\perfmon.exe" /res | C:\Windows\System32\perfmon.exe | resmon.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Resource and Performance Monitor Exit code: 3221226356 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | "C:\Windows\System32\perfmon.exe" /res | C:\Windows\System32\perfmon.exe | — | resmon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Resource and Performance Monitor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2180 --field-trial-handle=1132,i,16395484461639713926,16942646810409423376,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
5 967
Read events
5 658
Write events
291
Delete events
18
Modification events
| (PID) Process: | (1792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1792) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
56
Suspicious files
175
Text files
36
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe2b80.TMP | — | |
MD5:— | SHA256:— | |||
| 1792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 1792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe2e8d.TMP | — | |
MD5:— | SHA256:— | |||
| 1792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0b1f38fd-1672-4d74-a07b-4b7211c5615e.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 1792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
36
DNS requests
48
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 6.50 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 8.65 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 14.2 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 9.90 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 30.6 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 16.4 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 93.5 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 189 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acf5iuk6pnjlc6lnxtqm5ki6eoqq_112.300.200/gkmgaooipdjhmangpemjhigmamcehddo_112.300.200_win_aclnpjhtsv44pze3qmxsxb7fq66q.crx3 | US | binary | 70.5 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2336 | chrome.exe | 216.58.212.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
1792 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2336 | chrome.exe | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | unknown |
2336 | chrome.exe | 142.250.186.164:443 | www.google.com | GOOGLE | US | whitelisted |
2336 | chrome.exe | 216.58.212.174:443 | encrypted-tbn0.gstatic.com | GOOGLE | US | whitelisted |
2336 | chrome.exe | 142.250.185.163:443 | update.googleapis.com | GOOGLE | US | whitelisted |
2336 | chrome.exe | 142.250.186.97:443 | lh5.googleusercontent.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
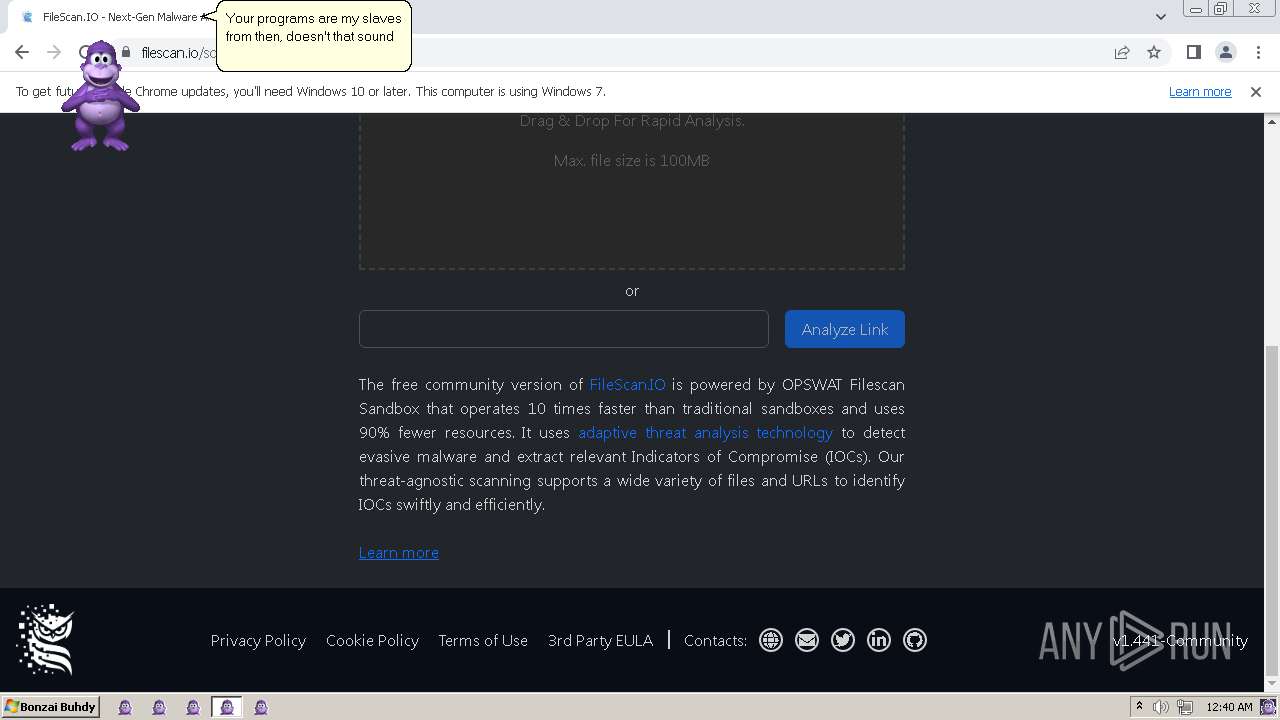
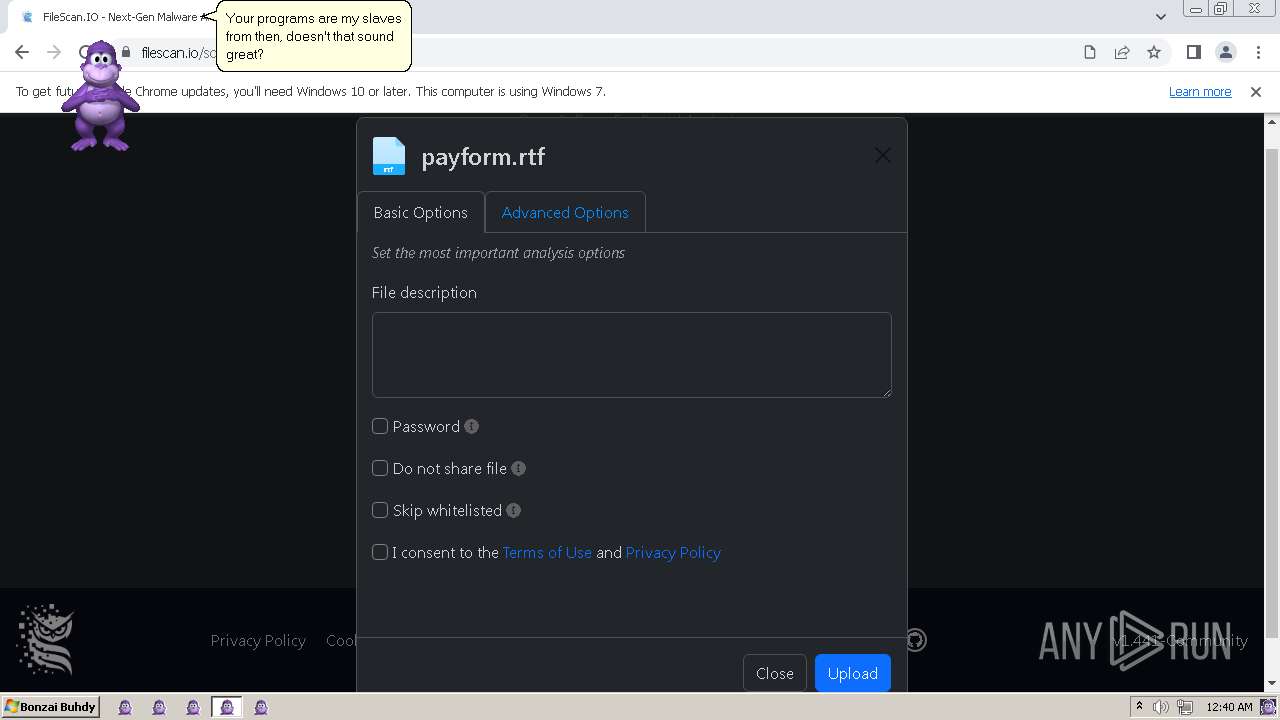
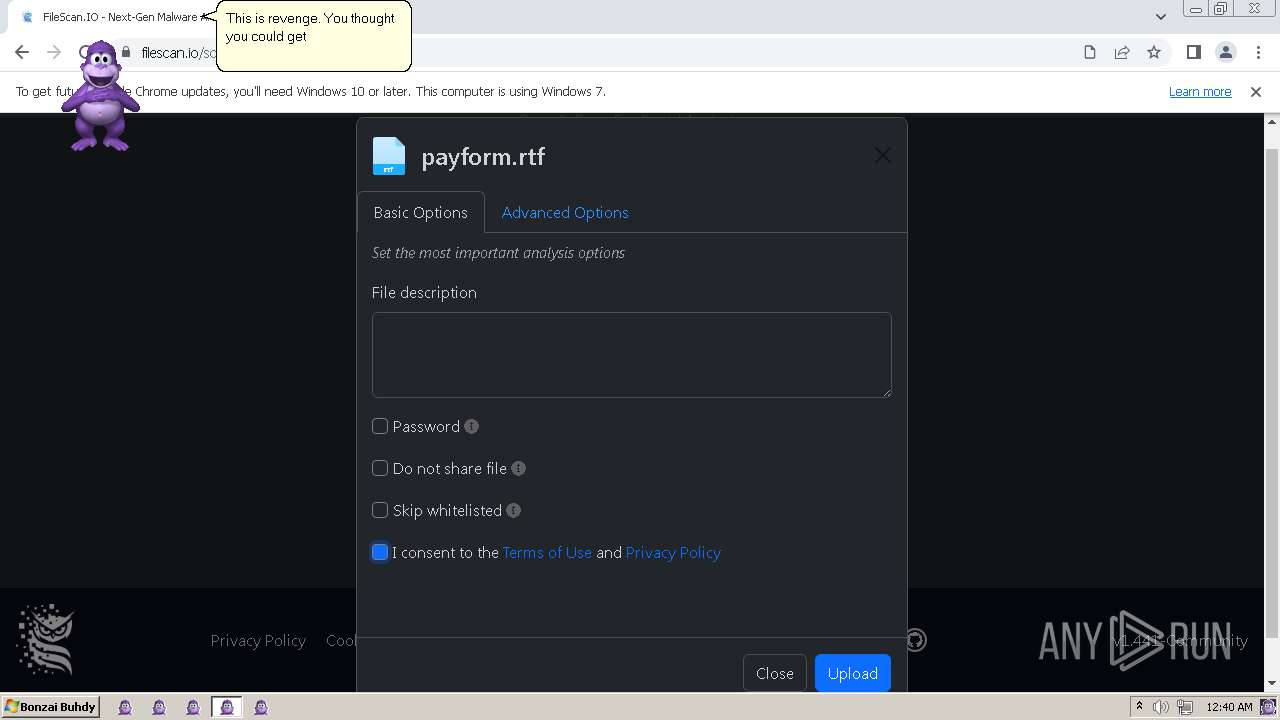
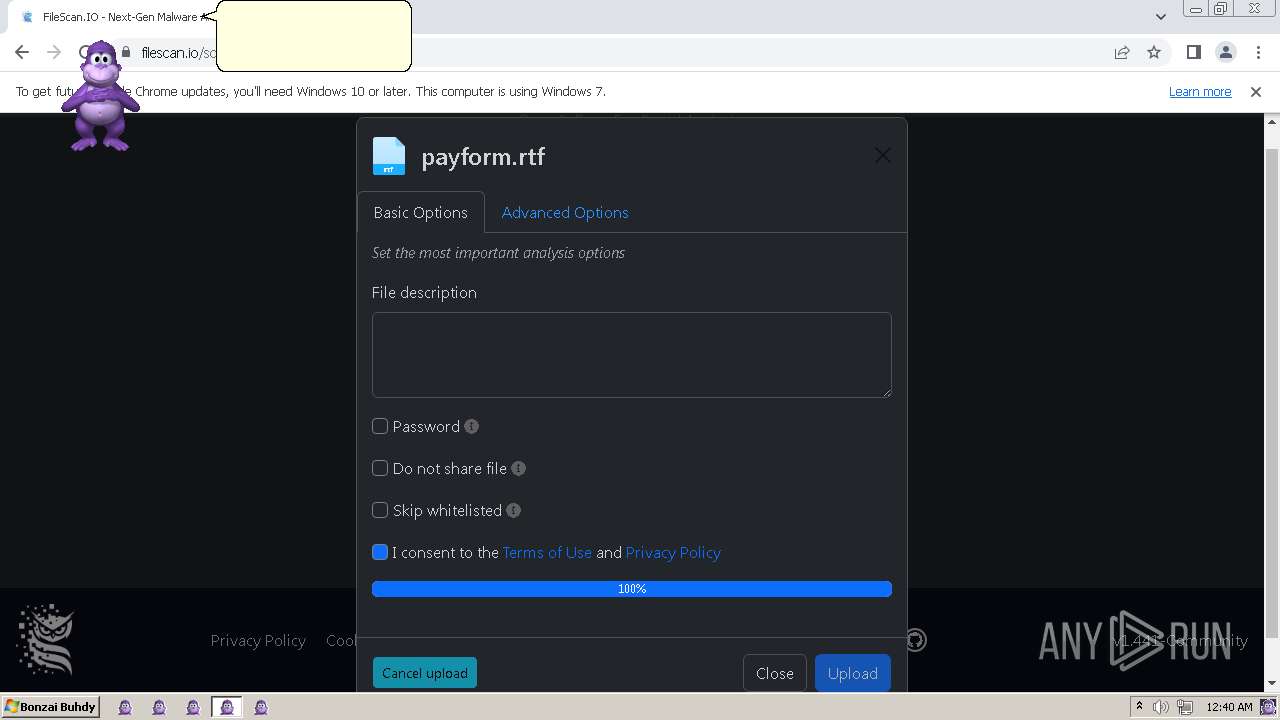
filescan.io |
| unknown |
www.filescan.io |
| unknown |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | ClaimOutput
|
AgentSvr.exe | UnclaimOutput
|
AgentSvr.exe | ClaimOutput
|