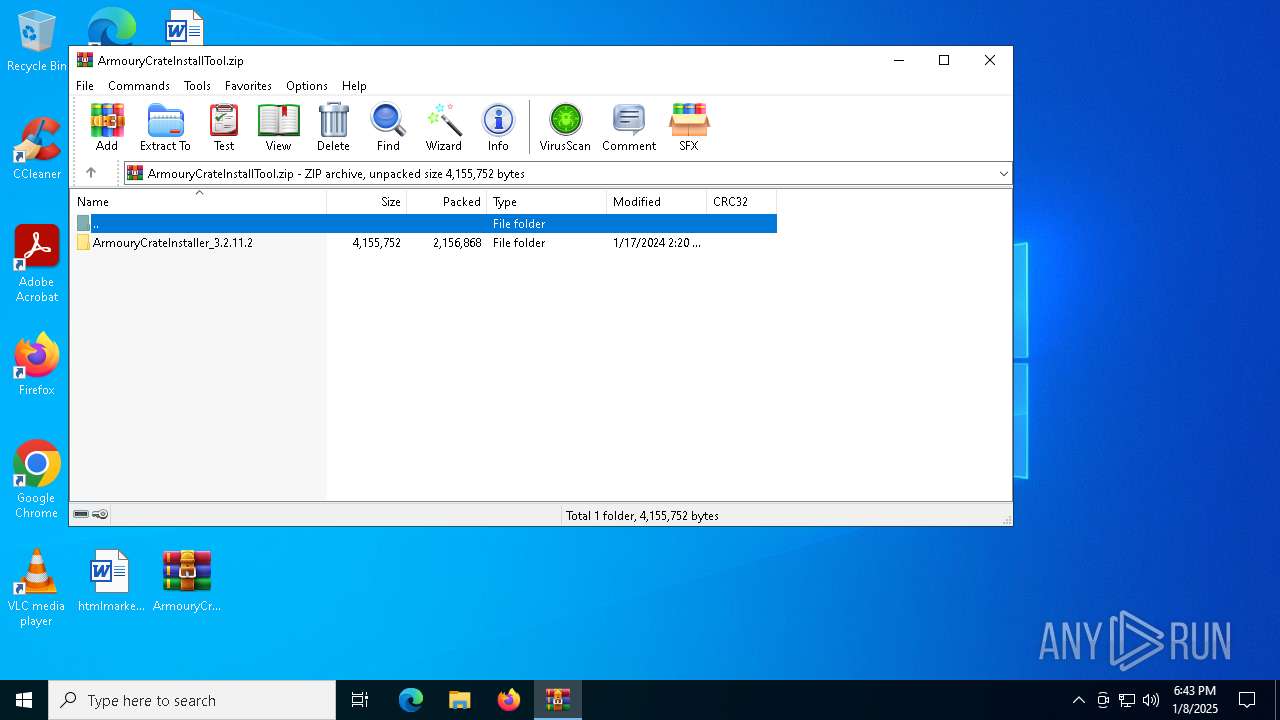
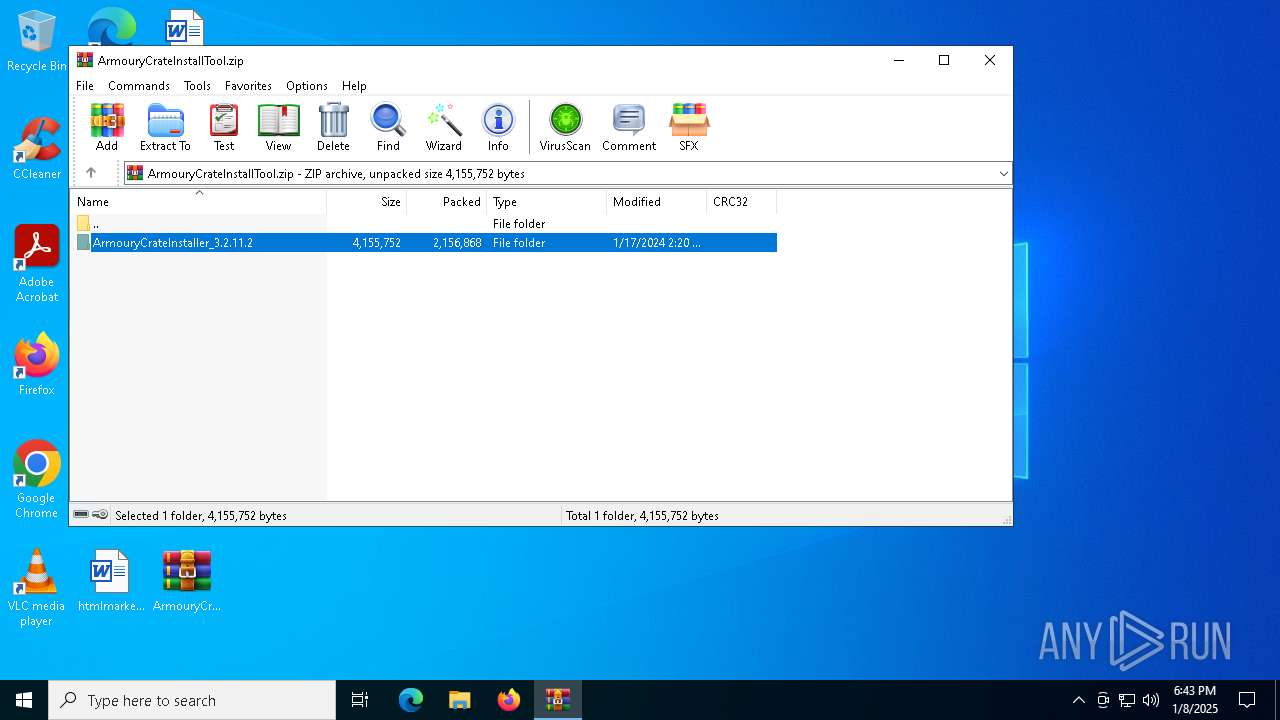
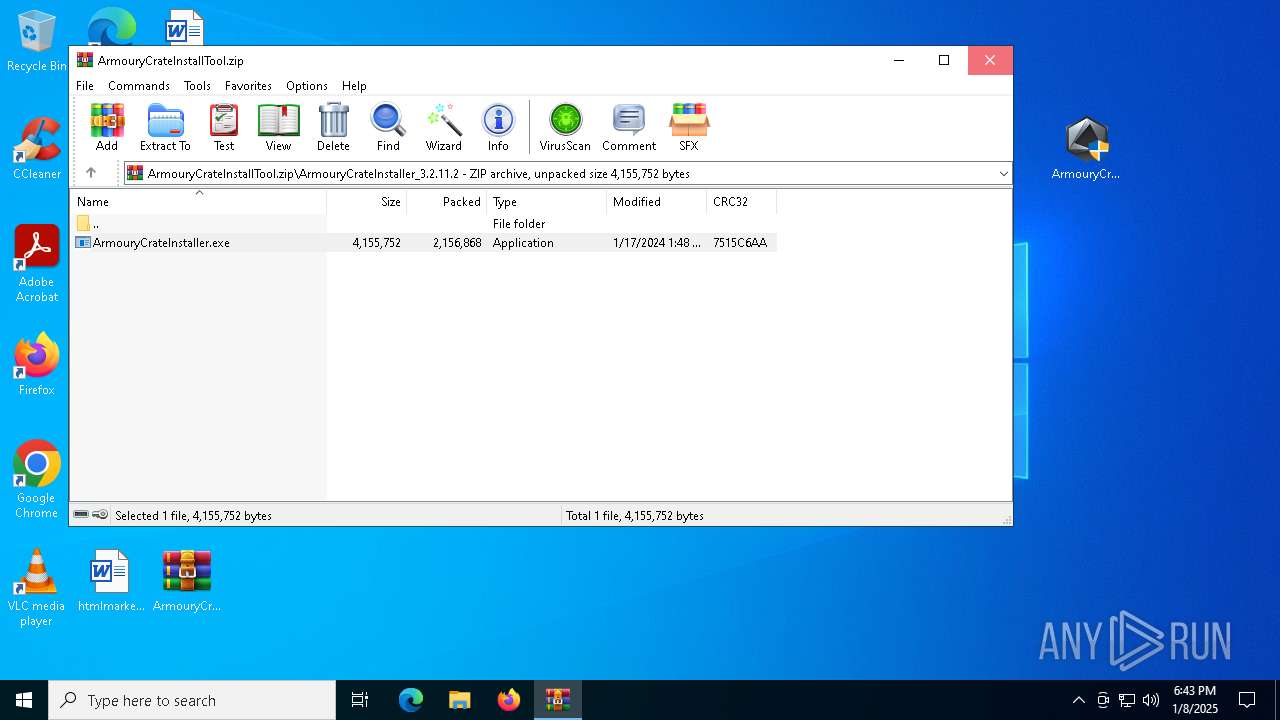
| File name: | ArmouryCrateInstallTool.zip |
| Full analysis: | https://app.any.run/tasks/2c281b77-0713-4cd9-b59b-556c7054d3ea |
| Verdict: | Malicious activity |
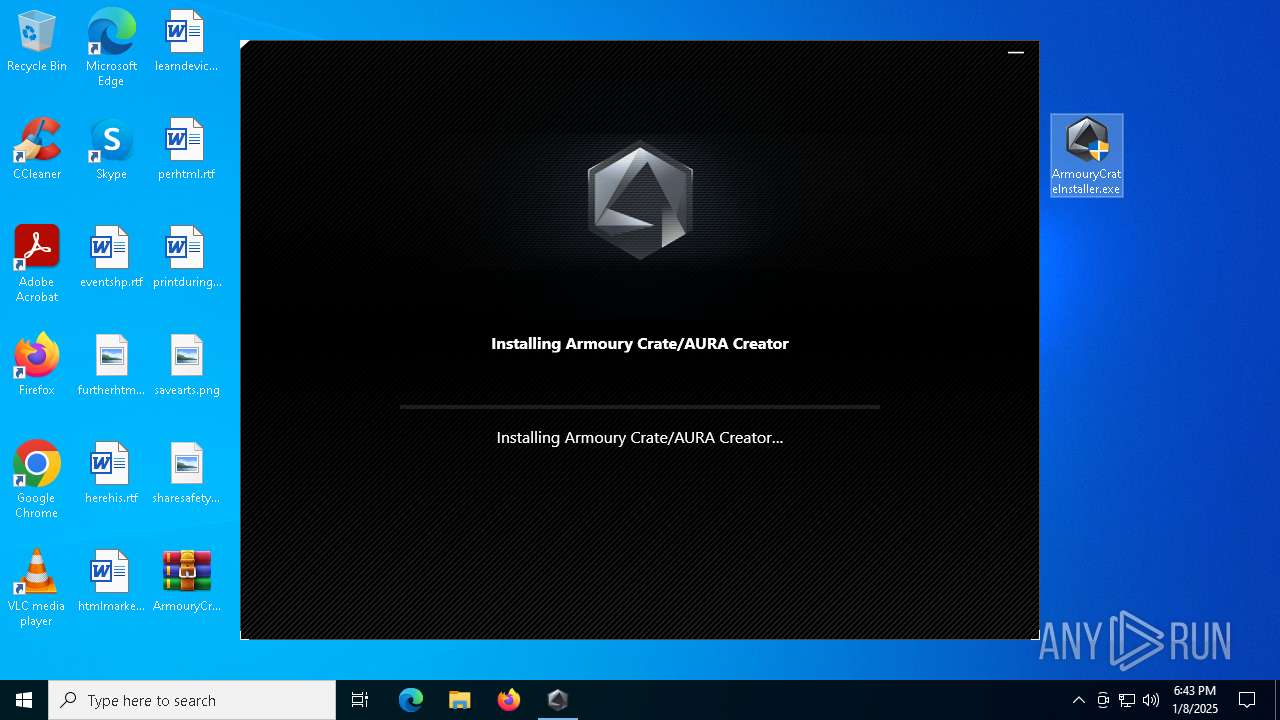
| Analysis date: | January 08, 2025, 18:43:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 5AA44ECC50E018B31837A73DB413DCD2 |
| SHA1: | AF87F99A9F370BB7BD38ACA26E63D07110B5D798 |
| SHA256: | E365596C8B51835DCEA310AF6603707A4C87BDA046E476FCFEB3A82869E6132E |
| SSDEEP: | 98304:Xskh3SEGMQIQqCUq/w3WVSjVV5BUuRLFbTBtShmq/X889S8qeilfHU+mpwm8/PFk:1z+ |
MALICIOUS
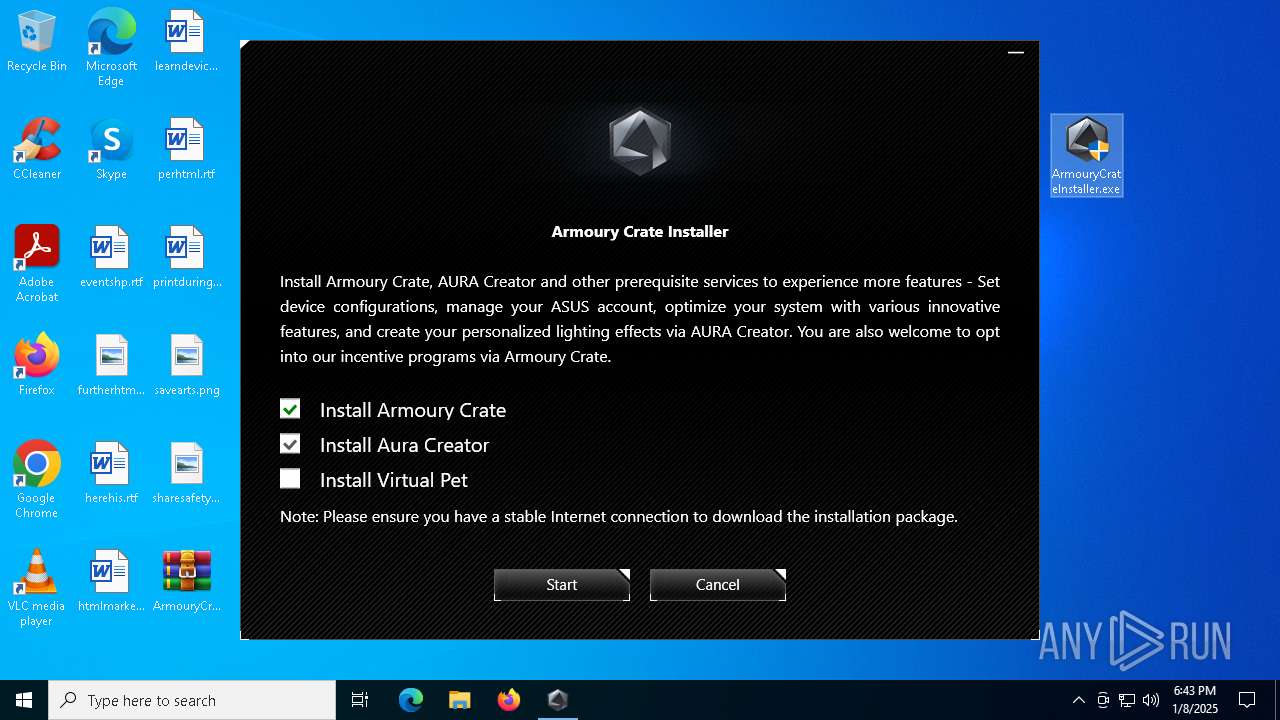
Generic archive extractor
- WinRAR.exe (PID: 6552)
SUSPICIOUS
Executable content was dropped or overwritten
- ArmouryCrateInstaller.exe (PID: 6192)
- AsZip.exe (PID: 628)
Reads the date of Windows installation
- ArmouryCrateInstaller.exe (PID: 6192)
- ROGLSLoader.exe (PID: 5032)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4816)
- cmd.exe (PID: 4540)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 6300)
Starts CMD.EXE for commands execution
- ArmouryCrateInstaller.exe (PID: 6192)
- QueryUWP.exe (PID: 6792)
Reads security settings of Internet Explorer
- ArmouryCrateInstaller.exe (PID: 6192)
- AsusROGLSLService.exe (PID: 7104)
- Armoury Crate Installer.exe (PID: 6452)
- ROGLSLoader.exe (PID: 5032)
Executes as Windows Service
- AsusROGLSLService.exe (PID: 7104)
The process drops C-runtime libraries
- AsusROGLSLService.exe (PID: 7104)
- AsZip.exe (PID: 628)
Process drops legitimate windows executable
- AsusROGLSLService.exe (PID: 7104)
- AsZip.exe (PID: 628)
INFO
Creates files in the program directory
- ArmouryCrateInstaller.exe (PID: 6192)
- AsusROGLSLService.exe (PID: 936)
- QueryUWP.exe (PID: 6792)
- Armoury Crate Installer.exe (PID: 7076)
- Armoury Crate Installer.exe (PID: 6452)
- AsZip.exe (PID: 5236)
- CheckTool.exe (PID: 836)
- AsusROGLSLService.exe (PID: 7104)
- AsZip.exe (PID: 628)
- ROGLSLoader.exe (PID: 5032)
- onePackageLoader.exe (PID: 6160)
- Armoury Crate Installer.exe (PID: 2072)
- onePackageLoader.exe (PID: 6968)
- onePackageLoader.exe (PID: 5096)
- CheckTool.exe (PID: 4468)
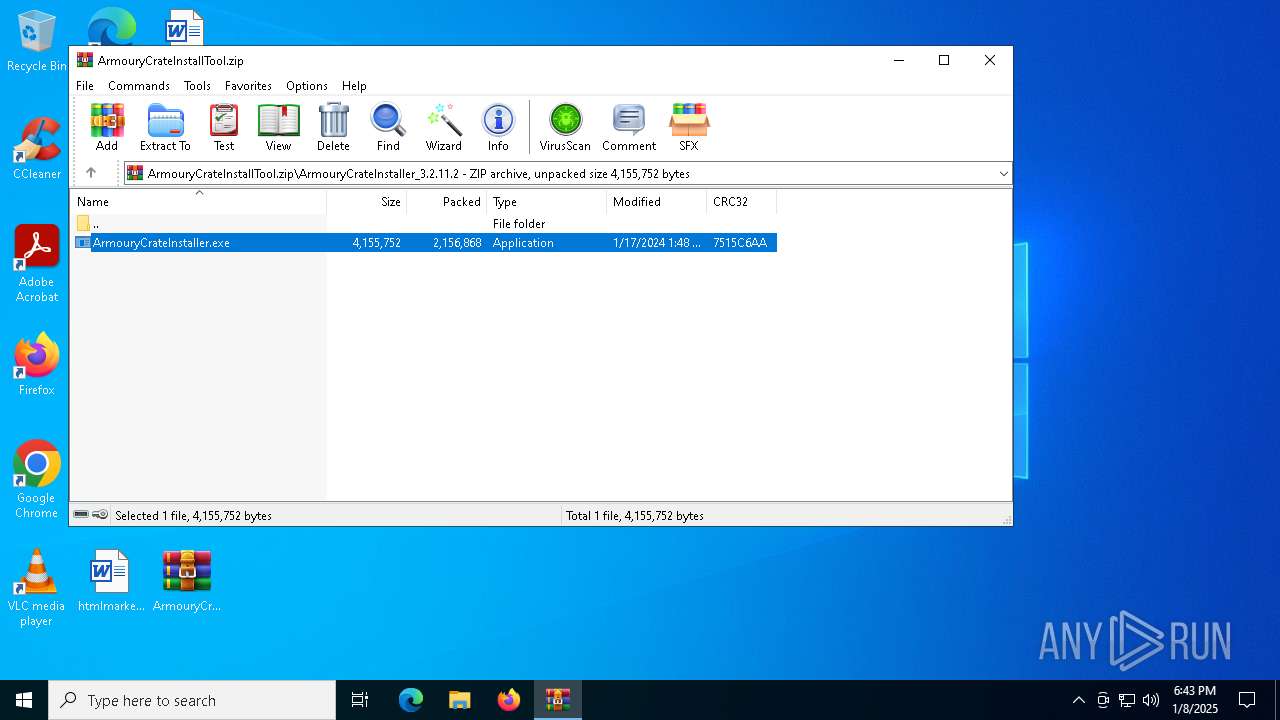
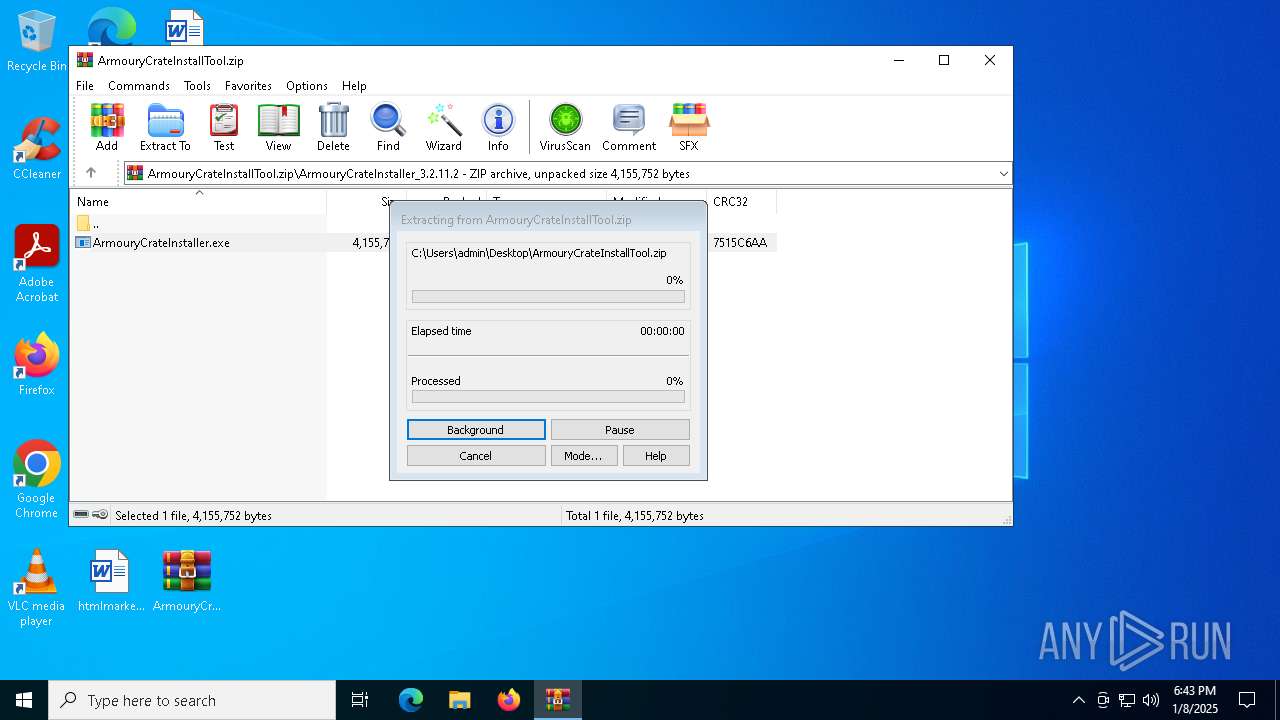
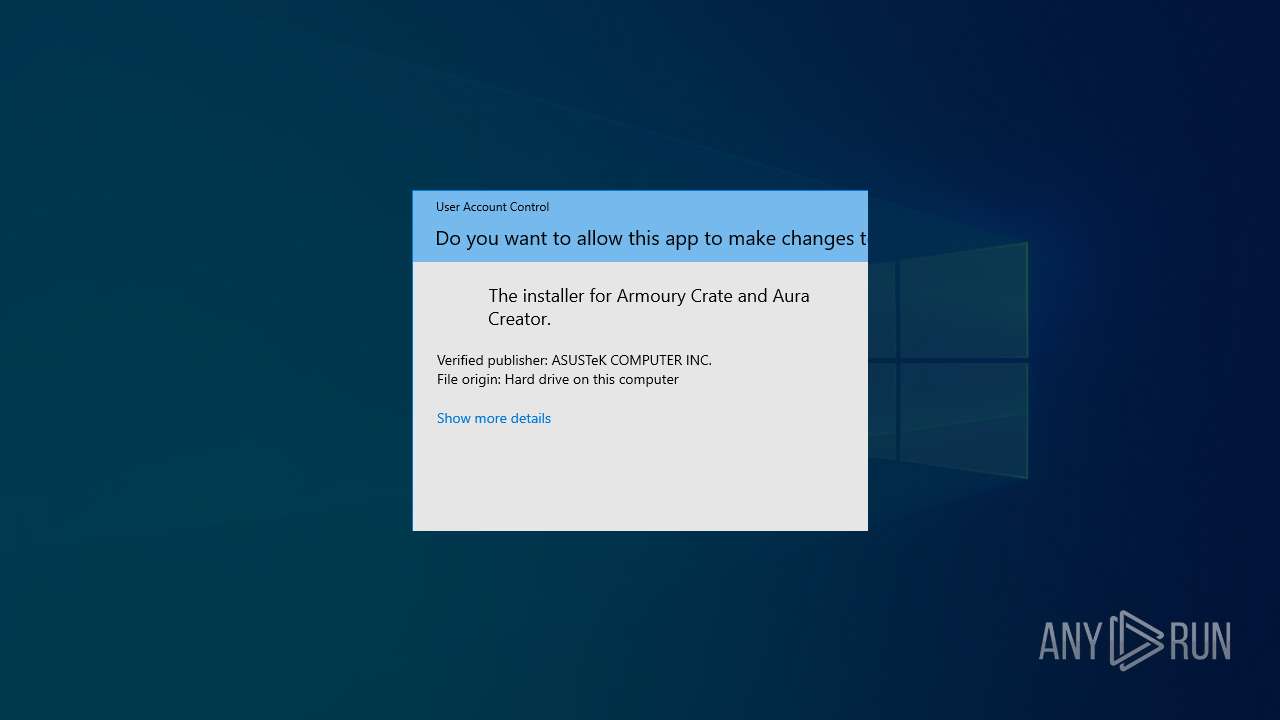
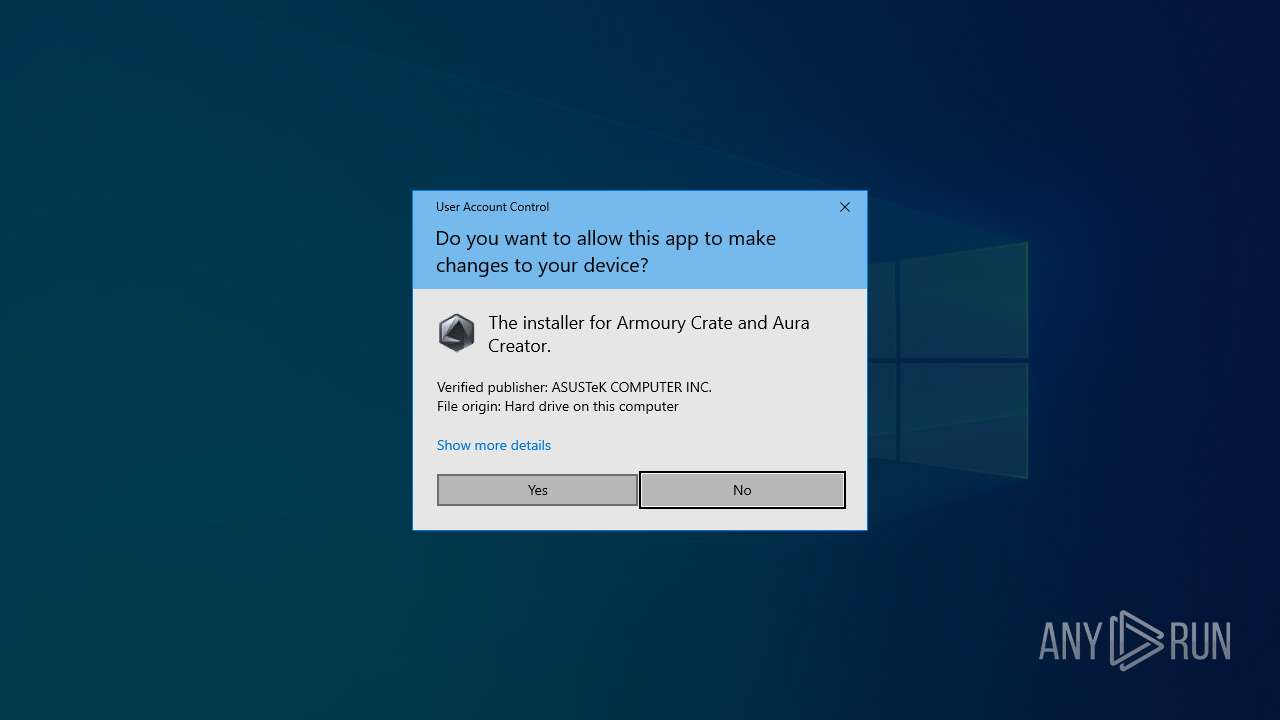
Manual execution by a user
- ArmouryCrateInstaller.exe (PID: 6192)
- ArmouryCrateInstaller.exe (PID: 6460)
The sample compiled with english language support
- ArmouryCrateInstaller.exe (PID: 6192)
- AsusROGLSLService.exe (PID: 7104)
- AsZip.exe (PID: 628)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6552)
The process uses the downloaded file
- WinRAR.exe (PID: 6552)
- ArmouryCrateInstaller.exe (PID: 6192)
- AsusROGLSLService.exe (PID: 7104)
- ROGLSLoader.exe (PID: 5032)
The sample compiled with chinese language support
- ArmouryCrateInstaller.exe (PID: 6192)
- AsusROGLSLService.exe (PID: 7104)
- AsZip.exe (PID: 628)
Checks supported languages
- ArmouryCrateInstaller.exe (PID: 6192)
- AsusROGLSLService.exe (PID: 936)
- AsusROGLSLService.exe (PID: 6960)
- Armoury Crate Installer.exe (PID: 7076)
- QueryUWP.exe (PID: 6792)
- AsusROGLSLService.exe (PID: 7104)
- Armoury Crate Installer.exe (PID: 6452)
- CheckTool.exe (PID: 836)
- AsZip.exe (PID: 5236)
- Armoury Crate Installer.exe (PID: 2072)
- onePackageLoader.exe (PID: 6160)
- onePackageLoader.exe (PID: 6968)
- onePackageLoader.exe (PID: 1864)
- CheckTool.exe (PID: 6448)
- onePackageLoader.exe (PID: 5096)
- CheckTool.exe (PID: 4468)
Reads the computer name
- ArmouryCrateInstaller.exe (PID: 6192)
- AsusROGLSLService.exe (PID: 936)
- AsusROGLSLService.exe (PID: 6960)
- Armoury Crate Installer.exe (PID: 7076)
- AsusROGLSLService.exe (PID: 7104)
- Armoury Crate Installer.exe (PID: 6452)
- ROGLSLoader.exe (PID: 5032)
- Armoury Crate Installer.exe (PID: 2072)
- onePackageLoader.exe (PID: 6968)
- onePackageLoader.exe (PID: 1864)
Process checks computer location settings
- ArmouryCrateInstaller.exe (PID: 6192)
Sends debugging messages
- AsusROGLSLService.exe (PID: 7104)
- ROGLSLoader.exe (PID: 5032)
Reads the machine GUID from the registry
- Armoury Crate Installer.exe (PID: 7076)
- CheckTool.exe (PID: 836)
- Armoury Crate Installer.exe (PID: 6452)
- Armoury Crate Installer.exe (PID: 2072)
- onePackageLoader.exe (PID: 6968)
- onePackageLoader.exe (PID: 1864)
- CheckTool.exe (PID: 6448)
- onePackageLoader.exe (PID: 5096)
- CheckTool.exe (PID: 4468)
Disables trace logs
- CheckTool.exe (PID: 836)
Reads the software policy settings
- AsusROGLSLService.exe (PID: 7104)
- CheckTool.exe (PID: 6448)
- CheckTool.exe (PID: 4468)
Reads Environment values
- CheckTool.exe (PID: 836)
- onePackageLoader.exe (PID: 6160)
- onePackageLoader.exe (PID: 6968)
- ROGLSLoader.exe (PID: 5032)
- onePackageLoader.exe (PID: 1864)
- onePackageLoader.exe (PID: 5096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:01:17 22:20:12 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | ArmouryCrateInstaller_3.2.11.2/ |
Total processes
166
Monitored processes
38
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CheckTool.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | "C:\Program Files (x86)\ASUS\AsusROGLSLService\AsZip.exe" "C:\Program Files (x86)\ASUS\ROGLSLoader.zip" | C:\Program Files (x86)\ASUS\AsusROGLSLService\AsZip.exe | AsusROGLSLService.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Version: 1.0.0.2 Modules
| |||||||||||||||
| 836 | "C:\Program Files (x86)\ASUS\AsusROGLSLService\CheckTool.exe" --is-china-network | C:\Program Files (x86)\ASUS\AsusROGLSLService\CheckTool.exe | AsusROGLSLService.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: CheckTool Exit code: 0 Version: 1.0.2.0 Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\ASUS\AsusROGLSLService\AsusROGLSLService.exe" -remove | C:\Program Files (x86)\ASUS\AsusROGLSLService\AsusROGLSLService.exe | — | ArmouryCrateInstaller.exe | |||||||||||
User: admin Company: ASUS Integrity Level: HIGH Exit code: 0 Version: 2.3.11.0 Modules
| |||||||||||||||
| 1864 | "C:\Program Files (x86)\ASUS\ROGLSLoader\onePackageLoader.exe" -install -product ArmouryCrate | C:\Program Files (x86)\ASUS\ROGLSLoader\onePackageLoader.exe | — | ROGLSLoader.exe | |||||||||||
User: admin Company: ASUSTek Computer Inc. Integrity Level: MEDIUM Description: onePackageLoader Exit code: 409 Version: 1.0.7.0 Modules
| |||||||||||||||
| 2072 | "C:\Program Files (x86)\ASUS\ROGLSLoader\Armoury Crate Installer.exe" -asusdownloadbar -bar_report 0 -interruptSatus interrupt_0 -barstyle armourycrate -barProduct "Armoury Crate" -progressbarstatus 2 | C:\Program Files (x86)\ASUS\ROGLSLoader\Armoury Crate Installer.exe | — | ROGLSLoader.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Armoury Crate Installer Version: 2.3.11.2 Modules
| |||||||||||||||
| 2972 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AsusROGLSLService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AsZip.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3584 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AsusROGLSLService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AsZip.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
30 404
Read events
30 361
Write events
41
Delete events
2
Modification events
| (PID) Process: | (6552) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6552) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6552) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6552) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\ArmouryCrateInstallTool.zip | |||
| (PID) Process: | (6552) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6552) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6552) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6552) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6552) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6552) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
25
Suspicious files
12
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6552 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6552.11462\ArmouryCrateInstaller_3.2.11.2\ArmouryCrateInstaller.exe | executable | |
MD5:350ADD77EC579BBBDE55F5CD84E5104F | SHA256:4D05106479102D0AC3B774FB5287DEE09A785CB27F9C64884D46631E2F52337F | |||
| 4244 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:6E9BD74DB919BA0FD764BEB17074C4FE | SHA256:873E7C548E53AA285E91B349B8DD7DE53C525D60D1005523DE93A3BB88A1B0F7 | |||
| 6192 | ArmouryCrateInstaller.exe | C:\ProgramData\ASUS\ALL\ACLoader\ACSE.ini | text | |
MD5:D79AAB1FE0A7F19EF95F2FD496C1E856 | SHA256:A6582FDCBF0787373491FECB74B4B7368DD796F3533F9A3A1FA181900B0699C9 | |||
| 936 | AsusROGLSLService.exe | C:\ProgramData\ASUS\ALL\ACLoader\ArmouryCrateInstaller.log | text | |
MD5:CE86DD12EB22F56A718ED9AF0BF43CD7 | SHA256:BEEC2C37809F453154177554A7C8113B0FC6B44A43D7736A42954891A44F4B24 | |||
| 6192 | ArmouryCrateInstaller.exe | C:\Program Files (x86)\ASUS\AsusROGLSLService\CheckTool.exe | executable | |
MD5:12AB05AE37EF47DA353EFF14D5A81382 | SHA256:87D2FF260502B5C954C1BB4B867264BD5343451260151070A8B56225A8B4986E | |||
| 5032 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_r2ocumae.qgu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5032 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uzkab3yj.0ye.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4544 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tje22clj.fdd.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6192 | ArmouryCrateInstaller.exe | C:\Program Files (x86)\ASUS\AsusROGLSLService\Newtonsoft.Json.dll | executable | |
MD5:081D9558BBB7ADCE142DA153B2D5577A | SHA256:B624949DF8B0E3A6153FDFB730A7C6F4990B6592EE0D922E1788433D276610F3 | |||
| 4544 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_24p2juie.mg5.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
42
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3700 | svchost.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3700 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6776 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6336 | SIHClient.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6336 | SIHClient.exe | GET | 200 | 184.30.230.103:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3700 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3700 | svchost.exe | 184.30.230.103:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.227.221:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
1176 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
AsusROGLSLService.exe | Failed to get baseboard manufacturer via WMI, get via registry. |
ROGLSLoader.exe | Failed to get baseboard manufacturer via WMI, get via registry. |