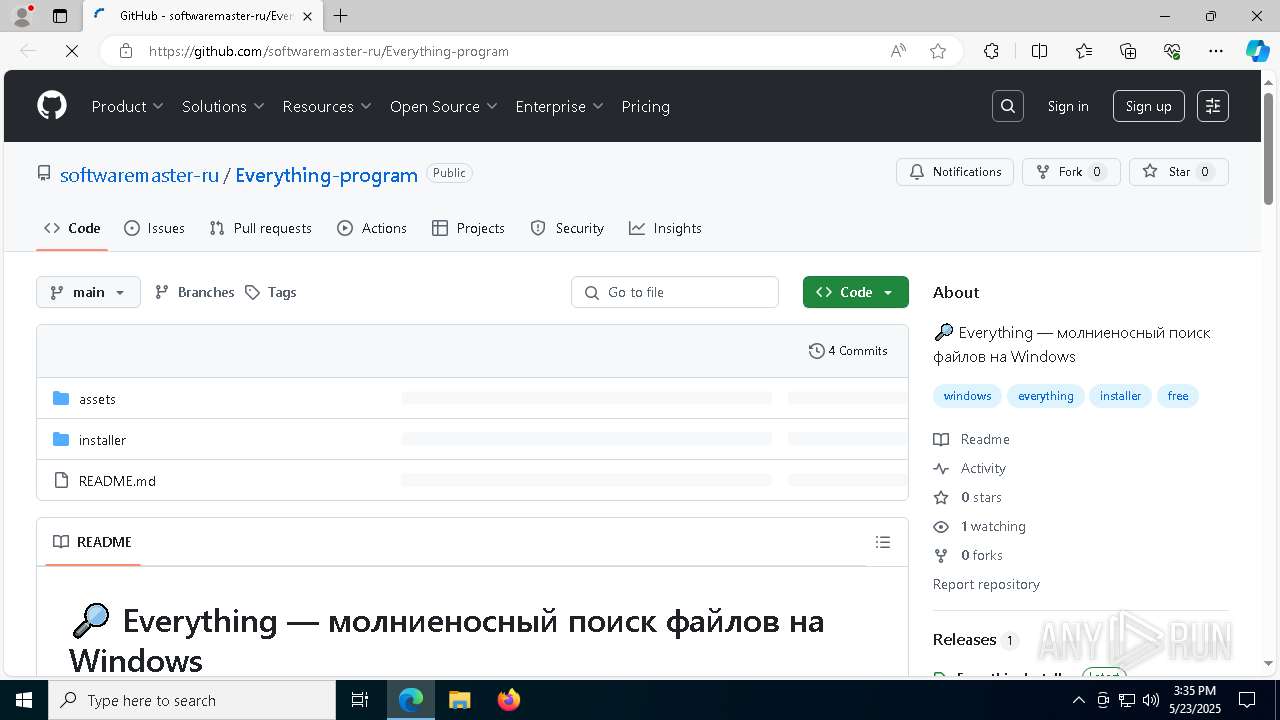
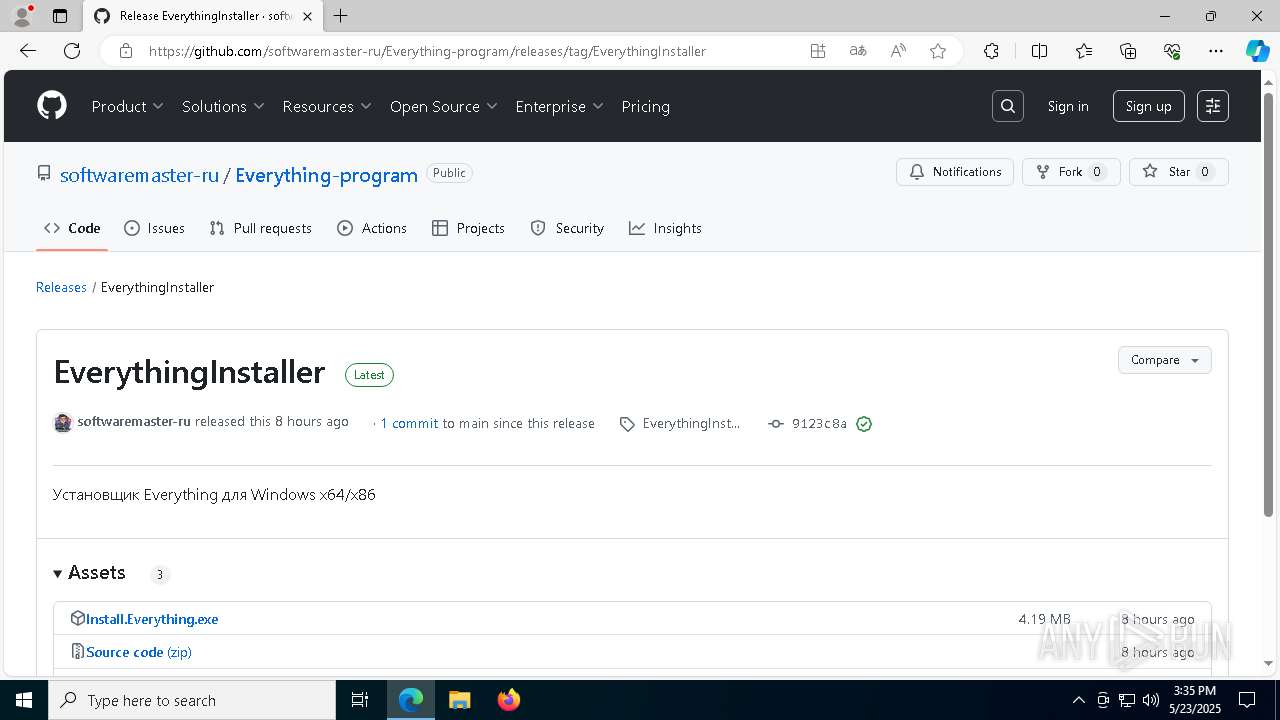
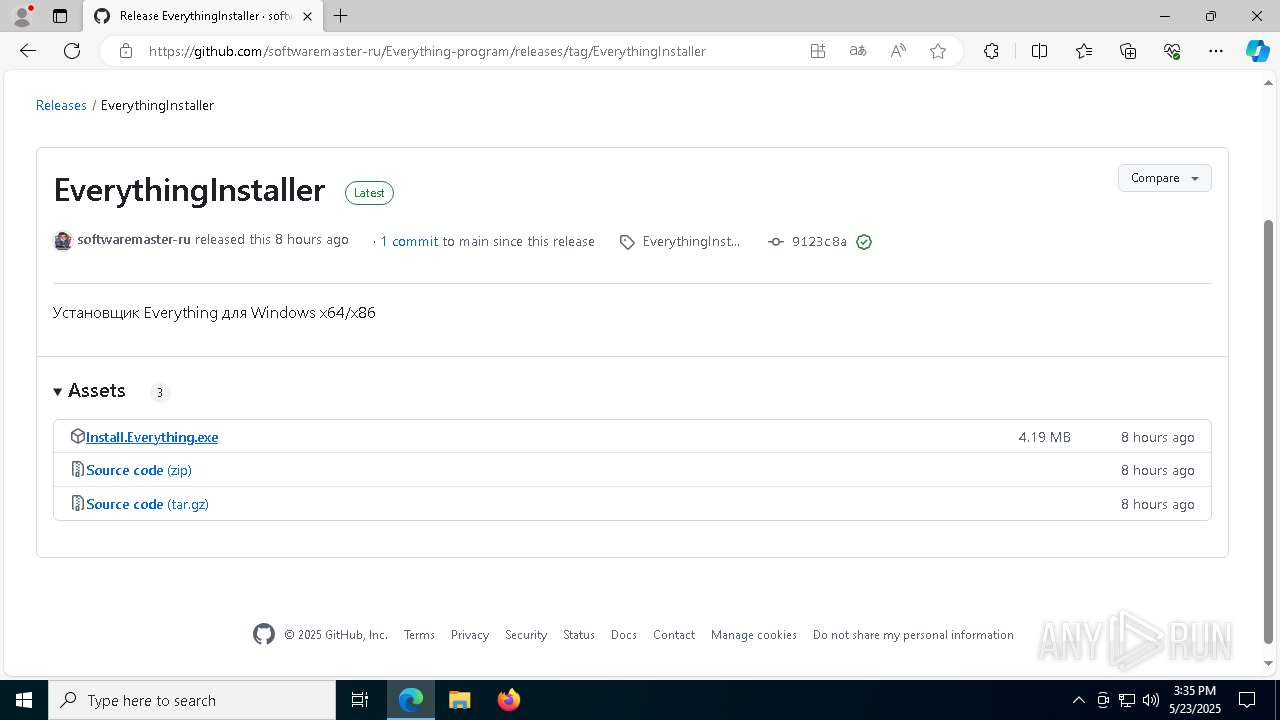
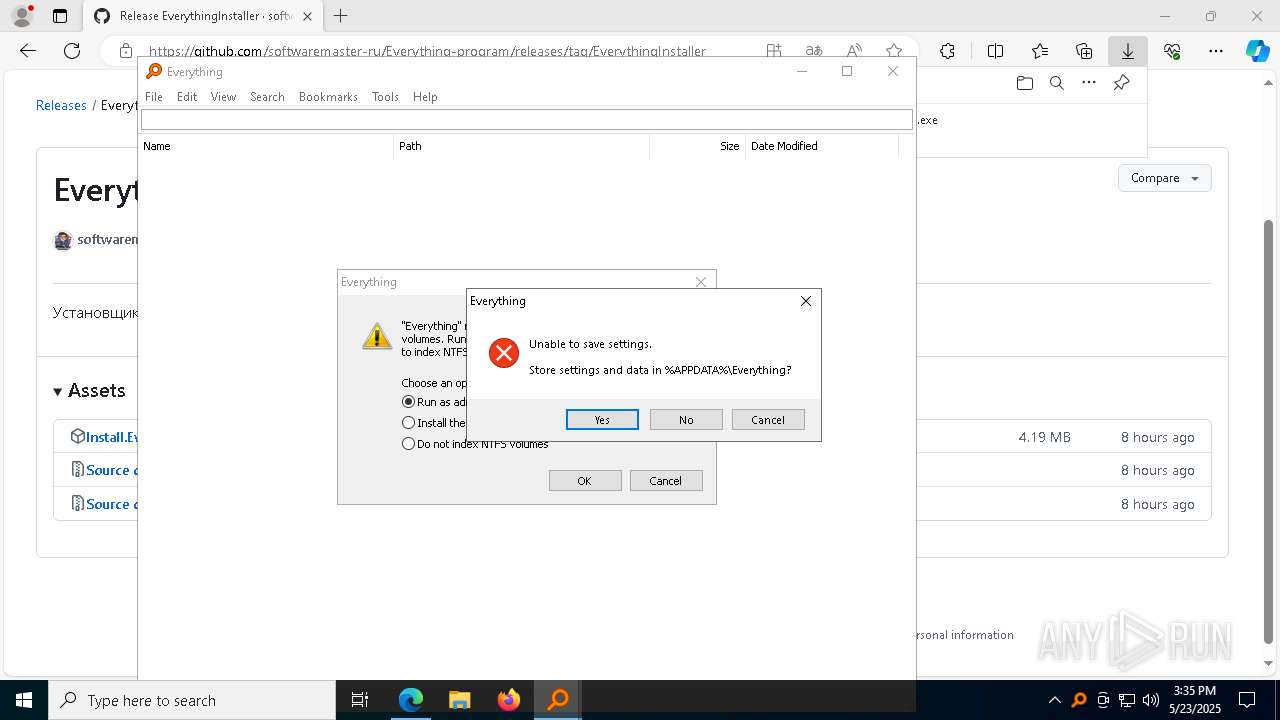
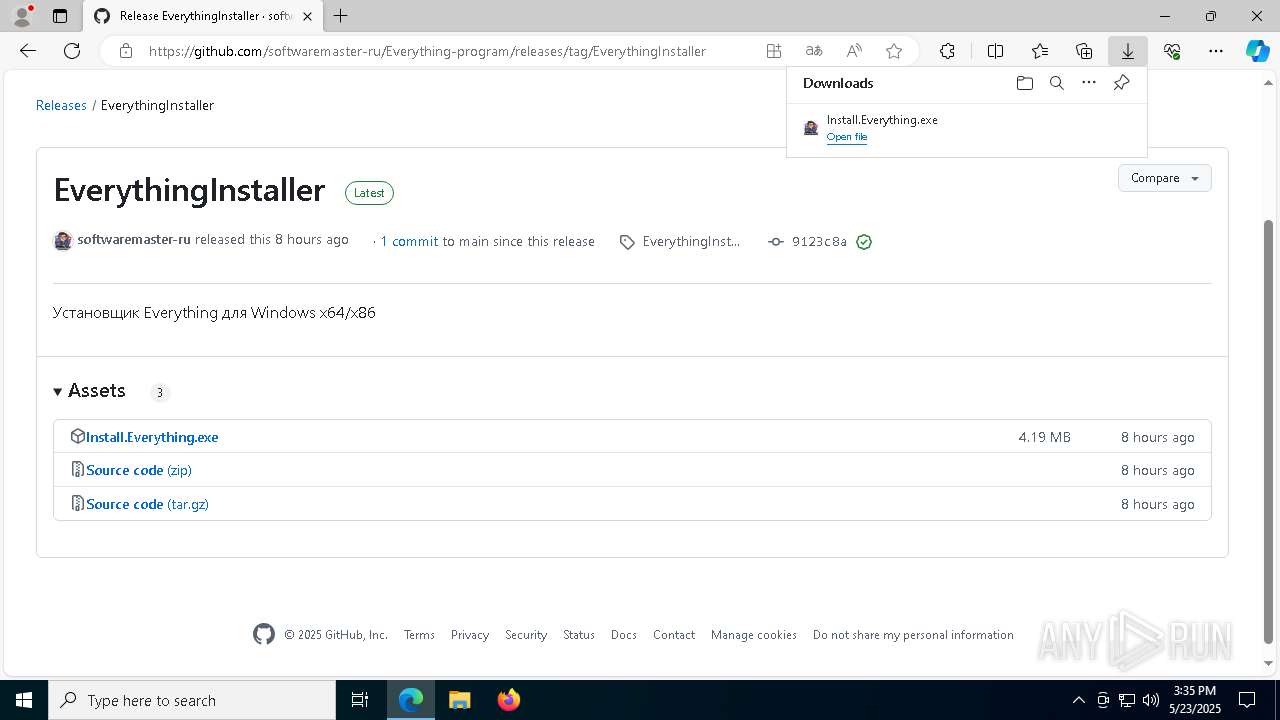
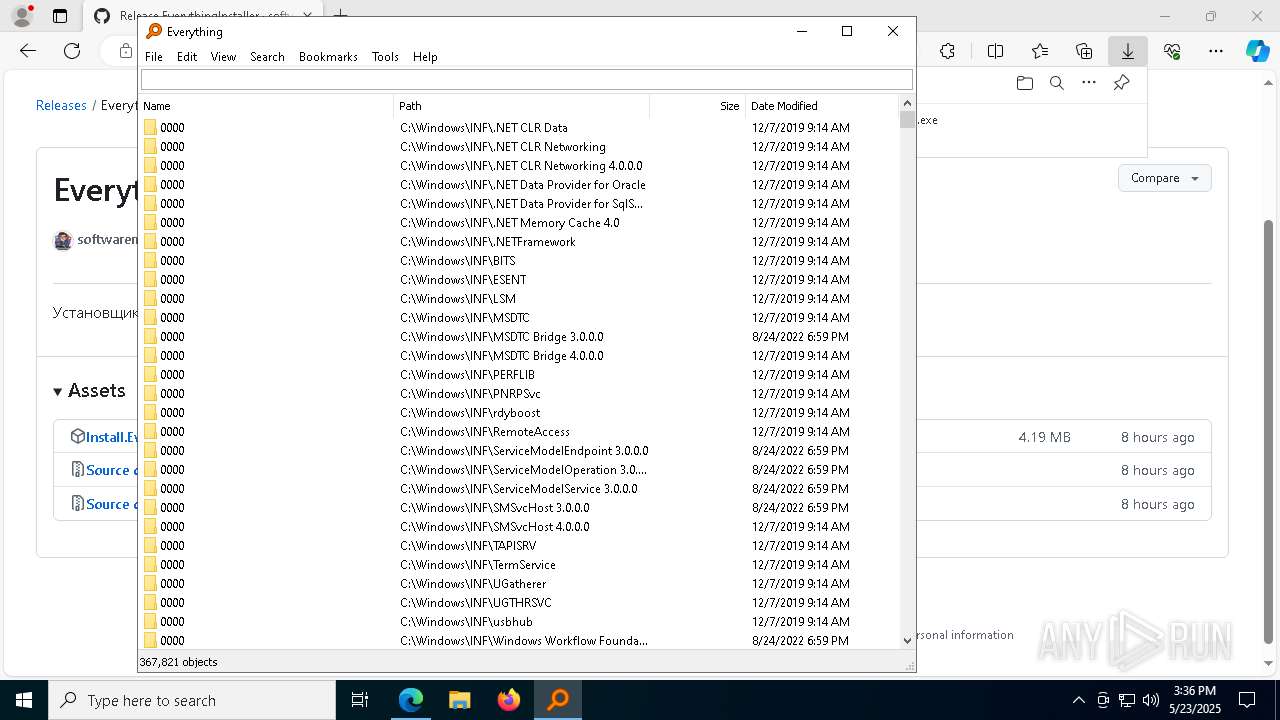
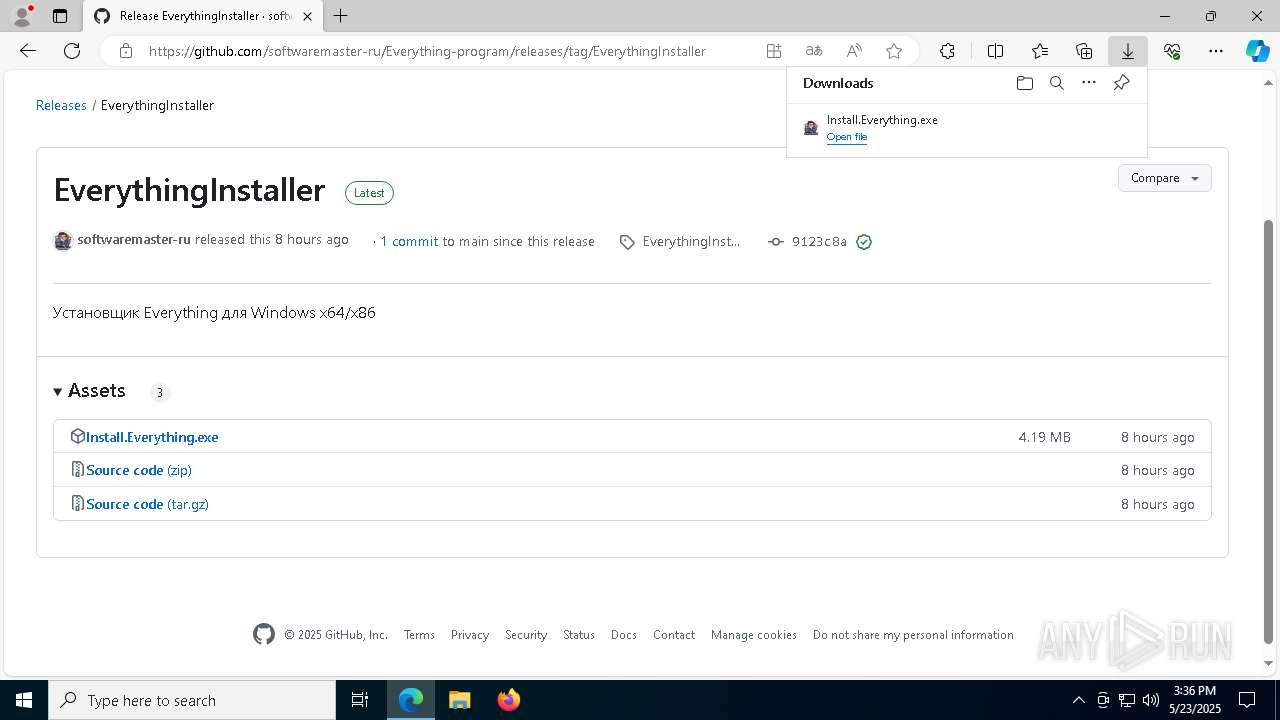
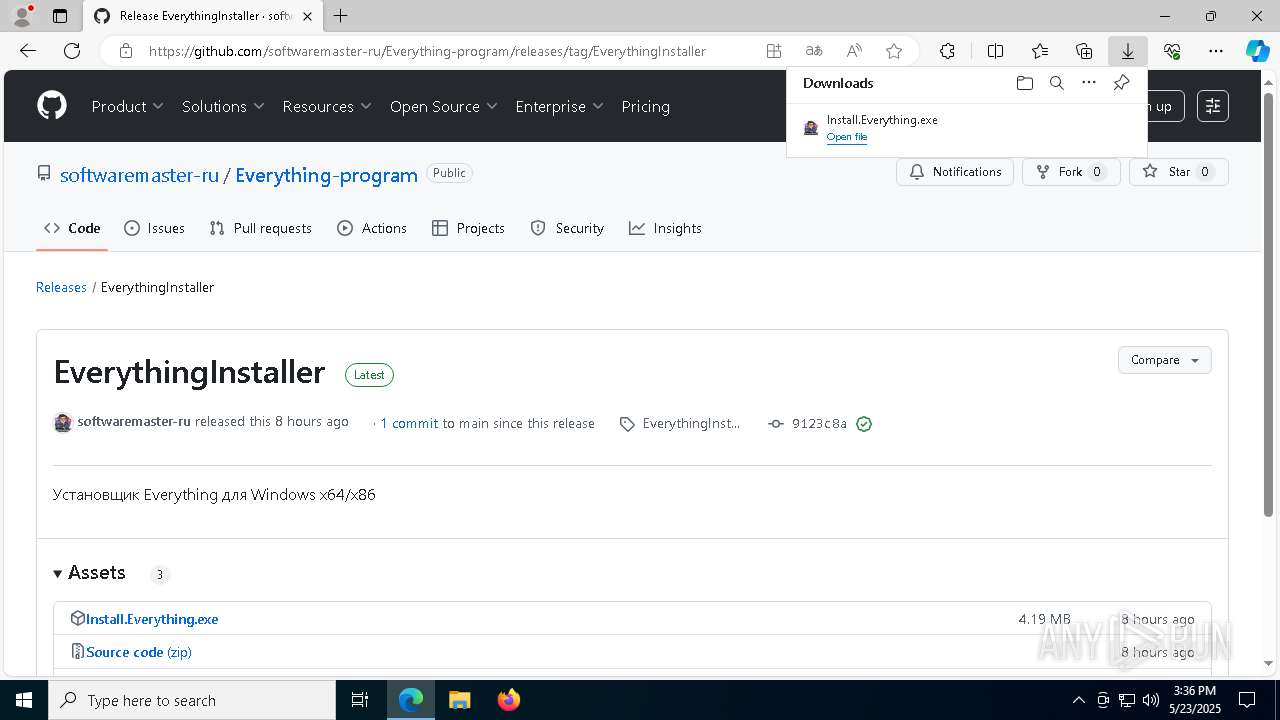
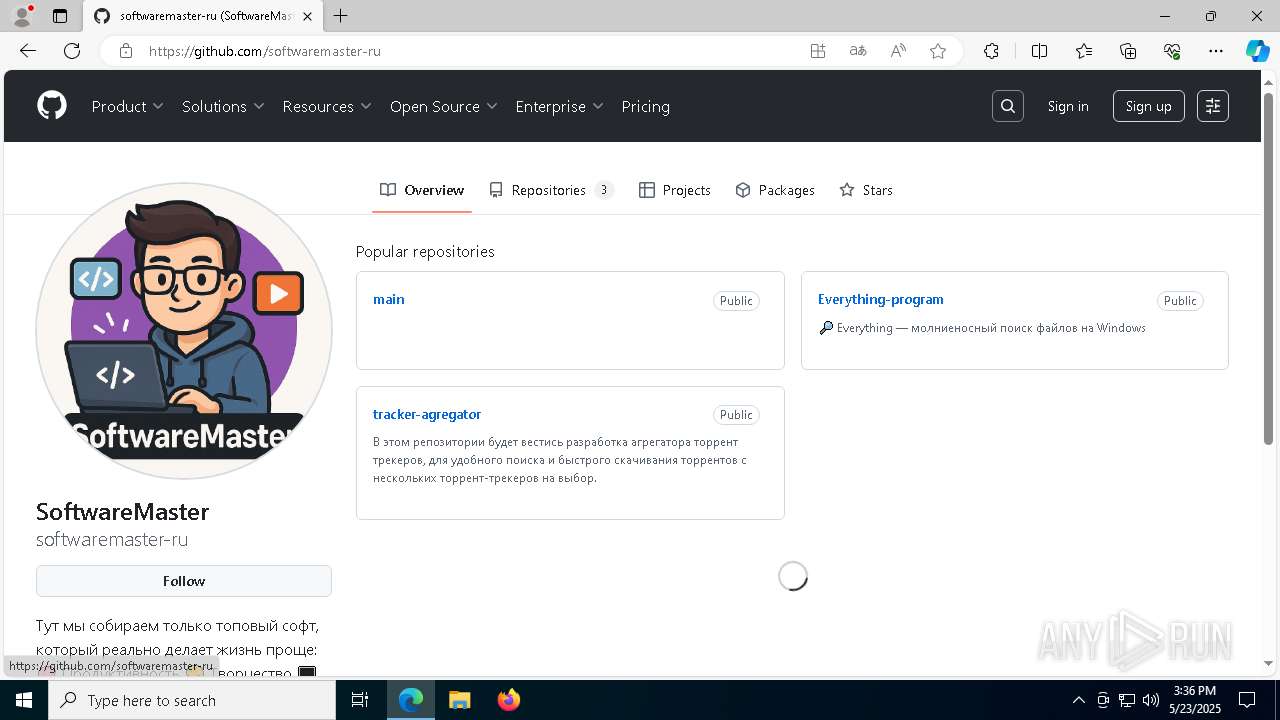
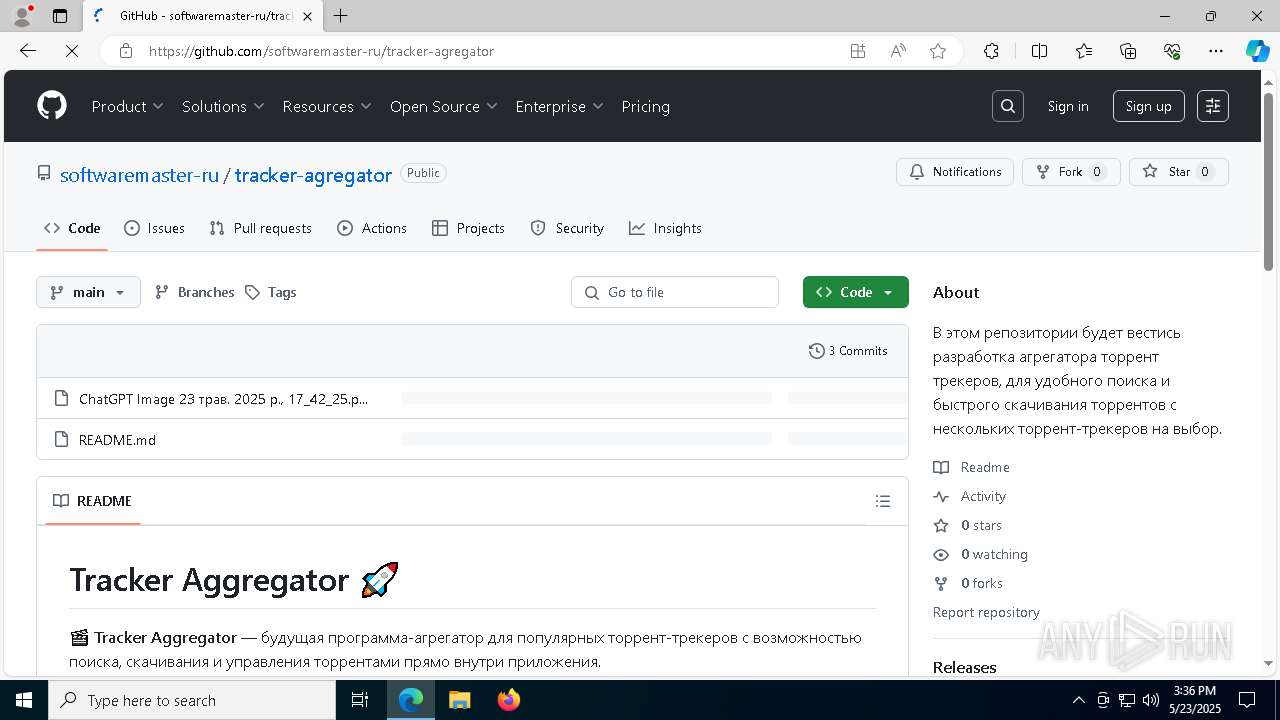
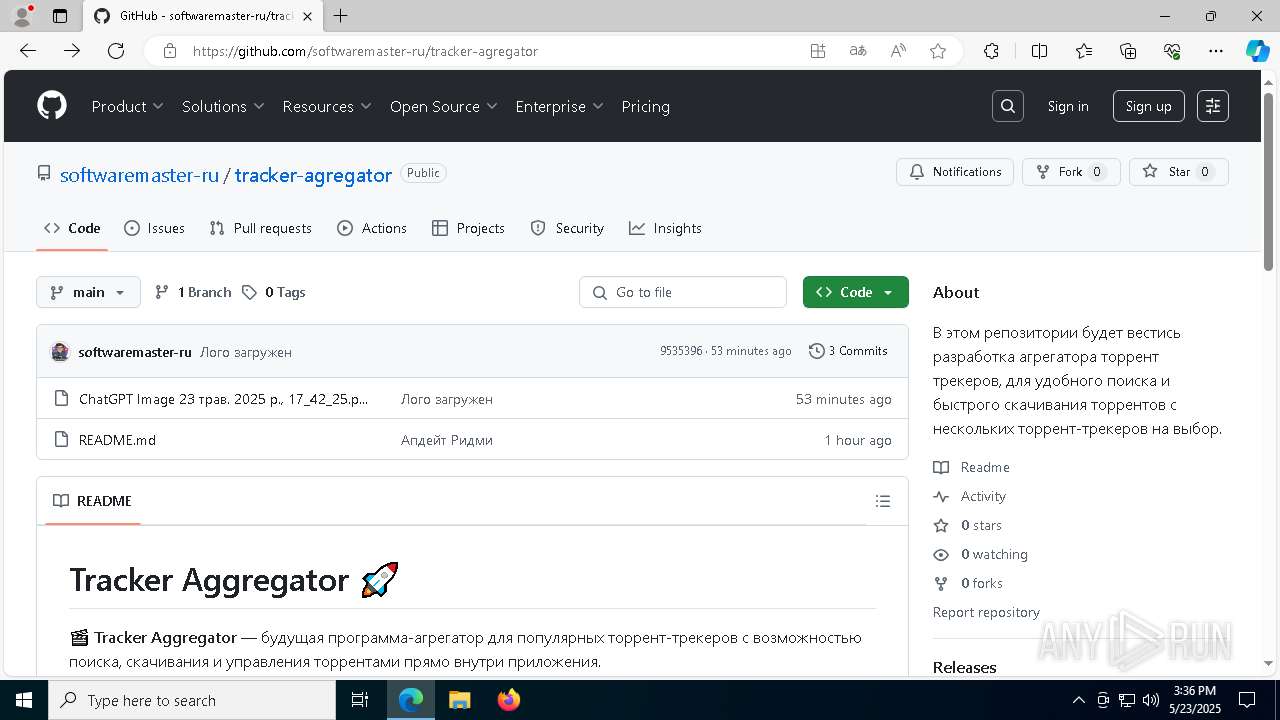
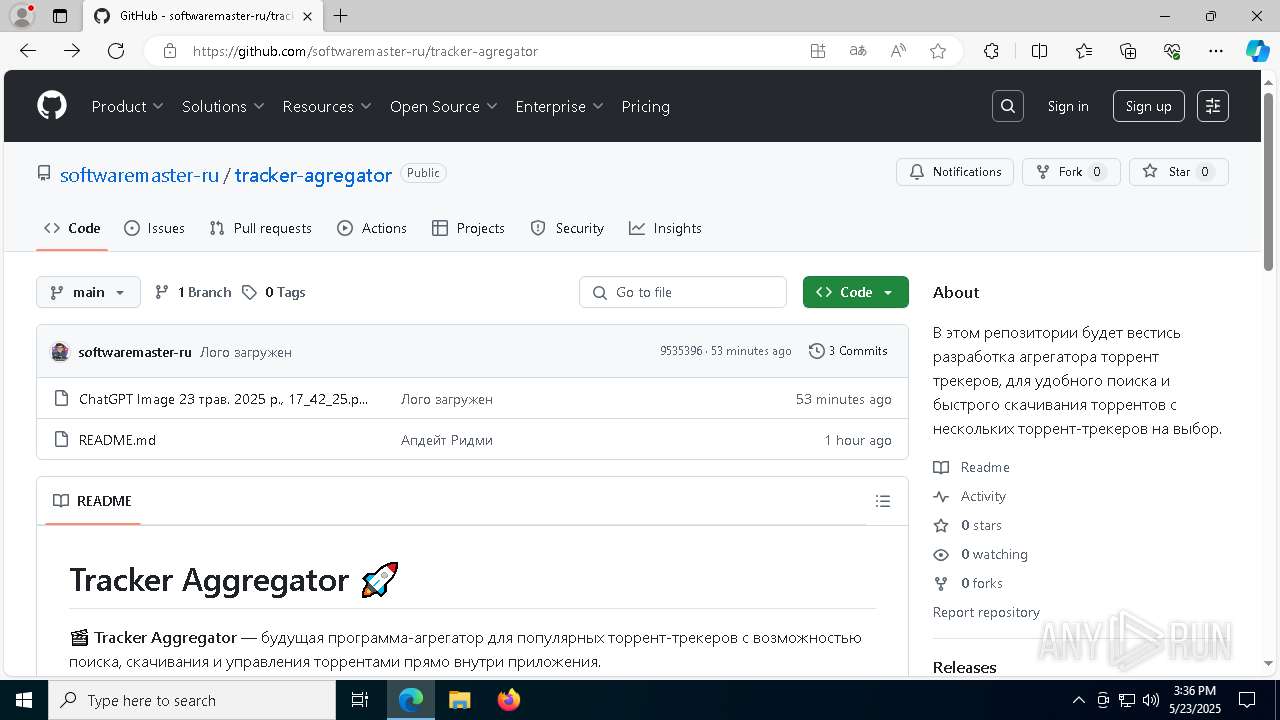
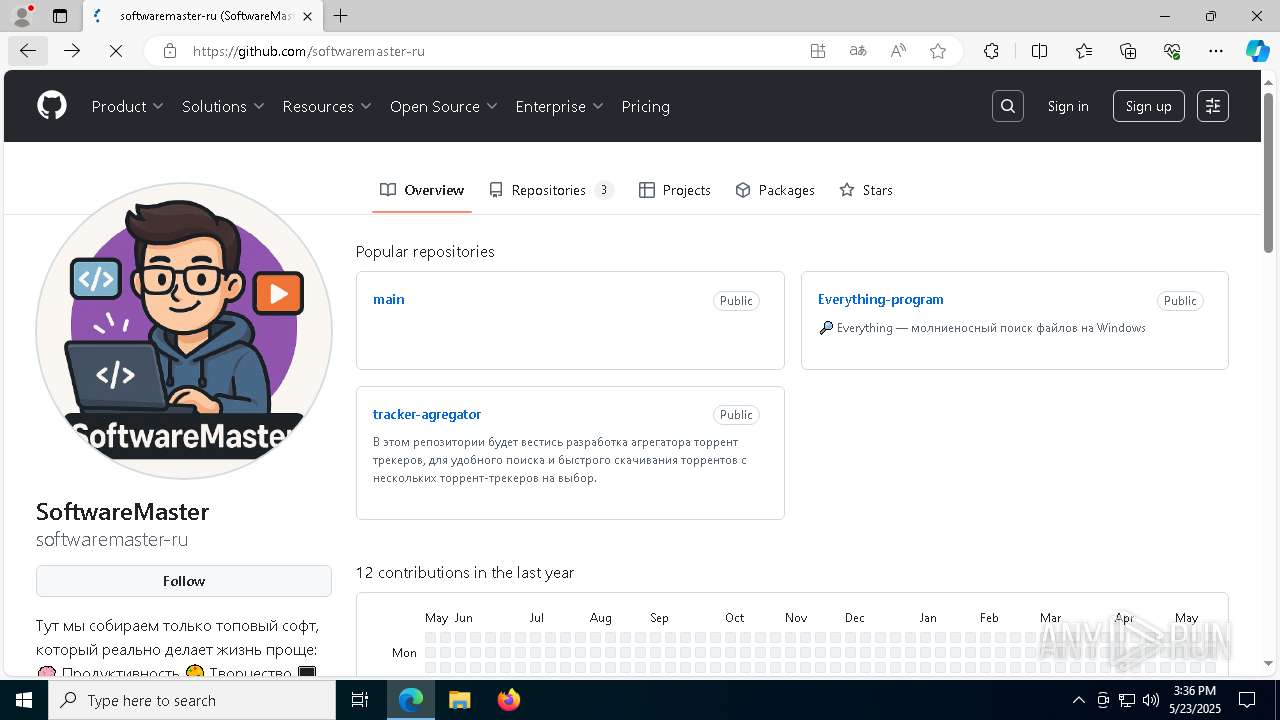
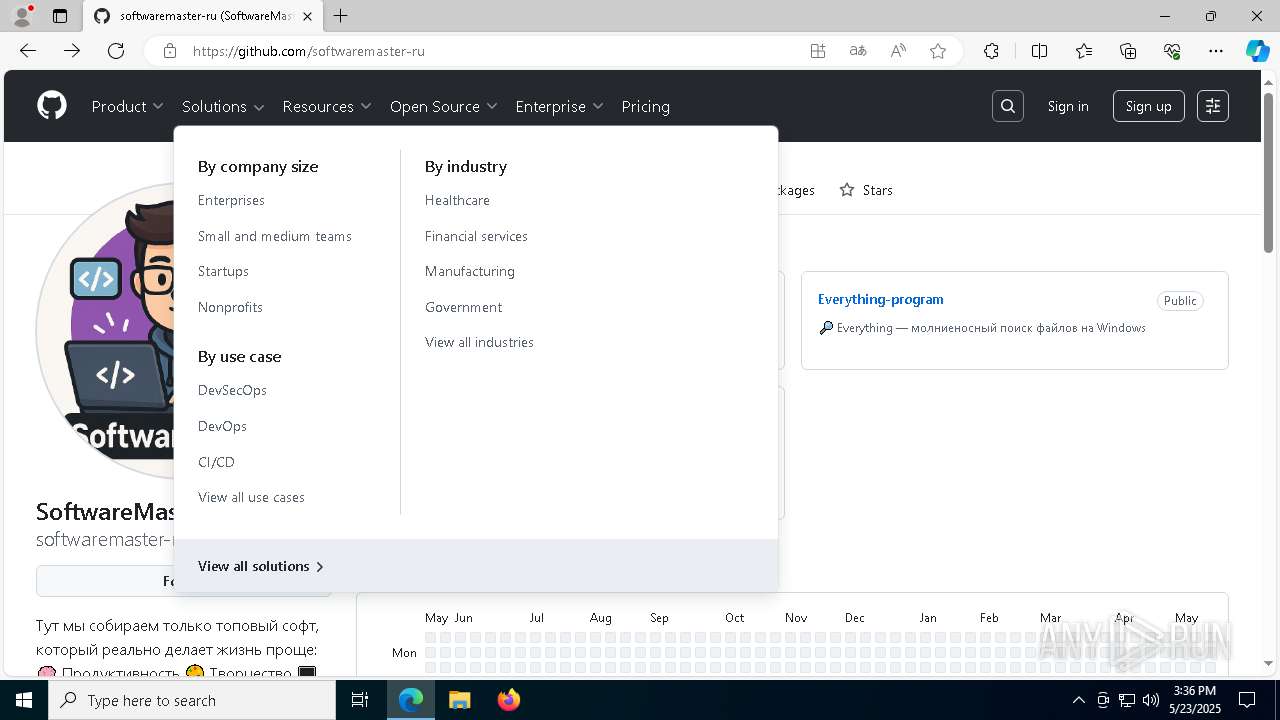
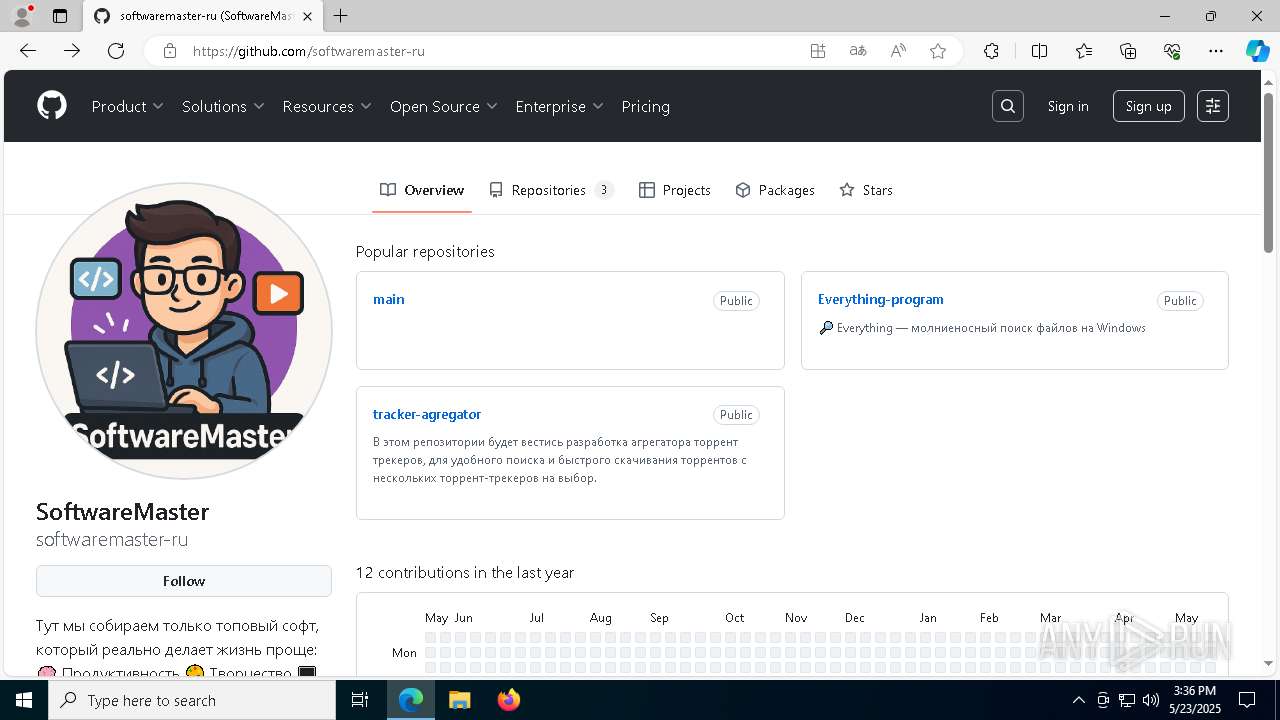
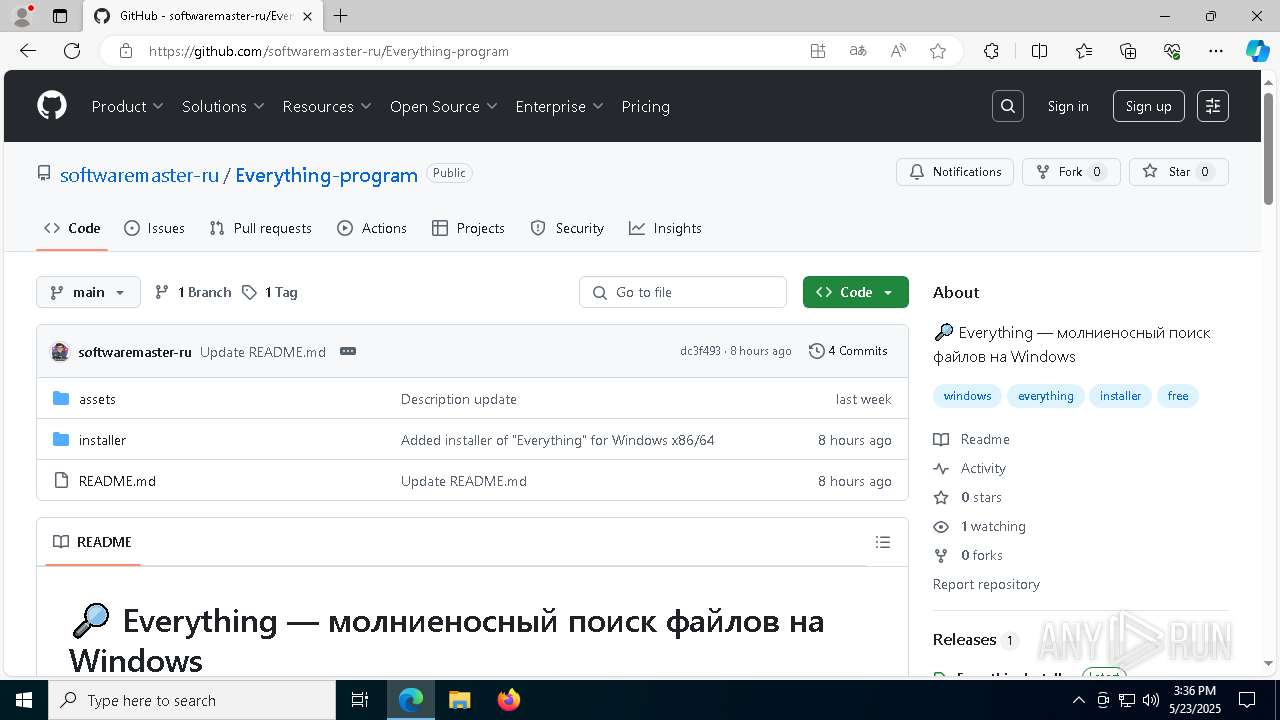
| URL: | https://github.com/softwaremaster-ru/Everything-program |
| Full analysis: | https://app.any.run/tasks/09caae17-1550-4041-95bc-bc3e1fae6b06 |
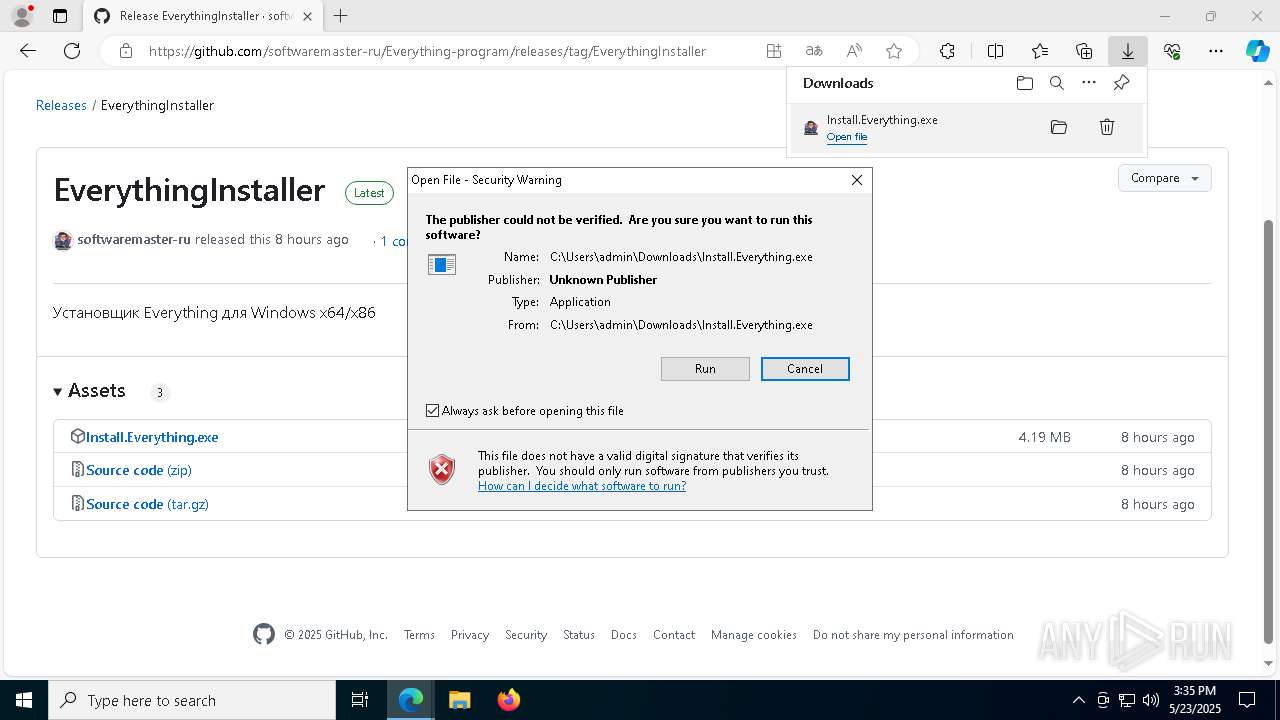
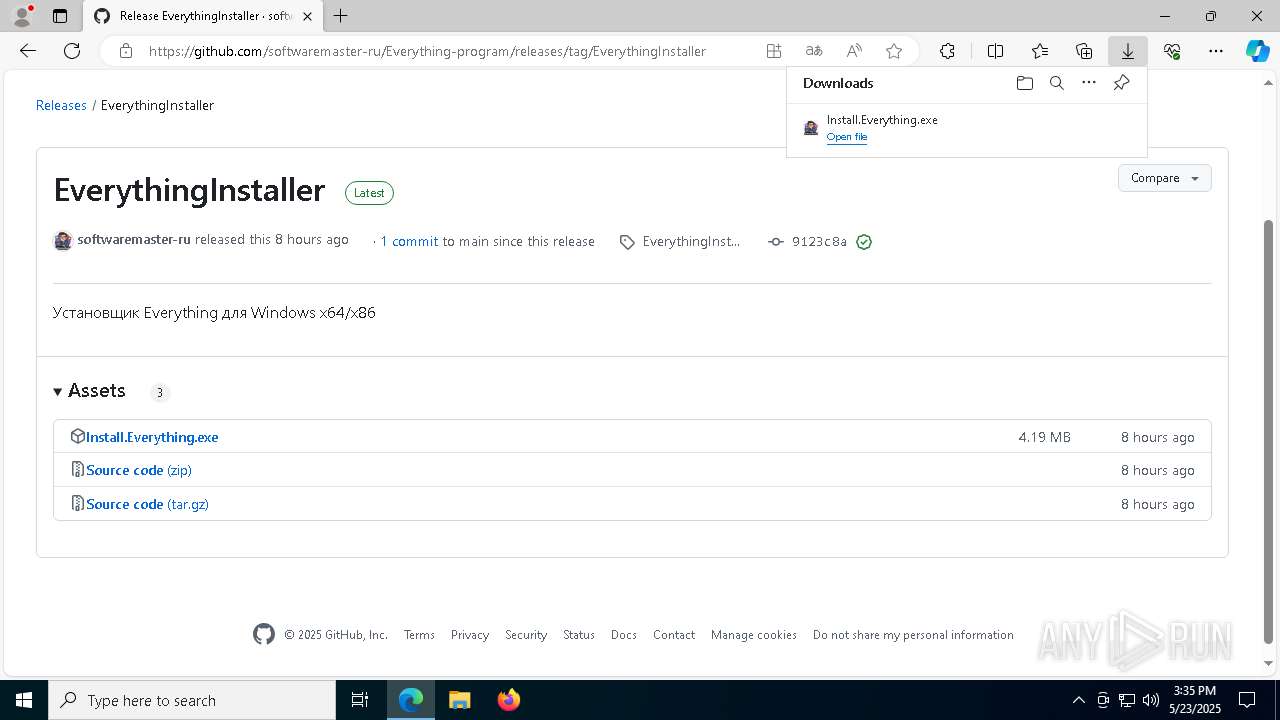
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2025, 15:34:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 56623EF2C4442345497699EC37911DF3 |
| SHA1: | 08F3CED4103A93D50F4D78C9E6472B8E7254C565 |
| SHA256: | E35C5A4992D35151CAED7ED198475A5E10554AD7D7B04E29AC8B801D932C66DF |
| SSDEEP: | 3:N8tEdmKcHrPRsoUEIn:2uw1HrpsJn |
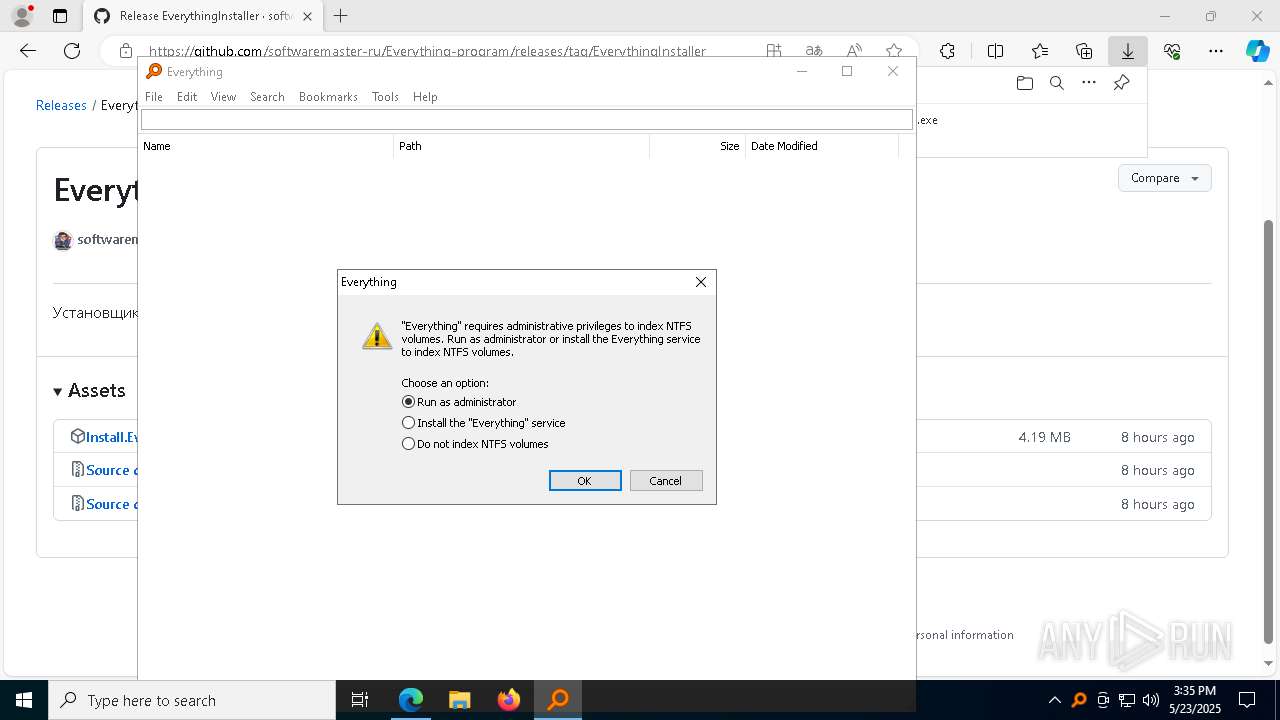
MALICIOUS
GENERIC has been found (auto)
- Install.Everything.tmp (PID: 864)
Changes the autorun value in the registry
- Install.Everything.tmp (PID: 864)
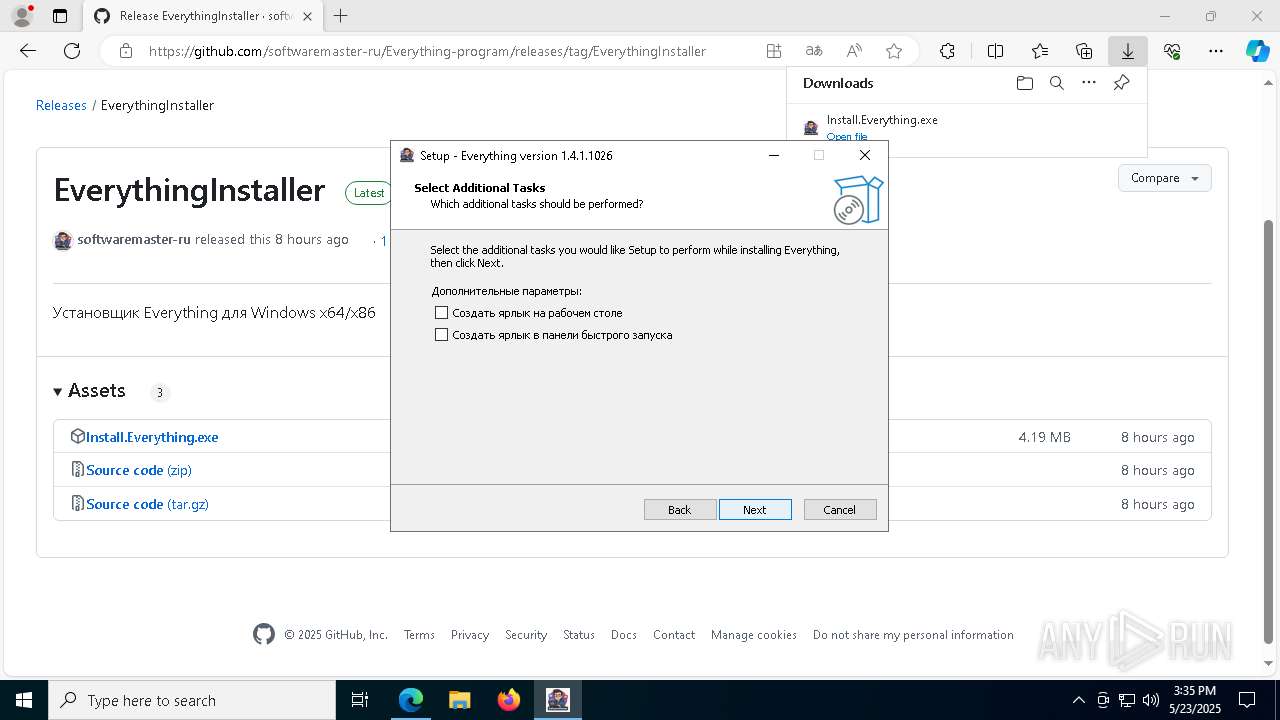
Changes powershell execution policy (Bypass)
- Install.Everything.tmp (PID: 864)
Bypass execution policy to execute commands
- powershell.exe (PID: 668)
SUSPICIOUS
Executable content was dropped or overwritten
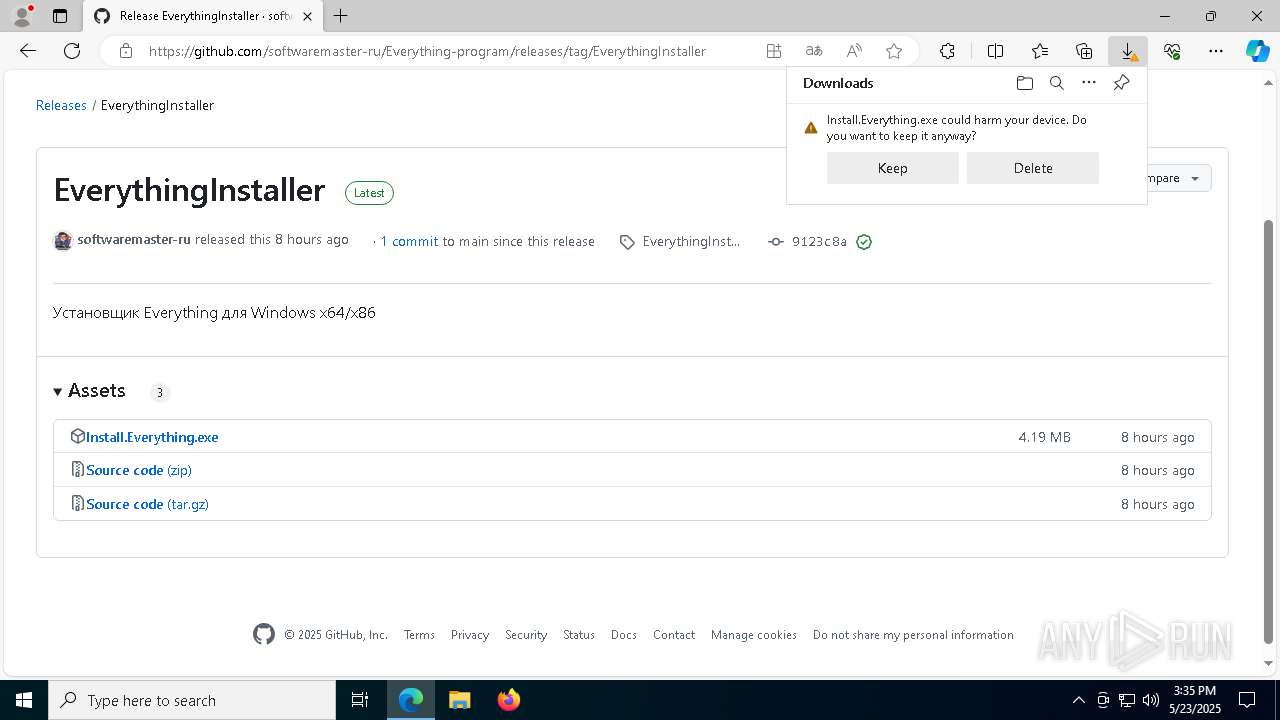
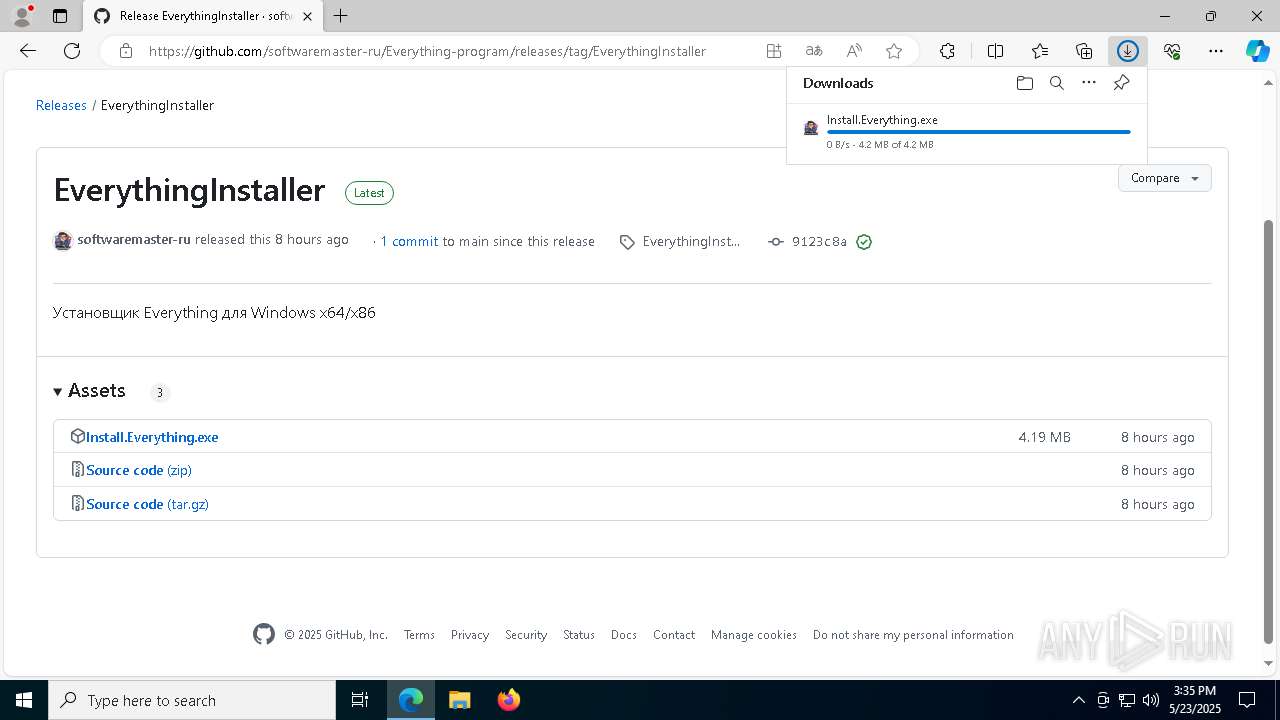
- Install.Everything.exe (PID: 1228)
- Install.Everything.exe (PID: 7952)
- Install.Everything.tmp (PID: 864)
- powershell.exe (PID: 668)
Reads security settings of Internet Explorer
- Install.Everything.tmp (PID: 3888)
- Everything.exe (PID: 1020)
- Everything.exe (PID: 2692)
Reads the Windows owner or organization settings
- Install.Everything.tmp (PID: 864)
The process executes Powershell scripts
- Install.Everything.tmp (PID: 864)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 668)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 668)
Application launched itself
- Everything.exe (PID: 1020)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 668)
Starts POWERSHELL.EXE for commands execution
- Install.Everything.tmp (PID: 864)
INFO
Checks supported languages
- identity_helper.exe (PID: 5504)
- Install.Everything.exe (PID: 1228)
- Install.Everything.tmp (PID: 3888)
- Install.Everything.exe (PID: 7952)
- Install.Everything.tmp (PID: 864)
- Everything.exe (PID: 7944)
- Everything.exe (PID: 1020)
- Everything.exe (PID: 8188)
- Everything.exe (PID: 2692)
Reads the computer name
- identity_helper.exe (PID: 5504)
- Install.Everything.tmp (PID: 3888)
- Install.Everything.exe (PID: 7952)
- Install.Everything.tmp (PID: 864)
- Everything.exe (PID: 1020)
- Everything.exe (PID: 7944)
- Everything.exe (PID: 8188)
- Everything.exe (PID: 2692)
Reads Environment values
- identity_helper.exe (PID: 5504)
Application launched itself
- msedge.exe (PID: 896)
Executable content was dropped or overwritten
- msedge.exe (PID: 896)
- msedge.exe (PID: 7340)
Create files in a temporary directory
- Install.Everything.exe (PID: 1228)
- Install.Everything.exe (PID: 7952)
- Install.Everything.tmp (PID: 864)
Process checks computer location settings
- Install.Everything.tmp (PID: 3888)
- Everything.exe (PID: 1020)
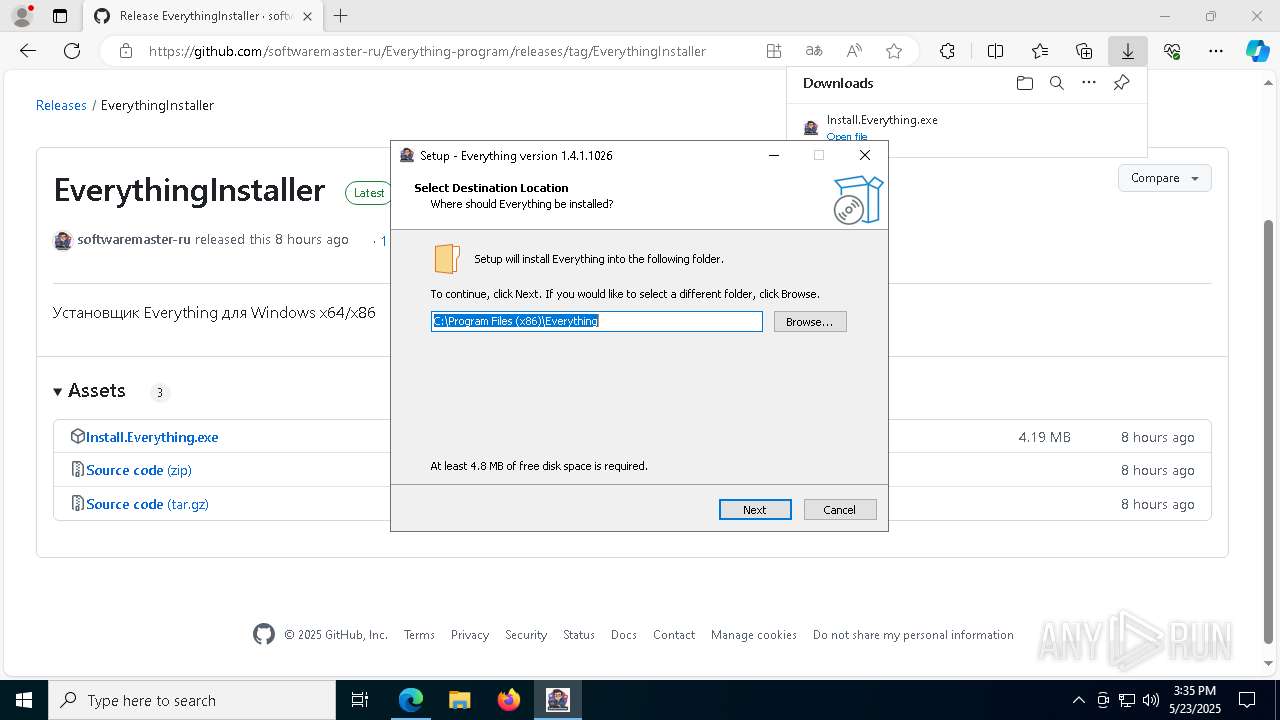
Compiled with Borland Delphi (YARA)
- Install.Everything.tmp (PID: 3888)
- Install.Everything.exe (PID: 1228)
Detects InnoSetup installer (YARA)
- Install.Everything.tmp (PID: 3888)
- Install.Everything.exe (PID: 1228)
Creates files in the program directory
- Install.Everything.tmp (PID: 864)
- Everything.exe (PID: 7944)
- Everything.exe (PID: 8188)
The sample compiled with english language support
- Install.Everything.tmp (PID: 864)
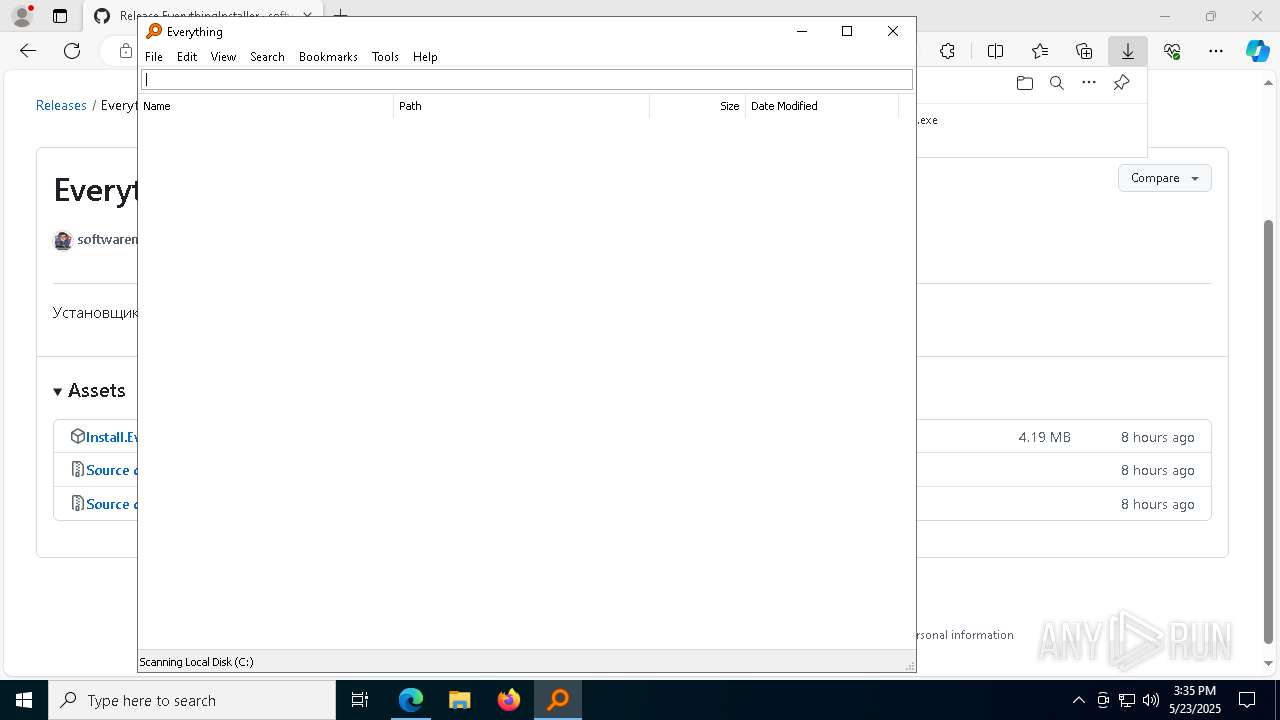
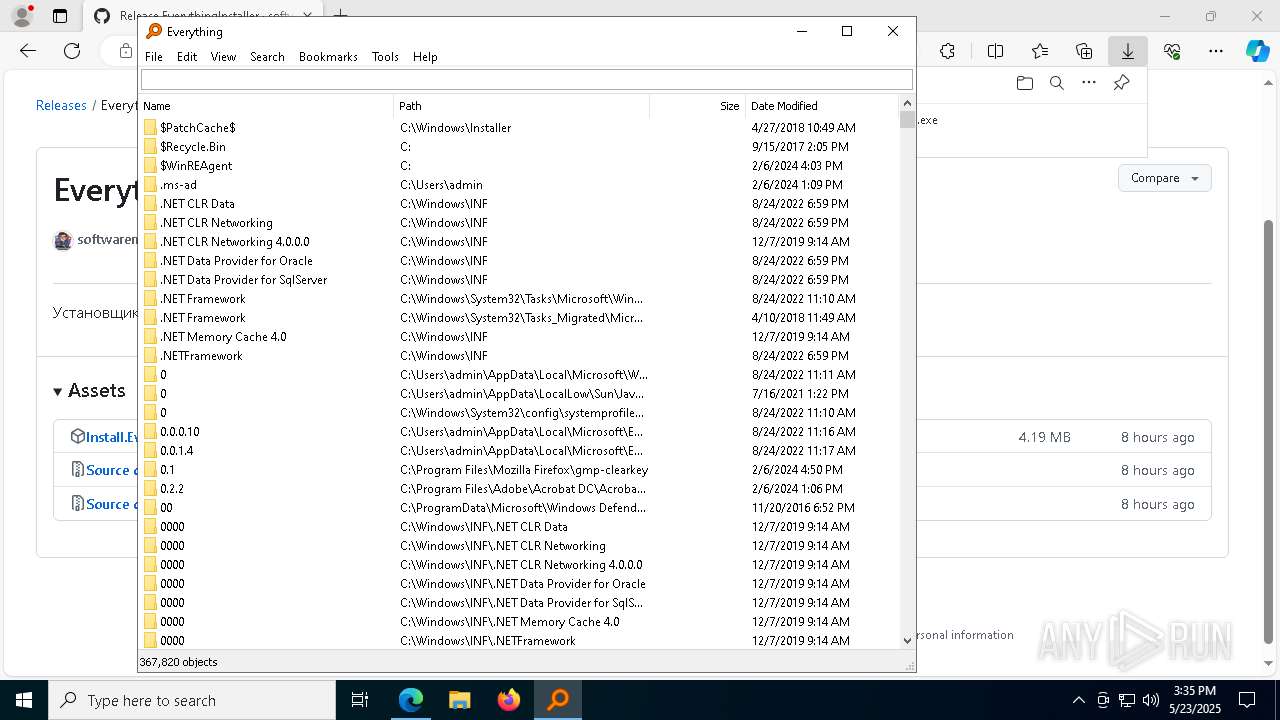
EVERYTHING mutex has been found
- Everything.exe (PID: 1020)
- Everything.exe (PID: 2692)
Gets data length (POWERSHELL)
- powershell.exe (PID: 668)
Disables trace logs
- powershell.exe (PID: 668)
Checks proxy server information
- powershell.exe (PID: 668)
Reads Internet Explorer settings
- powershell.exe (PID: 668)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 668)
Creates a software uninstall entry
- Install.Everything.tmp (PID: 864)
Creates files or folders in the user directory
- Everything.exe (PID: 1020)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
191
Monitored processes
53
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "powershell.exe" -ExecutionPolicy Bypass -File "C:\Program Files (x86)\Everything\post_install.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | Install.Everything.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5460 --field-trial-handle=2352,i,15301906313217026354,15133698121902190121,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | "C:\Users\admin\AppData\Local\Temp\is-MJIEE.tmp\Install.Everything.tmp" /SL5="$602DA,3269632,1061376,C:\Users\admin\Downloads\Install.Everything.exe" /SPAWNWND=$702B0 /NOTIFYWND=$1102DC | C:\Users\admin\AppData\Local\Temp\is-MJIEE.tmp\Install.Everything.tmp | Install.Everything.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/softwaremaster-ru/Everything-program" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5968 --field-trial-handle=2352,i,15301906313217026354,15133698121902190121,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Everything\Everything.exe" | C:\Program Files (x86)\Everything\Everything.exe | — | Install.Everything.tmp | |||||||||||
User: admin Company: voidtools Integrity Level: MEDIUM Description: Everything Exit code: 0 Version: 1.4.1.1026 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6936 --field-trial-handle=2352,i,15301906313217026354,15133698121902190121,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6640 --field-trial-handle=2352,i,15301906313217026354,15133698121902190121,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1228 | "C:\Users\admin\Downloads\Install.Everything.exe" | C:\Users\admin\Downloads\Install.Everything.exe | msedge.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Everything Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1452 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6608 --field-trial-handle=2352,i,15301906313217026354,15133698121902190121,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
15 218
Read events
15 140
Write events
78
Delete events
0
Modification events
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BB35EA9F65942F00 | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F37116A065942F00 | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197226 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {51DC0A76-884D-438B-98C2-9DCA0DEC6BB9} | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197226 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D3170F51-CA25-4178-88C5-740C8FEBFD6B} | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197226 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BB5A4114-B471-46FA-9ED3-C14F748C7A86} | |||
| (PID) Process: | (896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197226 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {57AC7BE9-D2BD-4139-A0EE-7B8ED06FE7C6} | |||
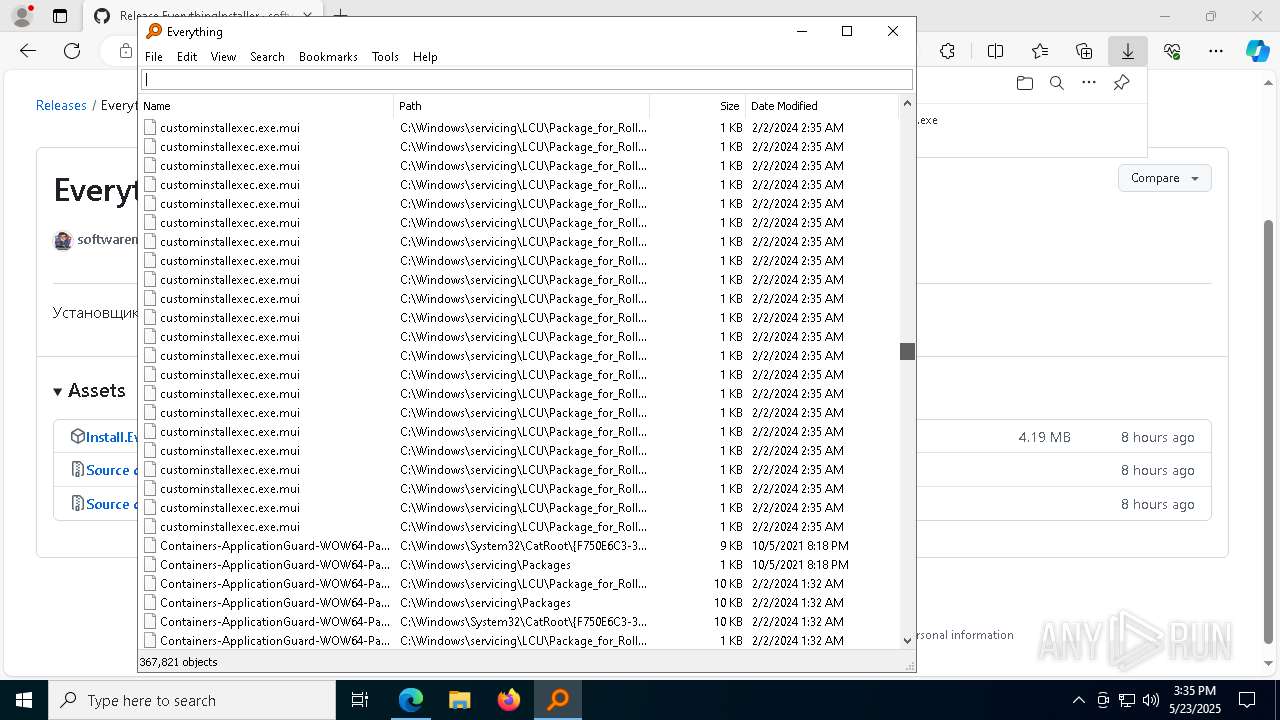
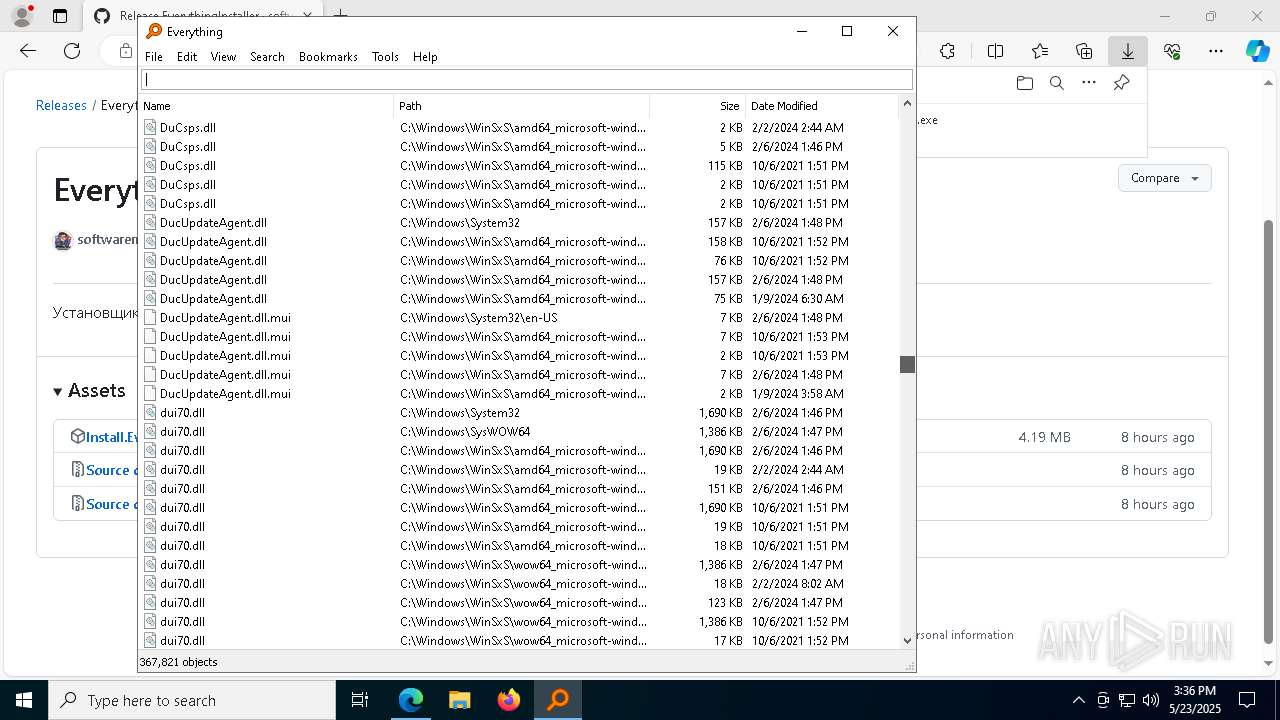
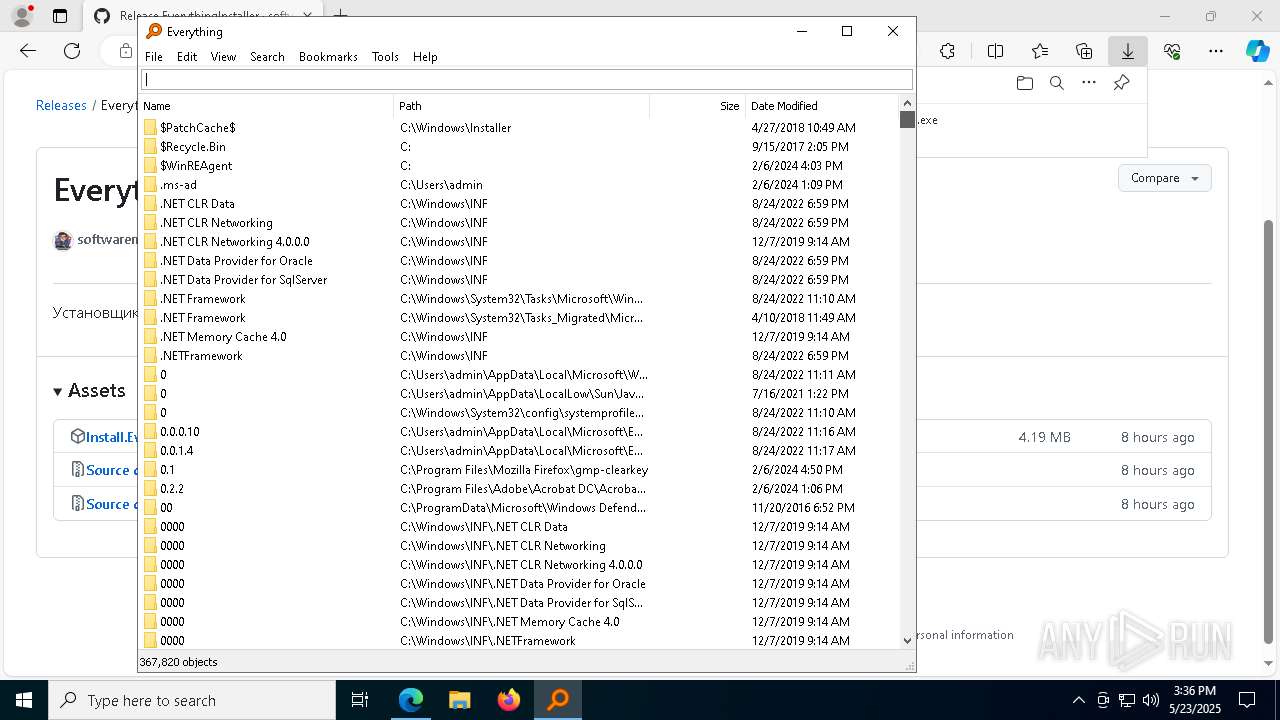
Executable files
21
Suspicious files
270
Text files
65
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ccd7.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10cce7.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10cce7.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ccd7.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10cce7.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
95
DNS requests
95
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
668 | powershell.exe | POST | 400 | 185.50.25.45:80 | http://v66387pu.beget.tech/notify.php | unknown | — | — | whitelisted |
668 | powershell.exe | POST | 400 | 185.50.25.45:80 | http://v66387pu.beget.tech/notify.php | unknown | — | — | whitelisted |
7824 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748301568&P2=404&P3=2&P4=G7ynlLl87eJxqSb4kJ9A5zTIfQTCDw8ASrKB8T6OPeF4uWvWH4EqmpC2w0ZJsElSUoHsQWoUFtQ7GTs98OffMA%3d%3d | unknown | — | — | whitelisted |
668 | powershell.exe | POST | 400 | 185.50.25.45:80 | http://v66387pu.beget.tech/notify.php | unknown | — | — | whitelisted |
7824 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748301568&P2=404&P3=2&P4=G7ynlLl87eJxqSb4kJ9A5zTIfQTCDw8ASrKB8T6OPeF4uWvWH4EqmpC2w0ZJsElSUoHsQWoUFtQ7GTs98OffMA%3d%3d | unknown | — | — | whitelisted |
7824 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748301568&P2=404&P3=2&P4=G7ynlLl87eJxqSb4kJ9A5zTIfQTCDw8ASrKB8T6OPeF4uWvWH4EqmpC2w0ZJsElSUoHsQWoUFtQ7GTs98OffMA%3d%3d | unknown | — | — | whitelisted |
7824 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748301568&P2=404&P3=2&P4=G7ynlLl87eJxqSb4kJ9A5zTIfQTCDw8ASrKB8T6OPeF4uWvWH4EqmpC2w0ZJsElSUoHsQWoUFtQ7GTs98OffMA%3d%3d | unknown | — | — | whitelisted |
7824 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748301568&P2=404&P3=2&P4=G7ynlLl87eJxqSb4kJ9A5zTIfQTCDw8ASrKB8T6OPeF4uWvWH4EqmpC2w0ZJsElSUoHsQWoUFtQ7GTs98OffMA%3d%3d | unknown | — | — | whitelisted |
7824 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748301568&P2=404&P3=2&P4=G7ynlLl87eJxqSb4kJ9A5zTIfQTCDw8ASrKB8T6OPeF4uWvWH4EqmpC2w0ZJsElSUoHsQWoUFtQ7GTs98OffMA%3d%3d | unknown | — | — | whitelisted |
7824 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748301568&P2=404&P3=2&P4=G7ynlLl87eJxqSb4kJ9A5zTIfQTCDw8ASrKB8T6OPeF4uWvWH4EqmpC2w0ZJsElSUoHsQWoUFtQ7GTs98OffMA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.181:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
896 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7340 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7340 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7340 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7340 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7340 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7340 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7340 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
668 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
668 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
668 | powershell.exe | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |
668 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
668 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
668 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |