| File name: | 096960eebbb01336864cfdfd27a622f2f699fe20.exe |
| Full analysis: | https://app.any.run/tasks/b789842b-6ebe-41b8-b783-b280dfa815ad |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2019, 20:48:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2E3E48011CCCBD8B72794D58DEC93551 |
| SHA1: | 096960EEBBB01336864CFDFD27A622F2F699FE20 |
| SHA256: | E359ABB919CD235944AA45A7C0AD591C717EF42BA0309A4D4A36113ED2F85191 |
| SSDEEP: | 12288:zjOcOGVK+ci4Gn1q1trnDMUEeheujWzKLo5uXltEsiC1bNzv:vRq+cNtrzh4uosXaMb |
MALICIOUS
Writes to a start menu file
- poish.exe (PID: 2372)
SUSPICIOUS
Creates files in the user directory
- 096960eebbb01336864cfdfd27a622f2f699fe20.exe (PID: 2944)
- poish.exe (PID: 2372)
- poish.exe (PID: 3324)
Executable content was dropped or overwritten
- 096960eebbb01336864cfdfd27a622f2f699fe20.exe (PID: 2944)
Application launched itself
- poish.exe (PID: 2372)
Starts itself from another location
- 096960eebbb01336864cfdfd27a622f2f699fe20.exe (PID: 2944)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3636)
Application launched itself
- iexplore.exe (PID: 3636)
Reads Internet Cache Settings
- iexplore.exe (PID: 4084)
Reads internet explorer settings
- iexplore.exe (PID: 4084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:05:25 20:05:56+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 445952 |
| InitializedDataSize: | 218112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6dc48 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-May-1992 18:05:56 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 25-May-1992 18:05:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0006CC90 | 0x0006CE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62431 |
DATA | 0x0006E000 | 0x00001A90 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.45993 |
BSS | 0x00070000 | 0x00000EC1 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00071000 | 0x0000244A | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.90111 |
.tls | 0x00074000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00075000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.20692 |
.reloc | 0x00076000 | 0x00008028 | 0x00008200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.62462 |
.rsrc | 0x0007F000 | 0x00028D04 | 0x00028E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.04937 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.03088 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
2 | 2.80231 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
226 | 5.60588 | 1462 | Latin 1 / Western European | English - United States | RT_BITMAP |
227 | 7.31199 | 1462 | Latin 1 / Western European | English - United States | RT_BITMAP |
228 | 7.40726 | 1462 | Latin 1 / Western European | English - United States | RT_BITMAP |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
user32.dll |
version.dll |
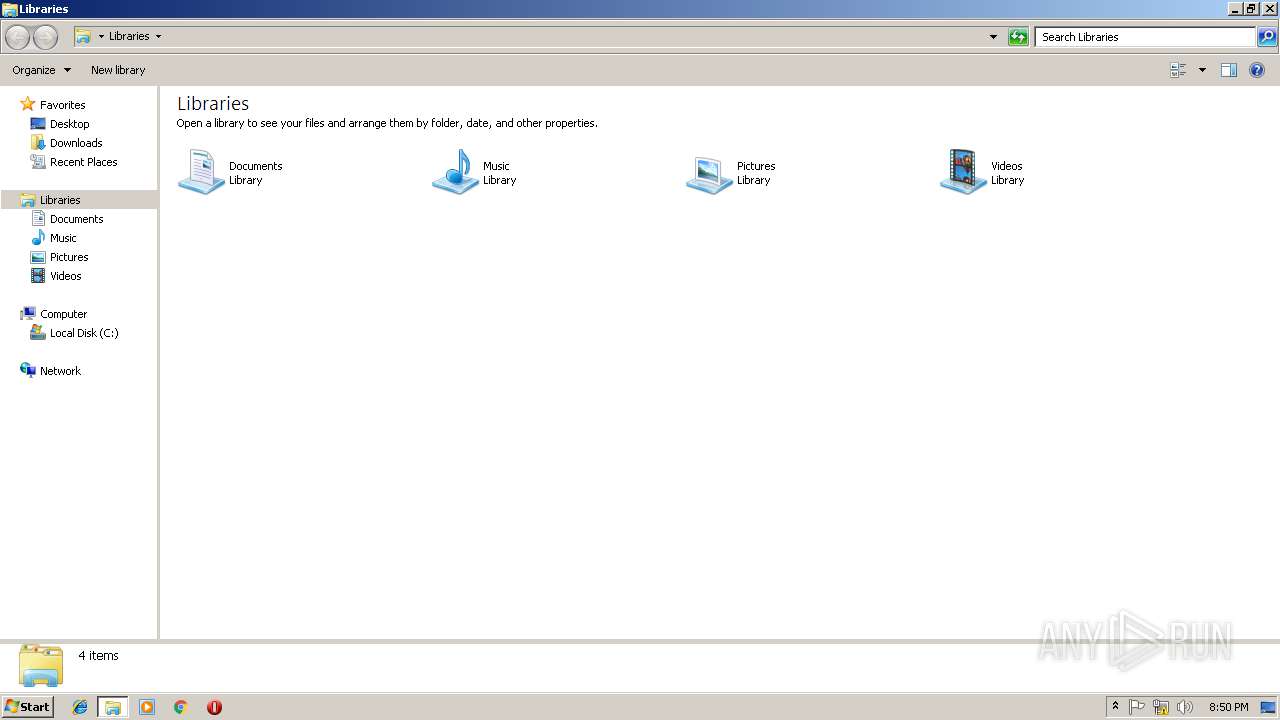
Total processes
34
Monitored processes
6
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | "C:\Users\admin\AppData\Roaming\bsig\poish.exe" | C:\Users\admin\AppData\Roaming\bsig\poish.exe | 096960eebbb01336864cfdfd27a622f2f699fe20.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2944 | "C:\Users\admin\AppData\Local\Temp\096960eebbb01336864cfdfd27a622f2f699fe20.exe" | C:\Users\admin\AppData\Local\Temp\096960eebbb01336864cfdfd27a622f2f699fe20.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3324 | "C:\Users\admin\AppData\Roaming\bsig\poish.exe" | C:\Users\admin\AppData\Roaming\bsig\poish.exe | — | poish.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3636 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4084 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3636 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
393
Read events
339
Write events
53
Delete events
1
Modification events
| (PID) Process: | (3324) poish.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\poish_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3324) poish.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\poish_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3324) poish.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\poish_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3324) poish.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\poish_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3324) poish.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\poish_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3324) poish.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\poish_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3324) poish.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\poish_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3324) poish.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\poish_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3324) poish.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\poish_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3324) poish.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\poish_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
1
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2944 | 096960eebbb01336864cfdfd27a622f2f699fe20.exe | C:\Users\admin\AppData\Roaming\bsig\poish.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 3636 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3636 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3636 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFBDAB0A55EAB14577.TMP | — | |
MD5:— | SHA256:— | |||
| 3636 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{4BBB6F4B-AC5C-11E8-969E-5254004AAD11}.dat | — | |
MD5:— | SHA256:— | |||
| 3636 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFD620B47FDC87CA0.TMP | — | |
MD5:— | SHA256:— | |||
| 3636 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF374D886D17CB990A.TMP | — | |
MD5:— | SHA256:— | |||
| 3636 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{5B00FB6F-1519-11E9-BAD8-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2372 | poish.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\bsig.vbs | text | |
MD5:— | SHA256:— | |||
| 2944 | 096960eebbb01336864cfdfd27a622f2f699fe20.exe | C:\Users\admin\AppData\Roaming\bsig\poish.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3636 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3636 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
exmops.ml |
| malicious |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ml Domain |