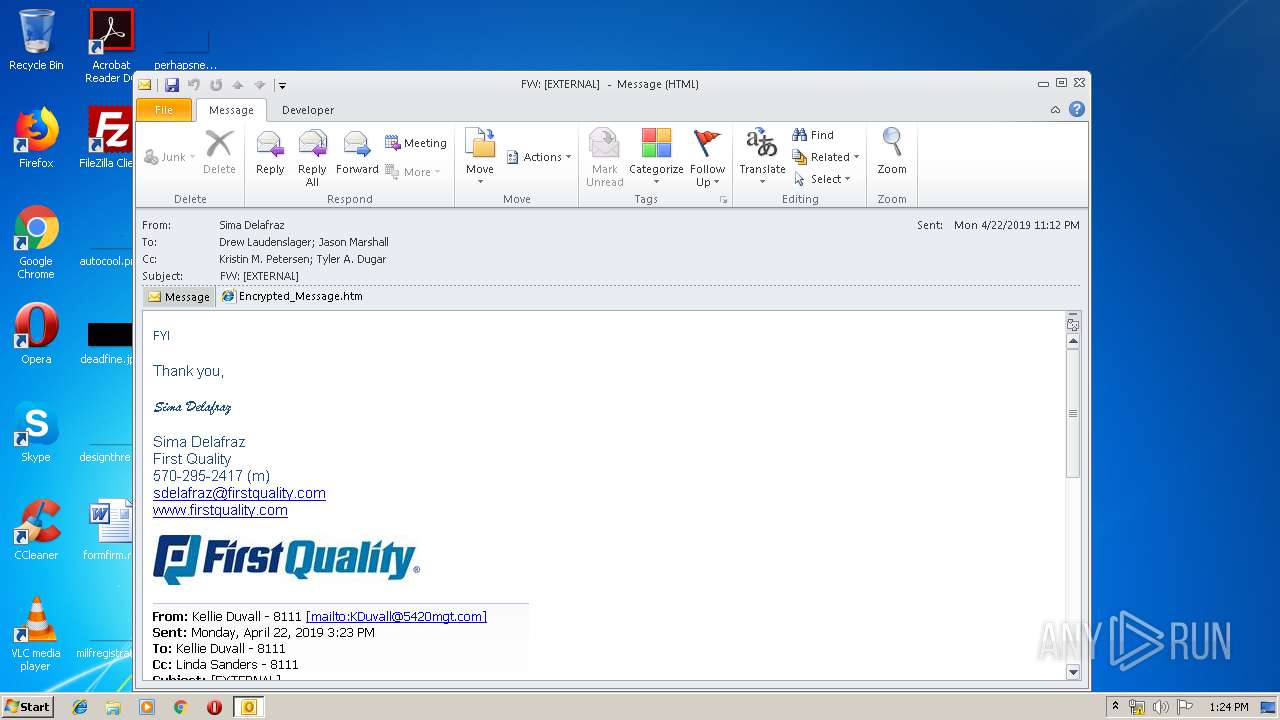
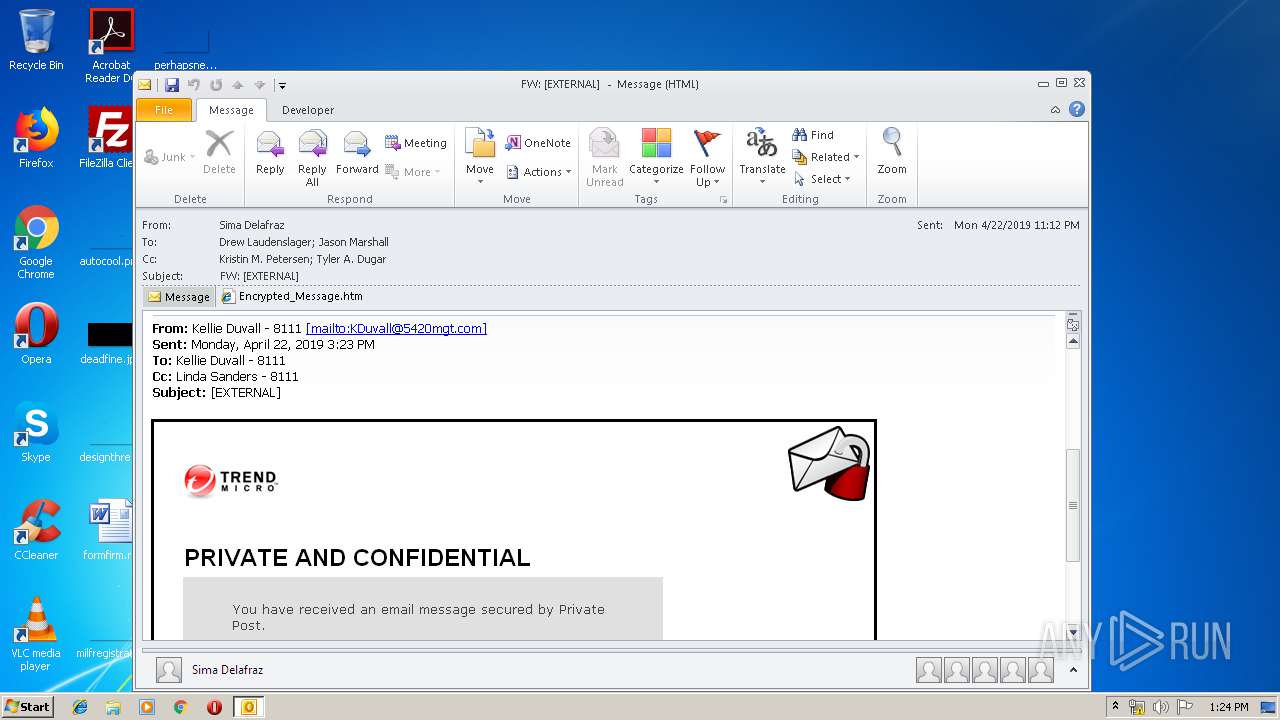
| File name: | FW EXTERNAL .msg |
| Full analysis: | https://app.any.run/tasks/8579bc18-974e-45bd-99bf-01dfa8aed73a |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 12:23:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 3FBEAB157B957F2EDE4AA68BE903B6DB |
| SHA1: | DC68922969DAD03D6C862A2A10AFF32DBE2708DE |
| SHA256: | E356AA4C17BE2382EDFAE985EAE4795527208CCDFED858A4D2F1E6CE247647F8 |
| SSDEEP: | 1536:nYW39zDx2heHb+AeAK+RDRdktghDUI7Slqc0R+AbWf+MgJ02O:YmcheHb+AeAhFRdigh0lXA76fkc |
MALICIOUS
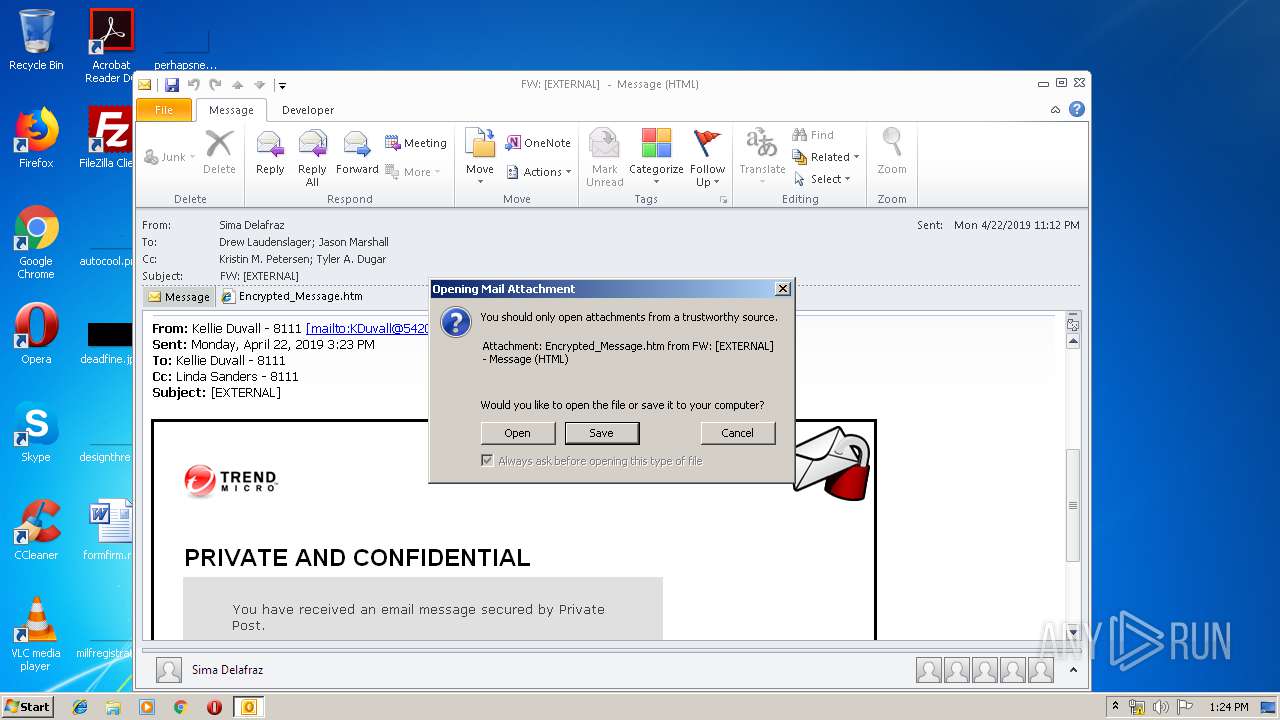
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 1204)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 1204)
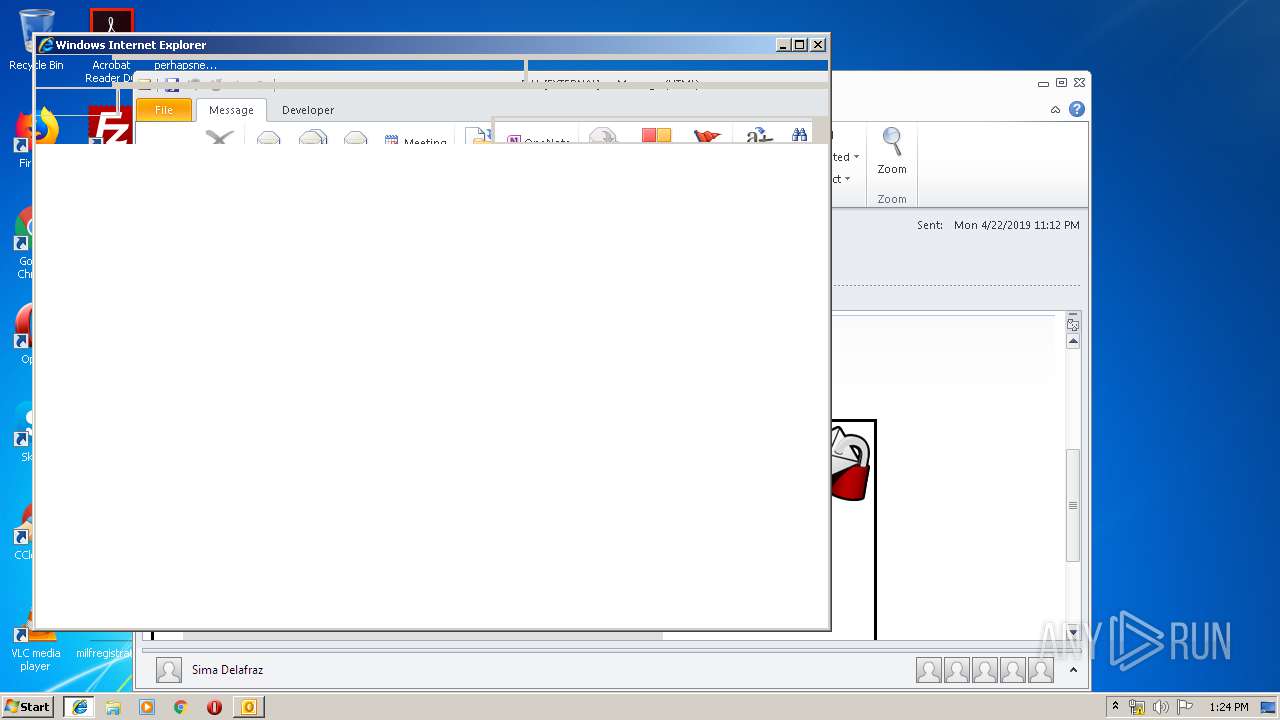
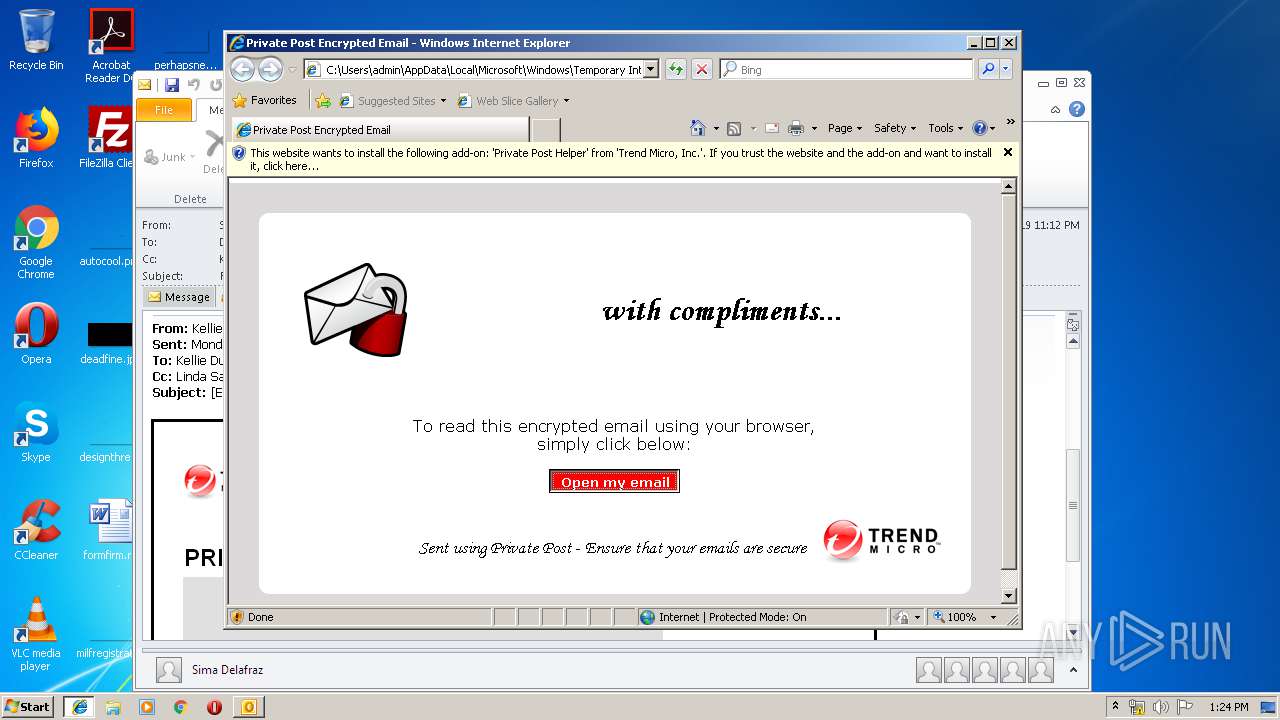
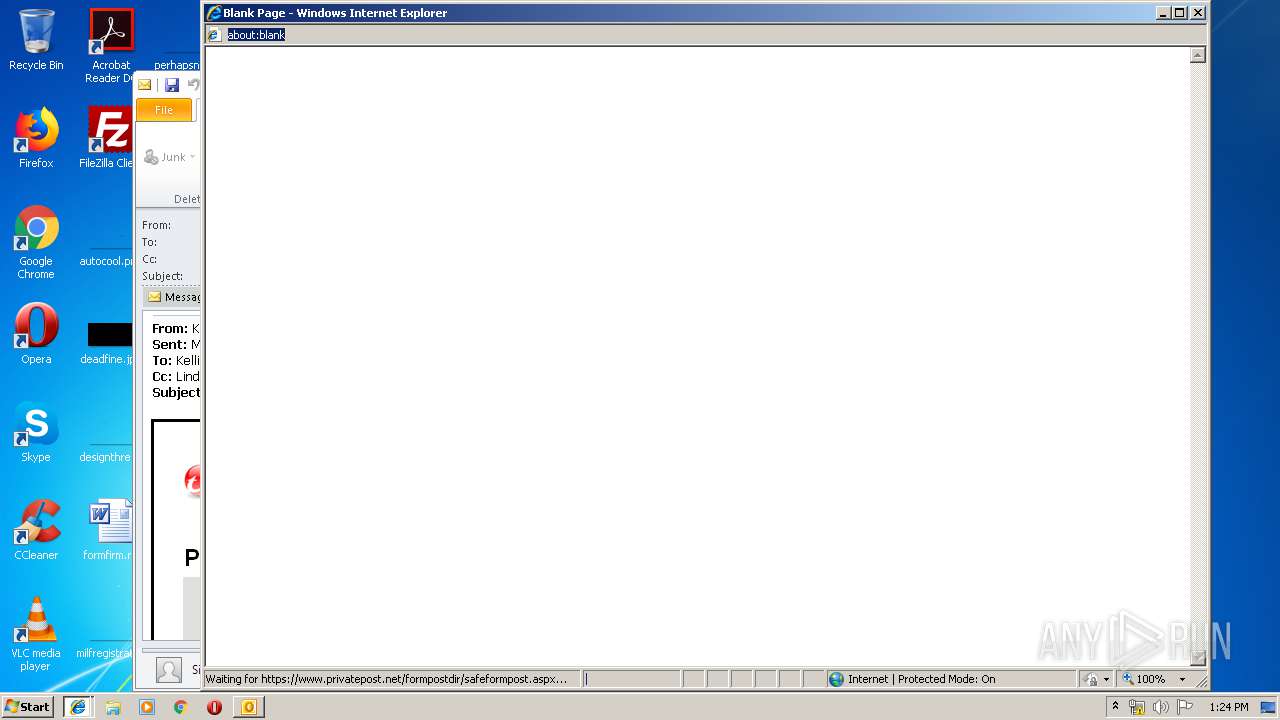
Starts Internet Explorer
- OUTLOOK.EXE (PID: 1204)
INFO
Dropped object may contain Bitcoin addresses
- OUTLOOK.EXE (PID: 1204)
Application launched itself
- iexplore.exe (PID: 3668)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1204)
Reads internet explorer settings
- iexplore.exe (PID: 3356)
- iexplore.exe (PID: 2068)
Changes internet zones settings
- iexplore.exe (PID: 3668)
Reads Internet Cache Settings
- iexplore.exe (PID: 3356)
- iexplore.exe (PID: 2068)
Creates files in the user directory
- iexplore.exe (PID: 3356)
- iexplore.exe (PID: 2068)
Reads settings of System Certificates
- iexplore.exe (PID: 3356)
- iexplore.exe (PID: 3668)
Changes settings of System certificates
- iexplore.exe (PID: 3668)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
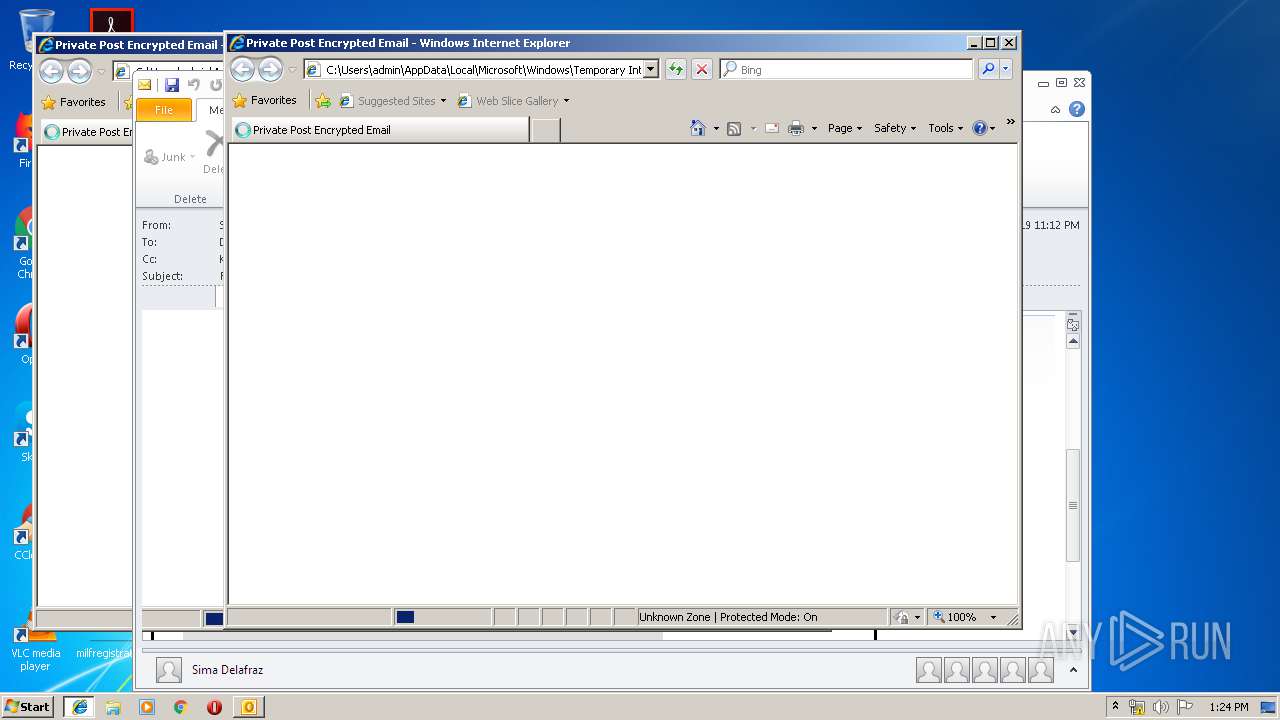
| 1204 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\FW EXTERNAL .msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3668 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3356 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3668 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
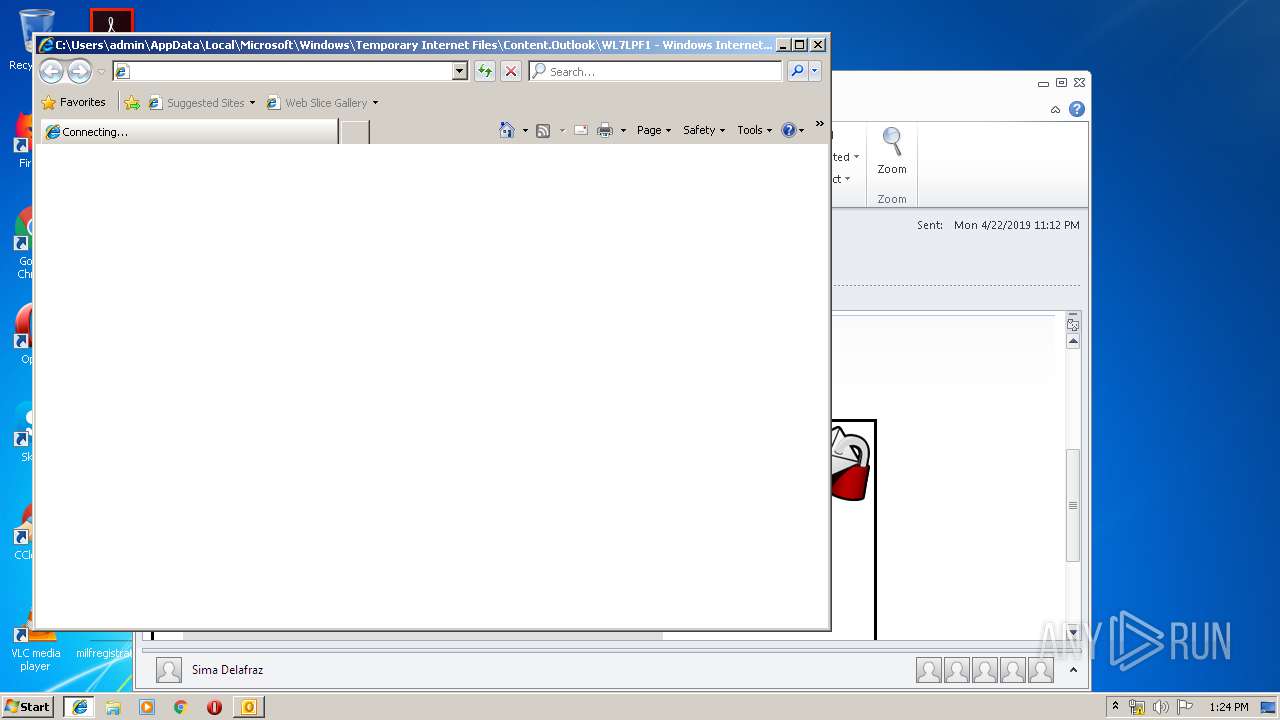
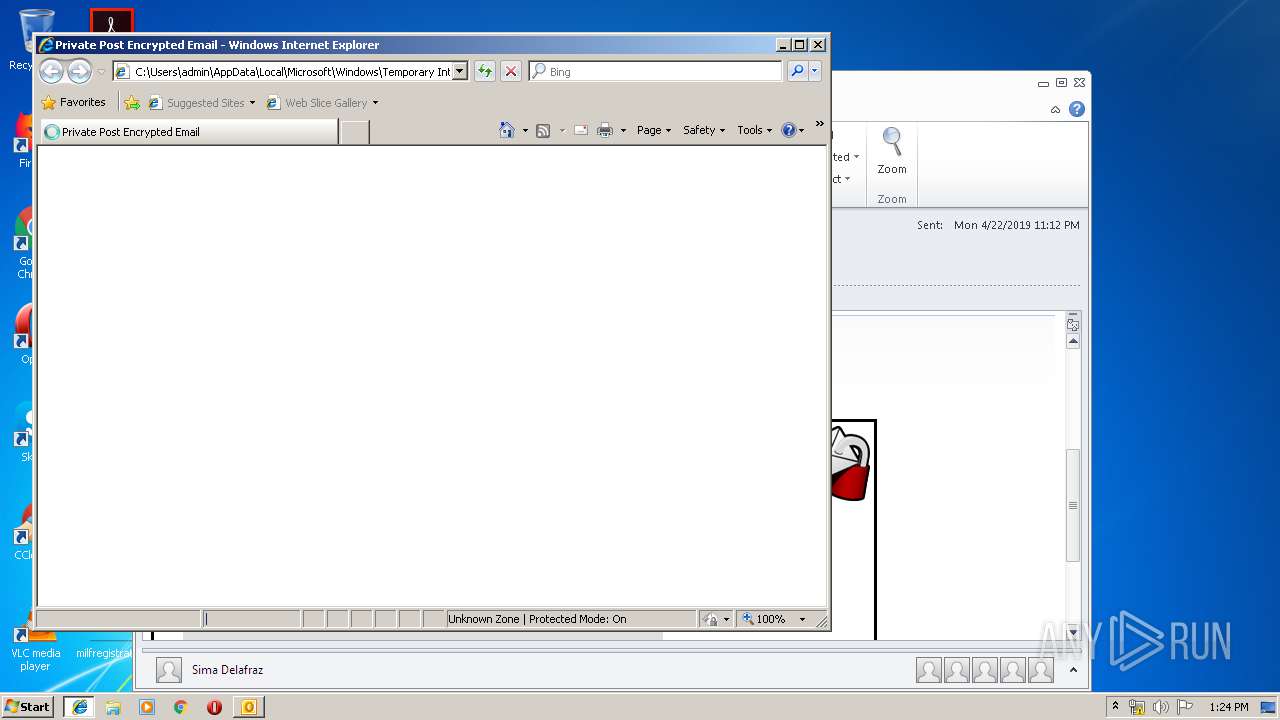
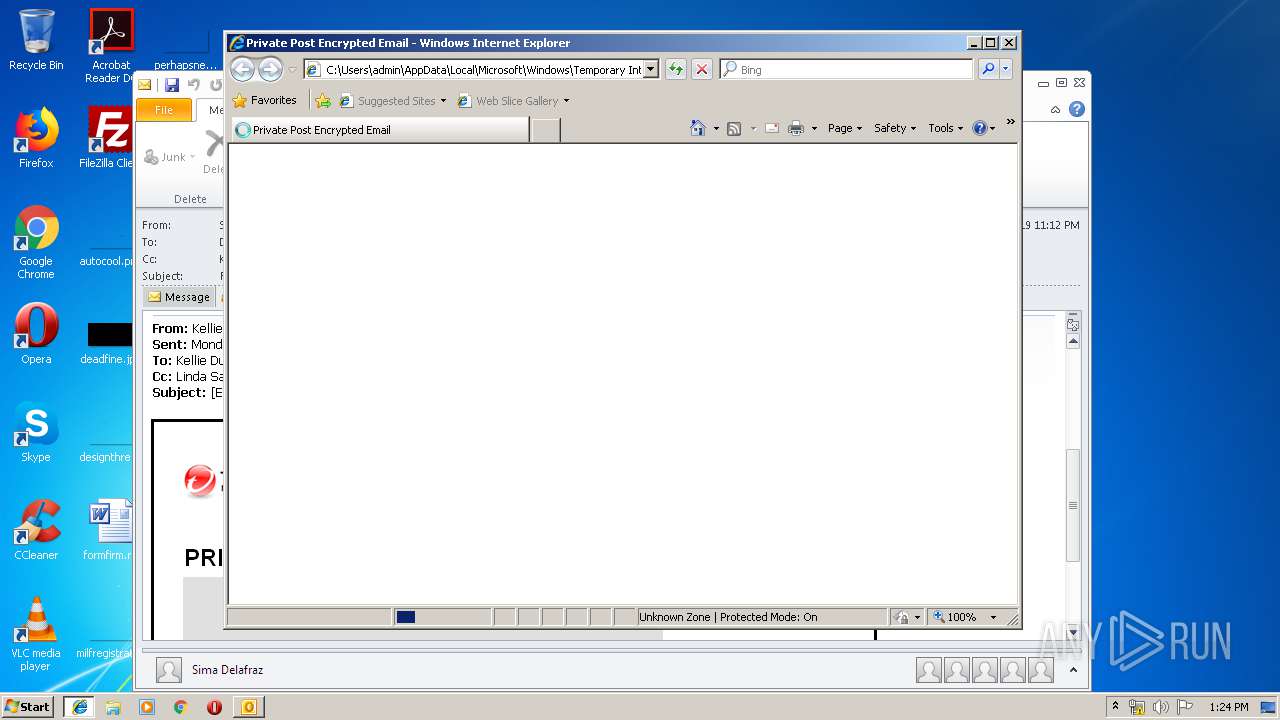
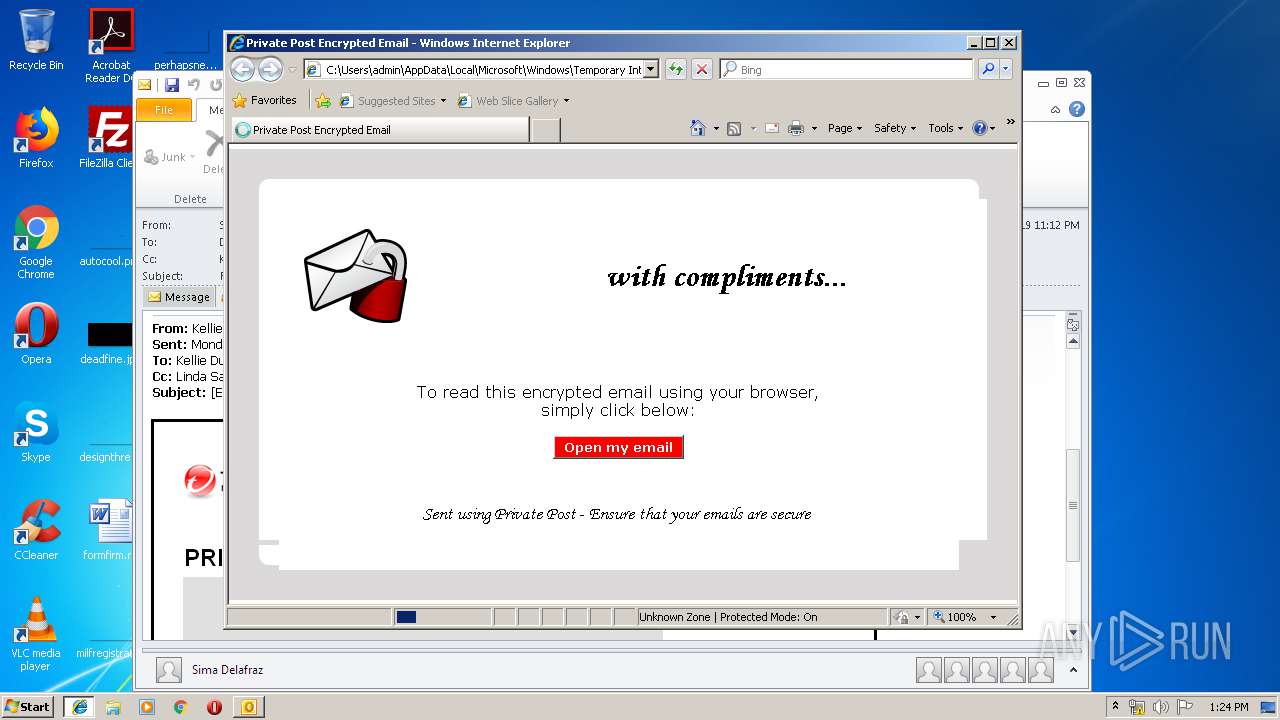
| 3668 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\WL7LPF18\Encrypted_Message.htm | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 263
Read events
1 737
Write events
503
Delete events
23
Modification events
| (PID) Process: | (1204) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1204) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1204) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | lr5 |
Value: 6C723500B4040000010000000000000000000000 | |||
| (PID) Process: | (1204) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: B4040000AC50A36FCFF9D40100000000 | |||
| (PID) Process: | (1204) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (1204) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220007520 | |||
| (PID) Process: | (1204) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (1204) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (1204) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (1204) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1318518805 | |||
Executable files
0
Suspicious files
6
Text files
114
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR62BD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\WL7LPF18\Encrypted_Message (2).htm\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\WL7LPF18\Encrypted_Message.htm | html | |
MD5:— | SHA256:— | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\74762339.dat | image | |
MD5:— | SHA256:— | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\WL7LPF18\Encrypted_Message (2).htm | html | |
MD5:— | SHA256:— | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_DBAFA4E5E2932F43B5CBAC995BCB707C.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1204 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_DB2B5271EB493C4D8521216713645B74.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
33
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3356 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/F9B5B632455F9CBEEC575F80DCE96E2CC7B278B7.crt | US | der | 848 b | whitelisted |
1204 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
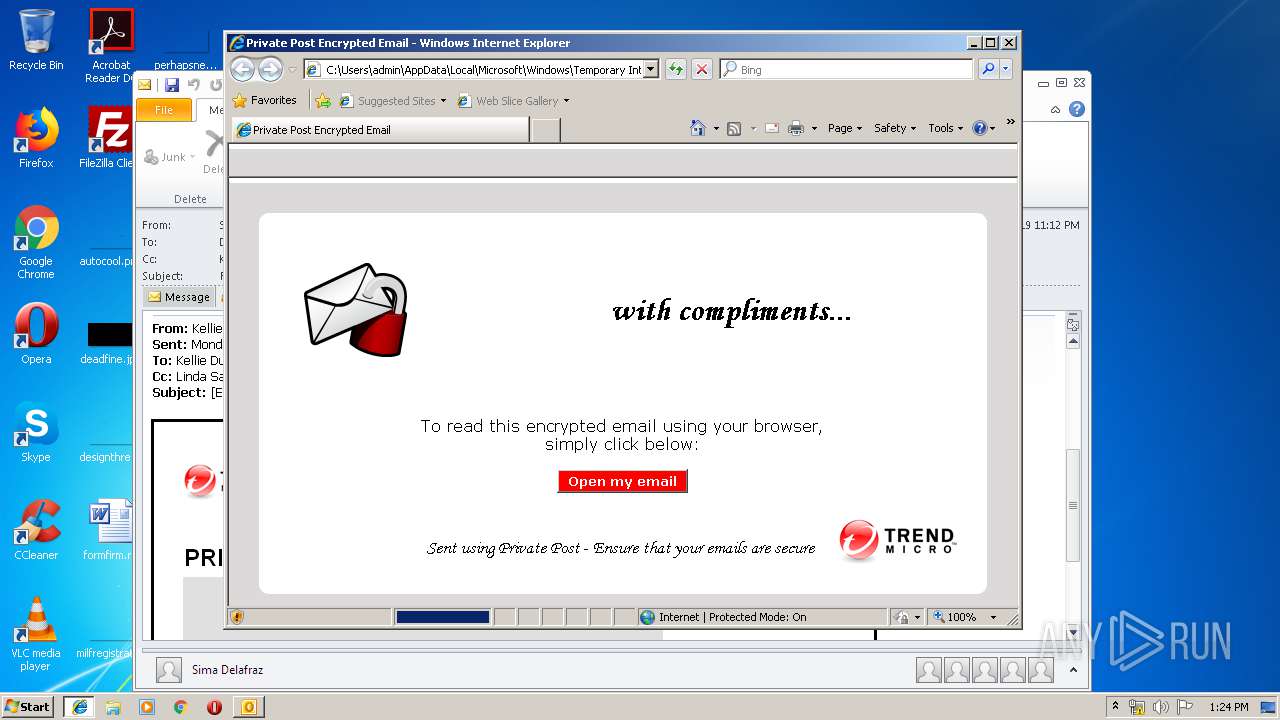
3356 | iexplore.exe | GET | 200 | 213.129.92.227:80 | http://downloads.privatepost.com/files/ppZDHelper/ppZDHelper.cab | GB | compressed | 389 Kb | suspicious |
3668 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3668 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3356 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/F9B5B632455F9CBEEC575F80DCE96E2CC7B278B7.crt | US | der | 848 b | whitelisted |
3356 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
3356 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1204 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
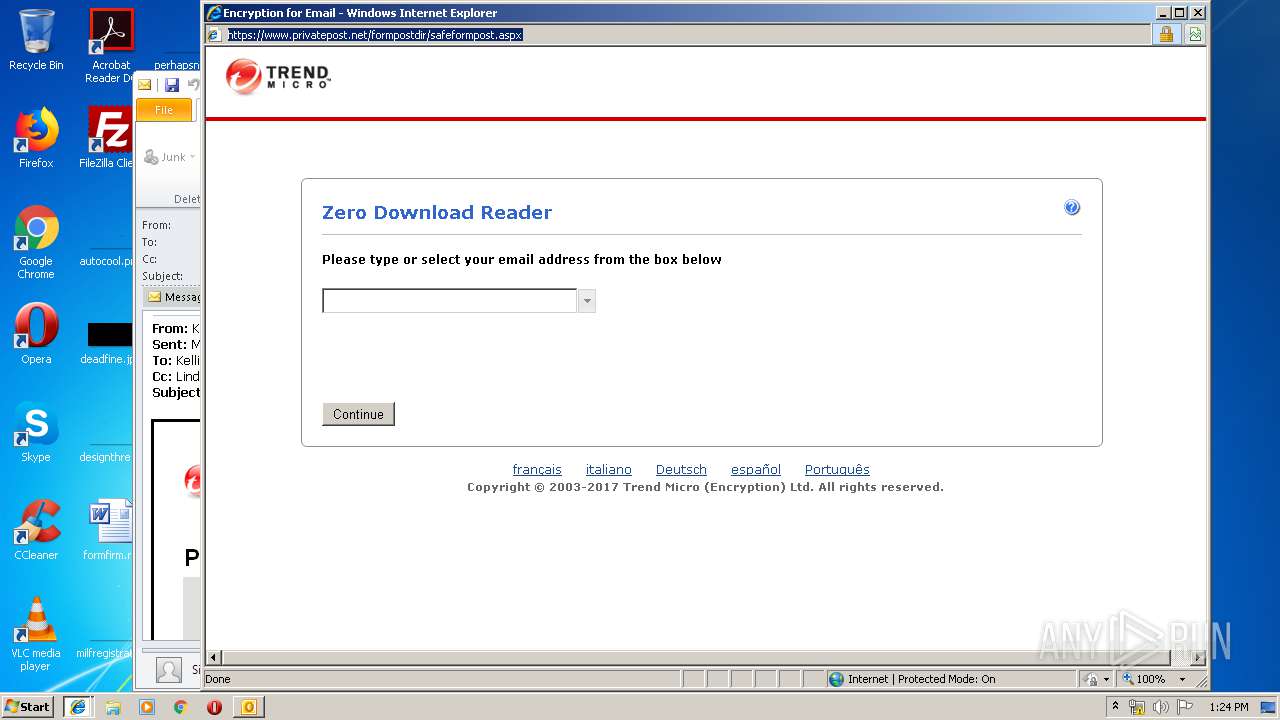
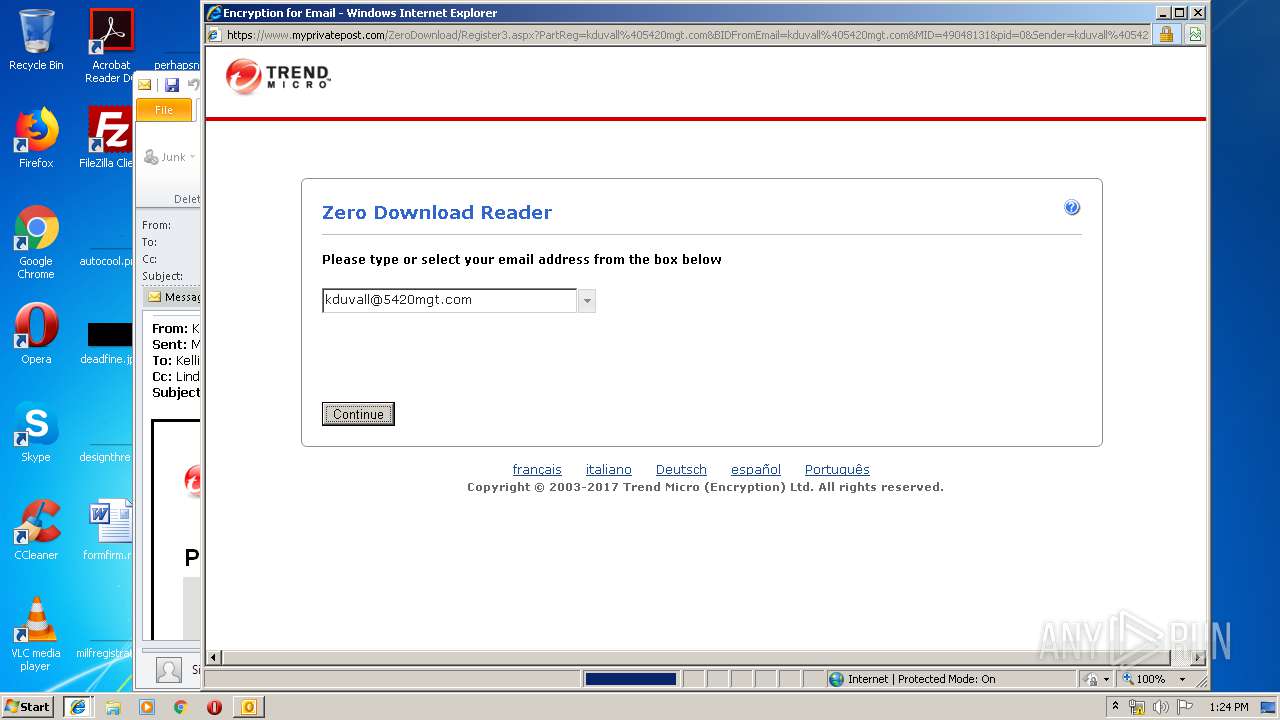
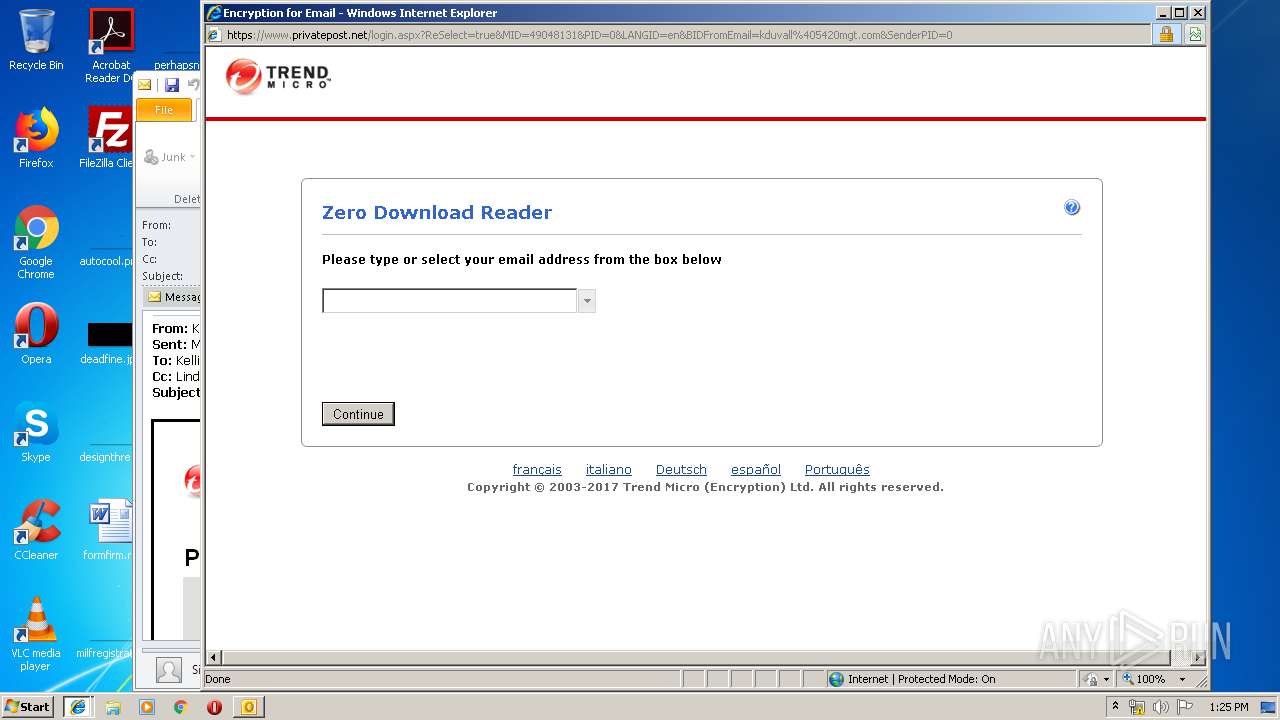
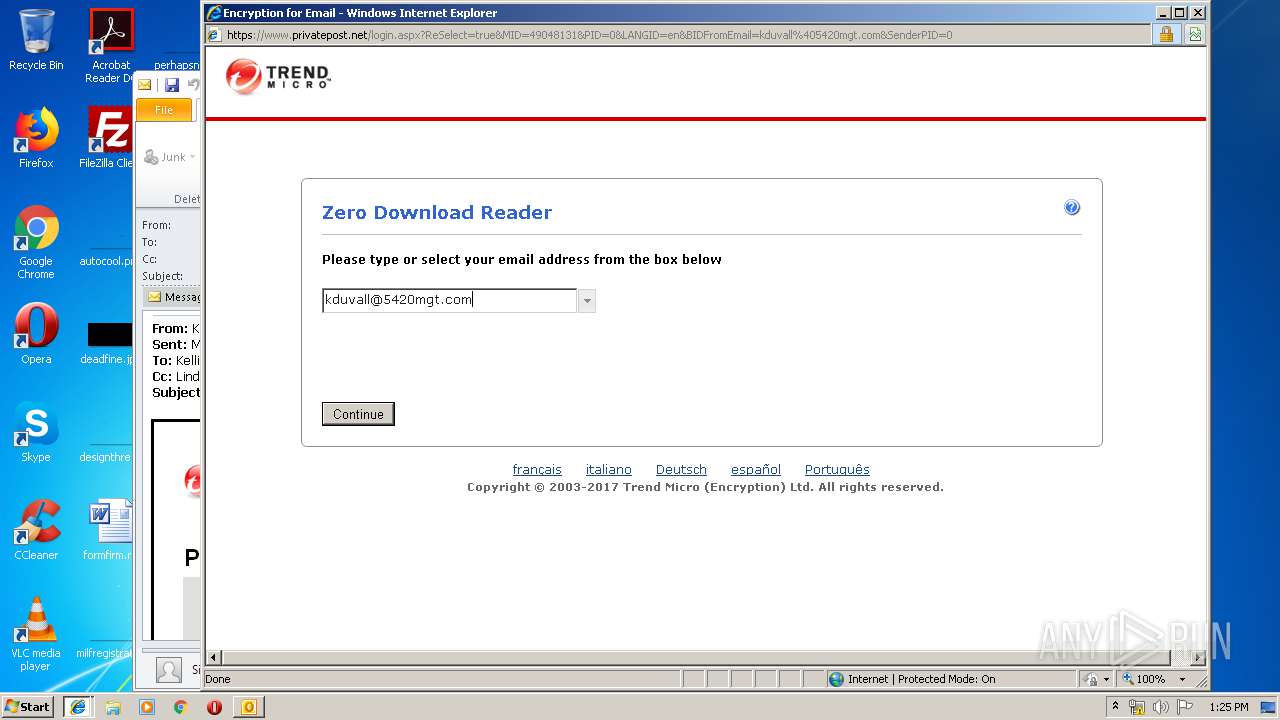
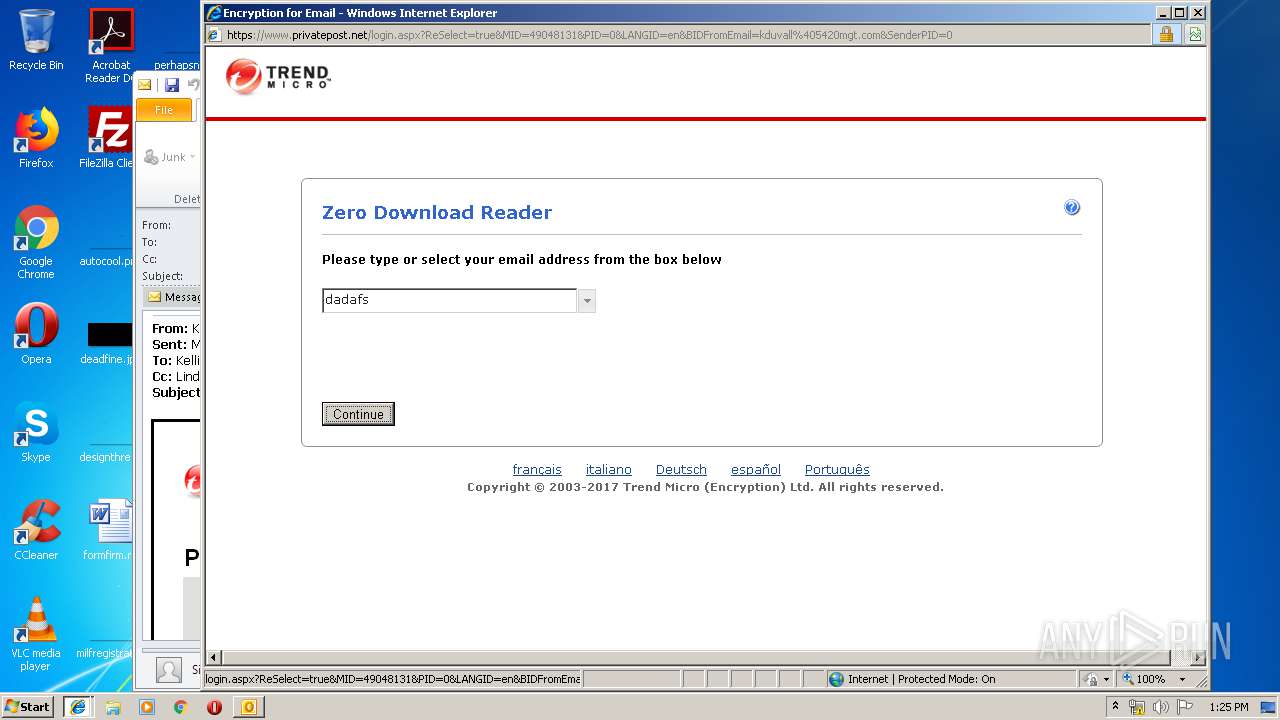
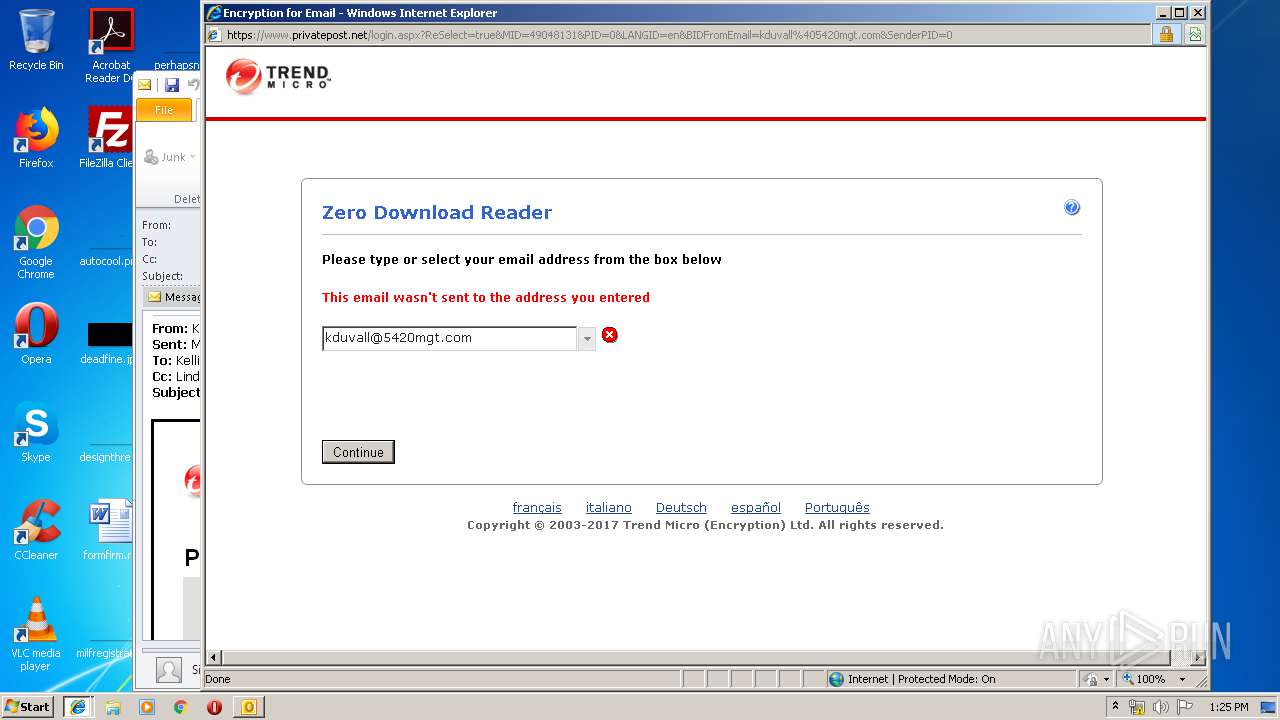
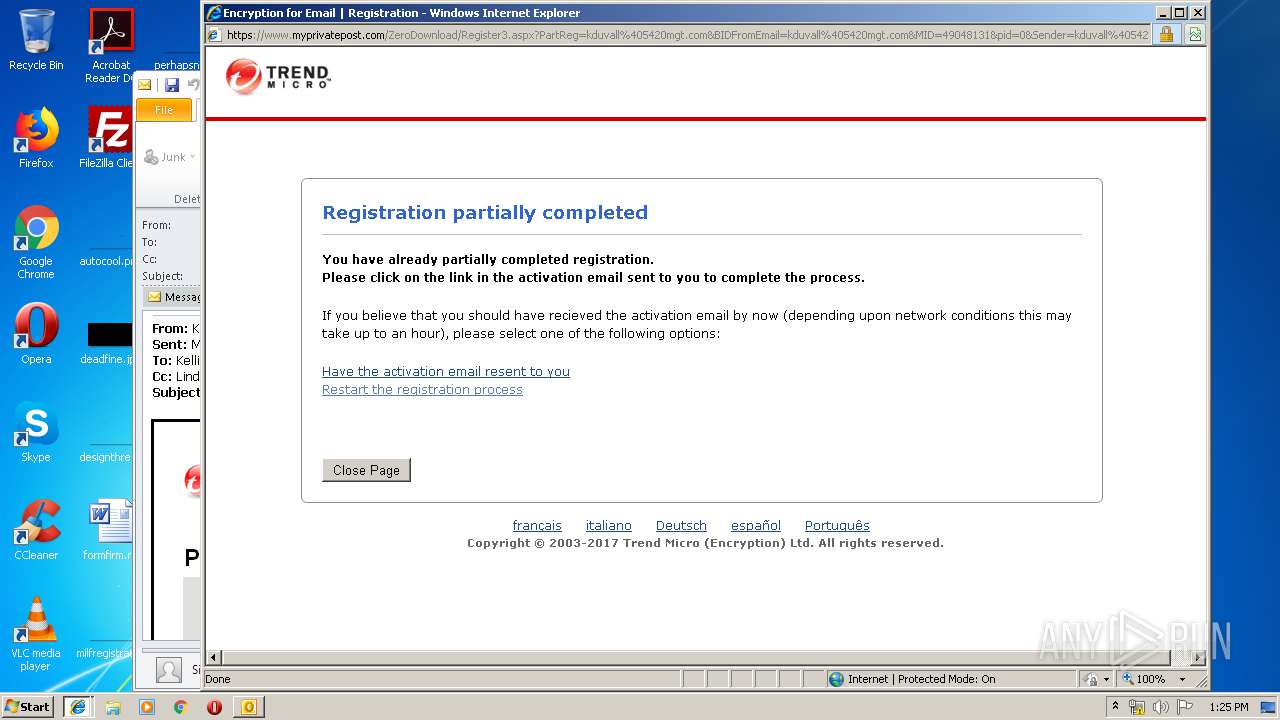
3356 | iexplore.exe | 213.129.92.228:443 | www.privatepost.net | The Bunker Secure Hosting Ltd | GB | unknown |
3356 | iexplore.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2068 | iexplore.exe | 213.129.92.228:443 | www.privatepost.net | The Bunker Secure Hosting Ltd | GB | unknown |
3356 | iexplore.exe | 213.129.92.227:80 | downloads.privatepost.com | The Bunker Secure Hosting Ltd | GB | unknown |
3668 | iexplore.exe | 213.129.92.228:443 | www.privatepost.net | The Bunker Secure Hosting Ltd | GB | unknown |
3668 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
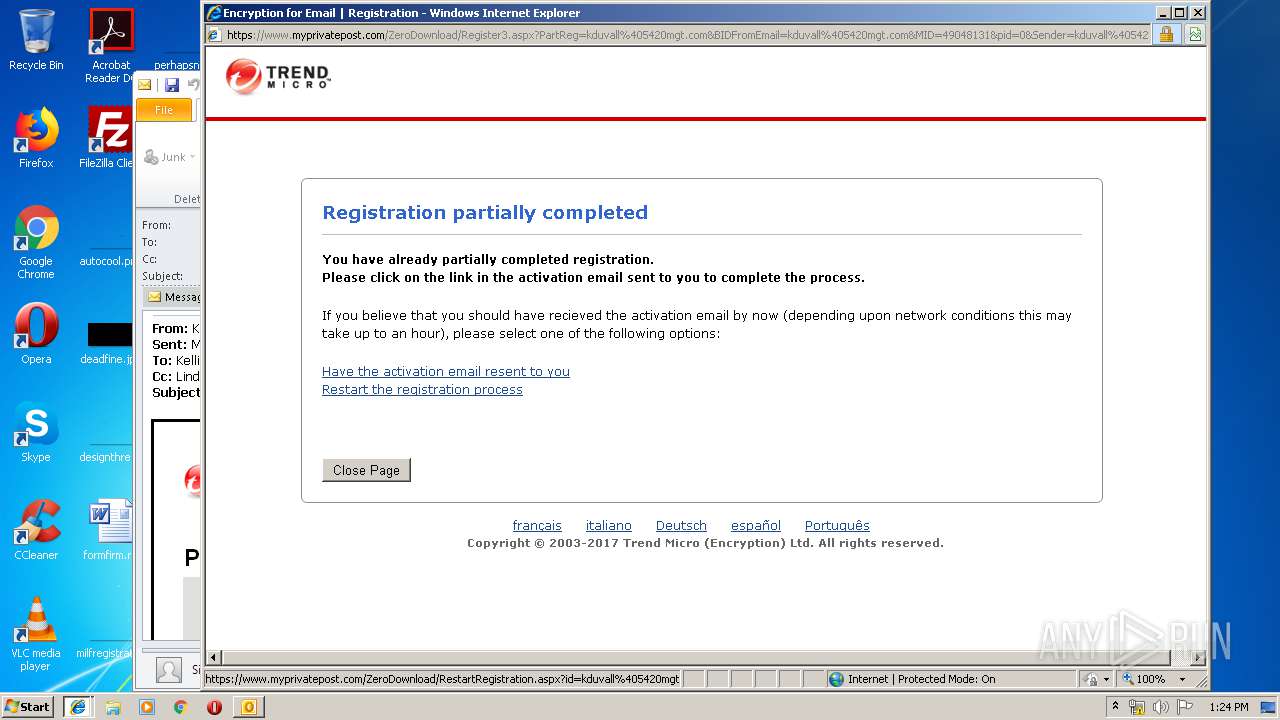
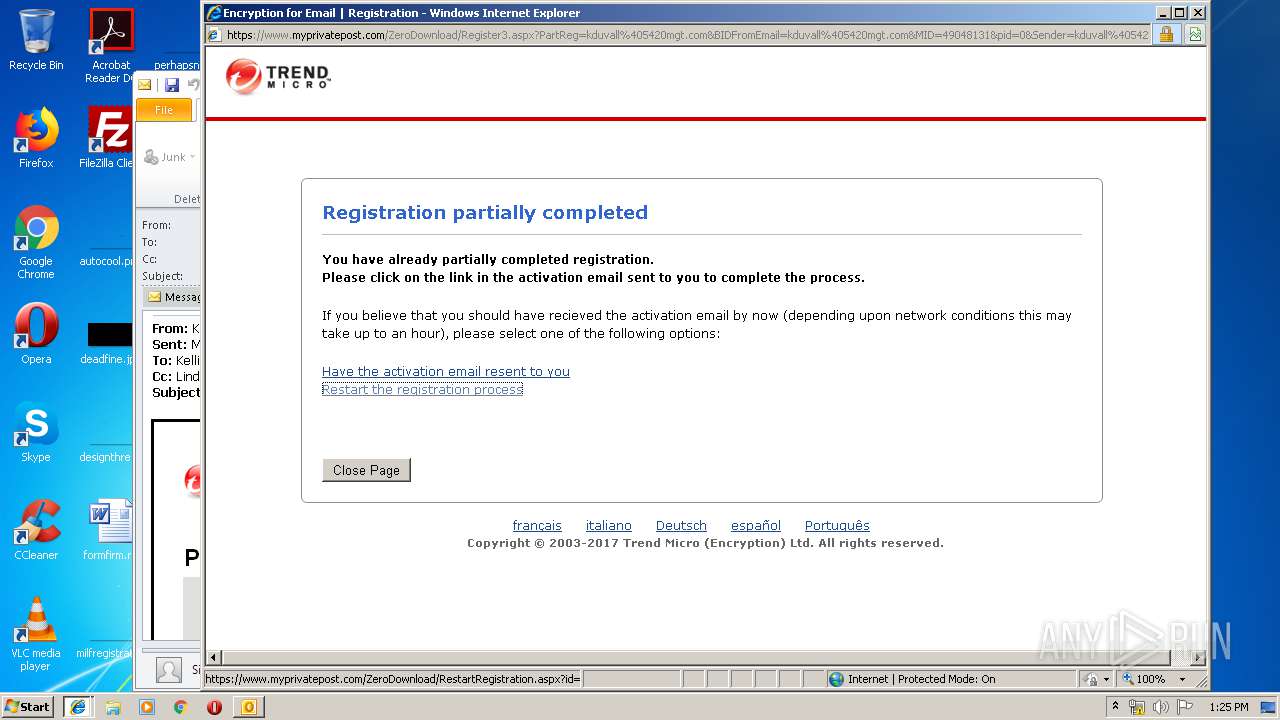
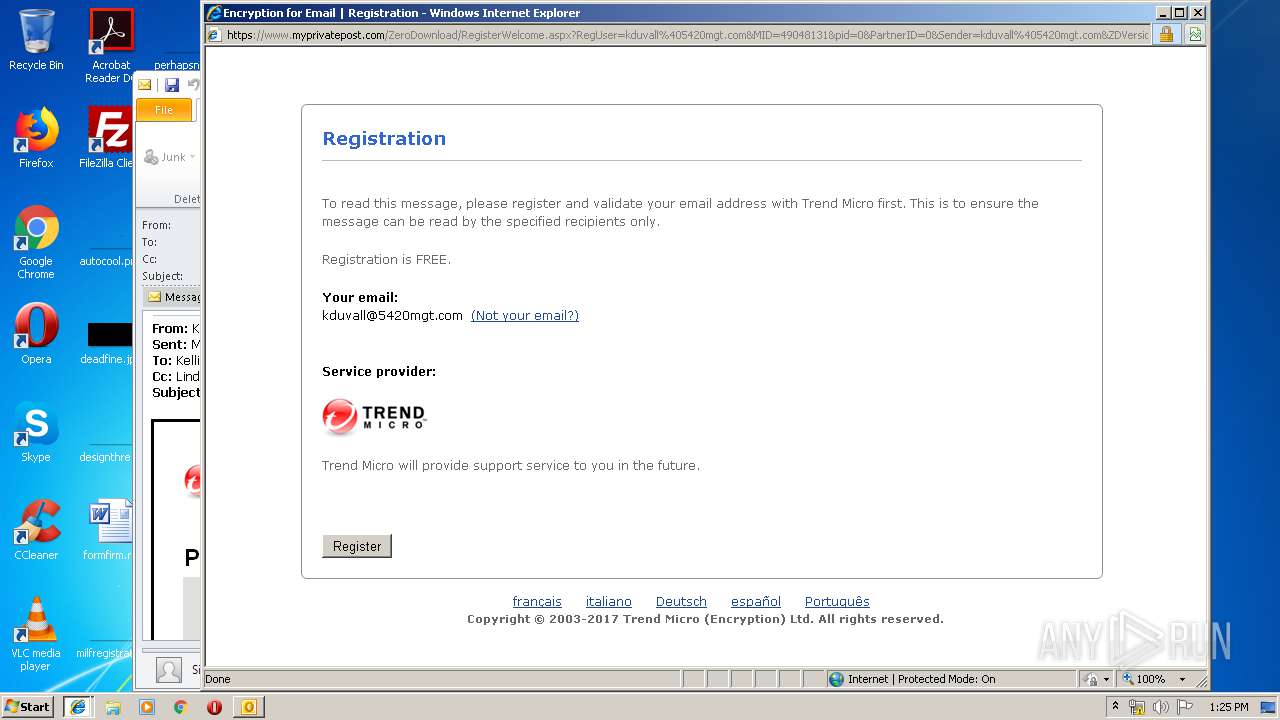
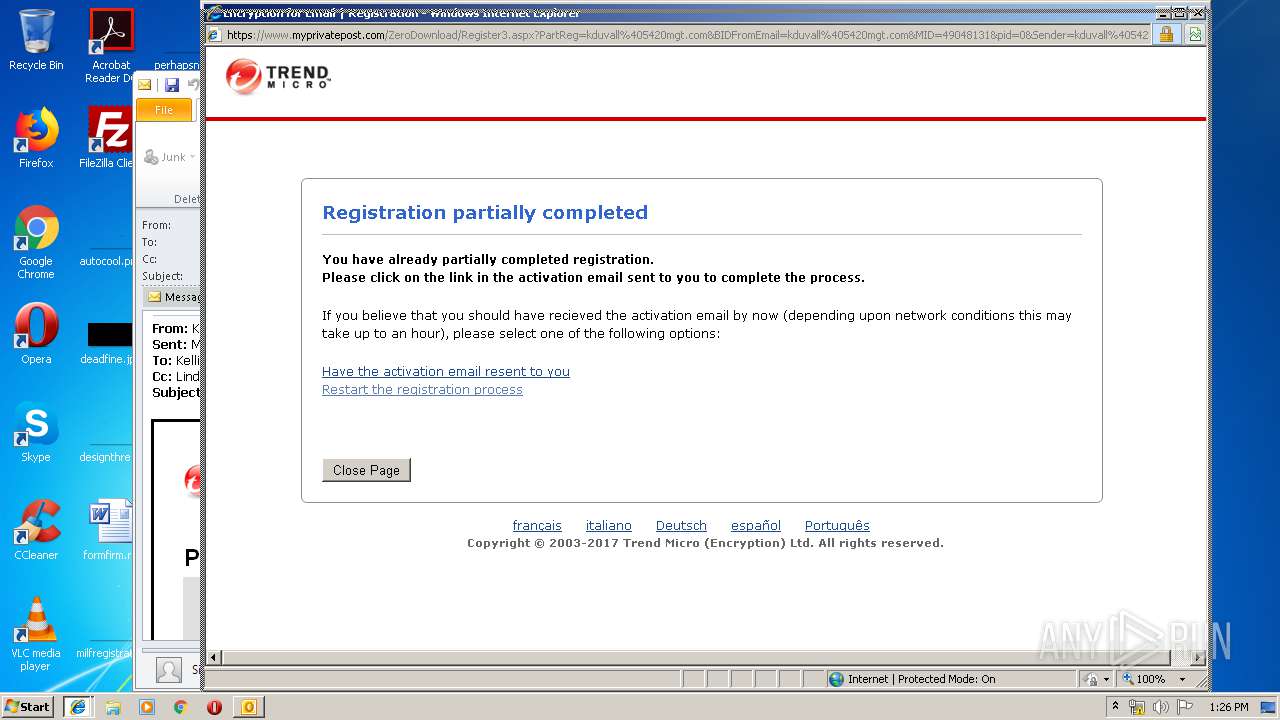
2068 | iexplore.exe | 150.70.226.87:443 | www.myprivatepost.com | TREND MICRO INCORPORATED | JP | unknown |
3668 | iexplore.exe | 150.70.226.87:443 | www.myprivatepost.com | TREND MICRO INCORPORATED | JP | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.privatepost.net |
| suspicious |
www.bing.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
downloads.privatepost.com |
| unknown |
www.myprivatepost.com |
| unknown |