| File name: | Odyssey-1KImproved.exe |
| Full analysis: | https://app.any.run/tasks/82c1b621-9c15-4d14-aec9-b31a52f130e5 |
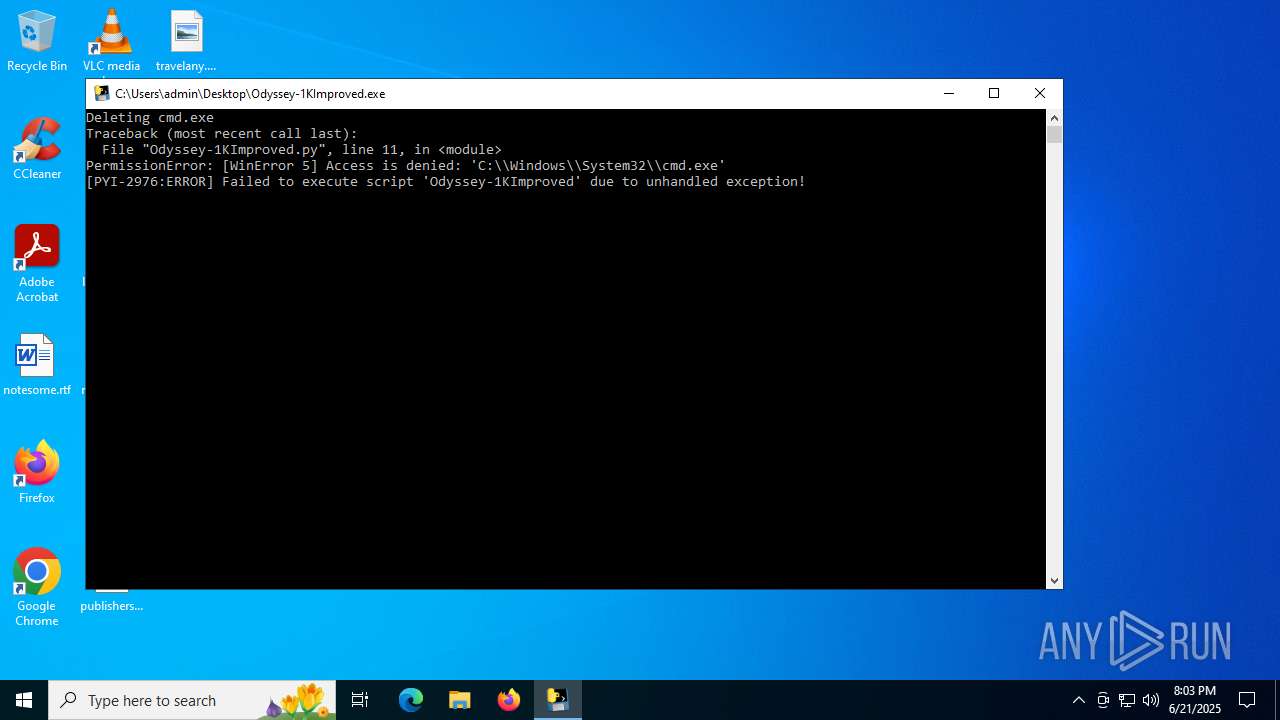
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 20:03:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | 79B3B4F44712EA3D795D7FD90E639988 |
| SHA1: | 8D3E3DAC89C506C239ACF7AFDF503F3B2FCD3A9E |
| SHA256: | E348262D7913634A2C9AFB2BB4430D0F6283BF799BC8C613B9E3843ABD95FE6D |
| SSDEEP: | 98304:Oxb2H2o5gv0Ve7xTT8lnasdu4WtHfktEzafhOsE+XZ0j1kV8sVcS77s8ohWnXZLT:ldrm2Qyreqdy |
MALICIOUS
No malicious indicators.SUSPICIOUS
Loads Python modules
- Odyssey-1KImproved.exe (PID: 2976)
Executable content was dropped or overwritten
- Odyssey-1KImproved.exe (PID: 6584)
The process drops C-runtime libraries
- Odyssey-1KImproved.exe (PID: 6584)
Process drops legitimate windows executable
- Odyssey-1KImproved.exe (PID: 6584)
Process drops python dynamic module
- Odyssey-1KImproved.exe (PID: 6584)
Application launched itself
- Odyssey-1KImproved.exe (PID: 6584)
INFO
Checks supported languages
- Odyssey-1KImproved.exe (PID: 2976)
- Odyssey-1KImproved.exe (PID: 6584)
Reads the computer name
- Odyssey-1KImproved.exe (PID: 6584)
Create files in a temporary directory
- Odyssey-1KImproved.exe (PID: 6584)
The sample compiled with english language support
- Odyssey-1KImproved.exe (PID: 6584)
Checks proxy server information
- slui.exe (PID: 1212)
Reads the software policy settings
- slui.exe (PID: 1212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:18 20:00:04+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 178688 |
| InitializedDataSize: | 153600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc380 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
137
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1212 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\Desktop\Odyssey-1KImproved.exe" | C:\Users\admin\Desktop\Odyssey-1KImproved.exe | — | Odyssey-1KImproved.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 5644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Odyssey-1KImproved.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6584 | "C:\Users\admin\Desktop\Odyssey-1KImproved.exe" | C:\Users\admin\Desktop\Odyssey-1KImproved.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
3 545
Read events
3 545
Write events
0
Delete events
0
Modification events
Executable files
49
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6584 | Odyssey-1KImproved.exe | C:\Users\admin\AppData\Local\Temp\_MEI65842\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:CFE0C1DFDE224EA5FED9BD5FF778A6E0 | SHA256:0D0F80CBF476AF5B1C9FD3775E086ED0DFDB510CD0CC208EC1CCB04572396E3E | |||
| 6584 | Odyssey-1KImproved.exe | C:\Users\admin\AppData\Local\Temp\_MEI65842\_bz2.pyd | executable | |
MD5:59D60A559C23202BEB622021AF29E8A9 | SHA256:706D4A0C26DD454538926CBB2FF6C64257C3D9BD48C956F7CABD6DEF36FFD13E | |||
| 6584 | Odyssey-1KImproved.exe | C:\Users\admin\AppData\Local\Temp\_MEI65842\_socket.pyd | executable | |
MD5:9C6283CC17F9D86106B706EC4EA77356 | SHA256:5CC62AAC52EDF87916DEB4EBBAD9ABB58A6A3565B32E7544F672ACA305C38027 | |||
| 6584 | Odyssey-1KImproved.exe | C:\Users\admin\AppData\Local\Temp\_MEI65842\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:33BBECE432F8DA57F17BF2E396EBAA58 | SHA256:7CF0944901F7F7E0D0B9AD62753FC2FE380461B1CCE8CDC7E9C9867C980E3B0E | |||
| 6584 | Odyssey-1KImproved.exe | C:\Users\admin\AppData\Local\Temp\_MEI65842\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:EFAD0EE0136532E8E8402770A64C71F9 | SHA256:3D2C55902385381869DB850B526261DDEB4628B83E690A32B67D2E0936B2C6ED | |||
| 6584 | Odyssey-1KImproved.exe | C:\Users\admin\AppData\Local\Temp\_MEI65842\api-ms-win-core-interlocked-l1-1-0.dll | executable | |
MD5:C6024CC04201312F7688A021D25B056D | SHA256:8751D30DF554AF08EF42D2FAA0A71ABCF8C7D17CE9E9FF2EA68A4662603EC500 | |||
| 6584 | Odyssey-1KImproved.exe | C:\Users\admin\AppData\Local\Temp\_MEI65842\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:ACCC640D1B06FB8552FE02F823126FF5 | SHA256:332BA469AE84AA72EC8CCE2B33781DB1AB81A42ECE5863F7A3CB5A990059594F | |||
| 6584 | Odyssey-1KImproved.exe | C:\Users\admin\AppData\Local\Temp\_MEI65842\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:1C58526D681EFE507DEB8F1935C75487 | SHA256:EF13DCE8F71173315DFC64AB839B033AB19A968EE15230E9D4D2C9D558EFEEE2 | |||
| 6584 | Odyssey-1KImproved.exe | C:\Users\admin\AppData\Local\Temp\_MEI65842\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:EB0978A9213E7F6FDD63B2967F02D999 | SHA256:AB25A1FE836FC68BCB199F1FE565C27D26AF0C390A38DA158E0D8815EFE1103E | |||
| 6584 | Odyssey-1KImproved.exe | C:\Users\admin\AppData\Local\Temp\_MEI65842\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:E89CDCD4D95CDA04E4ABBA8193A5B492 | SHA256:1A489E0606484BD71A0D9CB37A1DC6CA8437777B3D67BFC8C0075D0CC59E6238 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
42
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
416 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
416 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2664 | RUXIMICS.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.159.71:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.2:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 200 | 40.126.31.0:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 16.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2664 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.55.104.172:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
2664 | RUXIMICS.exe | 23.55.104.172:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.55.104.172:80 | crl.microsoft.com | Akamai International B.V. | US | whitelisted |
1268 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2664 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |