analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
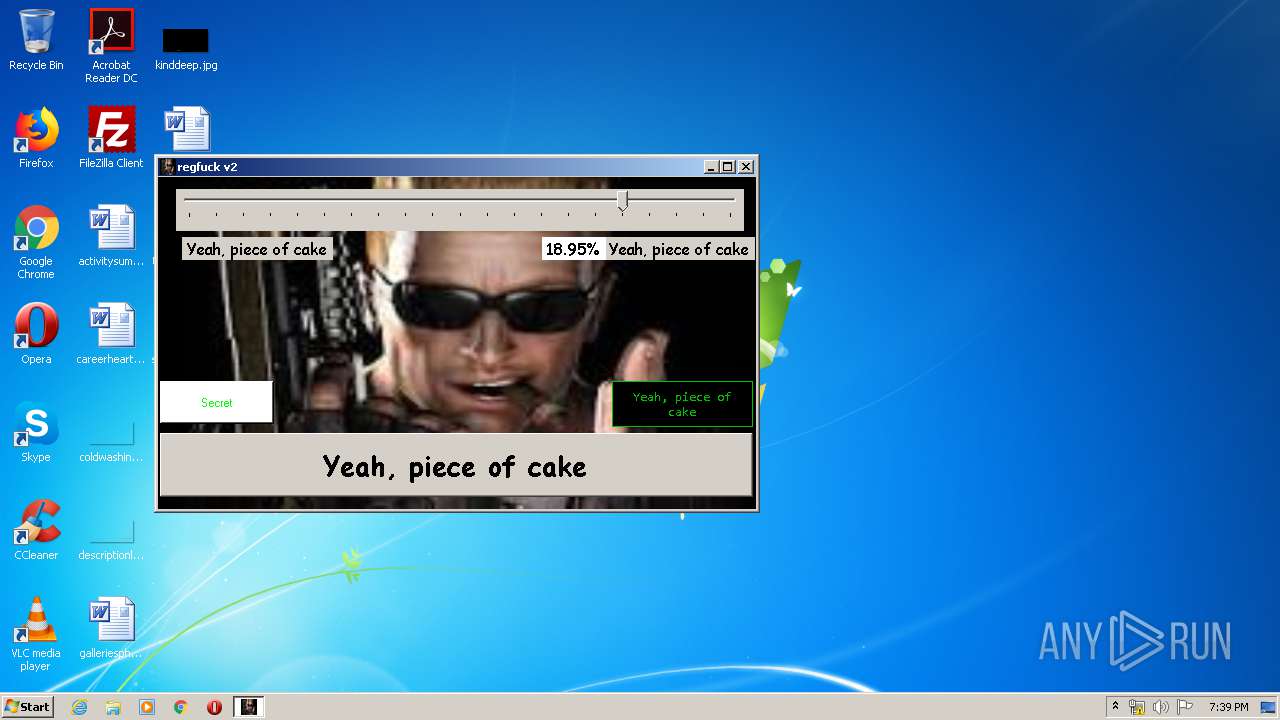
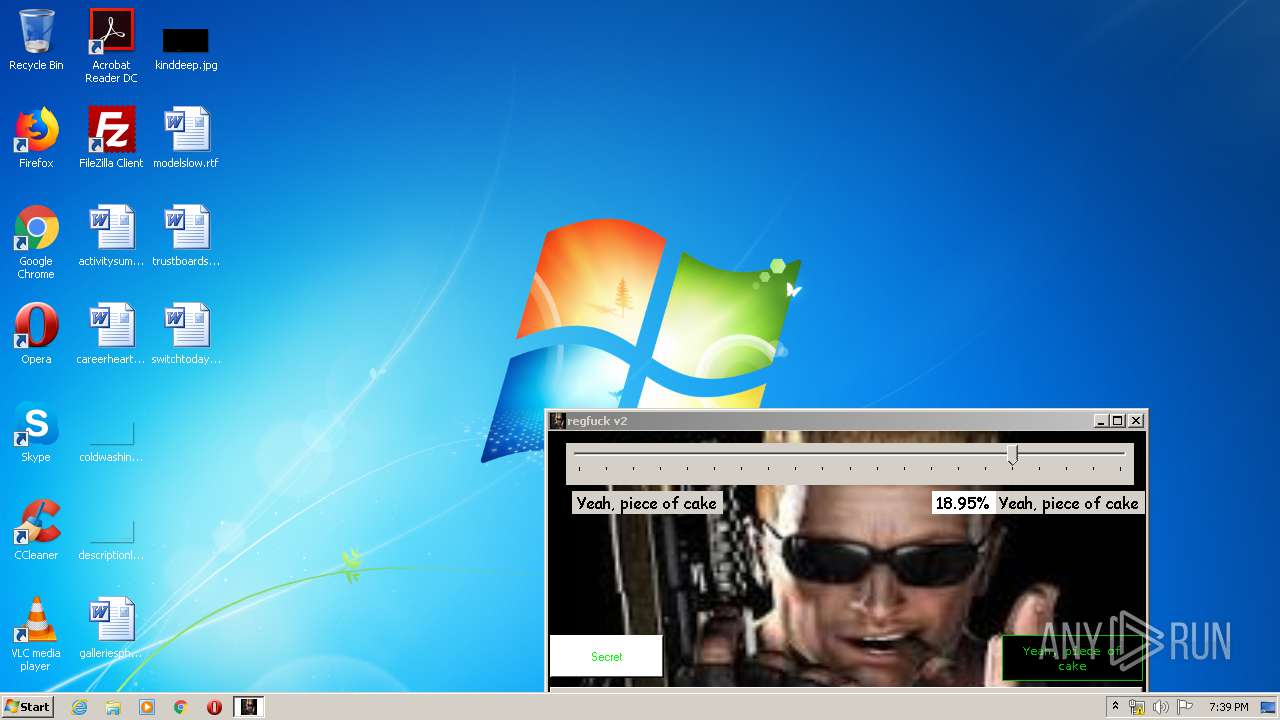
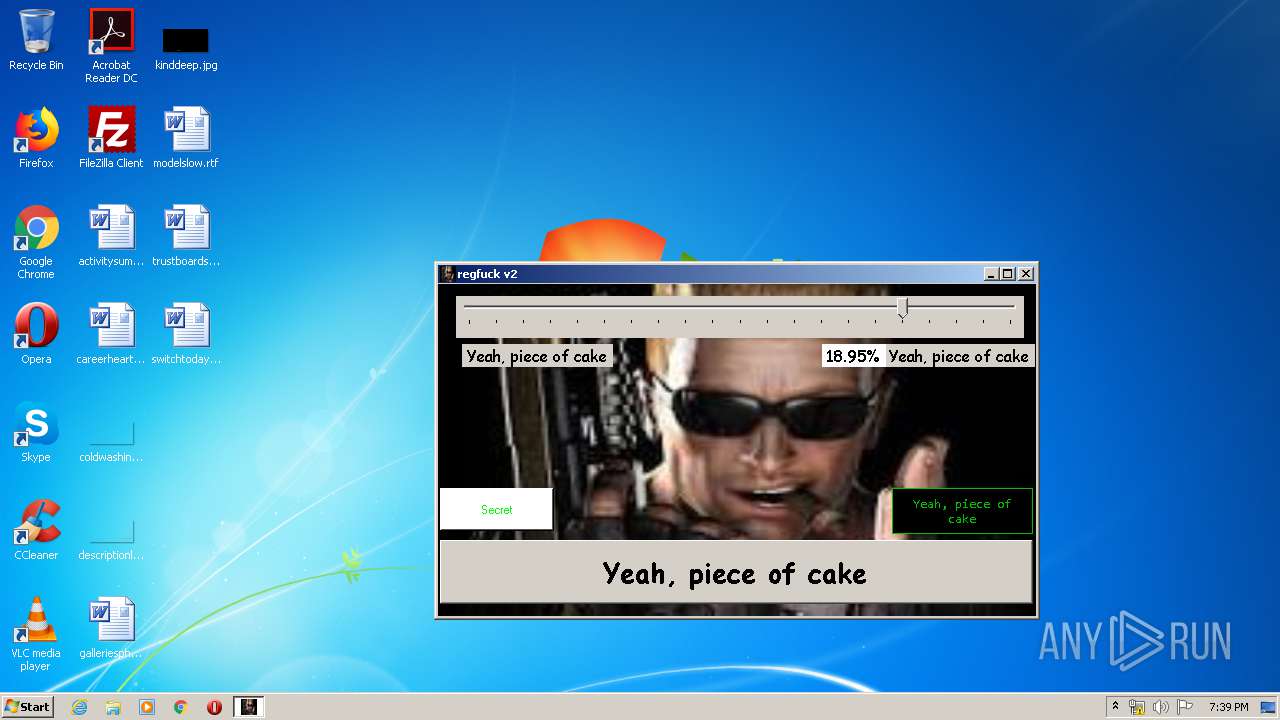
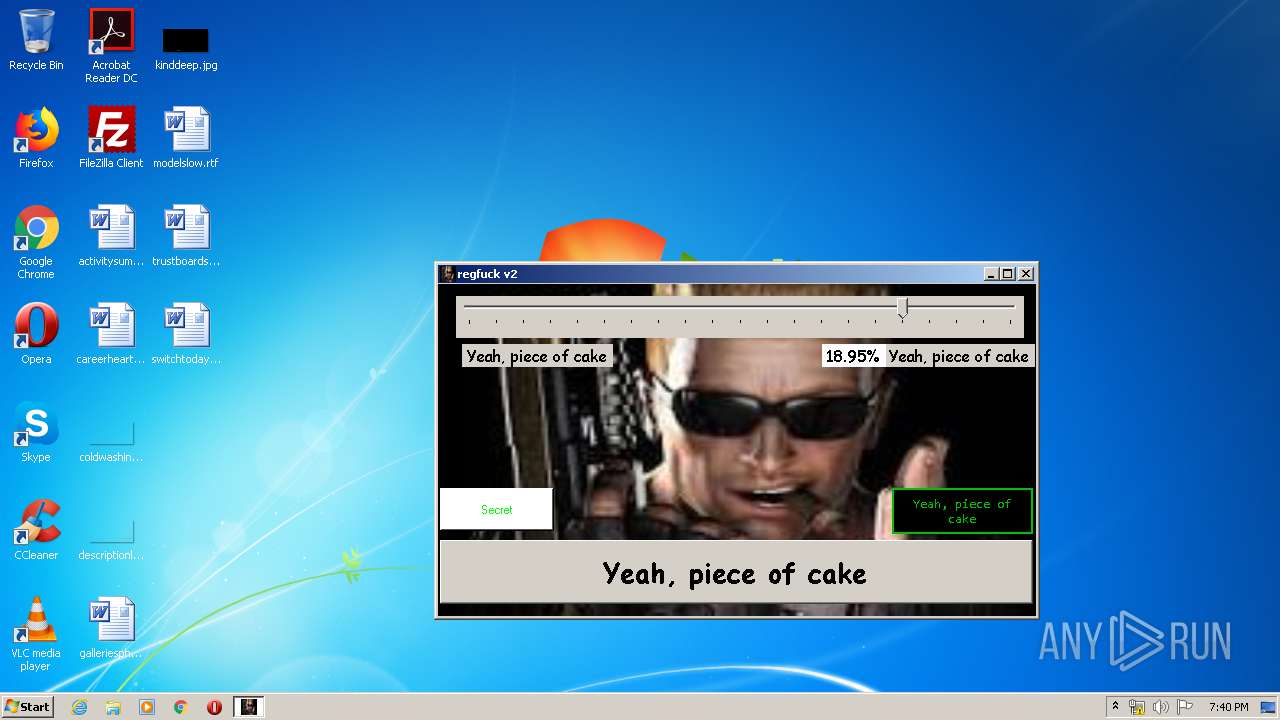
| File name: | RegFuck.exe |
| Full analysis: | https://app.any.run/tasks/a744e96a-57e1-48c0-b0fd-f4a42952fa6b |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 18:39:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | ECC4B8967214D3F4FB4C54D7B4C57B09 |
| SHA1: | AD1C1A70B1DCF88A917B8B10A00A9C200998868F |
| SHA256: | E33DADB8D39F0F25E92DCB9F0FC0413D98D9F06C4E4C5B815109E42B3AF660E4 |
| SSDEEP: | 98304:7Pusy0091Phpbcxgl6gs0VcVXqPsTm/lp:zPy0aWgl6gwaPMe |
MALICIOUS
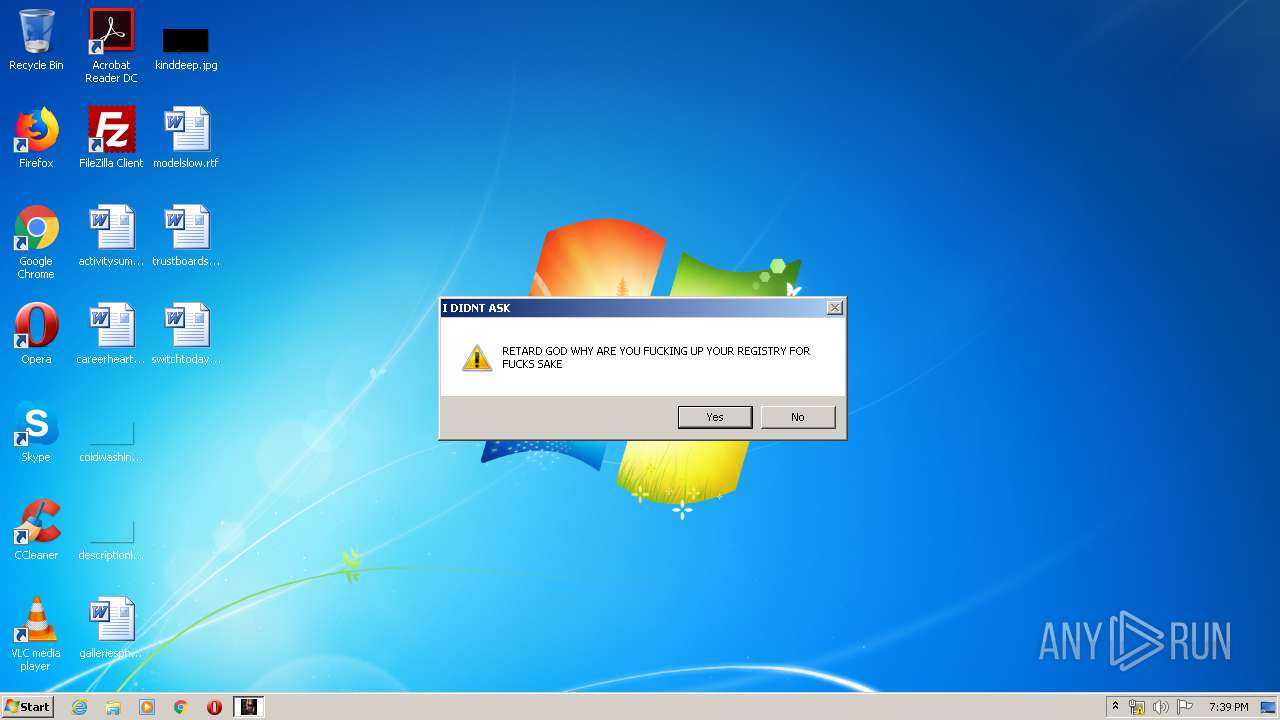
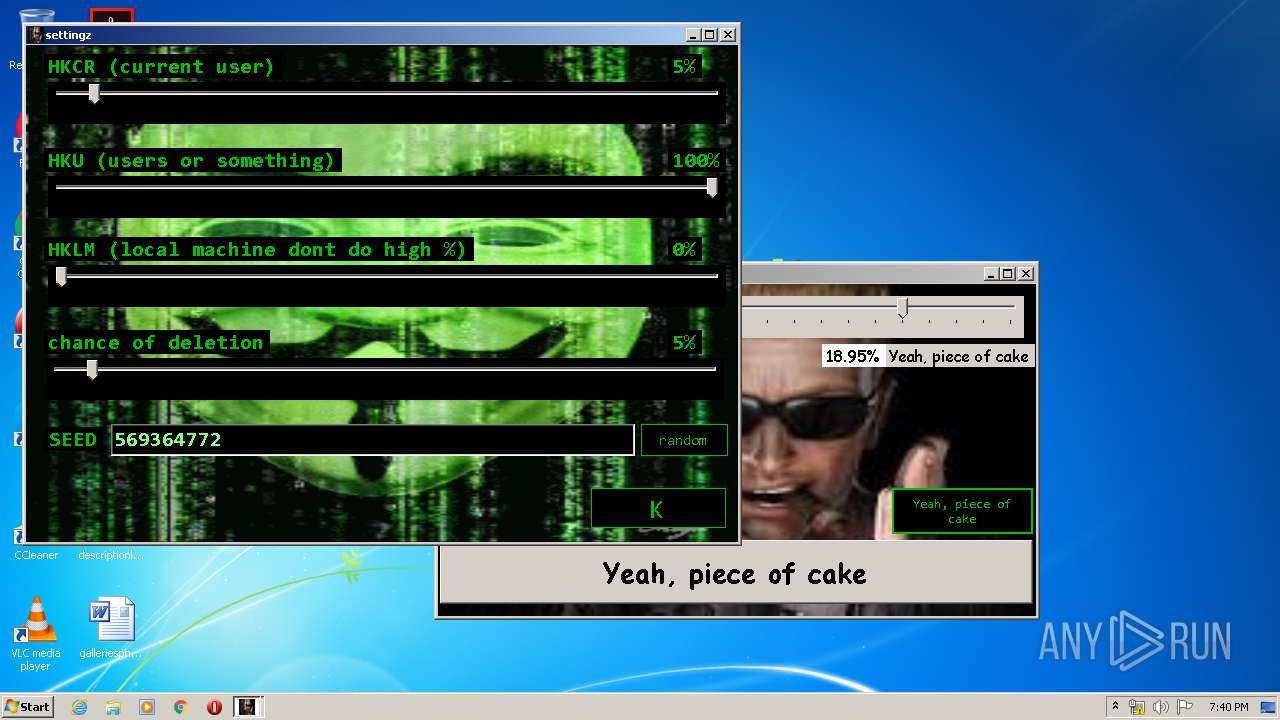
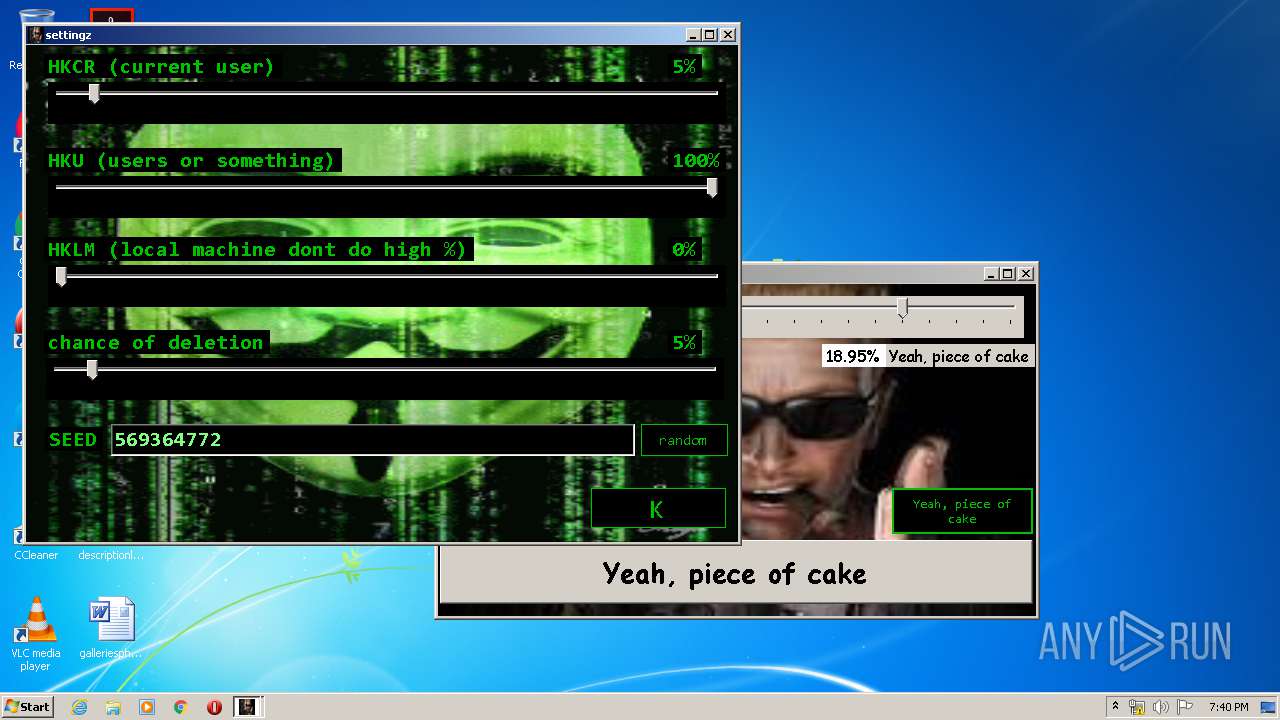
Changes AppInit_DLLs value (autorun option)
- RegFuck.exe (PID: 3700)
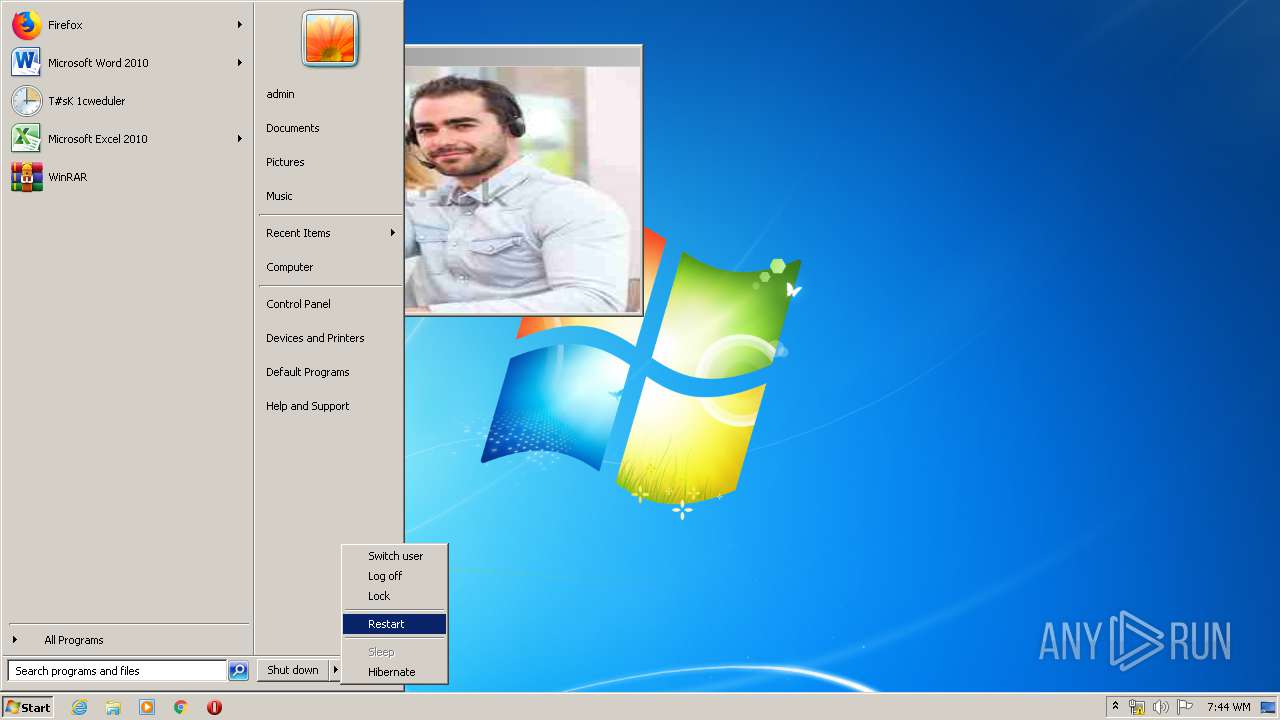
Changes the login/logoff helper path in the registry
- RegFuck.exe (PID: 3700)
Changes appearance of the explorer extensions
- RegFuck.exe (PID: 3700)
Changes Windows auto-update feature
- RegFuck.exe (PID: 3700)
Disables Windows Defender
- RegFuck.exe (PID: 3700)
Changes Windows Error Reporting flag
- RegFuck.exe (PID: 3700)
Changes the autorun value in the registry
- RegFuck.exe (PID: 3700)
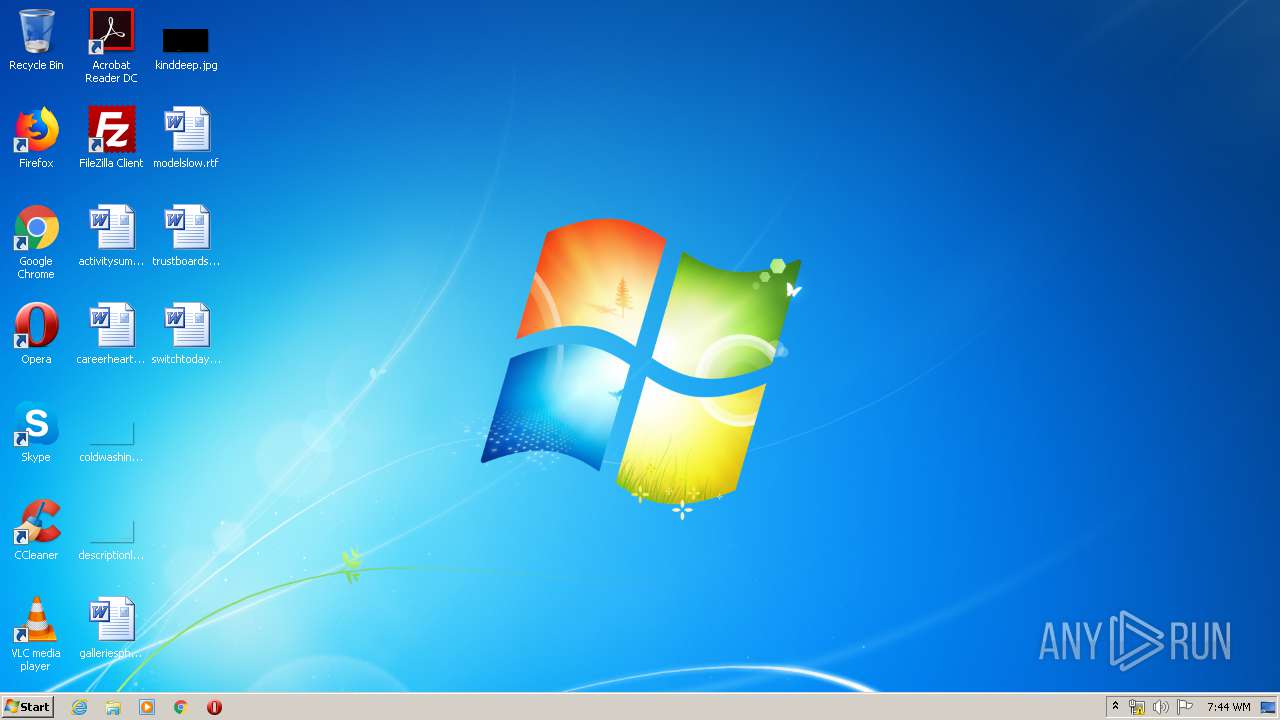
Changes the Startup folder
- RegFuck.exe (PID: 3700)
Modifies Windows security services settings
- RegFuck.exe (PID: 3700)
Changes firewall settings
- RegFuck.exe (PID: 3700)
Modifies Windows Defender service settings
- RegFuck.exe (PID: 3700)
Changes internet zones settings
- RegFuck.exe (PID: 3700)
SUSPICIOUS
Disables SEHOP
- RegFuck.exe (PID: 3700)
Changes the started page of IE
- RegFuck.exe (PID: 3700)
Reads default file associations for system extensions
- RegFuck.exe (PID: 3700)
Modifies the phishing filter of IE
- RegFuck.exe (PID: 3700)
Changes IE settings (feature browser emulation)
- RegFuck.exe (PID: 3700)
Searches for installed software
- RegFuck.exe (PID: 3700)
Reads Windows Product ID
- RegFuck.exe (PID: 3700)
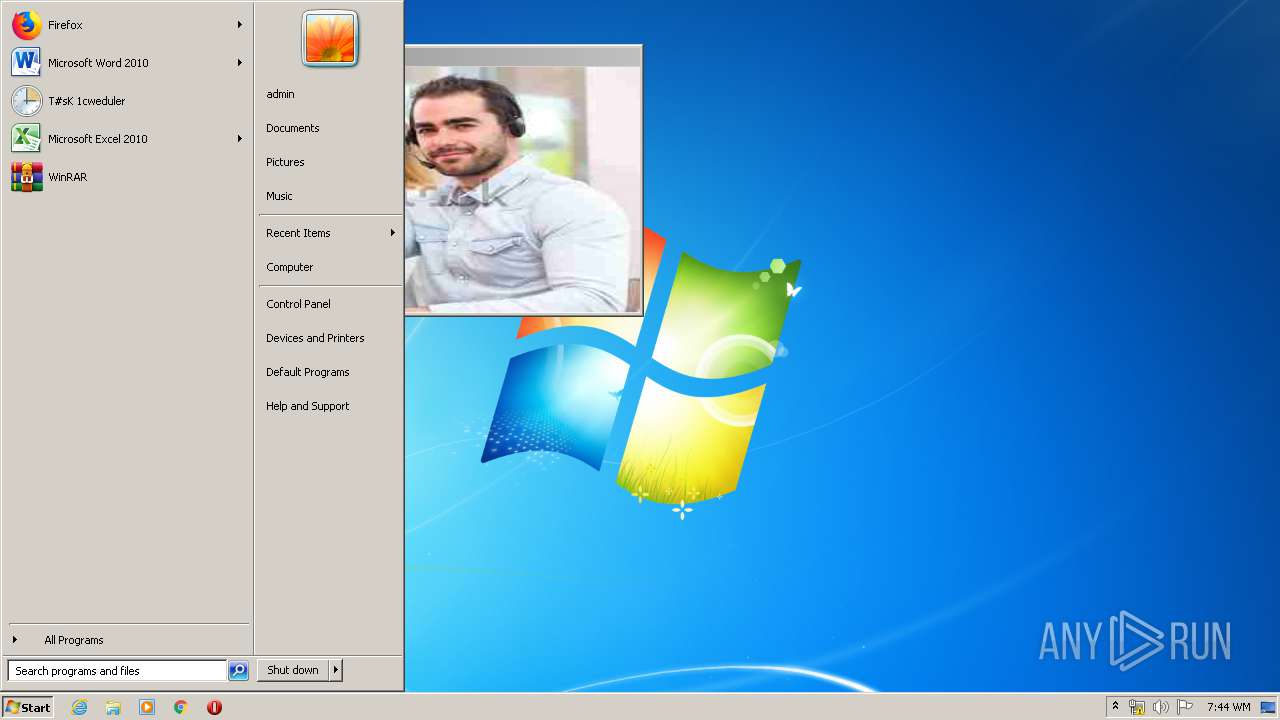
Changes the desktop background image
- RegFuck.exe (PID: 3700)
Modifies the open verb of a shell class
- RegFuck.exe (PID: 3700)
Creates a software uninstall entry
- RegFuck.exe (PID: 3700)
Creates COM task schedule object
- RegFuck.exe (PID: 3700)
Creates or modifies windows services
- RegFuck.exe (PID: 3700)
INFO
Reads Microsoft Office registry keys
- RegFuck.exe (PID: 3700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| AssemblyVersion: | 9.9.9.9 |
|---|---|
| ProductVersion: | 1.3.0.0 |
| ProductName: | RegFuck |
| OriginalFileName: | RegFuck.exe |
| LegalCopyright: | copyrigt 2020 :tm: |
| InternalName: | RegFuck.exe |
| FileVersion: | 1.3.0.0 |
| FileDescription: | retard racing |
| Comments: | tool to corrupt your ass |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.3.0.0 |
| FileVersionNumber: | 1.3.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x3b2a1e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 116736 |
| CodeSize: | 3869696 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2020:03:21 23:58:17+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Mar-2020 22:58:17 |
| Debug artifacts: |
|
| Comments: | tool to corrupt your ass |
| FileDescription: | retard racing |
| FileVersion: | 1.3.0.0 |
| InternalName: | RegFuck.exe |
| LegalCopyright: | copyrigt 2020 :tm: |
| OriginalFilename: | RegFuck.exe |
| ProductName: | RegFuck |
| ProductVersion: | 1.3.0.0 |
| Assembly Version: | 9.9.9.9 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 21-Mar-2020 22:58:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x003B0A24 | 0x003B0C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.84596 |
.rsrc | 0x003B4000 | 0x0001C588 | 0x0001C600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.61572 |
.reloc | 0x003D2000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92092 | 474 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.53953 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.63918 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.69496 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.67387 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.59012 | 96808 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.91268 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
43
Monitored processes
2
Malicious processes
1
Suspicious processes
0
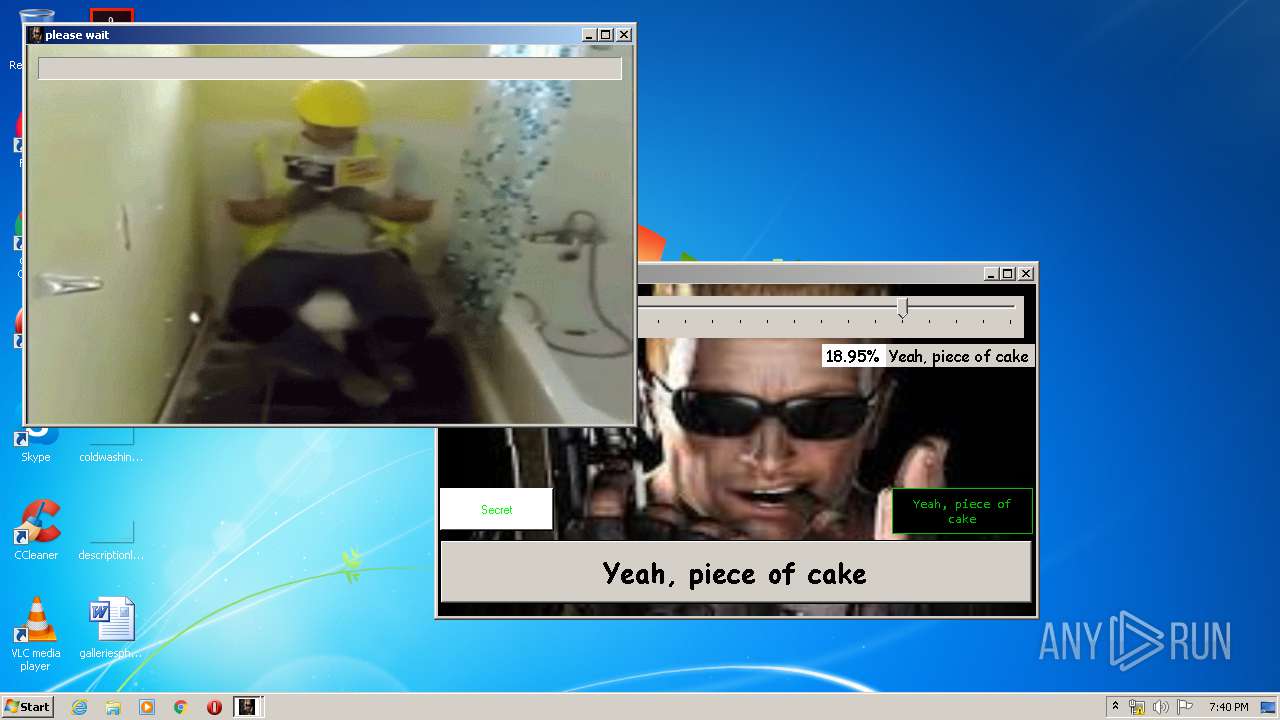
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2660 | "C:\Users\admin\AppData\Local\Temp\RegFuck.exe" | C:\Users\admin\AppData\Local\Temp\RegFuck.exe | — | explorer.exe |
User: admin Integrity Level: MEDIUM Description: retard racing Exit code: 3221226540 Version: 1.3.0.0 | ||||
| 3700 | "C:\Users\admin\AppData\Local\Temp\RegFuck.exe" | C:\Users\admin\AppData\Local\Temp\RegFuck.exe | explorer.exe | |
User: admin Integrity Level: HIGH Description: retard racing Version: 1.3.0.0 | ||||
Total events
335 273
Read events
4 561
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report