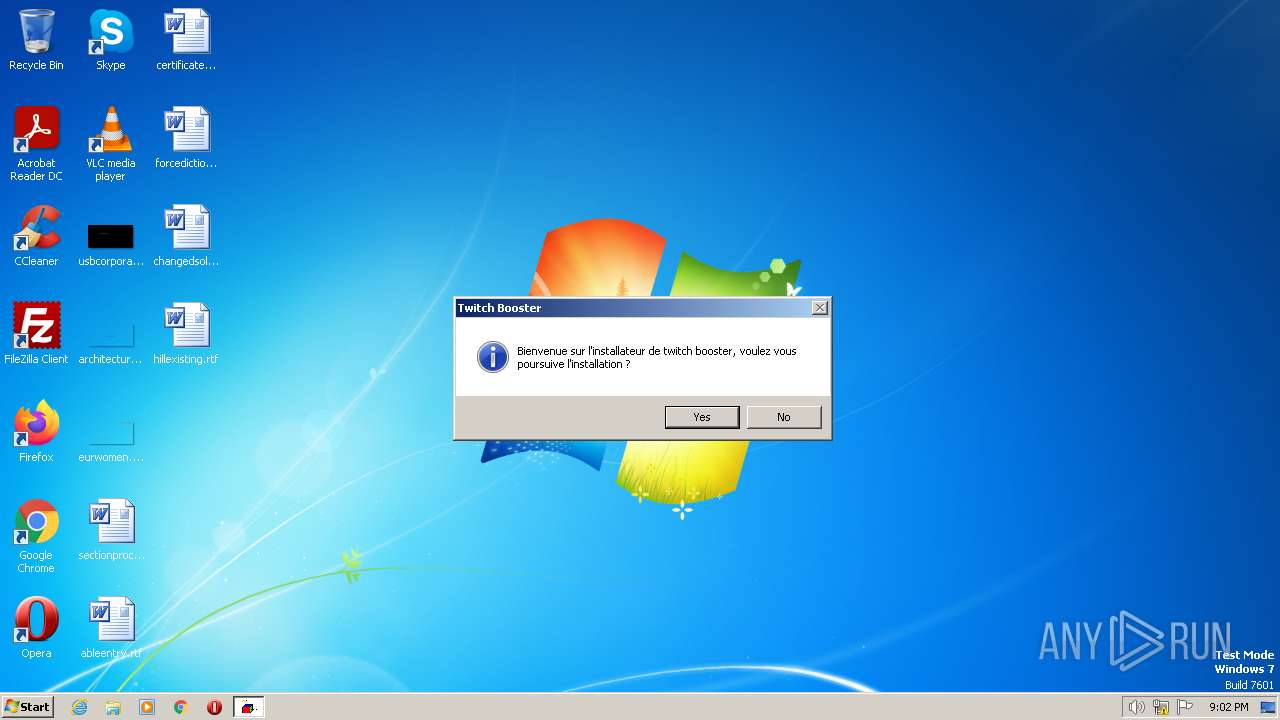
| File name: | Twitch Booster by back v6 cactus.exe |
| Full analysis: | https://app.any.run/tasks/b7387ae6-2742-4d42-adef-b32261c99493 |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2023, 20:02:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B9CD9A717A3C8617A23575C8A172986E |
| SHA1: | 7FDEA9E41445E7997E785C5421CF5343255825E1 |
| SHA256: | E32615F5E1F4381F14A6BB9C776B8ABF2A63E90FD9EF08472568EC09CBB6F1A6 |
| SSDEEP: | 49152:yJRT3FWaXWRhWG7Mpzr36AedKbh4el7s2Hsrn5XTW5IYcKm+K:gRT3qRQG7Mp+YxZGYF8 |
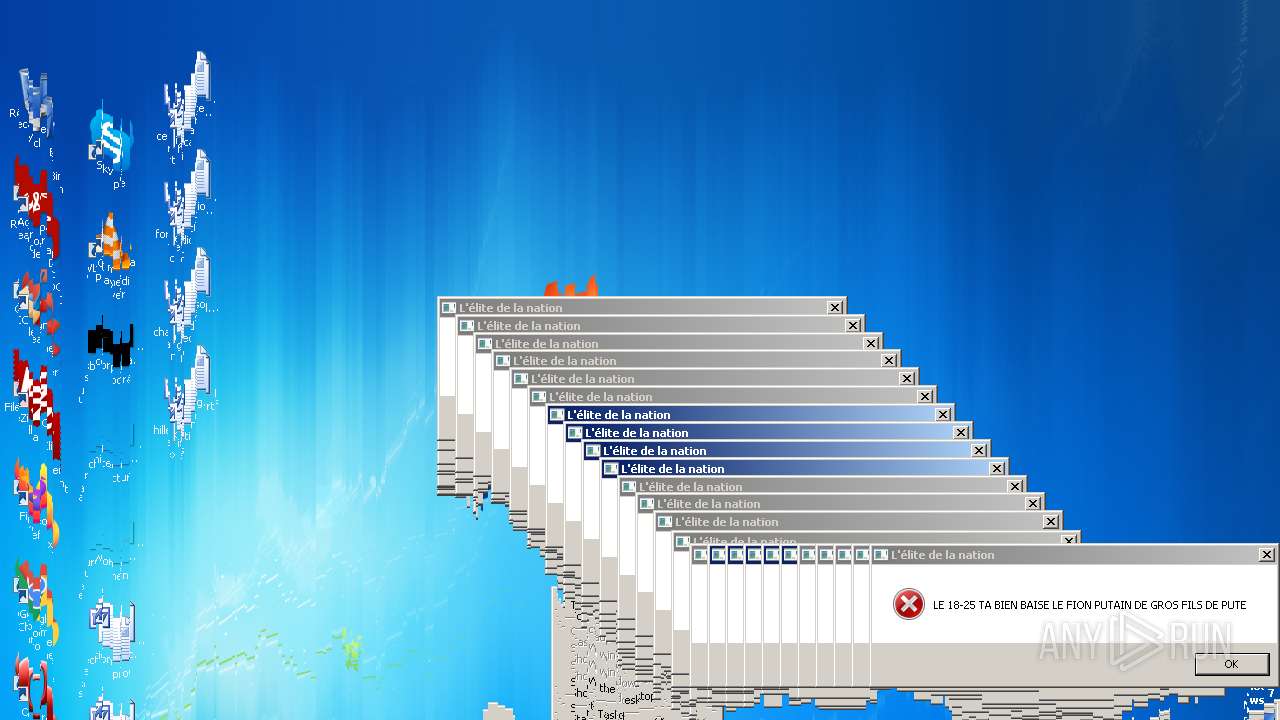
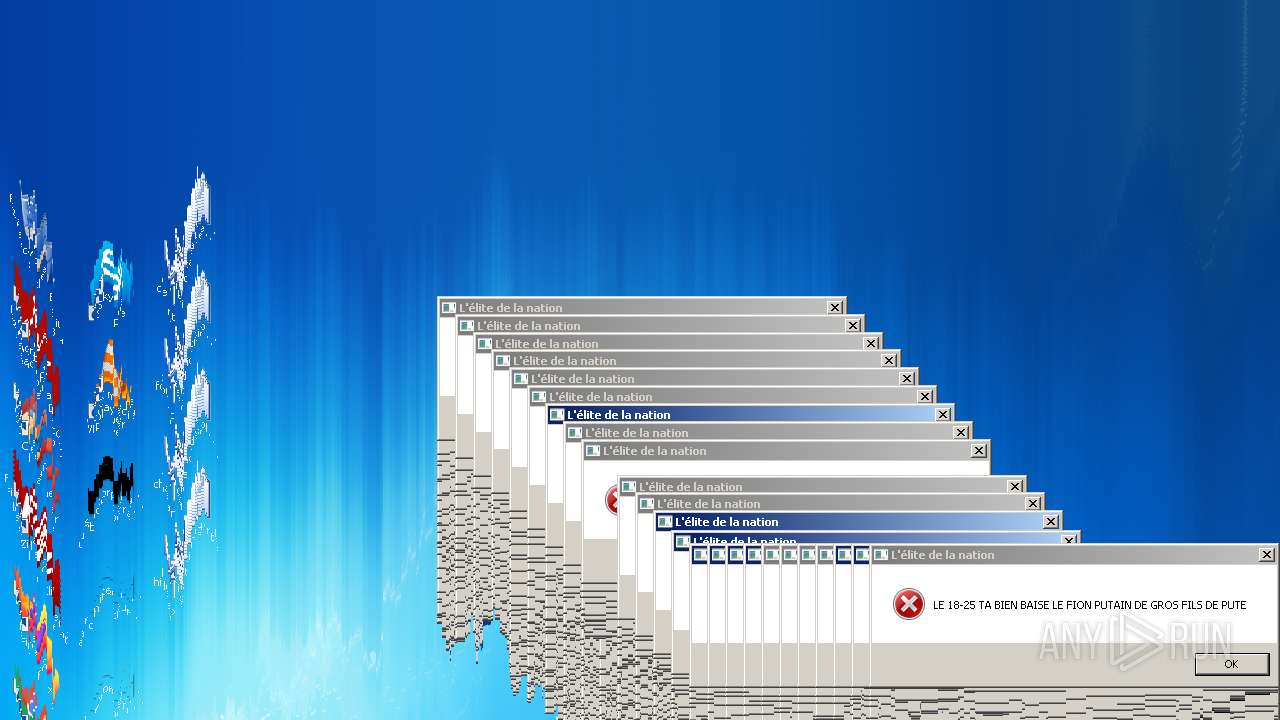
MALICIOUS
No malicious indicators.SUSPICIOUS
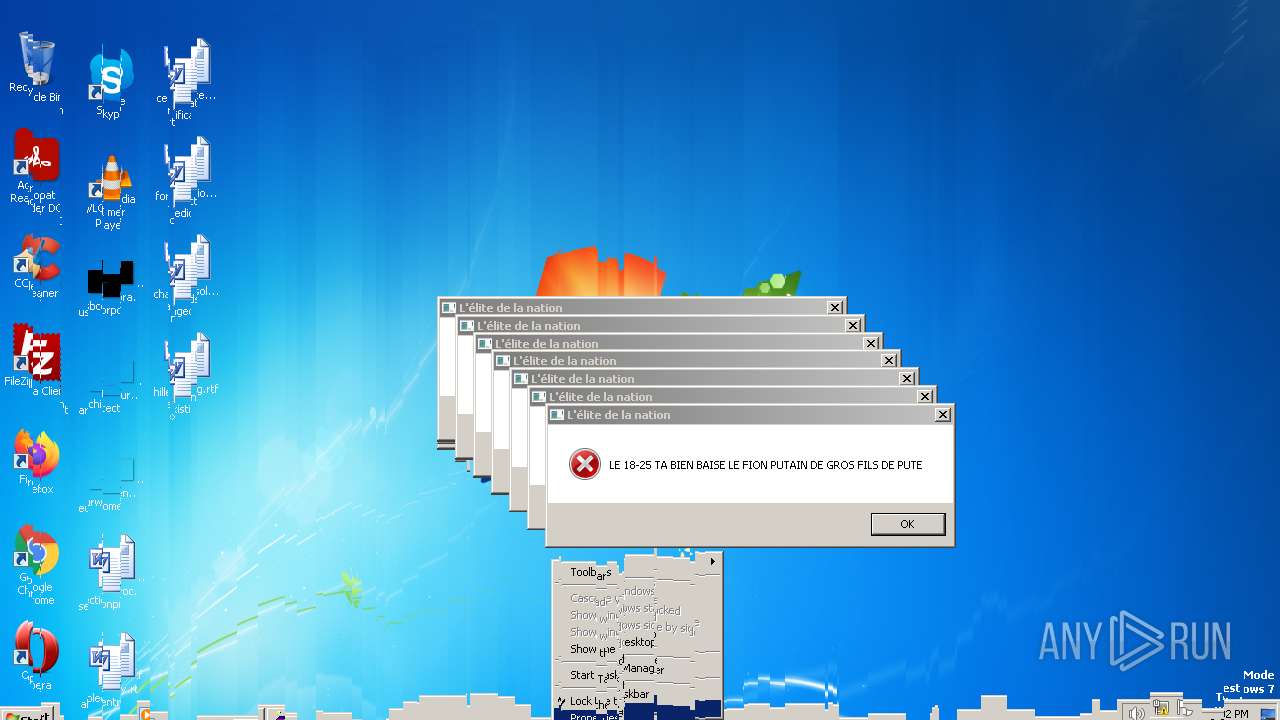
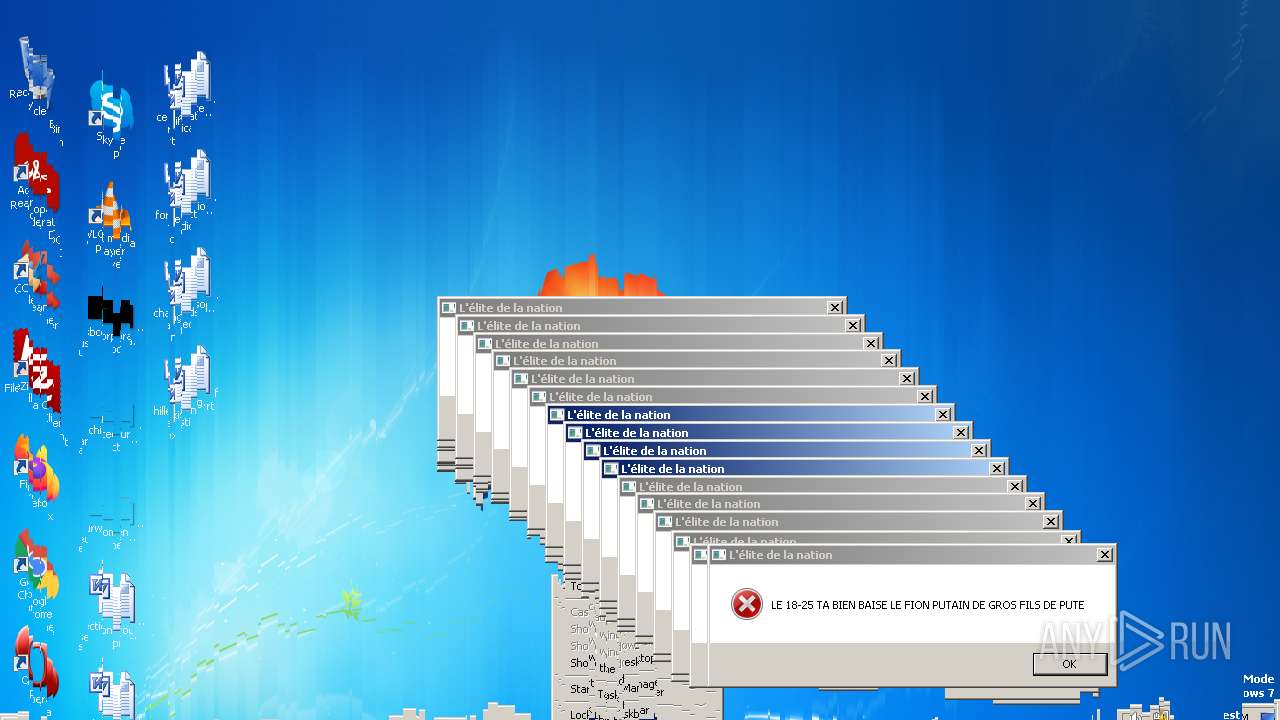
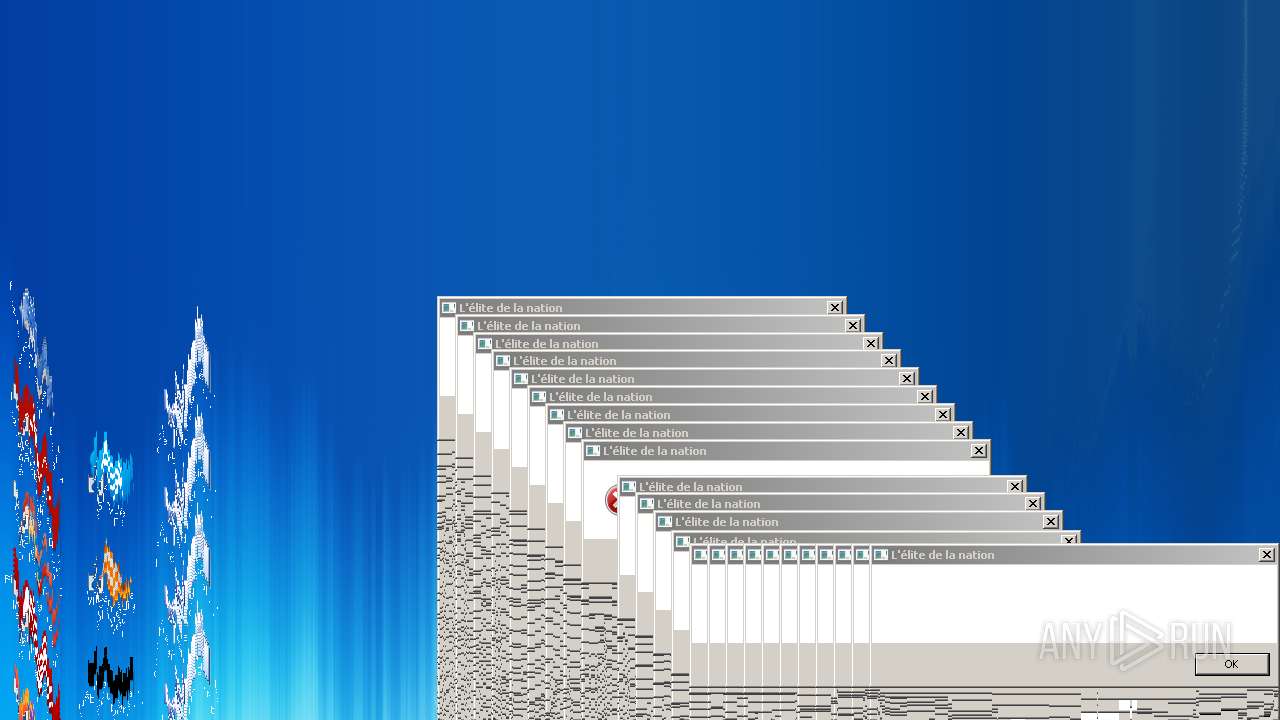
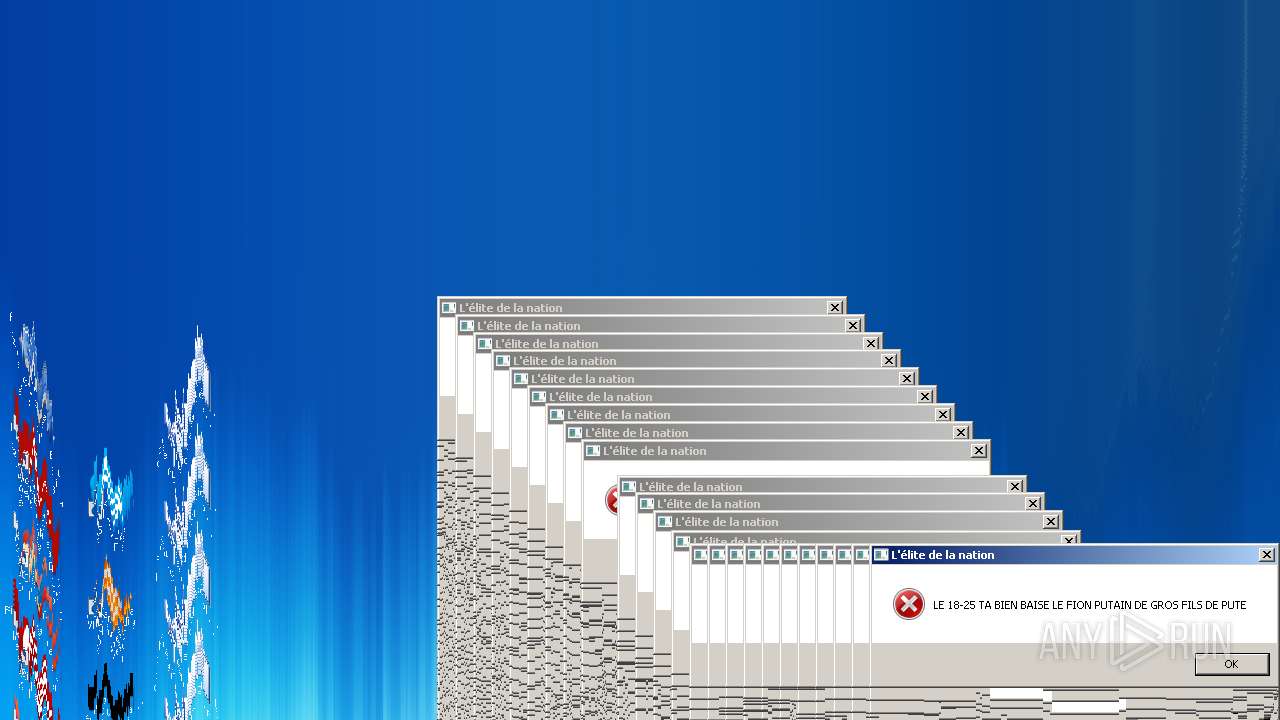
Application launched itself
- wscript.exe (PID: 1396)
- wscript.exe (PID: 3660)
- wscript.exe (PID: 1912)
- wscript.exe (PID: 3740)
- wscript.exe (PID: 2040)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 1368)
- wscript.exe (PID: 3056)
- wscript.exe (PID: 3428)
- wscript.exe (PID: 796)
- wscript.exe (PID: 276)
- wscript.exe (PID: 3160)
- wscript.exe (PID: 3652)
- wscript.exe (PID: 956)
- wscript.exe (PID: 1432)
- wscript.exe (PID: 3572)
- wscript.exe (PID: 2036)
- wscript.exe (PID: 1284)
- wscript.exe (PID: 2592)
- wscript.exe (PID: 2088)
- wscript.exe (PID: 1648)
- wscript.exe (PID: 116)
- wscript.exe (PID: 2628)
- wscript.exe (PID: 2764)
- wscript.exe (PID: 3144)
- wscript.exe (PID: 3944)
- wscript.exe (PID: 2060)
- wscript.exe (PID: 872)
- wscript.exe (PID: 3432)
- wscript.exe (PID: 2476)
- wscript.exe (PID: 976)
- wscript.exe (PID: 3872)
- wscript.exe (PID: 448)
- wscript.exe (PID: 1832)
- wscript.exe (PID: 1428)
- wscript.exe (PID: 2144)
- wscript.exe (PID: 3732)
- wscript.exe (PID: 2520)
- wscript.exe (PID: 3584)
- wscript.exe (PID: 3972)
- wscript.exe (PID: 3072)
- wscript.exe (PID: 940)
- wscript.exe (PID: 372)
- wscript.exe (PID: 868)
- wscript.exe (PID: 784)
- wscript.exe (PID: 1852)
- wscript.exe (PID: 3512)
- wscript.exe (PID: 2600)
- wscript.exe (PID: 2384)
- wscript.exe (PID: 2952)
- wscript.exe (PID: 2504)
- wscript.exe (PID: 1856)
- wscript.exe (PID: 2824)
- wscript.exe (PID: 4272)
- wscript.exe (PID: 4232)
- wscript.exe (PID: 3912)
- wscript.exe (PID: 240)
- wscript.exe (PID: 4872)
- wscript.exe (PID: 5520)
- wscript.exe (PID: 4584)
- wscript.exe (PID: 6024)
- wscript.exe (PID: 6112)
- wscript.exe (PID: 4704)
- wscript.exe (PID: 4832)
- wscript.exe (PID: 5408)
- wscript.exe (PID: 5960)
- wscript.exe (PID: 4576)
- wscript.exe (PID: 5404)
- wscript.exe (PID: 4728)
- wscript.exe (PID: 5312)
- wscript.exe (PID: 6092)
- wscript.exe (PID: 5264)
- wscript.exe (PID: 5376)
- wscript.exe (PID: 5728)
- wscript.exe (PID: 4860)
- wscript.exe (PID: 5704)
- wscript.exe (PID: 4456)
- wscript.exe (PID: 5444)
- wscript.exe (PID: 4628)
- wscript.exe (PID: 5588)
- wscript.exe (PID: 6108)
- wscript.exe (PID: 4848)
- wscript.exe (PID: 4304)
- wscript.exe (PID: 5352)
- wscript.exe (PID: 4364)
- wscript.exe (PID: 4448)
- wscript.exe (PID: 5392)
- wscript.exe (PID: 5640)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 4424)
- wscript.exe (PID: 5456)
- wscript.exe (PID: 4696)
- wscript.exe (PID: 5756)
- wscript.exe (PID: 5008)
- wscript.exe (PID: 4216)
- wscript.exe (PID: 4864)
- wscript.exe (PID: 5812)
- wscript.exe (PID: 5504)
- wscript.exe (PID: 4508)
- wscript.exe (PID: 5268)
- wscript.exe (PID: 4540)
- wscript.exe (PID: 5288)
- wscript.exe (PID: 4720)
- wscript.exe (PID: 5336)
- wscript.exe (PID: 5360)
- wscript.exe (PID: 4300)
- wscript.exe (PID: 6020)
- wscript.exe (PID: 5628)
- wscript.exe (PID: 4676)
- wscript.exe (PID: 6292)
- wscript.exe (PID: 6080)
- wscript.exe (PID: 4320)
- wscript.exe (PID: 5888)
- wscript.exe (PID: 7892)
- wscript.exe (PID: 7652)
- wscript.exe (PID: 7672)
- wscript.exe (PID: 6892)
- wscript.exe (PID: 5980)
The process executes VB scripts
- wscript.exe (PID: 1396)
- Twitch Booster by back v6 cactus.exe (PID: 3960)
- wscript.exe (PID: 3660)
- wscript.exe (PID: 1912)
- wscript.exe (PID: 3740)
- wscript.exe (PID: 2040)
- wscript.exe (PID: 3056)
- wscript.exe (PID: 3428)
- wscript.exe (PID: 796)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 1368)
- wscript.exe (PID: 276)
- wscript.exe (PID: 3652)
- wscript.exe (PID: 956)
- wscript.exe (PID: 1432)
- wscript.exe (PID: 3160)
- wscript.exe (PID: 3572)
- wscript.exe (PID: 2036)
- wscript.exe (PID: 2592)
- wscript.exe (PID: 2088)
- wscript.exe (PID: 1284)
- wscript.exe (PID: 116)
- wscript.exe (PID: 2628)
- wscript.exe (PID: 2764)
- wscript.exe (PID: 3144)
- wscript.exe (PID: 1648)
- wscript.exe (PID: 3944)
- wscript.exe (PID: 872)
- wscript.exe (PID: 2060)
- wscript.exe (PID: 3432)
- wscript.exe (PID: 2476)
- wscript.exe (PID: 976)
- wscript.exe (PID: 3872)
- wscript.exe (PID: 448)
- wscript.exe (PID: 2144)
- wscript.exe (PID: 3512)
- wscript.exe (PID: 3584)
- wscript.exe (PID: 1428)
- wscript.exe (PID: 3732)
- wscript.exe (PID: 2520)
- wscript.exe (PID: 1832)
- wscript.exe (PID: 372)
- wscript.exe (PID: 784)
- wscript.exe (PID: 940)
- wscript.exe (PID: 1852)
- wscript.exe (PID: 2600)
- wscript.exe (PID: 3972)
- wscript.exe (PID: 3072)
- wscript.exe (PID: 868)
- wscript.exe (PID: 2952)
- wscript.exe (PID: 2504)
- wscript.exe (PID: 1856)
- wscript.exe (PID: 4272)
- wscript.exe (PID: 3912)
- wscript.exe (PID: 240)
- wscript.exe (PID: 2384)
- wscript.exe (PID: 2824)
- wscript.exe (PID: 4872)
- wscript.exe (PID: 5408)
- wscript.exe (PID: 5520)
- wscript.exe (PID: 6112)
- wscript.exe (PID: 4704)
- wscript.exe (PID: 4584)
- wscript.exe (PID: 5264)
- wscript.exe (PID: 4232)
- wscript.exe (PID: 4832)
- wscript.exe (PID: 6024)
- wscript.exe (PID: 5980)
- wscript.exe (PID: 5960)
- wscript.exe (PID: 5404)
- wscript.exe (PID: 4728)
- wscript.exe (PID: 5312)
- wscript.exe (PID: 6092)
- wscript.exe (PID: 5376)
- wscript.exe (PID: 4576)
- wscript.exe (PID: 4860)
- wscript.exe (PID: 5728)
- wscript.exe (PID: 4456)
- wscript.exe (PID: 4628)
- wscript.exe (PID: 5444)
- wscript.exe (PID: 5588)
- wscript.exe (PID: 6108)
- wscript.exe (PID: 4848)
- wscript.exe (PID: 5704)
- wscript.exe (PID: 4424)
- wscript.exe (PID: 4304)
- wscript.exe (PID: 5352)
- wscript.exe (PID: 5456)
- wscript.exe (PID: 4448)
- wscript.exe (PID: 4364)
- wscript.exe (PID: 5392)
- wscript.exe (PID: 4696)
- wscript.exe (PID: 5640)
- wscript.exe (PID: 5052)
- wscript.exe (PID: 5756)
- wscript.exe (PID: 5008)
- wscript.exe (PID: 5812)
- wscript.exe (PID: 4864)
- wscript.exe (PID: 4508)
- wscript.exe (PID: 5504)
- wscript.exe (PID: 5268)
- wscript.exe (PID: 4216)
- wscript.exe (PID: 6020)
- wscript.exe (PID: 4540)
- wscript.exe (PID: 5288)
- wscript.exe (PID: 5360)
- wscript.exe (PID: 4300)
- wscript.exe (PID: 4720)
- wscript.exe (PID: 5888)
- wscript.exe (PID: 4676)
- wscript.exe (PID: 6292)
- wscript.exe (PID: 5336)
- wscript.exe (PID: 6080)
- wscript.exe (PID: 4320)
- wscript.exe (PID: 5628)
- wscript.exe (PID: 7892)
- wscript.exe (PID: 6892)
- wscript.exe (PID: 7652)
- wscript.exe (PID: 7672)
Reads the Internet Settings
- wscript.exe (PID: 1396)
- Twitch Booster by back v6 cactus.exe (PID: 3960)
- wscript.exe (PID: 3636)
- wscript.exe (PID: 2824)
- wscript.exe (PID: 1912)
- wscript.exe (PID: 3740)
- wscript.exe (PID: 2040)
- wscript.exe (PID: 3672)
- wscript.exe (PID: 3660)
- wscript.exe (PID: 1368)
- wscript.exe (PID: 3056)
- wscript.exe (PID: 3428)
- wscript.exe (PID: 796)
- wscript.exe (PID: 1036)
- wscript.exe (PID: 3160)
- wscript.exe (PID: 2592)
- wscript.exe (PID: 956)
- wscript.exe (PID: 1432)
- wscript.exe (PID: 276)
- wscript.exe (PID: 3652)
- wscript.exe (PID: 3572)
- wscript.exe (PID: 2036)
- wscript.exe (PID: 1284)
- wscript.exe (PID: 2764)
- wscript.exe (PID: 2088)
- wscript.exe (PID: 1648)
- wscript.exe (PID: 2628)
- wscript.exe (PID: 3944)
- wscript.exe (PID: 3144)
- wscript.exe (PID: 116)
- wscript.exe (PID: 2476)
- wscript.exe (PID: 2060)
- wscript.exe (PID: 872)
- wscript.exe (PID: 3432)
- wscript.exe (PID: 3732)
- wscript.exe (PID: 2144)
- wscript.exe (PID: 976)
- wscript.exe (PID: 3872)
- wscript.exe (PID: 448)
- wscript.exe (PID: 1428)
- wscript.exe (PID: 2520)
- wscript.exe (PID: 1832)
- wscript.exe (PID: 3584)
Executable content was dropped or overwritten
- Twitch Booster by back v6 cactus.exe (PID: 3960)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3636)
- wscript.exe (PID: 2824)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 3544)
Executing commands from a ".bat" file
- wscript.exe (PID: 3636)
- wscript.exe (PID: 2824)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3544)
- cmd.exe (PID: 4068)
INFO
Reads the computer name
- Twitch Booster by back v6 cactus.exe (PID: 3960)
The process checks LSA protection
- Twitch Booster by back v6 cactus.exe (PID: 3960)
- taskkill.exe (PID: 124)
- taskkill.exe (PID: 1092)
- taskkill.exe (PID: 276)
- taskkill.exe (PID: 1972)
Create files in a temporary directory
- Twitch Booster by back v6 cactus.exe (PID: 3960)
Checks supported languages
- Twitch Booster by back v6 cactus.exe (PID: 3960)
- extension6.exe (PID: 2968)
Checks proxy server information
- wscript.exe (PID: 3672)
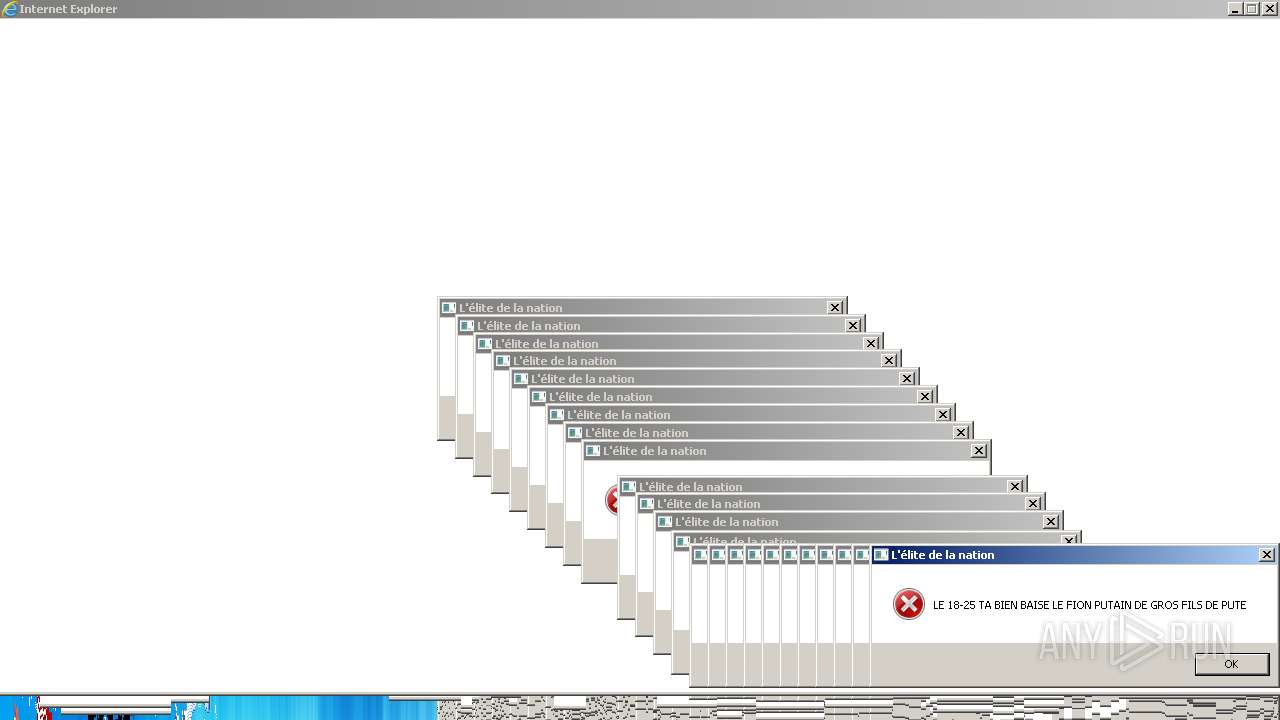
Application launched itself
- iexplore.exe (PID: 4664)
- iexplore.exe (PID: 4916)
- iexplore.exe (PID: 7116)
- iexplore.exe (PID: 6664)
- iexplore.exe (PID: 6232)
- iexplore.exe (PID: 6868)
- iexplore.exe (PID: 6444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1cab5 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 132096 |
| CodeSize: | 188416 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2016:08:14 19:15:49+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2016 19:15:49 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2016 19:15:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DFE8 | 0x0002E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71025 |
.rdata | 0x0002F000 | 0x000099D0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15287 |
.data | 0x00039000 | 0x0001F8B8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29547 |
.gfids | 0x00059000 | 0x000000F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12367 |
.rsrc | 0x0005A000 | 0x00013BA8 | 0x00013C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.38486 |
.reloc | 0x0006E000 | 0x00001F8C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.15447 | 494 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 2.95673 | 288 | Latin 1 / Western European | English - United States | RT_STRING |
14 | 2.77928 | 186 | Latin 1 / Western European | English - United States | RT_STRING |
15 | 2.83619 | 188 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
192
Monitored processes
155
Malicious processes
44
Suspicious processes
74
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\extension3.vbs" | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | |||||||||||||||
| 124 | taskkill /f /IM chrome.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 240 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\extension3.vbs" | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | |||||||||||||||
| 276 | taskkill /f /IM javaw.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 276 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\extension3.vbs" | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 372 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\extension3.vbs" | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | |||||||||||||||
| 448 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\extension3.vbs" | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | |||||||||||||||
| 784 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\extension3.vbs" | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | |||||||||||||||
| 796 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\extension3.vbs" | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 844 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\660.vbs" | C:\Windows\System32\wscript.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
38 166
Read events
37 770
Write events
394
Delete events
2
Modification events
| (PID) Process: | (3960) Twitch Booster by back v6 cactus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3960) Twitch Booster by back v6 cactus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3960) Twitch Booster by back v6 cactus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3960) Twitch Booster by back v6 cactus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1396) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1396) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1396) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1396) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (844) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} |
| Operation: | write | Name: | CLSID |
Value: {A8C680EB-3D32-11D2-9EE7-00C04F797396} | |||
| (PID) Process: | (844) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} |
| Operation: | write | Name: | DeviceName |
Value: Speakers (Realtek AC'97 Audio) | |||
Executable files
2
Suspicious files
4
Text files
24
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3960 | Twitch Booster by back v6 cactus.exe | C:\Users\admin\AppData\Local\Temp\TwitchBooster.vbs | text | |
MD5:2EFB51A876C89D1A9ED7D7C78E6269B3 | SHA256:DE37F43A4805404248337FD81BE427A702EA8AAF810C550A1A62E86B64EE832A | |||
| 3960 | Twitch Booster by back v6 cactus.exe | C:\Users\admin\AppData\Local\Temp\extension110.vbs | text | |
MD5:B883B3E1FE111D2C4CA97B90B153AD31 | SHA256:664D1C6B16E13B9B02998379D8835E435E629AD98E6CAAB274259DE2A0DA1EE6 | |||
| 3960 | Twitch Booster by back v6 cactus.exe | C:\Users\admin\AppData\Local\Temp\extension8.bat | text | |
MD5:A575A4815612BCF04F145CBFB0A352FC | SHA256:7C997A87F492E79232A47237DEE7DAB2A52E63B523CF520C5DB191E0CE544FE4 | |||
| 3960 | Twitch Booster by back v6 cactus.exe | C:\Users\admin\AppData\Local\Temp\extension5.vbs | text | |
MD5:643BC2D65DBD09E679FB65600DB3D259 | SHA256:4AC67004F88F757D327EAB80FAACFB3ED1105D662A190E7C03AA8E45C2B30CE6 | |||
| 3960 | Twitch Booster by back v6 cactus.exe | C:\Users\admin\AppData\Local\Temp\extension3.vbs | text | |
MD5:9A8A46120D9D373C5CC1D948DB1DEB8A | SHA256:7C1B0EA0414A81F6A3D294F194DA8B981702F1AE670F6BF435E6C58F789371F5 | |||
| 3960 | Twitch Booster by back v6 cactus.exe | C:\Users\admin\AppData\Local\Temp\4826.vbs | text | |
MD5:E17BD8B5285D5D2FAEF2DC1724240F97 | SHA256:600B23840A42C51411A479AB8053218C161DC5894804A122D9CCE336966CCB14 | |||
| 3960 | Twitch Booster by back v6 cactus.exe | C:\Users\admin\AppData\Local\Temp\7458.vbs | text | |
MD5:0ED13DB1EA0235F371DB35D25368F959 | SHA256:E6FA298F159AAFD799EC7A17606ED0420B181F68D0A13C80B0088D3C14D13FD9 | |||
| 3960 | Twitch Booster by back v6 cactus.exe | C:\Users\admin\AppData\Local\Temp\extension9.vbs | text | |
MD5:19360972F998F406B0C26097D6C16471 | SHA256:EAF0CDD76EFFFE3D643AC378390EDF872F8916510F7BA1791026E0E9A44A382D | |||
| 3960 | Twitch Booster by back v6 cactus.exe | C:\Users\admin\AppData\Local\Temp\extension6.exe | executable | |
MD5:D9BAAC374CC96E41C9F86C669E53F61C | SHA256:A1D883577BCB6C4F9DE47B06FE97C370C09BDDFFB6569B6CF93576371BDBC412 | |||
| 3960 | Twitch Booster by back v6 cactus.exe | C:\Users\admin\AppData\Local\Temp\589.bat | text | |
MD5:088E8BA1E0B96304109908D6DD92903A | SHA256:1D6AEA4D2D84399316B983C8A312C27407063C984DE8B1F1A01B8C58AF6A19A5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3372 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
0xad.net |
| whitelisted |