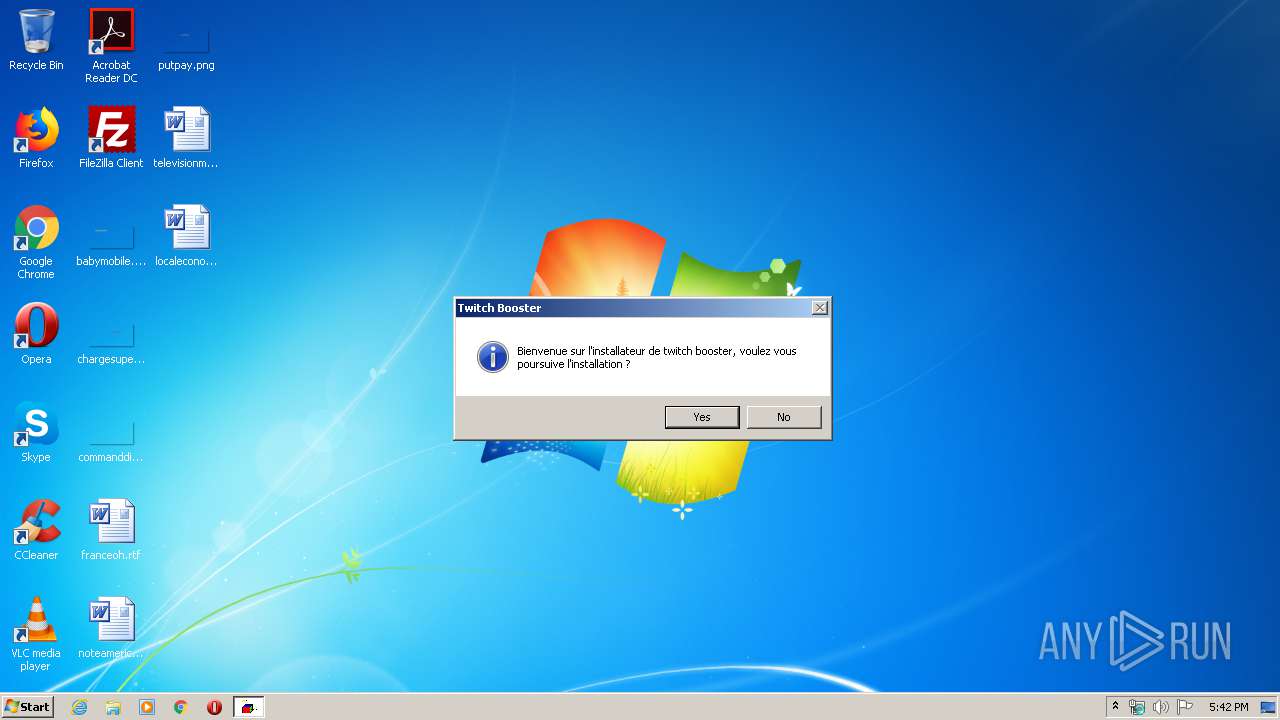
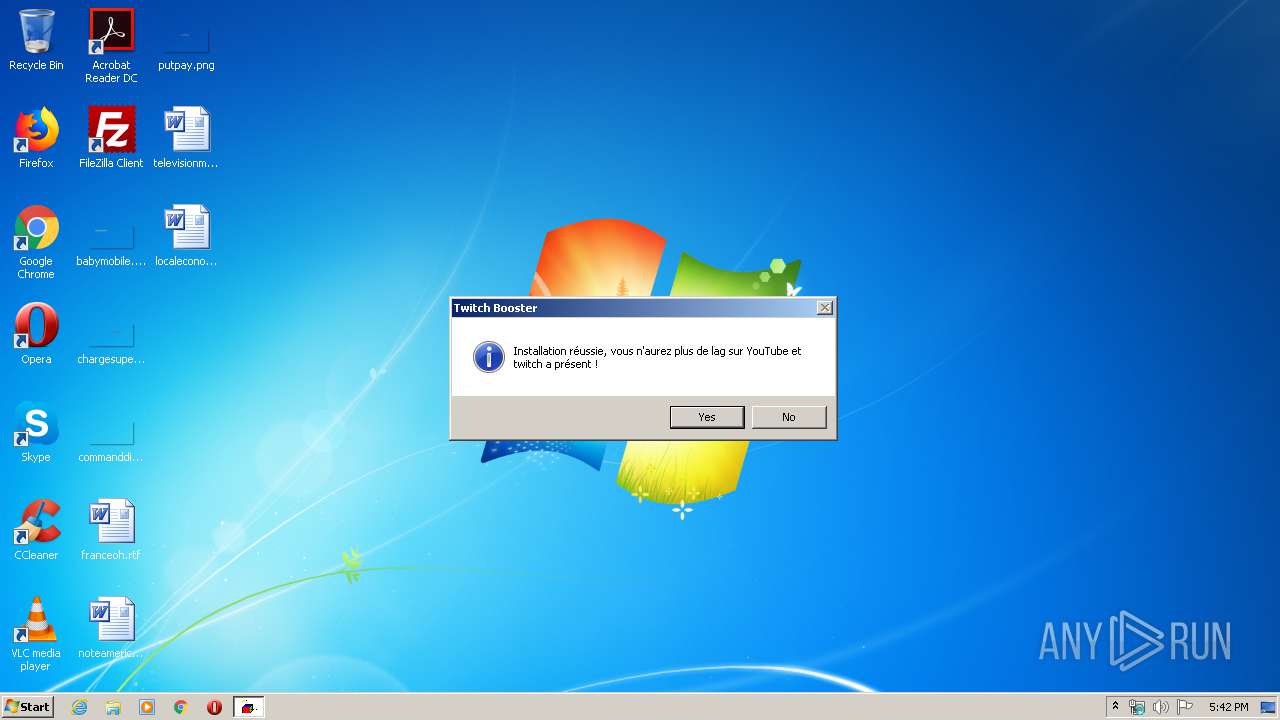
| File name: | Twitch Booster by back v6 cactus.exe |
| Full analysis: | https://app.any.run/tasks/14fc8037-c573-4e3f-8720-b58868ce4d66 |
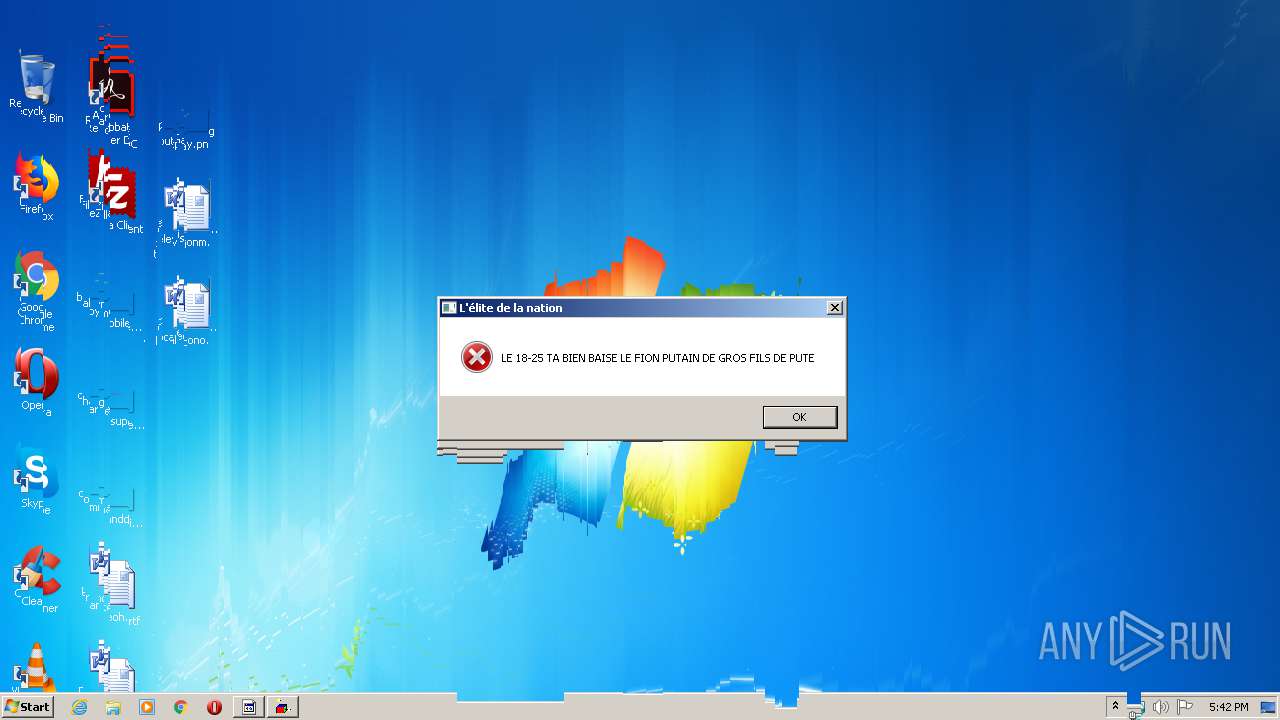
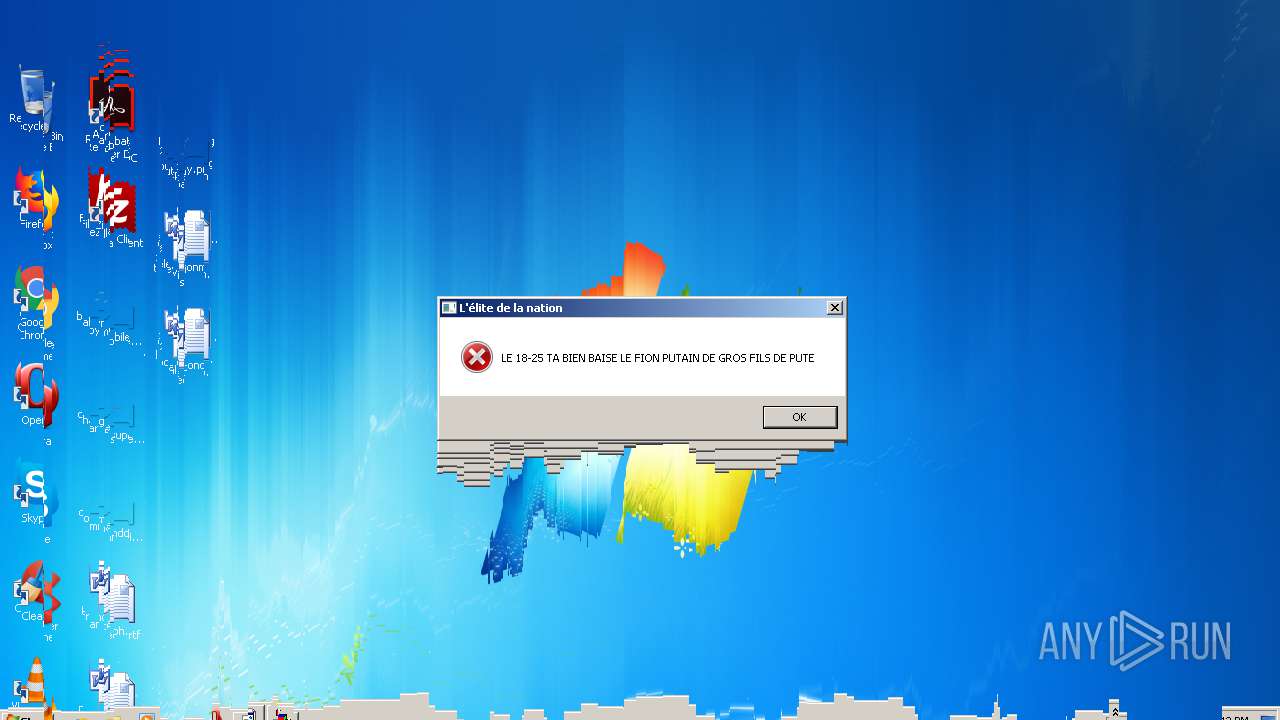
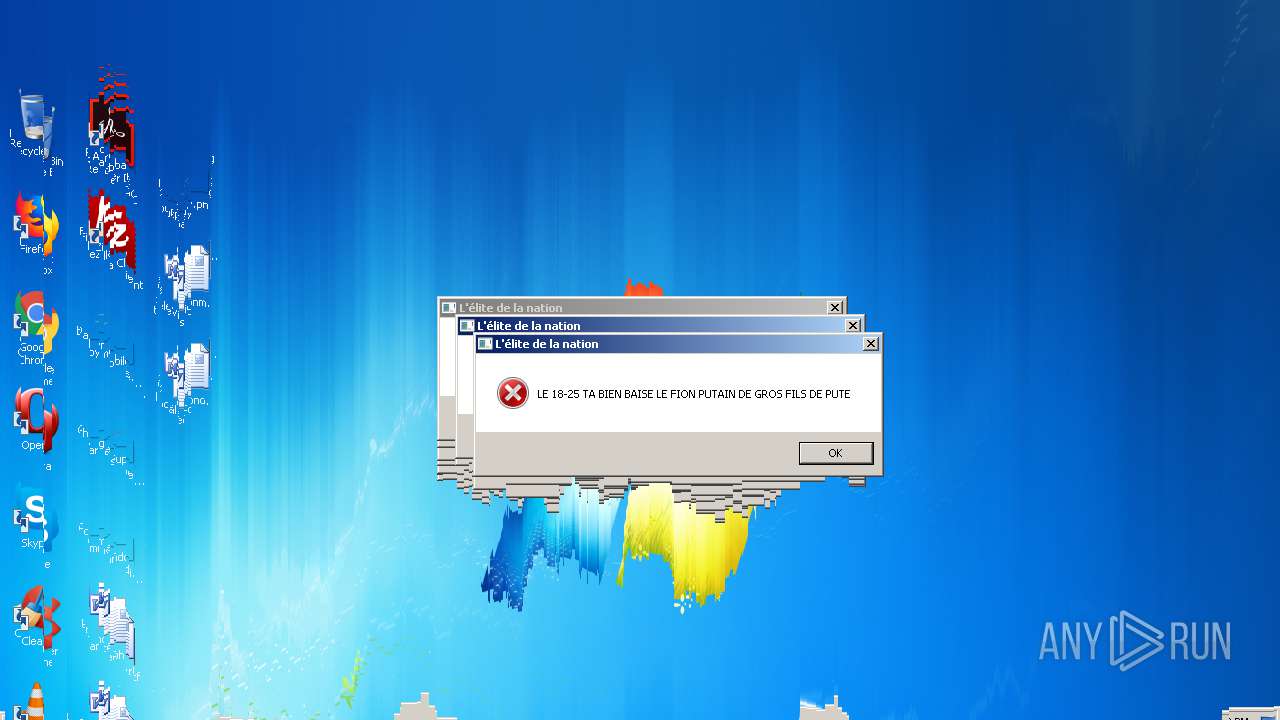
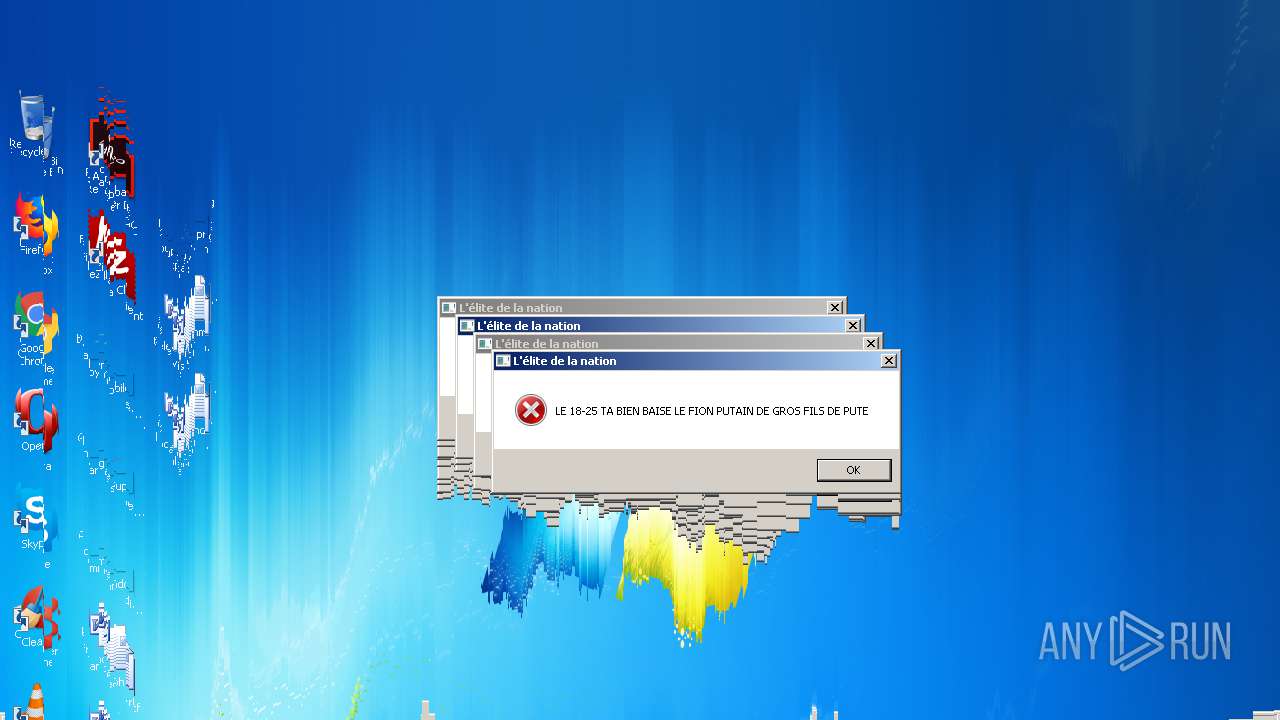
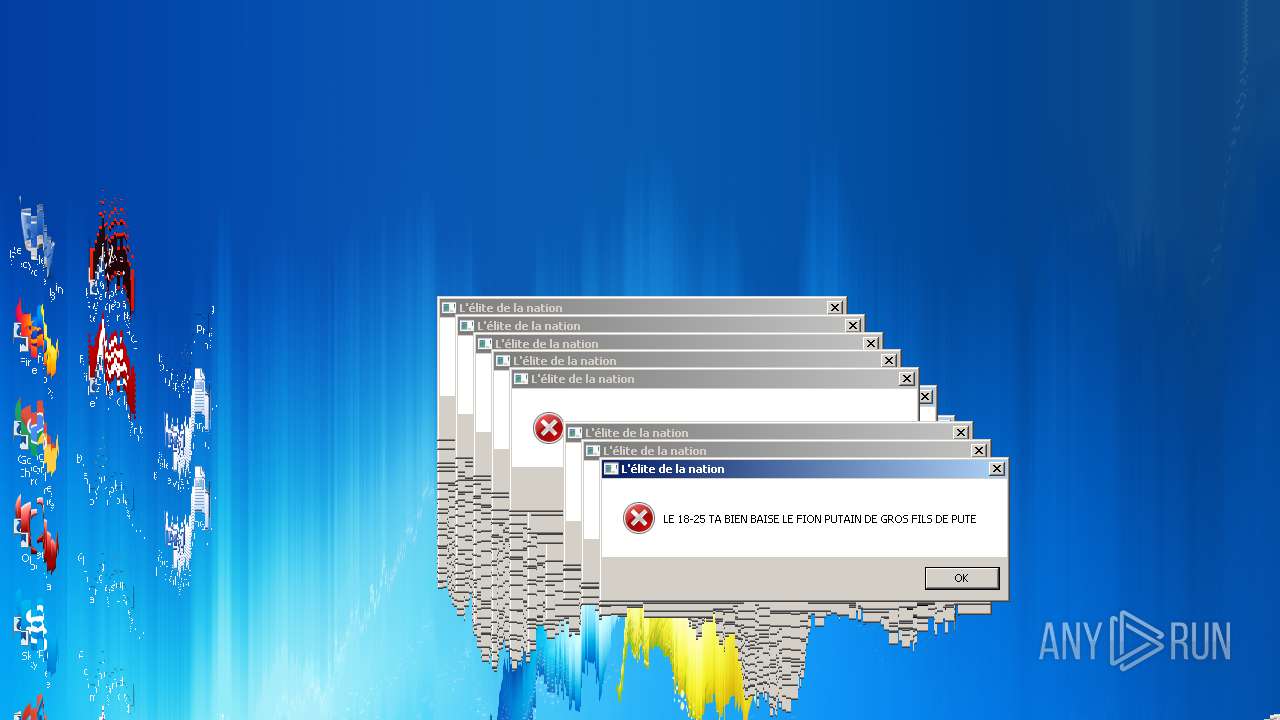
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2020, 16:41:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B9CD9A717A3C8617A23575C8A172986E |
| SHA1: | 7FDEA9E41445E7997E785C5421CF5343255825E1 |
| SHA256: | E32615F5E1F4381F14A6BB9C776B8ABF2A63E90FD9EF08472568EC09CBB6F1A6 |
| SSDEEP: | 49152:yJRT3FWaXWRhWG7Mpzr36AedKbh4el7s2Hsrn5XTW5IYcKm+K:gRT3qRQG7Mp+YxZGYF8 |
MALICIOUS
Application was dropped or rewritten from another process
- extension6.exe (PID: 3016)
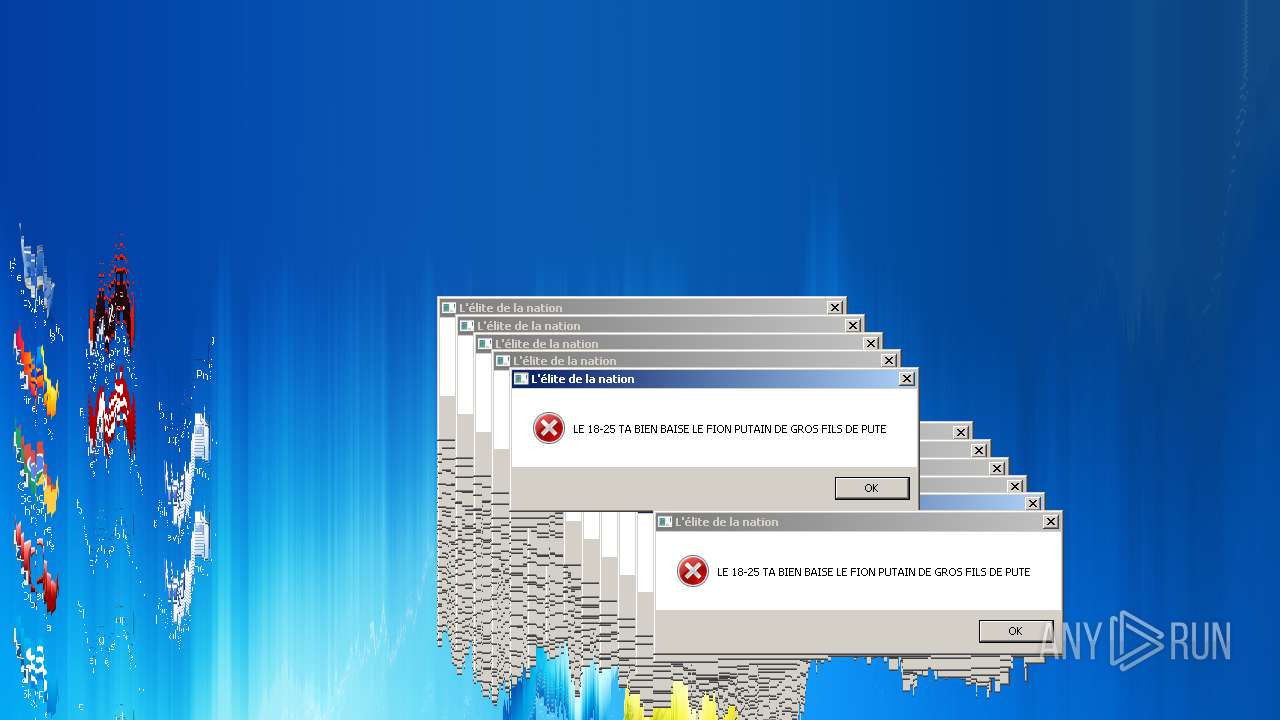
SUSPICIOUS
Creates files in the user directory
- WScript.exe (PID: 4084)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 4004)
- WScript.exe (PID: 2928)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3036)
- cmd.exe (PID: 376)
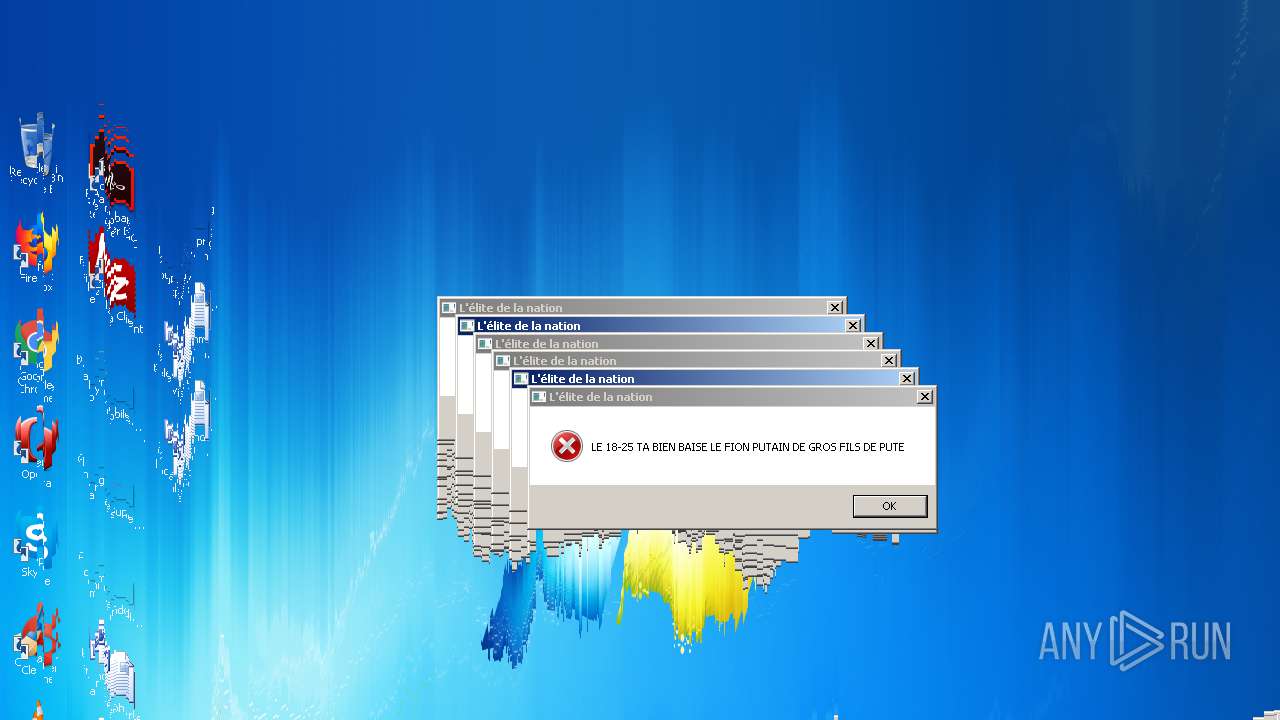
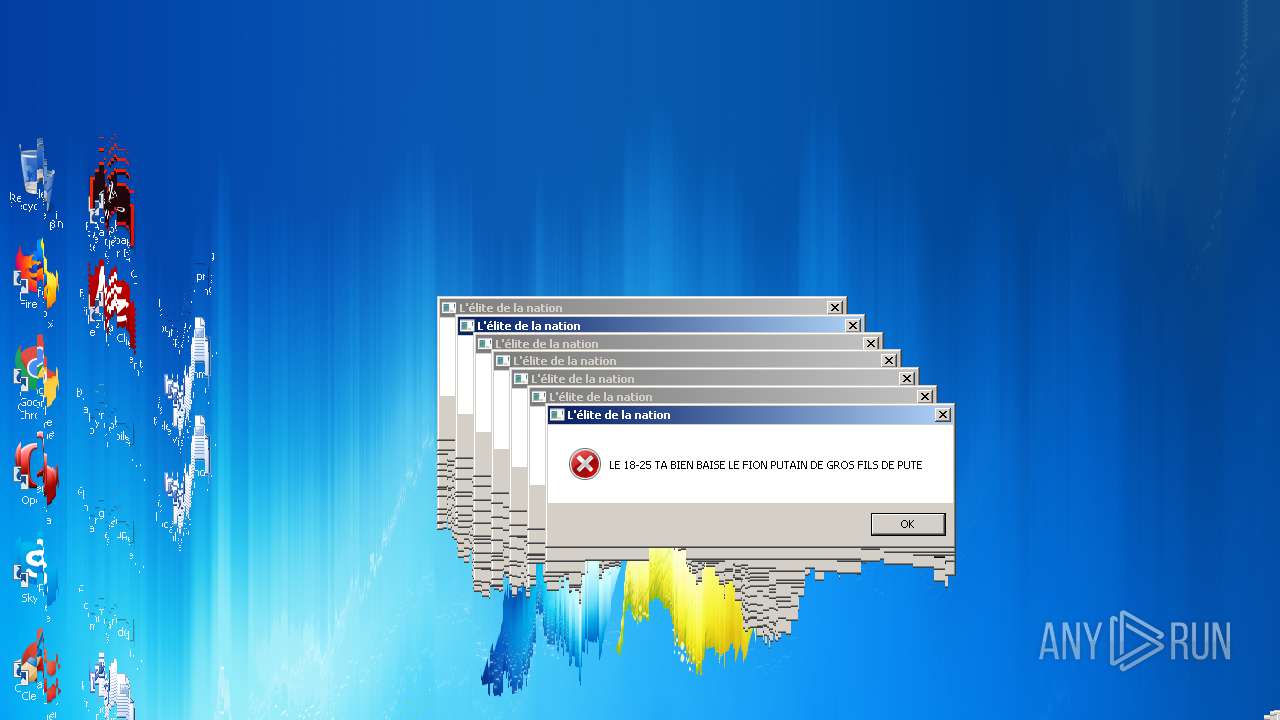
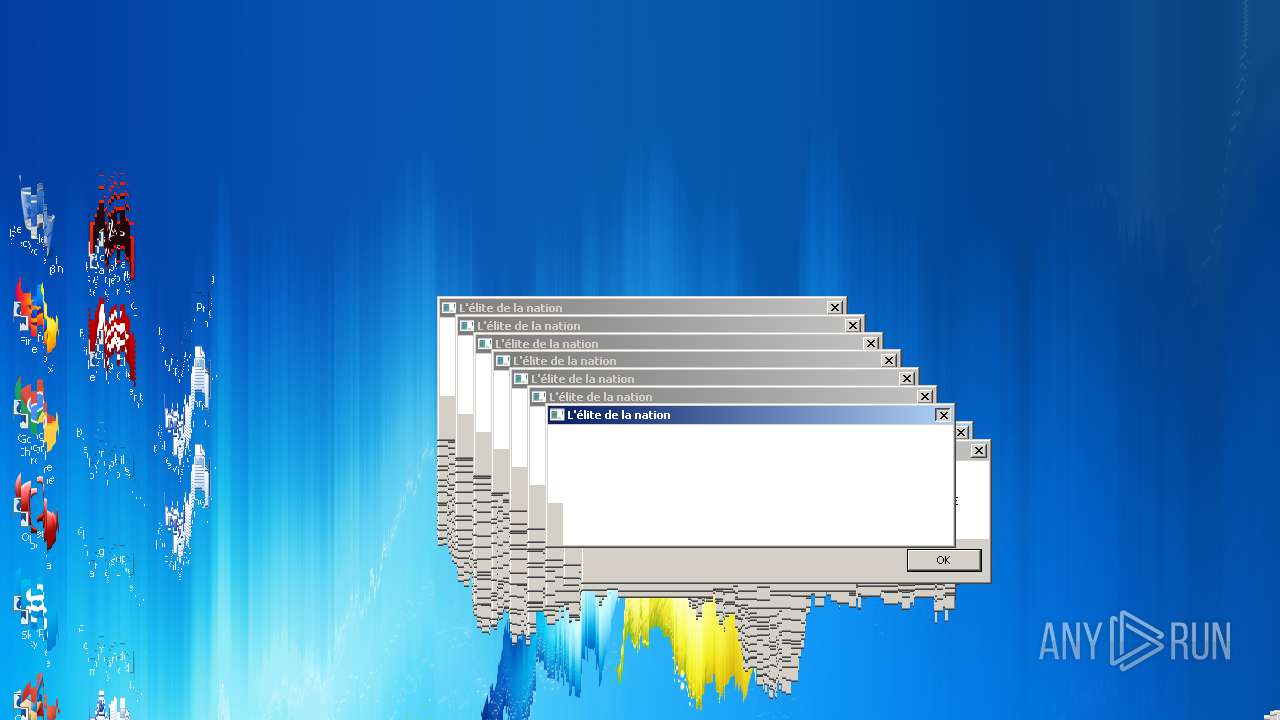
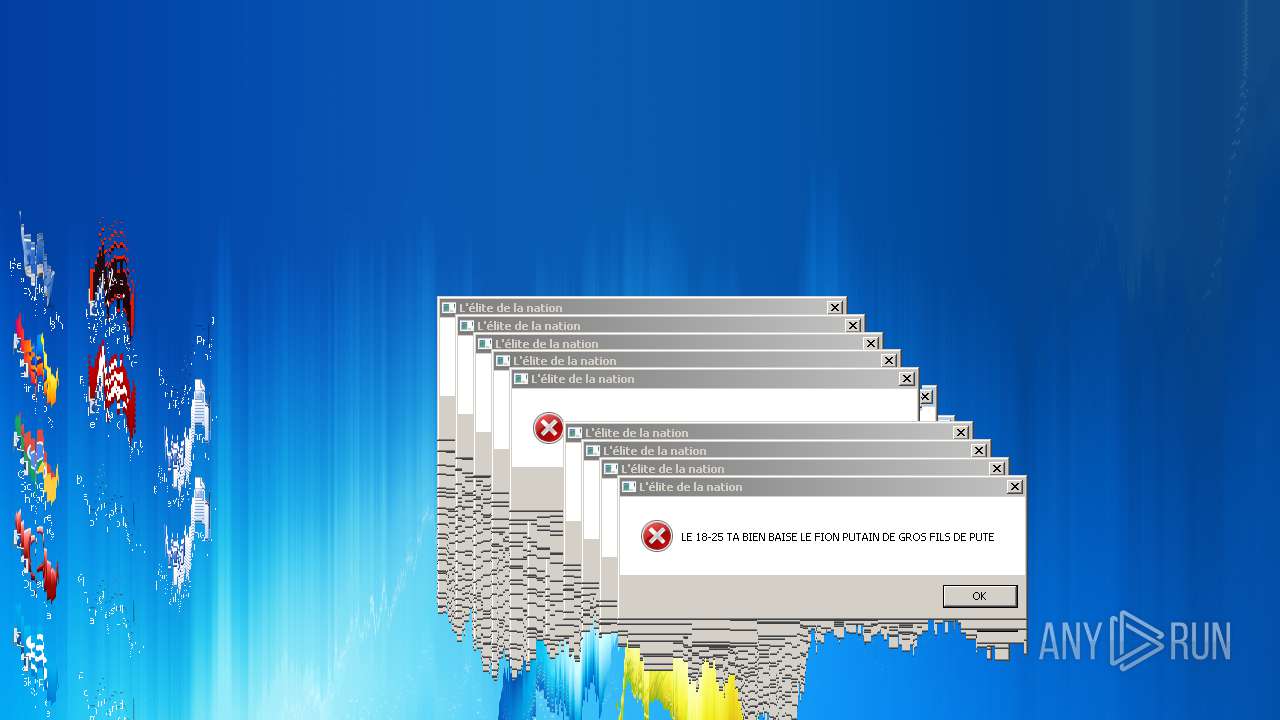
Application launched itself
- WScript.exe (PID: 3172)
- WScript.exe (PID: 3428)
- WScript.exe (PID: 3720)
- WScript.exe (PID: 2896)
- WScript.exe (PID: 2036)
- WScript.exe (PID: 3456)
- WScript.exe (PID: 3544)
- WScript.exe (PID: 3084)
- WScript.exe (PID: 2252)
- WScript.exe (PID: 2116)
- WScript.exe (PID: 3272)
- WScript.exe (PID: 3752)
- WScript.exe (PID: 1336)
- WScript.exe (PID: 3980)
- WScript.exe (PID: 3024)
- WScript.exe (PID: 2692)
- WScript.exe (PID: 2112)
- WScript.exe (PID: 2480)
- WScript.exe (PID: 2700)
- WScript.exe (PID: 3656)
- WScript.exe (PID: 4856)
- WScript.exe (PID: 4928)
- WScript.exe (PID: 4452)
Reads Internet Cache Settings
- WScript.exe (PID: 3556)
Executable content was dropped or overwritten
- Twitch Booster by back v6 cactus.exe (PID: 2712)
Executes scripts
- WScript.exe (PID: 3428)
- WScript.exe (PID: 3720)
- WScript.exe (PID: 3172)
- WScript.exe (PID: 2896)
- WScript.exe (PID: 2036)
- Twitch Booster by back v6 cactus.exe (PID: 2712)
- WScript.exe (PID: 3456)
- WScript.exe (PID: 3544)
- WScript.exe (PID: 3084)
- WScript.exe (PID: 2252)
- WScript.exe (PID: 2116)
- WScript.exe (PID: 3272)
- WScript.exe (PID: 1336)
- WScript.exe (PID: 3752)
- WScript.exe (PID: 3980)
- WScript.exe (PID: 2692)
- WScript.exe (PID: 3024)
- WScript.exe (PID: 2112)
- WScript.exe (PID: 2480)
- WScript.exe (PID: 2700)
- WScript.exe (PID: 3656)
- WScript.exe (PID: 4856)
- WScript.exe (PID: 4928)
- WScript.exe (PID: 4452)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 376)
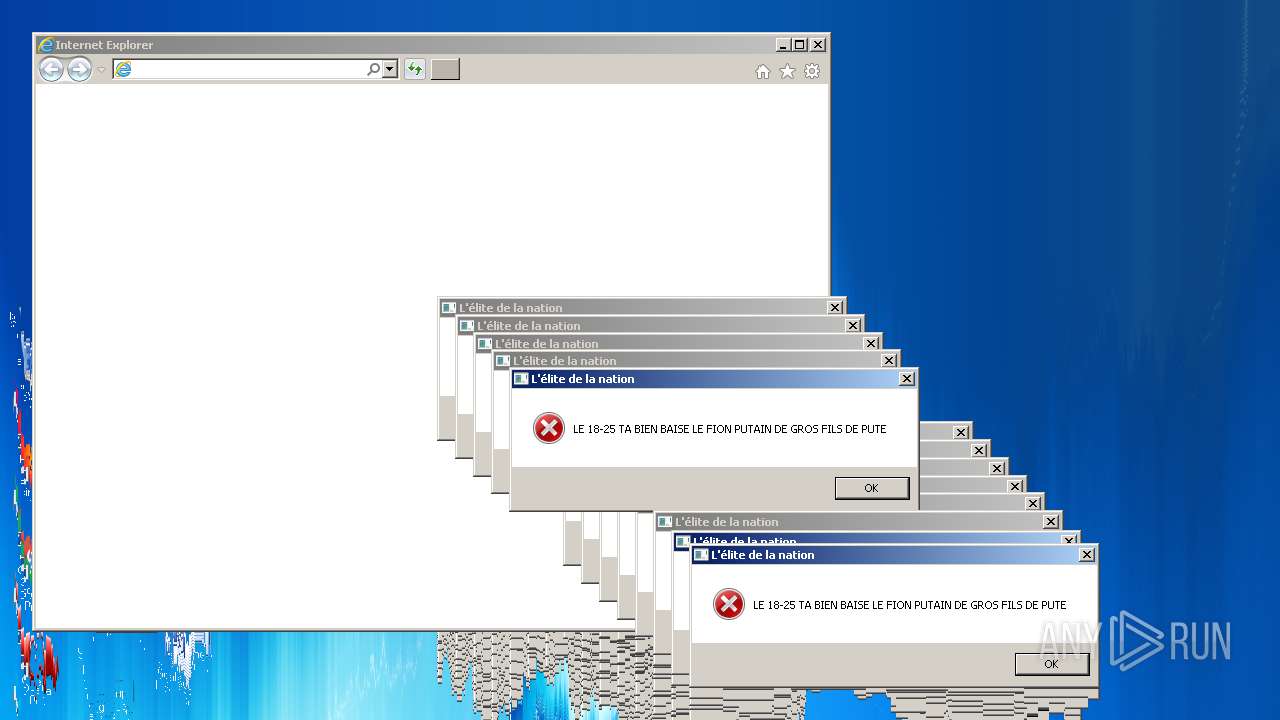
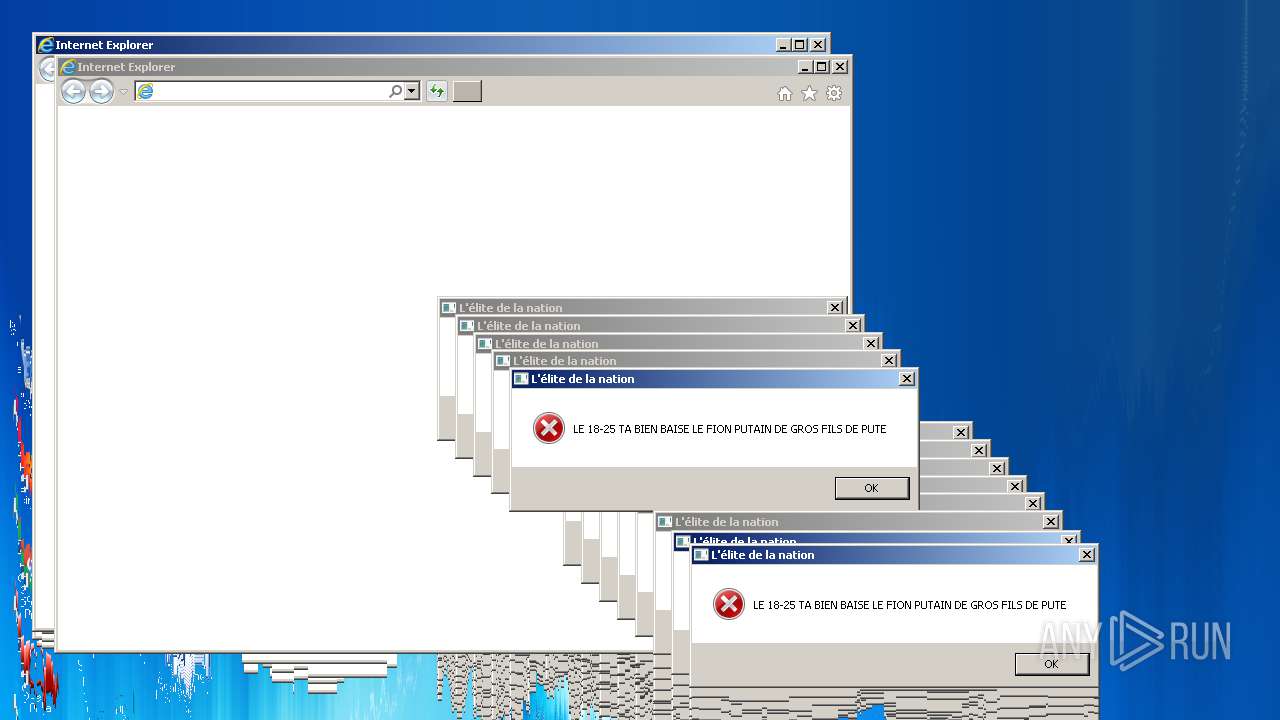
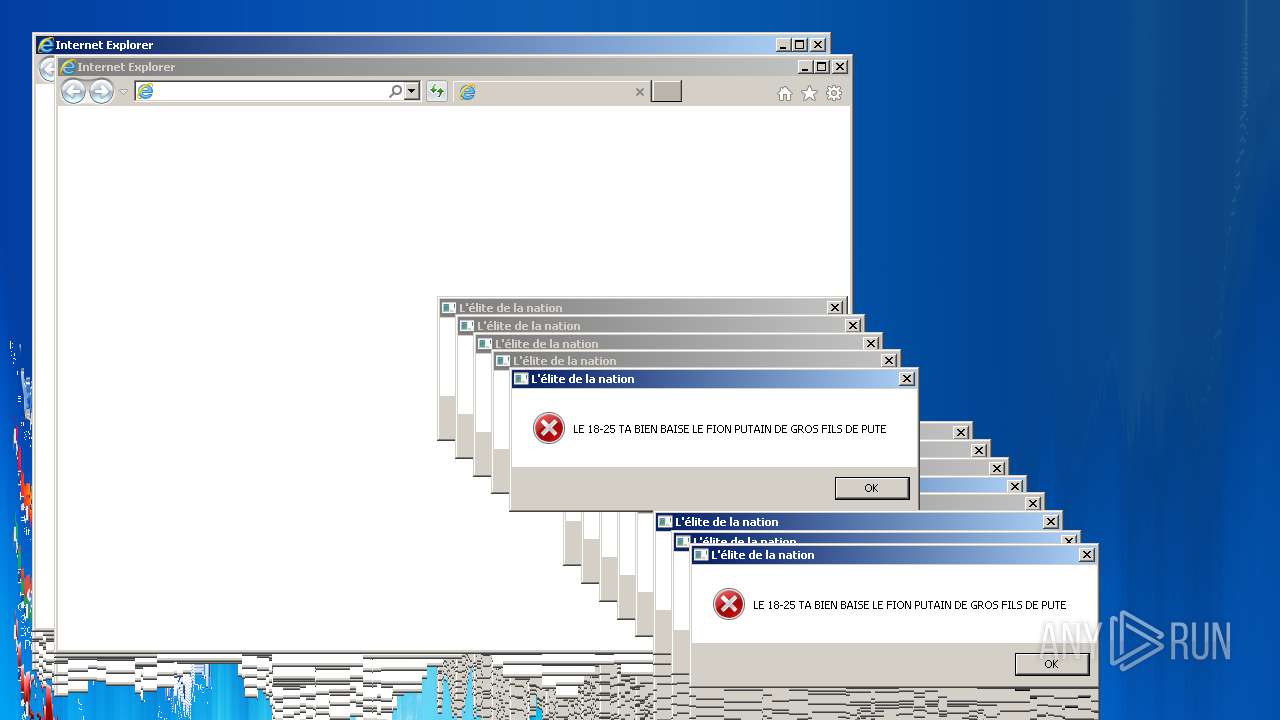
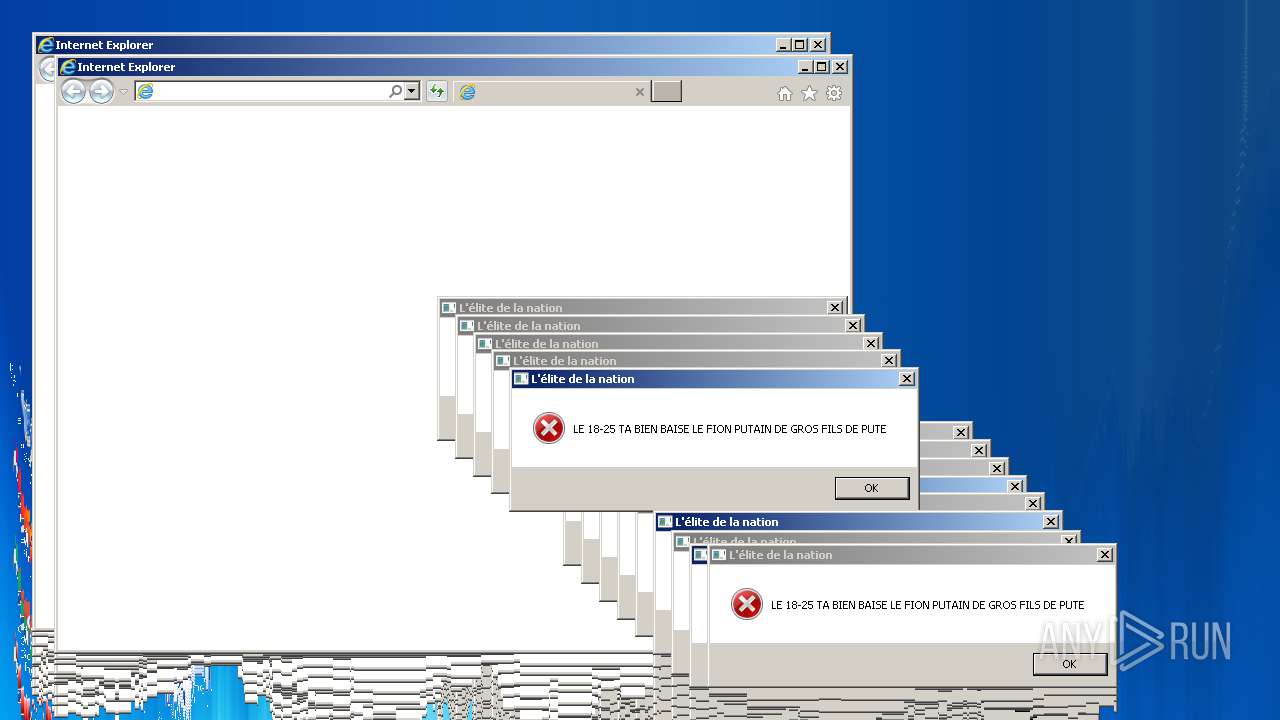
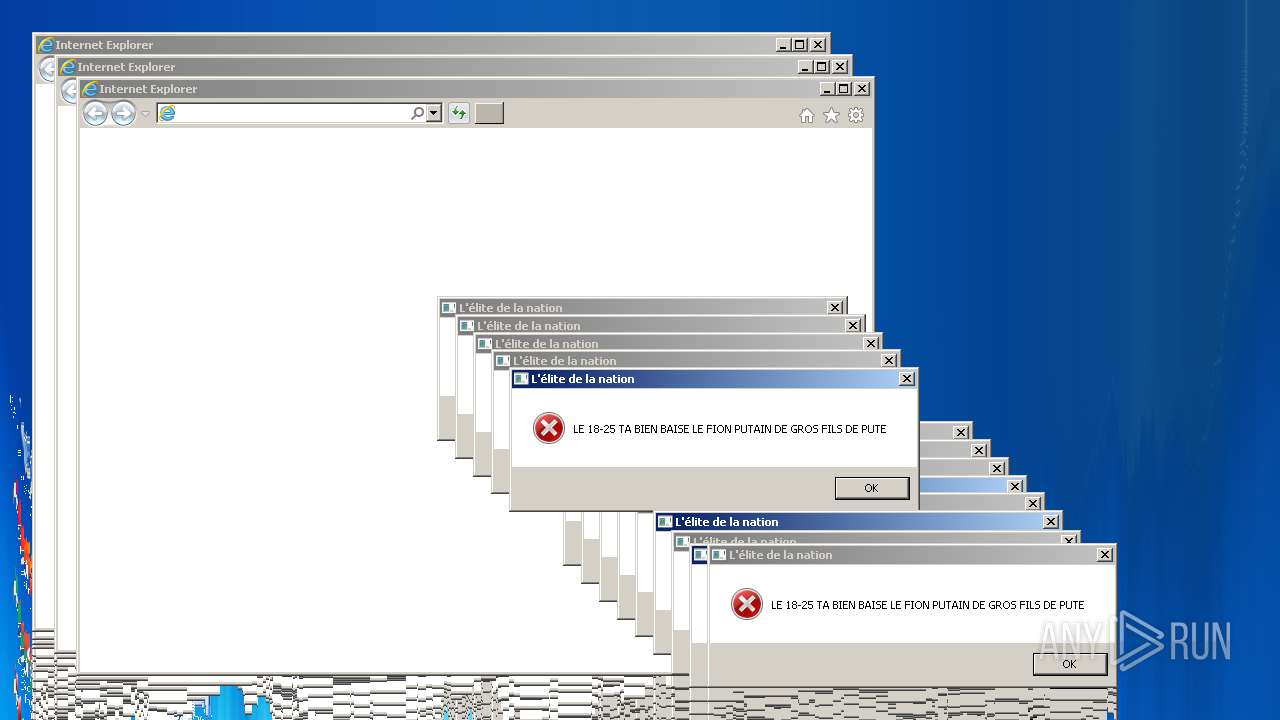
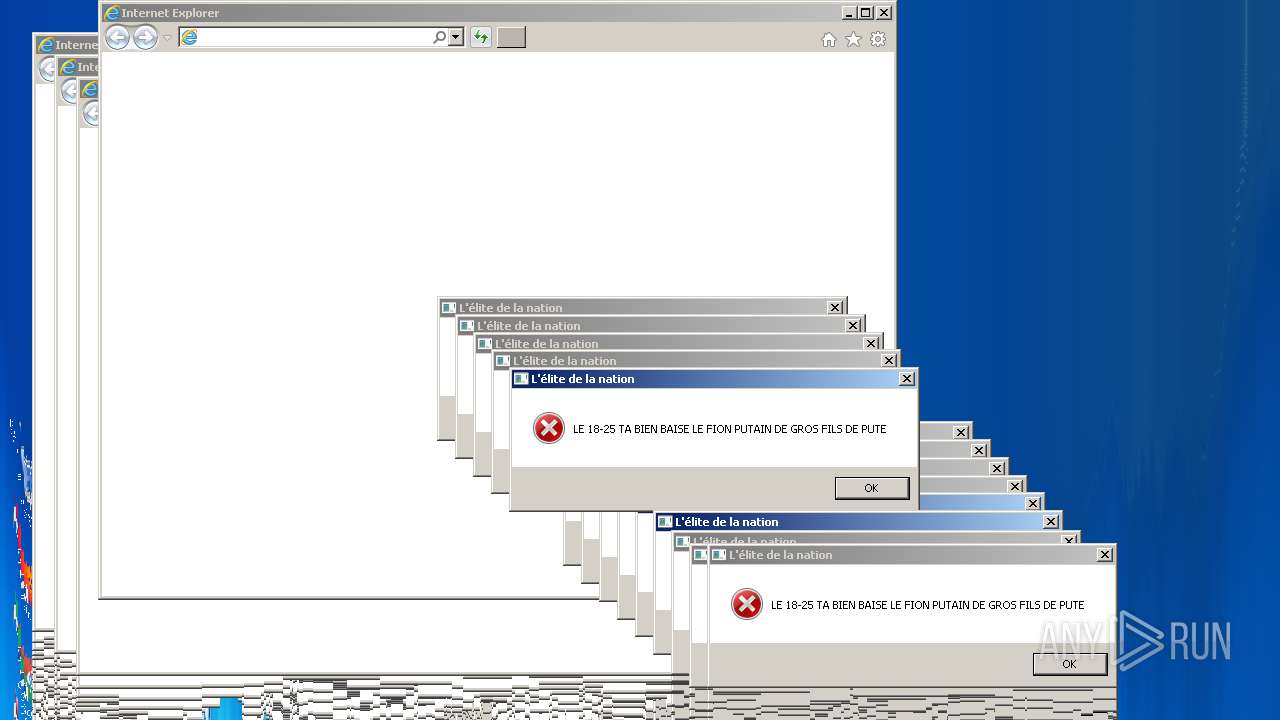
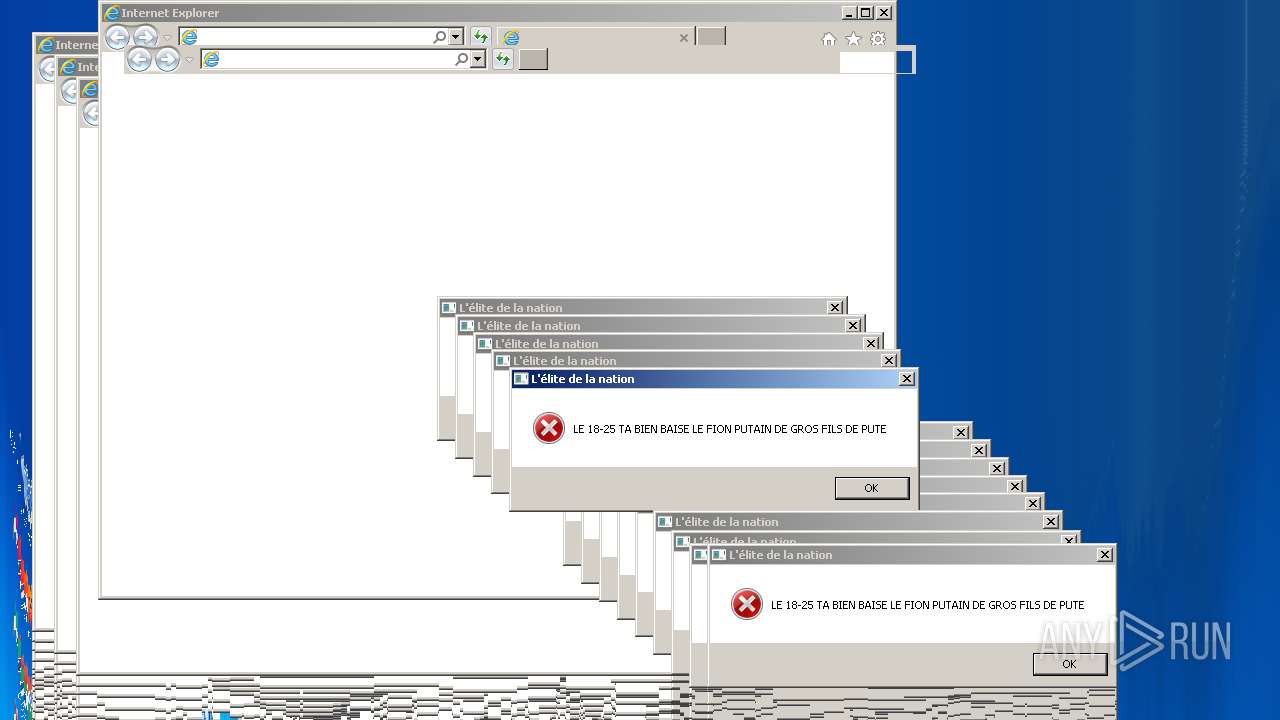
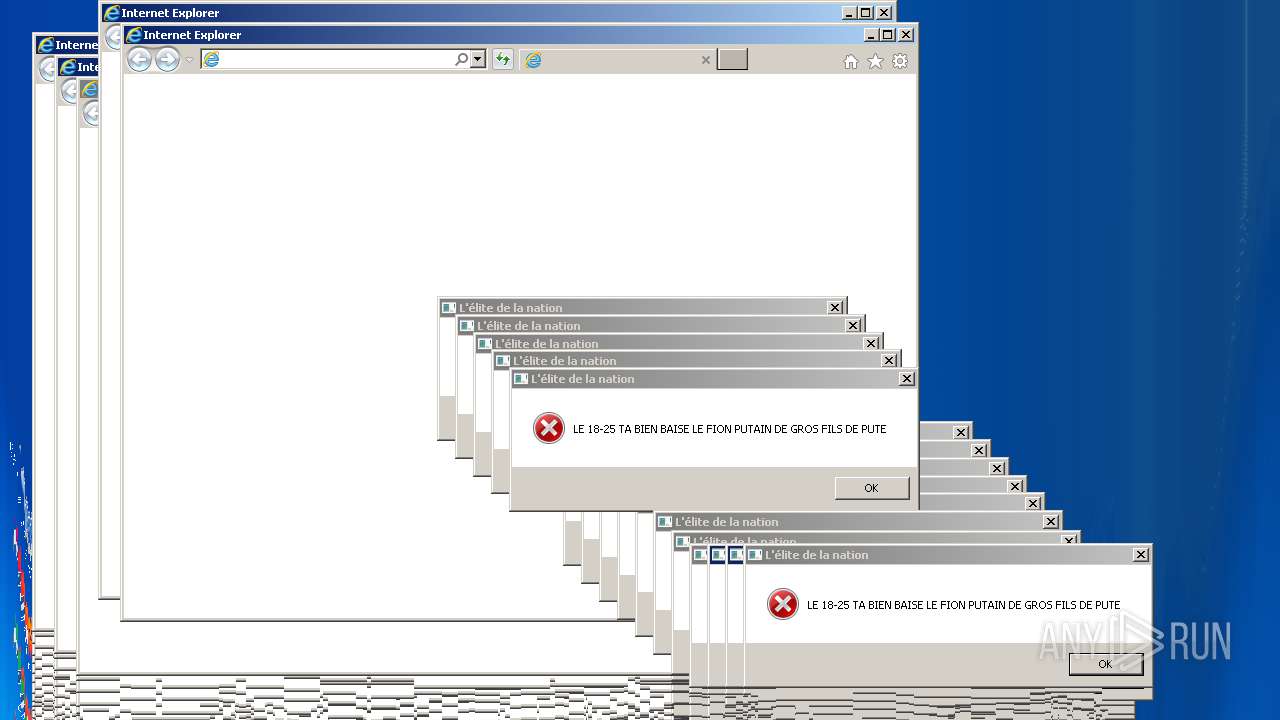
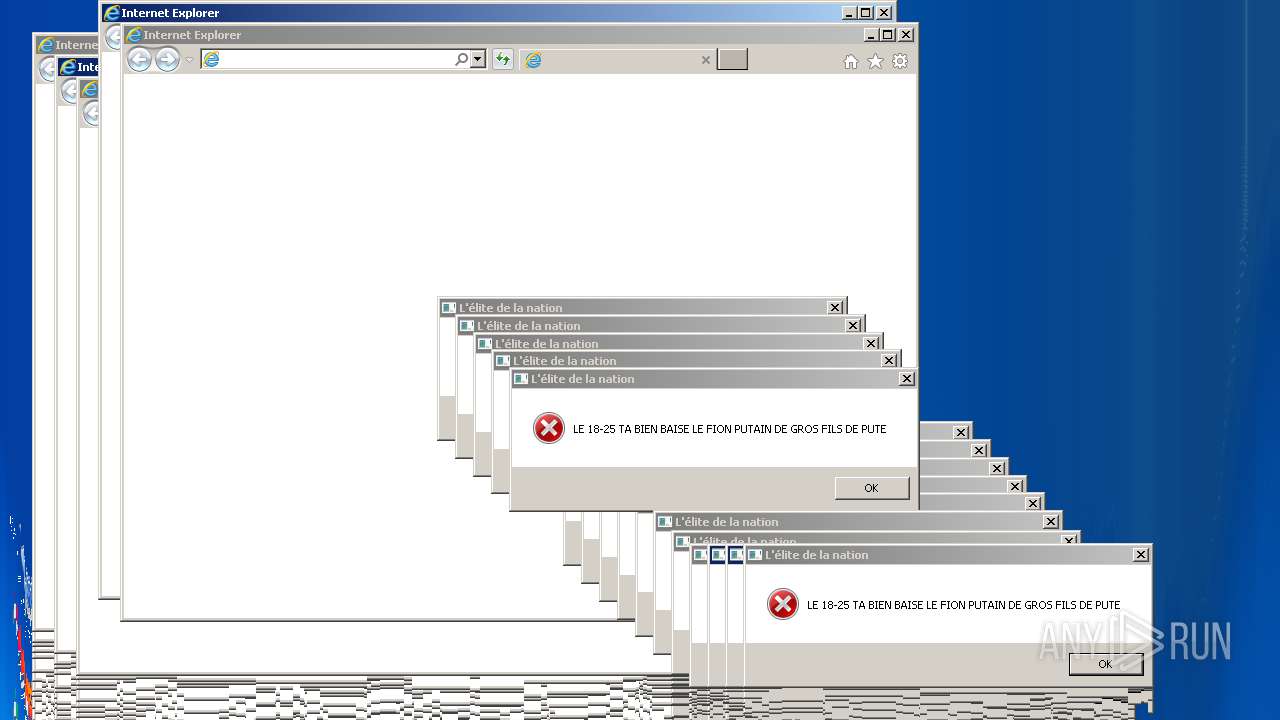
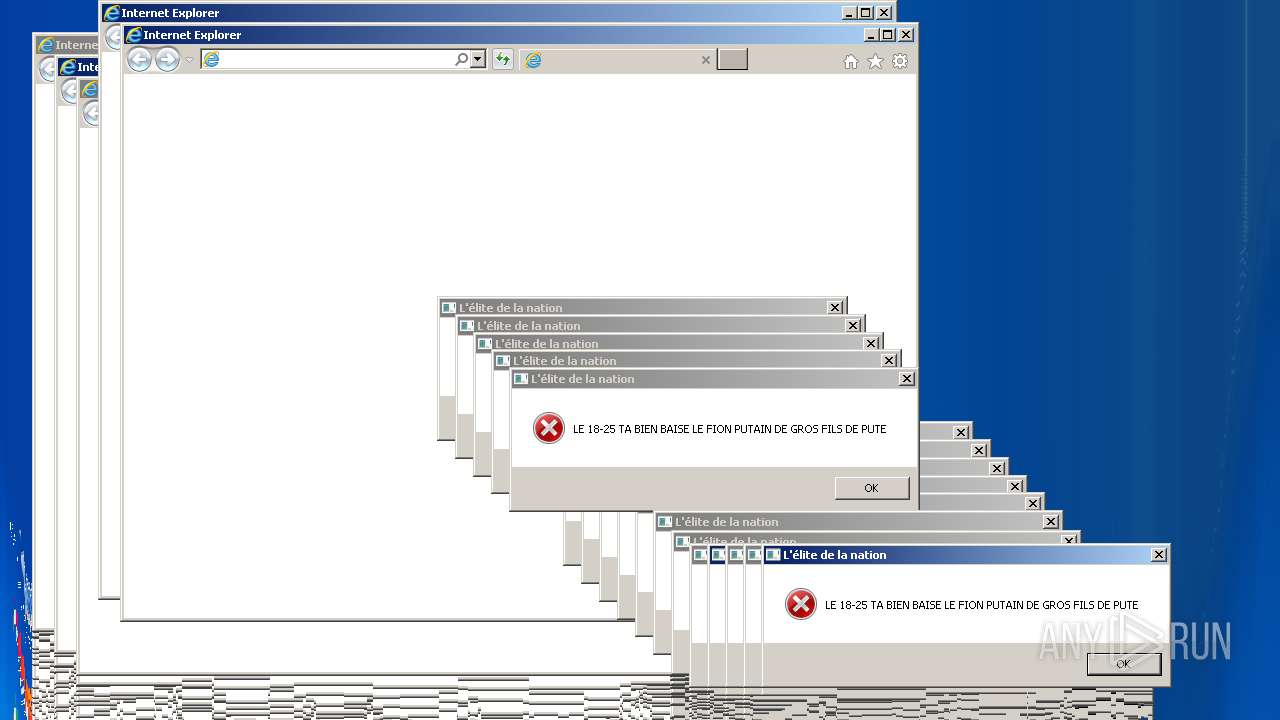
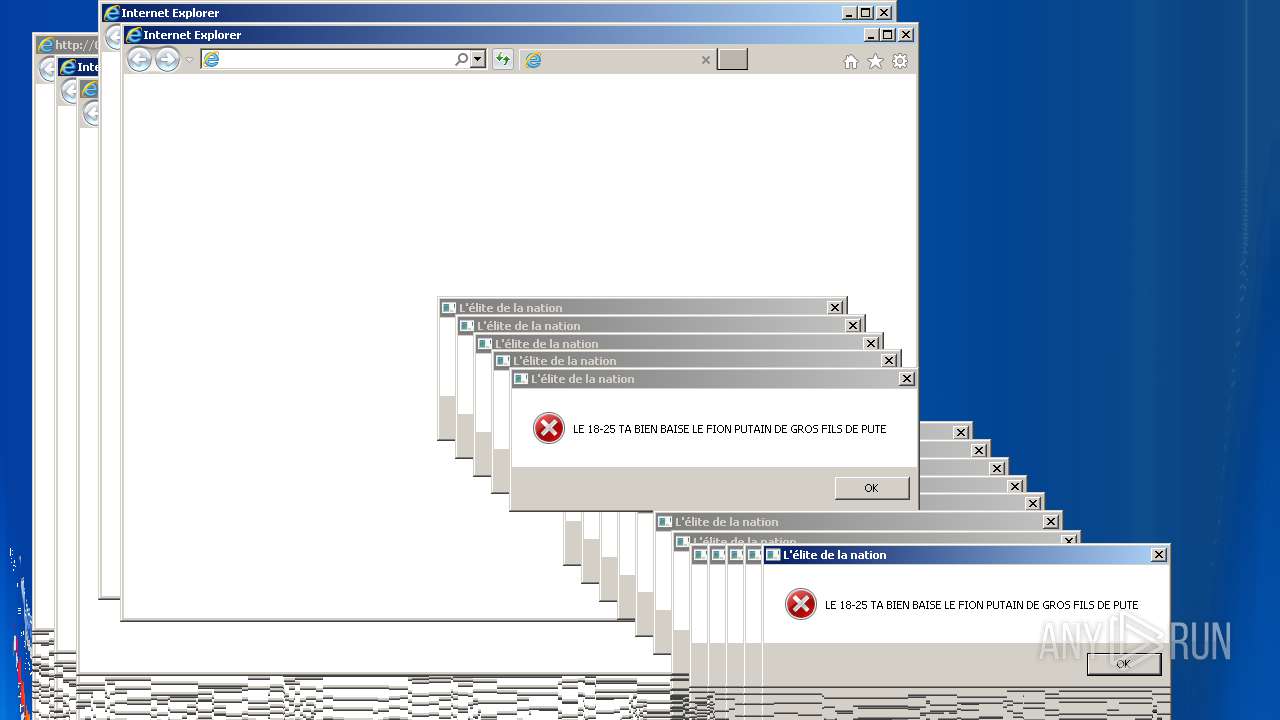
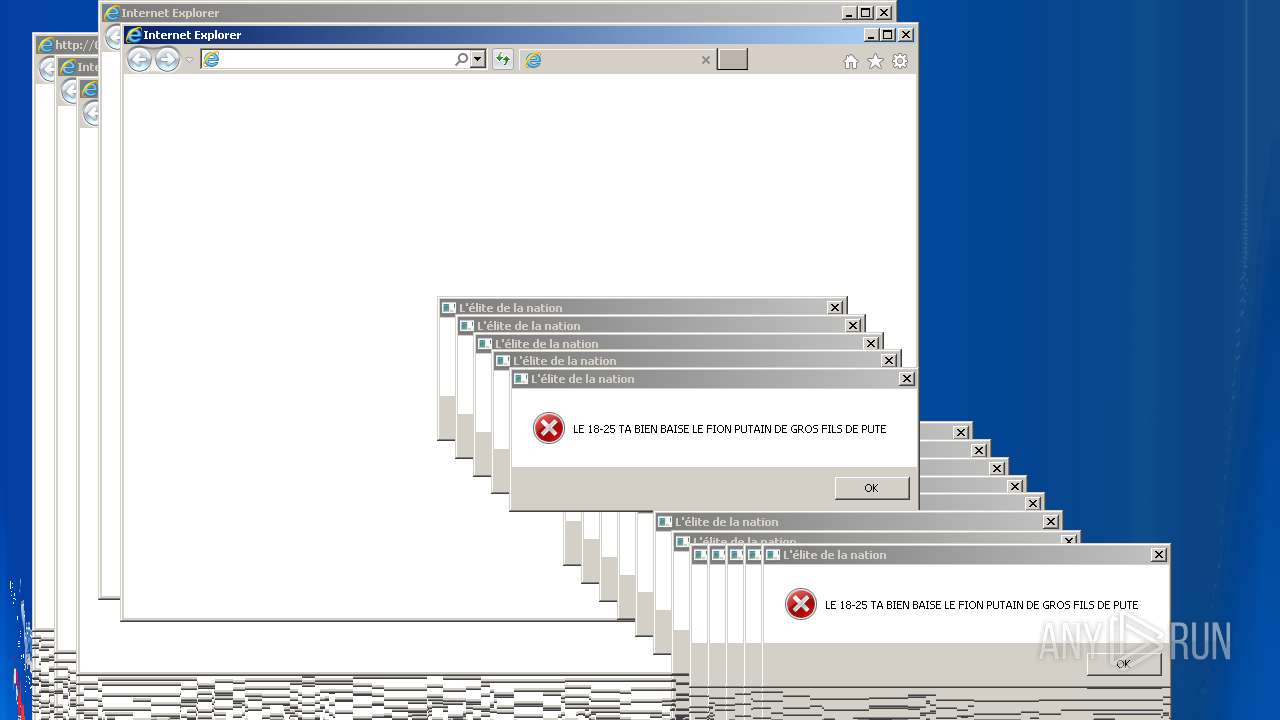
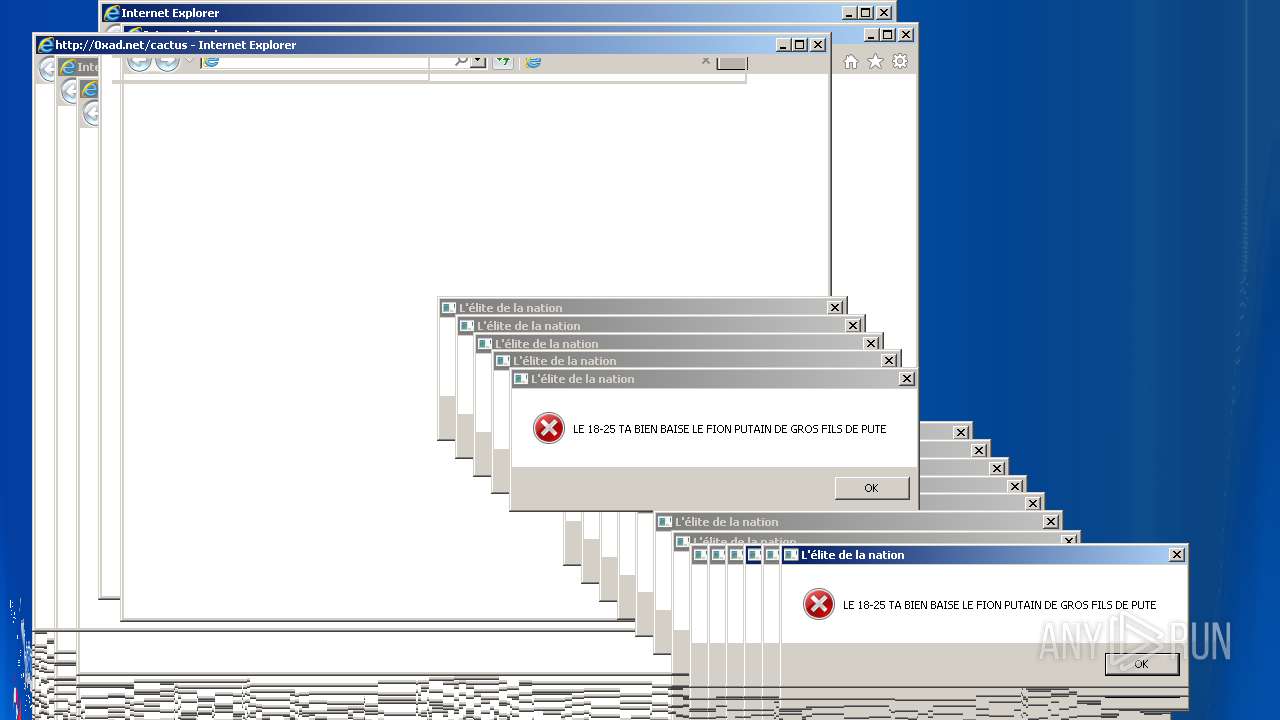
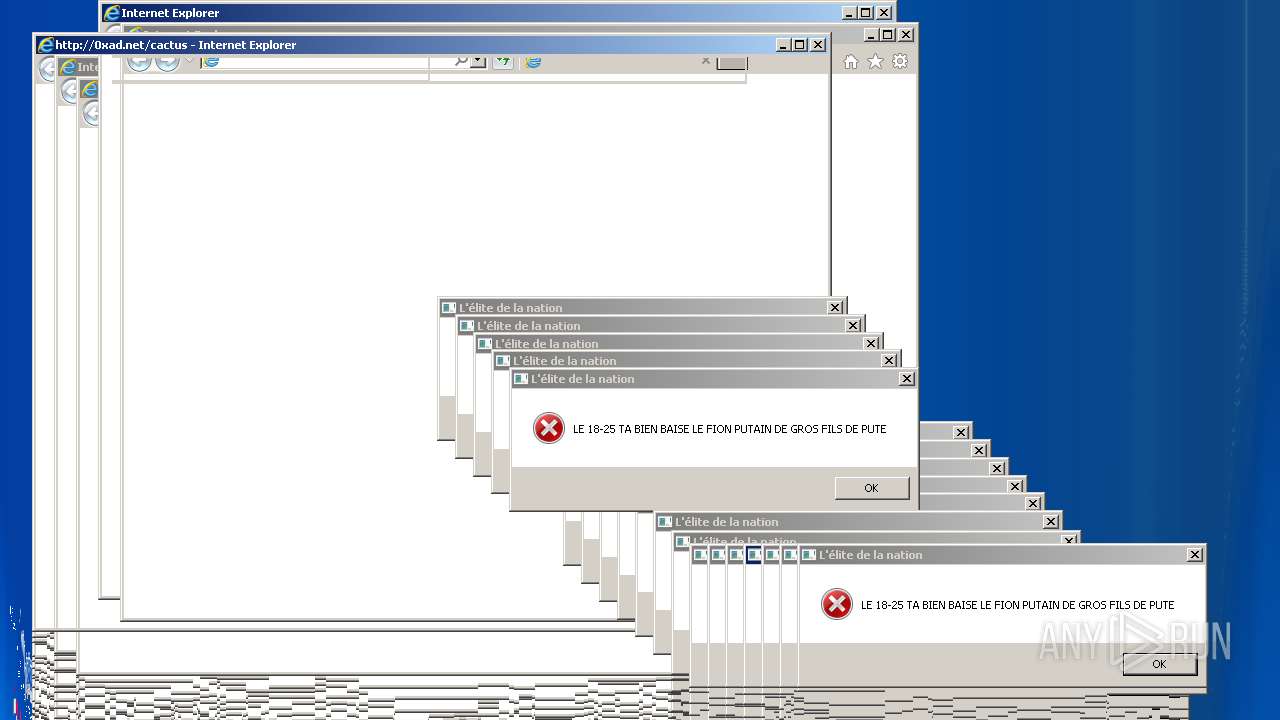
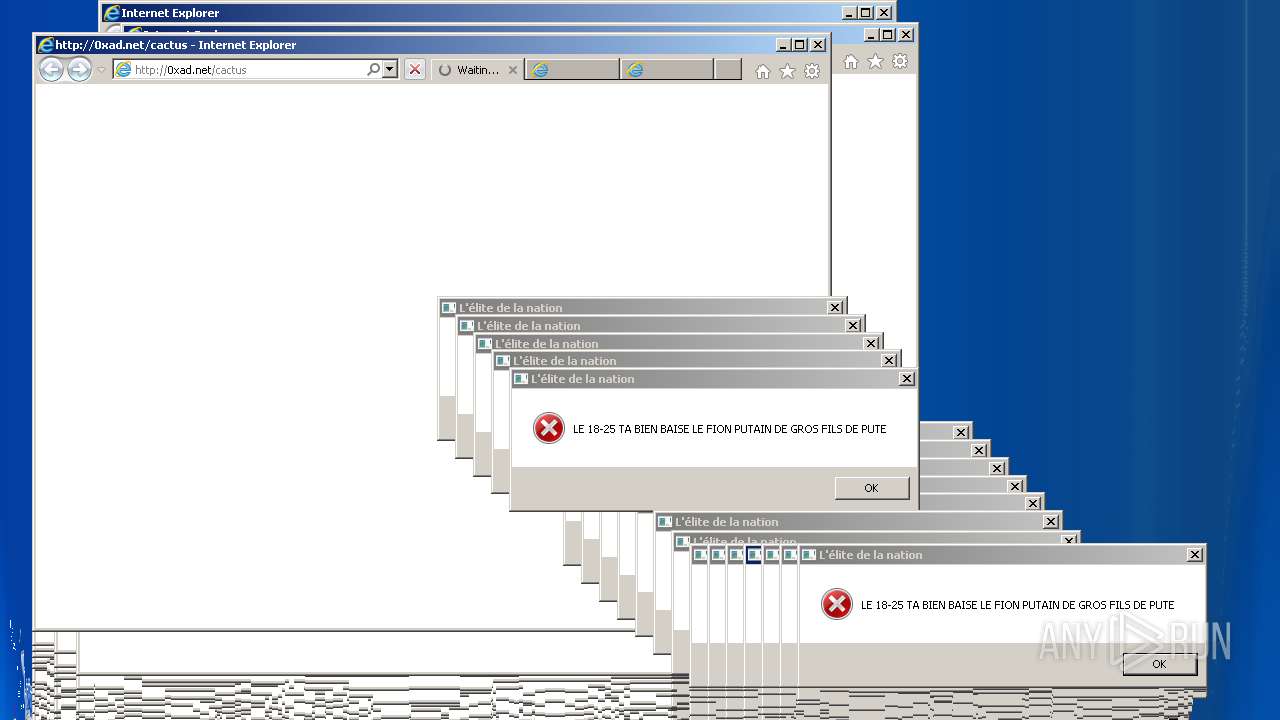
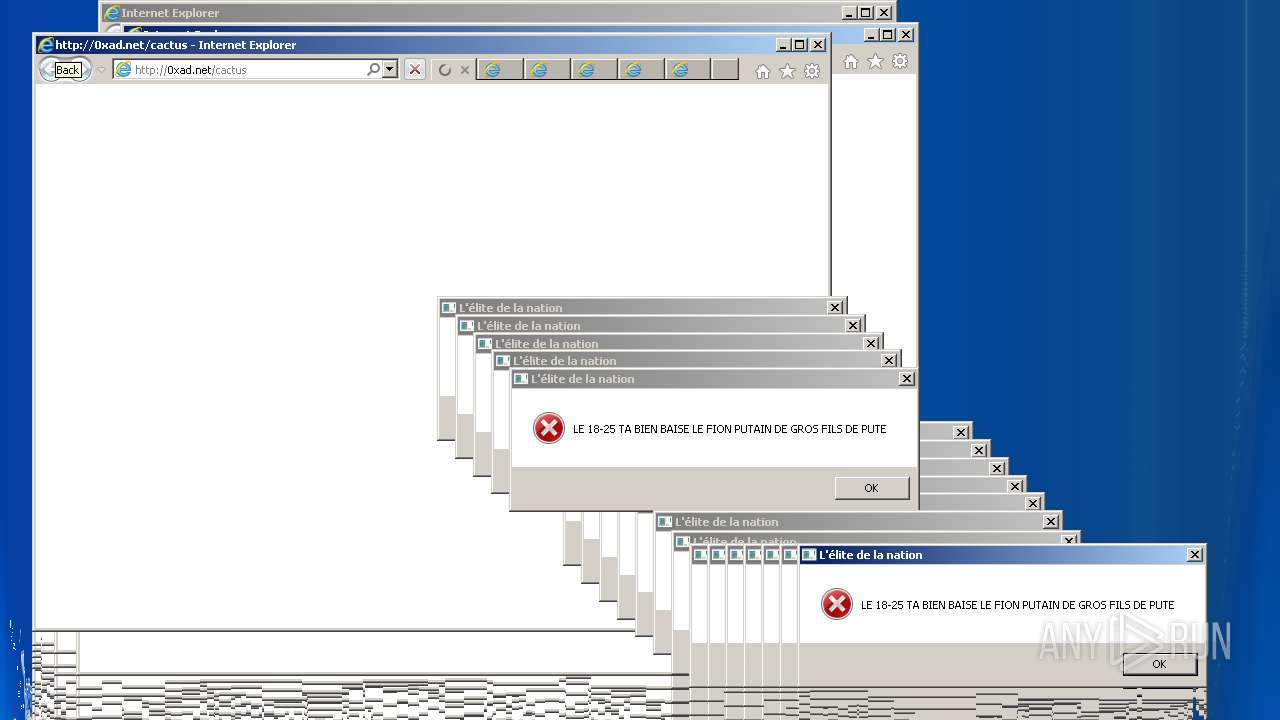
Starts Internet Explorer
- WScript.exe (PID: 3720)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1288)
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 1236)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 2240)
- iexplore.exe (PID: 1000)
- iexplore.exe (PID: 3012)
- iexplore.exe (PID: 3584)
- iexplore.exe (PID: 3124)
- iexplore.exe (PID: 3528)
- iexplore.exe (PID: 2644)
- iexplore.exe (PID: 2724)
- iexplore.exe (PID: 2460)
- iexplore.exe (PID: 2624)
- iexplore.exe (PID: 2376)
- iexplore.exe (PID: 2316)
- iexplore.exe (PID: 1604)
- iexplore.exe (PID: 5848)
- iexplore.exe (PID: 4280)
- iexplore.exe (PID: 5040)
- iexplore.exe (PID: 5612)
- iexplore.exe (PID: 4780)
Changes internet zones settings
- iexplore.exe (PID: 1288)
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 2240)
- iexplore.exe (PID: 1000)
- iexplore.exe (PID: 3124)
- iexplore.exe (PID: 2644)
- iexplore.exe (PID: 3012)
Application launched itself
- iexplore.exe (PID: 1288)
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 2572)
- iexplore.exe (PID: 2240)
- iexplore.exe (PID: 3012)
- iexplore.exe (PID: 1000)
- iexplore.exe (PID: 3124)
- iexplore.exe (PID: 2644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:08:14 21:15:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 188416 |
| InitializedDataSize: | 132096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cab5 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2016 19:15:49 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2016 19:15:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DFE8 | 0x0002E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71025 |
.rdata | 0x0002F000 | 0x000099D0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15287 |
.data | 0x00039000 | 0x0001F8B8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29547 |
.gfids | 0x00059000 | 0x000000F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12367 |
.rsrc | 0x0005A000 | 0x00013BA8 | 0x00013C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.38486 |
.reloc | 0x0006E000 | 0x00001F8C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
7 | 3.1586 | 482 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.11685 | 460 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.15447 | 494 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.99727 | 326 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.2036 | 1094 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.12889 | 358 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 2.95673 | 288 | Latin 1 / Western European | English - United States | RT_STRING |
14 | 2.77928 | 186 | Latin 1 / Western European | English - United States | RT_STRING |
15 | 2.83619 | 188 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
103
Monitored processes
62
Malicious processes
12
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | taskkill /f /IM chrome.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 376 | cmd /c ""C:\Users\admin\AppData\Local\Temp\extension4.bat" " | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Internet Explorer\iexplore.exe" http://0xad.net/cactus | C:\Program Files\Internet Explorer\iexplore.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1288 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Internet Explorer\iexplore.exe" http://0xad.net/cactus | C:\Program Files\Internet Explorer\iexplore.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1336 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\extension3.vbs" | C:\Windows\System32\WScript.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2644 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1784 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\4826.vbs" | C:\Windows\System32\WScript.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2036 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\extension3.vbs" | C:\Windows\System32\WScript.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2112 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\extension3.vbs" | C:\Windows\System32\WScript.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
12 828
Read events
12 337
Write events
490
Delete events
1
Modification events
| (PID) Process: | (2712) Twitch Booster by back v6 cactus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2712) Twitch Booster by back v6 cactus.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3720) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3720) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4084) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | CLSID |
Value: {C9E37C15-DF92-4727-85D6-72E5EEB6995A} | |||
| (PID) Process: | (4084) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | |
Value: Current User Lexicon | |||
| (PID) Process: | (4084) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon\{C9E37C15-DF92-4727-85D6-72E5EEB6995A}\Files |
| Operation: | write | Name: | Datafile |
Value: %1a%\Microsoft\Speech\Files\UserLexicons\SP_B4EE863FFB614870808DDAA4248F6DD0.dat | |||
| (PID) Process: | (4084) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | Generation |
Value: 0 | |||
| (PID) Process: | (4084) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\PhoneConverters |
| Operation: | write | Name: | DefaultTokenId |
Value: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech\PhoneConverters\Tokens\English | |||
| (PID) Process: | (4084) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} |
| Operation: | write | Name: | |
Value: Speakers (Realtek AC'97 Audio) | |||
Executable files
1
Suspicious files
1
Text files
19
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\cactus[1].txt | — | |
MD5:— | SHA256:— | |||
| 1288 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2428 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4084 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Speech\Files\UserLexicons\SP_B4EE863FFB614870808DDAA4248F6DD0.dat | binary | |
MD5:— | SHA256:— | |||
| 2724 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\cactus[1].txt | — | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\cactus[1].txt | text | |
MD5:— | SHA256:— | |||
| 1236 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\cactus[2].txt | text | |
MD5:— | SHA256:— | |||
| 3528 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\cactus[1].txt | text | |
MD5:— | SHA256:— | |||
| 2624 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\cactus[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
18
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2624 | iexplore.exe | GET | 301 | 142.93.108.123:80 | http://0xad.net/cactus | CA | text | 39 b | whitelisted |
3584 | iexplore.exe | GET | 301 | 142.93.108.123:80 | http://0xad.net/cactus | CA | text | 39 b | whitelisted |
1236 | iexplore.exe | GET | 301 | 142.93.108.123:80 | http://0xad.net/cactus | CA | text | 39 b | whitelisted |
2724 | iexplore.exe | GET | 301 | 142.93.108.123:80 | http://0xad.net/cactus | CA | text | 39 b | whitelisted |
1236 | iexplore.exe | GET | 301 | 142.93.108.123:80 | http://0xad.net/cactus | CA | text | 39 b | whitelisted |
3528 | iexplore.exe | GET | 301 | 142.93.108.123:80 | http://0xad.net/cactus | CA | text | 39 b | whitelisted |
2460 | iexplore.exe | GET | 301 | 142.93.108.123:80 | http://0xad.net/cactus | CA | text | 39 b | whitelisted |
3584 | iexplore.exe | GET | 301 | 142.93.108.123:80 | http://0xad.net/cactus | CA | text | 39 b | whitelisted |
1288 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1288 | iexplore.exe | 204.79.197.200:80 | 0xad.net | Microsoft Corporation | US | whitelisted |
1236 | iexplore.exe | 142.93.108.123:80 | — | — | CA | malicious |
1236 | iexplore.exe | 142.93.108.123:443 | — | — | CA | malicious |
2624 | iexplore.exe | 142.93.108.123:80 | — | — | CA | malicious |
3584 | iexplore.exe | 142.93.108.123:443 | — | — | CA | malicious |
2724 | iexplore.exe | 142.93.108.123:443 | — | — | CA | malicious |
3528 | iexplore.exe | 142.93.108.123:80 | — | — | CA | malicious |
3528 | iexplore.exe | 142.93.108.123:443 | — | — | CA | malicious |
3584 | iexplore.exe | 142.93.108.123:80 | — | — | CA | malicious |
— | — | 142.93.108.123:80 | — | — | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
0xad.net |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |