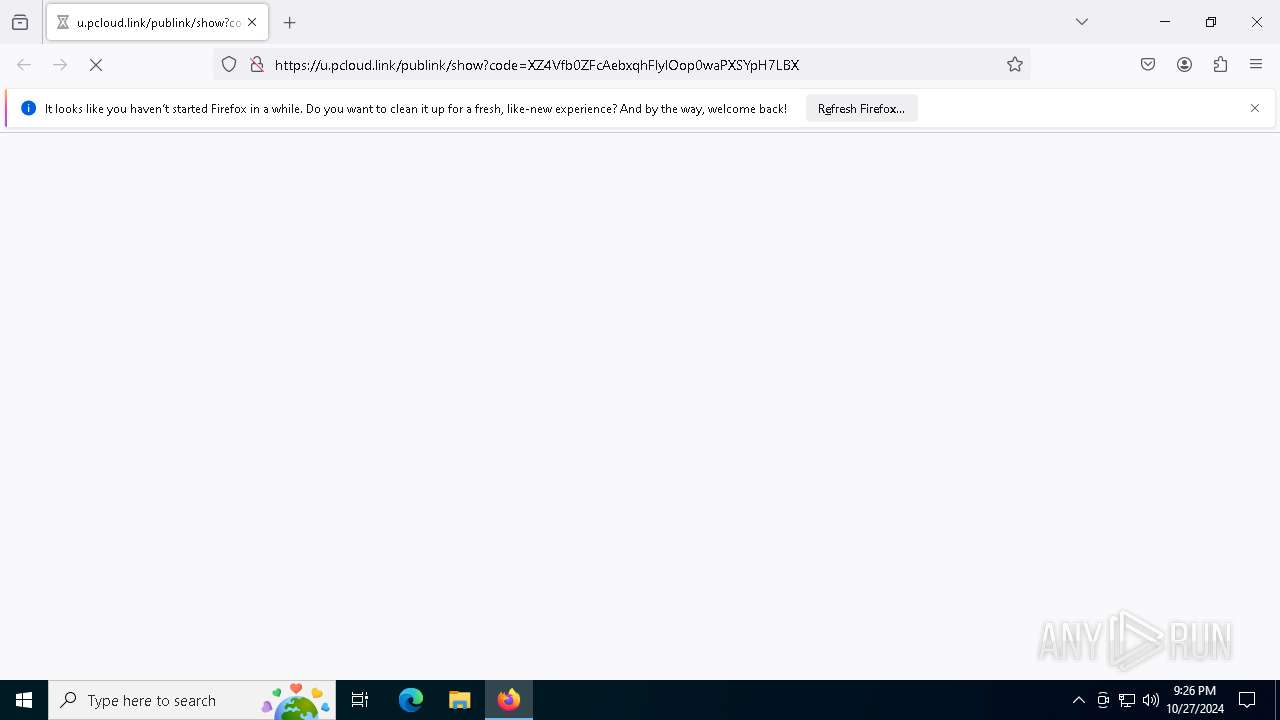
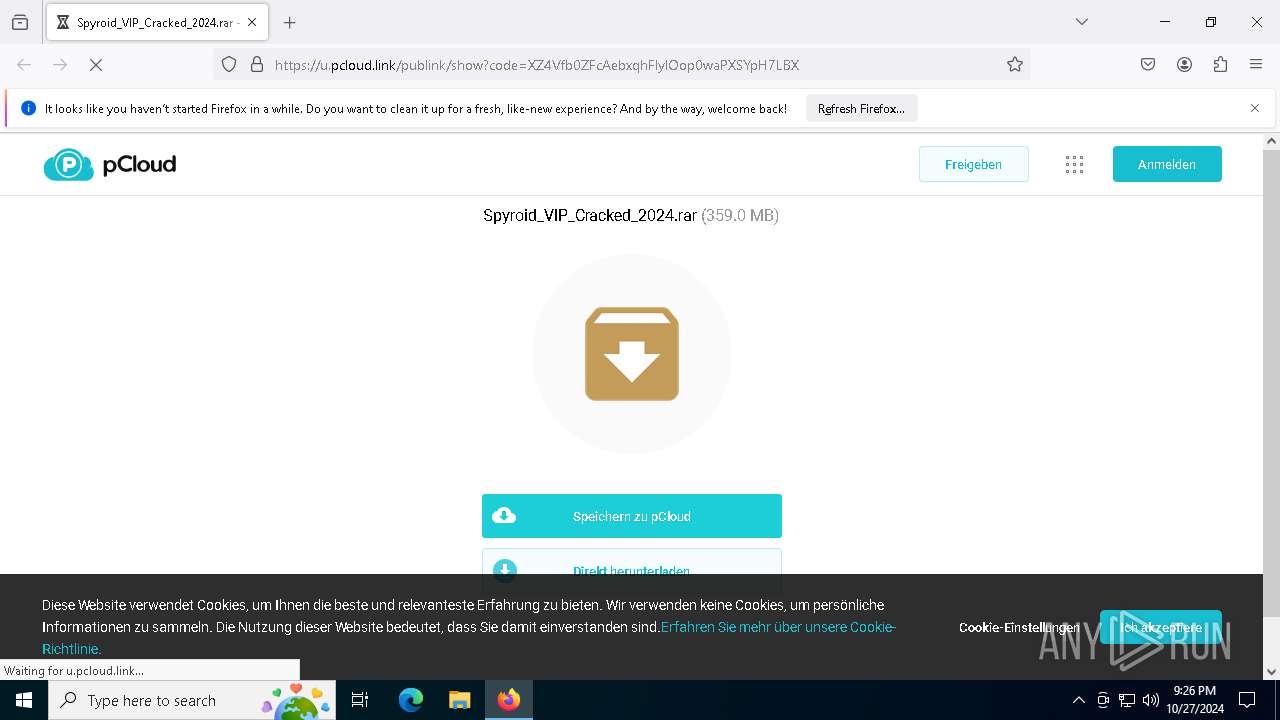
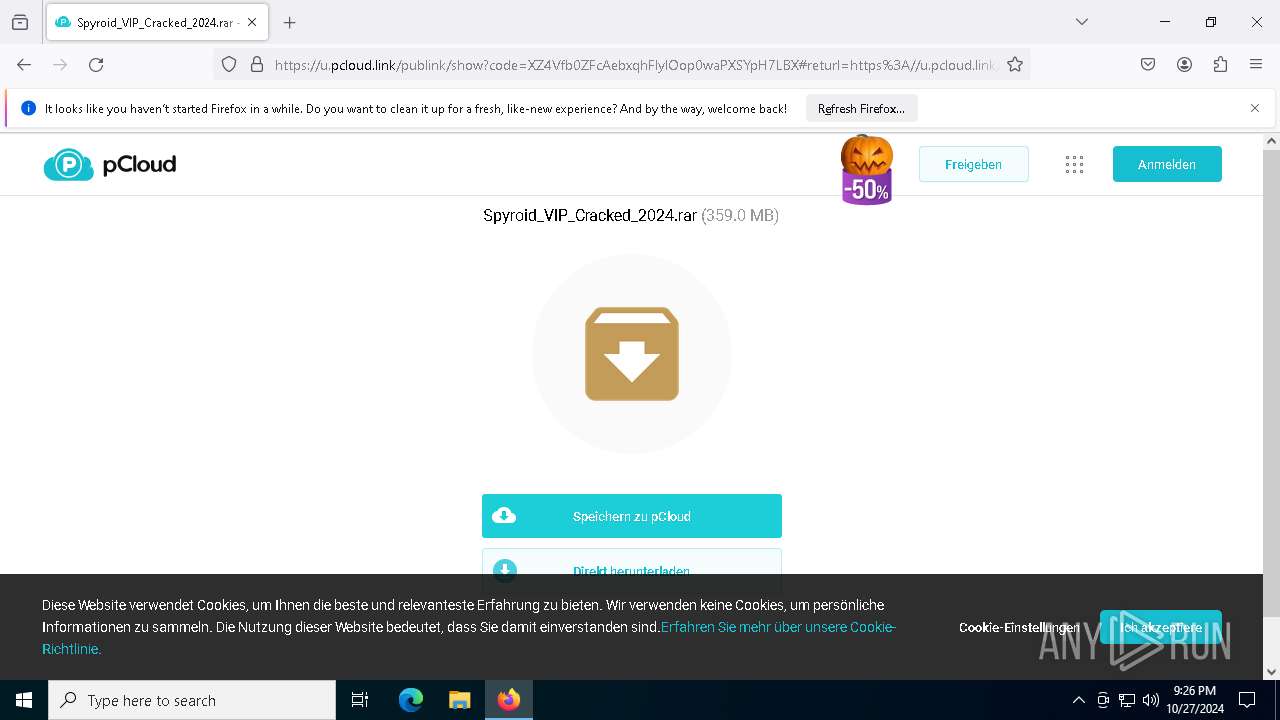
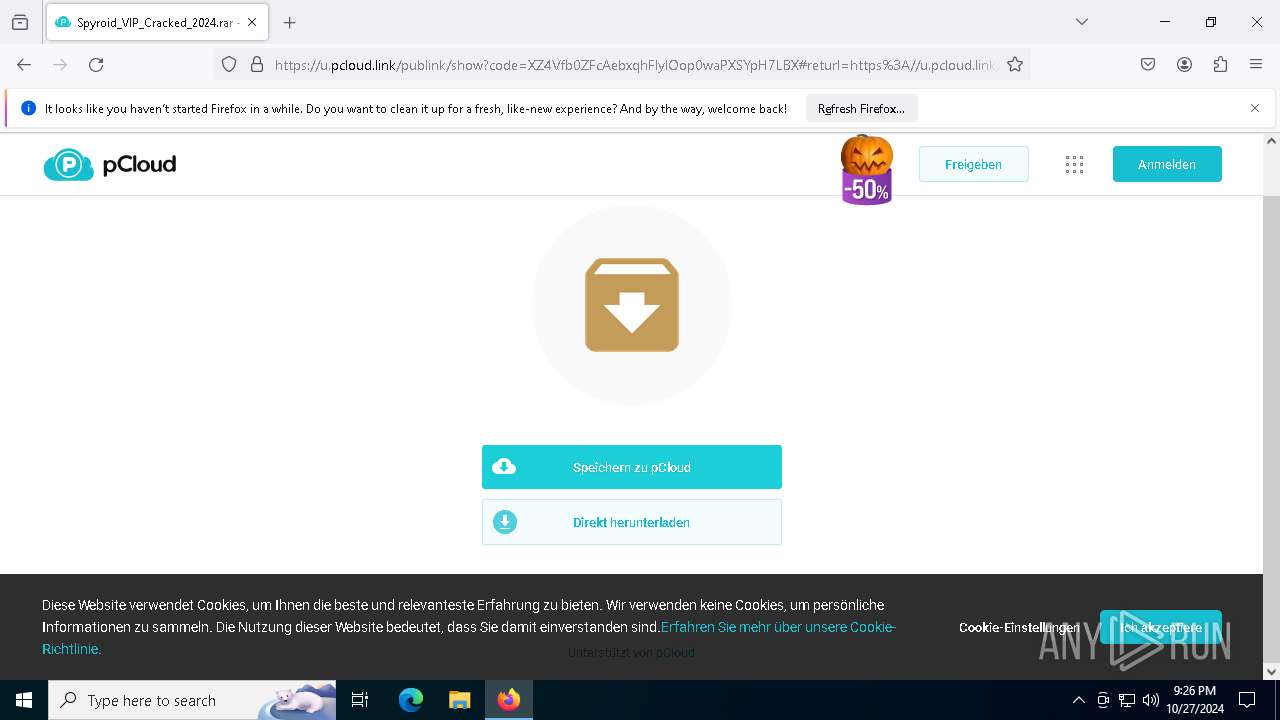
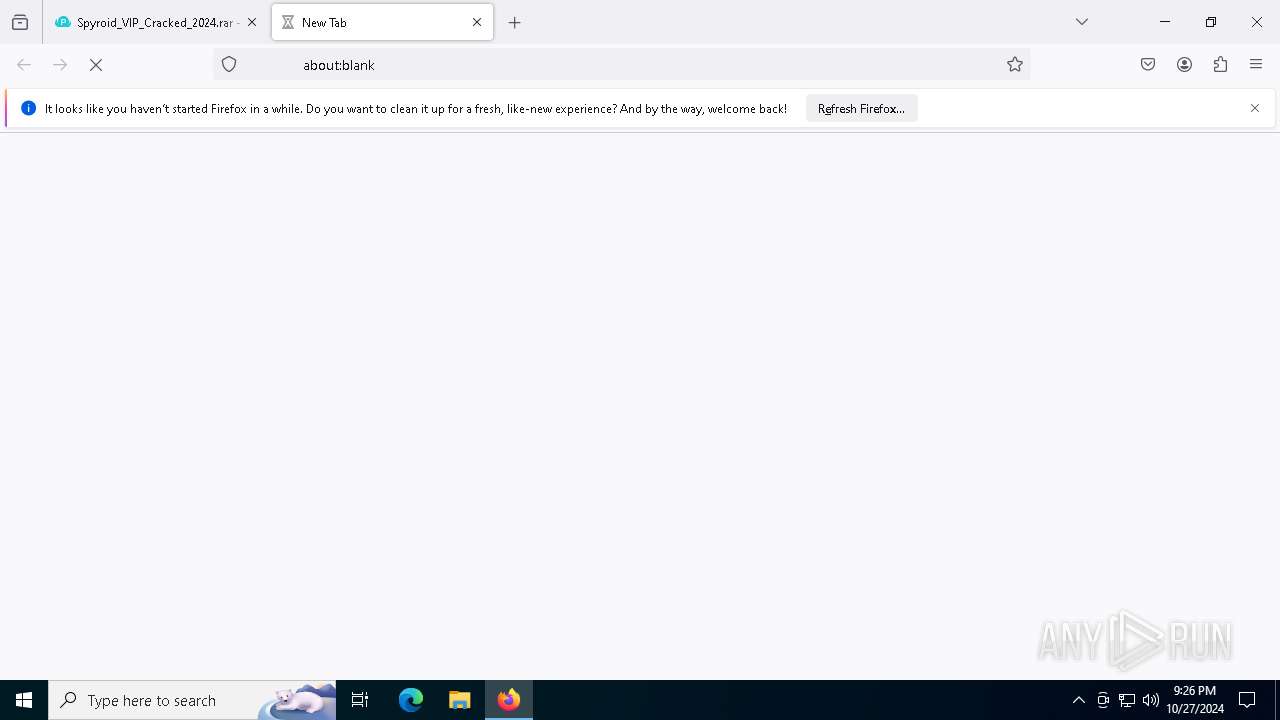
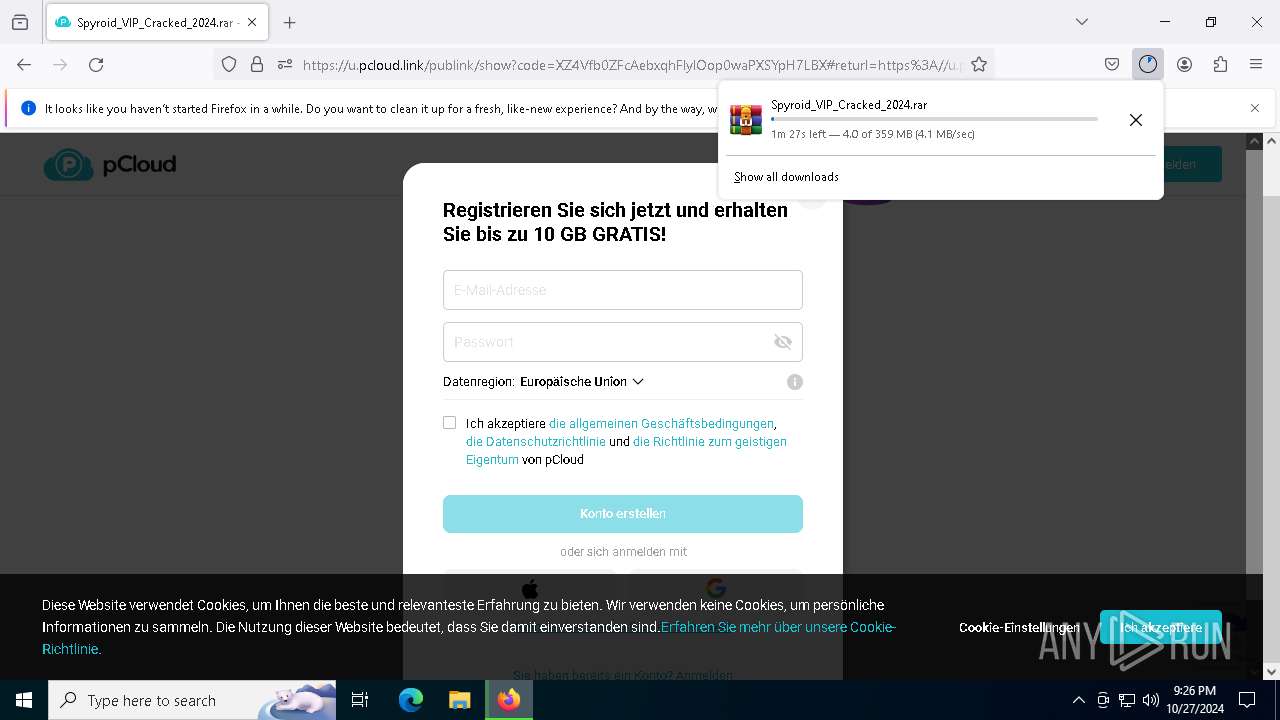
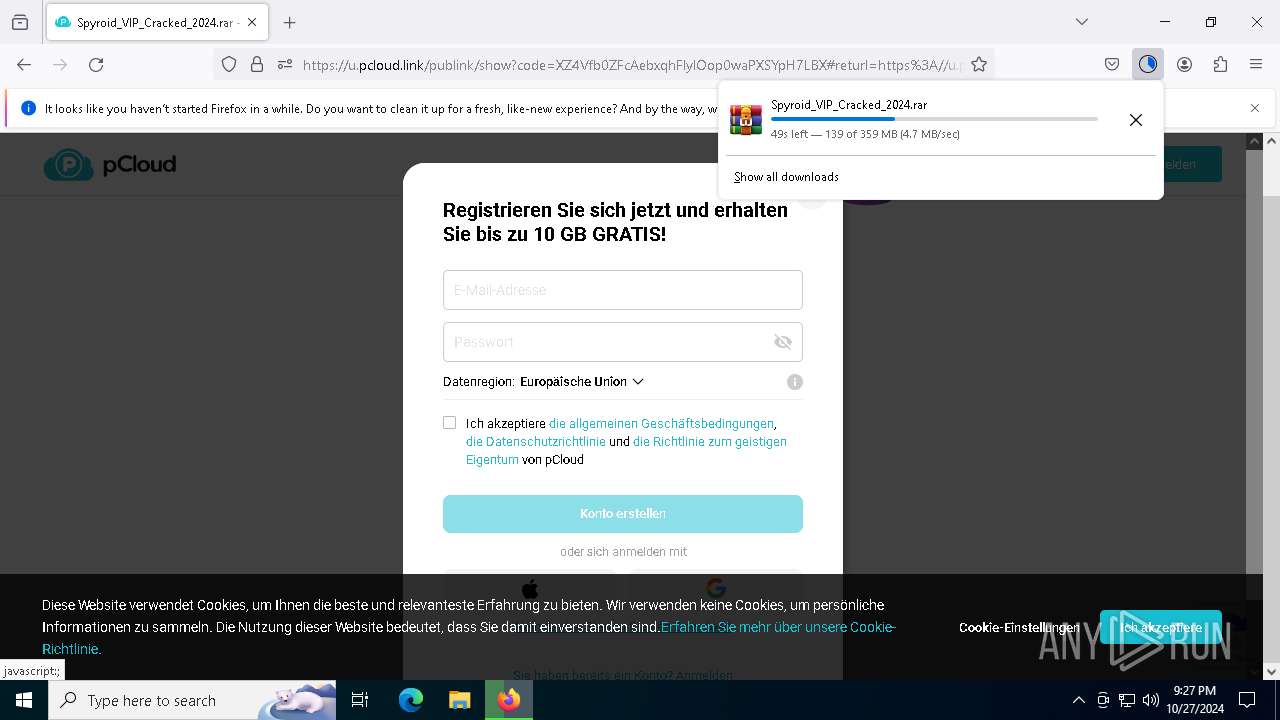
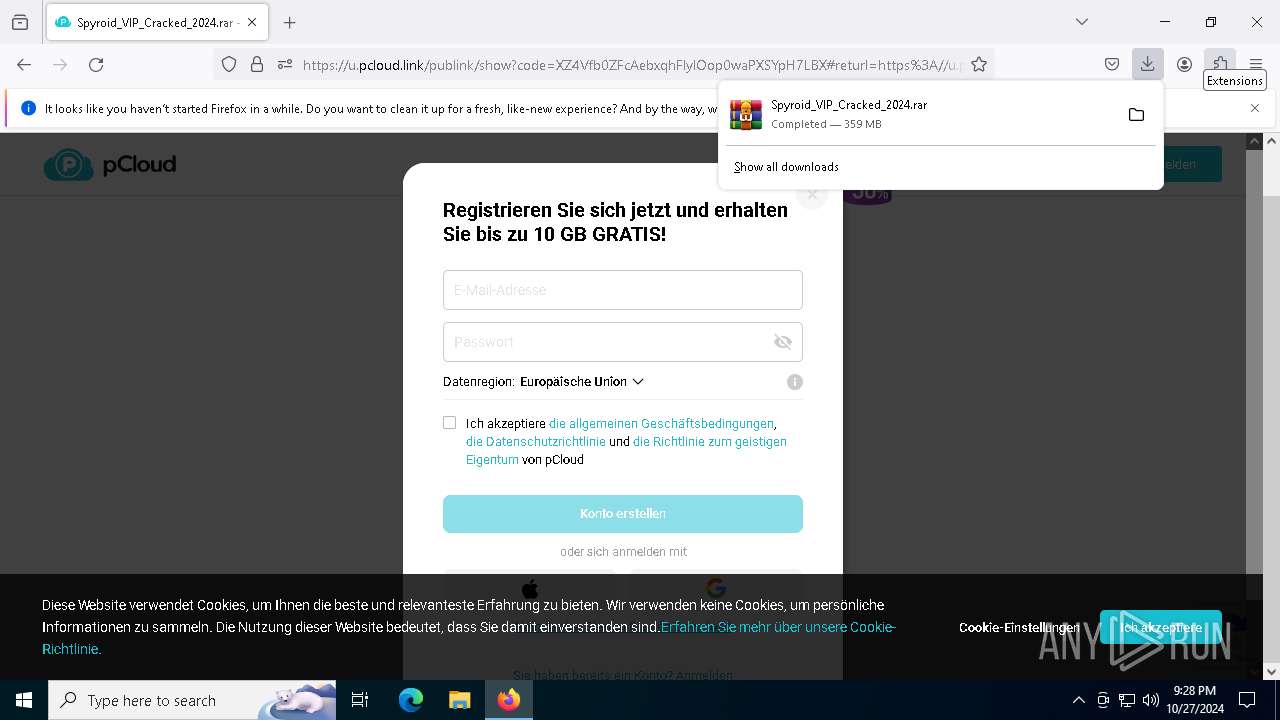
| URL: | https://u.pcloud.link/publink/show?code=XZ4Vfb0ZFcAebxqhFlylOop0waPXSYpH7LBX |
| Full analysis: | https://app.any.run/tasks/f2ad016c-114a-4347-b44f-11beda76b181 |
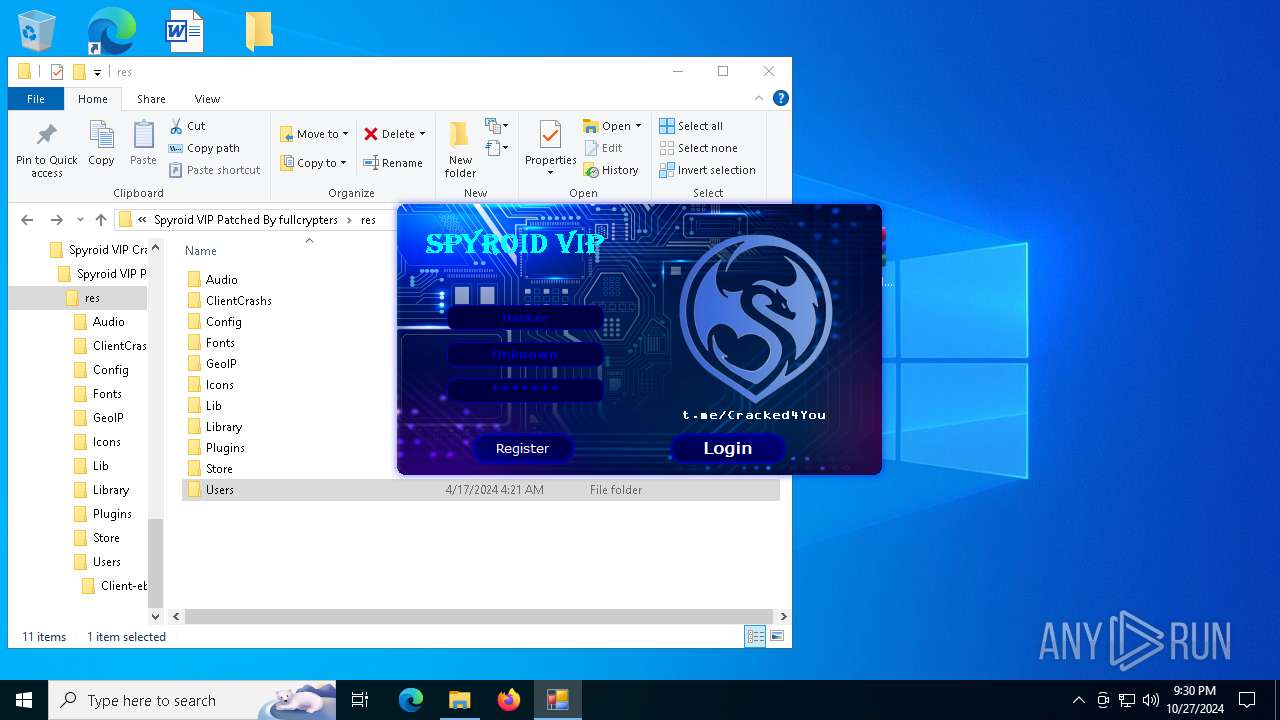
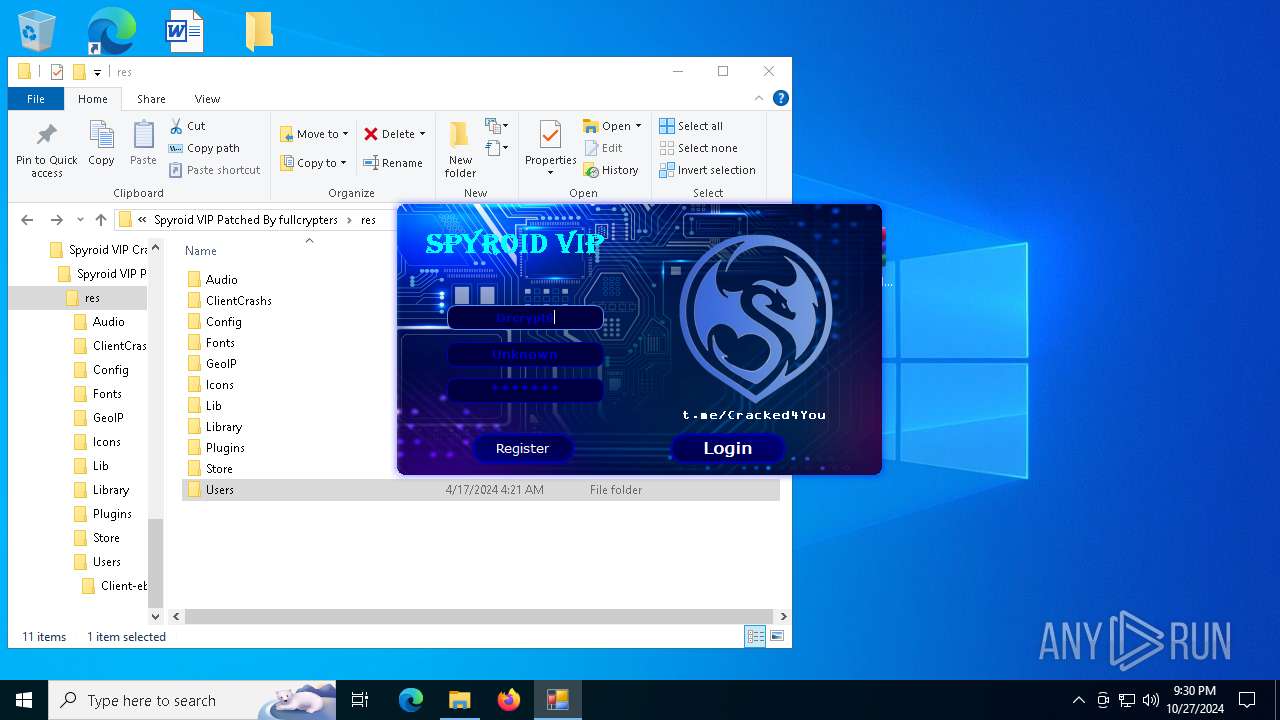
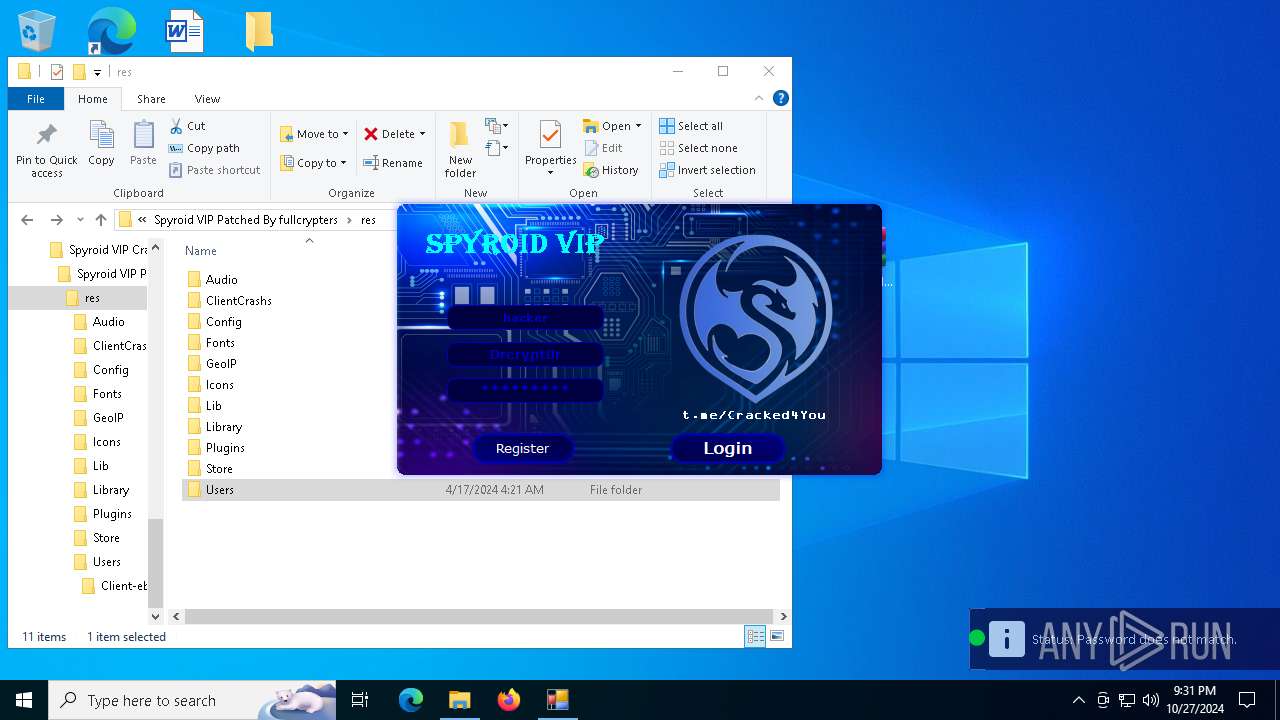
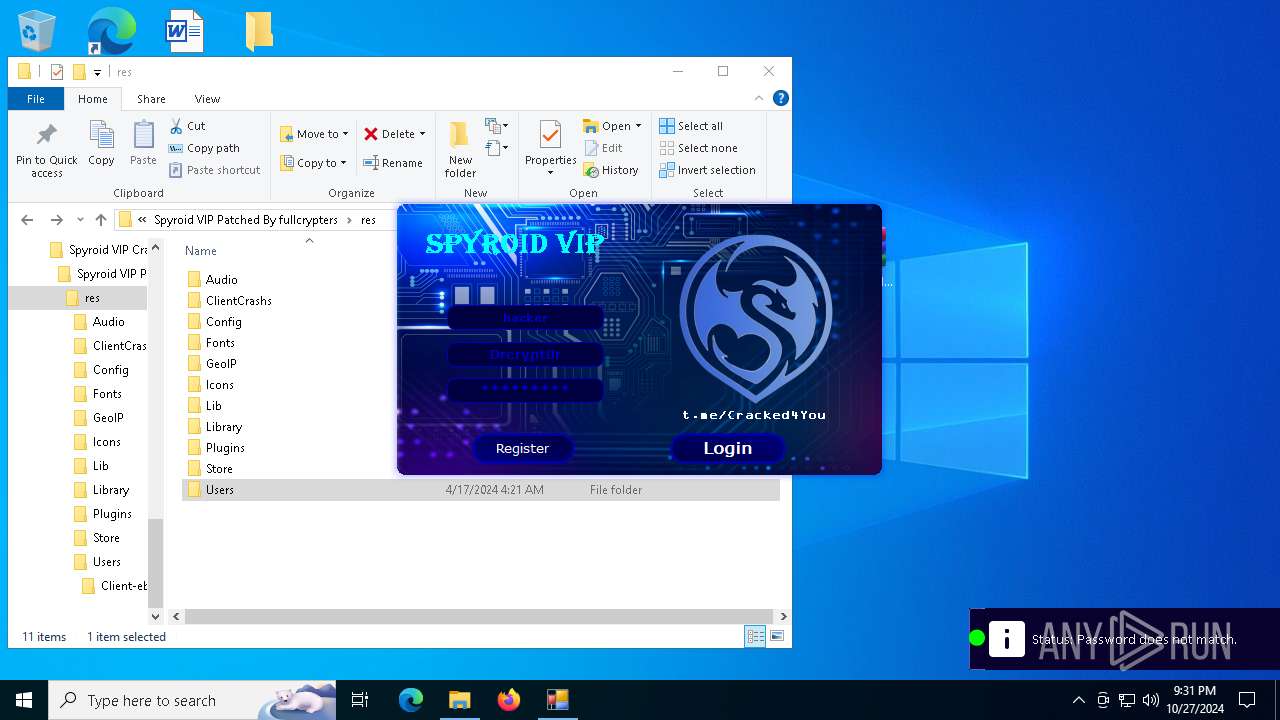
| Verdict: | Malicious activity |
| Analysis date: | October 27, 2024, 21:26:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 57F47BB2C9219427A31D41596E08BCE7 |
| SHA1: | 665A8EF726CE7E59A326F6223413FA0B342E9A9C |
| SHA256: | E31432C61C119301C85093124B81EE2744124D528069C7CD025B898DAB5FF6D7 |
| SSDEEP: | 3:N8sVnLoHCok/b+HdUAZHxgpn9:2sCiokEU6Y9 |
MALICIOUS
XORed URL has been found (YARA)
- Spyroid VIP.exe (PID: 6592)
- Spyroid VIP.exe (PID: 1396)
SUSPICIOUS
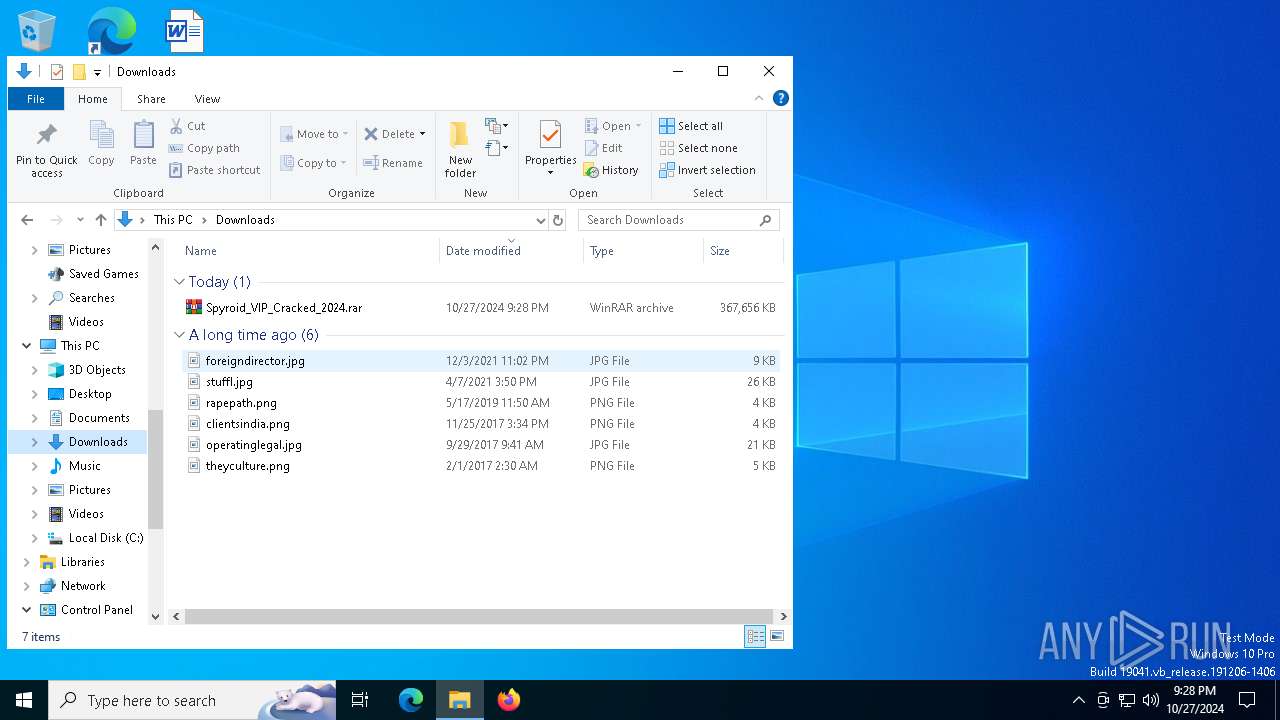
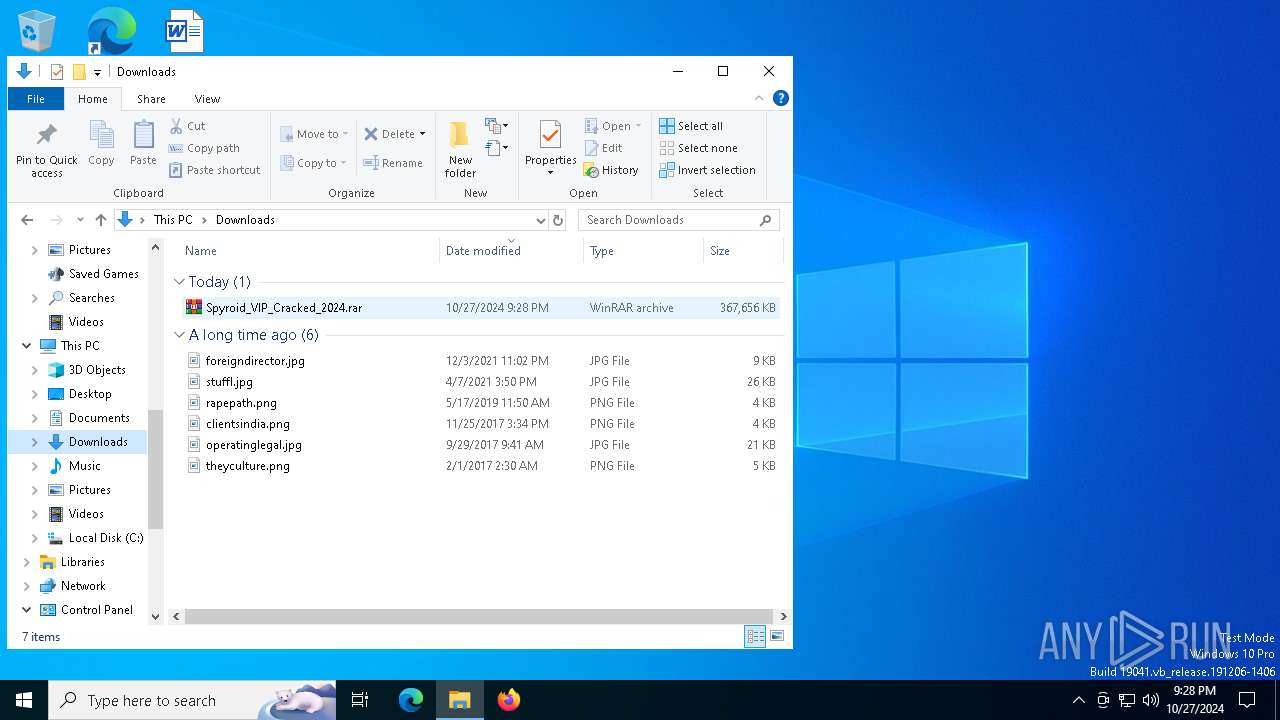
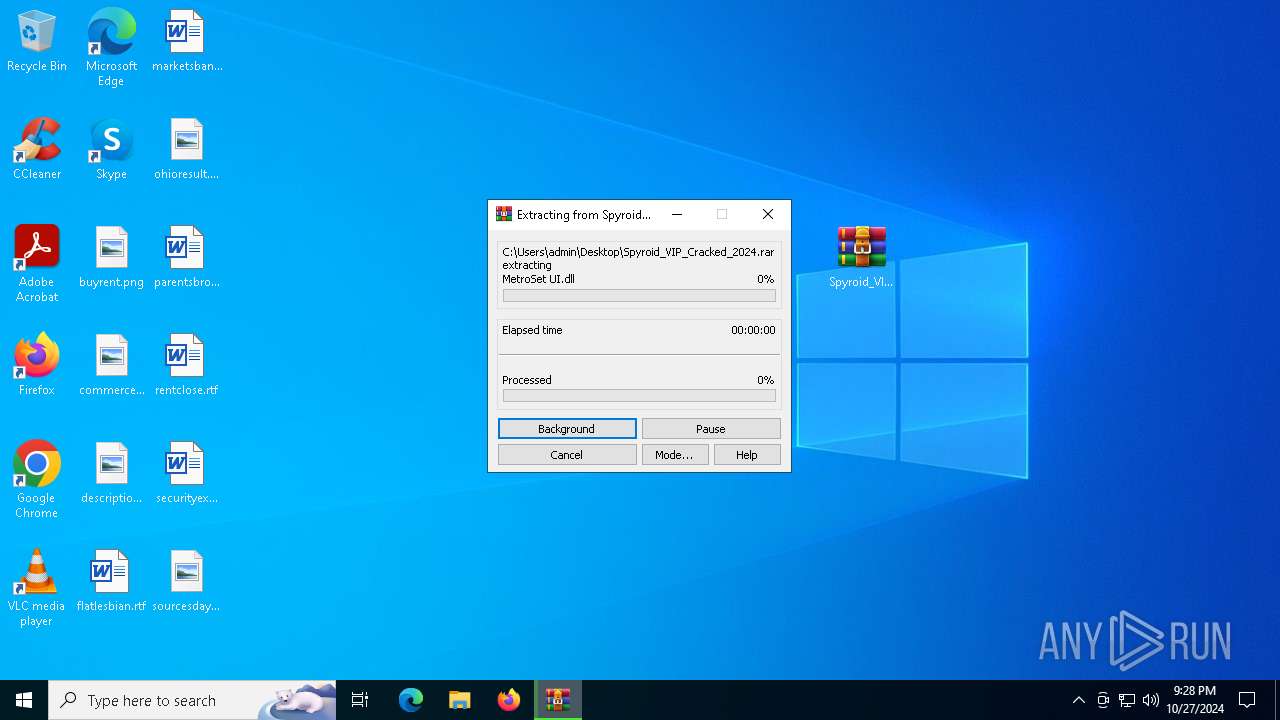
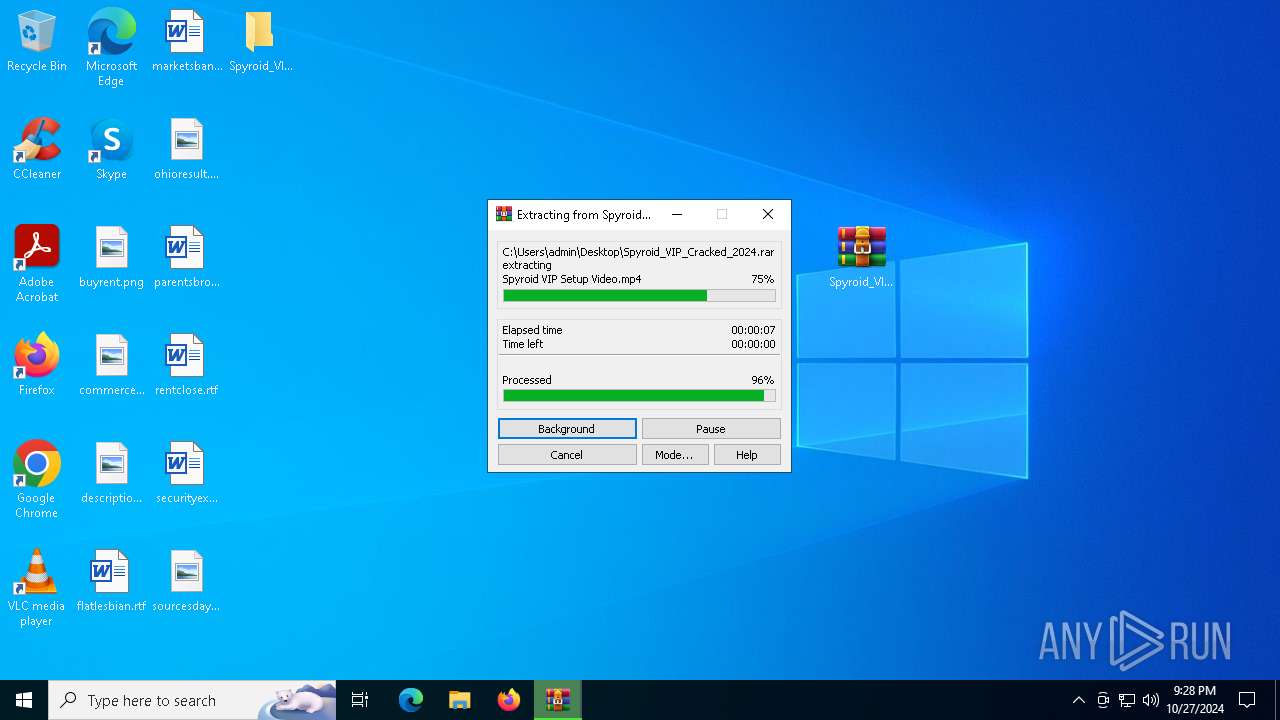
Drops 7-zip archiver for unpacking
- WinRAR.exe (PID: 8152)
Process drops legitimate windows executable
- WinRAR.exe (PID: 8152)
Reads security settings of Internet Explorer
- Spyroid VIP.exe (PID: 6592)
- Spyroid VIP.exe (PID: 1396)
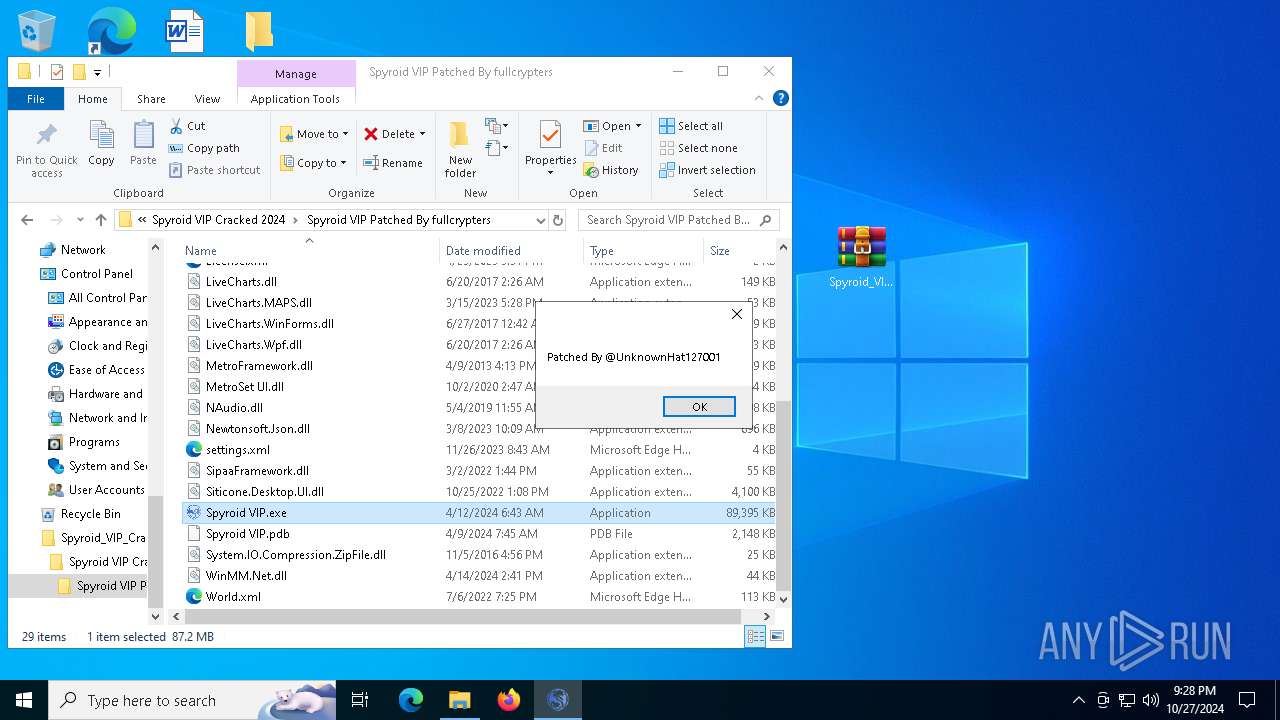
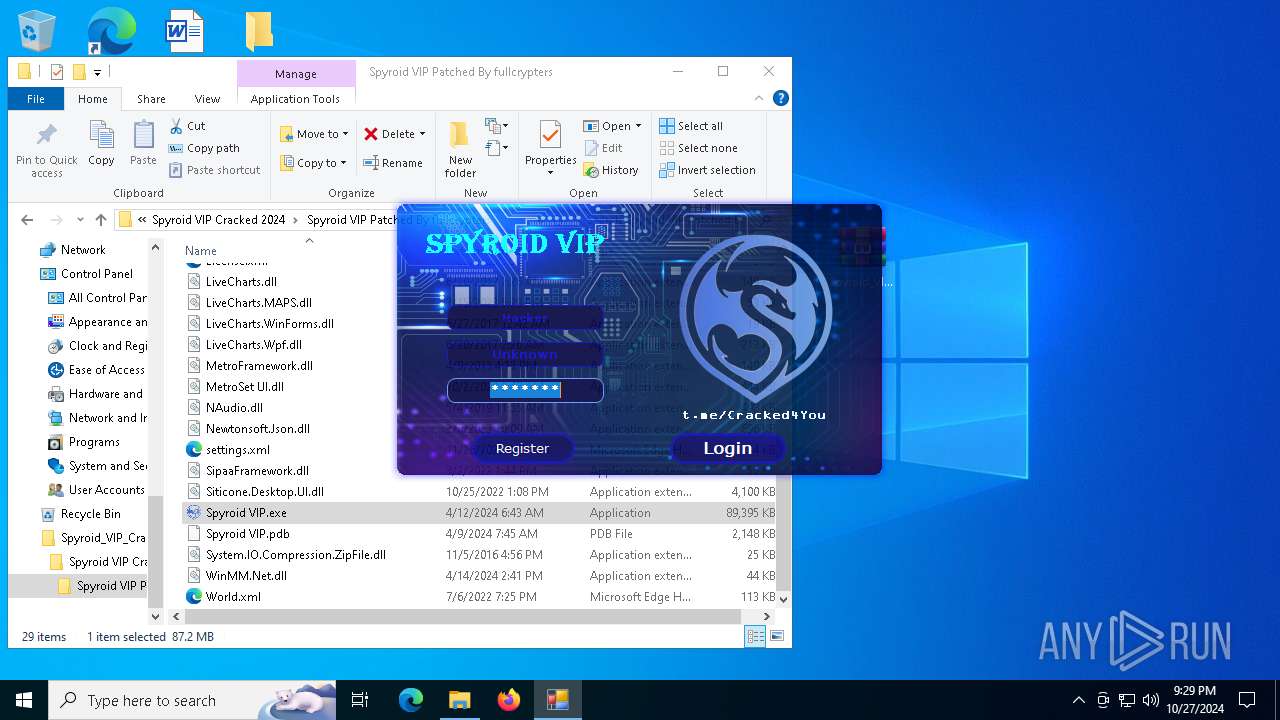
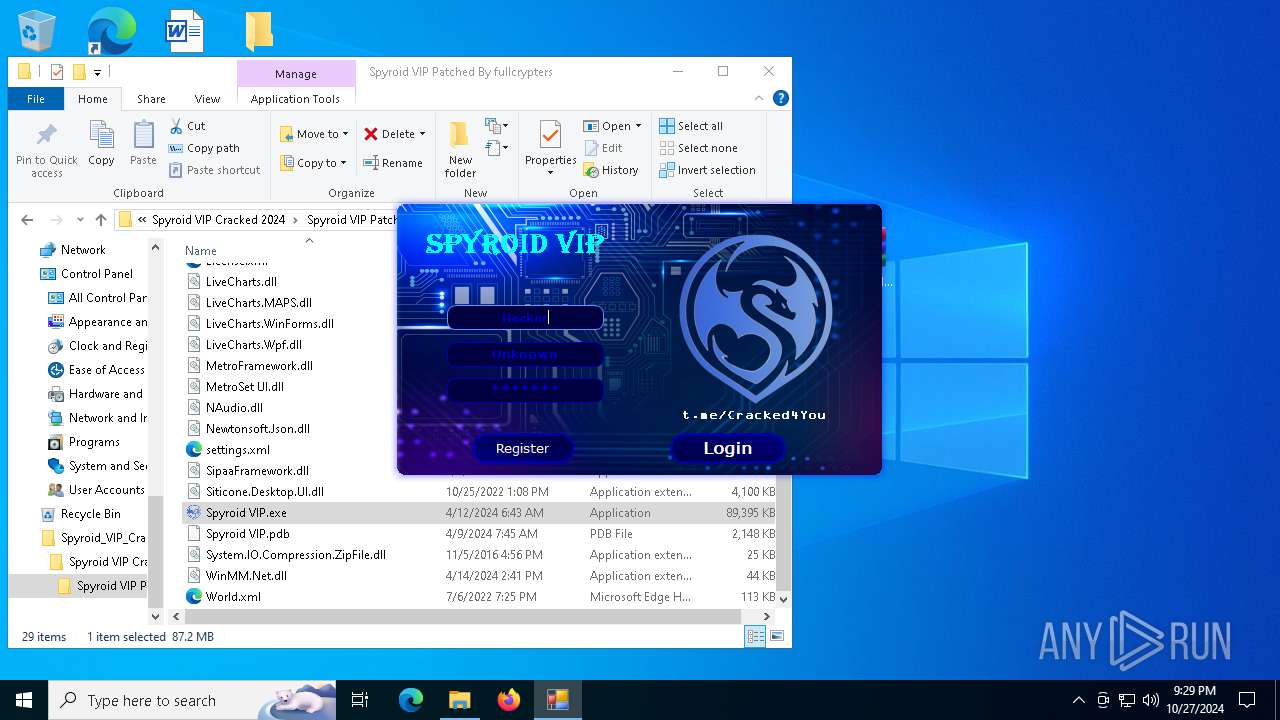
Application launched itself
- Spyroid VIP.exe (PID: 6592)
Reads the date of Windows installation
- Spyroid VIP.exe (PID: 6592)
INFO
Executable content was dropped or overwritten
- firefox.exe (PID: 5516)
- WinRAR.exe (PID: 8152)
Application launched itself
- firefox.exe (PID: 6224)
- firefox.exe (PID: 5516)
Checks supported languages
- Spyroid VIP.exe (PID: 6592)
- Spyroid VIP.exe (PID: 1396)
Reads the computer name
- Spyroid VIP.exe (PID: 6592)
- Spyroid VIP.exe (PID: 1396)
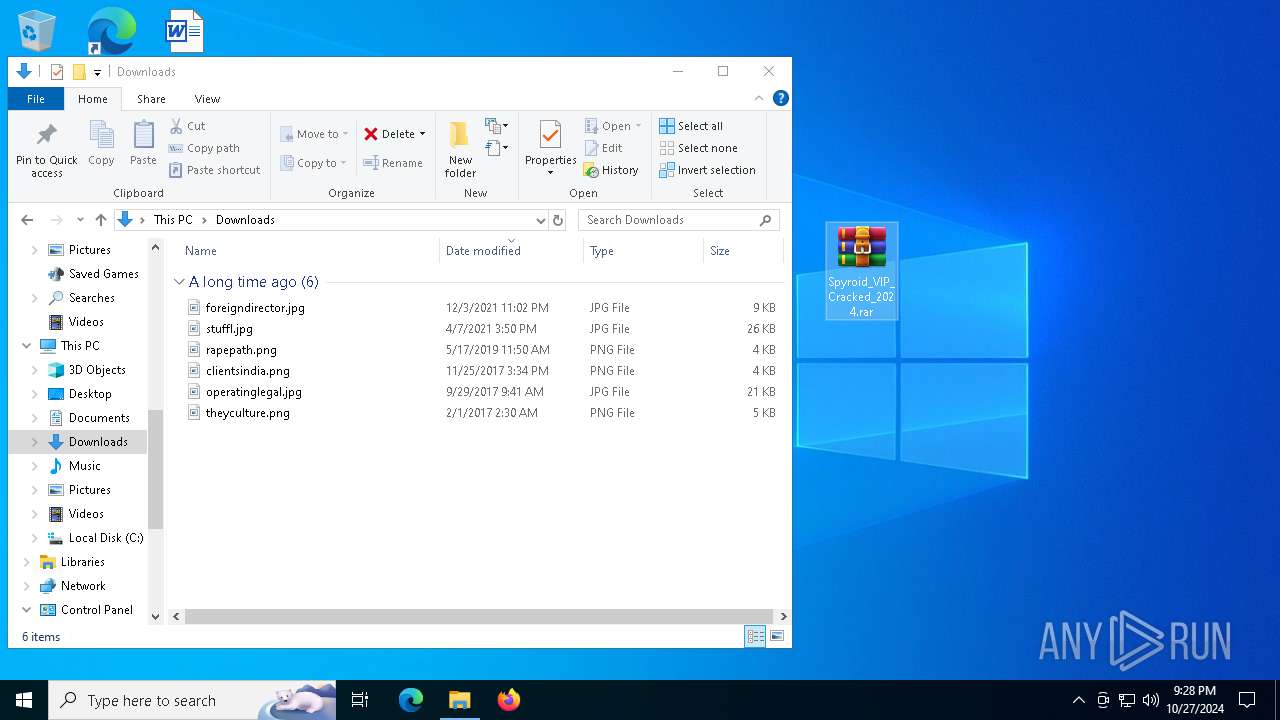
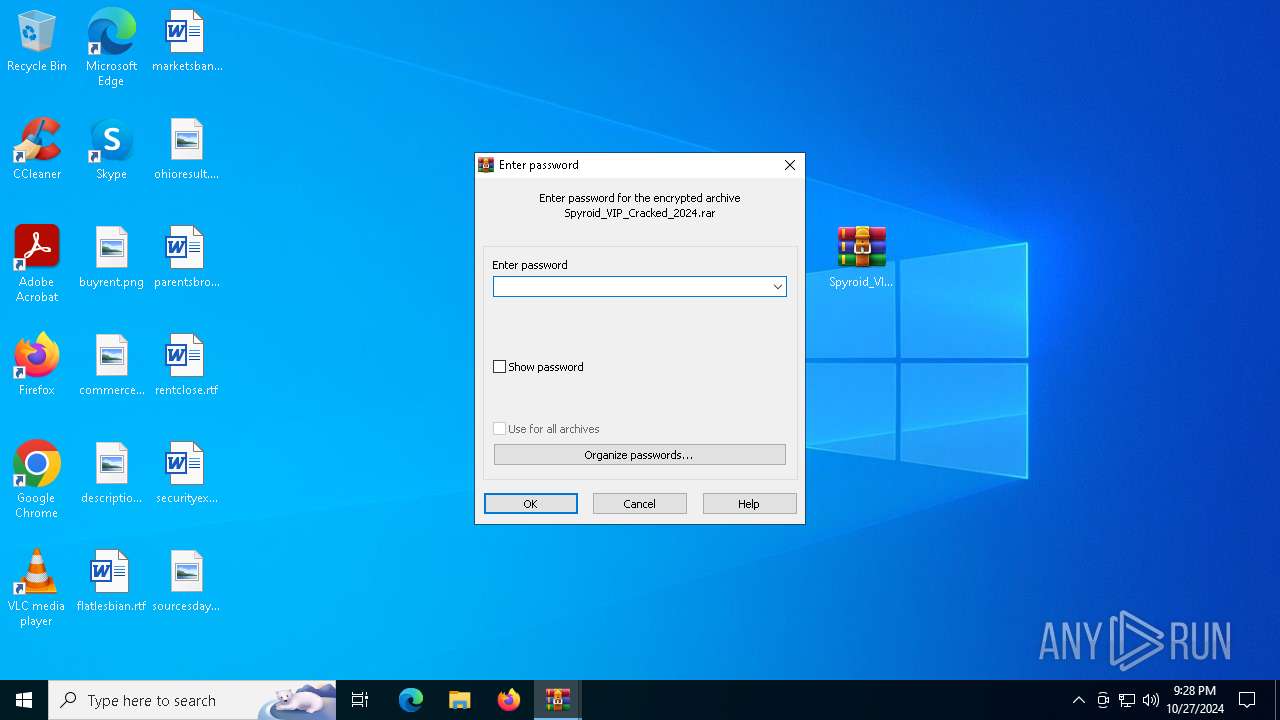
The process uses the downloaded file
- WinRAR.exe (PID: 8152)
- Spyroid VIP.exe (PID: 6592)
- firefox.exe (PID: 5516)
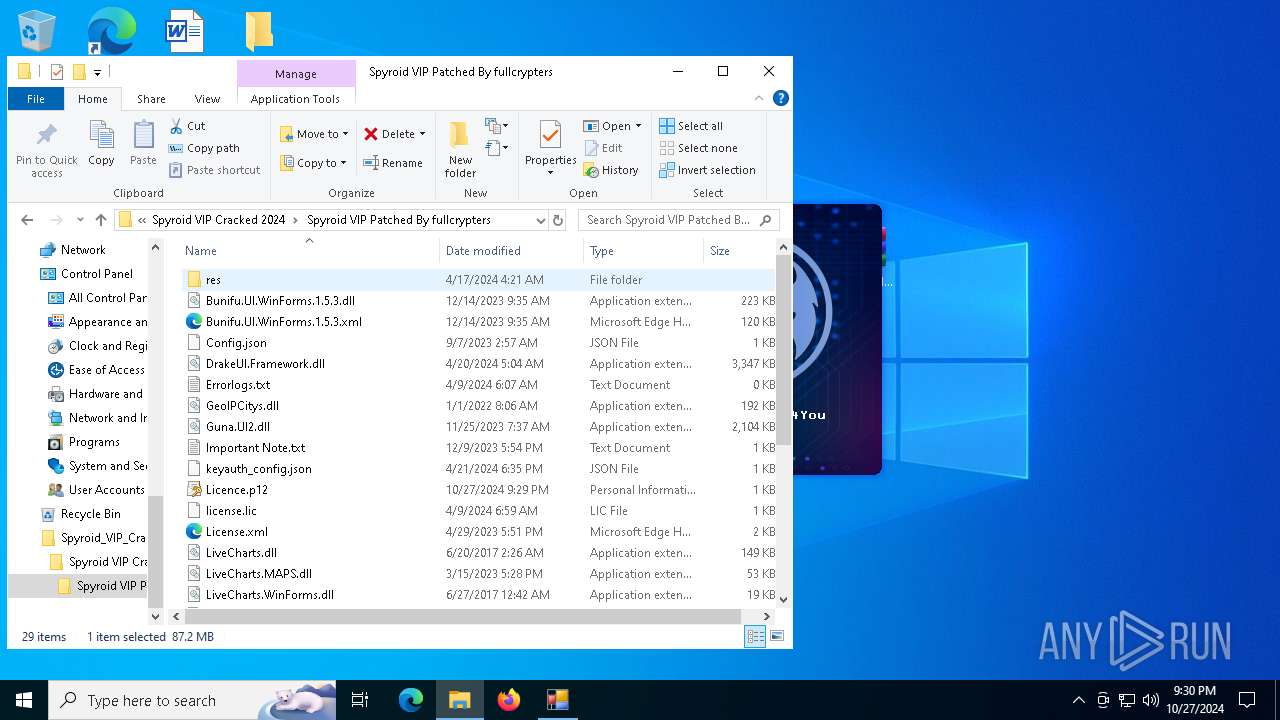
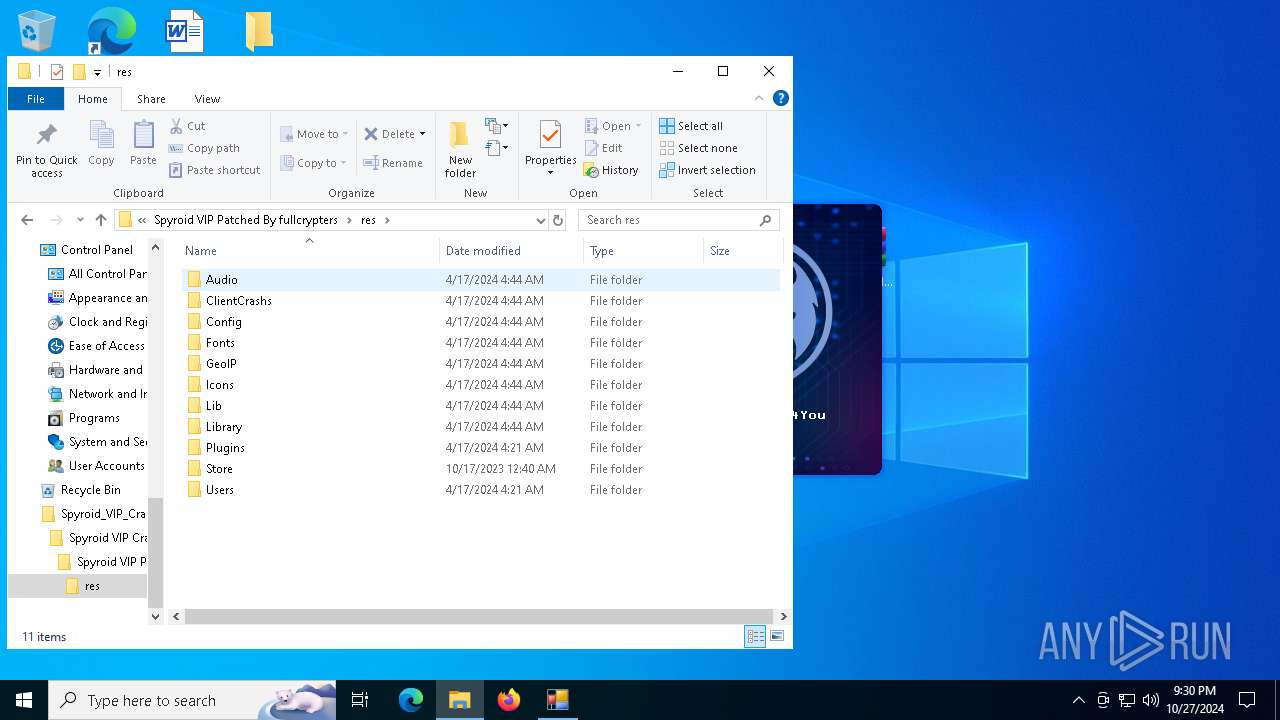
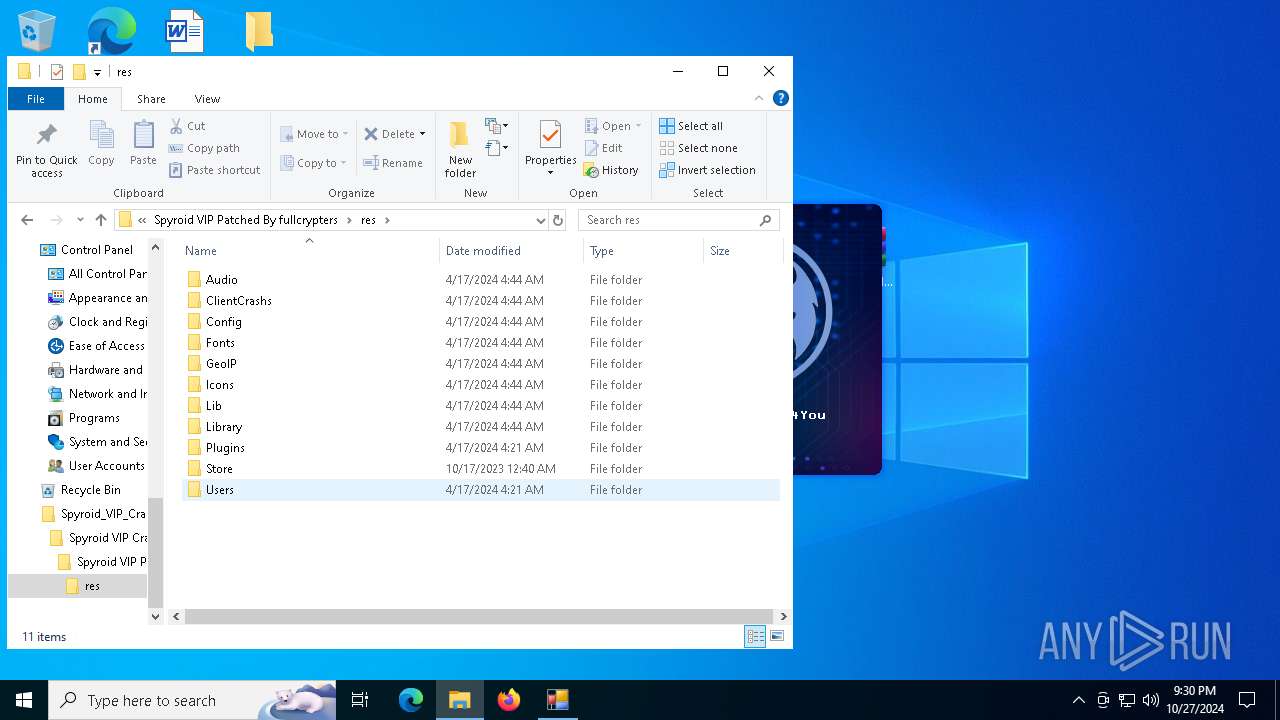
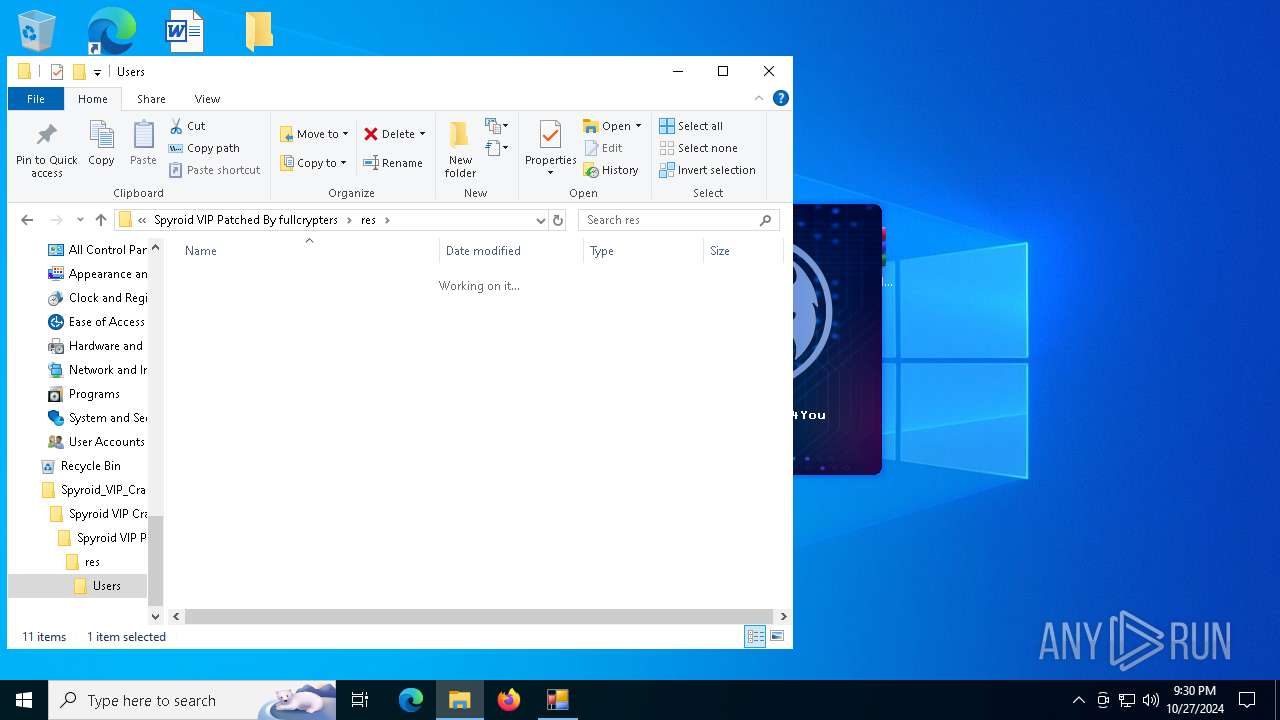
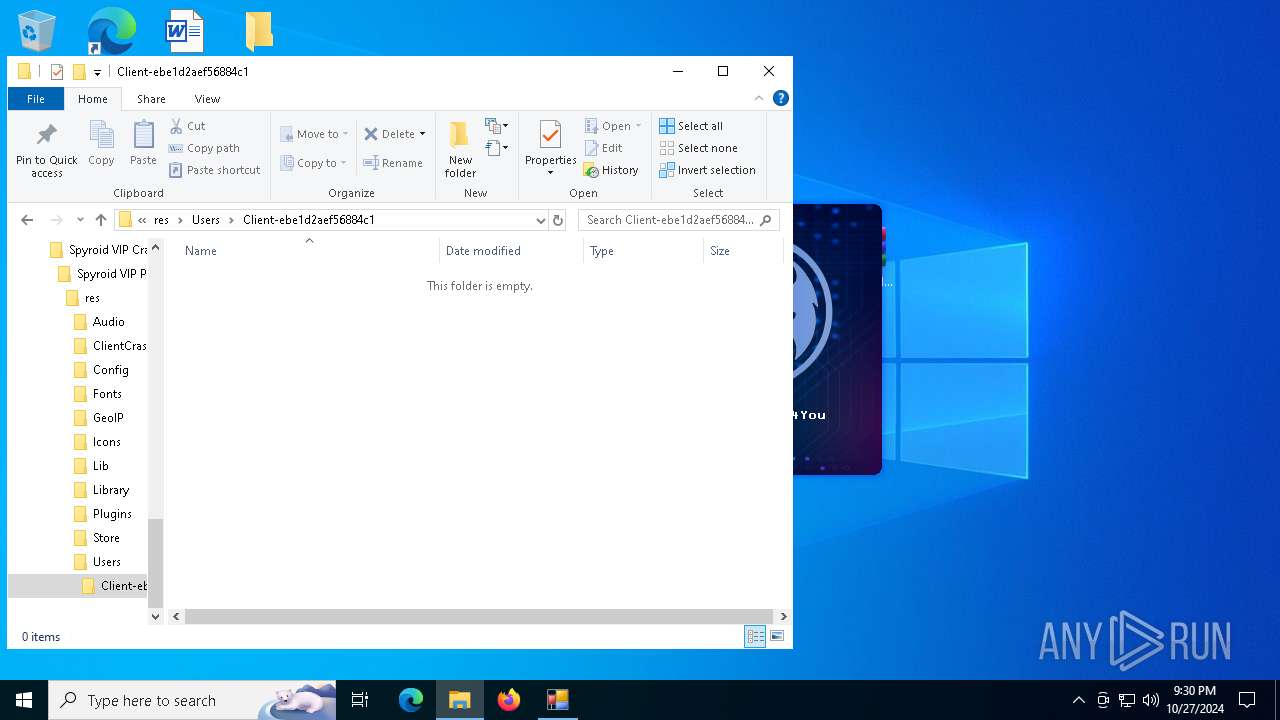
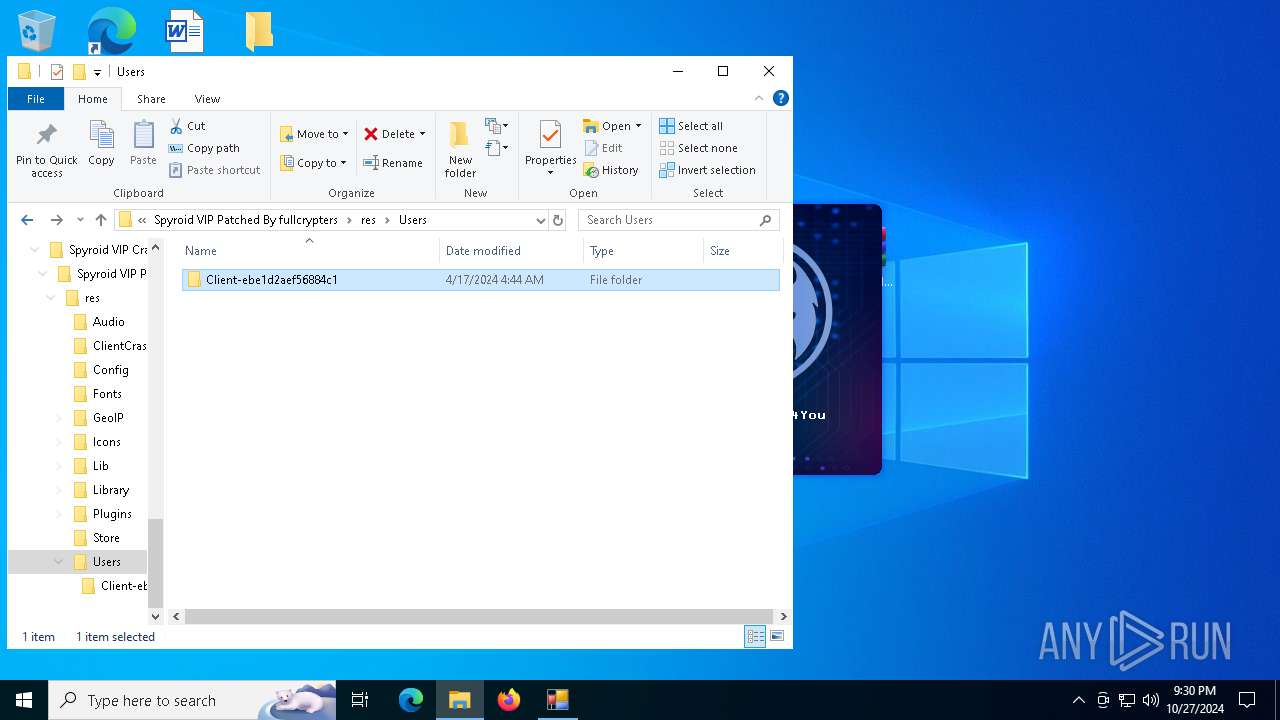
Creates files in the program directory
- Spyroid VIP.exe (PID: 6592)
- Spyroid VIP.exe (PID: 1396)
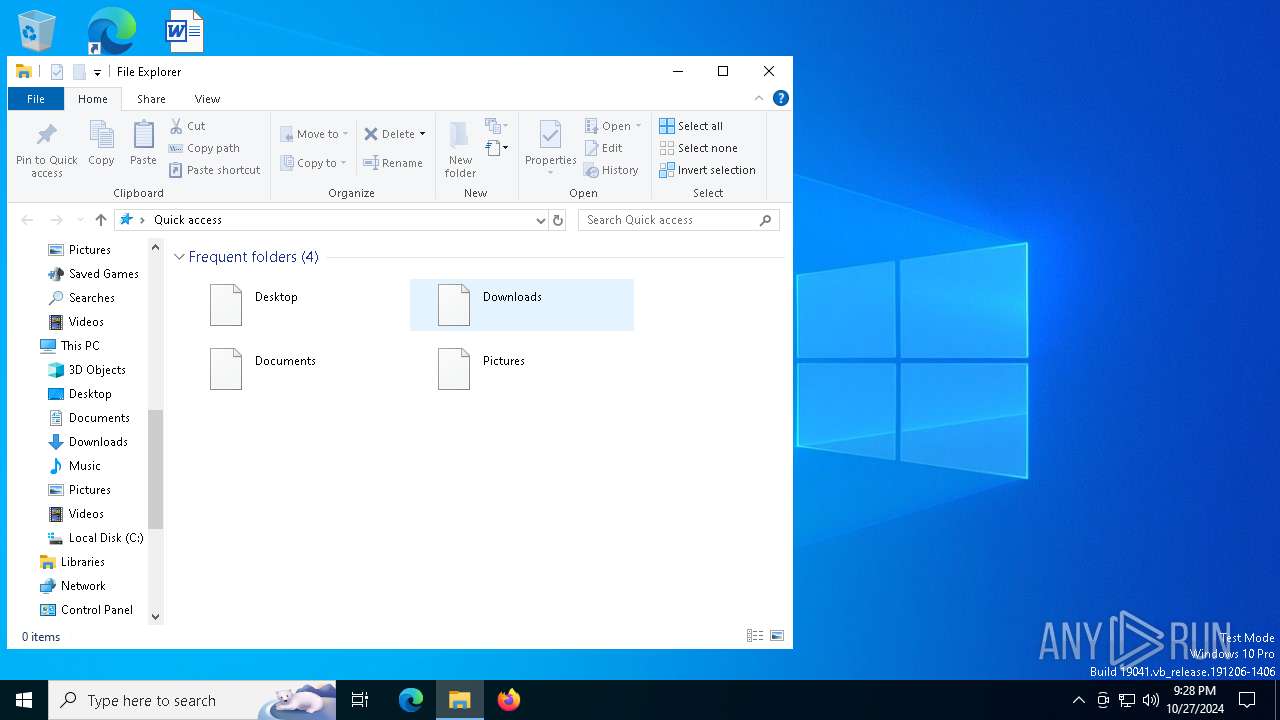
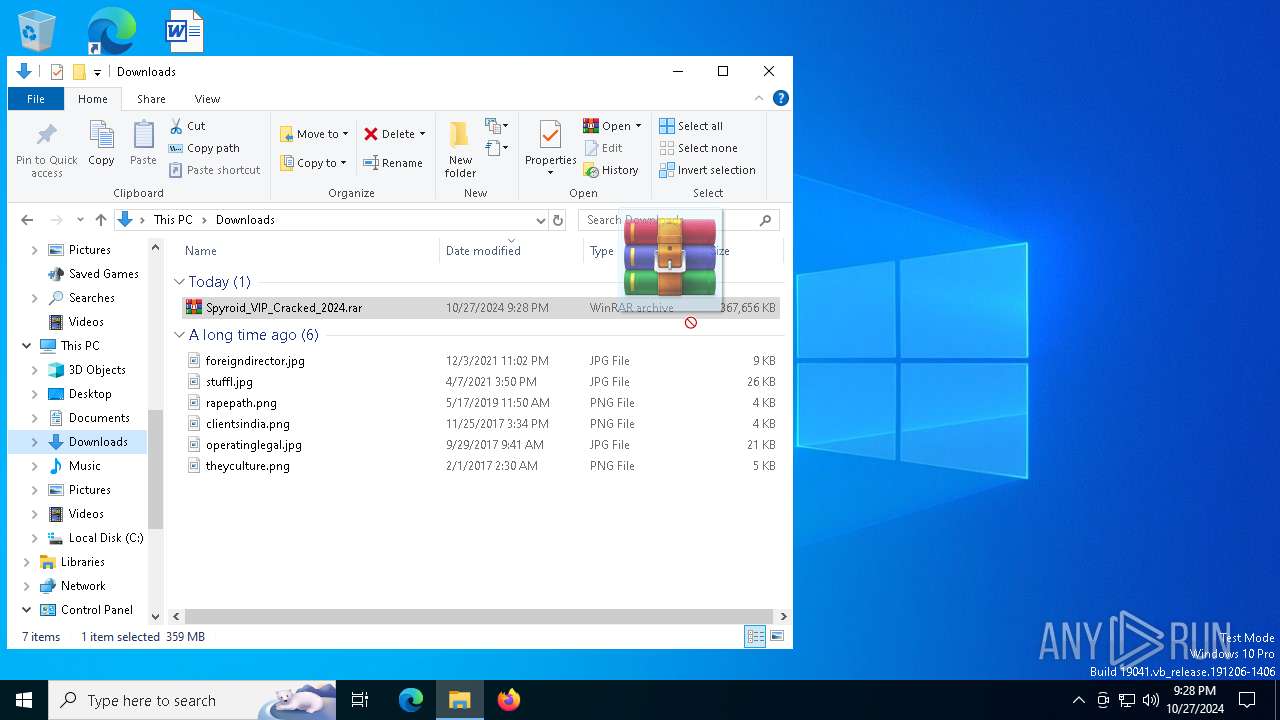
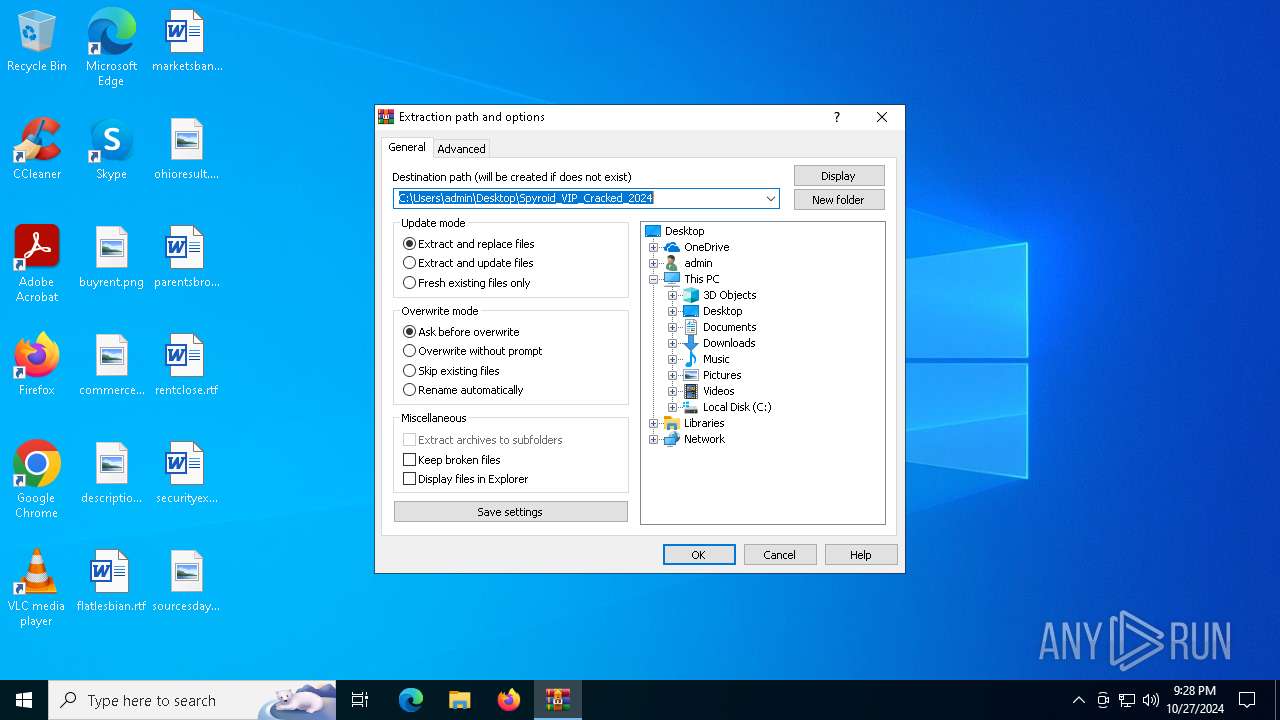
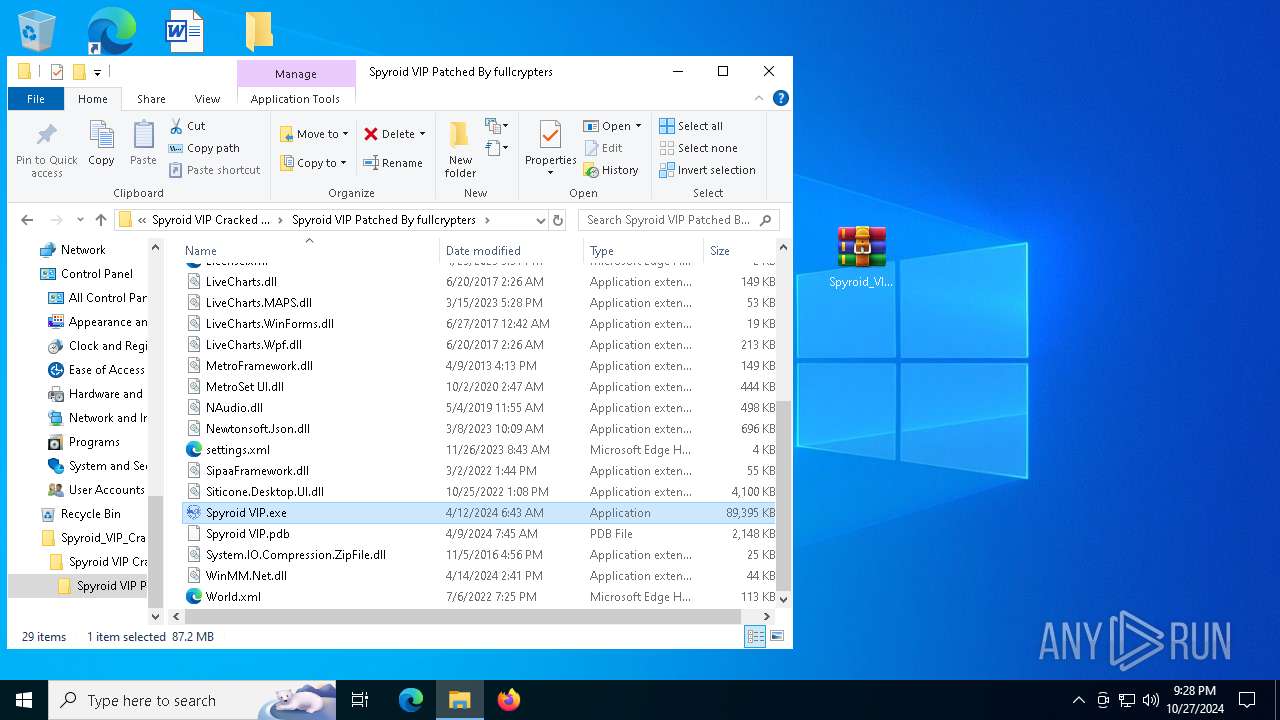
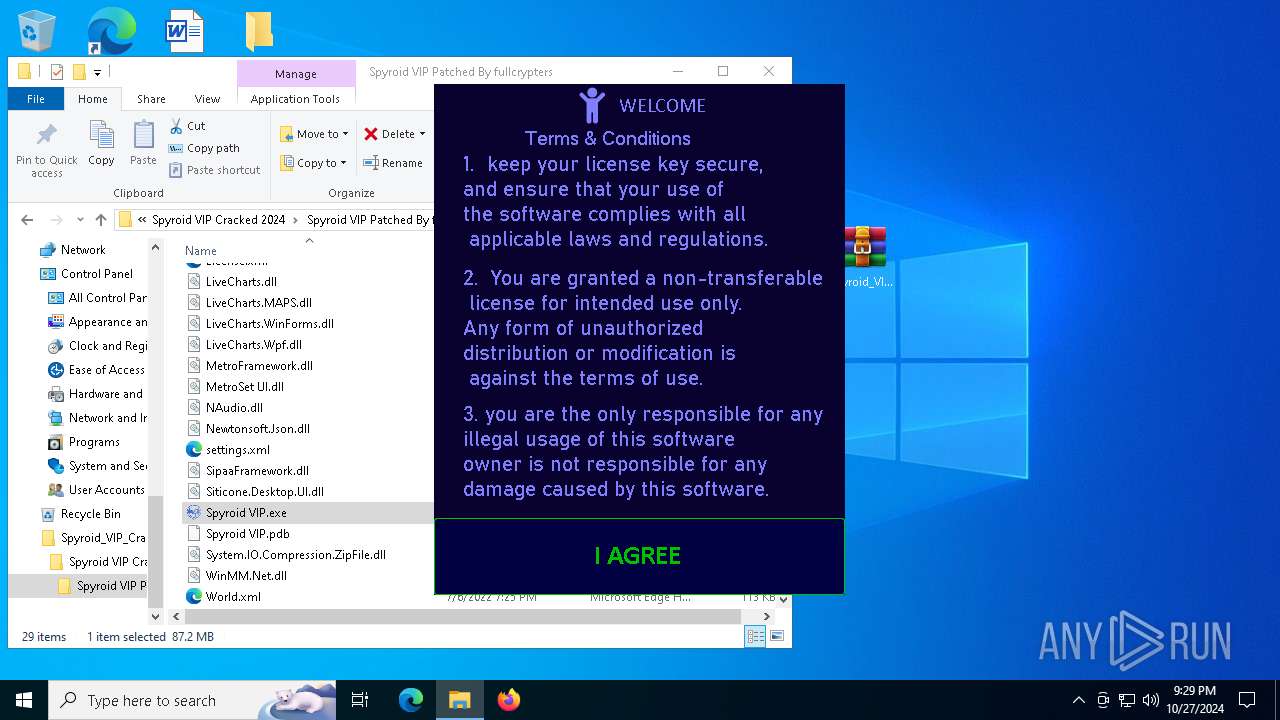
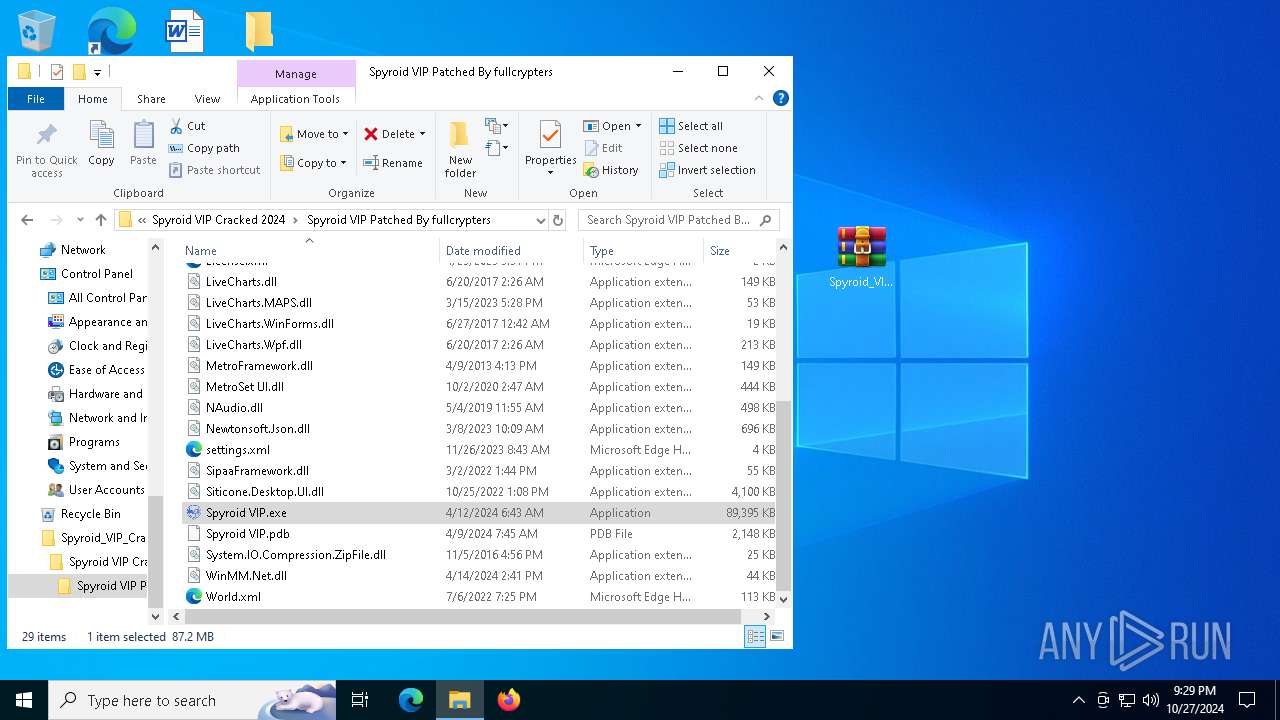
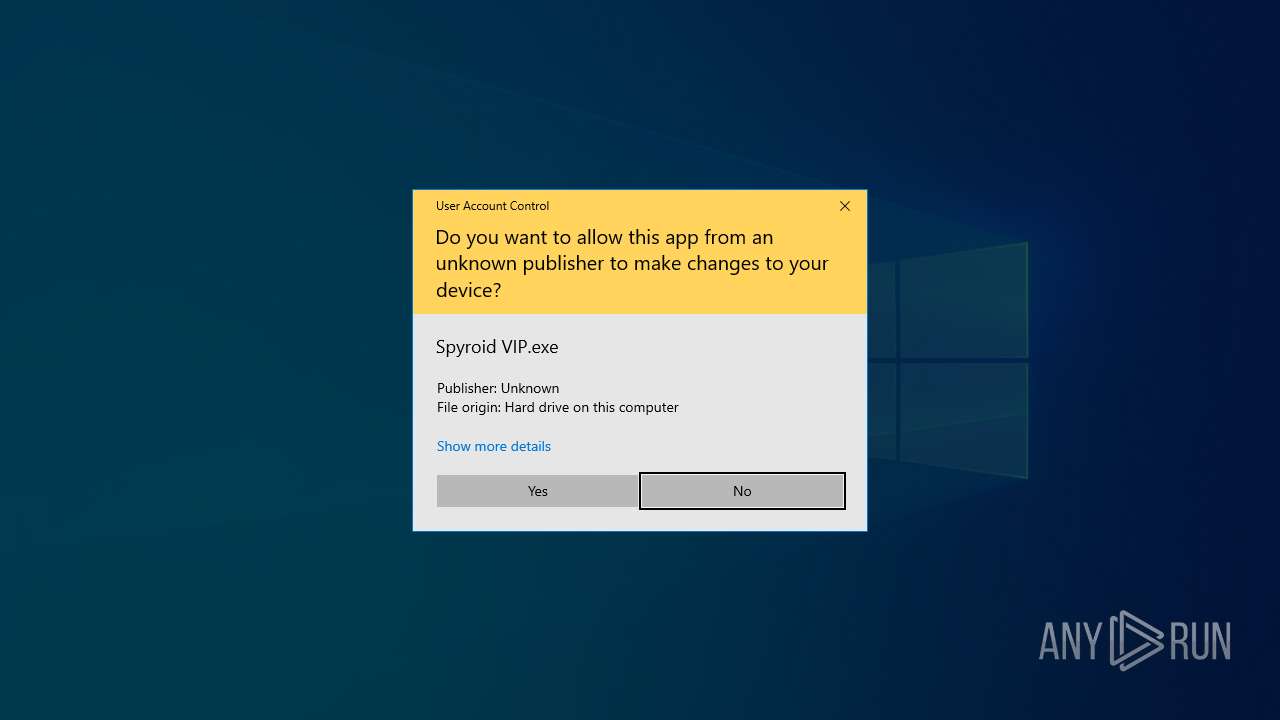
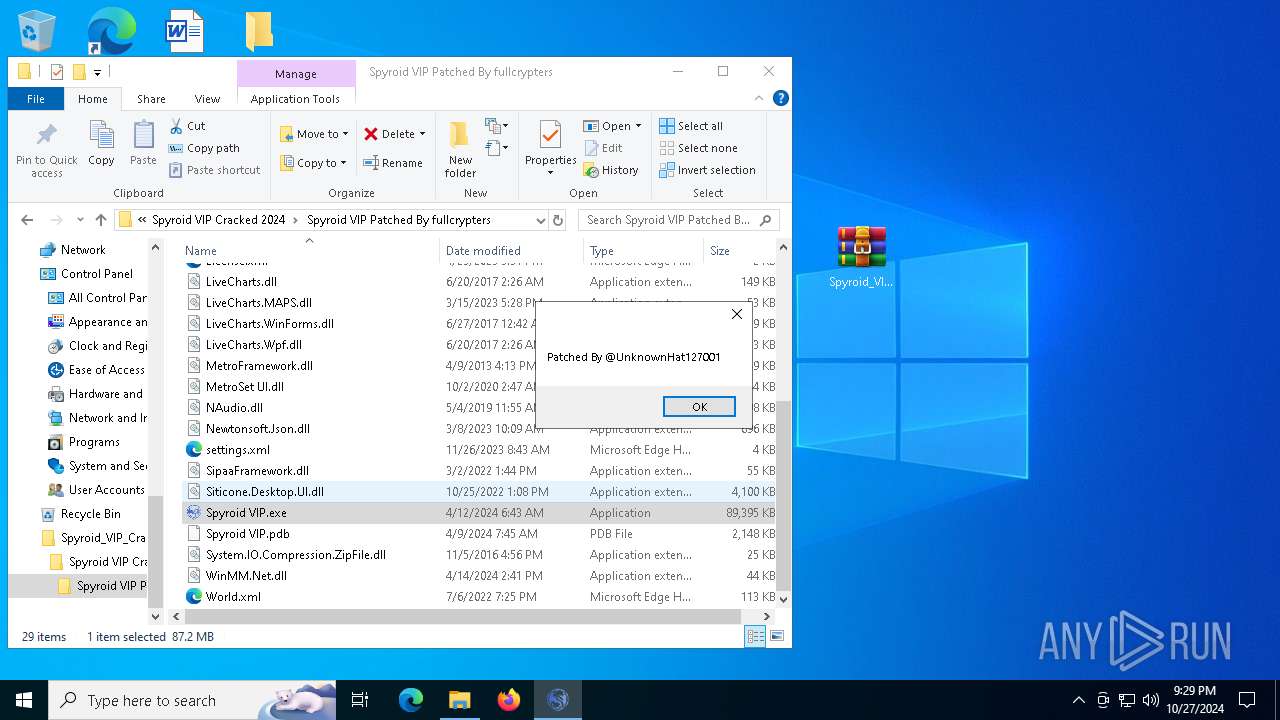
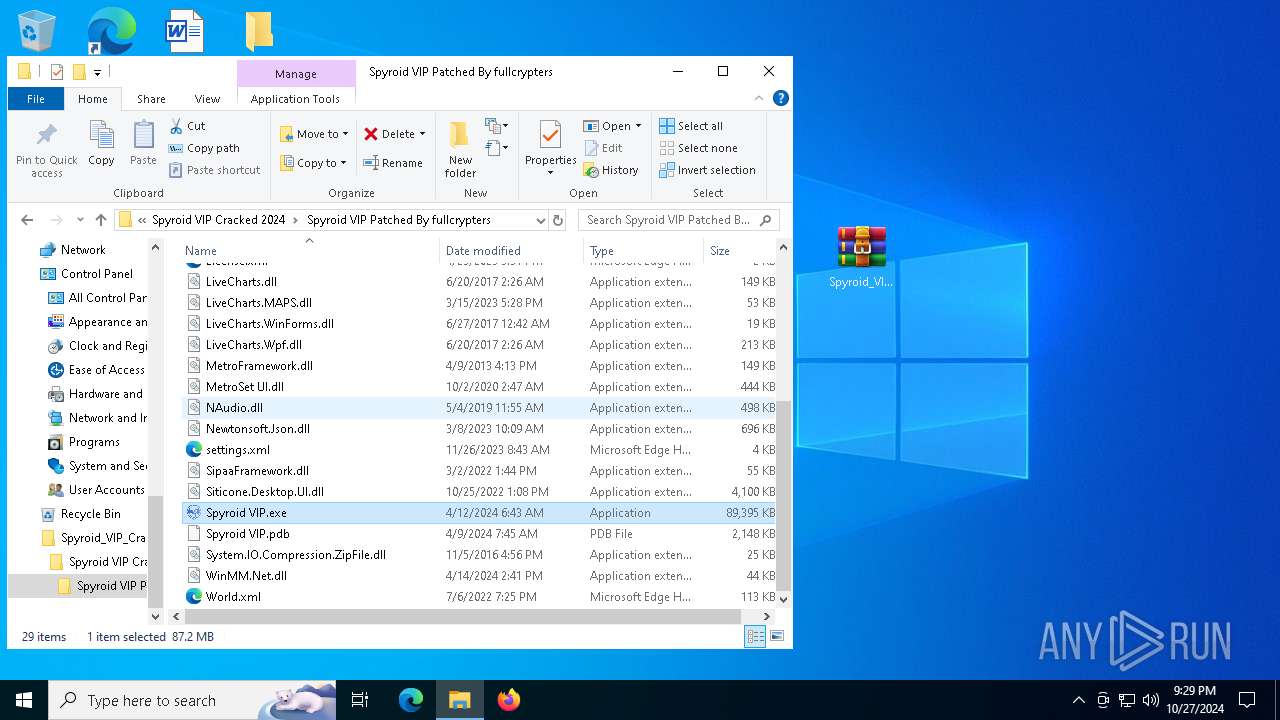
Manual execution by a user
- Spyroid VIP.exe (PID: 6592)
- WinRAR.exe (PID: 8152)
Reads the machine GUID from the registry
- Spyroid VIP.exe (PID: 6592)
- Spyroid VIP.exe (PID: 1396)
Reads the software policy settings
- slui.exe (PID: 2420)
- Spyroid VIP.exe (PID: 1396)
- slui.exe (PID: 6844)
Checks proxy server information
- slui.exe (PID: 2420)
- Spyroid VIP.exe (PID: 1396)
Process checks computer location settings
- Spyroid VIP.exe (PID: 6592)
Reads Environment values
- Spyroid VIP.exe (PID: 1396)
Disables trace logs
- Spyroid VIP.exe (PID: 1396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(6592) Spyroid VIP.exe
Decrypted-URLs (2)https://eagleauthservice.000webhostapp.com/KeyAuth.txt
https://www.github.com/
(PID) Process(1396) Spyroid VIP.exe
Decrypted-URLs (2)https://eagleauthservice.000webhostapp.com/KeyAuth.txt
https://www.github.com/
Total processes
158
Monitored processes
22
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
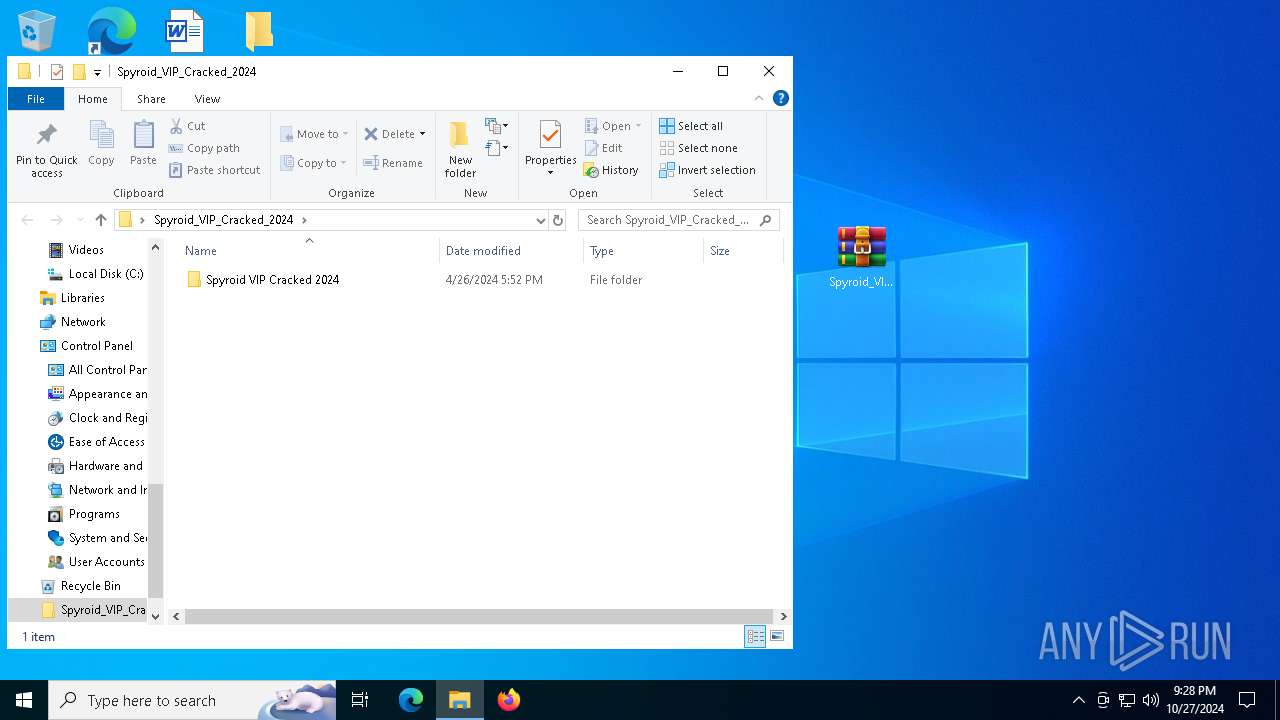
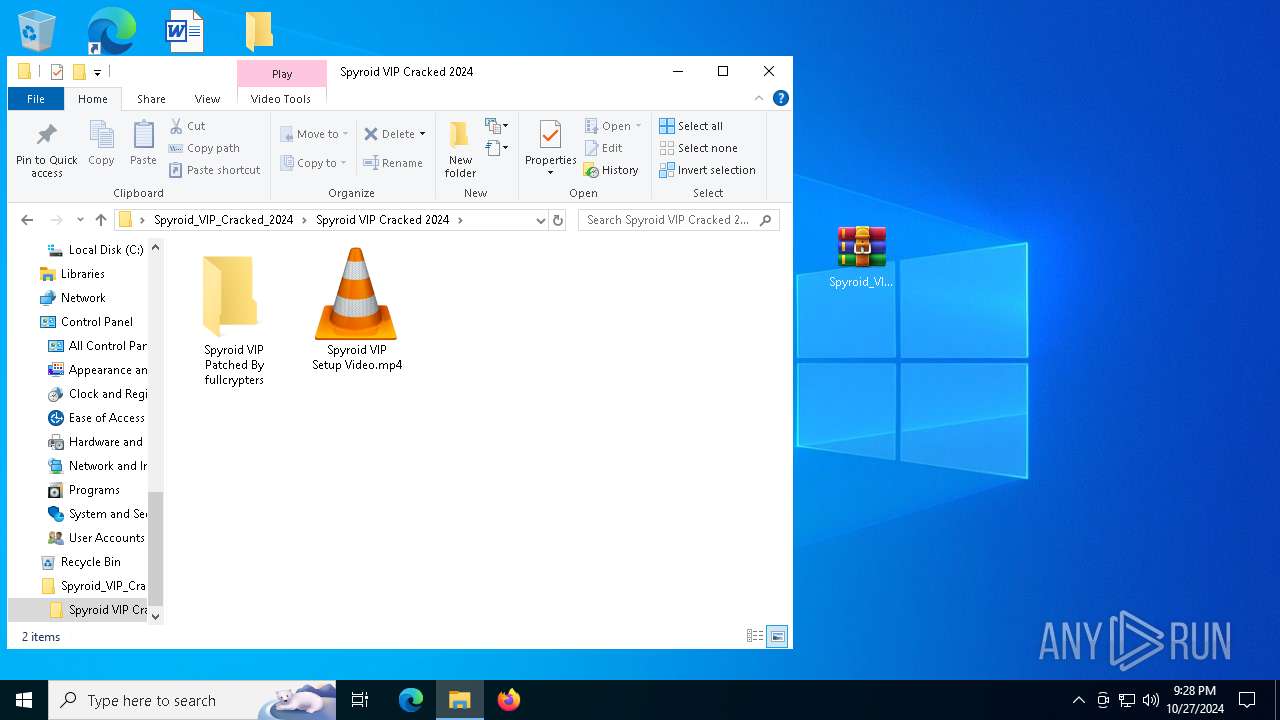
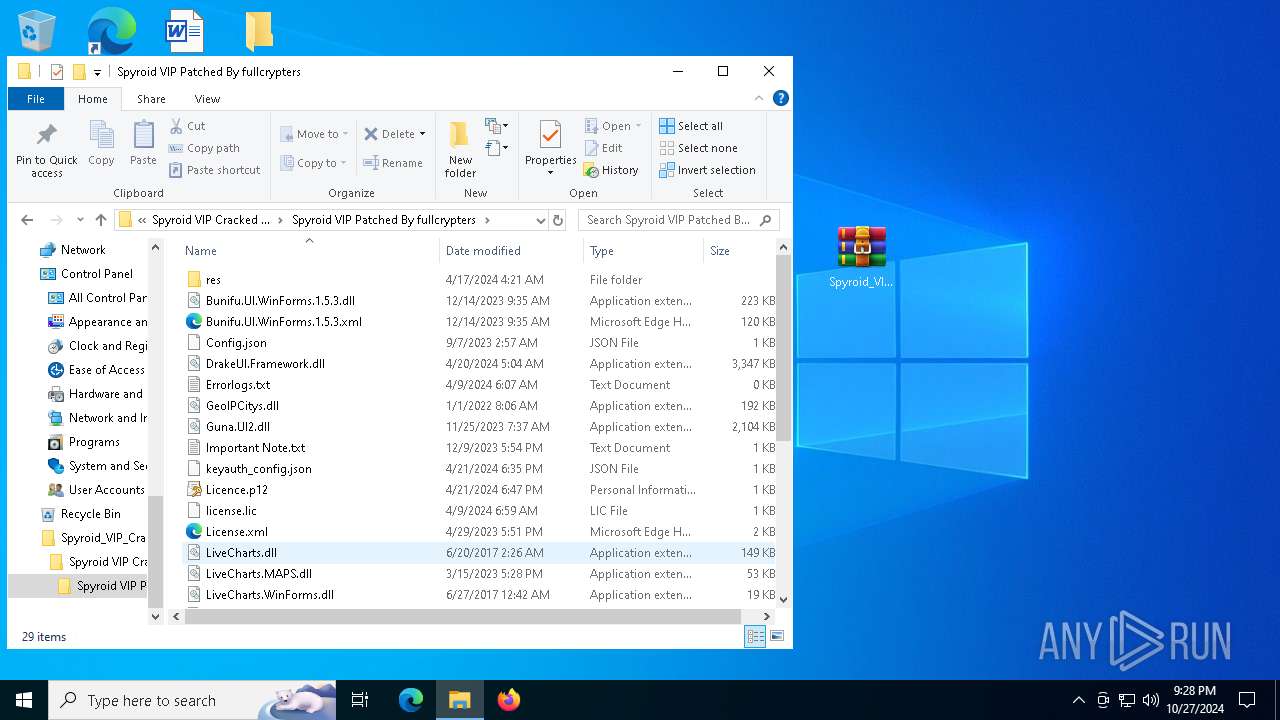
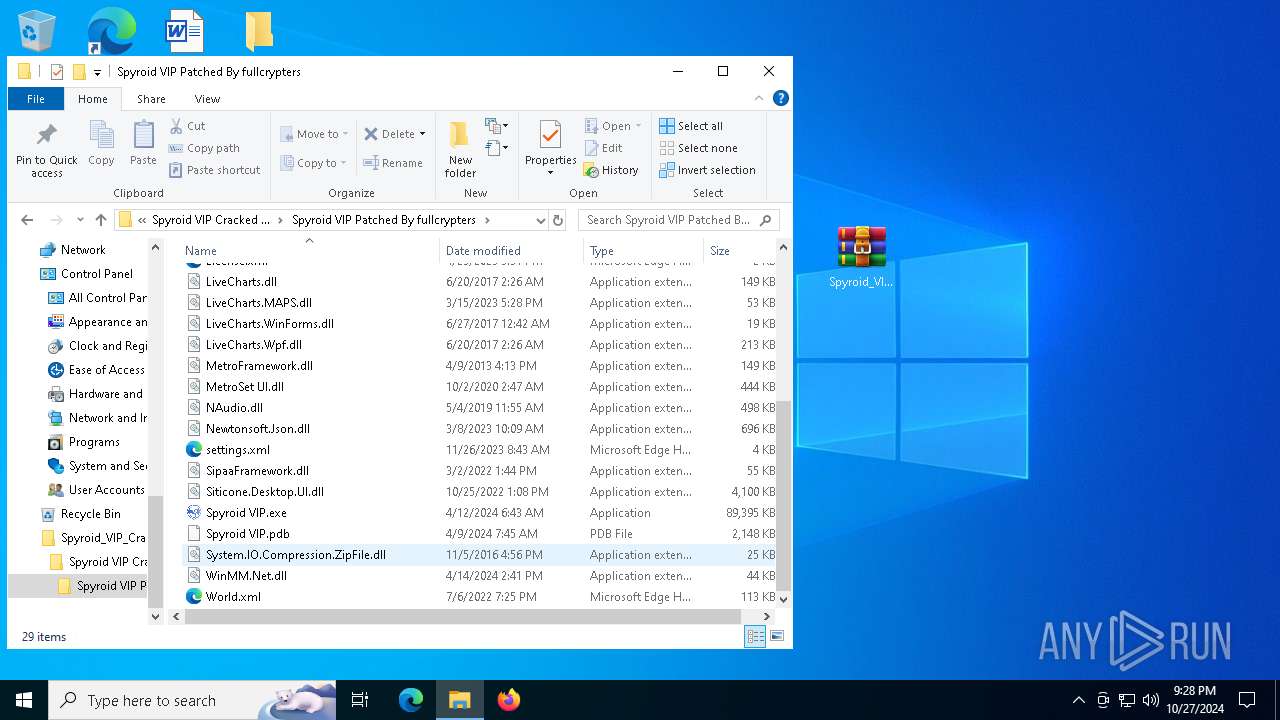
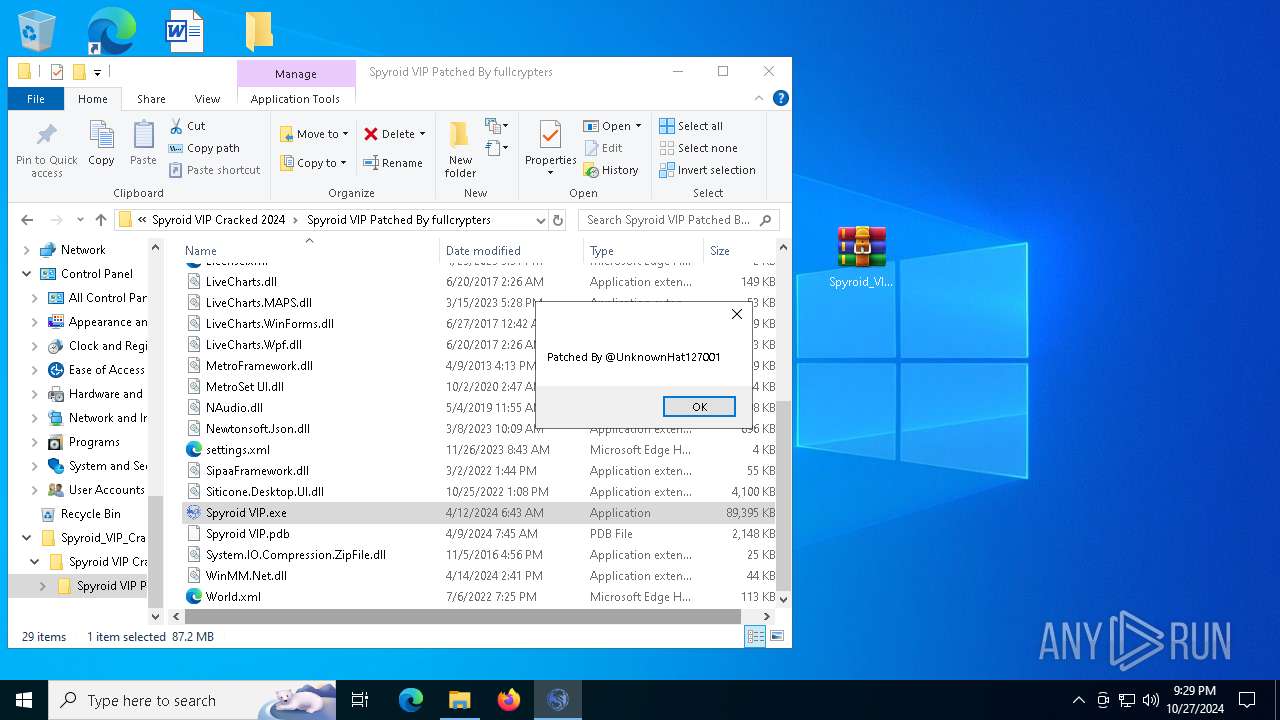
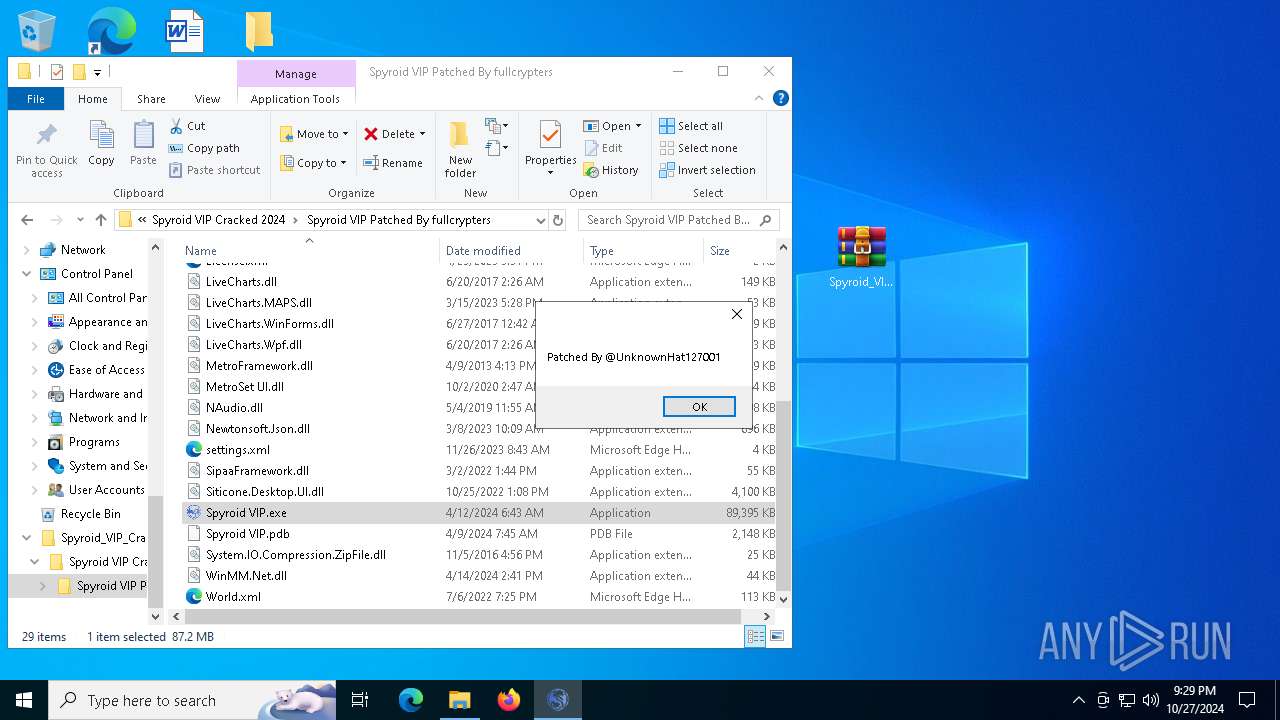
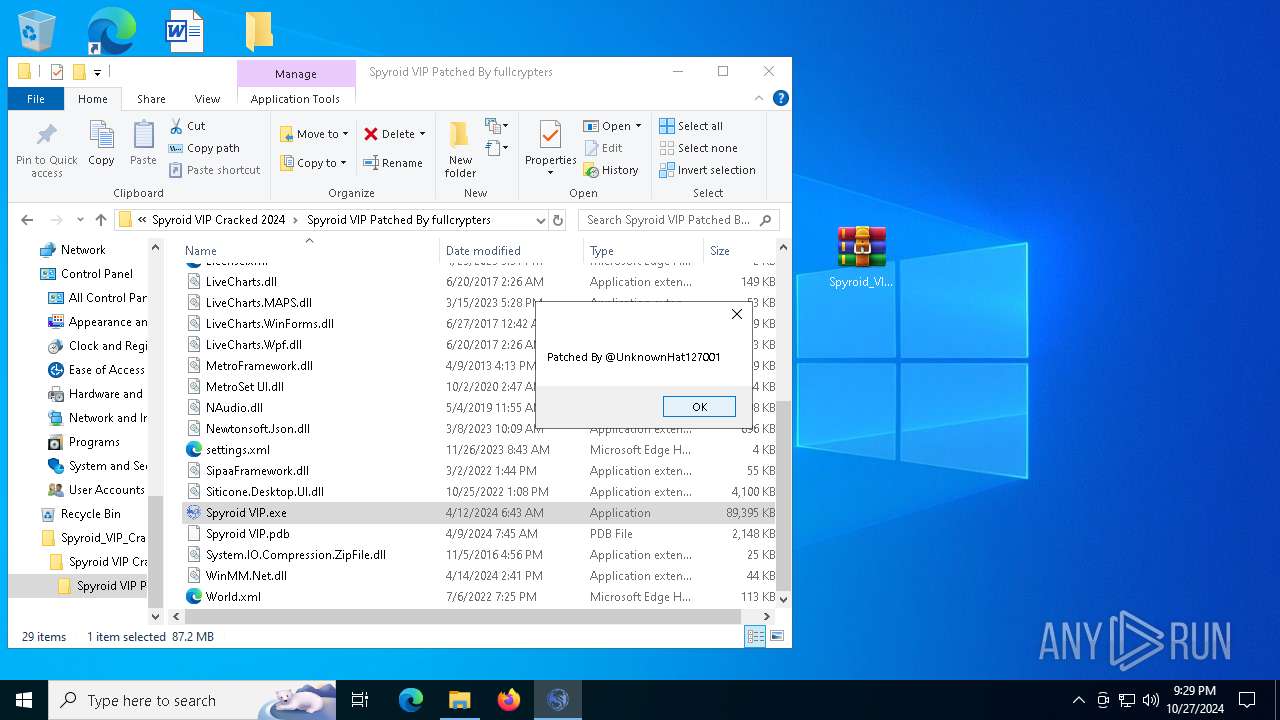
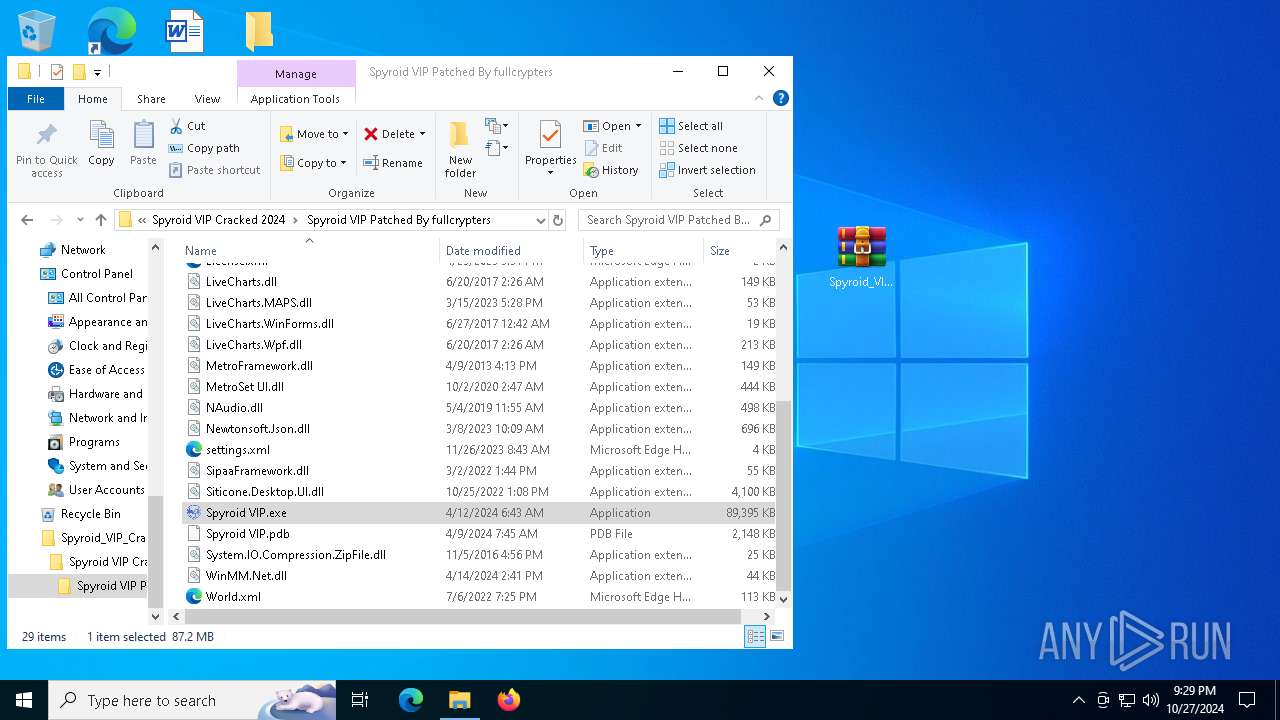
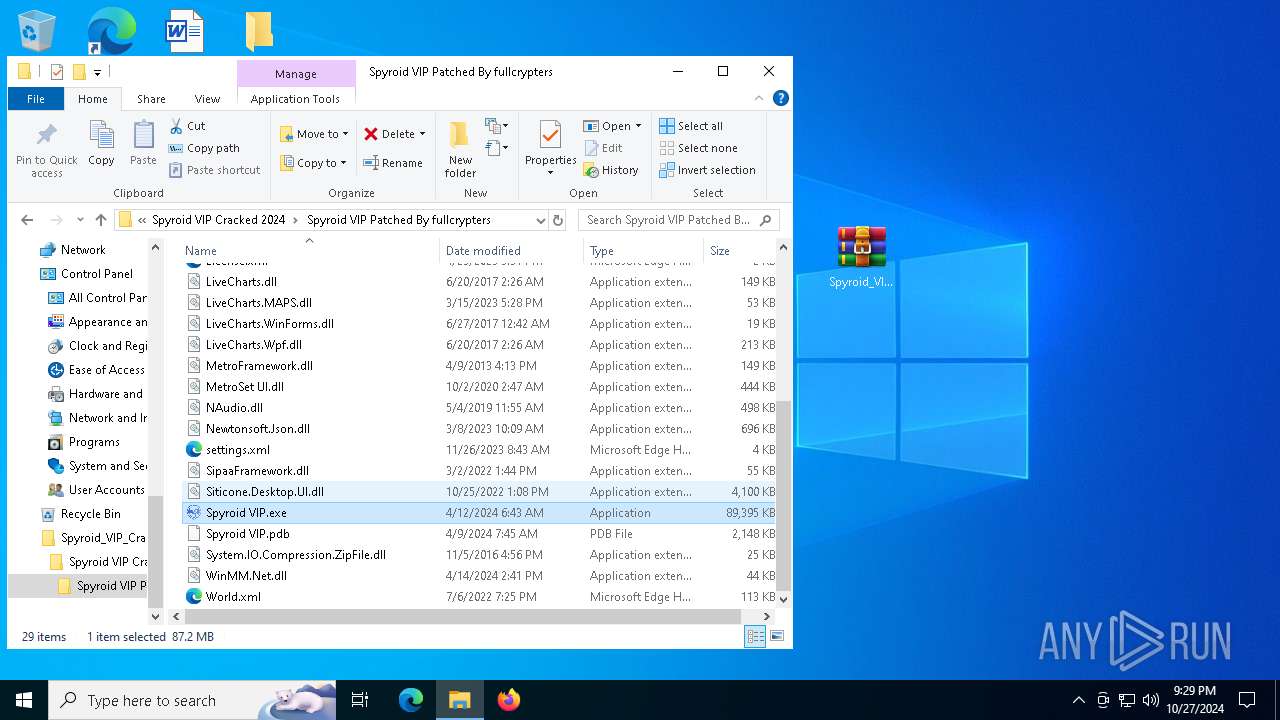
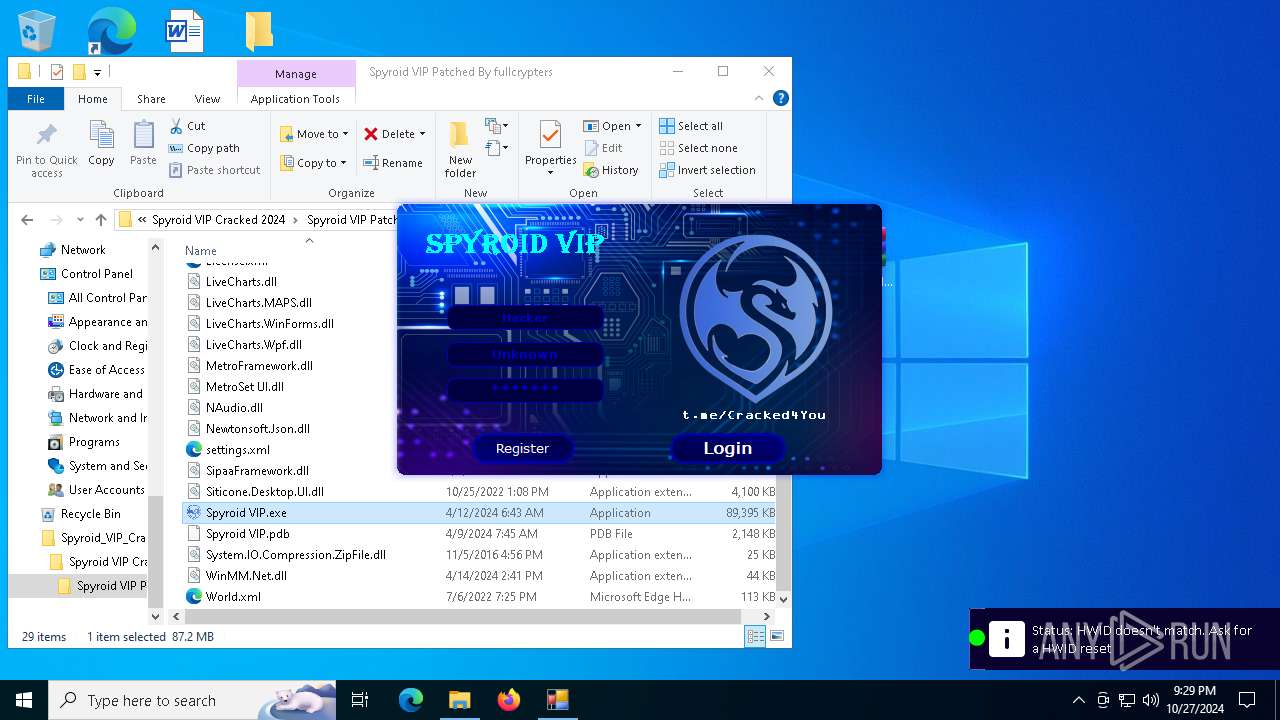
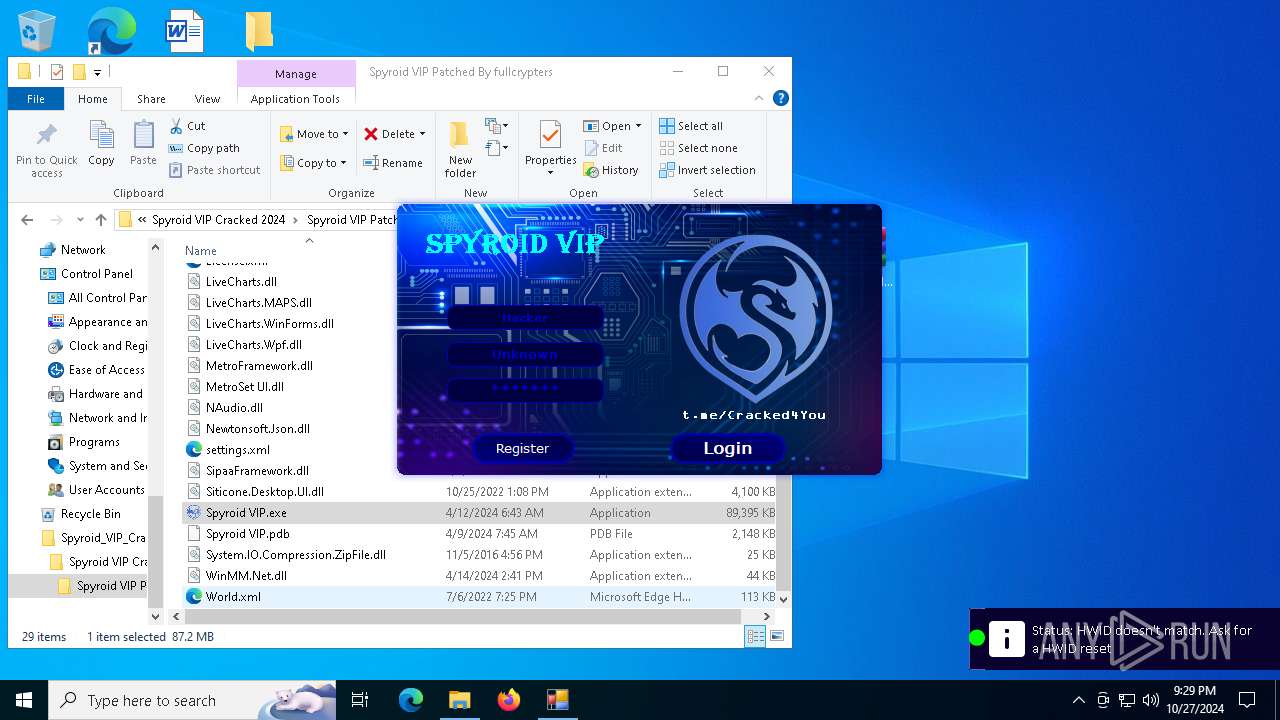
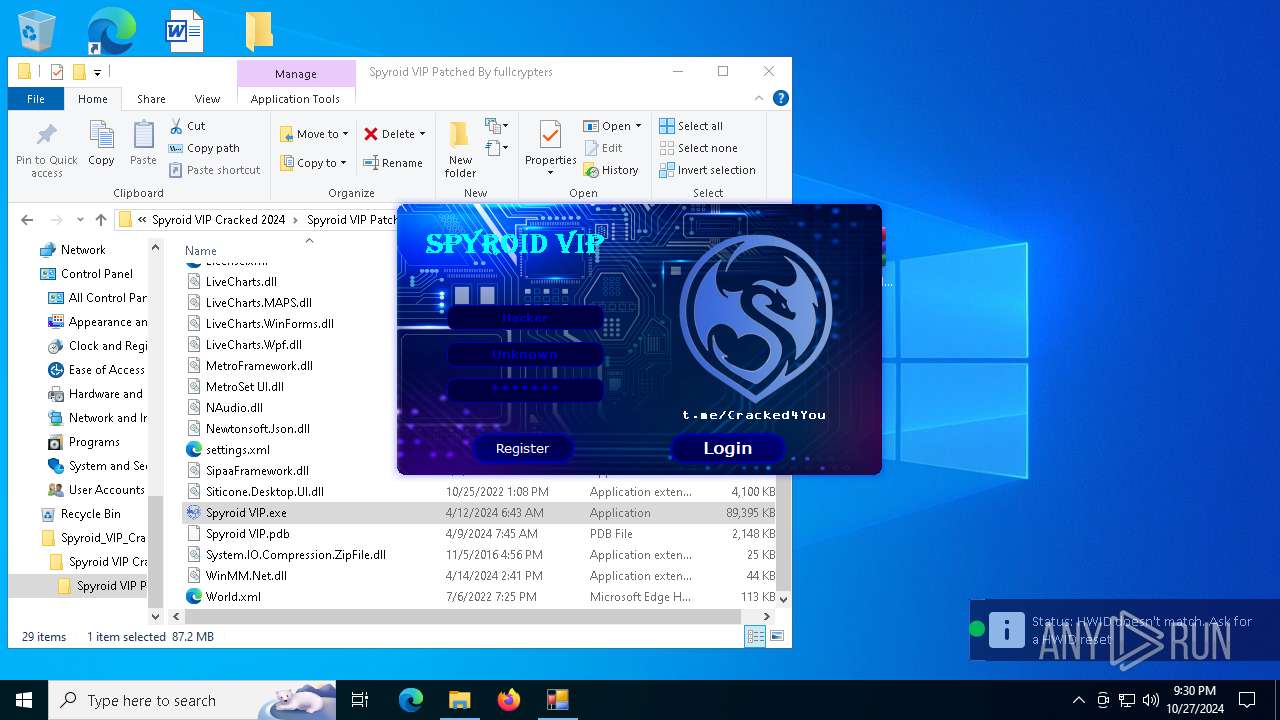
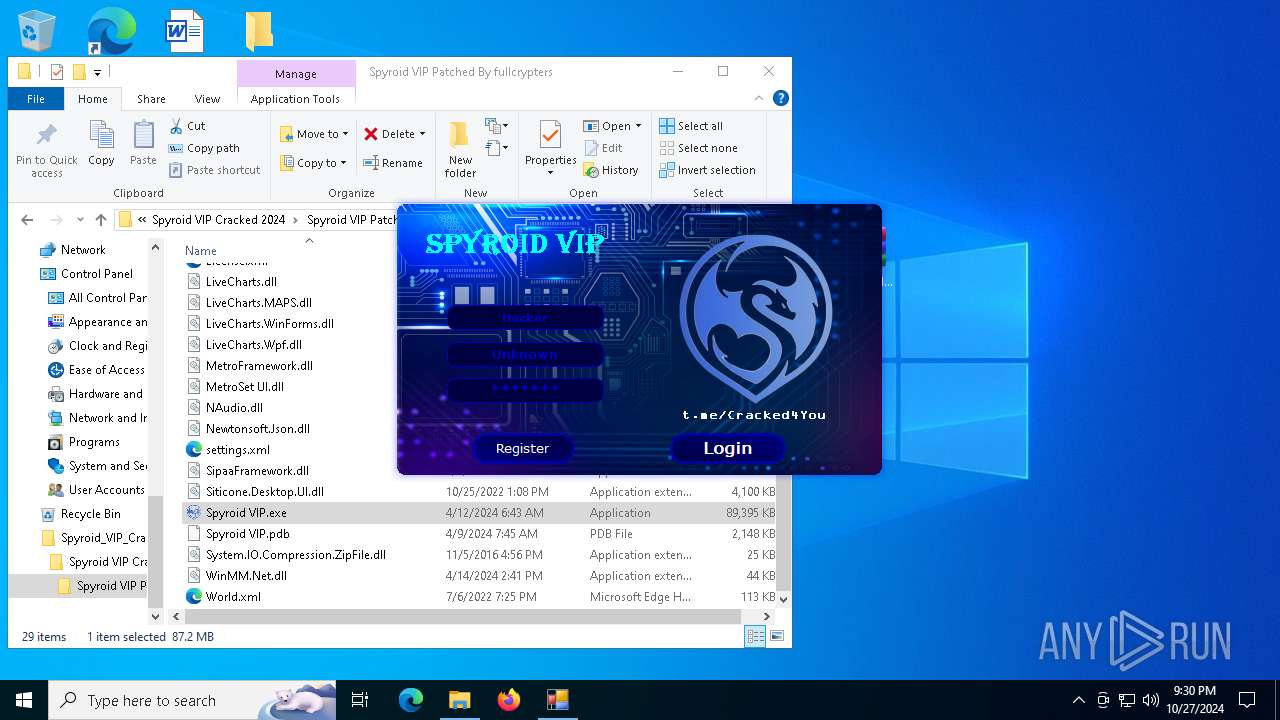
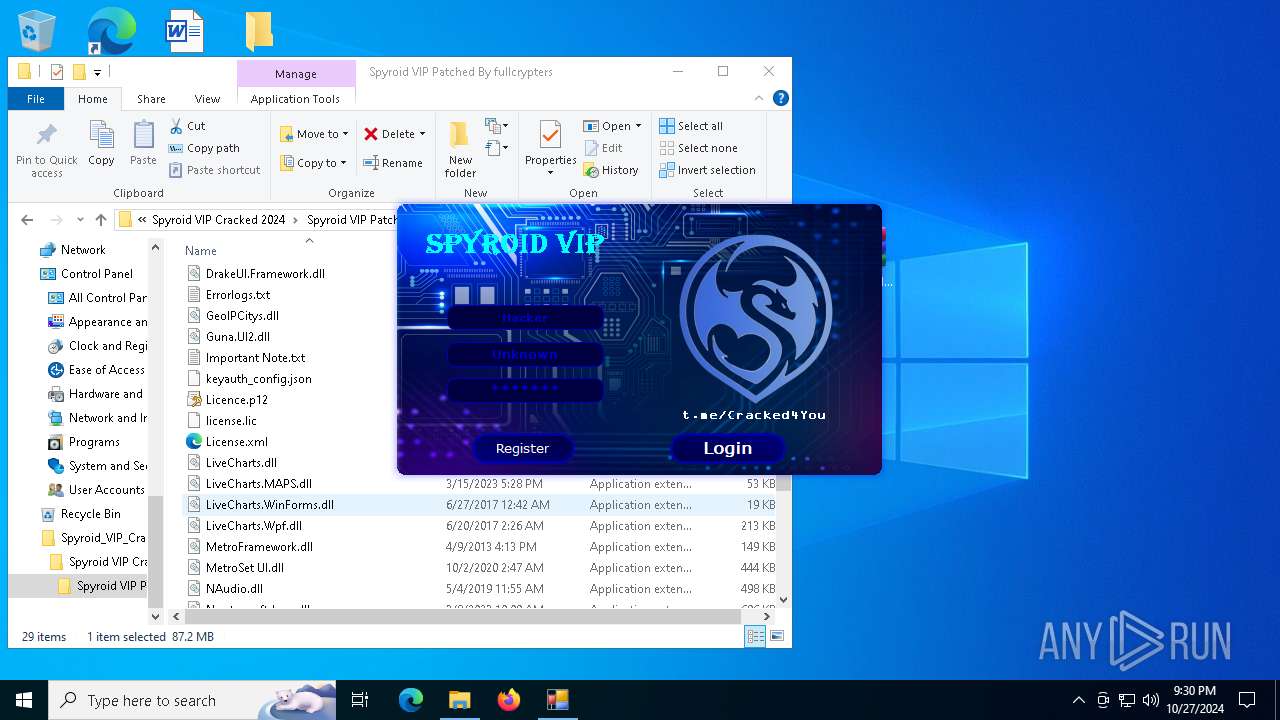
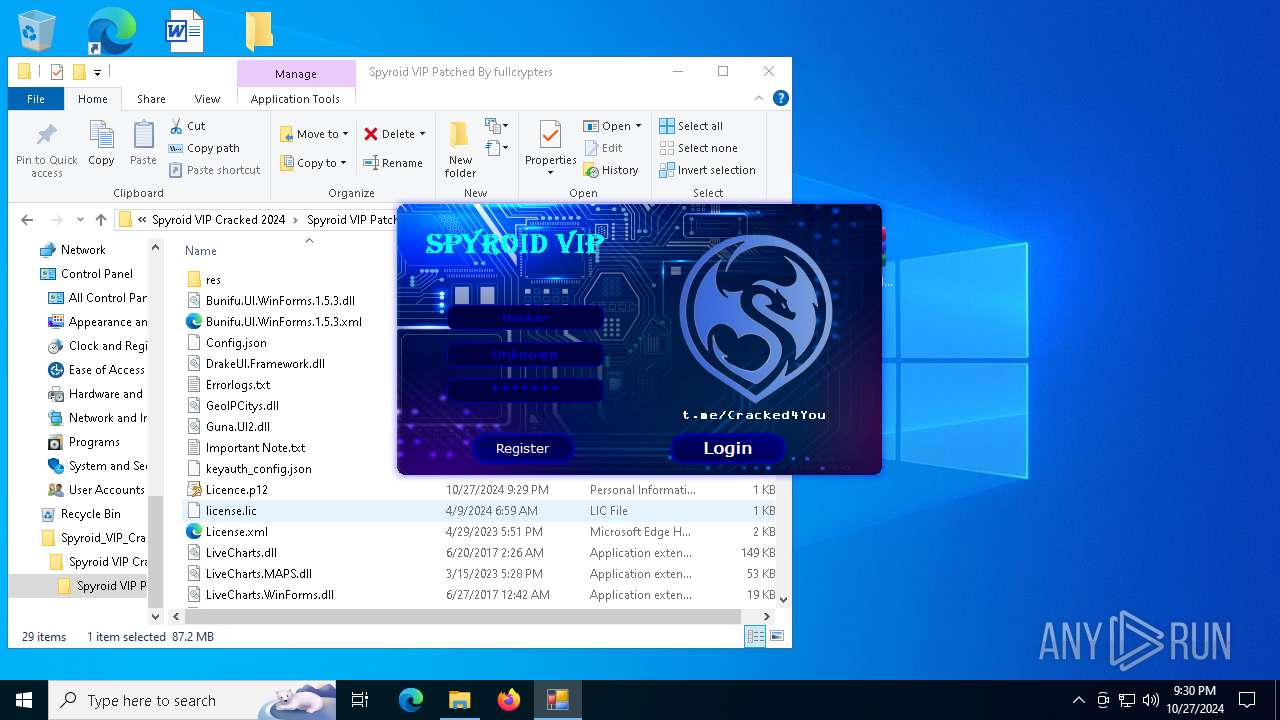
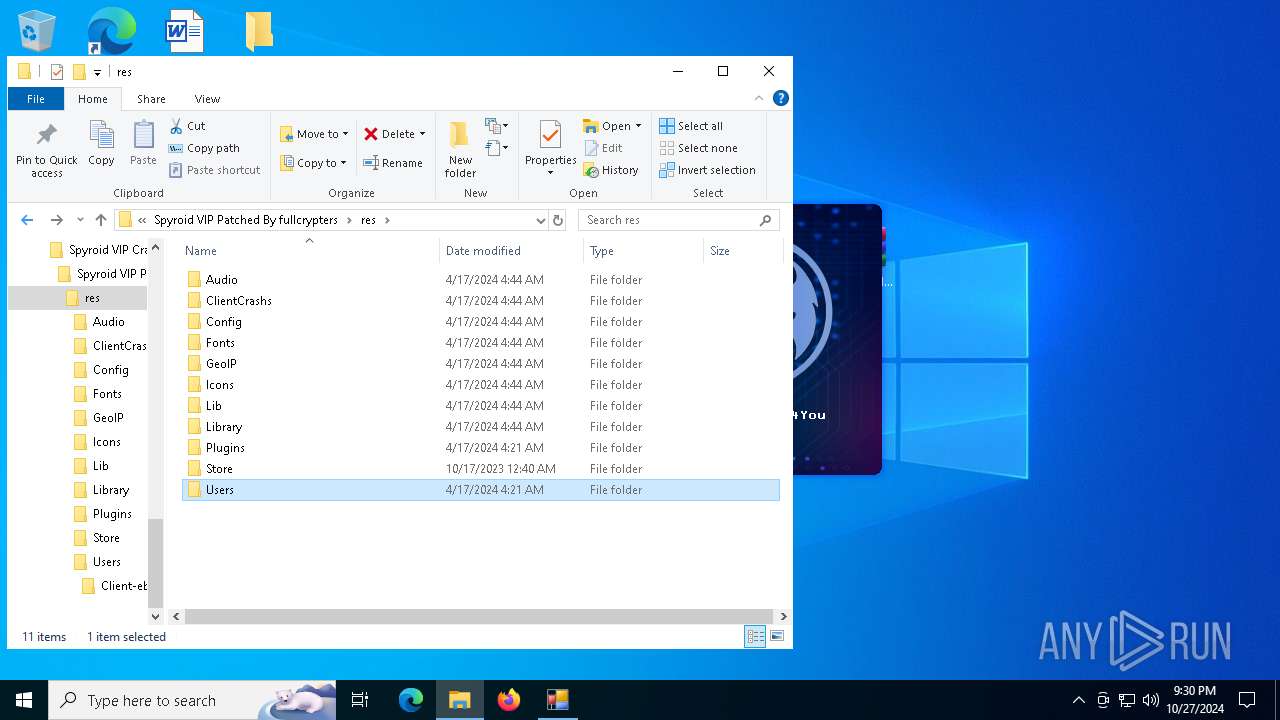
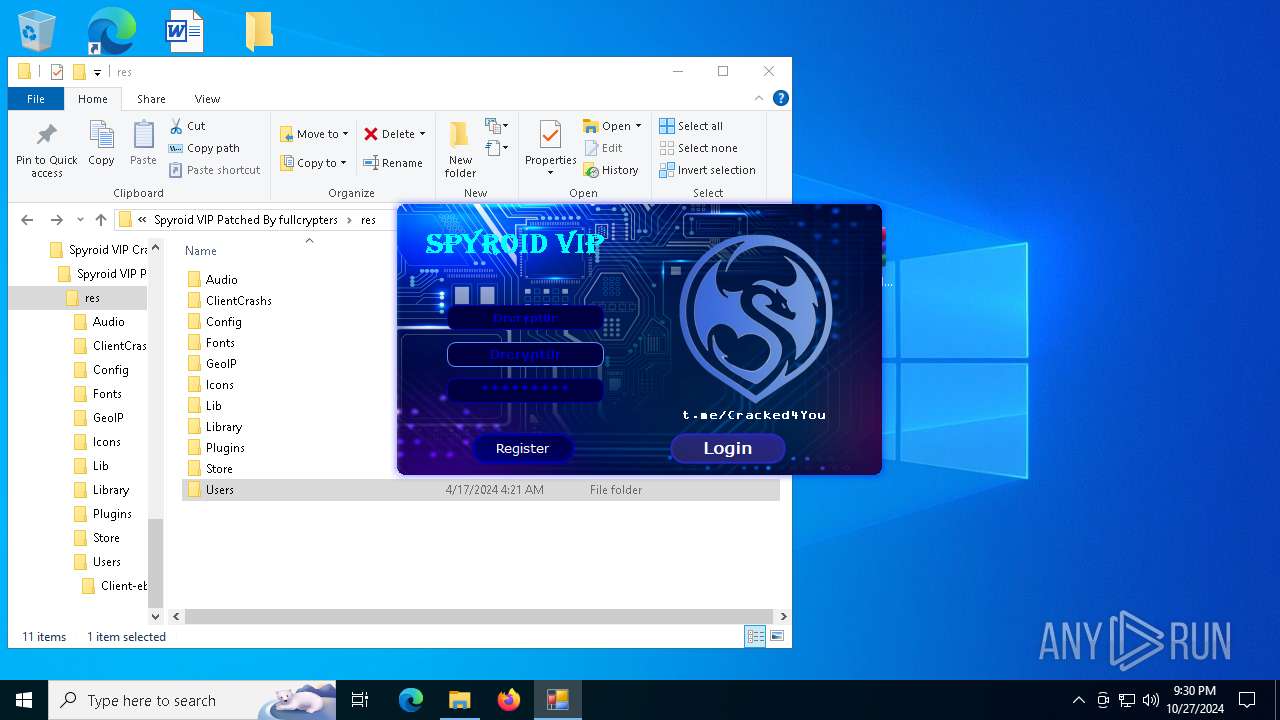
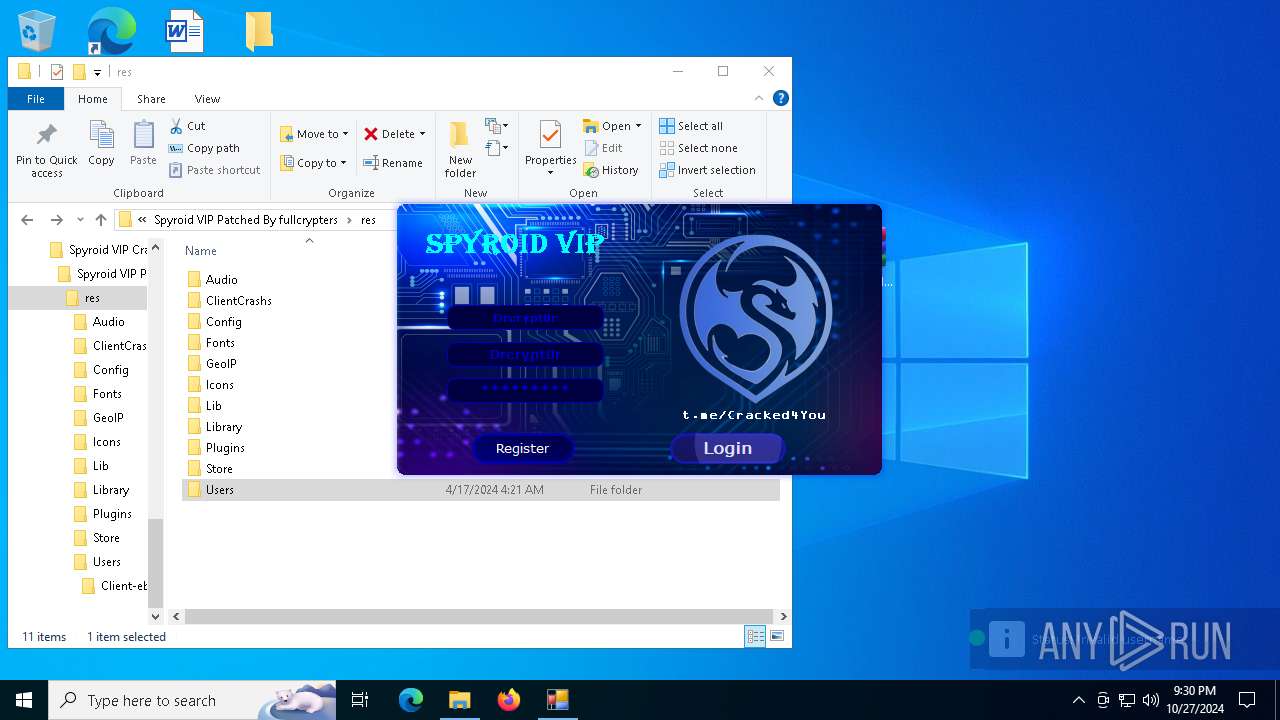
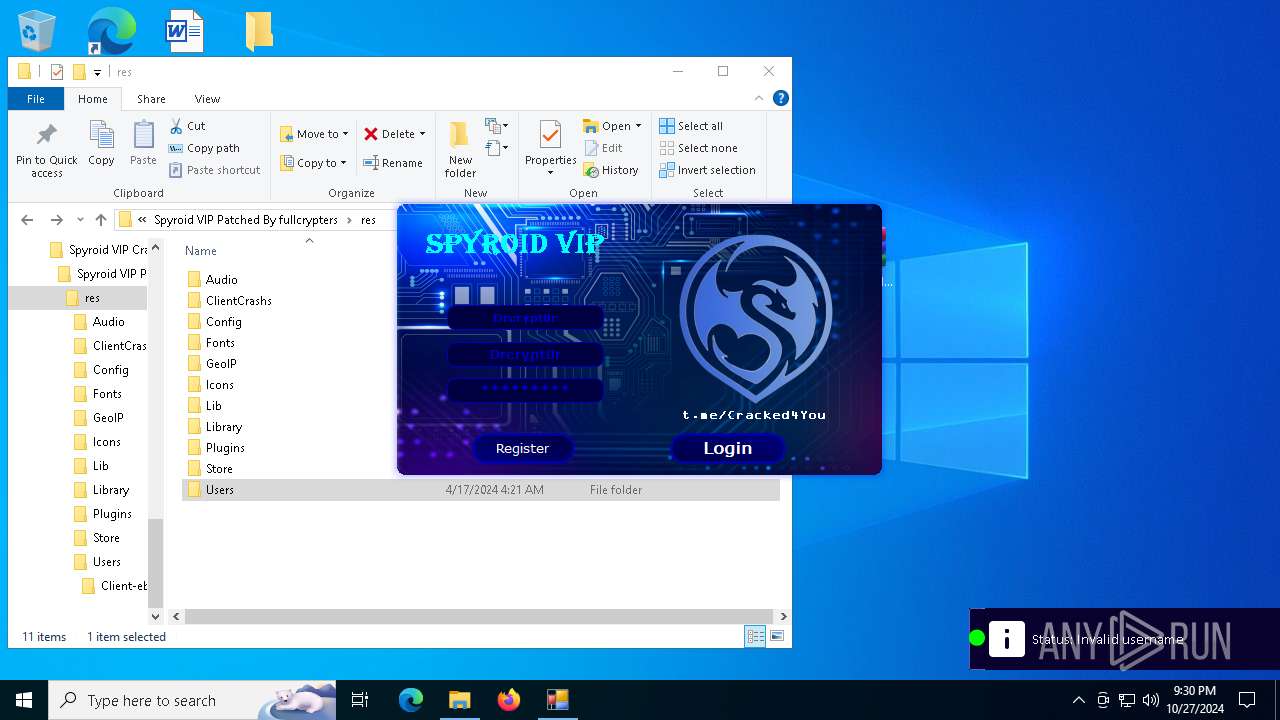
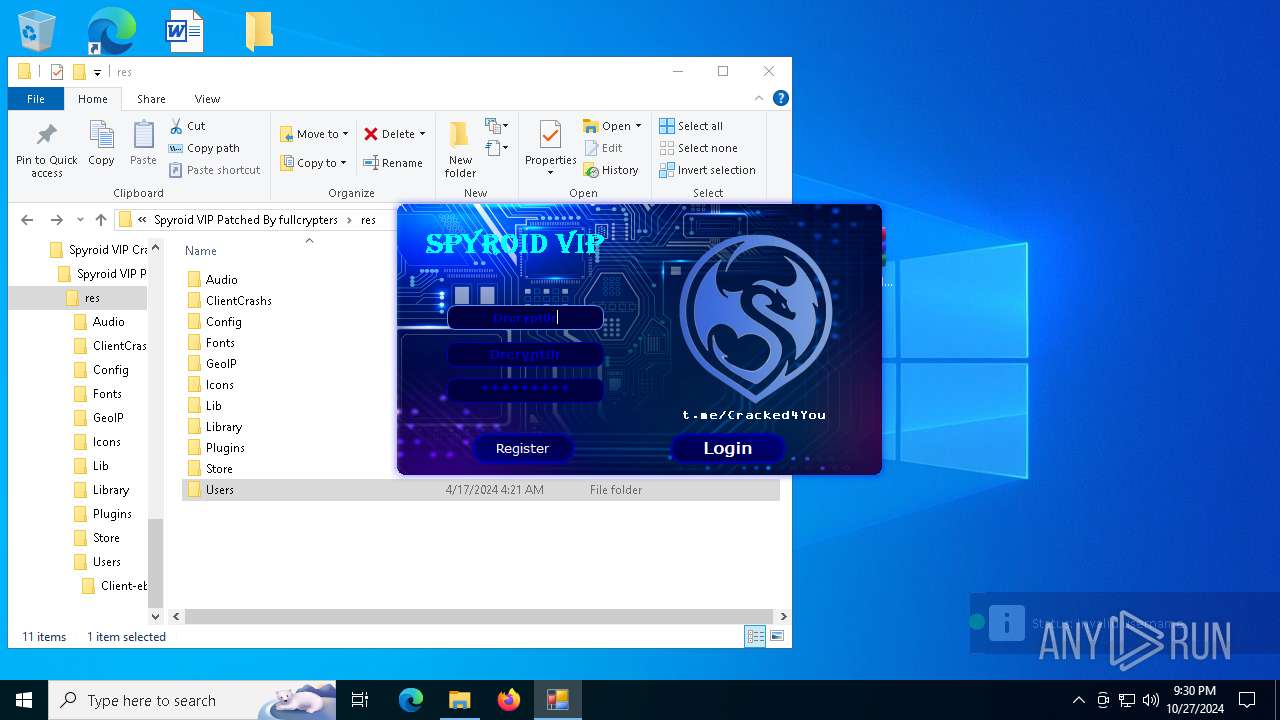
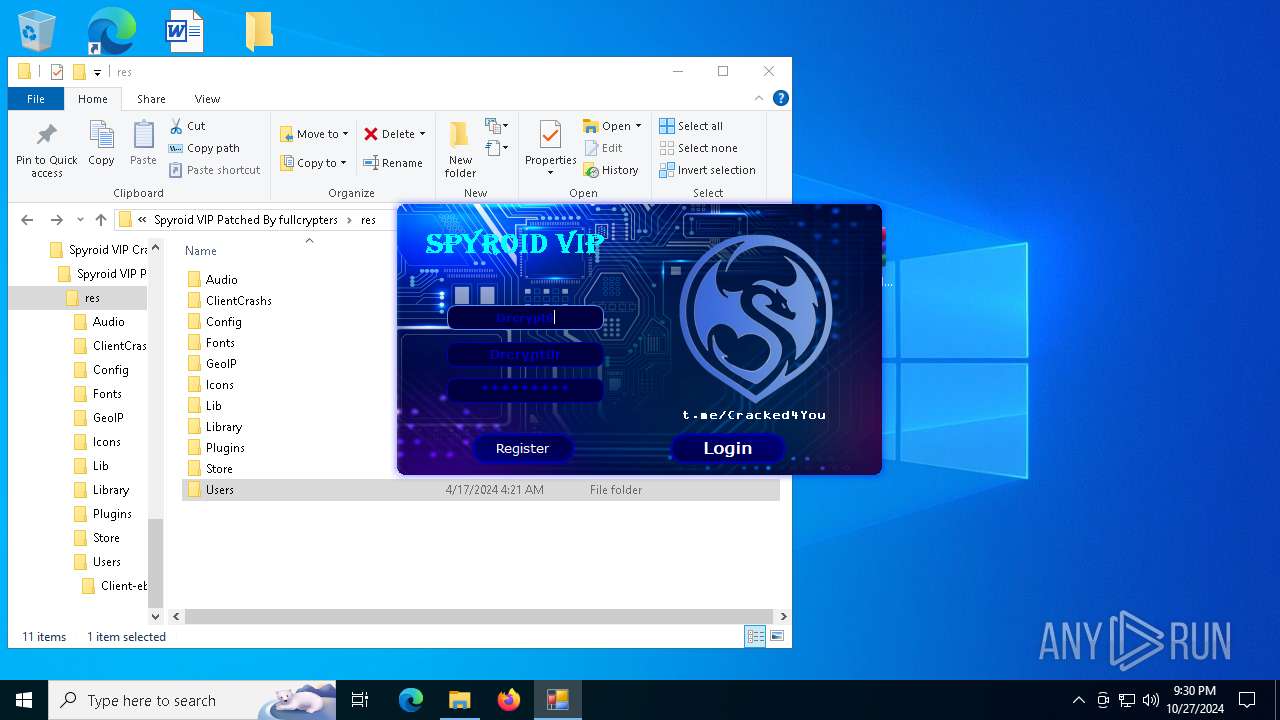
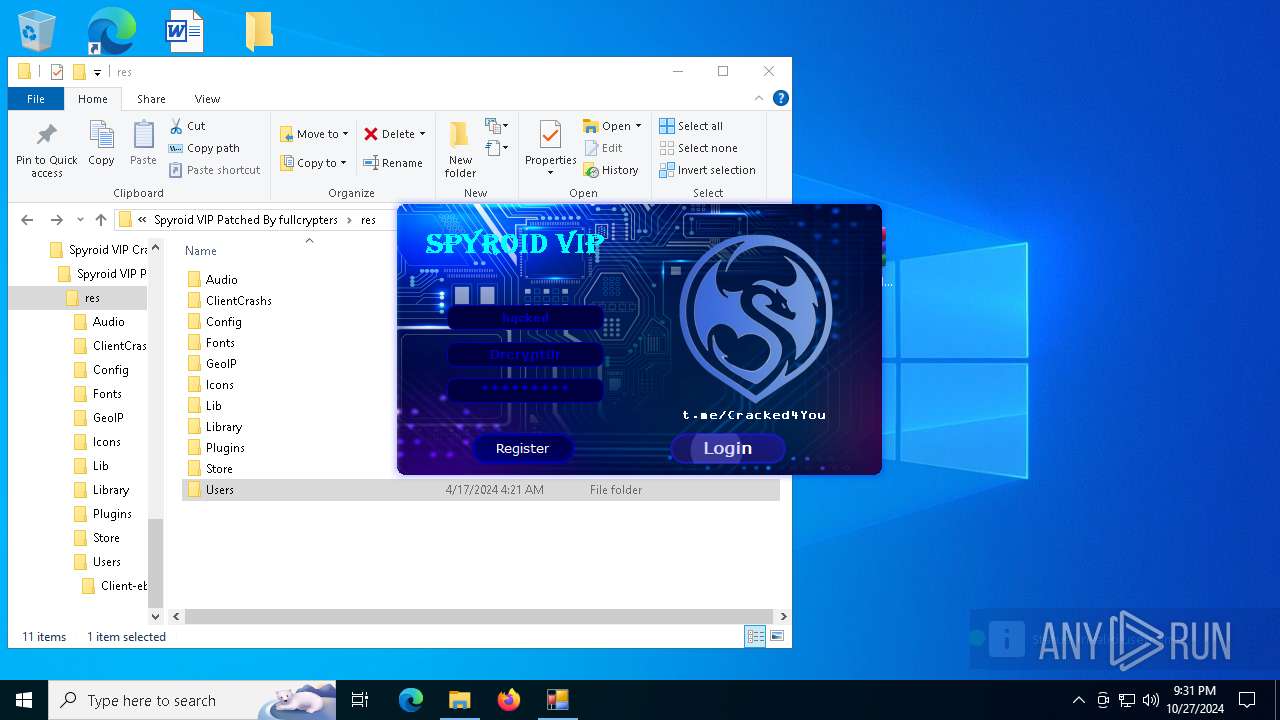
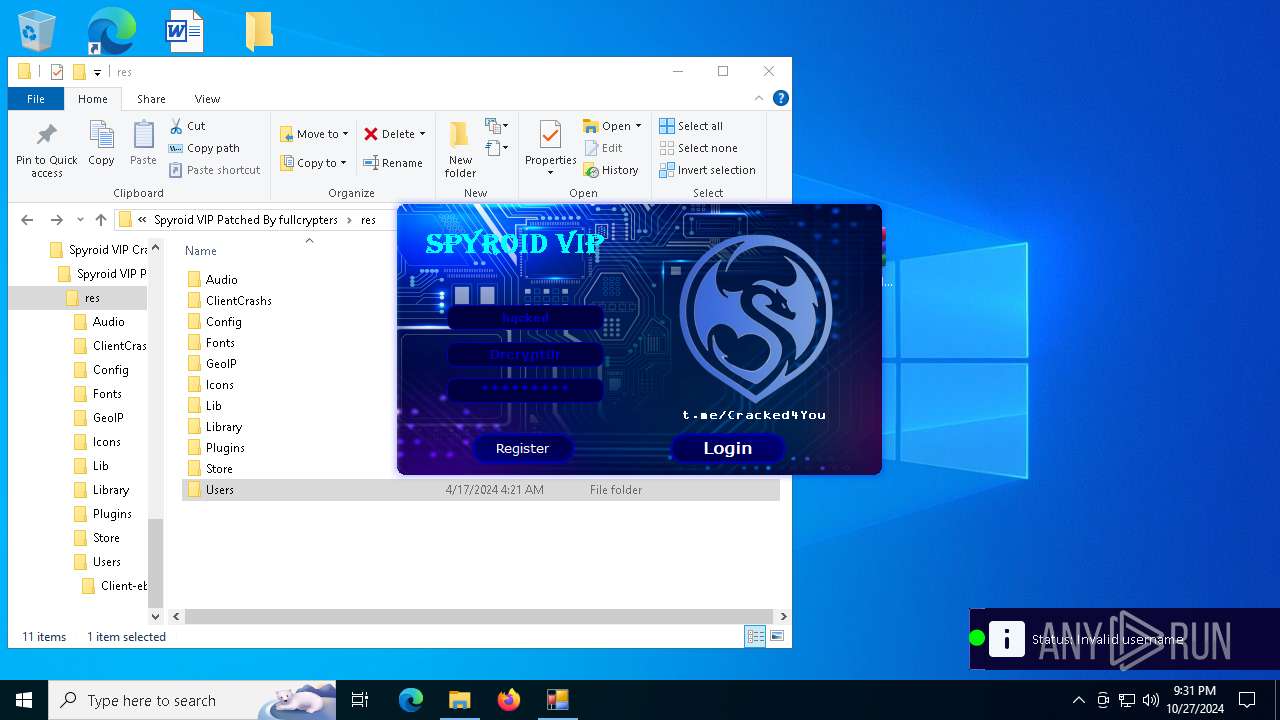
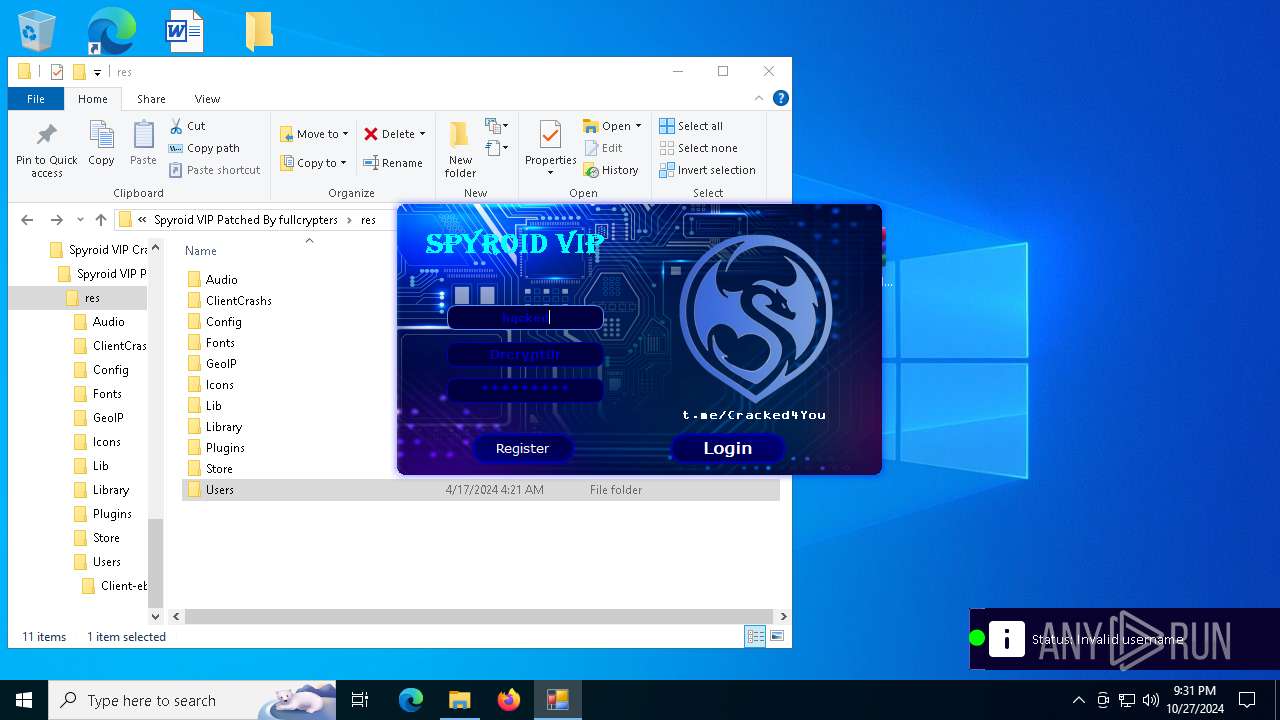
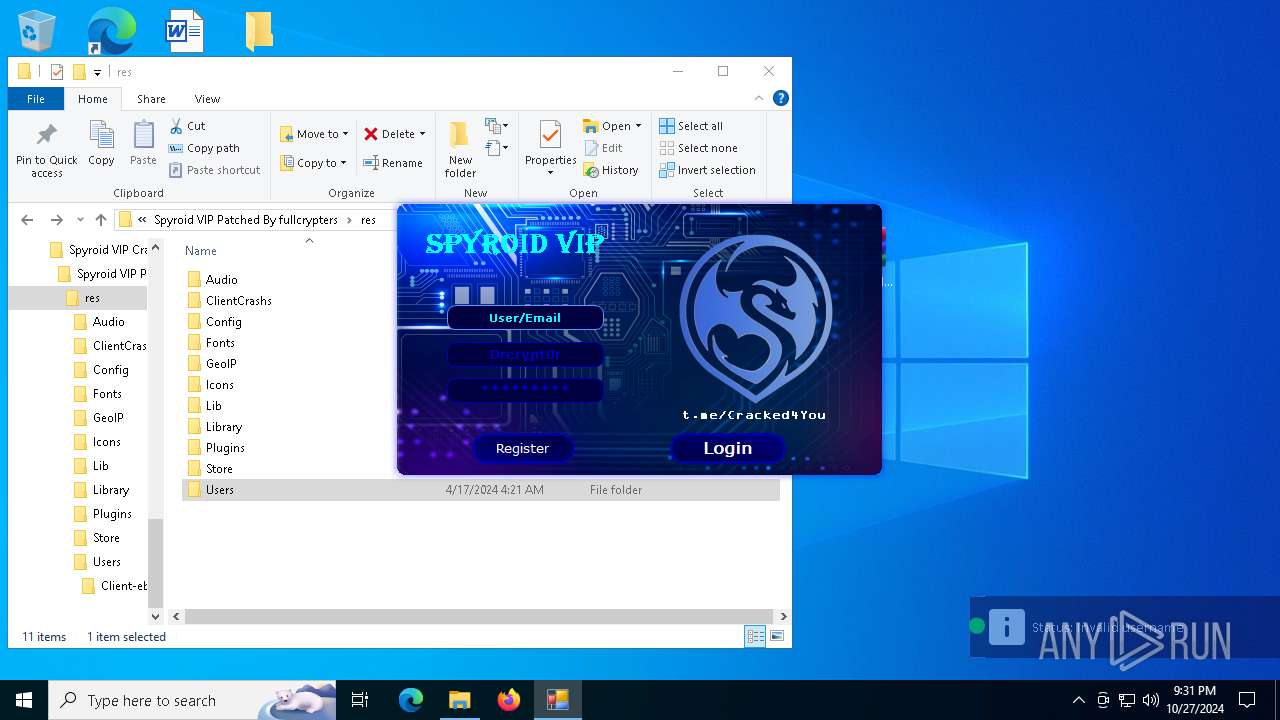
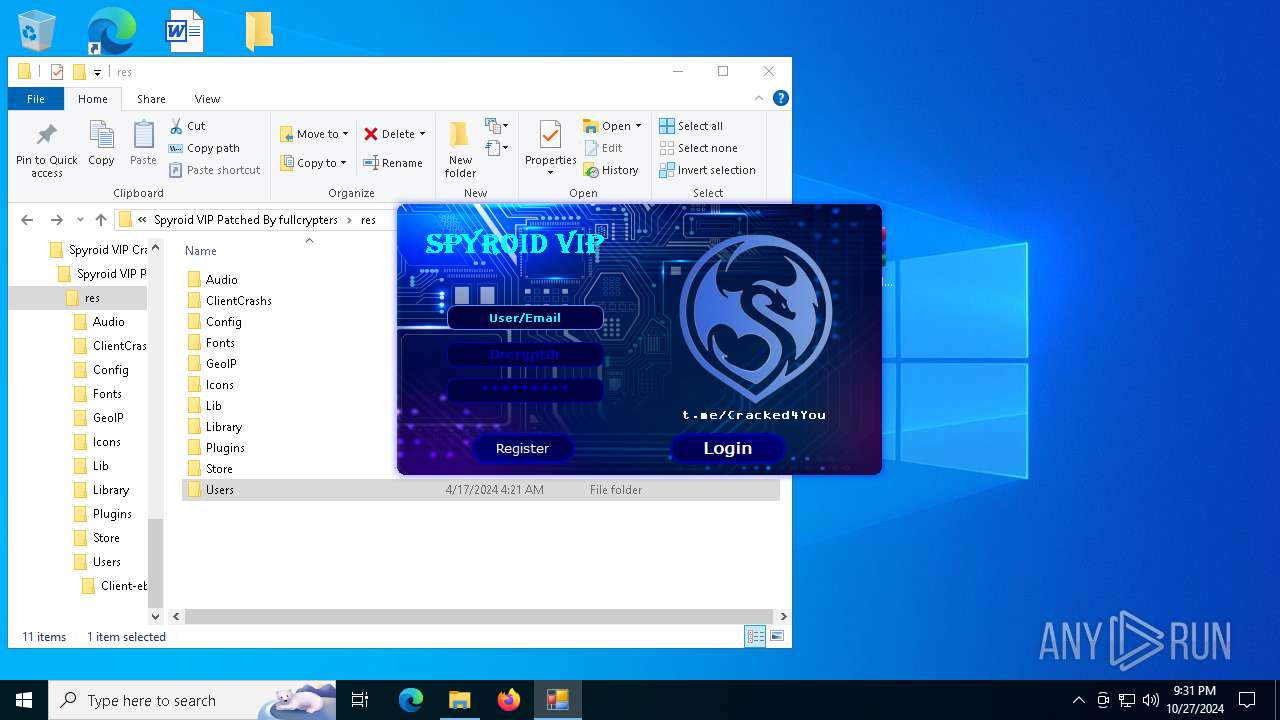
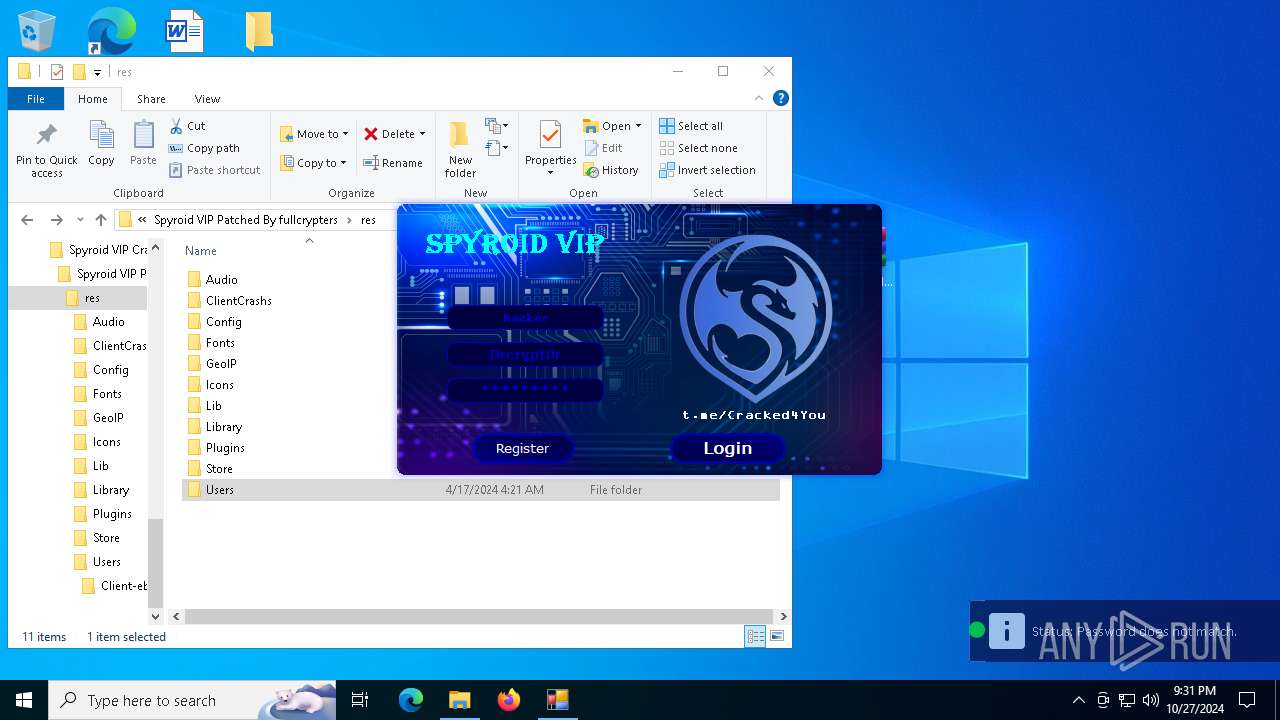
| 1396 | "C:\Users\admin\Desktop\Spyroid_VIP_Cracked_2024\Spyroid VIP Cracked 2024\Spyroid VIP Patched By fullcrypters\Spyroid VIP.exe" | C:\Users\admin\Desktop\Spyroid_VIP_Cracked_2024\Spyroid VIP Cracked 2024\Spyroid VIP Patched By fullcrypters\Spyroid VIP.exe | Spyroid VIP.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 4.0.0.0 Modules
xor-url(PID) Process(1396) Spyroid VIP.exe Decrypted-URLs (2)https://eagleauthservice.000webhostapp.com/KeyAuth.txt https://www.github.com/ | |||||||||||||||
| 1580 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2904 -childID 1 -isForBrowser -prefsHandle 2896 -prefMapHandle 2892 -prefsLen 26798 -prefMapSize 244343 -jsInitHandle 1304 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {3765ae68-9f05-478f-a235-7c2c34756875} 5516 "\\.\pipe\gecko-crash-server-pipe.5516" 1e463c8a150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5220 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1808 -parentBuildID 20240213221259 -prefsHandle 1736 -prefMapHandle 1716 -prefsLen 30705 -prefMapSize 244343 -appDir "C:\Program Files\Mozilla Firefox\browser" - {224b7407-4001-4245-b26b-58d05fd465ac} 5516 "\\.\pipe\gecko-crash-server-pipe.5516" 1e45dee3410 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 5324 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=7220 -childID 7 -isForBrowser -prefsHandle 7216 -prefMapHandle 7156 -prefsLen 31242 -prefMapSize 244343 -jsInitHandle 1304 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {dab4b931-1a93-4f73-b9c7-2a6b08674bf1} 5516 "\\.\pipe\gecko-crash-server-pipe.5516" 1e4679d7690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5372 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4380 -childID 2 -isForBrowser -prefsHandle 4372 -prefMapHandle 4368 -prefsLen 36339 -prefMapSize 244343 -jsInitHandle 1304 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c27ead4c-221f-4438-b47f-1d694b1e0a52} 5516 "\\.\pipe\gecko-crash-server-pipe.5516" 1e464a6f690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5516 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://u.pcloud.link/publink/show?code=XZ4Vfb0ZFcAebxqhFlylOop0waPXSYpH7LBX | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 6044 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2192 -parentBuildID 20240213221259 -prefsHandle 2184 -prefMapHandle 2148 -prefsLen 30705 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {ec78ace3-1887-492e-aef3-7dd4a298cf97} 5516 "\\.\pipe\gecko-crash-server-pipe.5516" 1e452181910 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 6224 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://u.pcloud.link/publink/show?code=XZ4Vfb0ZFcAebxqhFlylOop0waPXSYpH7LBX" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
21 997
Read events
21 960
Write events
24
Delete events
13
Modification events
| (PID) Process: | (5516) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (8152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (8152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (8152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (8152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
| (PID) Process: | (8152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 11 |
Value: | |||
| (PID) Process: | (8152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 10 |
Value: | |||
| (PID) Process: | (8152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 9 |
Value: | |||
| (PID) Process: | (8152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 8 |
Value: | |||
| (PID) Process: | (8152) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 7 |
Value: | |||
Executable files
24
Suspicious files
247
Text files
499
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5516 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 5516 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5516 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5516 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5516 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:C09FF302D57C404B61E6A89B0B9F36E7 | SHA256:6A5B4F82595799346D0E501FE6CC8629E0FD6ED27B74D0E6CB5073DDB2E3C40B | |||
| 5516 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5516 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:9B809136DC08C558917EAE78CBF306CE | SHA256:BAEE1A4E31BAF68EE8427D13C92A31B7D31F2A4C436A3B255E2FE50E777CC28A | |||
| 5516 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:EC7FD01EF2B1D89982181444E7AFEB92 | SHA256:DE6D1E7D5F3BD9601AC5EEF6378C89D6433F86720169B072C44390DD4D404804 | |||
| 5516 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | binary | |
MD5:4D0A029AAD3A15CA50507597E63D78D8 | SHA256:02A898F8F390E387AA9C65FA7CC1CA1399F48660628610852CB45824C76DF097 | |||
| 5516 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:9B809136DC08C558917EAE78CBF306CE | SHA256:BAEE1A4E31BAF68EE8427D13C92A31B7D31F2A4C436A3B255E2FE50E777CC28A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
137
DNS requests
160
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5516 | firefox.exe | POST | 200 | 2.17.100.136:80 | http://ocsp.swisssign.ch/sign/ocs-aaccced5-66e8-4069-9b1b-fd29ab73efec | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5516 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5516 | firefox.exe | POST | 200 | 2.17.100.184:80 | http://ocsp.swisssign.ch/sign/ocs-aaccced5-66e8-4069-9b1b-fd29ab73efec | unknown | — | — | unknown |
5516 | firefox.exe | POST | — | 142.250.185.67:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
5516 | firefox.exe | POST | 200 | 23.53.40.161:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5516 | firefox.exe | POST | 200 | 2.17.100.184:80 | http://ocsp.swisssign.ch/sign/ocs-aaccced5-66e8-4069-9b1b-fd29ab73efec | unknown | — | — | unknown |
5516 | firefox.exe | POST | 200 | 23.53.40.161:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
u.pcloud.link |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Potentially Bad Traffic | ET INFO Cloud Storage API Related Domain in DNS Lookup (api .pcloud .com) |
2172 | svchost.exe | Potentially Bad Traffic | ET INFO Cloud Storage API Related Domain in DNS Lookup (api .pcloud .com) |
2172 | svchost.exe | Potentially Bad Traffic | ET INFO Cloud Storage API Related Domain in DNS Lookup (api .pcloud .com) |
2172 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
1396 | Spyroid VIP.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |