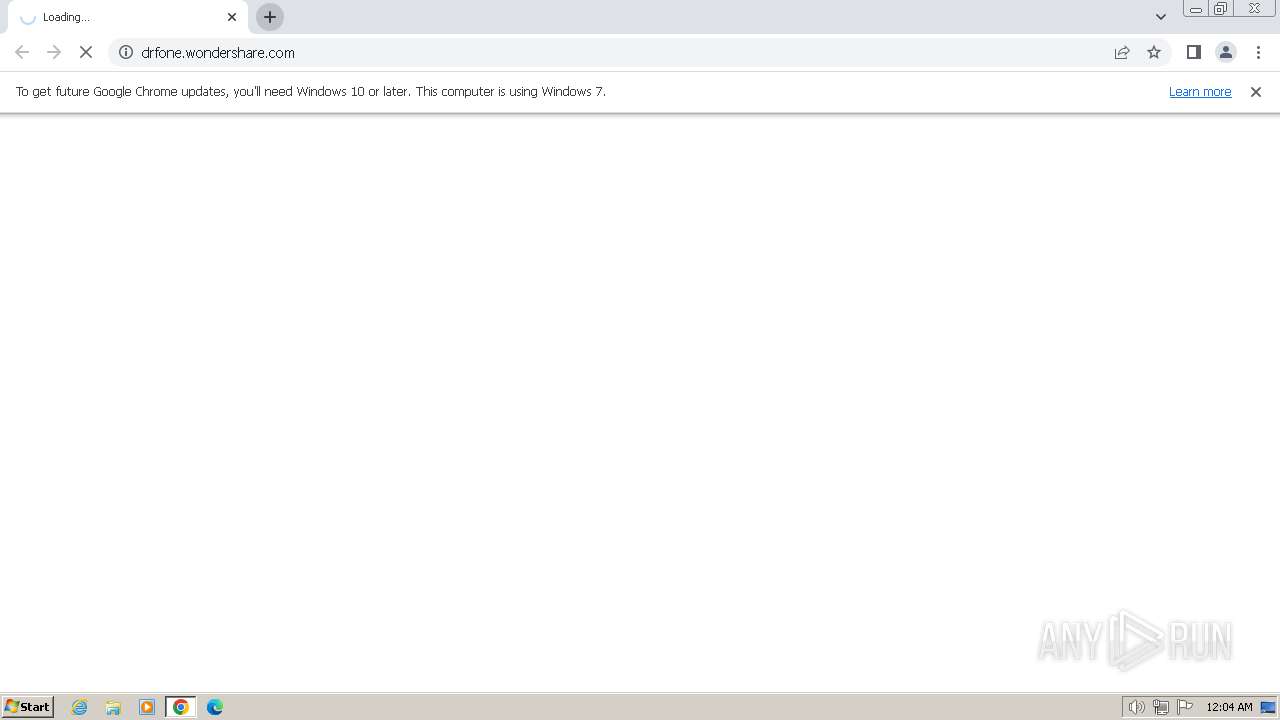
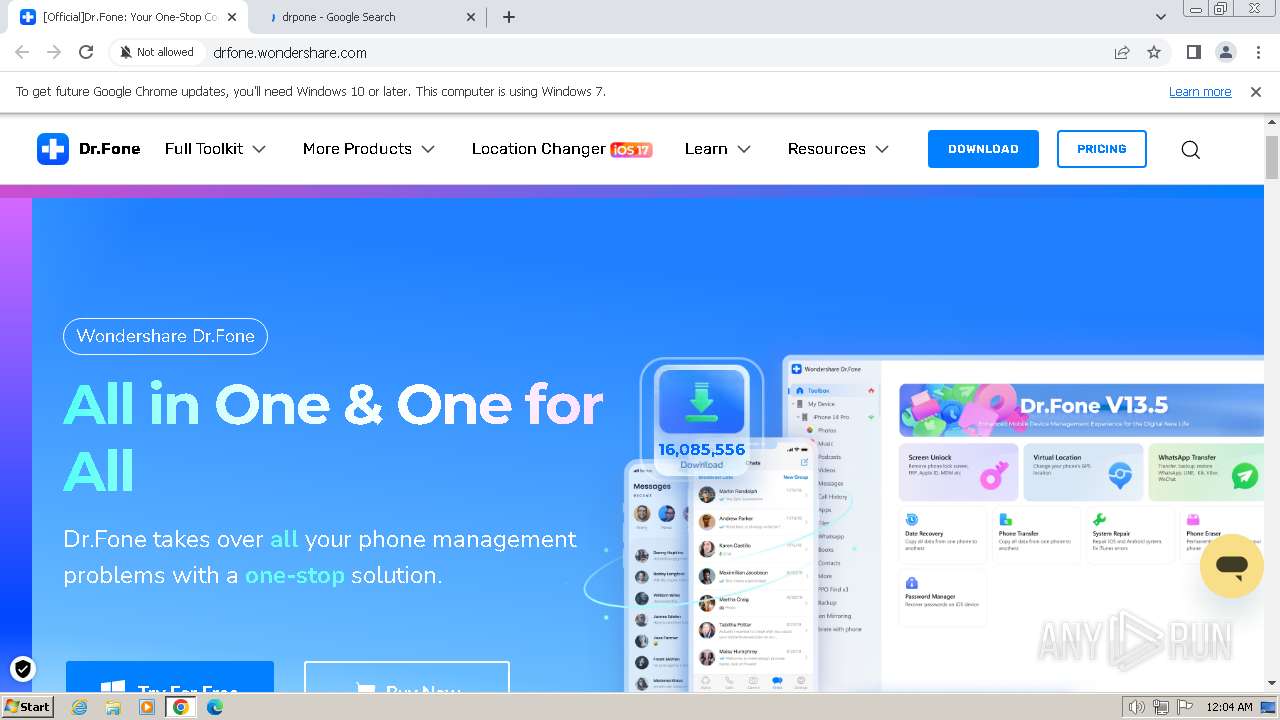
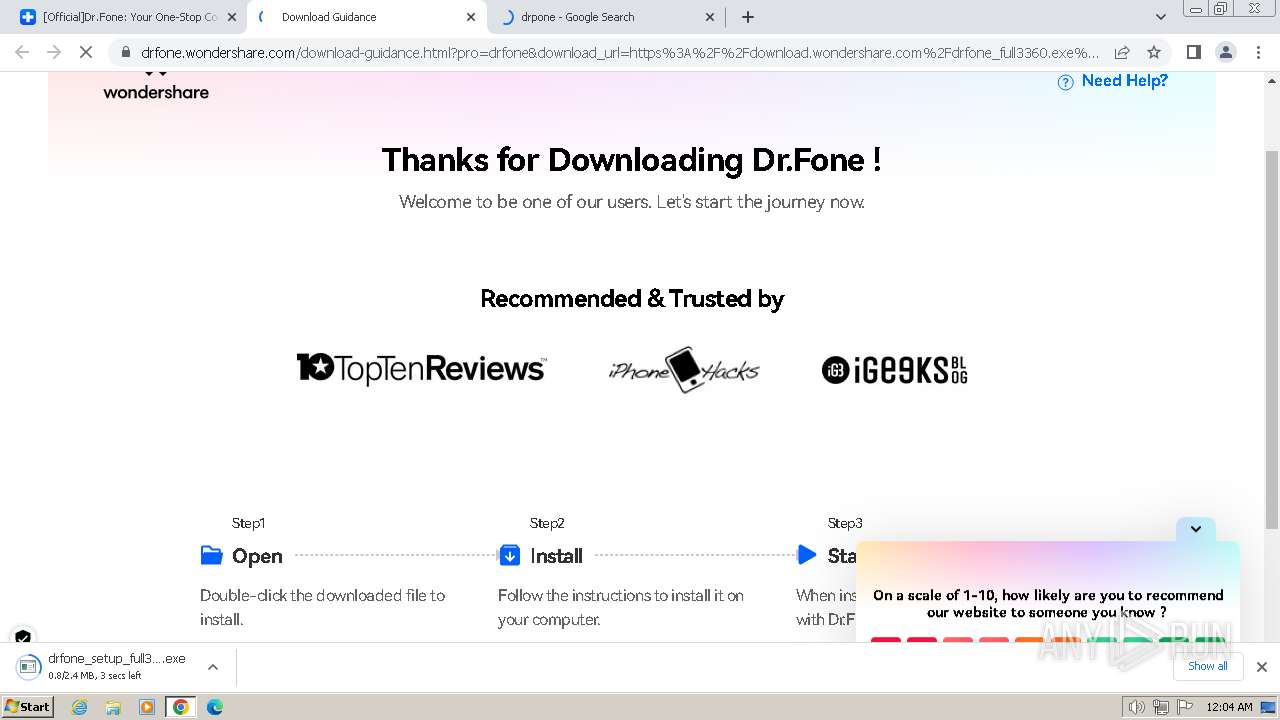
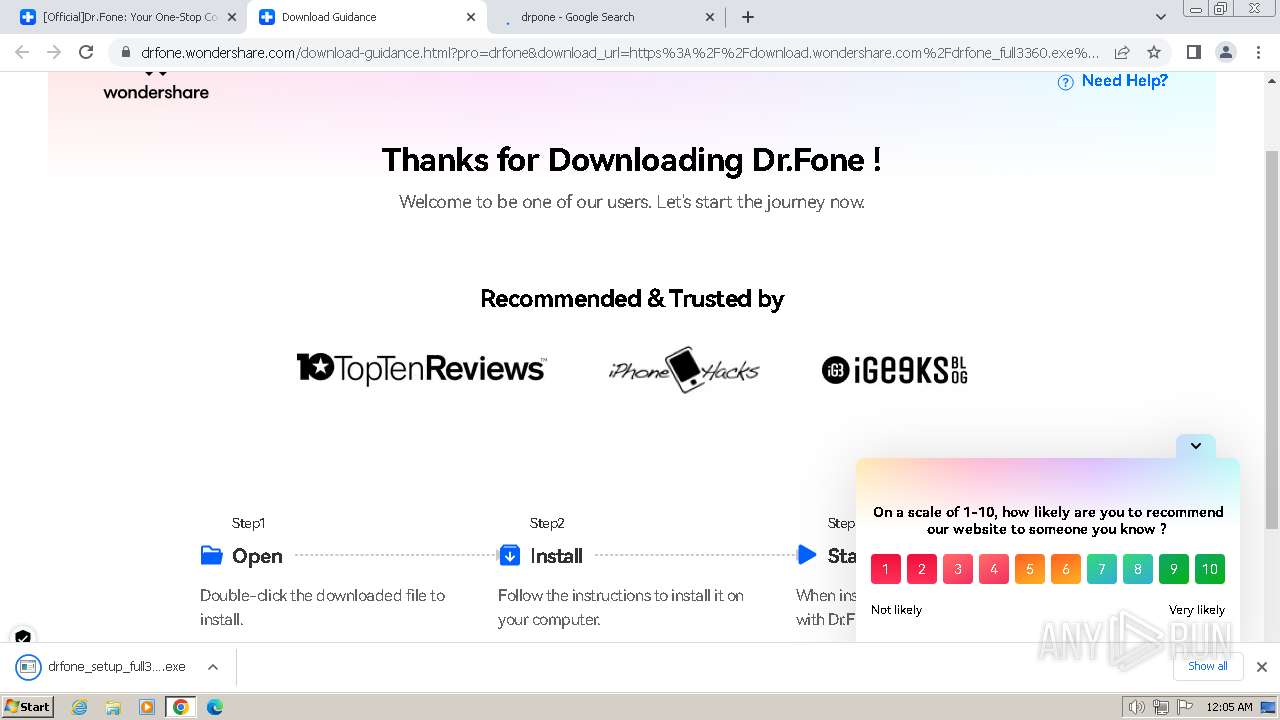
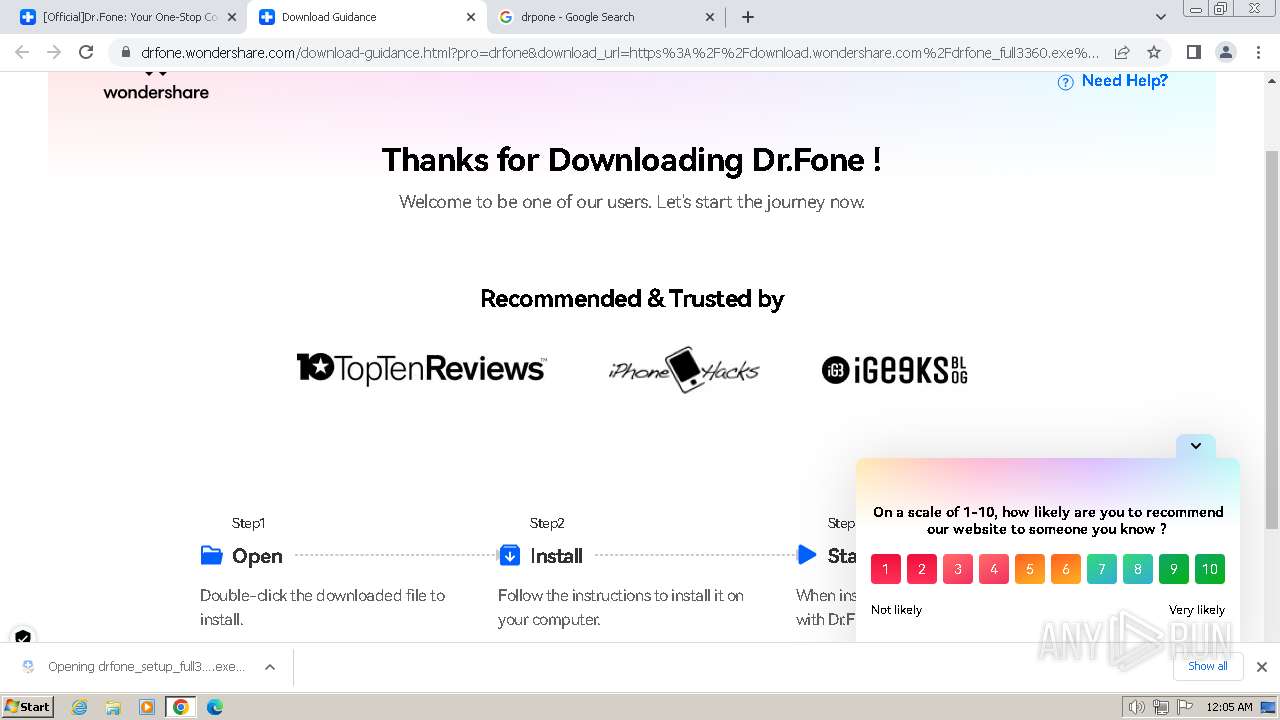
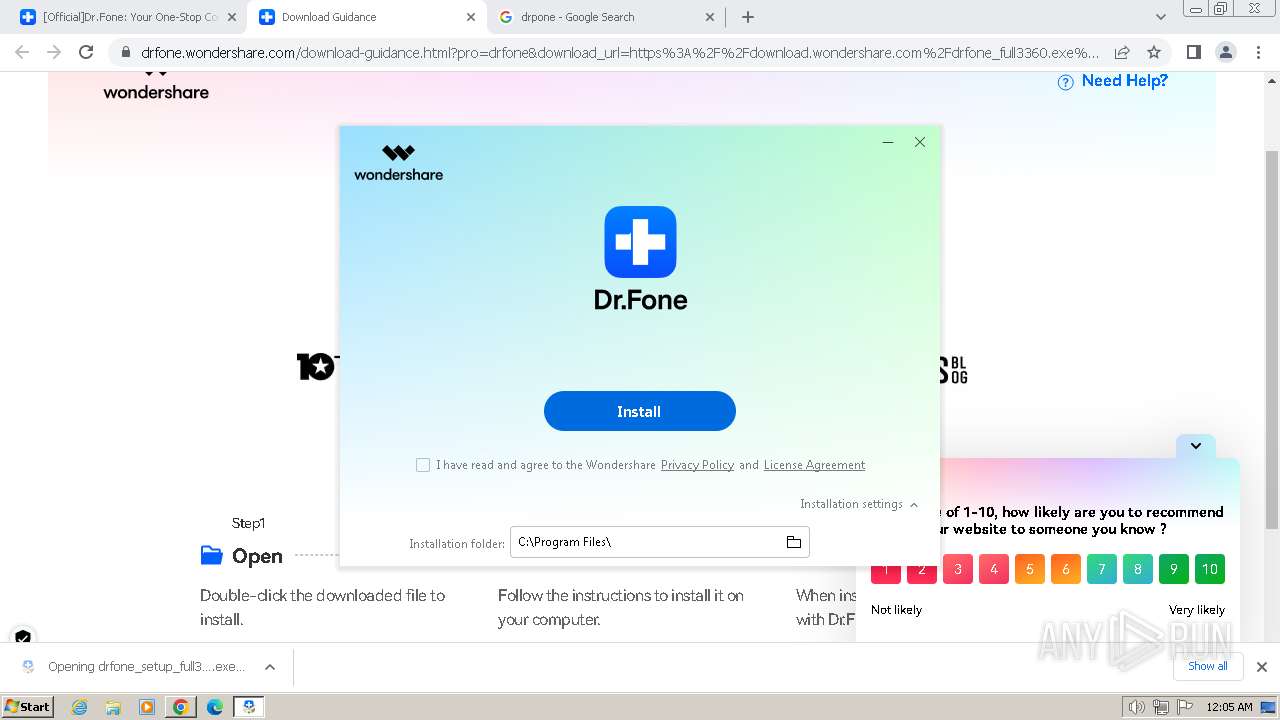
| URL: | drfone.wondershare.com |
| Full analysis: | https://app.any.run/tasks/35c2ae5f-4c50-4d87-988e-7c39e043a1c7 |
| Verdict: | Malicious activity |
| Analysis date: | March 20, 2024, 00:04:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 65139C3171EEFAA9467543C84C809941 |
| SHA1: | A80B27BFC1A56FF28E7333E081A246409B4FCA14 |
| SHA256: | E3062121C459B29FF62BEB0E4C9A4FF3D8726E7C86CDBEB1AA17BE93514F73F8 |
| SSDEEP: | 3:VQu5L2PQLGKI:O2CQLGT |
MALICIOUS
Drops the executable file immediately after the start
- drfone_setup_full3360.exe (PID: 3584)
SUSPICIOUS
Reads Microsoft Outlook installation path
- drfone_setup_full3360.exe (PID: 3584)
Reads security settings of Internet Explorer
- drfone_setup_full3360.exe (PID: 3584)
Reads the Internet Settings
- drfone_setup_full3360.exe (PID: 3584)
Checks Windows Trust Settings
- drfone_setup_full3360.exe (PID: 3584)
Reads settings of System Certificates
- drfone_setup_full3360.exe (PID: 3584)
Process requests binary or script from the Internet
- drfone_setup_full3360.exe (PID: 3584)
Reads Internet Explorer settings
- drfone_setup_full3360.exe (PID: 3584)
Likely accesses (executes) a file from the Public directory
- NFWCHK.exe (PID: 1636)
Executable content was dropped or overwritten
- drfone_setup_full3360.exe (PID: 3584)
Connects to unusual port
- drfone_setup_full3360.exe (PID: 3584)
INFO
Checks supported languages
- drfone_setup_full3360.exe (PID: 3584)
- NFWCHK.exe (PID: 1636)
Drops the executable file immediately after the start
- chrome.exe (PID: 2124)
- chrome.exe (PID: 1036)
Executable content was dropped or overwritten
- chrome.exe (PID: 2124)
- chrome.exe (PID: 1036)
Reads the machine GUID from the registry
- drfone_setup_full3360.exe (PID: 3584)
- NFWCHK.exe (PID: 1636)
The process uses the downloaded file
- chrome.exe (PID: 2356)
- chrome.exe (PID: 2124)
Create files in a temporary directory
- drfone_setup_full3360.exe (PID: 3584)
Reads the computer name
- drfone_setup_full3360.exe (PID: 3584)
- NFWCHK.exe (PID: 1636)
Checks proxy server information
- drfone_setup_full3360.exe (PID: 3584)
Creates files in the program directory
- drfone_setup_full3360.exe (PID: 3584)
Creates files or folders in the user directory
- drfone_setup_full3360.exe (PID: 3584)
Application launched itself
- chrome.exe (PID: 2124)
Reads the software policy settings
- drfone_setup_full3360.exe (PID: 3584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
34
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2016 --field-trial-handle=1160,i,8130996250787628257,8759052957091324260,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1900 --field-trial-handle=1160,i,8130996250787628257,8759052957091324260,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
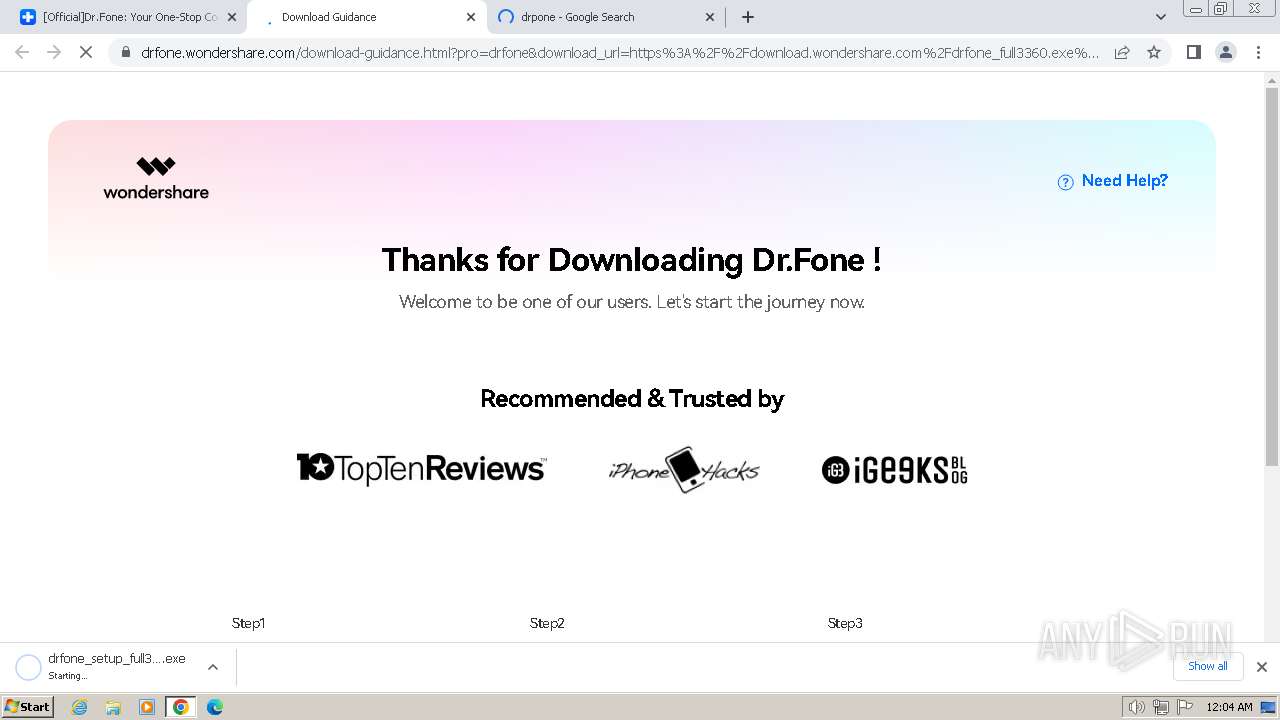
| 864 | "C:\Users\admin\Downloads\drfone_setup_full3360.exe" | C:\Users\admin\Downloads\drfone_setup_full3360.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: drfone_setup_full3360.exe Exit code: 3221226540 Version: 4.0.4.18 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3764 --field-trial-handle=1160,i,8130996250787628257,8759052957091324260,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3056 --field-trial-handle=1160,i,8130996250787628257,8759052957091324260,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1636 | C:\Users\Public\Documents\Wondershare\NFWCHK.exe | C:\Users\Public\Documents\Wondershare\NFWCHK.exe | — | drfone_setup_full3360.exe | |||||||||||
User: admin Company: Wondershare Integrity Level: HIGH Description: .NET Framework Checker Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=3468 --field-trial-handle=1160,i,8130996250787628257,8759052957091324260,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3496 --field-trial-handle=1160,i,8130996250787628257,8759052957091324260,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3648 --field-trial-handle=1160,i,8130996250787628257,8759052957091324260,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1500 --field-trial-handle=1160,i,8130996250787628257,8759052957091324260,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
19 982
Read events
19 808
Write events
157
Delete events
17
Modification events
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
8
Suspicious files
37
Text files
67
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF182a86.TMP | — | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF18408e.TMP | — | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF182aa5.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF184169.TMP | — | |
MD5:— | SHA256:— | |||
| 2124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
79
TCP/UDP connections
180
DNS requests
171
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
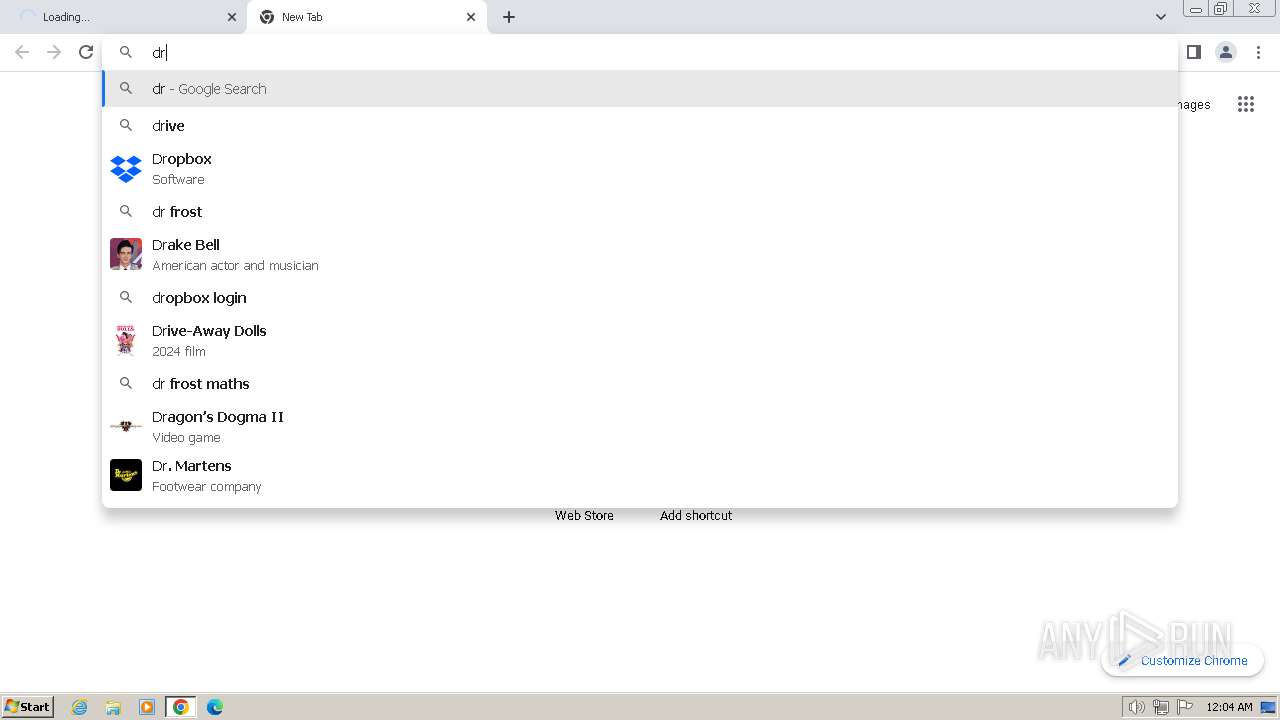
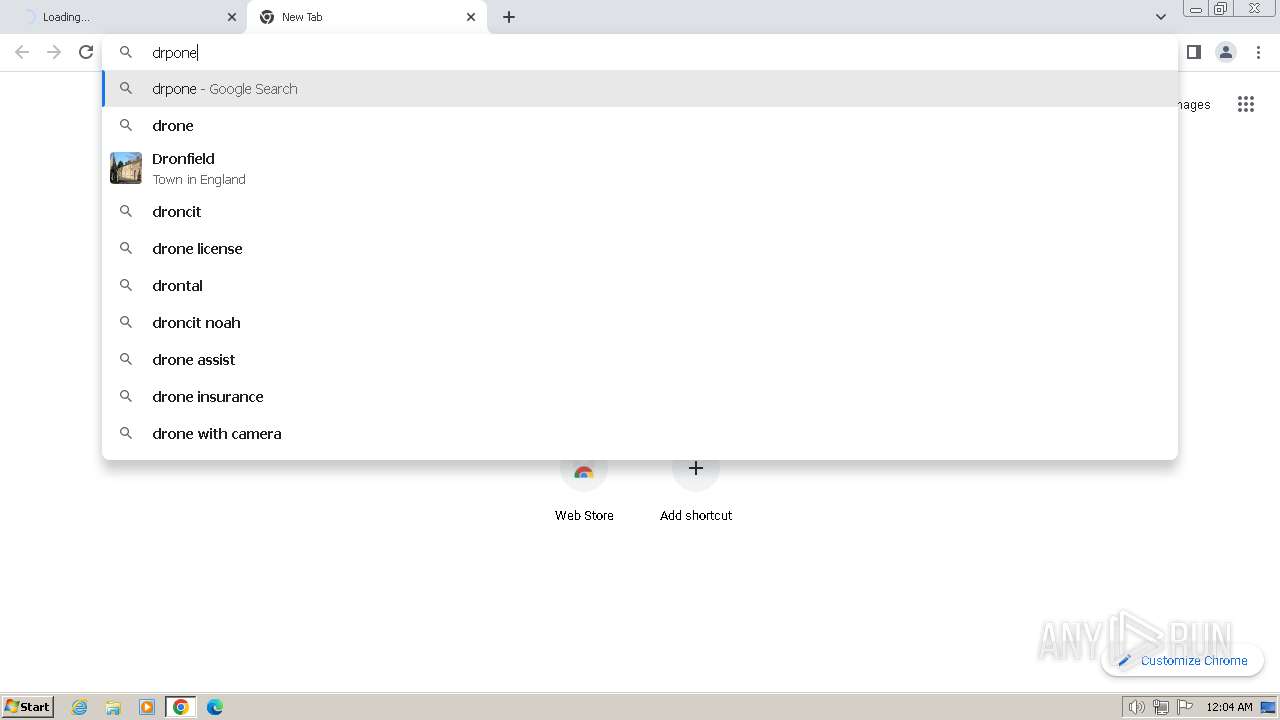
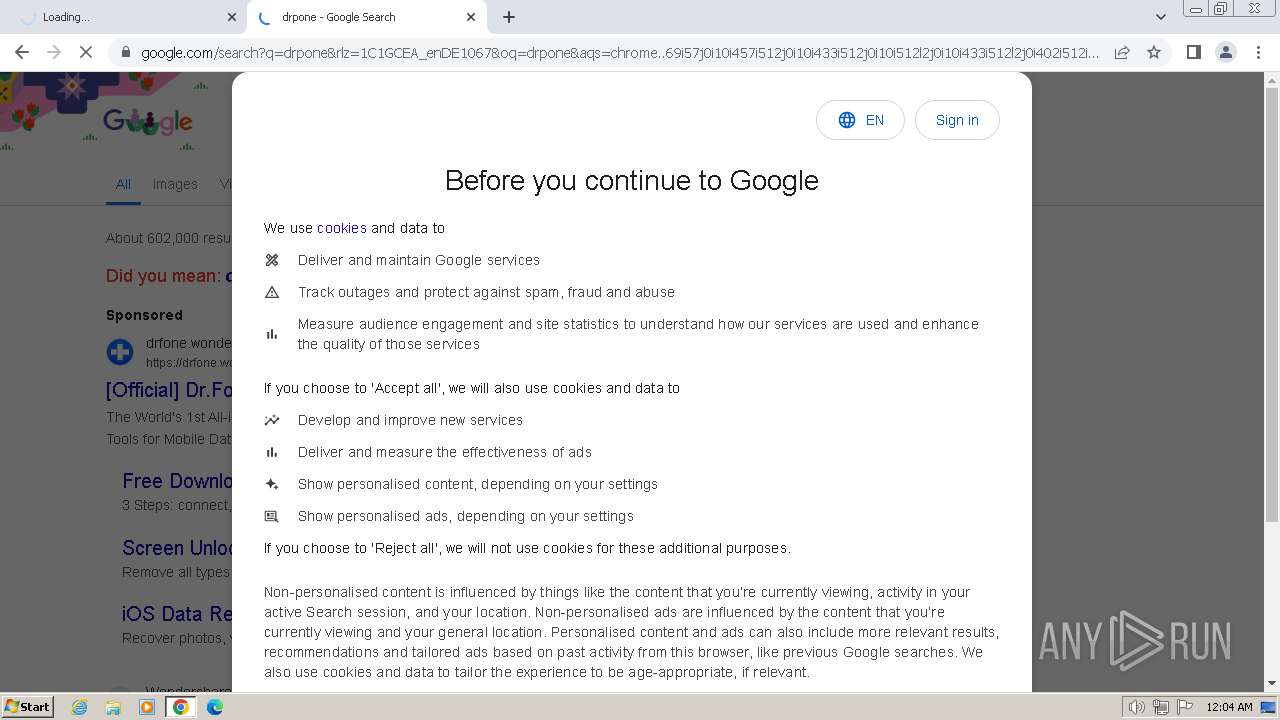
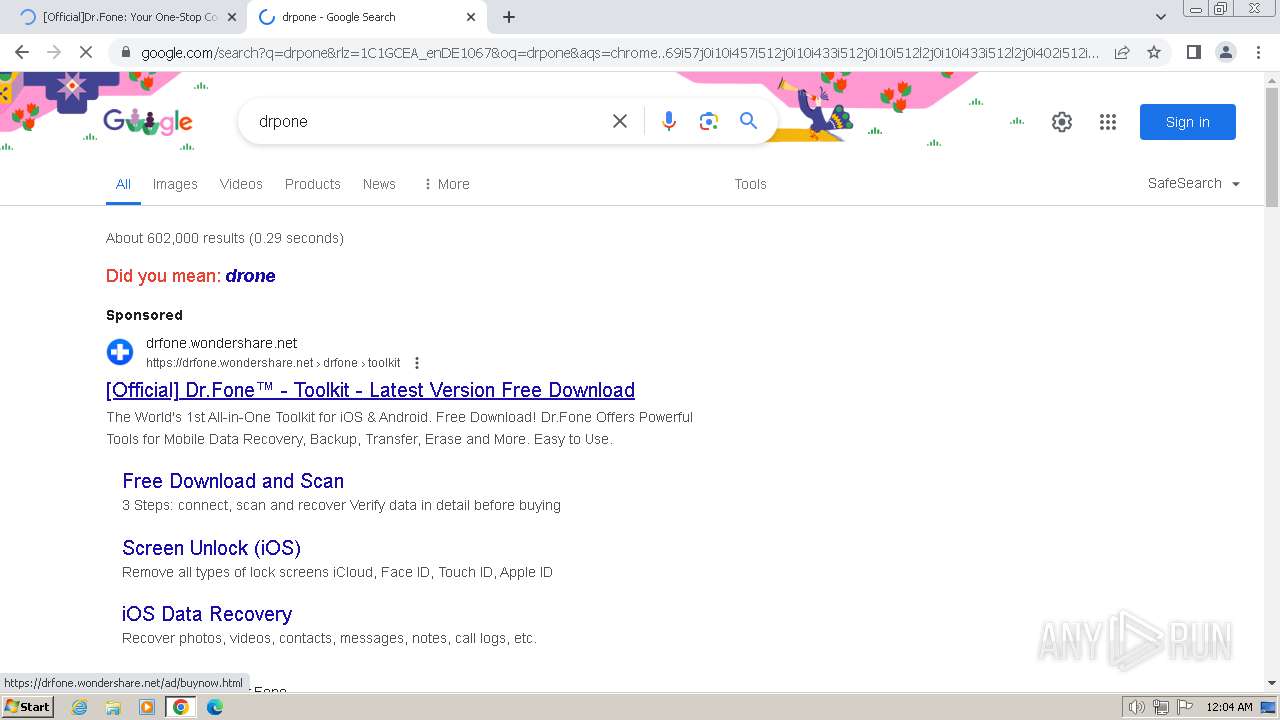
3180 | chrome.exe | GET | 301 | 2.16.164.16:80 | http://drfone.wondershare.com/ | NL | — | — | unknown |
3584 | drfone_setup_full3360.exe | GET | — | 8.209.73.211:80 | http://platform.wondershare.cc/rest/v2/downloader/runtime/?client_sign={d7886a02-be89-4368-9408-8fb73034536eG}&product_id=3360&wae=4.0.4&platform=win_x86 | DE | — | — | unknown |
3584 | drfone_setup_full3360.exe | HEAD | 200 | 23.48.23.50:80 | http://download.wondershare.com/cbs_down/drfone_full3360.exe | DE | — | — | unknown |
3180 | chrome.exe | GET | 204 | 216.58.206.67:80 | http://www.gstatic.com/generate_204 | US | — | — | unknown |
3584 | drfone_setup_full3360.exe | HEAD | 200 | 23.48.23.41:80 | http://download.wondershare.com/cbs_down/drfone_full3360.exe | DE | — | — | unknown |
3584 | drfone_setup_full3360.exe | HEAD | 200 | 23.48.23.50:80 | http://download.wondershare.com/cbs_down/drfone_full3360.exe | DE | — | — | unknown |
3584 | drfone_setup_full3360.exe | GET | — | 23.48.23.41:80 | http://download.wondershare.com/cbs_down/drfone_full3360.exe | DE | — | — | unknown |
3584 | drfone_setup_full3360.exe | GET | 304 | 23.53.40.83:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?096ed8c581ee0365 | DE | — | — | unknown |
3584 | drfone_setup_full3360.exe | GET | 206 | 23.48.23.50:80 | http://download.wondershare.com/cbs_down/drfone_full3360.exe | DE | text | 2 b | unknown |
3584 | drfone_setup_full3360.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQlOydjtpho0%2Bholo77zGjGxETUEQQU8JyF%2FaKffY%2FJaLvV1IlNHb7TkP8CEA3EQd5SLWy5mr7JXcu5TKw%3D | US | binary | 727 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3180 | chrome.exe | 173.194.76.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2124 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3180 | chrome.exe | 2.16.164.16:80 | drfone.wondershare.com | Akamai International B.V. | NL | unknown |
3180 | chrome.exe | 2.16.164.16:443 | drfone.wondershare.com | Akamai International B.V. | NL | unknown |
3180 | chrome.exe | 142.250.186.100:443 | www.google.com | GOOGLE | US | whitelisted |
2124 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3180 | chrome.exe | 2.16.164.90:443 | drfone.wondershare.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
drfone.wondershare.com |
| unknown |
www.google.com |
| whitelisted |
dns.msftncsi.com |
| shared |
encrypted-tbn0.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
lh5.googleusercontent.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3180 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3180 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3180 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3180 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
3584 | drfone_setup_full3360.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3 ETPRO signatures available at the full report