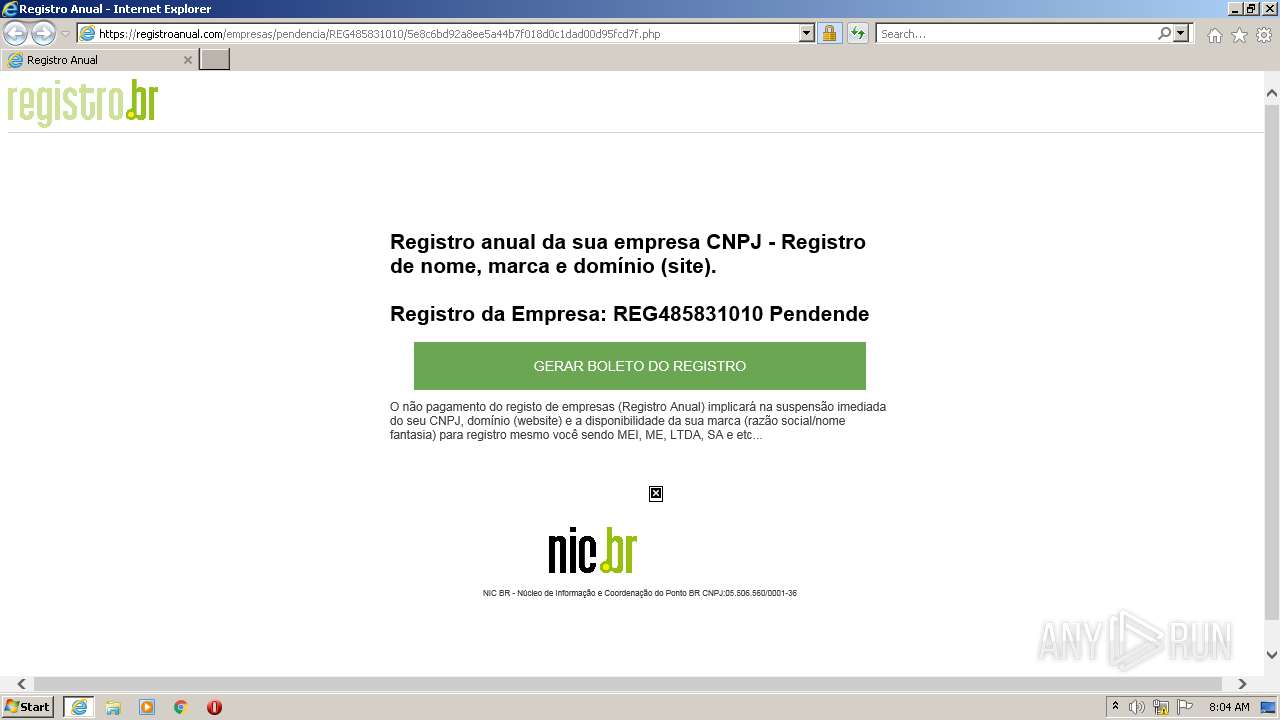
| URL: | http://url6411.registrandoanual.com/ls/click?upn=SVDY8ROdAvhh4-2FltNUSvq3soDLbe0KSK5Rh6jZGXGKAGVp79yJWiYgyv3r8PNp0heNDlp1n1q6BWwIycwqRmznUyP6Qb6NlAyNS3DRFqmP37EV-2BWRc6daOGiJhSl4zM6DMwIGSn3D-2F7QvSzWZZHykQ-3D-3DMTML_kXeW-2F-2FPnIg8g4SSQHK3wrr0ESm3A4gB5VYHpdzq0Q-2B5PTMygQCEtlHyTko98en0ig6NvlGU6lqyiiCxtykDcHCoY64MZz5ZnWuBYxmgTNoHpz-2Fd8qEDlt7pxzm4GEwO1HLKl-2BVdc3SJIFFXLH9ao1JoJYrsHwNWk9Pcdh-2FTs-2Fog7lHnewBG4ieB6trocT7j0mPJZcGNUM96L-2BdyHAa6f9JTHsLbxFxlL5sLOHH6BqOGdQaRyRnzF-2FGq3Hzapk11hE1vF9nvjHT7KIHDyFS9WKcF0k-2BrJTbP9A-2FPyD4maYaVmjrDQijkyQgtwEYZlrWgw2NdCormp0cMMysm37sDTtw-3D-3D |
| Full analysis: | https://app.any.run/tasks/e60211ec-e6eb-490b-bd92-042d39755826 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 07:03:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1700A21B5A4476B6687618E41639D993 |
| SHA1: | 396820C628490BA1C962540DEB33FE232234CA00 |
| SHA256: | E2FF5F4FE4A8552311A0D094E6D388E4613E5E53DAB6F7953EEC1309836834FF |
| SSDEEP: | 12:qLlSdVikD9Su5Eqnaf46GRIfh9ePMdlmaQJnwKa091/EVJfz0yWb:qELatGAhaMdwa7KVyVhk |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Create files in a temporary directory
- iexplore.exe (PID: 1916)
Application launched itself
- iexplore.exe (PID: 1916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1916 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://url6411.registrandoanual.com/ls/click?upn=SVDY8ROdAvhh4-2FltNUSvq3soDLbe0KSK5Rh6jZGXGKAGVp79yJWiYgyv3r8PNp0heNDlp1n1q6BWwIycwqRmznUyP6Qb6NlAyNS3DRFqmP37EV-2BWRc6daOGiJhSl4zM6DMwIGSn3D-2F7QvSzWZZHykQ-3D-3DMTML_kXeW-2F-2FPnIg8g4SSQHK3wrr0ESm3A4gB5VYHpdzq0Q-2B5PTMygQCEtlHyTko98en0ig6NvlGU6lqyiiCxtykDcHCoY64MZz5ZnWuBYxmgTNoHpz-2Fd8qEDlt7pxzm4GEwO1HLKl-2BVdc3SJIFFXLH9ao1JoJYrsHwNWk9Pcdh-2FTs-2Fog7lHnewBG4ieB6trocT7j0mPJZcGNUM96L-2BdyHAa6f9JTHsLbxFxlL5sLOHH6BqOGdQaRyRnzF-2FGq3Hzapk11hE1vF9nvjHT7KIHDyFS9WKcF0k-2BrJTbP9A-2FPyD4maYaVmjrDQijkyQgtwEYZlrWgw2NdCormp0cMMysm37sDTtw-3D-3D" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3108 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1916 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
36 076
Read events
35 864
Write events
208
Delete events
4
Modification events
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
24
Text files
28
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | der | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\5e8c6bd92a8ee5a44b7f018d0c1dad00d95fcd7f[1].htm | html | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\style[1].css | text | |
MD5:— | SHA256:— | |||
| 1916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 1916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\urlblockindex[1].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 3108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 1916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:BDBBD793778777706223B00A4EA24ED0 | SHA256:8B1034038298FAF34D3F580C1DED7212F40D146DE7E62CFF20826C8B53F80C36 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
33
DNS requests
19
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD%2FB2zZ7cy1JAocIdUzcD8Q | US | der | 472 b | whitelisted |
— | — | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
1916 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3108 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCI%2B8jA50qshI9kqyOKmkUR | US | der | 472 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | whitelisted |
3108 | iexplore.exe | GET | 302 | 167.89.123.124:80 | http://url6411.registrandoanual.com/ls/click?upn=SVDY8ROdAvhh4-2FltNUSvq3soDLbe0KSK5Rh6jZGXGKAGVp79yJWiYgyv3r8PNp0heNDlp1n1q6BWwIycwqRmznUyP6Qb6NlAyNS3DRFqmP37EV-2BWRc6daOGiJhSl4zM6DMwIGSn3D-2F7QvSzWZZHykQ-3D-3DMTML_kXeW-2F-2FPnIg8g4SSQHK3wrr0ESm3A4gB5VYHpdzq0Q-2B5PTMygQCEtlHyTko98en0ig6NvlGU6lqyiiCxtykDcHCoY64MZz5ZnWuBYxmgTNoHpz-2Fd8qEDlt7pxzm4GEwO1HLKl-2BVdc3SJIFFXLH9ao1JoJYrsHwNWk9Pcdh-2FTs-2Fog7lHnewBG4ieB6trocT7j0mPJZcGNUM96L-2BdyHAa6f9JTHsLbxFxlL5sLOHH6BqOGdQaRyRnzF-2FGq3Hzapk11hE1vF9nvjHT7KIHDyFS9WKcF0k-2BrJTbP9A-2FPyD4maYaVmjrDQijkyQgtwEYZlrWgw2NdCormp0cMMysm37sDTtw-3D-3D | US | html | 125 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 2.18 Kb | whitelisted |
— | — | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3108 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?76ce3b6368335e5d | US | compressed | 4.70 Kb | whitelisted |
3108 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3108 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3108 | iexplore.exe | 162.241.2.98:443 | registroanual.com | OIS1 | US | malicious |
1916 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3108 | iexplore.exe | 172.64.155.188:80 | ocsp.usertrust.com | CLOUDFLARENET | US | suspicious |
1916 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
3108 | iexplore.exe | 104.26.7.17:443 | logodownload.org | CLOUDFLARENET | US | malicious |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 91.198.174.208:443 | upload.wikimedia.org | WIKIMEDIA | US | suspicious |
1916 | iexplore.exe | 162.241.2.98:443 | registroanual.com | OIS1 | US | malicious |
3108 | iexplore.exe | 142.250.185.200:443 | www.googletagmanager.com | GOOGLE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
registroanual.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Custom Logo Domain Domain in DNS Lookup (logodownload .org) |
— | — | Misc activity | ET INFO Custom Logo Domain in DNS Lookup (seeklogo .com) |
3108 | iexplore.exe | Misc activity | ET INFO Observed Custom Logo Domain (seeklogo .com in TLS SNI) |
3108 | iexplore.exe | Misc activity | ET INFO Observed Custom Logo Domain (seeklogo .com in TLS SNI) |