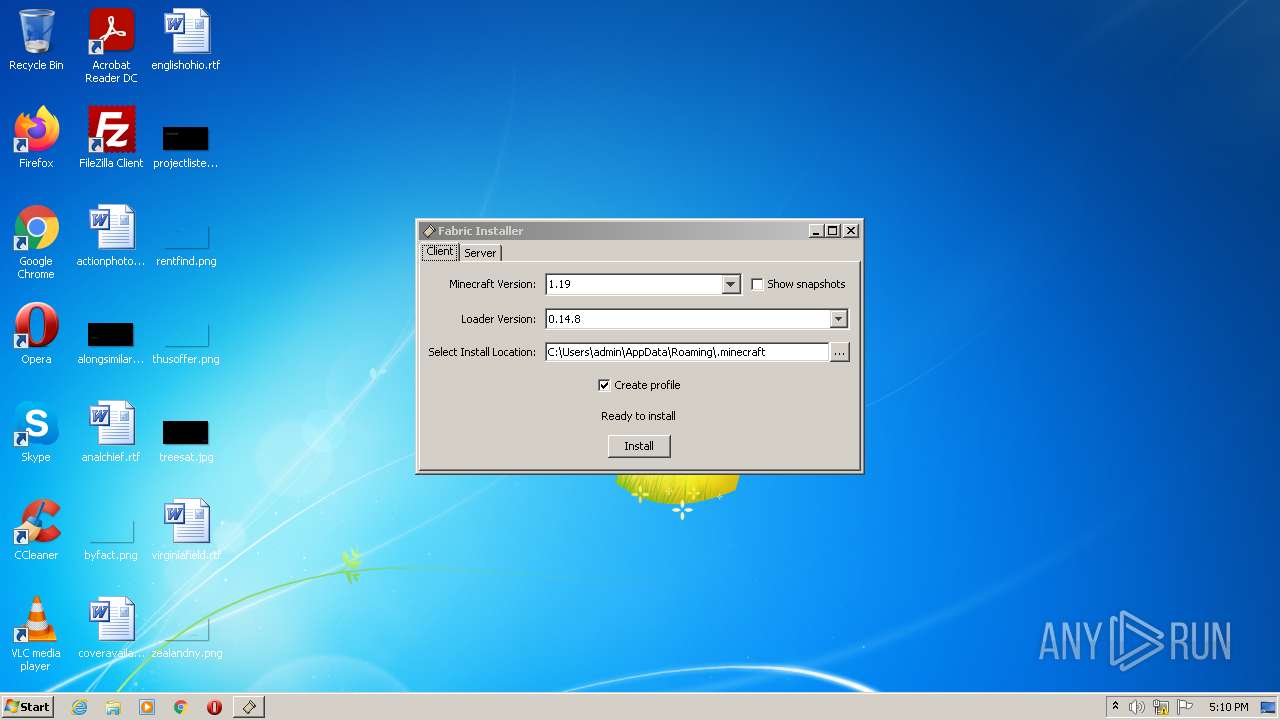
| File name: | fabric-installer-0.11.0.exe |
| Full analysis: | https://app.any.run/tasks/aa8915d3-bdca-40ab-8543-2ec4fdc806c3 |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2022, 16:10:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 63E2142033C22591D3639F10E3F749AF |
| SHA1: | 4FFC683629E8AB752D225C0058802210E45D4DCA |
| SHA256: | E2FDD27187734664147BC18725AE8C0ADA81782A3416AB58DD6974292B03A0F2 |
| SSDEEP: | 6144:XbOTF9+lw27APRw3zeFAO8X+KAWVPb/siEIxfc6rP2sbddie4syabpA0:L+z+u9ZF6uKAWVPbzEyV2uFfx |
MALICIOUS
Changes settings of System certificates
- javaw.exe (PID: 2604)
SUSPICIOUS
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 2936)
Checks supported languages
- javaw.exe (PID: 2936)
- fabric-installer-0.11.0.exe (PID: 3832)
- javaw.exe (PID: 2604)
- cmd.exe (PID: 3692)
- cmd.exe (PID: 3556)
Check for Java to be installed
- javaw.exe (PID: 2936)
- javaw.exe (PID: 2604)
Creates files in the program directory
- javaw.exe (PID: 2936)
Reads the computer name
- javaw.exe (PID: 2604)
INFO
Checks supported languages
- icacls.exe (PID: 2420)
Reads the computer name
- icacls.exe (PID: 2420)
Reads settings of System Certificates
- javaw.exe (PID: 2604)
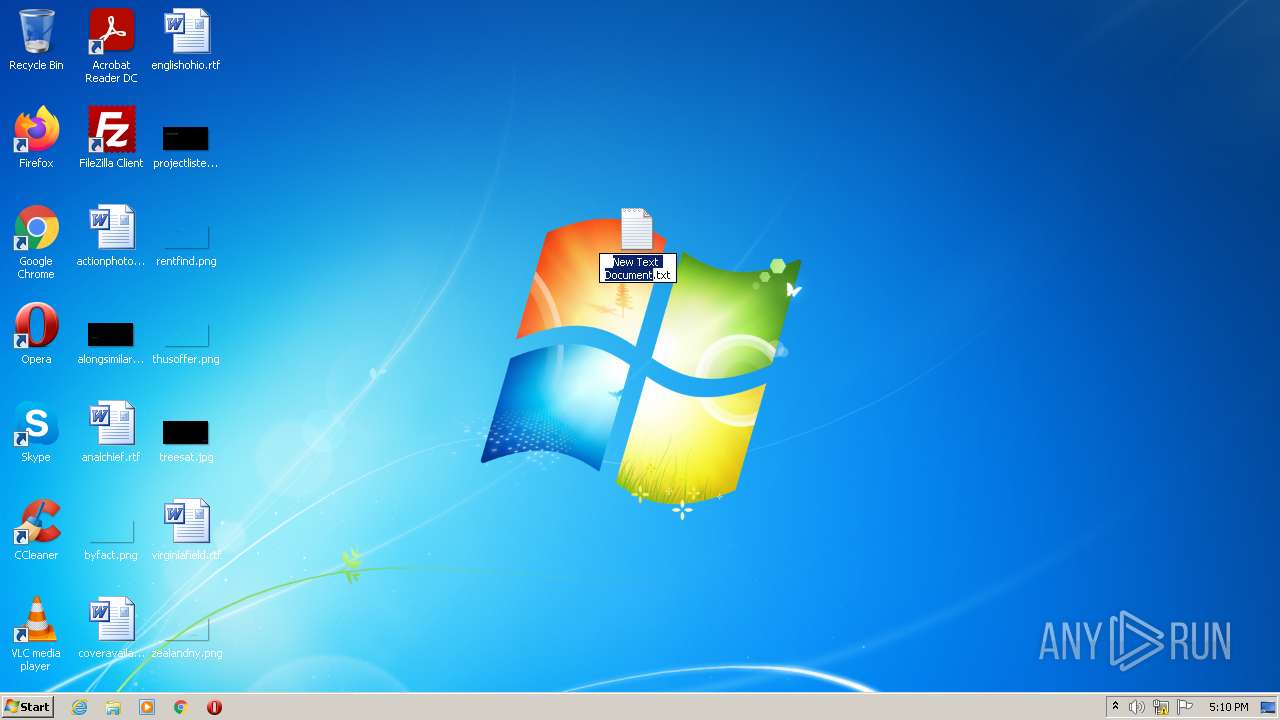
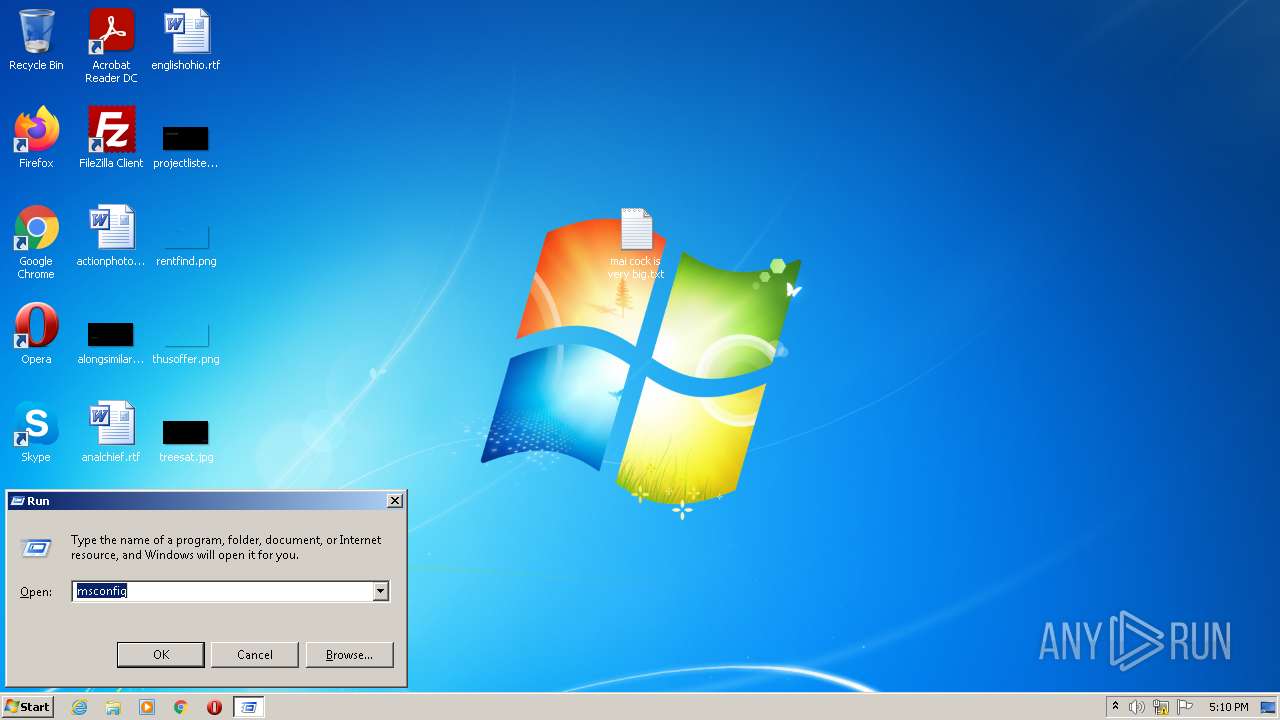
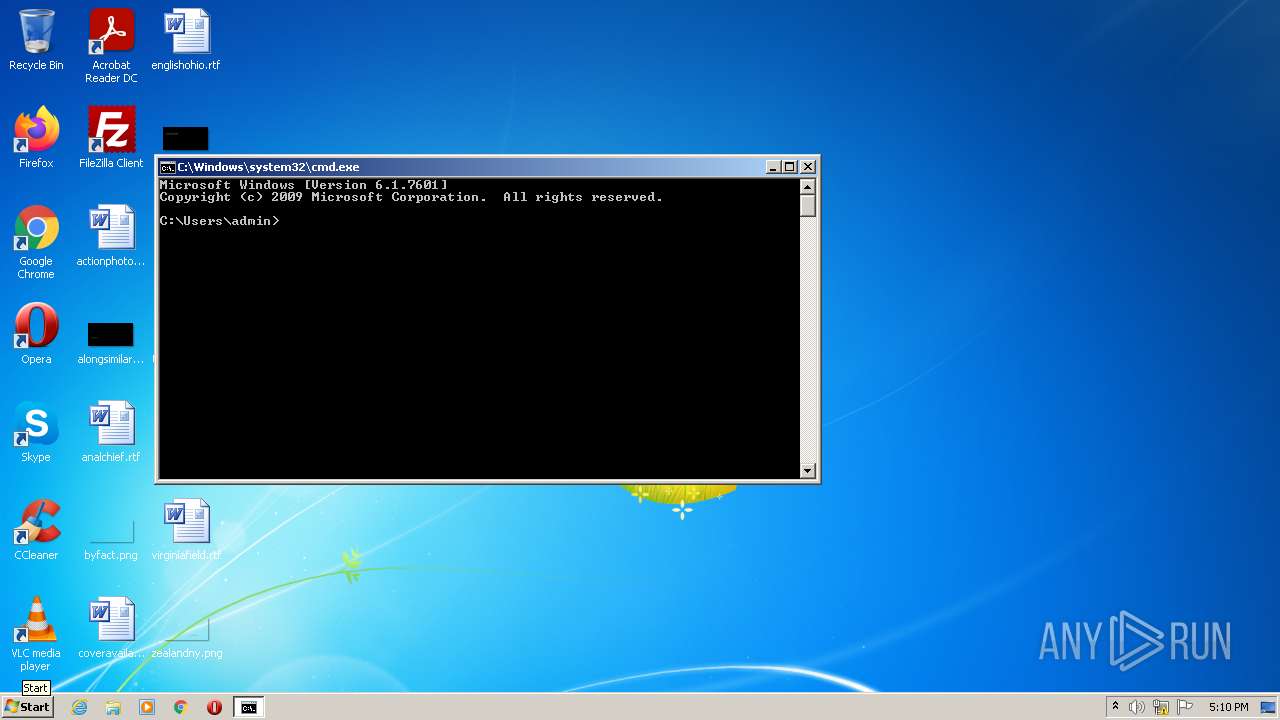
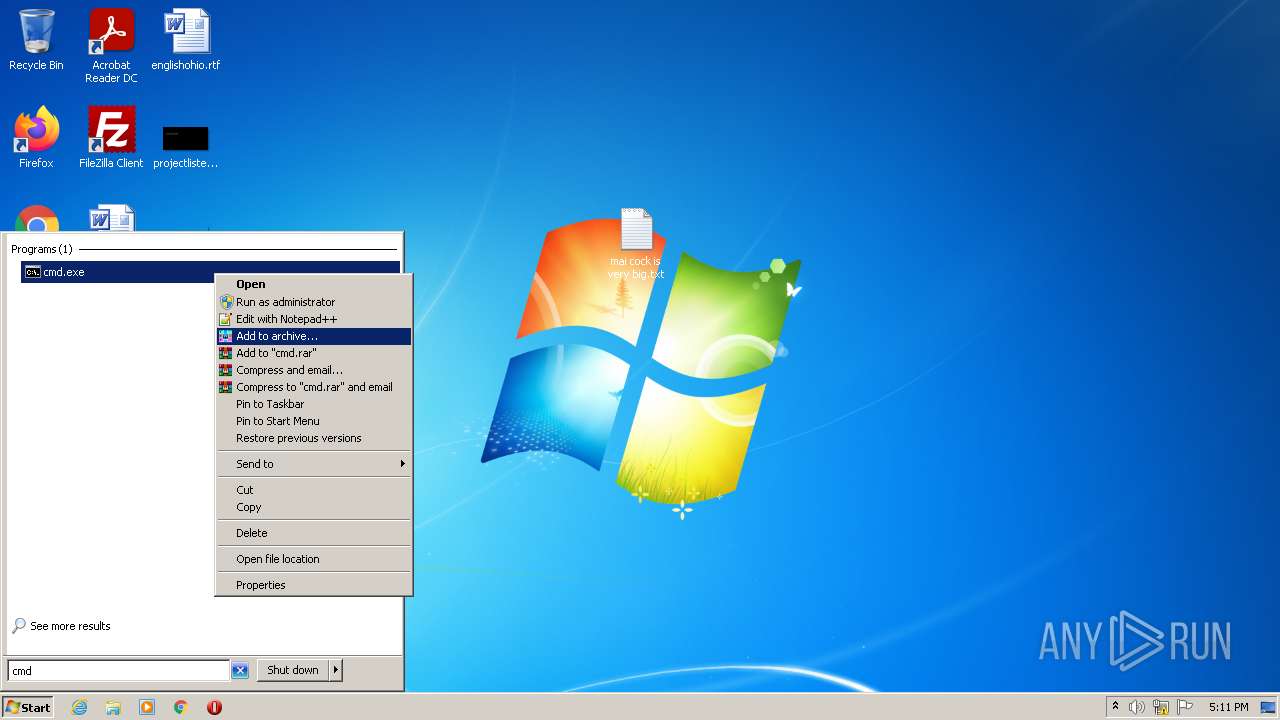
Manual execution by user
- cmd.exe (PID: 3692)
- cmd.exe (PID: 3556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| ProductVersion: | 1.0.0.1 |
|---|---|
| ProductName: | Fabric Installer |
| OriginalFileName: | fabric-installer-native-bootstrap.exe |
| LegalCopyright: | Copyright (C) 2022 |
| InternalName: | fabric-i.exe |
| FileVersion: | 1.0.0.1 |
| FileDescription: | Fabric Installer |
| CompanyName: | Fabric Team |
| CharacterSet: | Unicode |
| LanguageCode: | English (British) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.1 |
| FileVersionNumber: | 1.0.0.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x93b6 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 98304 |
| CodeSize: | 129024 |
| LinkerVersion: | 14.32 |
| PEType: | PE32 |
| TimeStamp: | 2022:05:18 13:44:43+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-May-2022 11:44:43 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Fabric Team |
| FileDescription: | Fabric Installer |
| FileVersion: | 1.0.0.1 |
| InternalName: | fabric-i.exe |
| LegalCopyright: | Copyright (C) 2022 |
| OriginalFilename: | fabric-installer-native-bootstrap.exe |
| ProductName: | Fabric Installer |
| ProductVersion: | 1.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 18-May-2022 11:44:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F60C | 0x0001F800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58408 |
.rdata | 0x00021000 | 0x0000E154 | 0x0000E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.31702 |
.data | 0x00030000 | 0x00001F08 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.09927 |
.rsrc | 0x00032000 | 0x00005E28 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.08215 |
.reloc | 0x00038000 | 0x00001D1C | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.47818 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18919 | 2053 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.47108 | 2440 | UNKNOWN | English - United States | RT_ICON |
3 | 4.15865 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 3.67261 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 7.45316 | 3220 | UNKNOWN | English - United States | RT_ICON |
101 | 2.81633 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
45
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2420 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2604 | "javaw.exe" "-jar" "C:\Users\admin\AppData\Local\Temp\fabric-installer-0.11.0.exe" "-fabricInstallerBootstrap" "true" | C:\Program Files\Common Files\Oracle\Java\javapath\javaw.exe | fabric-installer-0.11.0.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2936 | "javaw.exe" "-version" | C:\Program Files\Common Files\Oracle\Java\javapath\javaw.exe | — | fabric-installer-0.11.0.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 3556 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3692 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3832 | "C:\Users\admin\AppData\Local\Temp\fabric-installer-0.11.0.exe" | C:\Users\admin\AppData\Local\Temp\fabric-installer-0.11.0.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Fabric Team Integrity Level: MEDIUM Description: Fabric Installer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
5 718
Read events
5 699
Write events
19
Delete events
0
Modification events
| (PID) Process: | (2604) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (2604) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2604) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\SystemCertificates\Root\Certificates\C7C20953EB5AC83C81CA388170EEC982E577F810 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000F7998935234BC4DE2CB672C84BD550341900000001000000100000000FED148DCA9288CFE9E8CFEDE332D41E0F00000001000000200000003940FA3A00F54D92B7F88E2D48C2772C8ABB2A13E49A0D26CD13424C4B551832030000000100000014000000C7C20953EB5AC83C81CA388170EEC982E577F810140000000100000014000000396A962A0D9CA2D65CF53FD9D5915A728280AB800200000001000000CC0000001C0000006C00000001000000000000000000000000000000010000007B00410032003900380043003100300039002D0036004300440030002D0034004600410044002D0042003300370046002D004600430039003500360045003100340046004200440036007D00000000004D006900630072006F0073006F0066007400200045006E00680061006E006300650064002000430072007900700074006F0067007200610070006800690063002000500072006F00760069006400650072002000760031002E0030000000000020000000010000004C0300003082034830820230A0030201020209009BC2D79761F68C84300D06092A864886F70D01010B05003039310B30090603550406130241553113301106035504080C0A536F6D652D537461746531153013060355040A0C0C536F6D652D436F6D70616E79301E170D3230303932383036333030355A170D3330303932363036333030355A3039310B30090603550406130241553113301106035504080C0A536F6D652D537461746531153013060355040A0C0C536F6D652D436F6D70616E7930820122300D06092A864886F70D01010105000382010F003082010A0282010100A20B189EC9265492B7621FFE83B82E05923AB02D2DEE3E20C24BB7D8923FA45D5D62E0925DAF5EABBDD7C870E4D1229FF08A2D78D685E81450475802410F692FBBD1DFA12CE5E60EE26583458D949D7C0EDC212A1DCADB4426B6F6C2BE40B90B95BED978CC99FCBE9C00035C8FEE07200B20EA4B86FD3E9FFE42AAD926D2D381CC4C95AF963C3A19A7C90BC1C084F7434A83B0626E41A8E4EB3AC624E5DBB3D3214D535FC45294D746609F6E69B44DA48305DE63BA6FEF283E2778254E8579ABB0295629954E228B18AB5355FEF0F664D9DCD2C4A5047D4879BE8587687E37DE690C4E0D45927B2384E1BF09BE1F2744B50D54D5CD0B1223F5D31A446401D1A90203010001A3533051301D0603551D0E04160414396A962A0D9CA2D65CF53FD9D5915A728280AB80301F0603551D23041830168014396A962A0D9CA2D65CF53FD9D5915A728280AB80300F0603551D130101FF040530030101FF300D06092A864886F70D01010B0500038201010089391C5F3A6B3AA5CCD58C62CE4DC5E71A59F014066678C1ECB7959D4F5F5ACDF23E1EAD032ECC41C459B54A991C40E23F546C64C424BF954035D94C0F30EA7172E98E40F5D8A9B389A56360D837BDF5149754095403EE1AC7BE6415DEA18C10E98113868D6BD01C1FCA8A7704AAB167D9BA70D4FBCCC8E1836CC11AF03E8A62E13DB2EBF7038E469ED65D1D46B3074D92BB304F8FF41068DEC4BB499974635A8C524E4DA418B524529C641DBA82918A55FFBC82B8688B0838C3CEB24647B6142CDB17837E3978D7C551803638DE839DC9B2F9B368773E9148364ABEACF9ABB4A20A3D72122F22E3E17F0969B4C8C2CAF88C5B5D74EC82C19FA533D01ADD79A3 | |||
| (PID) Process: | (2604) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\SystemCertificates\Root\Certificates\C7C20953EB5AC83C81CA388170EEC982E577F810 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000000800000200000001000000CC0000001C0000006C00000001000000000000000000000000000000010000007B00410032003900380043003100300039002D0036004300440030002D0034004600410044002D0042003300370046002D004600430039003500360045003100340046004200440036007D00000000004D006900630072006F0073006F0066007400200045006E00680061006E006300650064002000430072007900700074006F0067007200610070006800690063002000500072006F00760069006400650072002000760031002E00300000000000140000000100000014000000396A962A0D9CA2D65CF53FD9D5915A728280AB80030000000100000014000000C7C20953EB5AC83C81CA388170EEC982E577F8100F00000001000000200000003940FA3A00F54D92B7F88E2D48C2772C8ABB2A13E49A0D26CD13424C4B5518321900000001000000100000000FED148DCA9288CFE9E8CFEDE332D41E040000000100000010000000F7998935234BC4DE2CB672C84BD5503420000000010000004C0300003082034830820230A0030201020209009BC2D79761F68C84300D06092A864886F70D01010B05003039310B30090603550406130241553113301106035504080C0A536F6D652D537461746531153013060355040A0C0C536F6D652D436F6D70616E79301E170D3230303932383036333030355A170D3330303932363036333030355A3039310B30090603550406130241553113301106035504080C0A536F6D652D537461746531153013060355040A0C0C536F6D652D436F6D70616E7930820122300D06092A864886F70D01010105000382010F003082010A0282010100A20B189EC9265492B7621FFE83B82E05923AB02D2DEE3E20C24BB7D8923FA45D5D62E0925DAF5EABBDD7C870E4D1229FF08A2D78D685E81450475802410F692FBBD1DFA12CE5E60EE26583458D949D7C0EDC212A1DCADB4426B6F6C2BE40B90B95BED978CC99FCBE9C00035C8FEE07200B20EA4B86FD3E9FFE42AAD926D2D381CC4C95AF963C3A19A7C90BC1C084F7434A83B0626E41A8E4EB3AC624E5DBB3D3214D535FC45294D746609F6E69B44DA48305DE63BA6FEF283E2778254E8579ABB0295629954E228B18AB5355FEF0F664D9DCD2C4A5047D4879BE8587687E37DE690C4E0D45927B2384E1BF09BE1F2744B50D54D5CD0B1223F5D31A446401D1A90203010001A3533051301D0603551D0E04160414396A962A0D9CA2D65CF53FD9D5915A728280AB80301F0603551D23041830168014396A962A0D9CA2D65CF53FD9D5915A728280AB80300F0603551D130101FF040530030101FF300D06092A864886F70D01010B0500038201010089391C5F3A6B3AA5CCD58C62CE4DC5E71A59F014066678C1ECB7959D4F5F5ACDF23E1EAD032ECC41C459B54A991C40E23F546C64C424BF954035D94C0F30EA7172E98E40F5D8A9B389A56360D837BDF5149754095403EE1AC7BE6415DEA18C10E98113868D6BD01C1FCA8A7704AAB167D9BA70D4FBCCC8E1836CC11AF03E8A62E13DB2EBF7038E469ED65D1D46B3074D92BB304F8FF41068DEC4BB499974635A8C524E4DA418B524529C641DBA82918A55FFBC82B8688B0838C3CEB24647B6142CDB17837E3978D7C551803638DE839DC9B2F9B368773E9148364ABEACF9ABB4A20A3D72122F22E3E17F0969B4C8C2CAF88C5B5D74EC82C19FA533D01ADD79A3 | |||
| (PID) Process: | (2604) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\SystemCertificates\Root\Certificates\1AD19E83B5CBE31C167AC2D1A3B39556D9D5BBA8 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000326D6193BF898E3DD1206D92E82BCE941400000001000000140000005B58AACB6285C8DA5FEB67AE64F380D2FDF2D1F90200000001000000CC0000001C0000006C00000001000000000000000000000000000000010000007B00440042004600420045003500460030002D0039004100430034002D0034004400370037002D0039003700440036002D004400360030004300410038003200320037003200380032007D00000000004D006900630072006F0073006F0066007400200045006E00680061006E006300650064002000430072007900700074006F0067007200610070006800690063002000500072006F00760069006400650072002000760031002E003000000000000300000001000000140000001AD19E83B5CBE31C167AC2D1A3B39556D9D5BBA80F00000001000000200000001CF3A0AEC1F739093FE97B9E8B77DC9365C5CCD0F726D165CECE7D688D7F2575190000000100000010000000988DECE9A422B1408893FCFCEC642FBB20000000010000007D0300003082037930820261A003020102021433491C4ADC568732917D1A48B1C45C497C992143300D06092A864886F70D01010B0500304C310B30090603550406130255533113301106035504080C0A43616C69666F726E696131133011060355040A0C0A436F6D5369676E2043413113301106035504030C0A436F6D5369676E204341301E170D3230313132363130353730325A170D3330313132343130353730325A304C310B30090603550406130255533113301106035504080C0A43616C69666F726E696131133011060355040A0C0A436F6D5369676E2043413113301106035504030C0A436F6D5369676E20434130820122300D06092A864886F70D01010105000382010F003082010A02820101009DC29041363C826AB5C6B6A161B41D580E749DC723C472121930361D1BF033124CB57764262A4BB4A982BE8FDE0BA1EB248FFF4EA011DFB3ED2B6B0C26D5F2EDFDAA7527F639799C315F748703939979EF689778EF45AC368C45C7F8B5FB9C72577150D44C7F3C95BCAA44E19E448F6AAEB5804D9F3CAFEF397602287B5B9C0AEC689B06F882867053BC20ACEF17AA6E7FAF0B08383D7AF96AC90D491287E1E7ED014AC0C447AF13DBC84F81E4355500284859656299D219A3F02AAA00E533696A4699D99F74ABF690219167F37E9D44BEF3DD3BD8AE6552A648CF5838E4B40DF3E5C952B5AA06721BF1E4C03D22B886E20473EA04AE941AA78BFAC0A00AFF490203010001A3533051301D0603551D0E041604145B58AACB6285C8DA5FEB67AE64F380D2FDF2D1F9301F0603551D230418301680145B58AACB6285C8DA5FEB67AE64F380D2FDF2D1F9300F0603551D130101FF040530030101FF300D06092A864886F70D01010B05000382010100163A9B27CDC22544DB104B30D2E368911B87549B58DFAA5E06FC42000606D118E0B6EA1773E7D898FAC2B4AFD56495F47E3EF68548D4FF6A9E7FFFCBC5B30D6A395A4D987BD9DE44E1FB7C0075723E6893E8D5ADEE600FE1D0F6EF25B15F99E6569E72B2E556CF4ED5C007D77E1096C944AC7E9508F6EB9893FEB900DBBA119816E6F93C3472E1F1A528A53A5D12175539B841831B595DF465708F5D7299A98F98609D7A80ADA0182BE5248056A00236E6B479B6454F449600E805AC59F380A2D887A3F253EB2C21C0FC2D71ADAE2E769364D62FADD4892F77224AEFA755B98D8E9A25920DCD1C16C46E25472DE04FF4D9D87E05894492973854C6F2424B578D | |||
| (PID) Process: | (2604) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\SystemCertificates\Root\Certificates\1AD19E83B5CBE31C167AC2D1A3B39556D9D5BBA8 |
| Operation: | write | Name: | Blob |
Value: 5C000000010000000400000000080000190000000100000010000000988DECE9A422B1408893FCFCEC642FBB0F00000001000000200000001CF3A0AEC1F739093FE97B9E8B77DC9365C5CCD0F726D165CECE7D688D7F25750300000001000000140000001AD19E83B5CBE31C167AC2D1A3B39556D9D5BBA80200000001000000CC0000001C0000006C00000001000000000000000000000000000000010000007B00440042004600420045003500460030002D0039004100430034002D0034004400370037002D0039003700440036002D004400360030004300410038003200320037003200380032007D00000000004D006900630072006F0073006F0066007400200045006E00680061006E006300650064002000430072007900700074006F0067007200610070006800690063002000500072006F00760069006400650072002000760031002E003000000000001400000001000000140000005B58AACB6285C8DA5FEB67AE64F380D2FDF2D1F9040000000100000010000000326D6193BF898E3DD1206D92E82BCE9420000000010000007D0300003082037930820261A003020102021433491C4ADC568732917D1A48B1C45C497C992143300D06092A864886F70D01010B0500304C310B30090603550406130255533113301106035504080C0A43616C69666F726E696131133011060355040A0C0A436F6D5369676E2043413113301106035504030C0A436F6D5369676E204341301E170D3230313132363130353730325A170D3330313132343130353730325A304C310B30090603550406130255533113301106035504080C0A43616C69666F726E696131133011060355040A0C0A436F6D5369676E2043413113301106035504030C0A436F6D5369676E20434130820122300D06092A864886F70D01010105000382010F003082010A02820101009DC29041363C826AB5C6B6A161B41D580E749DC723C472121930361D1BF033124CB57764262A4BB4A982BE8FDE0BA1EB248FFF4EA011DFB3ED2B6B0C26D5F2EDFDAA7527F639799C315F748703939979EF689778EF45AC368C45C7F8B5FB9C72577150D44C7F3C95BCAA44E19E448F6AAEB5804D9F3CAFEF397602287B5B9C0AEC689B06F882867053BC20ACEF17AA6E7FAF0B08383D7AF96AC90D491287E1E7ED014AC0C447AF13DBC84F81E4355500284859656299D219A3F02AAA00E533696A4699D99F74ABF690219167F37E9D44BEF3DD3BD8AE6552A648CF5838E4B40DF3E5C952B5AA06721BF1E4C03D22B886E20473EA04AE941AA78BFAC0A00AFF490203010001A3533051301D0603551D0E041604145B58AACB6285C8DA5FEB67AE64F380D2FDF2D1F9301F0603551D230418301680145B58AACB6285C8DA5FEB67AE64F380D2FDF2D1F9300F0603551D130101FF040530030101FF300D06092A864886F70D01010B05000382010100163A9B27CDC22544DB104B30D2E368911B87549B58DFAA5E06FC42000606D118E0B6EA1773E7D898FAC2B4AFD56495F47E3EF68548D4FF6A9E7FFFCBC5B30D6A395A4D987BD9DE44E1FB7C0075723E6893E8D5ADEE600FE1D0F6EF25B15F99E6569E72B2E556CF4ED5C007D77E1096C944AC7E9508F6EB9893FEB900DBBA119816E6F93C3472E1F1A528A53A5D12175539B841831B595DF465708F5D7299A98F98609D7A80ADA0182BE5248056A00236E6B479B6454F449600E805AC59F380A2D887A3F253EB2C21C0FC2D71ADAE2E769364D62FADD4892F77224AEFA755B98D8E9A25920DCD1C16C46E25472DE04FF4D9D87E05894492973854C6F2424B578D | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2604 | javaw.exe | 188.114.96.3:443 | meta.fabricmc.net | Cloudflare Inc | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
meta.fabricmc.net |
| whitelisted |