| download: | 12345.exe |
| Full analysis: | https://app.any.run/tasks/f616304c-a24f-44d4-8d9f-f305a9adbc62 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | January 25, 2022, 01:13:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 02A3C2D3F197ED23FC0A5EF370BB28CA |
| SHA1: | 2BE53D774B008E125B456BC40BEB92E9019A49A5 |
| SHA256: | E2F4F19D9B41B76AEEF1345D8F78B32E190C682BAFB8B9EBEA7D72681CF00DB6 |
| SSDEEP: | 196608:Fy+OxIYjoCaMM82kOsO/hx9/jDXj0uEQTUe1ii9MzyF:xyIytOXsyn9jD4GUepBF |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2612)
- cmd.exe (PID: 2312)
- cmd.exe (PID: 2580)
Changes the autorun value in the registry
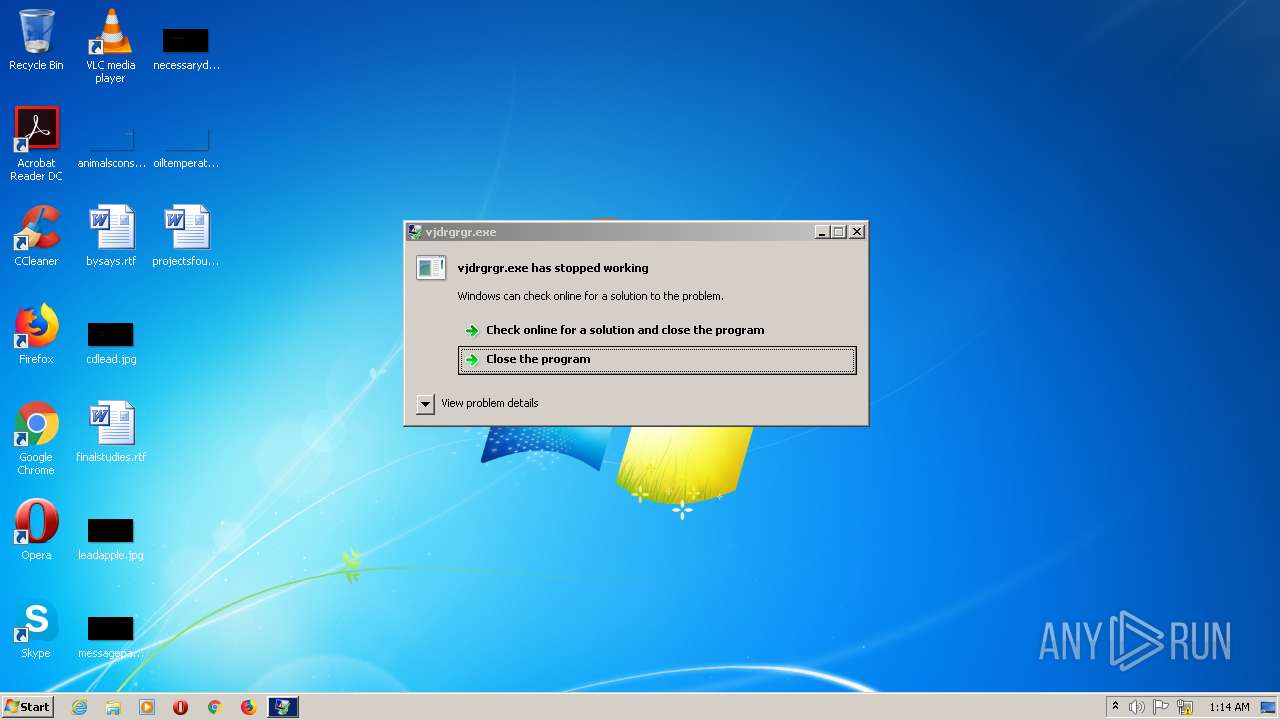
- vjdrgrgr.exe (PID: 3056)
Disables Windows Defender
- vjdrgrgr.exe (PID: 3056)
Drops executable file immediately after starts
- vjdrgrgr.exe (PID: 3056)
Application was dropped or rewritten from another process
- vjdrgrgr.exe (PID: 3056)
- sadido.exe (PID: 2548)
- addttc.exe (PID: 2692)
- sihost64.exe (PID: 2312)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 260)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2820)
MINER was detected
- explorer.exe (PID: 1700)
Connects to CnC server
- explorer.exe (PID: 1700)
SUSPICIOUS
Checks supported languages
- powershell.exe (PID: 3036)
- 12345.exe (PID: 2932)
- cmd.exe (PID: 2820)
- cmd.exe (PID: 2408)
- cmd.exe (PID: 2612)
- vjdrgrgr.exe (PID: 3056)
- sadido.exe (PID: 2548)
- powershell.exe (PID: 1384)
- cmd.exe (PID: 2312)
- powershell.exe (PID: 2400)
- cmd.exe (PID: 260)
- addttc.exe (PID: 2692)
- cmd.exe (PID: 2724)
- powershell.exe (PID: 3052)
- sihost64.exe (PID: 2312)
- cmd.exe (PID: 2580)
- powershell.exe (PID: 2648)
- powershell.exe (PID: 2848)
Drops a file with a compile date too recent
- 12345.exe (PID: 2932)
- vjdrgrgr.exe (PID: 3056)
Executable content was dropped or overwritten
- 12345.exe (PID: 2932)
- vjdrgrgr.exe (PID: 3056)
- sadido.exe (PID: 2548)
- addttc.exe (PID: 2692)
Starts CMD.EXE for commands execution
- 12345.exe (PID: 2932)
- sadido.exe (PID: 2548)
- addttc.exe (PID: 2692)
Drops a file with too old compile date
- 12345.exe (PID: 2932)
- sadido.exe (PID: 2548)
- addttc.exe (PID: 2692)
Reads the computer name
- powershell.exe (PID: 3036)
- vjdrgrgr.exe (PID: 3056)
- powershell.exe (PID: 1384)
- sadido.exe (PID: 2548)
- powershell.exe (PID: 2400)
- addttc.exe (PID: 2692)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 2648)
- powershell.exe (PID: 2848)
Creates files in the user directory
- vjdrgrgr.exe (PID: 3056)
- sadido.exe (PID: 2548)
- addttc.exe (PID: 2692)
Drops a file that was compiled in debug mode
- addttc.exe (PID: 2692)
INFO
Checks Windows Trust Settings
- powershell.exe (PID: 3036)
- powershell.exe (PID: 1384)
- powershell.exe (PID: 2400)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 2648)
- powershell.exe (PID: 2848)
Reads settings of System Certificates
- powershell.exe (PID: 3036)
- powershell.exe (PID: 1384)
- powershell.exe (PID: 2400)
- powershell.exe (PID: 3052)
- powershell.exe (PID: 2648)
- powershell.exe (PID: 2848)
Checks supported languages
- schtasks.exe (PID: 2820)
- explorer.exe (PID: 1700)
- conhost.exe (PID: 2388)
Reads the computer name
- schtasks.exe (PID: 2820)
- conhost.exe (PID: 2388)
- explorer.exe (PID: 1700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x14e5 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 6889472 |
| CodeSize: | 2048 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 0000:00:00 00:00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000680 | 0x00000800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.54686 |
.rdata | 0x00002000 | 0x00691D52 | 0x00691E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.39964 |
.bss | 0x00694000 | 0x00000004 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00695000 | 0x000001F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.80743 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85064 | 408 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
kernel32.dll |
msvcrt.dll |
Total processes
71
Monitored processes
22
Malicious processes
7
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 260 | "cmd" /c schtasks /create /f /sc onlogon /rl highest /tn "addttc" /tr "C:\Users\admin\AppData\Roaming\addttc.exe" | C:\Windows\system32\cmd.exe | sadido.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1384 | powershell -Command "Add-MpPreference -ExclusionExtension @('exe','dll') -Force" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1700 | C:\Windows\explorer.exe emyvmbcfz0 Xji3FXYfqqI2timPThbgZueMNpSES88mLhMz2ywydJS6kTcb2sZJ49Q3iSMDc1H0Gsol2ut25e0CiIvlYsuJiXFNJ4PET7Ssvm1Yua5cY1gF/Y8hpN2zPh3OaRZ3vTM5meO5JS5Nw3rXgdh0GbN9rnLxmH7ugFyhTdsZk/Jbs906EblI/VcGrhxHe9//FVV295PfmP2APVTPyGE5n4d3j3YxbmXRlVnCadTqKB6h+W6bYTAFBhewEjPxeF8UBT9yBch60hJayzqodyvRT6F8pllEZrOLuELWvI14PJOL1Vvh+YVDlxIOxBBMgzbblSfrfPS/WnuHafdsuYxQLX1UZN0xZNEgnLfciGlNOoMrtY7+oQD/xa69guncIxF58hUGpqkU/oM4NXAg8j/FCdJkscrfRIUYrgQEagnYsDDa1qzH/HmXj02FcYwoJXTor5ytwePPi1V/Ad+SfvSPYLKTSw== | C:\Windows\explorer.exe | addttc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2276 | "C:\Users\admin\AppData\Local\Temp\12345.exe" | C:\Users\admin\AppData\Local\Temp\12345.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2312 | "cmd" cmd /c powershell -EncodedCommand "QQBkAGQALQBNAHAAUAByAGUAZgBlAHIAZQBuAGMAZQAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEAAKAAkAGUAbgB2ADoAVQBzAGUAcgBQAHIAbwBmAGkAbABlACwAJABlAG4AdgA6AFMAeQBzAHQAZQBtAEQAcgBpAHYAZQApACAALQBGAG8AcgBjAGUA" & powershell -EncodedCommand "QQBkAGQALQBNAHAAUAByAGUAZgBlAHIAZQBuAGMAZQAgAC0ARQB4AGMAbAB1AHMAaQBvAG4ARQB4AHQAZQBuAHMAaQBvAG4AIABAACgAJwBlAHgAZQAnACwAJwBkAGwAbAAnACkAIAAtAEYAbwByAGMAZQA=" & exit | C:\Windows\system32\cmd.exe | — | sadido.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2312 | "C:\Users\admin\AppData\Roaming\Microsoft\Telemetry\sihost64.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Telemetry\sihost64.exe | — | addttc.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2388 | "C:\Windows\System32\conhost.exe" "xdbhhdrnm" | C:\Windows\System32\conhost.exe | — | sihost64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2400 | powershell -EncodedCommand "QQBkAGQALQBNAHAAUAByAGUAZgBlAHIAZQBuAGMAZQAgAC0ARQB4AGMAbAB1AHMAaQBvAG4AUABhAHQAaAAgAEAAKAAkAGUAbgB2ADoAVQBzAGUAcgBQAHIAbwBmAGkAbABlACwAJABlAG4AdgA6AFMAeQBzAHQAZQBtAEQAcgBpAHYAZQApACAALQBGAG8AcgBjAGUA" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2408 | cmd /c start "" "C:\Users\admin\AppData\Local\Temp\sadido.exe" | C:\Windows\SysWOW64\cmd.exe | — | 12345.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2548 | "C:\Users\admin\AppData\Local\Temp\sadido.exe" | C:\Users\admin\AppData\Local\Temp\sadido.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
8 938
Read events
8 828
Write events
110
Delete events
0
Modification events
| (PID) Process: | (3056) vjdrgrgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableBehaviorMonitoring |
Value: 1 | |||
| (PID) Process: | (3056) vjdrgrgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableOnAccessProtection |
Value: 1 | |||
| (PID) Process: | (3056) vjdrgrgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableScanOnRealtimeEnable |
Value: 1 | |||
| (PID) Process: | (3056) vjdrgrgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | RegHost |
Value: C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | |||
| (PID) Process: | (3036) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\14B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1384) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\14B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2400) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2400) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2400) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2400) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
6
Suspicious files
12
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | 12345.exe | C:\Users\admin\AppData\Local\Temp\vjdrgrgr.exe | executable | |
MD5:— | SHA256:— | |||
| 3036 | powershell.exe | C:\Users\admin\AppData\Local\Temp\l14qqlwb.21n.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2548 | sadido.exe | C:\Users\admin\AppData\Roaming\addttc.exe | executable | |
MD5:— | SHA256:— | |||
| 2932 | 12345.exe | C:\Users\admin\AppData\Local\Temp\sadido.exe | executable | |
MD5:— | SHA256:— | |||
| 3056 | vjdrgrgr.exe | C:\Users\admin\AppData\Roaming\Microsoft\RegHost.exe | executable | |
MD5:— | SHA256:— | |||
| 2848 | powershell.exe | C:\Users\admin\AppData\Local\Temp\jrxnelxl.vgx.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\qkkmbtqa.552.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2400 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wrfvhdhl.li1.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3052 | powershell.exe | C:\Users\admin\AppData\Local\Temp\3jia2jhq.r1m.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2848 | powershell.exe | C:\Users\admin\AppData\Local\Temp\50b4n55b.rtx.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3056 | vjdrgrgr.exe | GET | 502 | 193.163.203.41:80 | http://srv2-tunnel.ttl.ovh/lm | DK | html | 166 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3056 | vjdrgrgr.exe | 193.163.203.41:80 | srv2-tunnel.ttl.ovh | — | DK | suspicious |
1700 | explorer.exe | 91.121.140.167:5555 | pool.supportxmr.com | OVH SAS | FR | malicious |
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
srv2-tunnel.ttl.ovh |
| suspicious |
pool.supportxmr.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1700 | explorer.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |