| File name: | OIETIF.bat |
| Full analysis: | https://app.any.run/tasks/6ec1a708-0e09-4ad2-863c-1482a1224c18 |
| Verdict: | Malicious activity |
| Analysis date: | July 16, 2024, 20:44:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 9D1F2E92E9BC099C51AB4C2EF383C7A5 |
| SHA1: | 29309A89CC92326A2986FF6FC80150CE39D8745E |
| SHA256: | E2F49C0697343A801A595DFF9A38CED80E4A8820CC3D501356754ABFBD5C8B04 |
| SSDEEP: | 48:MjcTRXXobBg2oM9QpHt5xKQRNamZBFCZ7+Gyut9K2xGf7ohXGNtPBXDlyT:MATRX4S2ouYN5dsKFCZ3ydSGA2NtJzl0 |
MALICIOUS
Gets a file object corresponding to the file in a specified path (SCRIPT)
- cscript.exe (PID: 3532)
Uses base64 encoding (SCRIPT)
- cscript.exe (PID: 3532)
SUSPICIOUS
The process executes JS scripts
- cmd.exe (PID: 3384)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 3532)
Sets XML DOM element text (SCRIPT)
- cscript.exe (PID: 3532)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- cscript.exe (PID: 3532)
Creates XML DOM element (SCRIPT)
- cscript.exe (PID: 3532)
Script creates XML DOM node (SCRIPT)
- cscript.exe (PID: 3532)
Saves data to a binary file (SCRIPT)
- cscript.exe (PID: 3532)
Writes binary data to a Stream object (SCRIPT)
- cscript.exe (PID: 3532)
Creates a Folder object (SCRIPT)
- cscript.exe (PID: 3532)
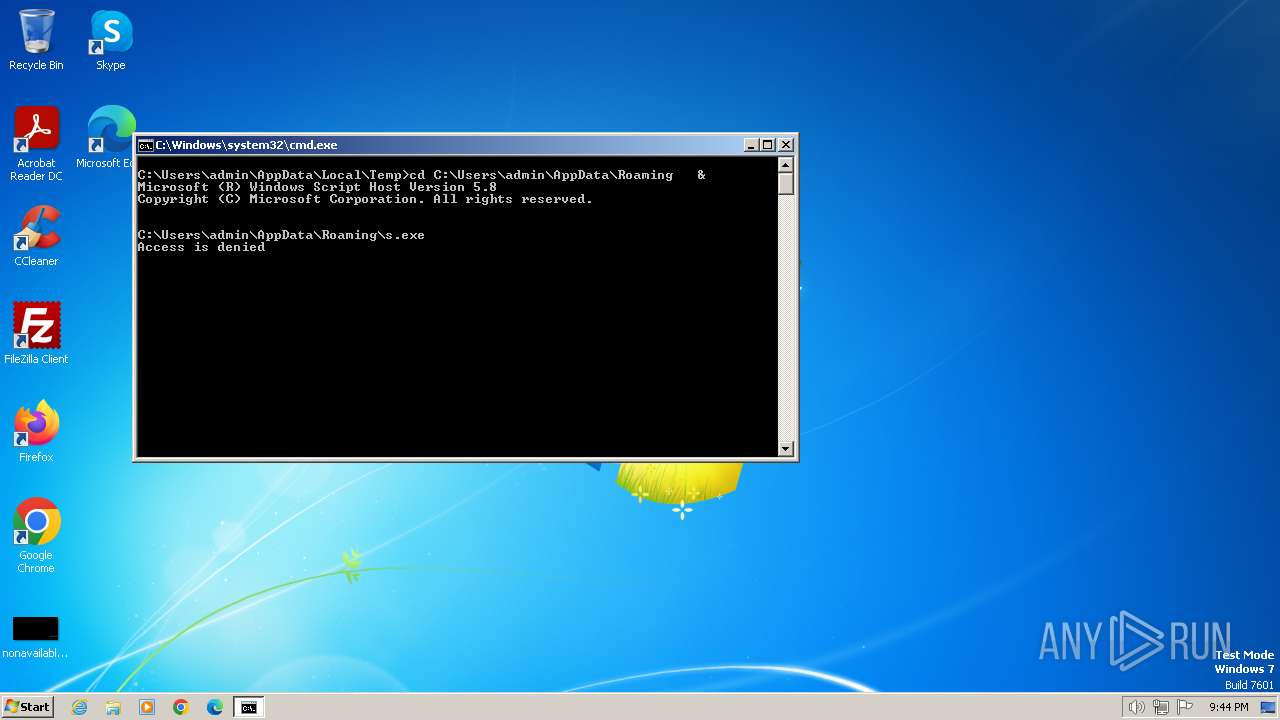
The executable file from the user directory is run by the CMD process
- s.exe (PID: 3096)
- s.exe (PID: 3196)
- s.exe (PID: 3220)
Reads the Internet Settings
- cmd.exe (PID: 3384)
- cscript.exe (PID: 3532)
Executable content was dropped or overwritten
- cscript.exe (PID: 3532)
INFO
Reads security settings of Internet Explorer
- cscript.exe (PID: 3532)
Creates files or folders in the user directory
- cscript.exe (PID: 3532)
Drops the executable file immediately after the start
- cscript.exe (PID: 3532)
Checks supported languages
- s.exe (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3096 | "C:\Users\admin\AppData\Roaming\s.exe" | C:\Users\admin\AppData\Roaming\s.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 3196 | "C:\Users\admin\AppData\Roaming\s.exe" | C:\Users\admin\AppData\Roaming\s.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3220 | "C:\Users\admin\AppData\Roaming\s.exe" | C:\Users\admin\AppData\Roaming\s.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3384 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\OIETIF.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3532 | cscript x.js | C:\Windows\System32\cscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
5 007
Read events
4 991
Write events
16
Delete events
0
Modification events
| (PID) Process: | (3532) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3532) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3532) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3532) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3384) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3384) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3384) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3384) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | s.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 3384 | cmd.exe | C:\Users\admin\AppData\Roaming\x | text | |
MD5:12D767F69C1AFFEDECA4317F0F3769B2 | SHA256:2297A03E988AB10EE392D3551B860183F60A44FADC9D5FB1ED5EE1FEA18581E1 | |||
| 3532 | cscript.exe | C:\Users\admin\AppData\Roaming\s.exe | executable | |
MD5:F65488EB1D760D8DD4D7AF57B998D97E | SHA256:433108B9E2980710769469406C928047A3FD2CF08E6B910EBEA39DF97995F1CA | |||
| 3532 | cscript.exe | C:\Users\admin\AppData\Roaming\z.zip | compressed | |
MD5:99EF3E18AA3A42AB577BC876D659091F | SHA256:1511FA661CEF3D2C5E8C85E603C28EF5B6CB0B66C47CF915AB8EE23B847F11EC | |||
| 3384 | cmd.exe | C:\Users\admin\AppData\Roaming\x.js | text | |
MD5:D94C93F882CF030ED9D66CC35796731D | SHA256:F7941E6BE49D757B46B9D6FB5ECB15392EC36A64E8906692D2EEB2BA9FC67CB6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1372 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |