| File name: | TA.exe |
| Full analysis: | https://app.any.run/tasks/f0f93d19-1576-4990-a8c1-92d7269e2959 |
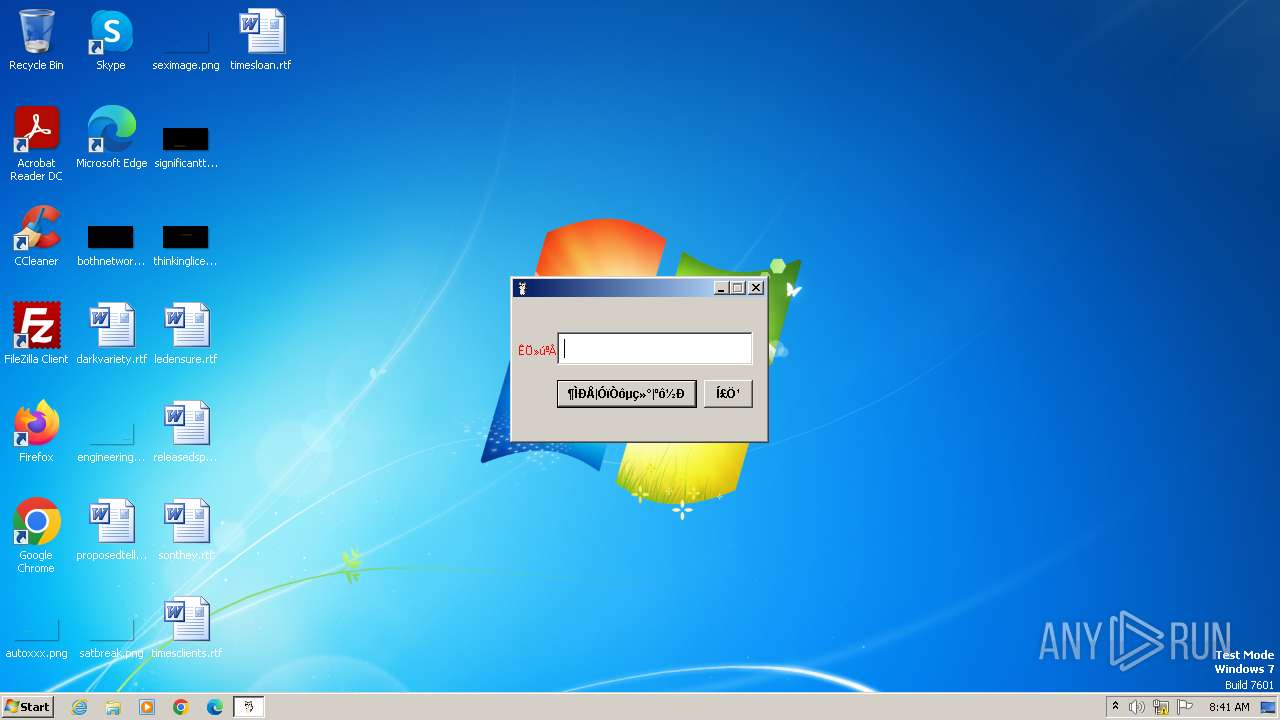
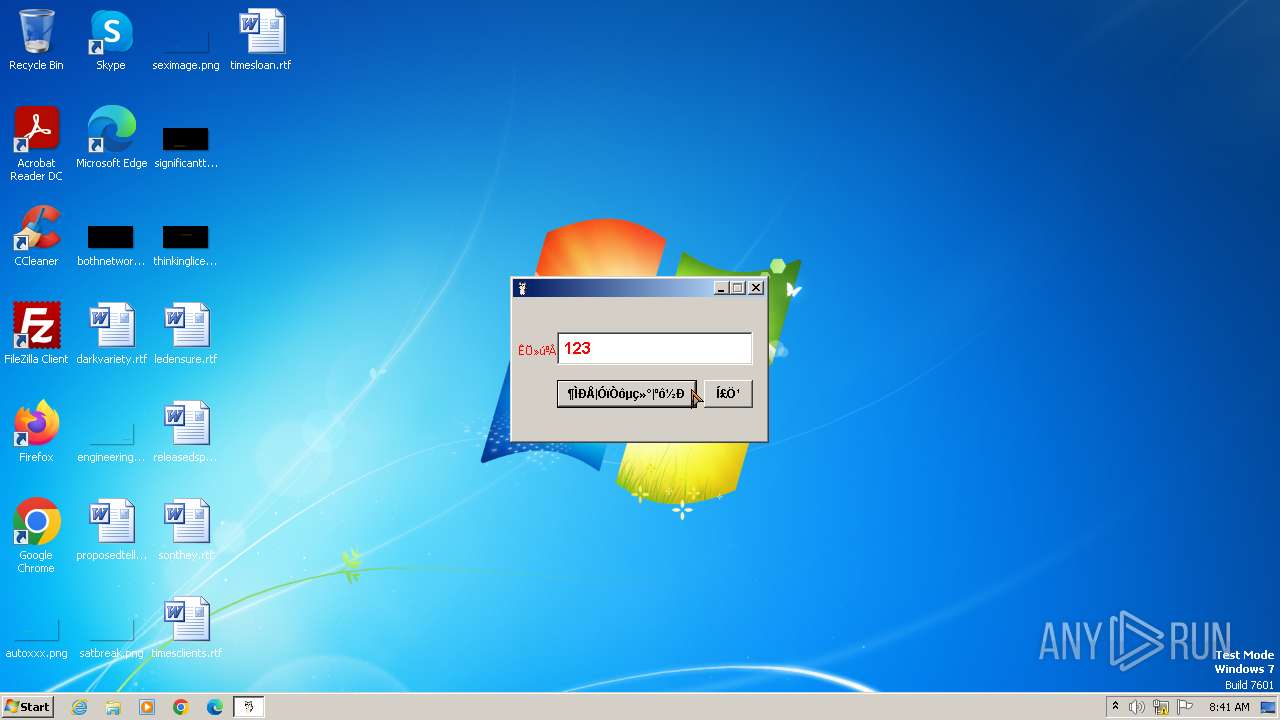
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2023, 08:41:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C11A8A38C5E29BE8C6419D493DD2CBE4 |
| SHA1: | 952636F0D3A3620BBEBC5C726D7A99788C0BBC4A |
| SHA256: | E2DD1C63B8A995B7616586157B8CECD43A460AFCCF052929CF852998B1AB4D3B |
| SSDEEP: | 49152:WY1y9Z3bu622I7r88988Nt2aydduJTTS+Se585HAMM2gqZZ:91y9Z3b12ToTgRTS+Se5Kg6Z |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads settings of System Certificates
- TA.exe (PID: 3440)
Connects to unusual port
- TA.exe (PID: 3440)
INFO
Checks supported languages
- TA.exe (PID: 3440)
- wmpnscfg.exe (PID: 2932)
Reads the computer name
- TA.exe (PID: 3440)
- wmpnscfg.exe (PID: 2932)
Manual execution by a user
- wmpnscfg.exe (PID: 2932)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 2932)
- TA.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (32.3) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (24.2) |
| .exe | | | Win64 Executable (generic) (21.4) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:09:12 07:31:56+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 937984 |
| InitializedDataSize: | 675840 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc4c9d |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
| FileDescription: | 尊重原版,谢谢 |
| ProductName: | 小懒猫呼死TA(内部测试) |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | 作者版权所有 请尊重并使用正版 |
| Comments: | 本程序使用易语言编写(http://www.eyuyan.com) |
Total processes
35
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2932 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3440 | "C:\Users\admin\AppData\Local\Temp\TA.exe" | C:\Users\admin\AppData\Local\Temp\TA.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 尊重原版,谢谢 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
3 349
Read events
3 322
Write events
20
Delete events
7
Modification events
| (PID) Process: | (2932) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{15193EDB-CF6A-4C56-9B5F-DCA967A57713}\{DDAB5A81-3EFA-4471-A655-033223ABF3A6} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2932) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{15193EDB-CF6A-4C56-9B5F-DCA967A57713} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2932) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{FF75C268-00A7-44AA-98B6-FAFA45AD6EB8} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3440) TA.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3440) TA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D69B561148F01C77C54578C10926DF5B856976AD |
| Operation: | write | Name: | Blob |
Value: 530000000100000040000000303E301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0190000000100000010000000D0FD3C9C380D7B65E26B9A3FEDD39B8F0B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D002000520033000000620000000100000020000000CBB522D7B7F127AD6A0113865BDF1CD4102E7D0759AF635A7CF4720DC963C53B1400000001000000140000008FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC1D000000010000001000000001728E1ECF7A9D86FB3CEC8948ABA953030000000100000014000000D69B561148F01C77C54578C10926DF5B856976AD0F00000001000000200000005229BA15B31B0C6F4CCA89C2985177974327D1B689A3B935A0BD975532AF22AB090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703082000000001000000630300003082035F30820247A003020102020B04000000000121585308A2300D06092A864886F70D01010B0500304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3039303331383130303030305A170D3239303331383130303030305A304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E30820122300D06092A864886F70D01010105000382010F003082010A0282010100CC2576907906782216F5C083B684CA289EFD057611C5AD8872FC460243C7B28A9D045F24CB2E4BE1608246E152AB0C8147706CDD64D1EBF52CA30F823D0C2BAE97D7B614861079BB3B1380778C08E149D26A622F1F5EFA9668DF892795389F06D73EC9CB26590D73DEB0C8E9260E8315C6EF5B8BD20460CA49A628F6693BF6CBC82891E59D8A615737AC7414DC74E03AEE722F2E9CFBD0BBBFF53D00E10633E8822BAE53A63A16738CDD410E203AC0B4A7A1E9B24F902E3260E957CBB904926868E538266075B29F77FF9114EFAE2049FCAD401548D1023161195EB897EFAD77B7649A7ABF5FC113EF9B62FB0D6CE0546916A903DA6EE983937176C6698582170203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604148FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC300D06092A864886F70D01010B050003820101004B40DBC050AAFEC80CEFF796544549BB96000941ACB3138686280733CA6BE674B9BA002DAEA40AD3F5F1F10F8ABF73674A83C7447B78E0AF6E6C6F03298E333945C38EE4B9576CAAFC1296EC53C62DE4246CB99463FBDC536867563E83B8CF3521C3C968FECEDAC253AACC908AE9F05D468C95DD7A58281A2F1DDECD0037418FED446DD75328977EF367041E15D78A96B4D3DE4C27A44C1B737376F41799C21F7A0EE32D08AD0A1C2CFF3CAB550E0F917E36EBC35749BEE12E2D7C608BC3415113239DCEF7326B9401A899E72C331F3A3B25D28640CE3B2C8678C9612F14BAEEDB556FDF84EE05094DBD28D872CED36250651EEB92978331D9B3B5CA47583F5F | |||
| (PID) Process: | (3440) TA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D69B561148F01C77C54578C10926DF5B856976AD |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3440) TA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D1EB23A46D17D68FD92564C2F1F1601764D8E349 |
| Operation: | write | Name: | Blob |
Value: 53000000010000004300000030413022060C2B06010401B231010201050130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C01900000001000000100000002AA1C05E2AE606F198C2C5E937C97AA2620000000100000020000000D7A7A0FB5D7E2731D771E9484EBCDEF71D5F0C3E0A2948782BC83EE0EA699EF40B000000010000001C0000005300650063007400690067006F002000280041004100410029000000140000000100000014000000A0110A233E96F107ECE2AF29EF82A57FD030A4B41D00000001000000100000002E0D6875874A44C820912E85E964CFDB030000000100000014000000D1EB23A46D17D68FD92564C2F1F1601764D8E3490F00000001000000140000003E8E6487F8FD27D322A269A71EDAAC5D57811286090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B06010505070308200000000100000036040000308204323082031AA003020102020101300D06092A864886F70D0101050500307B310B3009060355040613024742311B301906035504080C1247726561746572204D616E636865737465723110300E06035504070C0753616C666F7264311A3018060355040A0C11436F6D6F646F204341204C696D697465643121301F06035504030C18414141204365727469666963617465205365727669636573301E170D3034303130313030303030305A170D3238313233313233353935395A307B310B3009060355040613024742311B301906035504080C1247726561746572204D616E636865737465723110300E06035504070C0753616C666F7264311A3018060355040A0C11436F6D6F646F204341204C696D697465643121301F06035504030C1841414120436572746966696361746520536572766963657330820122300D06092A864886F70D01010105000382010F003082010A0282010100BE409DF46EE1EA76871C4D45448EBE46C883069DC12AFE181F8EE402FAF3AB5D508A16310B9A06D0C57022CD492D5463CCB66E68460B53EACB4C24C0BC724EEAF115AEF4549A120AC37AB23360E2DA8955F32258F3DEDCCFEF8386A28C944F9F68F29890468427C776BFE3CC352C8B5E07646582C048B0A891F9619F762050A891C766B5EB78620356F08A1A13EA31A31EA099FD38F6F62732586F07F56BB8FB142BAFB7AACCD6635F738CDA0599A838A8CB17783651ACE99EF4783A8DCF0FD942E2980CAB2F9F0E01DEEF9F9949F12DDFAC744D1B98B547C5E529D1F99018C7629CBE83C7267B3E8A25C7C0DD9DE6356810209D8FD8DED2C3849C0D5EE82FC90203010001A381C03081BD301D0603551D0E04160414A0110A233E96F107ECE2AF29EF82A57FD030A4B4300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF307B0603551D1F047430723038A036A0348632687474703A2F2F63726C2E636F6D6F646F63612E636F6D2F414141436572746966696361746553657276696365732E63726C3036A034A0328630687474703A2F2F63726C2E636F6D6F646F2E6E65742F414141436572746966696361746553657276696365732E63726C300D06092A864886F70D010105050003820101000856FC02F09BE8FFA4FAD67BC64480CE4FC4C5F60058CCA6B6BC1449680476E8E6EE5DEC020F60D68D50184F264E01E3E6B0A5EEBFBC745441BFFDFC12B8C74F5AF48960057F60B7054AF3F6F1C2BFC4B97486B62D7D6BCCD2F346DD2FC6E06AC3C334032C7D96DD5AC20EA70A99C1058BAB0C2FF35C3ACF6C37550987DE53406C58EFFCB6AB656E04F61BDC3CE05A15C69ED9F15948302165036CECE92173EC9B03A1E037ADA015188FFABA02CEA72CA910132CD4E50826AB229760F8905E74D4A29A53BDF2A968E0A26EC2D76CB1A30F9EBFEB68E756F2AEF2E32B383A0981B56B85D7BE2DED3F1AB7B263E2F5622C82D46A004150F139839F95E93696986E | |||
| (PID) Process: | (3440) TA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D1EB23A46D17D68FD92564C2F1F1601764D8E349 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
107
DNS requests
65
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3440 | TA.exe | POST | 200 | 47.110.217.117:80 | http://www.nejmqianyan.cn/index.php?c=register&m=send_sms | unknown | html | 15.2 Kb | unknown |
3440 | TA.exe | POST | 404 | 121.41.121.91:80 | http://www.jiaoping.com/user/makeVerCode | unknown | html | 564 b | unknown |
3440 | TA.exe | POST | 200 | 47.110.217.117:80 | http://www.nejmqianyan.cn/index.php?c=register&m=send_sms | unknown | html | 15.2 Kb | unknown |
3440 | TA.exe | POST | 503 | 8.135.45.254:80 | http://xym.xuyuanmiao.com/new/login/valid | unknown | html | 190 b | unknown |
3440 | TA.exe | POST | — | 121.41.121.91:80 | http://www.jiaoping.com/user/makeVerCode | unknown | — | — | unknown |
3440 | TA.exe | POST | 503 | 8.135.45.254:80 | http://xym.xuyuanmiao.com/new/login/valid | unknown | html | 190 b | unknown |
3440 | TA.exe | POST | 200 | 47.110.217.117:80 | http://www.nejmqianyan.cn/index.php?c=register&m=send_sms | unknown | html | 15.1 Kb | unknown |
3440 | TA.exe | POST | — | 47.110.217.117:80 | http://www.nejmqianyan.cn/index.php?c=register&m=send_sms | unknown | — | — | unknown |
3440 | TA.exe | POST | 404 | 121.41.121.91:80 | http://www.jiaoping.com/user/makeVerCode | unknown | html | 564 b | unknown |
3440 | TA.exe | POST | 404 | 121.41.121.91:80 | http://www.jiaoping.com/user/makeVerCode | unknown | html | 564 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3440 | TA.exe | 121.41.121.91:80 | www.jiaoping.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3440 | TA.exe | 52.175.28.82:443 | v4.passport.sohu.com | MICROSOFT-CORP-MSN-AS-BLOCK | HK | unknown |
3440 | TA.exe | 47.110.217.117:80 | www.nejmqianyan.cn | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3440 | TA.exe | 47.110.148.132:443 | global.lianlianpay.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3440 | TA.exe | 47.95.47.92:443 | www.huanxi.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3440 | TA.exe | 43.240.73.100:443 | i.22.cn | China Mobile communications corporation | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.jiaoping.com |
| unknown |
www.nejmqianyan.cn |
| unknown |
case.100.com |
| unknown |
global.lianlianpay.com |
| unknown |
v4.passport.sohu.com |
| unknown |
www.huanxi.com |
| unknown |
www.1ddy.com |
| unknown |
i.22.cn |
| unknown |
cloud.mfu.cn |
| unknown |
id.juranguanjia.com |
| unknown |