| URL: | https://anonfiles.com/R6x0z4idyc/Synapse_X_exe |
| Full analysis: | https://app.any.run/tasks/c69c50f8-4eff-44c4-85f2-d0a7d6303ee3 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 06:32:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5692587C432399321ABE9F2E22C4B770 |
| SHA1: | 124BD8F992ABABA25DE28AB4D649A041EACBE278 |
| SHA256: | E2C380D4E0036556A42C76DA190848B4A463DFBE873F8422DC03BA5078B8AB97 |
| SSDEEP: | 3:N8M2O0K26EcY4An:2M23EE5n |
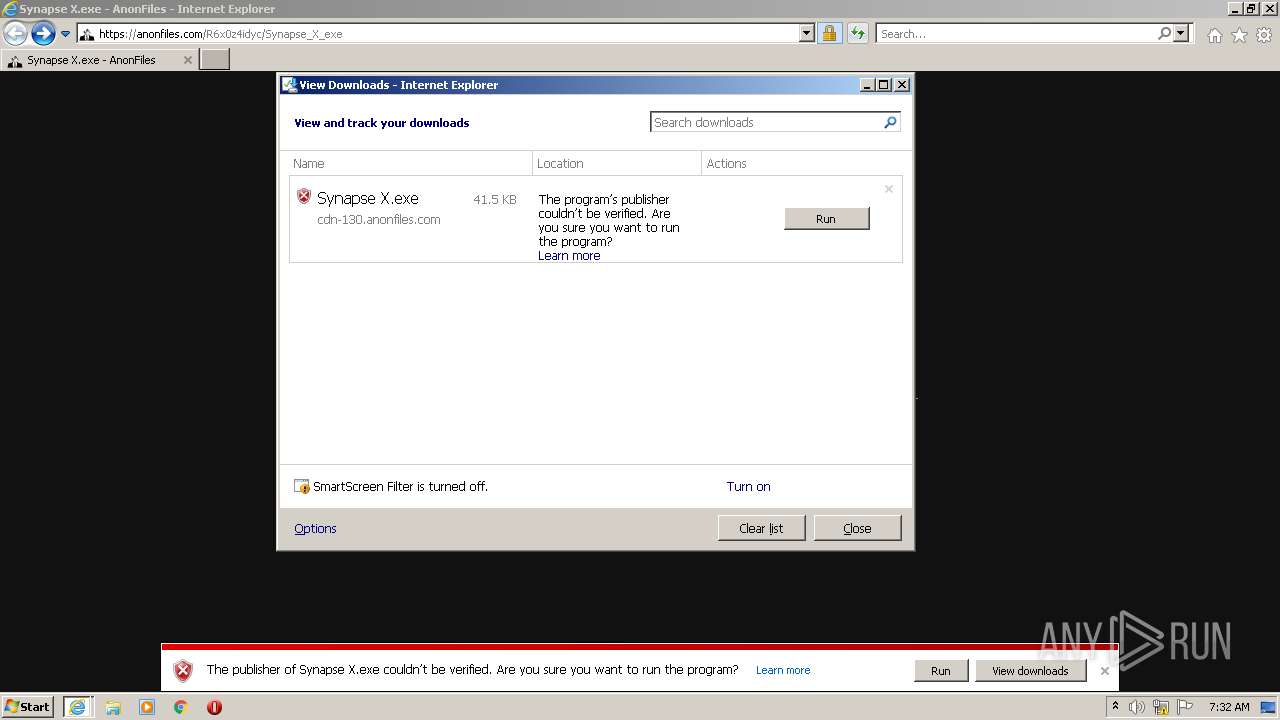
MALICIOUS
Drops executable file immediately after starts
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2936)
Application was dropped or rewritten from another process
- Synapse X.exe (PID: 1064)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3376)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2936)
Drops a file with a compile date too recent
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2936)
Reads the computer name
- Synapse X.exe (PID: 1064)
Checks supported languages
- Synapse X.exe (PID: 1064)
INFO
Checks supported languages
- iexplore.exe (PID: 2936)
- iexplore.exe (PID: 3376)
Changes internet zones settings
- iexplore.exe (PID: 2936)
Application launched itself
- iexplore.exe (PID: 2936)
Checks Windows Trust Settings
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2936)
Reads settings of System Certificates
- iexplore.exe (PID: 2936)
- iexplore.exe (PID: 3376)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2936)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2936)
Reads the computer name
- iexplore.exe (PID: 2936)
- iexplore.exe (PID: 3376)
Reads internet explorer settings
- iexplore.exe (PID: 3376)
Changes settings of System certificates
- iexplore.exe (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1064 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Synapse X.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Synapse X.exe | — | iexplore.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2936 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://anonfiles.com/R6x0z4idyc/Synapse_X_exe" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2936 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
19 895
Read events
19 768
Write events
125
Delete events
2
Modification events
| (PID) Process: | (2936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960860 | |||
| (PID) Process: | (2936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960860 | |||
| (PID) Process: | (2936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2936) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
3
Suspicious files
16
Text files
30
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE056.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE045.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE057.tmp | cat | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE046.tmp | cat | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\34195BFB217E10391B83D6B576B83BD0 | der | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Synapse_X_exe[1].htm | html | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\34195BFB217E10391B83D6B576B83BD0 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
32
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3376 | iexplore.exe | GET | 200 | 92.123.195.28:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgNu0fhzwLRxYIjzRdYSnQiCNw%3D%3D | unknown | der | 503 b | shared |
3376 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0d968b90b26f608f | US | compressed | 60.0 Kb | whitelisted |
3376 | iexplore.exe | GET | 200 | 18.64.100.55:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3376 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHophRq39F1meVBmQbb%2F1x0%3D | US | der | 1.40 Kb | whitelisted |
3376 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?2d01434a46b7a66d | US | compressed | 60.0 Kb | whitelisted |
3376 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?84e65fa95d72fa7a | US | compressed | 4.70 Kb | whitelisted |
3376 | iexplore.exe | GET | 200 | 18.66.242.58:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3376 | iexplore.exe | GET | 200 | 104.89.32.83:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
3376 | iexplore.exe | GET | 200 | 18.66.242.45:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2936 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3376 | iexplore.exe | 45.154.253.151:443 | anonfiles.com | — | — | suspicious |
3376 | iexplore.exe | 104.89.32.83:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
2936 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3376 | iexplore.exe | 92.123.195.28:80 | r3.o.lencr.org | Akamai International B.V. | — | suspicious |
3376 | iexplore.exe | 151.101.66.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
3376 | iexplore.exe | 18.66.242.45:80 | ocsp.rootg2.amazontrust.com | Massachusetts Institute of Technology | US | whitelisted |
3376 | iexplore.exe | 18.66.242.58:80 | ocsp.rootg2.amazontrust.com | Massachusetts Institute of Technology | US | whitelisted |
2936 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3376 | iexplore.exe | 45.154.253.59:443 | cdn-130.anonfiles.com | — | — | unknown |
2936 | iexplore.exe | 45.154.253.151:443 | anonfiles.com | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
ocsp2.globalsign.com |
| whitelisted |
o.ss2.us |
| whitelisted |