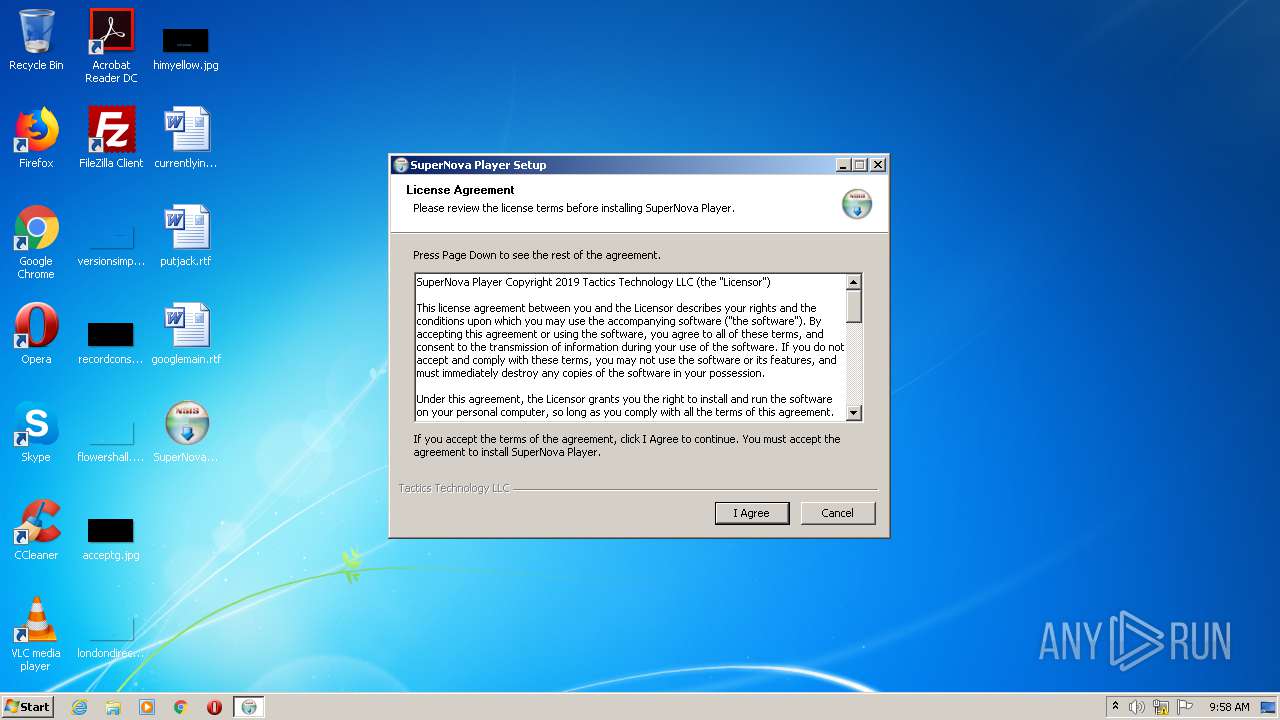
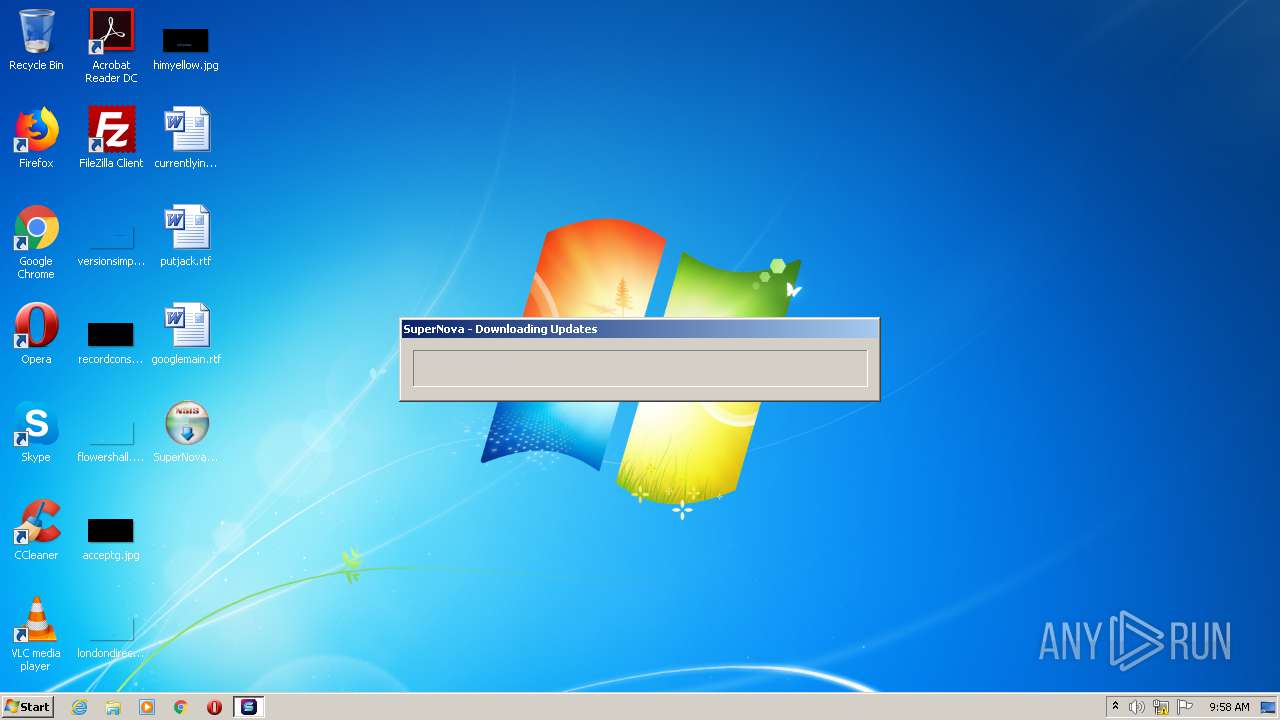
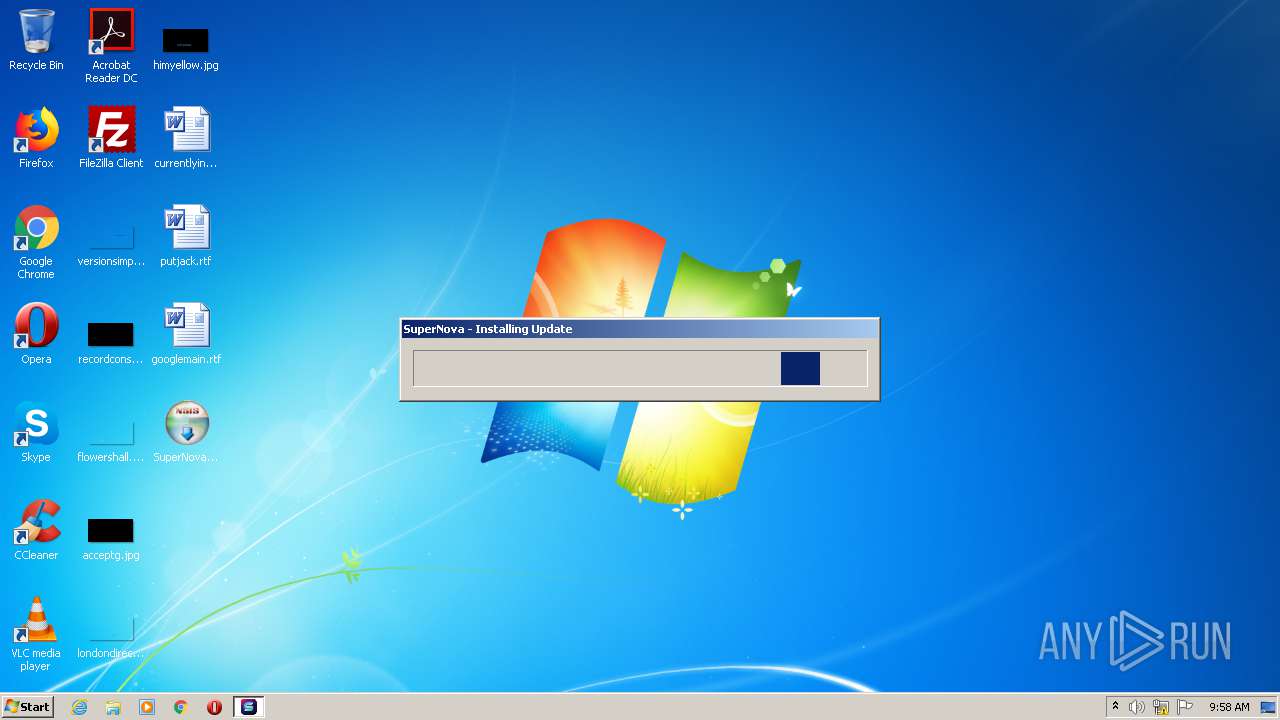
| File name: | SuperNovaSetup.exe |
| Full analysis: | https://app.any.run/tasks/cf9fe446-c086-44cd-9901-0d77a5260d07 |
| Verdict: | Malicious activity |
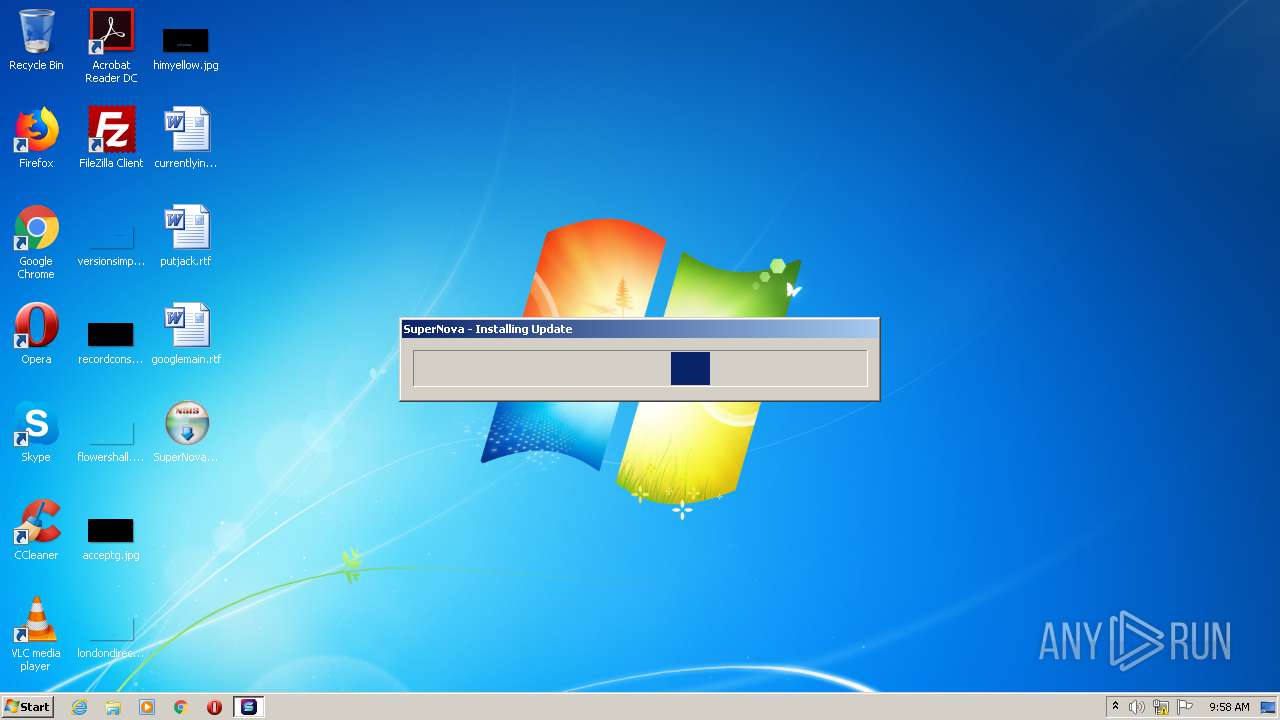
| Analysis date: | January 17, 2021, 09:58:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 3F6D3AC37364C2D0DFE2169FDAD4F6C1 |
| SHA1: | 900F03D3E357E7D877E5C13FA7EEE236ACDDEFAC |
| SHA256: | E2B12EC20216D087D95C26A1AC3FA05491BAB26483DDECE7FB575286836863F2 |
| SSDEEP: | 24576:WsGIZyqCBZI3OzsT4++brcco8WlLpeyu4NNqZ6DQgIzCnHjWym3yo:5yqCCOz7brVoH00N2428H/m3H |
MALICIOUS
Application was dropped or rewritten from another process
- SuperNova Launcher.exe (PID: 2688)
- chginteg.exe (PID: 2184)
- chginteg.exe (PID: 3544)
- chginteg.exe (PID: 2388)
- chginteg.exe (PID: 2256)
- chginteg.exe (PID: 2408)
- chginteg.exe (PID: 3628)
- chginteg.exe (PID: 2264)
- patchfile.tmp (PID: 2384)
SUSPICIOUS
Executable content was dropped or overwritten
- patchfile.tmp (PID: 2384)
- SuperNovaSetup.exe (PID: 1020)
- SuperNova Launcher.exe (PID: 2688)
Creates a software uninstall entry
- patchfile.tmp (PID: 2384)
- SuperNovaSetup.exe (PID: 1020)
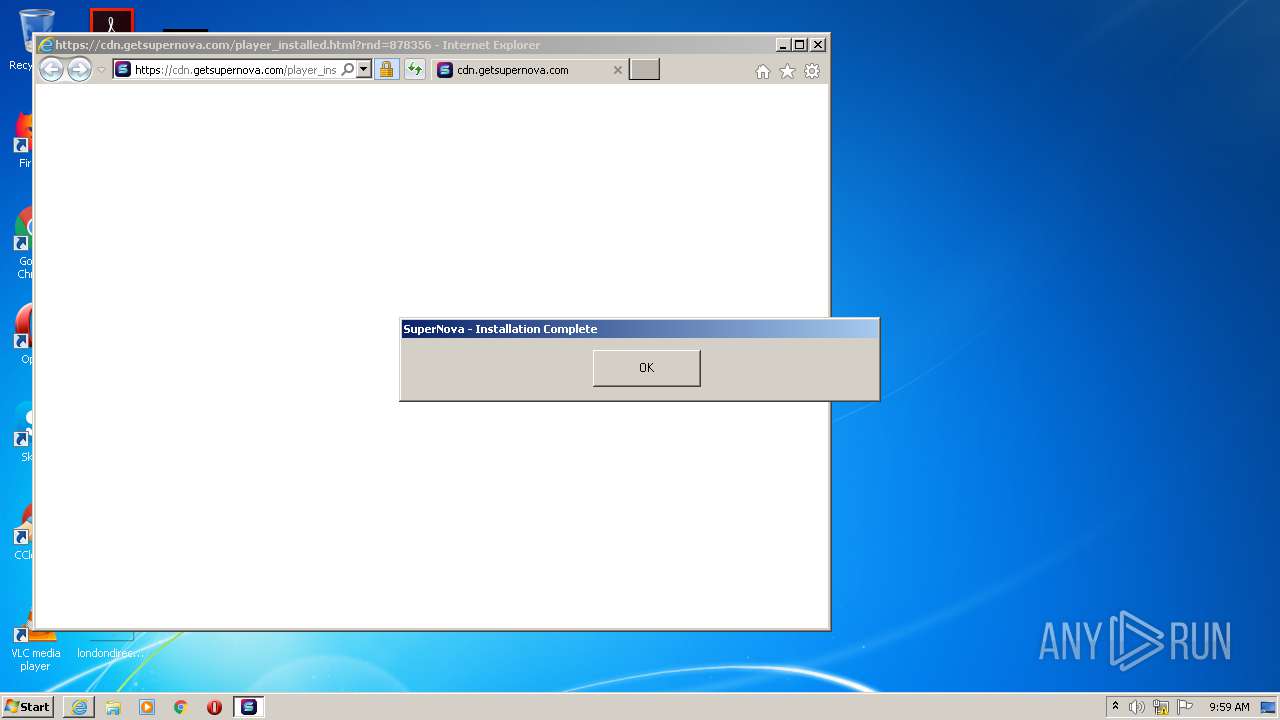
Starts Internet Explorer
- patchfile.tmp (PID: 2384)
Drops a file that was compiled in debug mode
- SuperNovaSetup.exe (PID: 1020)
- patchfile.tmp (PID: 2384)
Creates files in the user directory
- patchfile.tmp (PID: 2384)
Changes default file association
- patchfile.tmp (PID: 2384)
Starts application with an unusual extension
- SuperNova Launcher.exe (PID: 2688)
INFO
Application launched itself
- iexplore.exe (PID: 2436)
Reads internet explorer settings
- iexplore.exe (PID: 1976)
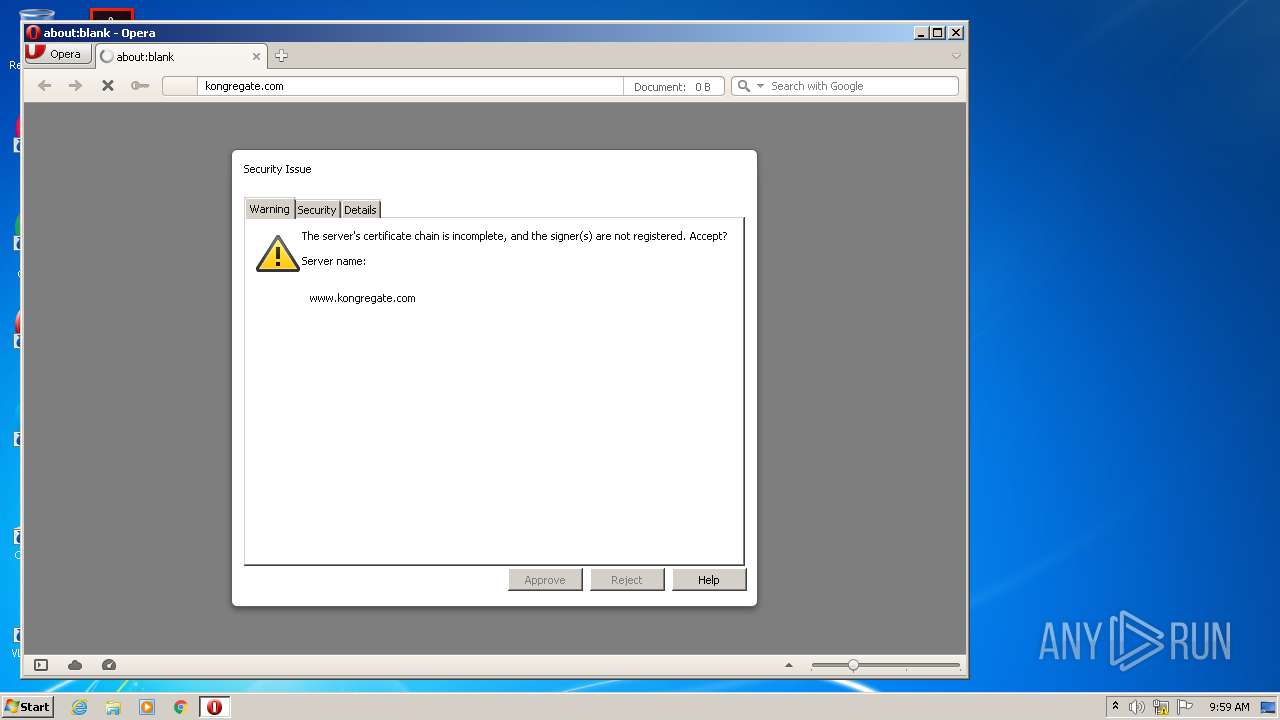
Changes internet zones settings
- iexplore.exe (PID: 2436)
Reads settings of System Certificates
- iexplore.exe (PID: 2436)
- iexplore.exe (PID: 1976)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2436)
Changes settings of System certificates
- iexplore.exe (PID: 2436)
Manual execution by user
- opera.exe (PID: 2960)
Creates files in the user directory
- opera.exe (PID: 2960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x320c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:41 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000628F | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44221 |
.rdata | 0x00008000 | 0x0000135C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.24004 |
.data | 0x0000A000 | 0x00025518 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04938 |
.ndata | 0x00030000 | 0x0000E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003E000 | 0x000042C0 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.93415 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29611 | 1059 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
47
Monitored processes
13
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "C:\Users\admin\Desktop\SuperNovaSetup.exe" | C:\Users\admin\Desktop\SuperNovaSetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2436 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2184 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\chginteg.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low" -low | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\chginteg.exe | — | patchfile.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2256 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\chginteg.exe" "C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\www.macromedia.com" -low | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\chginteg.exe | — | patchfile.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2264 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\chginteg.exe" "C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sol" -med | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\chginteg.exe | — | patchfile.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3 Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.0.0\patchfile.tmp" /S | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.0.0\patchfile.tmp | SuperNova Launcher.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2388 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\chginteg.exe" "C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com" -low | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\chginteg.exe | — | patchfile.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2408 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\chginteg.exe" "C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\Logs" -low | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\chginteg.exe | — | patchfile.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Internet Explorer\iexplore.exe" https://cdn.getsupernova.com/player_installed.html?rnd=878356 | C:\Program Files\Internet Explorer\iexplore.exe | patchfile.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2688 | "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.0.0\SuperNova Launcher.exe" | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.0.0\SuperNova Launcher.exe | SuperNovaSetup.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 267
Read events
1 047
Write events
216
Delete events
4
Modification events
| (PID) Process: | (1020) SuperNovaSetup.exe | Key: | HKEY_CURRENT_USER\Software\TacticsTechnologySuperNova |
| Operation: | write | Name: | Install_Dir |
Value: C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova | |||
| (PID) Process: | (1020) SuperNovaSetup.exe | Key: | HKEY_CURRENT_USER\Software\TacticsTechnologySuperNova |
| Operation: | write | Name: | Version |
Value: 0.0.0 | |||
| (PID) Process: | (1020) SuperNovaSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\TacticsTechnologySuperNova |
| Operation: | write | Name: | DisplayName |
Value: SuperNova Player | |||
| (PID) Process: | (1020) SuperNovaSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\TacticsTechnologySuperNova |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\uninstall.exe" | |||
| (PID) Process: | (1020) SuperNovaSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\TacticsTechnologySuperNova |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.0.0\SuperNova Launcher.exe | |||
| (PID) Process: | (1020) SuperNovaSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\TacticsTechnologySuperNova |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (1020) SuperNovaSetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\TacticsTechnologySuperNova |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (2384) patchfile.tmp | Key: | HKEY_CURRENT_USER\Software\TacticsTechnologySuperNova |
| Operation: | write | Name: | Install_Dir |
Value: C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova | |||
| (PID) Process: | (2384) patchfile.tmp | Key: | HKEY_CURRENT_USER\Software\TacticsTechnologySuperNova |
| Operation: | write | Name: | Version |
Value: 0.1.21 | |||
| (PID) Process: | (2384) patchfile.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\TacticsTechnologySuperNova |
| Operation: | write | Name: | DisplayName |
Value: SuperNova Player | |||
Executable files
26
Suspicious files
34
Text files
61
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2688 | SuperNova Launcher.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.0.0\~patchfile.tmp | — | |
MD5:— | SHA256:— | |||
| 2688 | SuperNova Launcher.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.0.0\patchversion | — | |
MD5:— | SHA256:— | |||
| 2688 | SuperNova Launcher.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.0.0\patchfile.tmp | executable | |
MD5:— | SHA256:— | |||
| 2384 | patchfile.tmp | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\launcher\snlauncher.swf | swf | |
MD5:— | SHA256:— | |||
| 2384 | patchfile.tmp | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\launcher\snlauncher.exe | executable | |
MD5:— | SHA256:— | |||
| 2384 | patchfile.tmp | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\launcher\META-INF\signatures.xml | text | |
MD5:— | SHA256:— | |||
| 1020 | SuperNovaSetup.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\license.txt | text | |
MD5:735FAEFD349186FE6ACC42A7AEFFB48F | SHA256:94696D8C8A0A12C2025D55BFC749530CF886B2B1C82461D246855D3F0DDFF8F5 | |||
| 1020 | SuperNovaSetup.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.0.0\SuperNova Launcher.exe | executable | |
MD5:A35D5F372F46820311C59840EBA6FFFB | SHA256:EAD1DCFD124FE9005917B375EBC950A9770C49C218236EDA7B46C680C015354F | |||
| 1020 | SuperNovaSetup.exe | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\uninstall.exe | executable | |
MD5:5FF72AEB133B1819DCD7BCDEB04A521C | SHA256:7488D42E602B1CE062B4B07D1A63CEC14342812EE79F86019020F46CFD2DB0CF | |||
| 2384 | patchfile.tmp | C:\Users\admin\AppData\Local\TacticsTechnology\SuperNova\versions\0.1.21\currentversion | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
31
DNS requests
14
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2960 | opera.exe | GET | 301 | 65.9.58.12:80 | http://kongregate.com/ | US | — | — | whitelisted |
— | — | GET | 200 | 2.16.186.10:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgNRc4ab%2FFw1%2F%2FteYB3lFEg8aA%3D%3D | unknown | der | 503 b | shared |
2960 | opera.exe | GET | 200 | 172.217.212.100:80 | http://clients1.google.com/complete/search?q=kongre&client=opera-suggest-omnibox&hl=de | US | text | 127 b | whitelisted |
2436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2960 | opera.exe | GET | 200 | 172.217.212.100:80 | http://clients1.google.com/complete/search?q=kon&client=opera-suggest-omnibox&hl=de | US | text | 122 b | whitelisted |
2436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2960 | opera.exe | GET | 200 | 172.217.212.100:80 | http://clients1.google.com/complete/search?q=kongregat&client=opera-suggest-omnibox&hl=de | US | text | 156 b | whitelisted |
2960 | opera.exe | GET | 302 | 199.232.193.36:80 | http://www.kongregate.com/ | US | html | 93 b | suspicious |
— | — | GET | 200 | 2.16.186.27:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2688 | SuperNova Launcher.exe | 185.59.220.197:443 | cdn.getsupernova.com | Datacamp Limited | DE | unknown |
— | — | 2.16.186.27:80 | crl.identrust.com | Akamai International B.V. | — | whitelisted |
— | — | 2.16.186.10:80 | crl.identrust.com | Akamai International B.V. | — | whitelisted |
2436 | iexplore.exe | 185.59.220.197:443 | cdn.getsupernova.com | Datacamp Limited | DE | unknown |
1976 | iexplore.exe | 185.59.220.197:443 | cdn.getsupernova.com | Datacamp Limited | DE | unknown |
2436 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2436 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2436 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2960 | opera.exe | 199.232.193.36:443 | www.kongregate.com | — | US | suspicious |
2960 | opera.exe | 199.232.193.36:80 | www.kongregate.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.getsupernova.com |
| malicious |
crl.identrust.com |
| whitelisted |
r3.o.lencr.org |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
certs.opera.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2960 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2960 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2960 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2960 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2960 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2960 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |